Powerpoint Templates and Google slides for Access To Data
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
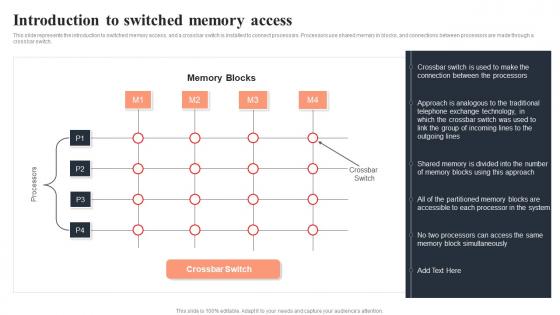
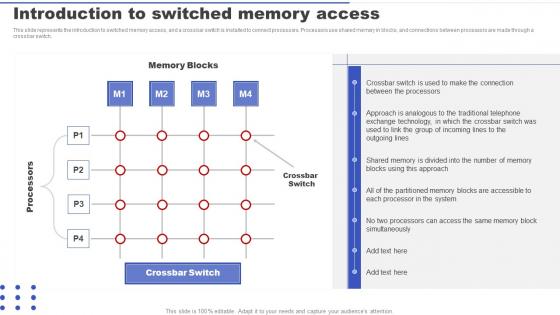 Parallel Processing Applications Introduction To Switched Memory Access
Parallel Processing Applications Introduction To Switched Memory AccessThis slide represents the introduction to switched memory access, and a crossbar switch is installed to connect processors. Processors use shared memory in blocks, and connections between processors are made through a crossbar switch. Present the topic in a bit more detail with this Parallel Processing Applications Introduction To Switched Memory Access. Use it as a tool for discussion and navigation on Exchange Technology, Traditional Telephone, System. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
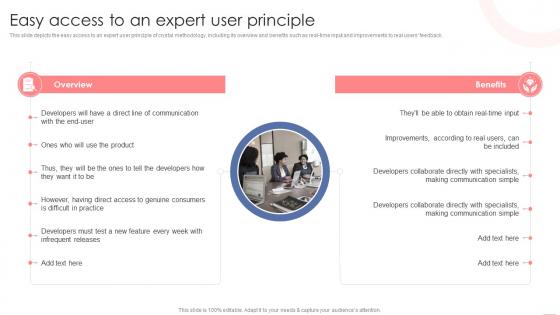 Easy Access To An Expert User Principle Agile Crystal Methodology IT
Easy Access To An Expert User Principle Agile Crystal Methodology ITThis slide depicts the easy access to an expert user principle of crystal methodology, including its overview and benefits such as real-time input and improvements to real users feedback. Introducing Easy Access To An Expert User Principle Agile Crystal Methodology IT to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Overview, Benefits, Communication Simple, using this template. Grab it now to reap its full benefits.
-
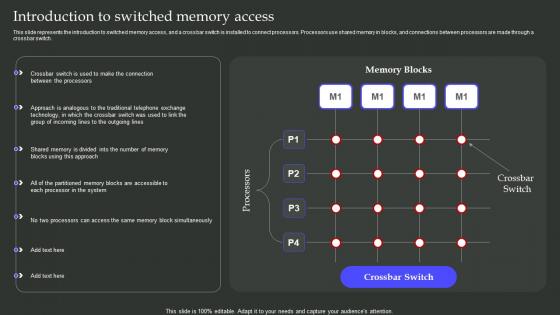 Introduction To Switched Memory Access Parallel Processing Architecture Ppt Slides Files
Introduction To Switched Memory Access Parallel Processing Architecture Ppt Slides FilesThis slide represents the introduction to switched memory access, and a crossbar switch is installed to connect processors. Processors use shared memory in blocks, and connections between processors are made through a crossbar switch. Present the topic in a bit more detail with this Introduction To Switched Memory Access Parallel Processing Architecture Ppt Slides Files. Use it as a tool for discussion and navigation on Memory Blocks, Crossbar Switch, Processors. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
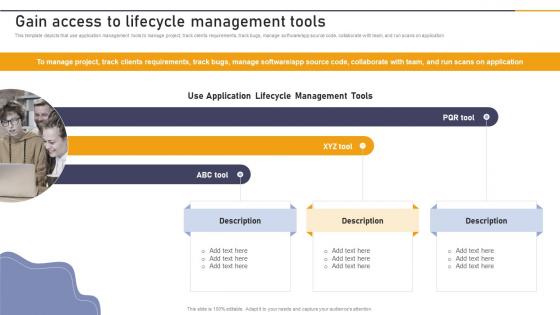 Gain Access To Lifecycle Management Tools Enterprise Application Playbook
Gain Access To Lifecycle Management Tools Enterprise Application PlaybookThis template depicts that use application management tools to manage project, track clients requirements, track bugs, manage software or app source code, collaborate with team, and run scans on application. Introducing Gain Access To Lifecycle Management Tools Enterprise Application Playbook to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Use Application, Lifecycle Management Tools, ABC Tool, using this template. Grab it now to reap its full benefits.
