Powerpoint Templates and Google slides for Application Security Threats
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 5G Security Applications In Different Industries
5G Security Applications In Different IndustriesThis slide shows applications in 5G security to boost business operations. It further includes integrate IOT solutions, AR or VR,offers precision solutions etc. Presenting our set of slides with 5G Security Applications In Different Industries. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Healthcare, Public Sector.
-
 Key Uses And Applications Of Cryptographic Security Cloud Cryptography
Key Uses And Applications Of Cryptographic Security Cloud CryptographyThis slide outlines the various uses of cryptography. The purpose of this slide is to elaborate the key applications of cryptography. These are computer security, digital currencies, web surfing security, electronic signatures, authentication, cryptocurrencies, etc. Increase audience engagement and knowledge by dispensing information using Key Uses And Applications Of Cryptographic Security Cloud Cryptography. This template helps you present information on nine stages. You can also present information on Computer Security, Digital Currencies, Web Surfing Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
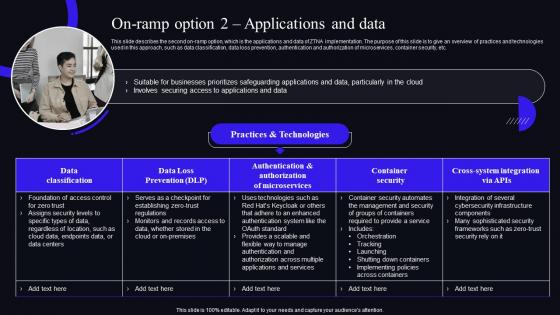 On Ramp Option 2 Applications And Data Zero Trust Security Model
On Ramp Option 2 Applications And Data Zero Trust Security ModelThis slide describes the second on-ramp option, which is the applications and data of ZTNA implementation. The purpose of this slide is to give an overview of practices and technologies used in this approach, such as data classification, data loss prevention, authentication and authorization of microservices, container security, etc. Deliver an outstanding presentation on the topic using this On Ramp Option 2 Applications And Data Zero Trust Security Model. Dispense information and present a thorough explanation of Authentication, Authorization, Microservices using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Social Security Restricted Application In Powerpoint And Google Slides Cpb
Social Security Restricted Application In Powerpoint And Google Slides CpbPresenting our Social Security Restricted Application In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases Four stages. It is useful to share insightful information on Social Security Restricted Application This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
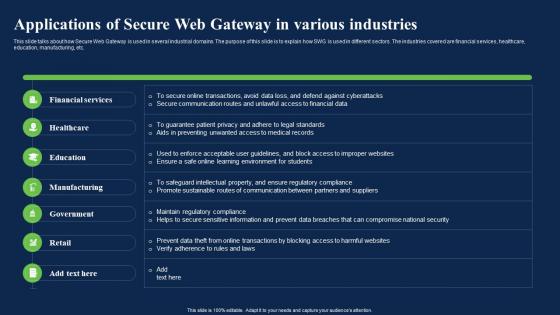 Applications Of Secure Web Gateway In Various Industries Network Security Using Secure Web Gateway
Applications Of Secure Web Gateway In Various Industries Network Security Using Secure Web GatewayThis slide talks about how Secure Web Gateway is used in several industrial domains. The purpose of this slide is to explain how SWG is used in different sectors. The industries covered are financial services, healthcare, education, manufacturing, etc. Present the topic in a bit more detail with this Applications Of Secure Web Gateway In Various Industries Network Security Using Secure Web Gateway. Use it as a tool for discussion and navigation on Applications, Financial Services, Education. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Impact Of Secure Web Gateway On Application Security Network Security Using Secure Web Gateway
Impact Of Secure Web Gateway On Application Security Network Security Using Secure Web GatewayThis slide represents the various factors which showcase the improvement of application security after adopting SWG. The parameters discussed are enhanced protection against web-based attacks, content filtering, policy enforcement, Data Loss Prevention, etc. Present the topic in a bit more detail with this Impact Of Secure Web Gateway On Application Security Network Security Using Secure Web Gateway. Use it as a tool for discussion and navigation on Enforcement, Application, Prevention. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Benefits Of Microsoft Security Copilot Application Microsoft AI Solutions AI SS
Benefits Of Microsoft Security Copilot Application Microsoft AI Solutions AI SSThis slide highlights various benefits of Microsoft security copilot tool for medium and large scale organizations. Various benefits are incident response, threat hunting and security reporting for faster mitigation of future attacks. Introducing Benefits Of Microsoft Security Copilot Application Microsoft AI Solutions AI SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Incident Response, Threat Hunting, Security Reporting, using this template. Grab it now to reap its full benefits.
