Powerpoint Templates and Google slides for Utilize Security Tools
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
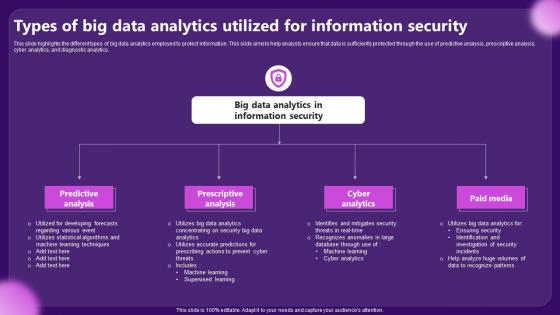 Types Of Big Data Analytics Utilized For Information Security
Types Of Big Data Analytics Utilized For Information SecurityThis slide highlights the different types of big data analytics employed to protect information. This slide aims to help analysts ensure that data is sufficiently protected through the use of predictive analysis, prescriptive analysis, cyber analytics, and diagnostic analytics. Presenting our set of slides with Types Of Big Data Analytics Utilized For Information Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Predictive Analysis, Prescriptive Analysis.
-
 Overview Of Utility Tokens With Pros And Cons Security Token Offerings BCT SS
Overview Of Utility Tokens With Pros And Cons Security Token Offerings BCT SSThe following slide illustrates brief introduction of utility token offerings to facilitate tokenization of assets along with its pros and cons. It includes elements such as offering accessibility, providing rewards, ensuring high liquidity, changing market conditions, etc. Increase audience engagement and knowledge by dispensing information using Overview Of Utility Tokens With Pros And Cons Security Token Offerings BCT SS. This template helps you present information on two stages. You can also present information on Provides Accessibility, Particular Services, Market Conditions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
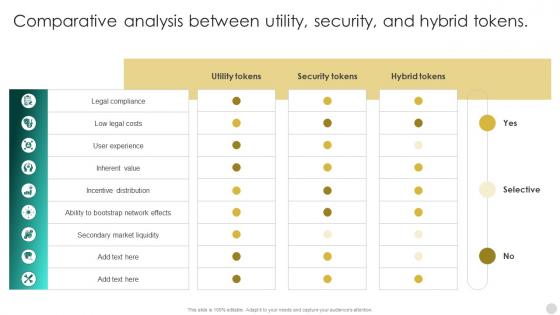 Crypto Tokens Unlocking Comparative Analysis Between Utility Security And Hybrid BCT SS
Crypto Tokens Unlocking Comparative Analysis Between Utility Security And Hybrid BCT SSThis slide compares security and utility tokens based on regulation, ownership rights, profitability, use case, liquidity, token value, security, redemption, etc. Present the topic in a bit more detail with this Crypto Tokens Unlocking Comparative Analysis Between Utility Security And Hybrid BCT SS Use it as a tool for discussion and navigation on Utility Tokens, Security Tokens, Hybrid Tokens This template is free to edit as deemed fit for your organization. Therefore download it now.
-
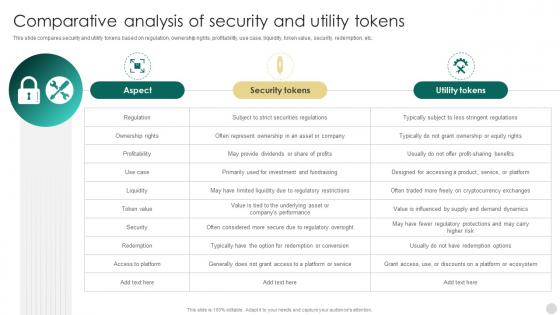 Crypto Tokens Unlocking Comparative Analysis Of Security And Utility Tokens BCT SS
Crypto Tokens Unlocking Comparative Analysis Of Security And Utility Tokens BCT SSDeliver an outstanding presentation on the topic using this Crypto Tokens Unlocking Comparative Analysis Of Security And Utility Tokens BCT SS Dispense information and present a thorough explanation of Aspect, Security Tokens, Utility Tokens using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Advantages Of Utilizing Advanced Threat Protection In Cyber Security
Advantages Of Utilizing Advanced Threat Protection In Cyber SecurityThe following slide highlights the possible benefits of implementing advanced threat protection against sophisticated cyber threats and attacks. Presenting our set of slides with Advantages Of Utilizing Advanced Threat Protection In Cyber Security. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security, Analytics, Protection.
