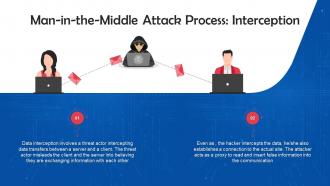
Interception Mode Of Executing Man In The Middle Attacks Training Ppt
This slide discusses the first step, i.e. Interception, for executing MiTM attacks. Data interception involves a threat actor intercepting data transfers between a server and a client. The threat actor misleads the client and the server into believing they are exchanging information with each other.
This slide discusses the first step, i.e. Interception, for executing MiTM attacks. Data interception involves a threat act..
- Google Slides is a new FREE Presentation software from Google.
- All our content is 100% compatible with Google Slides.
- Just download our designs, and upload them to Google Slides and they will work automatically.
- Amaze your audience with SlideTeam and Google Slides.
-
Want Changes to This PPT Slide? Check out our Presentation Design Services
- WideScreen Aspect ratio is becoming a very popular format. When you download this product, the downloaded ZIP will contain this product in both standard and widescreen format.
-

- Some older products that we have may only be in standard format, but they can easily be converted to widescreen.
- To do this, please open the SlideTeam product in Powerpoint, and go to
- Design ( On the top bar) -> Page Setup -> and select "On-screen Show (16:9)” in the drop down for "Slides Sized for".
- The slide or theme will change to widescreen, and all graphics will adjust automatically. You can similarly convert our content to any other desired screen aspect ratio.
Compatible With Google Slides

Get This In WideScreen
You must be logged in to download this presentation.
PowerPoint presentation slides
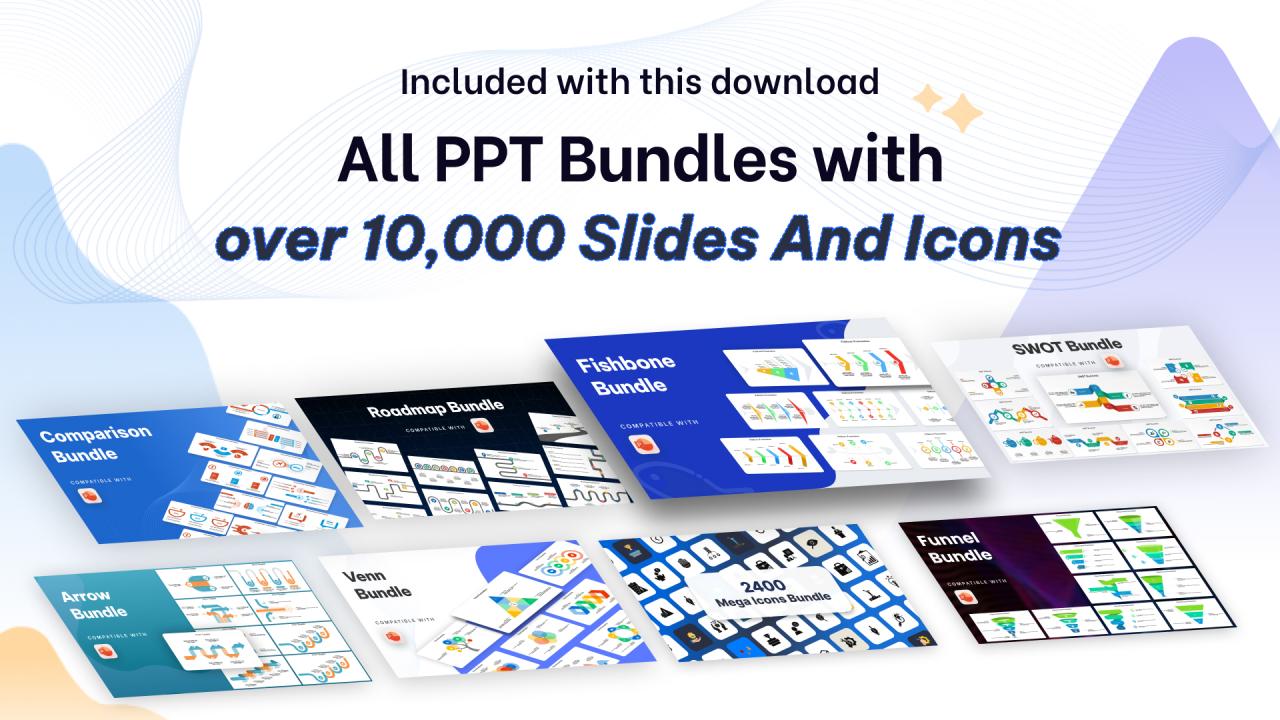
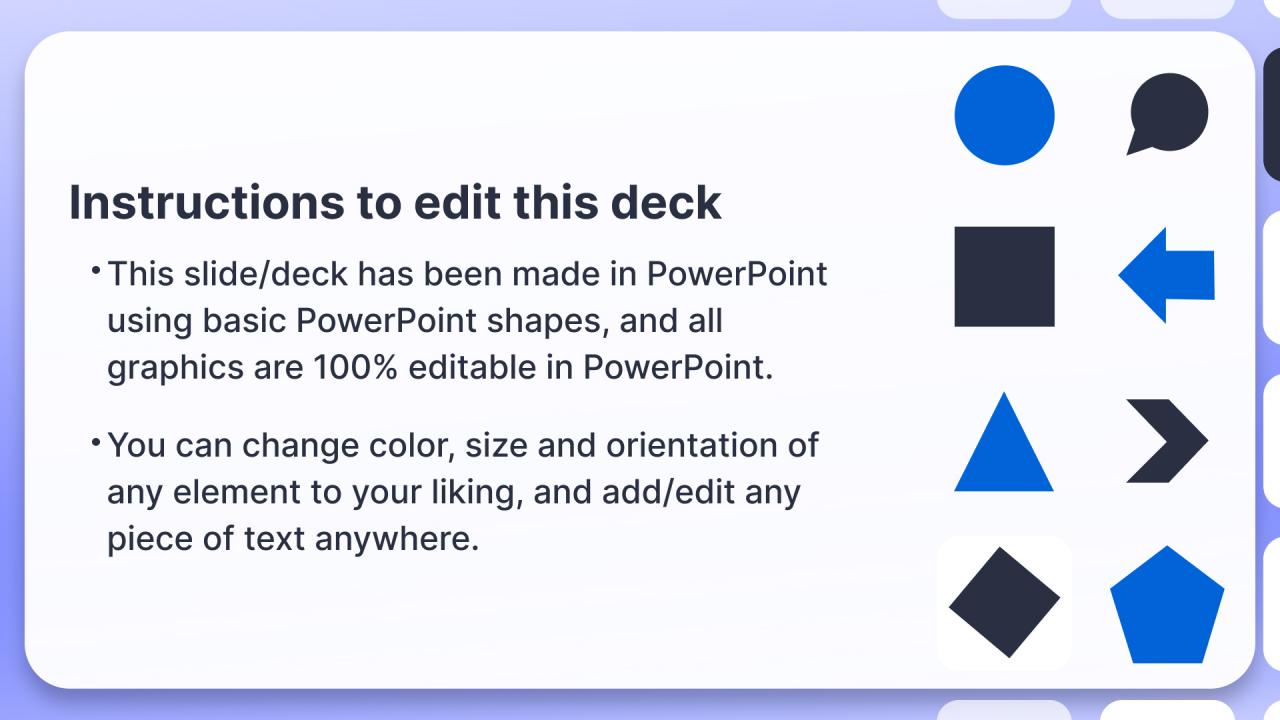
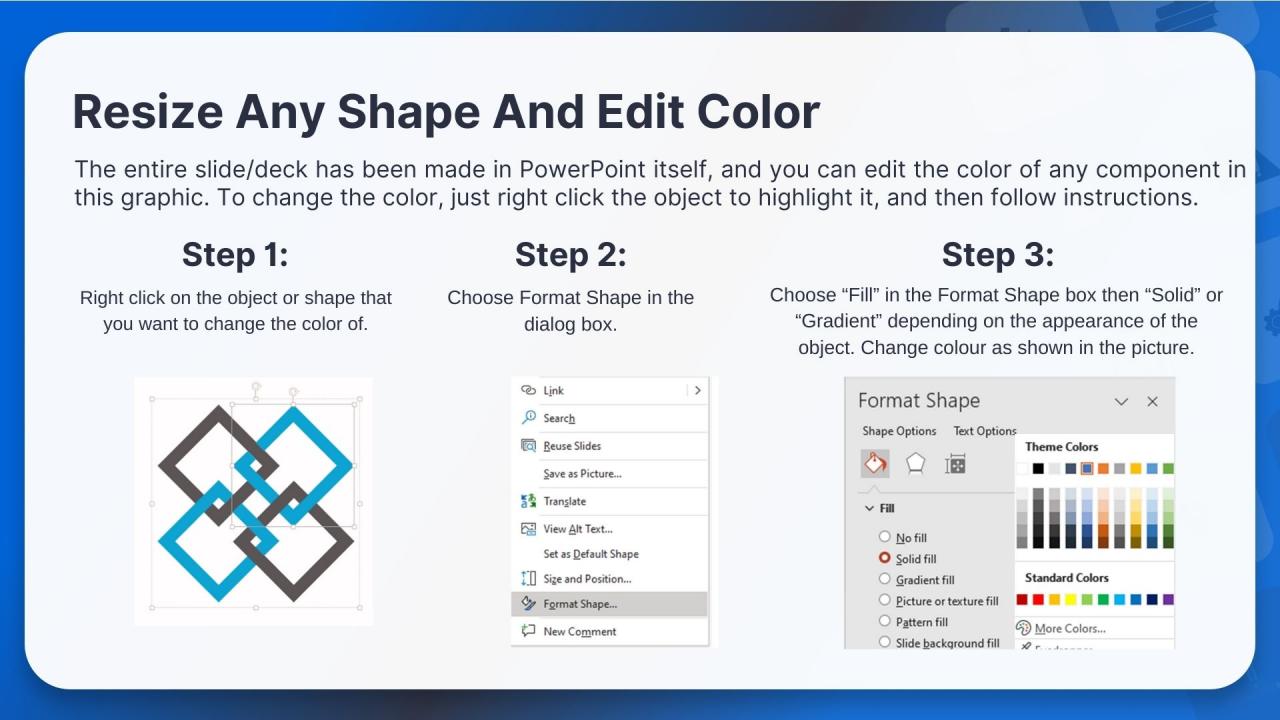
Presenting Interception Mode of Executing Man in the Middle Attacks. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
People who downloaded this PowerPoint presentation also viewed the following :
Interception Mode Of Executing Man In The Middle Attacks Training Ppt with all 21 slides:
Use our Interception Mode Of Executing Man In The Middle Attacks Training Ppt to effectively help you save your valuable time. They are readymade to fit into any presentation structure.
-
I looked at their huge selection of themes and designs. They appeared to be ideal for my profession. I'm sure I'll grab a few of them.
-
Great combination of visuals and information. Glad I purchased your subscription.