-
 Models Of Access To Information And Communication IT For Communication In Business
Models Of Access To Information And Communication IT For Communication In BusinessThis slide describes the models of access described by scholar Mark Warschauer as a framework for examining information and communication technology accessibility. The models include devices, conduits, and literacy. Increase audience engagement and knowledge by dispensing information using Models Of Access To Information And Communication IT For Communication In Business. This template helps you present information on one stages. You can also present information on Conduits, Device, Literacy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
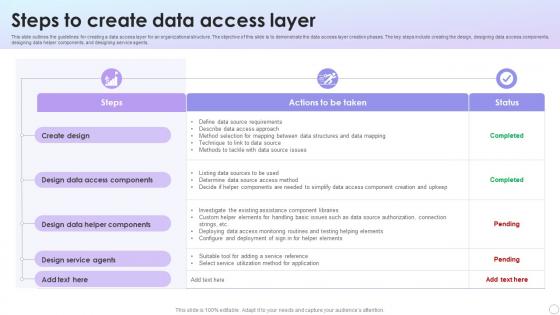 Steps To Create Data Access Layer
Steps To Create Data Access LayerThis slide outlines the guidelines for creating a data access layer for an organizational structure. The objective of this slide is to demonstrate the data access layer creation phases. The key steps include creating the design, designing data access components, designing data helper components, and designing service agents. Introducing our Steps To Create Data Access Layer set of slides. The topics discussed in these slides are Create Design, Design Data Access, Design Service Agents. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
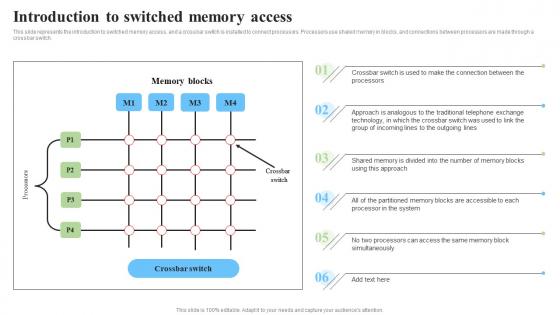 Introduction To Switched Memory Access Parallel Processor System And Computing Types
Introduction To Switched Memory Access Parallel Processor System And Computing TypesThis slide represents the introduction to switched memory access, and a crossbar switch is installed to connect processors. Processors use shared memory in blocks, and connections between processors are made through a crossbar switch. Deliver an outstanding presentation on the topic using this Introduction To Switched Memory Access Parallel Processor System And Computing Types. Dispense information and present a thorough explanation of Processors, Exchange Technology, Traditional Telephone using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Parallel Computing Introduction To Switched Memory Access Ppt Show Background Images
Parallel Computing Introduction To Switched Memory Access Ppt Show Background ImagesThis slide shows the fundamentals of parallel computer architecture that can be found in a wide range of parallel computers, which are categorized according to the amount of parallelism supported by the hardware components. It includes multi-core computing, symmetric multiprocessing, and distributed computing. Present the topic in a bit more detail with this Parallel Computing Introduction To Switched Memory Access Ppt Show Background Images. Use it as a tool for discussion and navigation on Fundamentals, Computer, Architecture. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
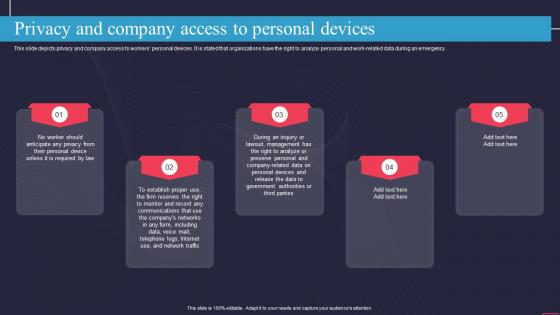 Privacy And Company Access To Personal Devices Information Technology Policy
Privacy And Company Access To Personal Devices Information Technology PolicyThis slide depicts privacy and company access to workers personal devices. It is stated that organizations have the right to analyze personal and work related data during an emergency. Increase audience engagement and knowledge by dispensing information using Privacy And Company Access To Personal Devices Information Technology Policy. This template helps you present information on five stages. You can also present information on Communications, Management, Government Authorities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
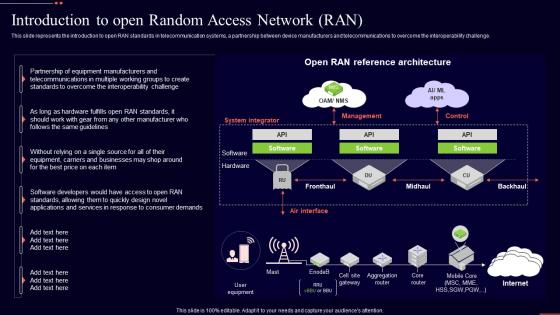 Introduction To Open Random Access Network Ran Open Ran It Ppt Professional Example Topics
Introduction To Open Random Access Network Ran Open Ran It Ppt Professional Example TopicsThis slide represents the introduction to open RAN standards in telecommunication systems, a partnership between device manufacturers and telecommunications to overcome the interoperability challenge. Deliver an outstanding presentation on the topic using this Introduction To Open Random Access Network Ran Open Ran It Ppt Professional Example Topics. Dispense information and present a thorough explanation of Introduction, Telecommunications, Interoperability Challenge using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
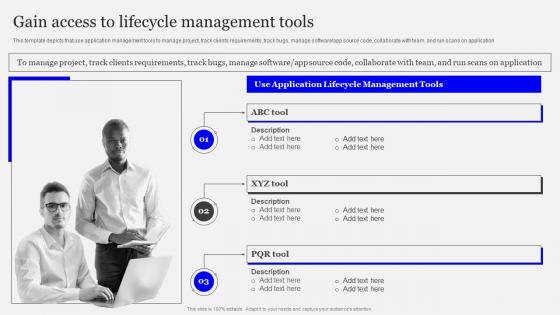 Gain Access To Lifecycle Management Tools Playbook Designing Developing Software
Gain Access To Lifecycle Management Tools Playbook Designing Developing SoftwareThis template depicts that use application management tools to manage project, track clients requirements, track bugs, manage software app source code, collaborate with team, and run scans on application. Introducing Gain Access To Lifecycle Management Tools Playbook Designing Developing Software to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Application Lifecycle, Management Tools, Gain Access, using this template. Grab it now to reap its full benefits.
-
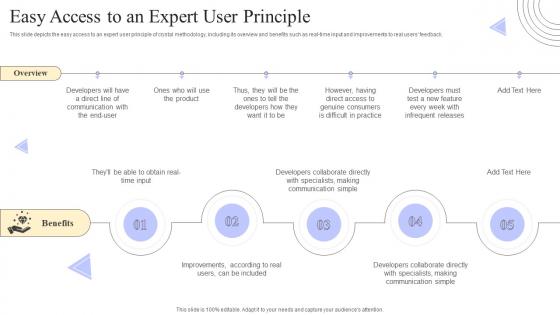 Crystal Methods Easy Access To An Expert User Principle Ppt Powerpoint Presentation File Infographics
Crystal Methods Easy Access To An Expert User Principle Ppt Powerpoint Presentation File InfographicsThis slide depicts the easy access to an expert user principle of crystal methodology, including its overview and benefits such as real time input and improvements to real users feedback. Increase audience engagement and knowledge by dispensing information using Crystal Methods Easy Access To An Expert User Principle Ppt Powerpoint Presentation File Infographics. This template helps you present information on five stages. You can also present information on Infrequent Releases, Communication, Developers Collaborate using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Components Of Brand Portfolio Strategy For Better Access To New Brand Portfolio Strategy Guide
Components Of Brand Portfolio Strategy For Better Access To New Brand Portfolio Strategy GuideThis slide covers the fundamental principles of creating an effective brand communication strategy. It includes guidelines such as building and leveraging strong corporate bonds, defining strategic objectives for brands, employing simple and clear brand architecture, etc. Introducing Components Of Brand Portfolio Strategy For Better Access To New Brand Portfolio Strategy Guide to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Strategic Role, Business Objectives, Brand Architecture, using this template. Grab it now to reap its full benefits.
-
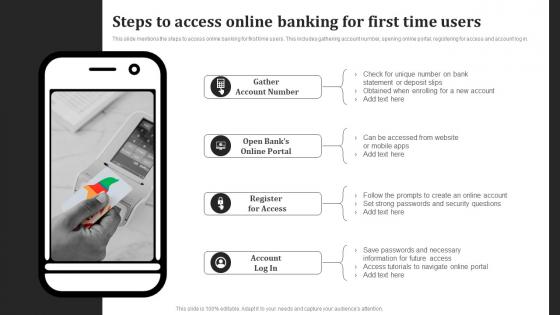 Steps To Access Online Banking For First Time Users
Steps To Access Online Banking For First Time UsersThis slide mentions the steps to access online banking for first time users. This includes gathering account number, opening online portal, registering for access and account log in. Introducing our premium set of slides with Steps To Access Online Banking For First Time Users. Elucidate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Steps To Access, Online Banking, First Time Users. So download instantly and tailor it with your information.
