Social engineering with five steps include data collection and attack
Create a bunch of happy faces with our Social Engineering With Five Steps Include Data Collection And Attack. Convert frowns into grins.
You must be logged in to download this presentation.
PowerPoint presentation slides
Presenting this set of slides with name - Social Engineering With Five Steps Include Data Collection And Attack. This is a five stage process. The stages in this process are Social Engineering, Information Security, Psychological Manipulation.
People who downloaded this PowerPoint presentation also viewed the following :
Content of this Powerpoint Presentation
Description:
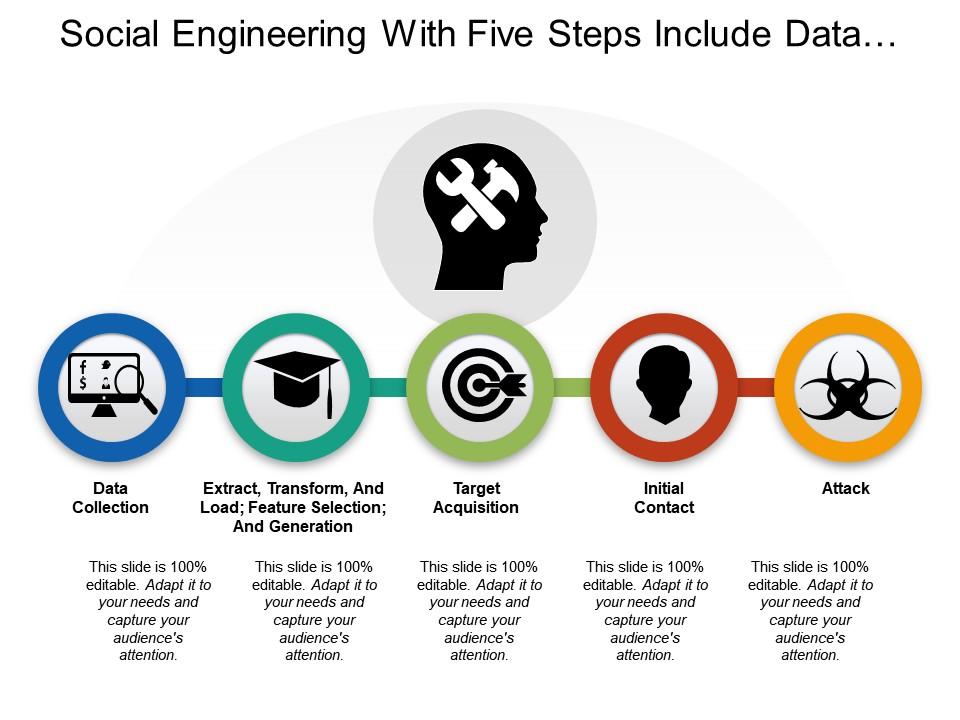
The image illustrates a presentation slide titled "Social Engineering With Five Steps Include Data..." which outlines a process divided into five sequential steps. Each step is represented by a circular icon connected in a flow and accompanied by a brief description.
1. Data Collection:
This step involves gathering information and is depicted by a computer monitor with a magnifying glass, symbolizing search or research.
2. Extract, Transform, And Load; Feature Selection; And Generalization:
This stage is about processing the collected data. Here, the graduation cap icon implies the application of knowledge or skill to refine the information gathered during the data collection.
3. Target Acquisition:
A target and arrow symbolize the identification of the target or victim for the social engineering attempt.
4. Initial Contact:
Represented by silhouettes shaking hands, indicating the act of establishing a connection with the target.
5. Attack:
The final stage is denoted by a biohazard symbol, suggesting the launch of the malicious social engineering attack.
Use Cases:
Seven industries where these slides can be applicable:
1. Cybersecurity:
Use: Educating staff on social engineering tactics
Presenter: IT Security Trainer
Audience: Company employees
2. Law Enforcement:
Use: Training on cybercrime investigation techniques
Presenter: Cybercrime Specialist
Audience: Law enforcement officers
3. Corporate Training:
Use: Enhancing awareness of information security
Presenter: Corporate Trainer
Audience: Corporate professionals
4. Education:
Use: Teaching about data privacy and security
Presenter: Professor or Educator
Audience: Students in technology and cybersecurity courses
5. Financial Services:
Use: Preventing fraud and phishing attacks
Presenter: Fraud Prevention Expert
Audience: Bank employees and financial advisors
6. Healthcare:
Use: Safeguarding patient information from phishing
Presenter: Compliance Officer
Audience: Healthcare providers and administrative staff
7. Marketing:
Use: Understanding the ethical boundaries in consumer data use
Presenter: Marketing Ethicist
Audience: Marketing professionals and strategists
Social engineering with five steps include data collection and attack with all 5 slides:
Our Social Engineering With Five Steps Include Data Collection And Attack will familiarise them with the craft. Expose them to the expertise available.
-
Great designs, really helpful.
-
Content of slide is easy to understand and edit.