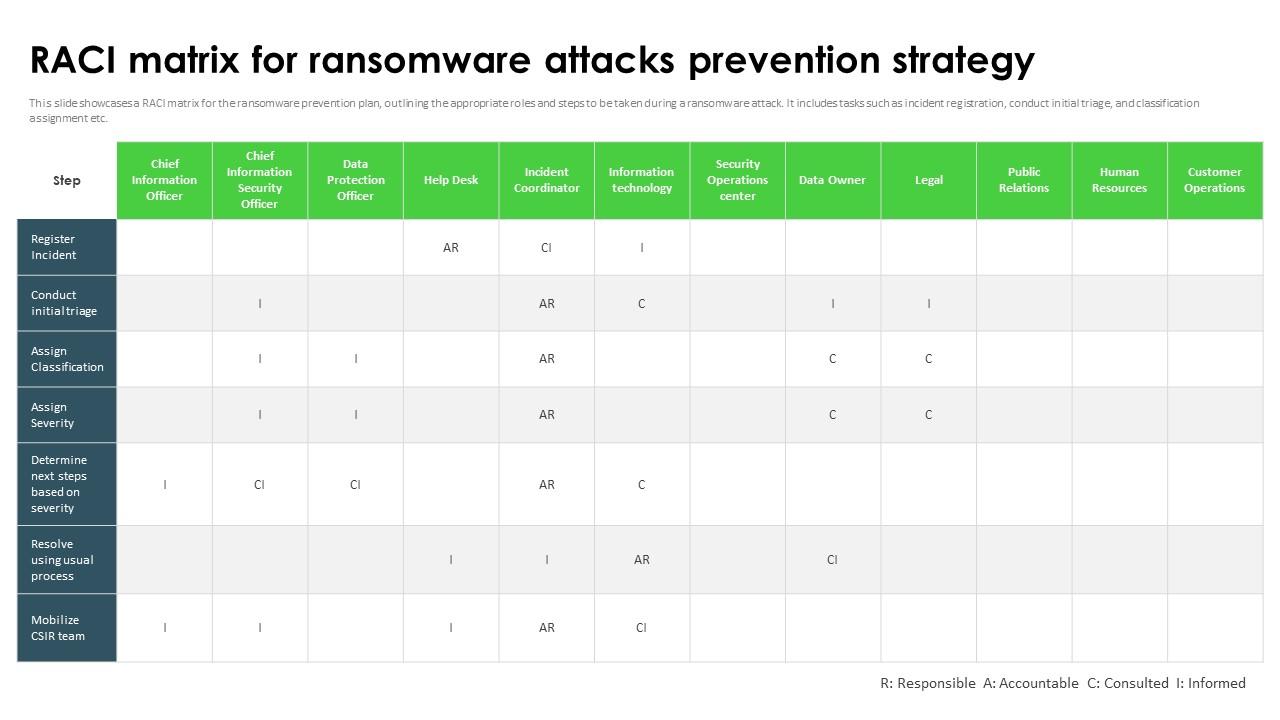
Ransomware In Digital Age RACI Matrix For Ransomware Attacks Prevention Strategy
This slide showcases a RACI matrix for the ransomware prevention plan, outlining the appropriate roles and steps to be taken during a ransomware attack. It includes tasks such as incident registration, conduct initial triage, and classification assignment etc.
This slide showcases a RACI matrix for the ransomware prevention plan, outlining the appropriate roles and steps to be take..
- Google Slides is a new FREE Presentation software from Google.
- All our content is 100% compatible with Google Slides.
- Just download our designs, and upload them to Google Slides and they will work automatically.
- Amaze your audience with SlideTeam and Google Slides.
-
Want Changes to This PPT Slide? Check out our Presentation Design Services
- WideScreen Aspect ratio is becoming a very popular format. When you download this product, the downloaded ZIP will contain this product in both standard and widescreen format.
-

- Some older products that we have may only be in standard format, but they can easily be converted to widescreen.
- To do this, please open the SlideTeam product in Powerpoint, and go to
- Design ( On the top bar) -> Page Setup -> and select "On-screen Show (16:9)” in the drop down for "Slides Sized for".
- The slide or theme will change to widescreen, and all graphics will adjust automatically. You can similarly convert our content to any other desired screen aspect ratio.
Compatible With Google Slides

Get This In WideScreen
You must be logged in to download this presentation.
PowerPoint presentation slides
This slide showcases a RACI matrix for the ransomware prevention plan, outlining the appropriate roles and steps to be taken during a ransomware attack. It includes tasks such as incident registration, conduct initial triage, and classification assignment etc. Present the topic in a bit more detail with this Ransomware In Digital Age RACI Matrix For Ransomware Attacks Prevention Strategy. Use it as a tool for discussion and navigation on Ransomware Attacks, Prevention Strategy, Classification Assignment, Conduct Initial Triage. This template is free to edit as deemed fit for your organization. Therefore download it now.
People who downloaded this PowerPoint presentation also viewed the following :
Ransomware In Digital Age RACI Matrix For Ransomware Attacks Prevention Strategy with all 10 slides:
Use our Ransomware In Digital Age RACI Matrix For Ransomware Attacks Prevention Strategy to effectively help you save your valuable time. They are readymade to fit into any presentation structure.
-
Good research work and creative work done on every template.
-
Love how there are no boring templates here! The design is fresh and creative, just the way I like it. Can't wait to edit and use them for my extended projects!