-
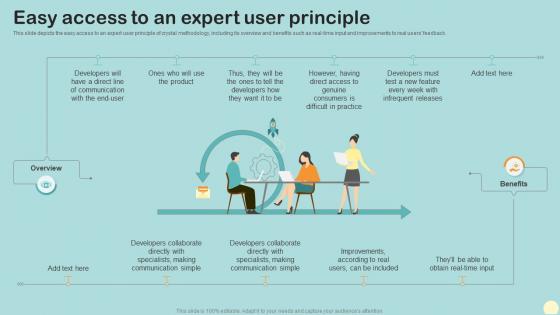 Easy Access To An Expert User Principle Crystal Agile Framework
Easy Access To An Expert User Principle Crystal Agile FrameworkThis slide depicts the easy access to an expert user principle of crystal methodology, including its overview and benefits such as real time input and improvements to real users feedback.Increase audience engagement and knowledge by dispensing information using Easy Access To An Expert User Principle Crystal Agile Framework. This template helps you present information on one stages. You can also present information on Developers Collaborate, Communication Simple, Improvements According using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Monitor Access To Sensitive And Regulated Data Information Privacy Ppt Powerpoint Presentation Outline Images
Monitor Access To Sensitive And Regulated Data Information Privacy Ppt Powerpoint Presentation Outline ImagesThis slide explains we help you with data privacy by monitoring access of sensitive and regulated data, in which automation engine assists you in achieving the least privilege and compliance faster.Increase audience engagement and knowledge by dispensing information using Monitor Access To Sensitive And Regulated Data Information Privacy Ppt Powerpoint Presentation Outline Images. This template helps you present information on five stages. You can also present information on Entitlement Assessments, Individuals Access, Unrestricted Access using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
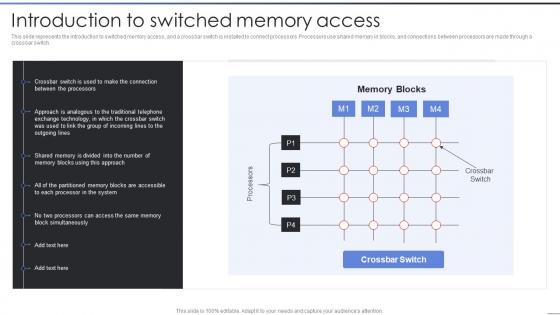 Parallel Processing IT Introduction To Switched Memory Access
Parallel Processing IT Introduction To Switched Memory AccessThis slide represents the introduction to switched memory access, and a crossbar switch is installed to connect processors. Processors use shared memory in blocks, and connections between processors are made through a crossbar switch. Present the topic in a bit more detail with this Parallel Processing IT Introduction To Switched Memory Access. Use it as a tool for discussion and navigation on Crossbar Switch, Memory Blocks, Crossbar Switch, Processors. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Gain Access To Lifecycle Management Tools Enterprise Software Development Playbook
Gain Access To Lifecycle Management Tools Enterprise Software Development PlaybookThis template depicts that use application management tools to manage project, track clients requirements, track bugs, manage software and app source code, collaborate with team, and run scans on application Present the topic in a bit more detail with this Gain Access To Lifecycle Management Tools Enterprise Software Development Playbook. Use it as a tool for discussion and navigation on Gain Access, Lifecycle, Management Tools. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Privacy Implementation Monitor Access To Sensitive And Regulated Data
Data Privacy Implementation Monitor Access To Sensitive And Regulated DataThis slide explains we help you with data privacy by monitoring access of sensitive and regulated data, in which automation engine assists you in achieving the least privilege and compliance faster. Introducing Data Privacy Implementation Monitor Access To Sensitive And Regulated Data to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Frequent Entitlement, Appropriate Individuals, Relevant Data, using this template. Grab it now to reap its full benefits.
-
 Gain Access To Lifecycle Management Tools Design And Build Custom
Gain Access To Lifecycle Management Tools Design And Build CustomThis template depicts that use application management tools to manage project, track clients requirements, track bugs, manage software or app source code, collaborate with team, and run scans on application. Introducing Gain Access To Lifecycle Management Tools Design And Build Custom to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on ABC Tool, XYZ Tool, PQR Tool, using this template. Grab it now to reap its full benefits.
-
 Gain Access To Lifecycle Management Tools Playbook For Enterprise Software Firms
Gain Access To Lifecycle Management Tools Playbook For Enterprise Software FirmsThis template depicts that use application management tools to manage project, track clients requirements, track bugs, manage software app source code, collaborate with team, and run scans on application.Increase audience engagement and knowledge by dispensing information using Gain Access To Lifecycle Management Tools Playbook For Enterprise Software Firms. This template helps you present information on two stages. You can also present information on Apple Developer Enterprise, Program License, Organizations using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Remote Access To Live Coaching And Training Uplift Seed Funding Pitch Deck
Remote Access To Live Coaching And Training Uplift Seed Funding Pitch DeckThe following slide highlights the platform which allows athletes to have access coaching and training at remote locations Increase audience engagement and knowledge by dispensing information using Remote Access To Live Coaching And Training Uplift Seed Funding Pitch Deck. This template helps you present information on one stages. You can also present information on Locations, Coaching, Constraints using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
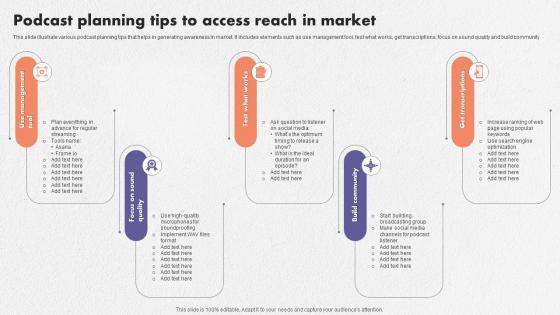 Podcast Planning Tips To Access Reach In Market
Podcast Planning Tips To Access Reach In MarketThis slide illustrate various podcast planning tips that helps in generating awareness in market. It includes elements such as use management tool, test what works, get transcriptions, focus on sound quality and build community. Introducing our premium set of slides with Podcast Planning Tips To Access Reach In Market. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Focus On Sound Quality, Test What Works, Community. So download instantly and tailor it with your information.