-
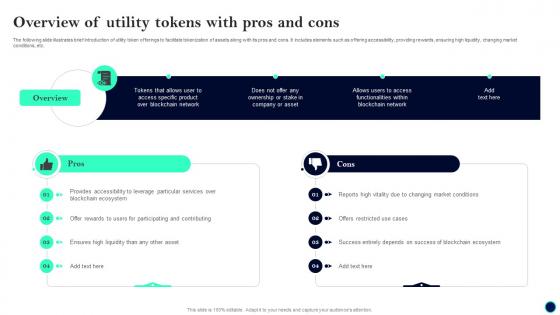 Overview Of Utility Beginners Guide To Successfully Launch Security Token BCT SS V
Overview Of Utility Beginners Guide To Successfully Launch Security Token BCT SS VThe following slide illustrates brief introduction of utility token offerings to facilitate tokenization of assets along with its pros and cons. It includes elements such as offering accessibility, providing rewards, ensuring high liquidity, changing market conditions, etc. Increase audience engagement and knowledge by dispensing information using Overview Of Utility Beginners Guide To Successfully Launch Security Token BCT SS V. This template helps you present information on two stages. You can also present information on Market Conditions, Blockchain Ecosystem, Overview using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
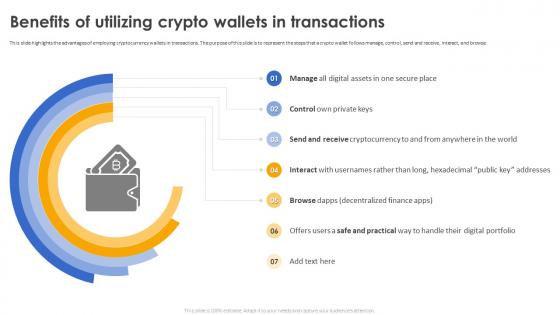 Secure Your Digital Assets Benefits Of Utilizing Crypto Wallets In Transactions
Secure Your Digital Assets Benefits Of Utilizing Crypto Wallets In TransactionsThis slide highlights the advantages of employing cryptocurrency wallets in transactions. The purpose of this slide is to represent the steps that a crypto wallet follows manage, control, send and receive, interact, and browse. Increase audience engagement and knowledge by dispensing information using Secure Your Digital Assets Benefits Of Utilizing Crypto Wallets In Transactions. This template helps you present information on seven stages. You can also present information on Employing Cryptocurrency, Wallets In Transactions, Interact And Browse, Digital Portfolio using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icon For Utilization Of Blockchain In Automotive Cyber Security
Icon For Utilization Of Blockchain In Automotive Cyber SecurityPresenting our set of slides with Icon For Utilization Of Blockchain In Automotive Cyber Security This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Icon For Utilization, Blockchain In Automotive, Cyber Security
-
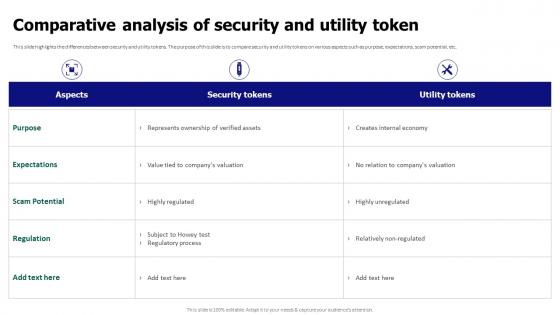 Comparative Analysis Of Security And Utility Token Tokenization For Improved Data Security
Comparative Analysis Of Security And Utility Token Tokenization For Improved Data SecurityThis slide highlights the differences between security and utility tokens. The purpose of this slide is to compare security and utility tokens on various aspects such as purpose, expectations, scam potential, etc. Present the topic in a bit more detail with this Comparative Analysis Of Security And Utility Token Tokenization For Improved Data Security. Use it as a tool for discussion and navigation on Comparative Analysis, Security And Utility Token, Expectations, Scam Potential. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
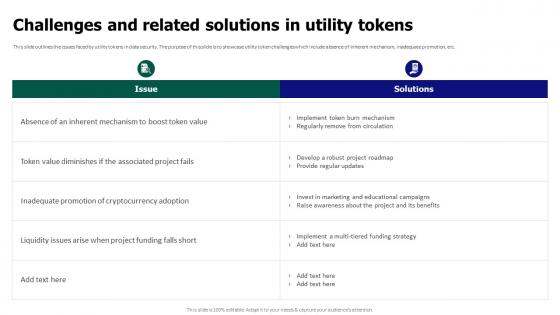 Tokenization For Improved Data Security Challenges And Related Solutions In Utility Tokens
