Powerpoint Templates and Google slides for Zero Initiatives Icon
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Endpoint Initiated Vs Service Initiated Zero Trust Security Model
Endpoint Initiated Vs Service Initiated Zero Trust Security ModelThis Slide Represents The Comparison Between The Two Primary Approaches To Implementing Zero-Trust Network Access For Organizations. The Purpose Of This Slide Is To Showcase The Endpoint-Initiated And Service-Initiated Approach Of Zero-Trust Network Access. Present The Topic In A Bit More Detail With This Endpoint Initiated Vs Service Initiated Zero Trust Security Model. Use It As A Tool For Discussion And Navigation On Enterprise, Environment, Connection. This Template Is Free To Edit As Deemed Fit For Your Organization. Therefore Download It Now.
-
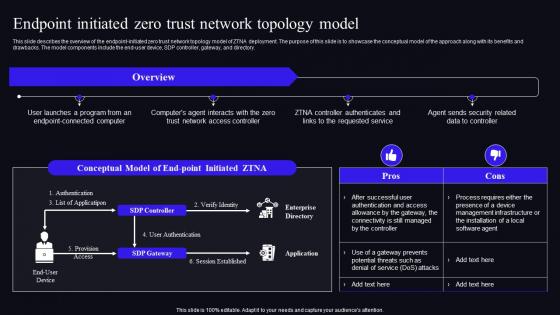 Endpoint Initiated Zero Trust Network Topology Model Zero Trust Security Model
Endpoint Initiated Zero Trust Network Topology Model Zero Trust Security ModelThis slide describes the overview of the endpoint-initiated zero trust network topology model of ZTNA deployment. The purpose of this slide is to showcase the conceptual model of the approach along with its benefits and drawbacks. The model components include the end-user device, SDP controller, gateway, and directory. Deliver an outstanding presentation on the topic using this Endpoint Initiated Zero Trust Network Topology Model Zero Trust Security Model. Dispense information and present a thorough explanation of Management, Infrastructure, Installation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
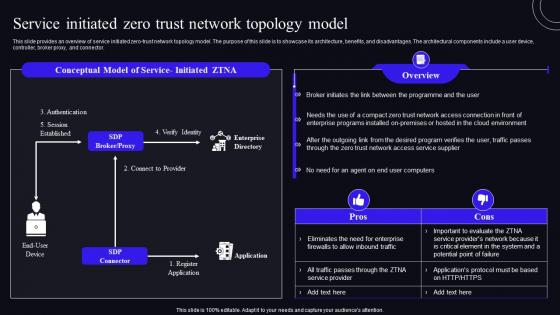 Service Initiated Zero Trust Network Topology Model Zero Trust Security Model
Service Initiated Zero Trust Network Topology Model Zero Trust Security ModelThis slide provides an overview of service initiated zero-trust network topology model. The purpose of this slide is to showcase its architecture, benefits, and disadvantages. The architectural components include a user device, controller, broker proxy, and connector. Deliver an outstanding presentation on the topic using this Service Initiated Zero Trust Network Topology Model Zero Trust Security Model. Dispense information and present a thorough explanation of Environment, Enterprise, Access Connection using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
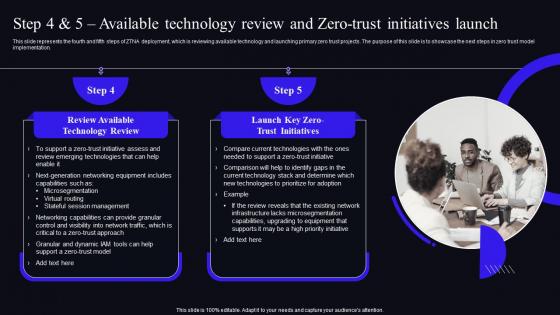 Zero Trust Security Model Step 4 And 5 Available Technology Review And Zero Trust Initiatives Launch
Zero Trust Security Model Step 4 And 5 Available Technology Review And Zero Trust Initiatives LaunchThis slide represents the fourth and fifth steps of ZTNA deployment, which is reviewing available technology and launching primary zero trust projects. The purpose of this slide is to showcase the next steps in zero trust model implementation. Present the topic in a bit more detail with this Zero Trust Security Model Step 4 And 5 Available Technology Review And Zero Trust Initiatives Launch. Use it as a tool for discussion and navigation on Technology, Equipment, Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
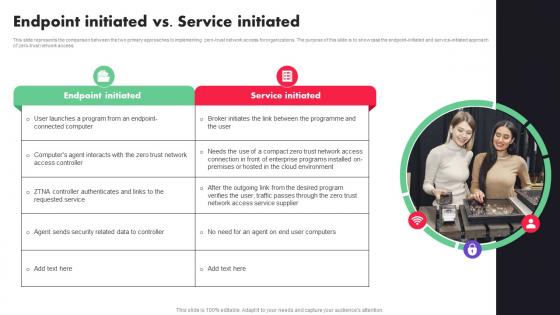 Endpoint Initiated Vs Service Initiated Zero Trust Architecture ZTA
Endpoint Initiated Vs Service Initiated Zero Trust Architecture ZTAThis slide represents the comparison between the two primary approaches to implementing zero-trust network access for organizations. The purpose of this slide is to showcase the endpoint-initiated and service-initiated approach of zero-trust network access. Introducing Endpoint Initiated Vs Service Initiated Zero Trust Architecture ZTA to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Endpoint Initiated, Service Initiated, Requested Service, using this template. Grab it now to reap its full benefits.