-
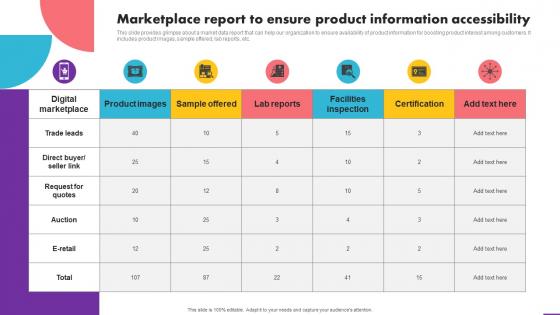 Marketplace Report To Ensure Product Information Accessibility Analyzing User Experience Journey
Marketplace Report To Ensure Product Information Accessibility Analyzing User Experience JourneyThis slide provides glimpse about a market data report that can help our organization to ensure availability of product information for boosting product interest among customers. It includes product images, sample offered, lab reports, etc. Deliver an outstanding presentation on the topic using this Marketplace Report To Ensure Product Information Accessibility Analyzing User Experience Journey. Dispense information and present a thorough explanation of Marketplace, Product, Accessibility using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
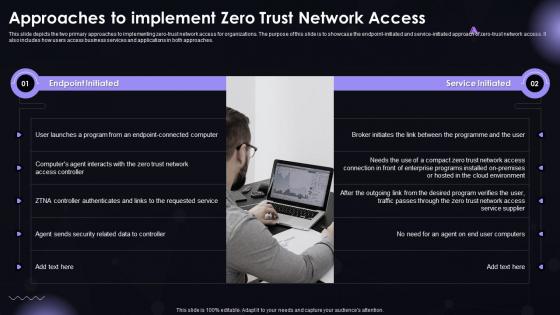 SASE IT Approaches To Implement Zero Trust Network Access Ppt Demonstration
SASE IT Approaches To Implement Zero Trust Network Access Ppt DemonstrationThis slide depicts the two primary approaches to implementing zero-trust network access for organizations. The purpose of this slide is to showcase the endpoint-initiated and service-initiated approach of zero-trust network access. It also includes how users access business services and applications in both approaches. Introducing SASE IT Approaches To Implement Zero Trust Network Access Ppt Demonstration to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Endpoint Initiated, Service Initiated, using this template. Grab it now to reap its full benefits.
-
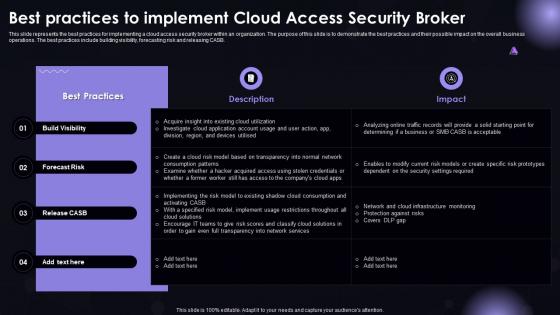 SASE IT Best Practices To Implement Cloud Access Security Broker Ppt Powerpoint Microsoft
SASE IT Best Practices To Implement Cloud Access Security Broker Ppt Powerpoint MicrosoftThis slide represents the best practices for implementing a cloud access security broker within an organization. The purpose of this slide is to demonstrate the best practices and their possible impact on the overall business operations. The best practices include building visibility, forecasting risk and releasing CASB. Deliver an outstanding presentation on the topic using this SASE IT Best Practices To Implement Cloud Access Security Broker Ppt Powerpoint Microsoft. Dispense information and present a thorough explanation of Build Visibility, Forecast Risk, Release CASB using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 SASE IT Budget To Implement Secure Access Service Edge Ppt Powerpoint Designs
SASE IT Budget To Implement Secure Access Service Edge Ppt Powerpoint DesignsThis slide depicts the budget calculation for implementing a secure access service edge model in an organization. The purpose of this slide is to showcase the estimated and actual cost and variance for SASE model spending. The key components include SD-WAN, SWG, ZTNA, CASB, and FWaaS. Present the topic in a bit more detail with this SASE IT Budget To Implement Secure Access Service Edge Ppt Powerpoint Designs. Use it as a tool for discussion and navigation on Secure Web Gateway, Zero Trust Network Access, Cloud Access Security Broker. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
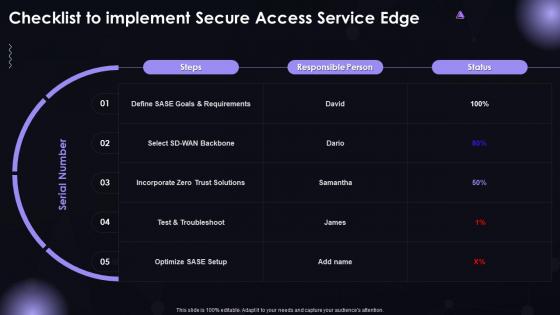 SASE IT Checklist To Implement Secure Access Service Edge Ppt Powerpoint Demonstration
SASE IT Checklist To Implement Secure Access Service Edge Ppt Powerpoint DemonstrationPresent the topic in a bit more detail with this SASE IT Checklist To Implement Secure Access Service Edge Ppt Powerpoint Demonstration. Use it as a tool for discussion and navigation on Test And Troubleshoot, Incorporate Zero Trust Solutions, SASE Goals And Requirements. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
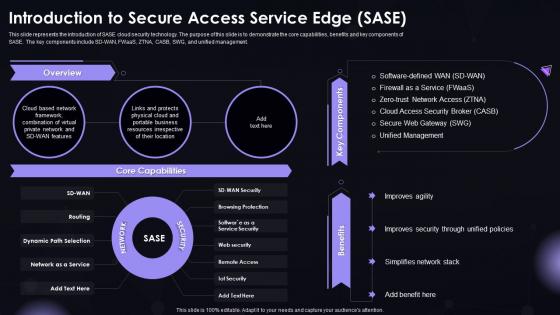 SASE IT Introduction To Secure Access Service Edge SASE Ppt Powerpoint Graphics
SASE IT Introduction To Secure Access Service Edge SASE Ppt Powerpoint GraphicsThis slide represents the introduction of SASE cloud security technology. The purpose of this slide is to demonstrate the core capabilities, benefits and key components of SASE. The key components include SD-WAN, FWaaS, ZTNA, CASB, SWG, and unified management. Present the topic in a bit more detail with this SASE IT Introduction To Secure Access Service Edge SASE Ppt Powerpoint Graphics. Use it as a tool for discussion and navigation on Core Capabilities, Key Components, Benefits. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 SASE IT Roadmap To Implement Secure Access Service Edge Ppt Powerpoint Formats
SASE IT Roadmap To Implement Secure Access Service Edge Ppt Powerpoint FormatsThis slide depicts the roadmap to implementing secure access service edge in an organization. The purpose of this slide is to demonstrate all the steps to be taken in the SASE implementation process, covering defining SASE objectives and needs, examining the environment and, discovering gaps, etc. Introducing SASE IT Roadmap To Implement Secure Access Service Edge Ppt Powerpoint Formats to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Transition, Troubleshooting, And Assistance, SASE Providers And Solutions, using this template. Grab it now to reap its full benefits.