Tokenization For Improved Data Security Challenges And Related Solutions In Utility TokensThis slide outlines the issues faced by utility tokens in data security. The purpose of this slide is to showcase utility token challenges which include absence of inherent mechanism, inadequate promotion, etc. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Challenges And Related Solutions In Utility Tokens. Dispense information and present a thorough explanation of Regularly Remove From Circulation, Inadequate Promotion, Cryptocurrency Adoption using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
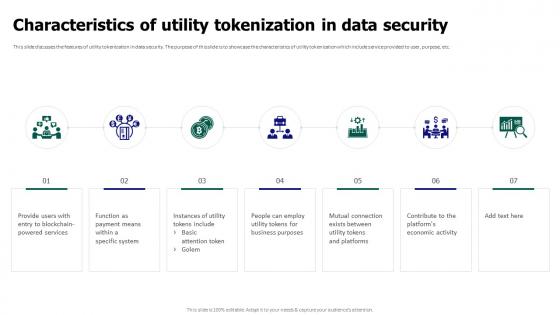 Tokenization For Improved Data Security Characteristics Of Utility Tokenization In Data Security
Tokenization For Improved Data Security Characteristics Of Utility Tokenization In Data SecurityThis slide discusses the features of utility tokenization in data security. The purpose of this slide is to showcase the characteristics of utility tokenization which include service provided to user, purpose, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Characteristics Of Utility Tokenization In Data Security. This template helps you present information on seven stages. You can also present information on Utility Tokenization, Data Security, Platforms Economic Activity, Blockchain Powered Services using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
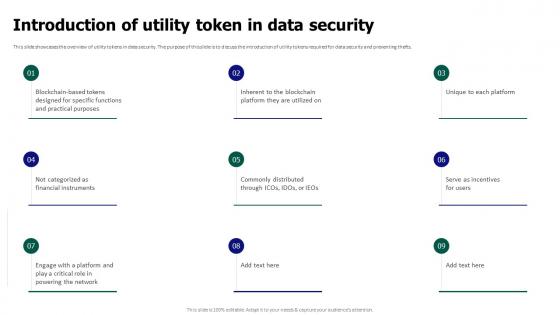 Tokenization For Improved Data Security Introduction Of Utility Token In Data Security
Tokenization For Improved Data Security Introduction Of Utility Token In Data SecurityThis slide showcases the overview of utility tokens in data security. The purpose of this slide is to discuss the introduction of utility tokens required for data security and preventing thefts. Introducing Tokenization For Improved Data Security Introduction Of Utility Token In Data Security to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Data Security, Utility Tokens, Preventing Thefts, Unique To Each Platform, using this template. Grab it now to reap its full benefits.
-
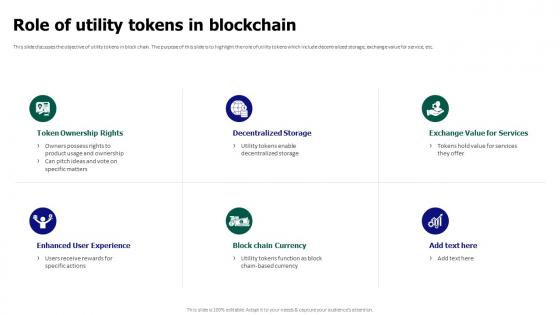 Tokenization For Improved Data Security Role Of Utility Tokens In Blockchain
Tokenization For Improved Data Security Role Of Utility Tokens In BlockchainThis slide discusses the objective of utility tokens in block chain. The purpose of this slide is to highlight the role of utility tokens which include decentralized storage, exchange value for service, etc. Introducing Tokenization For Improved Data Security Role Of Utility Tokens In Blockchain to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Decentralized Storage, Block Chain Currency, Enhanced User Experience, Token Ownership Rights, using this template. Grab it now to reap its full benefits.