-
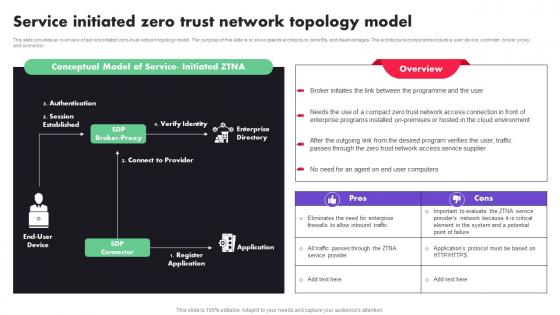 Service Initiated Zero Trust Network Topology Model Ppt File Professional
Service Initiated Zero Trust Network Topology Model Ppt File ProfessionalThis slide provides an overview of service initiated zero-trust network topology model. The purpose of this slide is to showcase its architecture, benefits, and disadvantages. The architectural components include a user device, controller, broker proxy, and connector. Present the topic in a bit more detail with this Service Initiated Zero Trust Network Topology Model Ppt File Professional. Use it as a tool for discussion and navigation on Model, Computers, Service. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
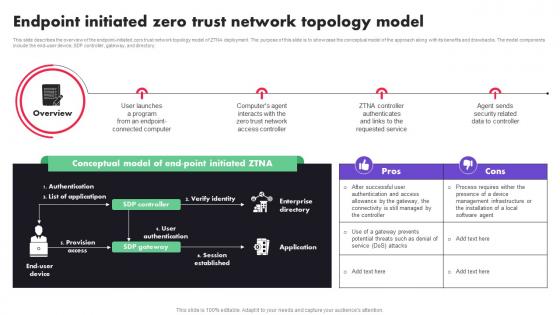 Zero Trust Architecture ZTA Endpoint Initiated Zero Trust Network Topology Model
Zero Trust Architecture ZTA Endpoint Initiated Zero Trust Network Topology ModelThis slide describes the overview of the endpoint-initiated zero trust network topology model of ZTNA deployment. The purpose of this slide is to showcase the conceptual model of the approach along with its benefits and drawbacks. The model components include the end-user device, SDP controller, gateway, and directory. Introducing Zero Trust Architecture ZTA Endpoint Initiated Zero Trust Network Topology Model to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Overview, Computer, service, using this template. Grab it now to reap its full benefits.
-
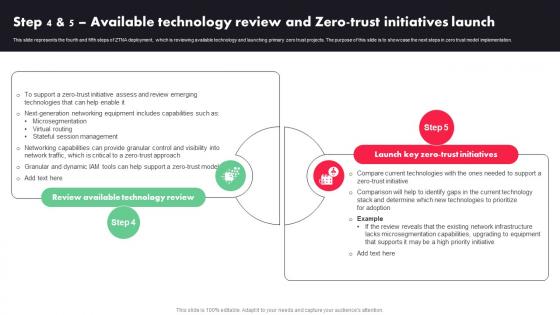 Zero Trust Architecture ZTA Step 4 And 5 Available Technology Review And Zero Trust Initiatives Launch
Zero Trust Architecture ZTA Step 4 And 5 Available Technology Review And Zero Trust Initiatives LaunchThis slide represents the fourth and fifth steps of ZTNA deployment, which is reviewing available technology and launching primary zero trust projects. The purpose of this slide is to showcase the next steps in zero trust model implementation. Introducing Zero Trust Architecture ZTA Step 4 And 5 Available Technology Review And Zero Trust Initiatives Launch to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Microsegmentation, Virtual Routing, Stateful Session Management, using this template. Grab it now to reap its full benefits.
-
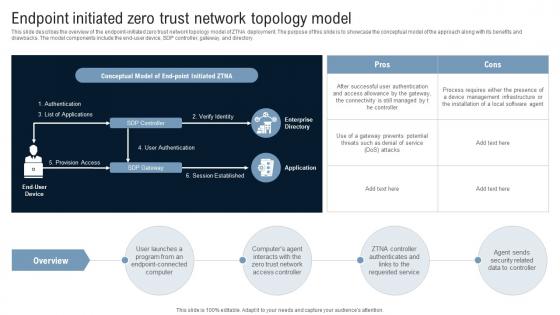 Endpoint Initiated Zero Trust Network Topology Model Identity Defined Networking
Endpoint Initiated Zero Trust Network Topology Model Identity Defined NetworkingThis slide describes the overview of the endpoint-initiated zero trust network topology model of ZTNA deployment. The purpose of this slide is to showcase the conceptual model of the approach along with its benefits and drawbacks. The model components include the end-user device, SDP controller, gateway, and directory. Present the topic in a bit more detail with this Endpoint Initiated Zero Trust Network Topology Model Identity Defined Networking Use it as a tool for discussion and navigation on Conceptual Model, Enterprise Directory, Provision Access This template is free to edit as deemed fit for your organization. Therefore download it now.