-
 Steps For Building Brand Portfolio Components Of Brand Portfolio Strategy For Better Access To New Markets
Steps For Building Brand Portfolio Components Of Brand Portfolio Strategy For Better Access To New MarketsThis slide covers the fundamental principles of creating an effective brand communication strategy. It includes guidelines such as building and leveraging strong corporate bonds, defining strategic objectives for brands, employing simple and clear brand architecture, etc. Introducing Steps For Building Brand Portfolio Components Of Brand Portfolio Strategy For Better Access To New Markets to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Brand Positioning, Business Objectives, Brand Positioning, using this template. Grab it now to reap its full benefits.
-
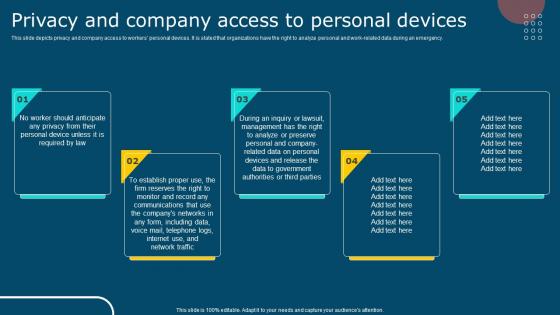 IT Policy Privacy And Company Access To Personal Devices
IT Policy Privacy And Company Access To Personal DevicesThis slide depicts privacy and company access to workers personal devices. It is stated that organizations have the right to analyze personal and work-related data during an emergency. Introducing IT Policy Privacy And Company Access To Personal Devices to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Privacy, Company Access, Personal Devices, using this template. Grab it now to reap its full benefits.
-
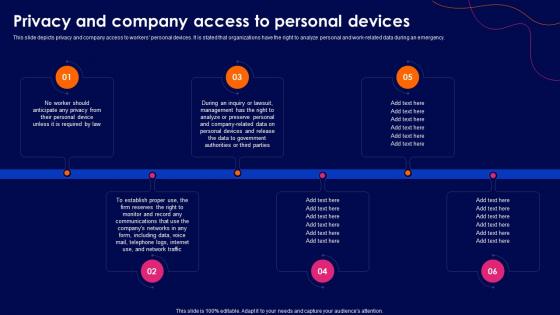 Cyber Security Policy Privacy And Company Access To Personal Devices
Cyber Security Policy Privacy And Company Access To Personal DevicesThis slide depicts privacy and company access to workers personal devices. It is stated that organizations have the right to analyze personal and work-related data during an emergency. Increase audience engagement and knowledge by dispensing information using Cyber Security Policy Privacy And Company Access To Personal Devices. This template helps you present information on six stages. You can also present information on Management, Government, Authorities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
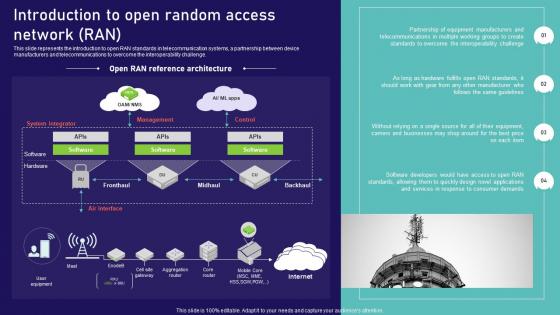 Open Ran Technology Introduction To Open Random Access Network Ran Ppt Professional Display
Open Ran Technology Introduction To Open Random Access Network Ran Ppt Professional DisplayThis slide represents the introduction to open RAN standards in telecommunication systems, a partnership between device manufacturers and telecommunications to overcome the interoperability challenge. Deliver an outstanding presentation on the topic using this Open Ran Technology Introduction To Open Random Access Network Ran Ppt Professional Display. Dispense information and present a thorough explanation of Introduction, Telecommunications, Businesses using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
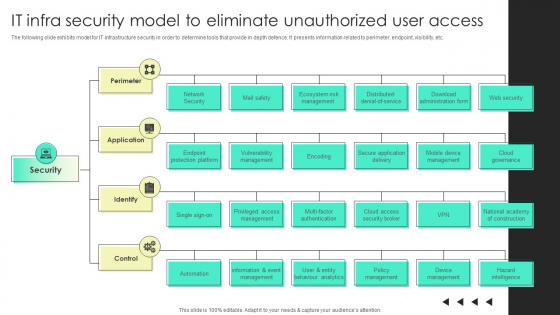 It Infra Security Model To Eliminate Unauthorized User Access
It Infra Security Model To Eliminate Unauthorized User AccessThe following slide exhibits model for IT infrastructure security in order to determine tools that provide in depth defence. It presents information related to perimeter, endpoint, visibility, etc. Introducing It Infra Security Model To Eliminate Unauthorized User Access to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Perimeter, Application, Identify, using this template. Grab it now to reap its full benefits.