-
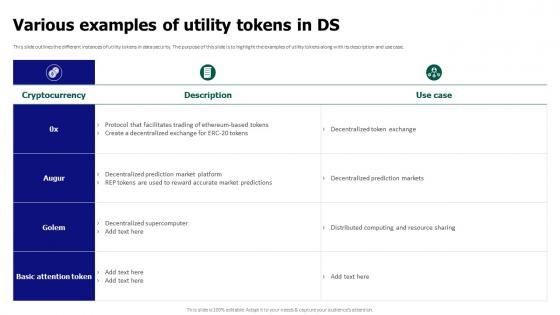 Tokenization For Improved Data Security Various Examples Of Utility Tokens In Ds
Tokenization For Improved Data Security Various Examples Of Utility Tokens In DsThis slide outlines the different instances of utility tokens in data security. The purpose of this slide is to highlight the examples of utility tokens along with its description and use case. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Various Examples Of Utility Tokens In Ds. Dispense information and present a thorough explanation of Decentralized Token Exchange, Decentralized Prediction Markets, Distributed Computing And Resource using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Icon For Utilization Of Blockchain In Retail Cyber Security
Icon For Utilization Of Blockchain In Retail Cyber SecurityPresenting our well structured Icon For Utilization Of Blockchain In Retail Cyber Security The topics discussed in this slide are Icon For Utilization Of Blockchain, Retail Cyber Security This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
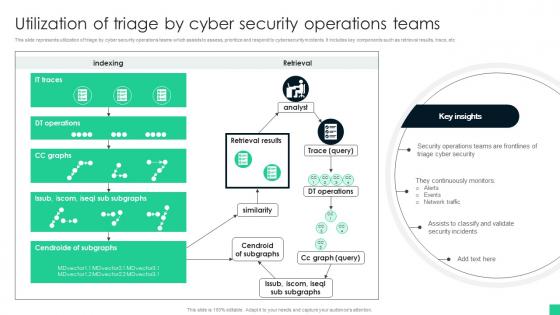 Utilization Of Triage By Cyber Security Operations Teams
Utilization Of Triage By Cyber Security Operations TeamsThis slide represents utilization of triage by cyber security operations teams which assists to assess, prioritize and respond to cybersecurity incidents. It includes key components such as retrieval results, trace, etc Introducing our Utilization Of Triage By Cyber Security Operations Teams set of slides. The topics discussed in these slides are Triage Cyber Security, Network Traffic, Security Incidents. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
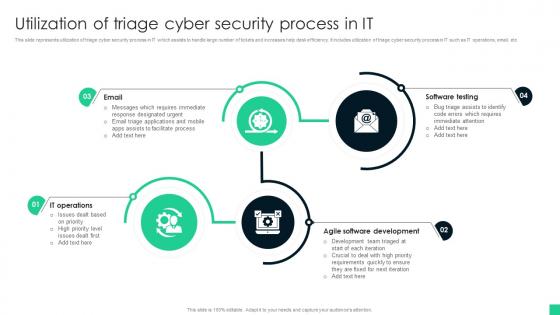 Utilization Of Triage Cyber Security Process In It
Utilization Of Triage Cyber Security Process In ItThis slide represents utilization of triage cyber security process in IT which assists to handle large number of tickets and increases help desk efficiency. It includes utilization of triage cyber security process in IT such as IT operations, email, etc Presenting our set of slides with name Utilization Of Triage Cyber Security Process In It This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Software Testing, Agile Software Development, IT Operations
-
 Utilization Of Advanced Encryption Standards In Secure File Transfer
Utilization Of Advanced Encryption Standards In Secure File TransferThis slide represents working of advanced encryption standards which assists to encrypt files and folders on computers, external devices and cloud storage. It includes key components such as client, server, public key, etc. Introducing our premium set of slides with name Utilization Of Advanced Encryption Standards In Secure File Transfer. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Utilizes Combination, Encrypts Actual Data, Implemented. So download instantly and tailor it with your information.