-
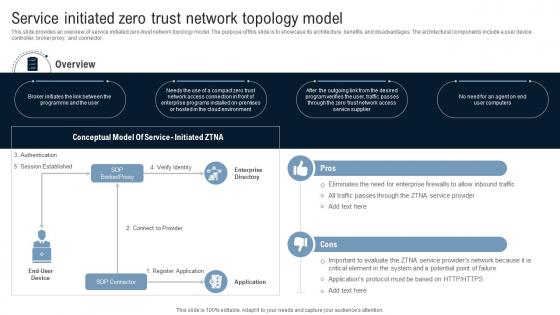 Service Initiated Zero Trust Network Topology Model Identity Defined Networking
Service Initiated Zero Trust Network Topology Model Identity Defined NetworkingThis slide provides an overview of service initiated zero-trust network topology model. The purpose of this slide is to showcase its architecture, benefits, and disadvantages. The architectural components include a user device, controller, broker proxy, and connector. Present the topic in a bit more detail with this Service Initiated Zero Trust Network Topology Model Identity Defined Networking Use it as a tool for discussion and navigation on Conceptual Model, Service Initiated, Overview This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Step 4 And 5 Available Technology Review And Zero Trust Initiatives Launch
Step 4 And 5 Available Technology Review And Zero Trust Initiatives LaunchThis slide represents the fourth and fifth steps of ZTNA deployment, which is reviewing available technology and launching primary zero trust projects. The purpose of this slide is to showcase the next steps in zero trust model implementation. Increase audience engagement and knowledge by dispensing information using Step 4 And 5 Available Technology Review And Zero Trust Initiatives Launch. This template helps you present information on two stages. You can also present information on Review Available Technology Review, Launch Key Zero Trust Initiatives using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
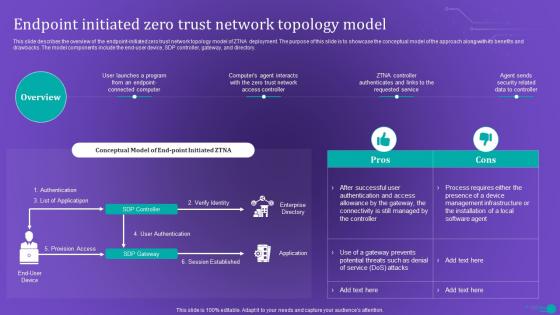 ZTNA Endpoint Initiated Zero Trust Network Topology Model
ZTNA Endpoint Initiated Zero Trust Network Topology ModelThis slide describes the overview of the endpoint initiated zero trust network topology model of ZTNA deployment. The purpose of this slide is to showcase the conceptual model of the approach along with its benefits and drawbacks. The model components include the end user device, SDP controller, gateway, and directory. Present the topic in a bit more detail with this ZTNA Endpoint Initiated Zero Trust Network Topology Model. Use it as a tool for discussion and navigation on Network, Security, Service. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
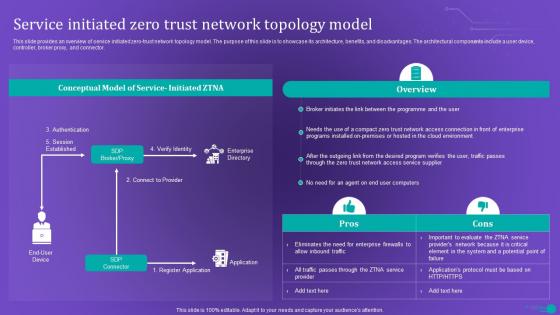 ZTNA Service Initiated Zero Trust Network Topology Model
ZTNA Service Initiated Zero Trust Network Topology ModelThis slide provides an overview of service initiated zero trust network topology model. The purpose of this slide is to showcase its architecture, benefits, and disadvantages. The architectural components include a user device, controller, broker proxy, and connector. Present the topic in a bit more detail with this ZTNA Service Initiated Zero Trust Network Topology Model. Use it as a tool for discussion and navigation on System, Enterprise, Evaluate. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Adverse federal initiatives below zero customer system process
Adverse federal initiatives below zero customer system processPresenting this set of slides with name - Adverse Federal Initiatives Below Zero Customer System Process. This is an editable seven stages graphic that deals with topics like Adverse Federal Initiatives, Below Zero Customer, System Process to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