-
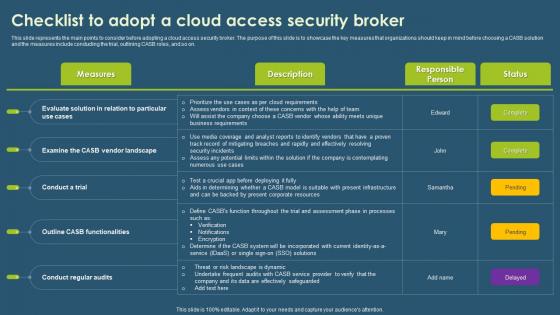 Checklist To Adopt A Cloud Access Security Broker Ppt Show Visuals
Checklist To Adopt A Cloud Access Security Broker Ppt Show VisualsThis slide represents the main points to consider before adopting a cloud access security broker. The purpose of this slide is to showcase the key measures that organizations should keep in mind before choosing a CASB solution and the measures include conducting the trial, outlining CASB roles, and so on. Present the topic in a bit more detail with this Checklist To Adopt A Cloud Access Security Broker Ppt Show Visuals. Use it as a tool for discussion and navigation on Measures, Description, Responsible Person. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
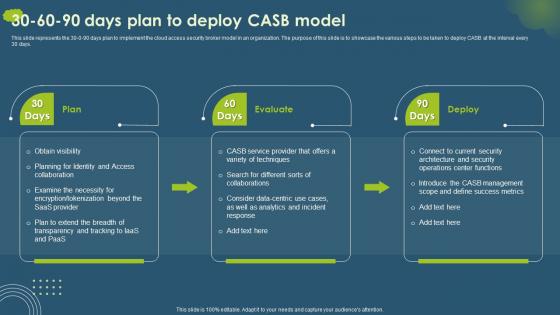 Cloud Access Security Broker CASB 30 60 90 Days Plan To Deploy CASB Model
Cloud Access Security Broker CASB 30 60 90 Days Plan To Deploy CASB ModelThis slide represents the 30 0 90 days plan to implement the cloud access security broker model in an organization. The purpose of this slide is to showcase the various steps to be taken to deploy CASB at the interval every 30 days. Present the topic in a bit more detail with this Cloud Access Security Broker CASB 30 60 90 Days Plan To Deploy CASB Model. Use it as a tool for discussion and navigation on Plan, Evaluate, Deploy. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
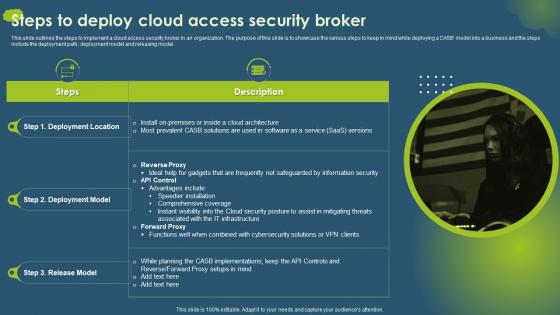 Steps To Deploy Cloud Access Security Broker Ppt Slides Clipart Images
Steps To Deploy Cloud Access Security Broker Ppt Slides Clipart ImagesThis slide outlines the steps to implement a cloud access security broker in an organization. The purpose of this slide is to showcase the various steps to keep in mind while deploying a CASB model into a business and the steps include the deployment path, deployment model and releasing model. Deliver an outstanding presentation on the topic using this Steps To Deploy Cloud Access Security Broker Ppt Slides Clipart Images. Dispense information and present a thorough explanation of Deployment Location, Deployment Model, Release Model using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
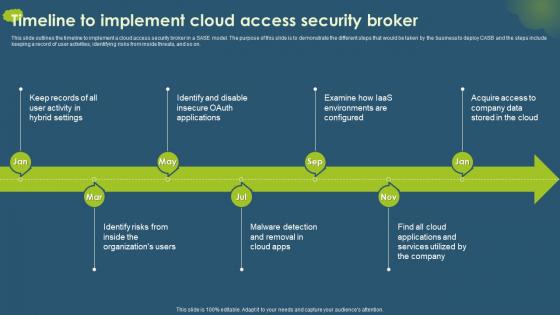 Timeline To Implement Cloud Access Security Broker Ppt Ideas Tips
Timeline To Implement Cloud Access Security Broker Ppt Ideas TipsThis slide outlines the timeline to implement a cloud access security broker in a SASE model. The purpose of this slide is to demonstrate the different steps that would be taken by the business to deploy CASB and the steps include keeping a record of user activities, identifying risks from inside threats, and so on. Increase audience engagement and knowledge by dispensing information using Timeline To Implement Cloud Access Security Broker Ppt Ideas Tips. This template helps you present information on seven stages. You can also present information on Keep Records, Identify And Disable, Examine using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 ZTNA Checklist To Build Zero Trust Network Access Architecture
ZTNA Checklist To Build Zero Trust Network Access ArchitectureThis slide outlines the checklist to develop a zero trust network access architecture. The purpose of this slide is to define the various measures organizations should take while building a ZTNA architecture. The measures include knowing the architecture, creating a strong device identity, and so on. Present the topic in a bit more detail with this ZTNA Checklist To Build Zero Trust Network Access Architecture. Use it as a tool for discussion and navigation on Network, Resources, Communication. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
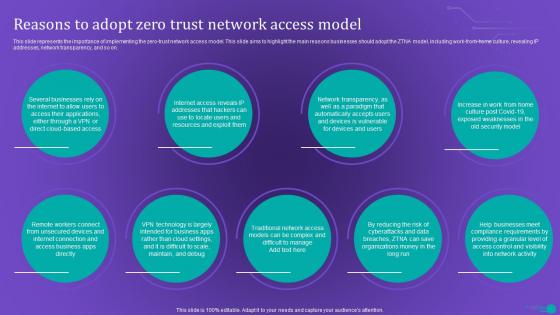 ZTNA Reasons To Adopt Zero Trust Network Access Model
ZTNA Reasons To Adopt Zero Trust Network Access ModelThis slide represents the importance of implementing the zero trust network access model. This slide aims to highlight the main reasons businesses should adopt the ZTNA model, including work from home culture, revealing IP addresses, network transparency, and so on. Introducing ZTNA Reasons To Adopt Zero Trust Network Access Model to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Internet, Resources, Devices, using this template. Grab it now to reap its full benefits.
-
 ZTNA Steps To Implement Zero Trust Network Access Model
ZTNA Steps To Implement Zero Trust Network Access ModelThis slide outlines the crucial steps to implement the zero trust network access model in an organization. The purpose of this slide is to highlight the key steps to perform to deploy the ZTNA model. The steps include identifying assets, defining protection surface, understanding the businesss security model, etc. Present the topic in a bit more detail with this ZTNA Steps To Implement Zero Trust Network Access Model. Use it as a tool for discussion and navigation on Mapping Transaction Flows, Protection Surface, Design Ztna Architecture. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
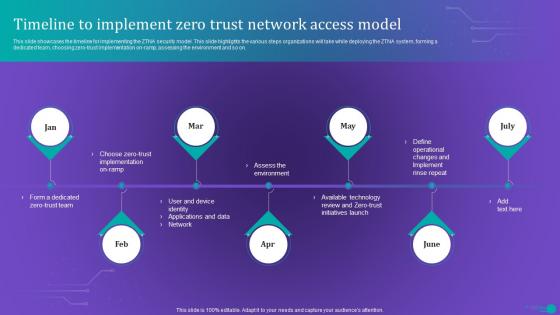 ZTNA Timeline To Implement Zero Trust Network Access Model
ZTNA Timeline To Implement Zero Trust Network Access ModelIntroducing ZTNA Timeline To Implement Zero Trust Network Access Model to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Assess The Environment, Implement, Technology, using this template. Grab it now to reap its full benefits.
-
 Offering Exclusive Pre Launch Access To Customers Implementing New Marketing Campaign Plan Strategy SS
Offering Exclusive Pre Launch Access To Customers Implementing New Marketing Campaign Plan Strategy SSThis slide provides glimpse about exclusive pre-launch campaign through email marketing for boosting customer engagement. It includes overview, implementation guidelines, impact, etc. Introducing Offering Exclusive Pre Launch Access To Customers Implementing New Marketing Campaign Plan Strategy SS to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Overview, Implementation Guidelines using this template. Grab it now to reap its full benefits.