-
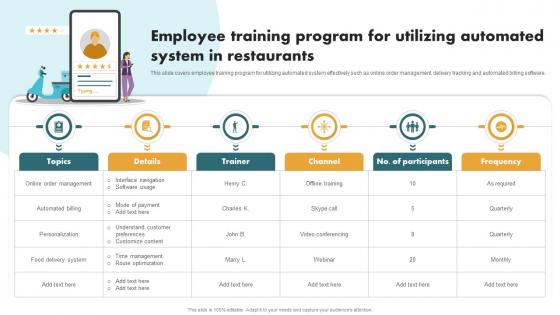 Securing Food Safety In Online Employee Training Program For Utilizing Automated
Securing Food Safety In Online Employee Training Program For Utilizing AutomatedThis slide covers employee training program for utilizing automated system effectively such as online order management, delivery tracking and automated billing software. Introducing Securing Food Safety In Online Employee Training Program For Utilizing Automated to increase your presentation threshold. Encompassed with Six stages, this template is a great option to educate and entice your audience. Dispence information on Online Order Management, Automated Billing, Personalization, Food Delivery System, using this template. Grab it now to reap its full benefits.
-
 Securing Food Safety In Online Utilizing Food Delivery Management System
Securing Food Safety In Online Utilizing Food Delivery Management SystemThis slide covers utilizing food delivery management software to keep track of deliveries. It involves bill number, channel and estimated duration. Introducing Securing Food Safety In Online Utilizing Food Delivery Management System to increase your presentation threshold. Encompassed with One stages, this template is a great option to educate and entice your audience. Dispence information on Bill Number, Channel, Customer Location, Estimated Duration, using this template. Grab it now to reap its full benefits.
-
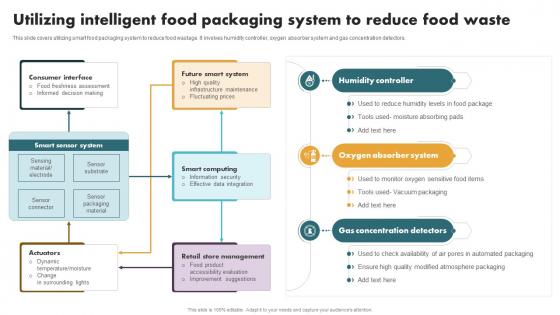 Securing Food Safety In Online Utilizing Intelligent Food Packaging System To Reduce
Securing Food Safety In Online Utilizing Intelligent Food Packaging System To ReduceThis slide covers utilizing smart food packaging system to reduce food wastage. It involves humidity controller, oxygen absorber system and gas concentration detectors. Present the topic in a bit more detail with this Securing Food Safety In Online Utilizing Intelligent Food Packaging System To Reduce. Use it as a tool for discussion and navigation on Humidity Controller, Oxygen Absorber System, Gas Concentration Detectors. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
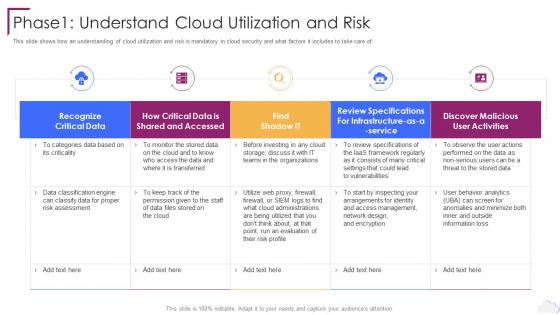 Cloud Computing Security Phase1 Understand Cloud Utilization And Risk
Cloud Computing Security Phase1 Understand Cloud Utilization And RiskThis slide shows how an understanding of cloud utilization and risk is mandatory in cloud security and what factors it includes to take care of. Present the topic in a bit more detail with this Cloud Computing Security Phase1 Understand Cloud Utilization And Risk. Use it as a tool for discussion and navigation on Recognize Critical Data, User Activities, Risk Assessment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Phase 1 Understand Cloud Utilization And Risk Cloud Information Security
Phase 1 Understand Cloud Utilization And Risk Cloud Information SecurityThis slide shows how an understanding of cloud utilization and risk is mandatory in cloud security and what factors it includes to take care of.Introducing Phase 1 Understand Cloud Utilization And Risk Cloud Information Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Authentication Process, Cloud Access, Eliminate Malware using this template. Grab it now to reap its full benefits.
-
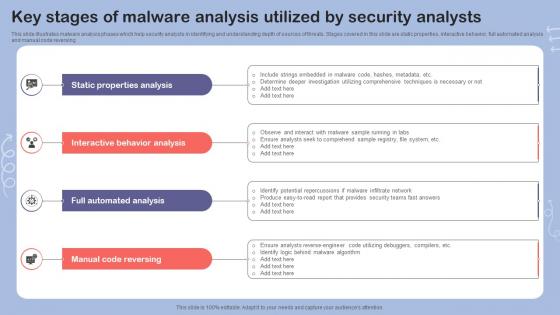 Key Stages Of Malware Analysis Utilized By Security Analysts
Key Stages Of Malware Analysis Utilized By Security AnalystsThis slide illustrates malware analysis phases which help security analysts in identifying and understanding depth of sources of threats. Stages covered in this slide are static properties, interactive behavior, full automated analysis and manual code reversing. Introducing our premium set of slides with name Key Stages Of Malware Analysis Utilized By Security Analysts. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Properties Analysis, Behavior Analysis, Automated Analysis. So download instantly and tailor it with your information.
-
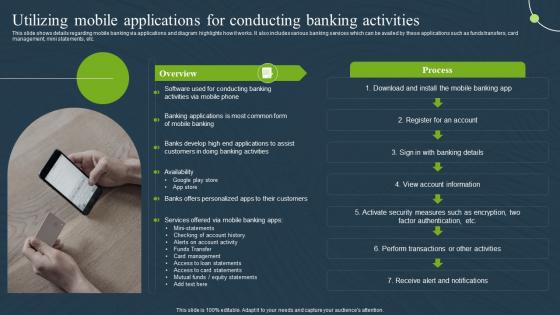 Utilizing Mobile Applications Activities Mobile Banking For Convenient And Secure Online Payments Fin SS
Utilizing Mobile Applications Activities Mobile Banking For Convenient And Secure Online Payments Fin SSThis slide shows details regarding mobile banking via applications and diagram highlights how it works. It also includes various banking services which can be availed by these applications such as funds transfers, card management, mini statements, etc. Deliver an outstanding presentation on the topic using this Utilizing Mobile Applications Activities Mobile Banking For Convenient And Secure Online Payments Fin SS. Dispense information and present a thorough explanation of Applications, Conducting, Process using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Utilities security ppt powerpoint presentation infographic template design ideas cpb
Utilities security ppt powerpoint presentation infographic template design ideas cpbPresenting this set of slides with name Utilities Security Ppt Powerpoint Presentation Infographic Template Design Ideas Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Utilities Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Utility security system ppt powerpoint presentation summary slide download cpb
Utility security system ppt powerpoint presentation summary slide download cpbPresenting our Utility Security System Ppt Powerpoint Presentation Summary Slide Download Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Utility Security System This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Security tokens vs utility tokens ppt powerpoint presentation portfolio objects cpb
Security tokens vs utility tokens ppt powerpoint presentation portfolio objects cpbPresenting our Security Tokens Vs Utility Tokens Ppt Powerpoint Presentation Portfolio Objects Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Security Tokens Vs Utility Tokens This PPT slide can be easily accessed in standard screen 4.3 and widescreen 16.9 aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
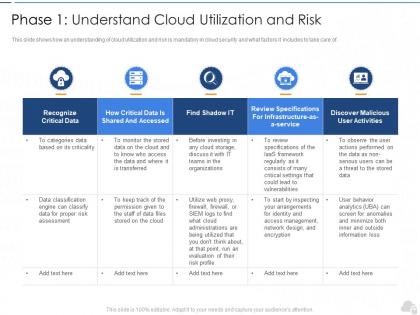 Phase 1 understand cloud utilization and risk cloud security it ppt information
Phase 1 understand cloud utilization and risk cloud security it ppt informationThis slide shows how an understanding of cloud utilization and risk is mandatory in cloud security and what factors it includes to take care of.Present the topic in a bit more detail with this Phase 1 Understand Cloud Utilization And Risk Cloud Security IT Ppt Information. Use it as a tool for discussion and navigation on Recognize Critical Data, Discover Malicious User Activities, Find Shadow It. This template is free to edit as deemed fit for your organization. Therefore download it now.