-
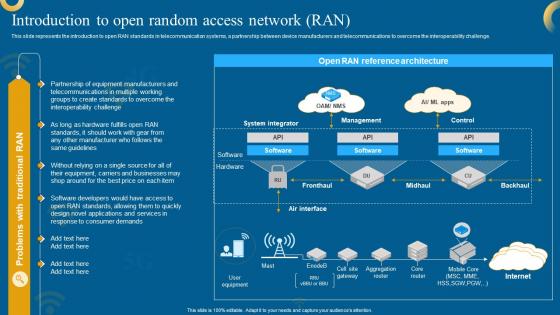 Open RAN 5G Introduction To Open RANdom Access Network RAN
Open RAN 5G Introduction To Open RANdom Access Network RANThis slide represents the introduction to open RAN standards in telecommunication systems, a partnership between device manufacturers and telecommunications to overcome the interoperability challenge. Deliver an outstanding presentation on the topic using this Open RAN 5G Introduction To Open RANdom Access Network RAN. Dispense information and present a thorough explanation of System Integrator, Management, Control using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
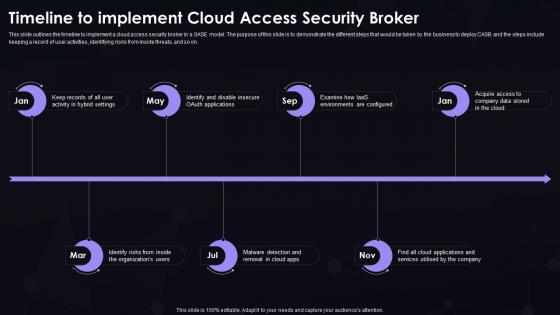 SASE IT Timeline To Implement Cloud Access Security Broker Ppt Powerpoint Portrait
SASE IT Timeline To Implement Cloud Access Security Broker Ppt Powerpoint PortraitThis slide outlines the timeline to implement a cloud access security broker in a SASE model. The purpose of this slide is to demonstrate the different steps that would be taken by the business to deploy CASB and the steps include keeping a record of user activities, identifying risks from inside threats, and so on. Increase audience engagement and knowledge by dispensing information using SASE IT Timeline To Implement Cloud Access Security Broker Ppt Powerpoint Portrait. This template helps you present information on seven stages. You can also present information on Hybrid Settings, Organizations Users, Cloud Apps using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 SASE IT Timeline To Implement Secure Access Service Edge Ppt Powerpoint Brochure
SASE IT Timeline To Implement Secure Access Service Edge Ppt Powerpoint BrochureThis slide outlines the timeline to implement secure access service edge in an organization. The purpose of this slide is to demonstrate all the steps to be taken in the SASE implementation process, covering defining SASE objectives and needs, examining the environment and discovering gaps, etc. Introducing SASE IT Timeline To Implement Secure Access Service Edge Ppt Powerpoint Brochure to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on SASE Objectives And Needs, SASE Providers And Solutions,Transition, Troubleshooting, And Assistance, using this template. Grab it now to reap its full benefits.
-
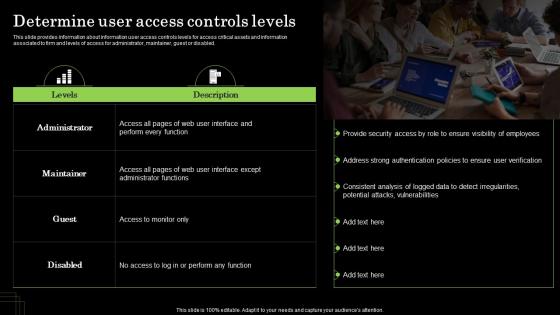 Determine User Access Controls Levels Defense Plan To Protect Firm Assets
Determine User Access Controls Levels Defense Plan To Protect Firm AssetsThis slide provides information about information user access controls levels for access critical assets and information associated to firm and levels of access for administrator, maintainer, guest or disabled. Increase audience engagement and knowledge by dispensing information using Determine User Access Controls Levels Defense Plan To Protect Firm Assets. This template helps you present information on One stage. You can also present information on User Verification, Ensure Visibility Of Employees, Detect Irregularities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Procedure To Access Chatgpt 4 And Chatgpt 3 Apis How To Use Openai Api In Business ChatGPT SS
Procedure To Access Chatgpt 4 And Chatgpt 3 Apis How To Use Openai Api In Business ChatGPT SSThis slide showcases process to get access key for OpenAIs ChatGPT-3 and ChatGPT-4 APIs which companies can use as a guide to get easy login and signup procedure. It provides details about client library, installation, switching, etc. Deliver an outstanding presentation on the topic using this Procedure To Access Chatgpt 4 And Chatgpt 3 Apis How To Use Openai Api In Business ChatGPT SS. Dispense information and present a thorough explanation of Applications, Procedure, Requirements using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
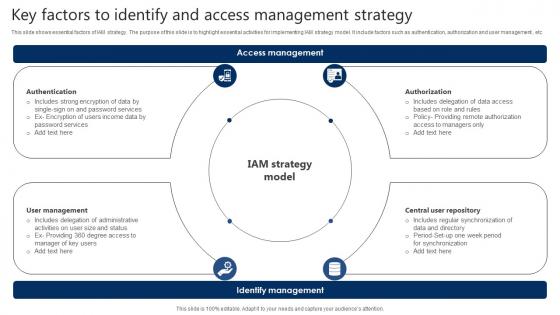 Key Factors To Identify And Access Management Strategy
Key Factors To Identify And Access Management StrategyThis slide shows essential factors of IAM strategy. The purpose of this slide is to highlight essential activities for implementing IAM strategy model. It include factors such as authentication, authorization and user management , etc Presenting our set of slides with Key Factors To Identify And Access Management Strategy. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Access, Management, Strategy.
-
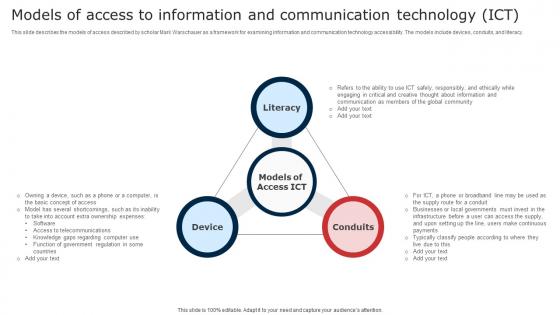 Models Of Access To Information And Communication Technology ICT Digital Signage In Internal
Models Of Access To Information And Communication Technology ICT Digital Signage In InternalThis slide describes the models of access described by scholar Mark Warschauer as a framework for examining information and communication technology accessibility. The models include devices, conduits, and literacy. Deliver an outstanding presentation on the topic using this Models Of Access To Information And Communication Technology ICT Digital Signage In Internal. Dispense information and present a thorough explanation of Literacy, Device, Conduits using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
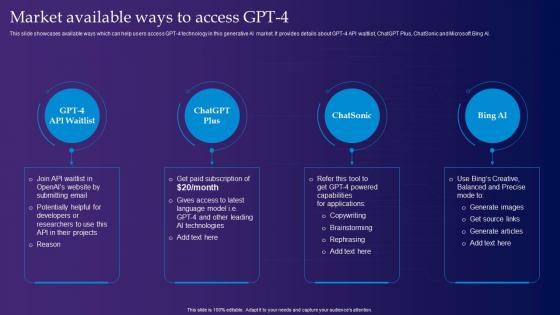 Market Available Ways To Access Gpt 4 Gpt 4 Latest Generative Ai Revolution ChatGPT SS
Market Available Ways To Access Gpt 4 Gpt 4 Latest Generative Ai Revolution ChatGPT SSThis slide showcases available ways which can help users access GPT-4 technology in this generative AI market. It provides details about GPT-4 API waitlist, ChatGPT Plus, ChatSonic and Microsoft Bing AI. Introducing Market Available Ways To Access Gpt 4 Gpt 4 Latest Generative Ai Revolution ChatGPT SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Potentially, Brainstorming, Capabilities, using this template. Grab it now to reap its full benefits.
-
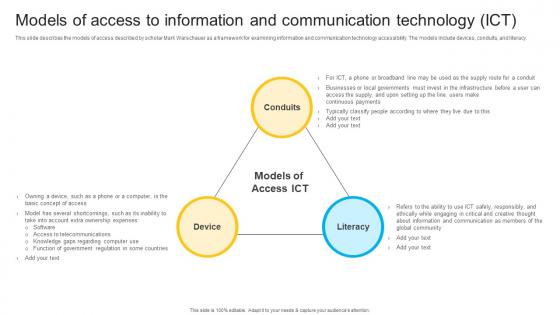 W96 Models Of Access To Information And Communication Technology Ict Instant Messenger In Internal
W96 Models Of Access To Information And Communication Technology Ict Instant Messenger In InternalThis slide describes the models of access described by scholar Mark Warschauer as a framework for examining information and communication technology accessibility. The models include devices, conduits, and literacy. Deliver an outstanding presentation on the topic using this W96 Models Of Access To Information And Communication Technology Ict Instant Messenger In Internal. Dispense information and present a thorough explanation of Information, Communication, Technology using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
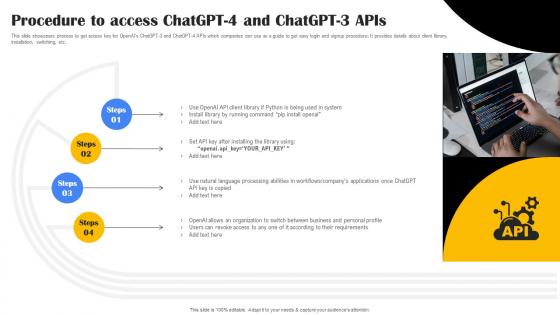 Procedure To Access Playground OpenAI API Use Cases ChatGPT SS V
Procedure To Access Playground OpenAI API Use Cases ChatGPT SS VThis slide showcases process to get access key for OpenAIs ChatGPT 3 and ChatGPT 4 APIs which companies can use as a guide to get easy login and signup procedure. It provides details about client library,installation, switching, etc.Increase audience engagement and knowledge by dispensing information using Procedure To Access Playground OpenAI API Use Cases ChatGPT SS V. This template helps you present information on one stage. You can also present information on Running Command, Natural Language, Processing Abilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
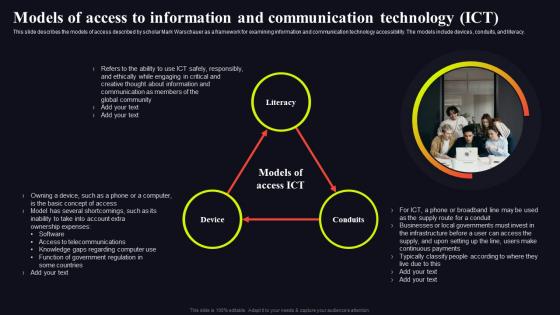 Models Of Access To Information Video Conferencing In Internal Communication
Models Of Access To Information Video Conferencing In Internal CommunicationThis slide describes the models of access described by scholar Mark Warschauer as a framework for examining information and communication technology accessibility. The models include devices, conduits, and literacy. Introducing Models Of Access To Information Video Conferencing In Internal Communication to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Literacy, Device, Conduits using this template. Grab it now to reap its full benefits.
-
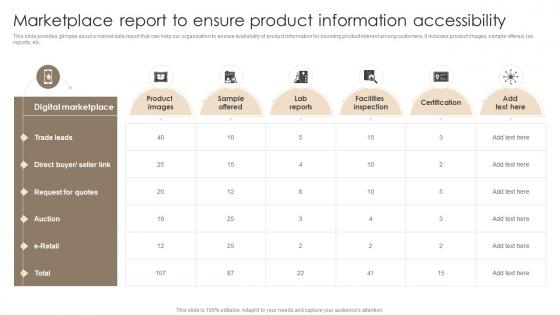 Marketplace Report To Ensure Product Information Accessibility Techniques For Customer
Marketplace Report To Ensure Product Information Accessibility Techniques For CustomerThis slide provides glimpse about a market data report that can help our organization to ensure availability of product information for boosting product interest among customers. It includes product images, sample offered, lab reports, etc. Present the topic in a bit more detail with this Marketplace Report To Ensure Product Information Accessibility Techniques For Customer Use it as a tool for discussion and navigation on Trade Leads, Request For Quotes This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Streamlined Consumer Adoption Process Marketplace Report To Ensure Product Information Accessibility
Streamlined Consumer Adoption Process Marketplace Report To Ensure Product Information AccessibilityThis slide provides glimpse about a market data report that can help our organization to ensure availability of product information for boosting product interest among customers. It includes product images, sample offered, lab reports, etc. Present the topic in a bit more detail with this Streamlined Consumer Adoption Process Marketplace Report To Ensure Product Information Accessibility. Use it as a tool for discussion and navigation on Product Images, Lab Reports, Facilities Inspection. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 System access to management powerpoint shapes
System access to management powerpoint shapesPresenting system access to management powerpoint shapes. This is a system access to management powerpoint shapes. This is a five stage process. The stages in this process are business, management, analysis, strategy, success, process.
-
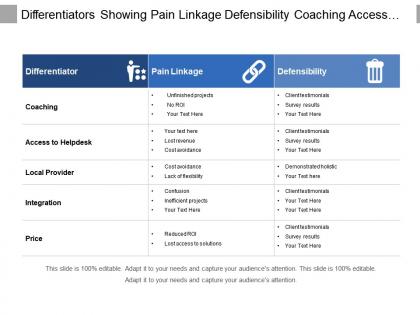 Differentiators showing pain linkage defensibility coaching access to helpdesk and local provider
Differentiators showing pain linkage defensibility coaching access to helpdesk and local providerPresenting this set of slides with name - Differentiators Showing Pain Linkage Defensibility Coaching Access To Helpdesk And Local Provider. This is a three stage process. The stages in this process are Differentiators, Difference, Unique.
-
 Good governance rule of law access to justice
Good governance rule of law access to justicePresenting this set of slides with name - Good Governance Rule Of Law Access To Justice. This is a three stage process. The stages in this process are Good Governance, International Development, Anti Corruption Measures.