-
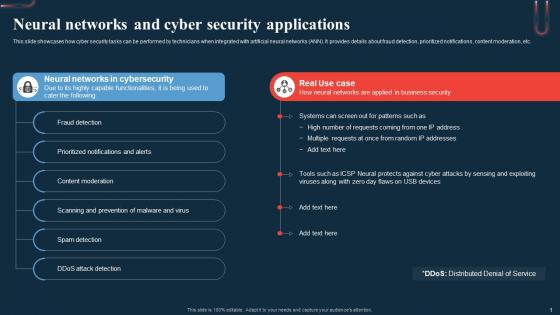 Neural Networks And Cyber Security Applications A Beginners Guide To Neural AI SS
Neural Networks And Cyber Security Applications A Beginners Guide To Neural AI SSThis slide showcases how cyber security tasks can be performed by technicians when integrated with artificial neural networks ANN. It provides details about fraud detection, prioritized notifications, content moderation, etc. Increase audience engagement and knowledge by dispensing information using Neural Networks And Cyber Security Applications A Beginners Guide To Neural AI SS. This template helps you present information on six stages. You can also present information on Detection, Notifications, Prevention using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social Security Restricted Application Strategy In Powerpoint And Google Slides Cpb
Social Security Restricted Application Strategy In Powerpoint And Google Slides CpbPresenting Social Security Restricted Application Strategy In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Social Security Restricted Application Strategy. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
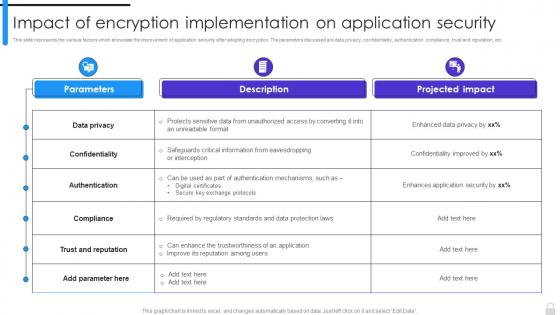 Encryption Implementation Strategies Impact Of Encryption Implementation On Application Security
Encryption Implementation Strategies Impact Of Encryption Implementation On Application SecurityThis slide represents the various factors which showcase the improvement of application security after adopting encryption. The parameters discussed are data privacy, confidentiality, authentication, compliance, trust and reputation, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Impact Of Encryption Implementation On Application Security. Dispense information and present a thorough explanation of Confidentiality, Data Privacy, Trust And Reputation, Application Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
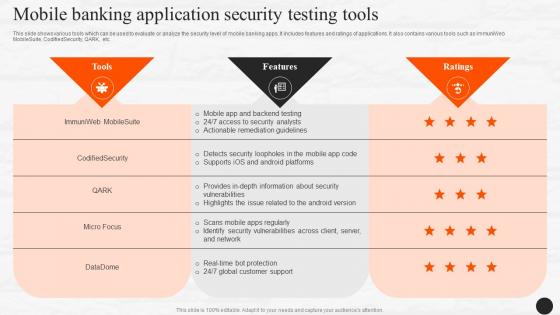 Mobile Banking Application Security Testing Tools E Wallets As Emerging Payment Method Fin SS V
Mobile Banking Application Security Testing Tools E Wallets As Emerging Payment Method Fin SS VThis slide shows various tools which can be used to evaluate or analyze the security level of mobile banking apps. It includes features and ratings of applications. It also contains various tools such as ImmuniWeb MobileSuite, CodifiedSecurity, QARK, etc. Present the topic in a bit more detail with this Mobile Banking Application Security Testing Tools E Wallets As Emerging Payment Method Fin SS V. Use it as a tool for discussion and navigation on Application, Evaluate, Analyze. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
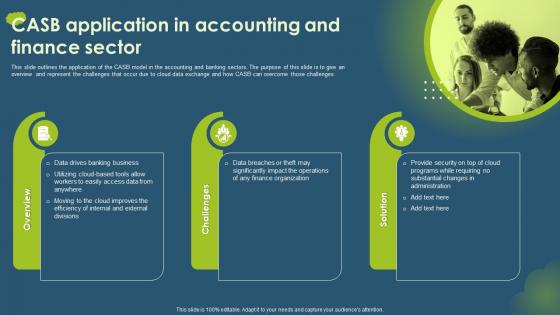 Cloud Access Security Broker CASB V2 CASB Application In Accounting And Finance Sector
Cloud Access Security Broker CASB V2 CASB Application In Accounting And Finance SectorThis slide outlines the application of the CASB model in the accounting and banking sectors. The purpose of this slide is to give an overview and represent the challenges that occur due to cloud data exchange and how CASB can overcome those challenges. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 CASB Application In Accounting And Finance Sector. This template helps you present information on three stages. You can also present information on Accounting And Banking Sectors, Cloud Data Exchange, Finance Organization, Data Drives Banking Business using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
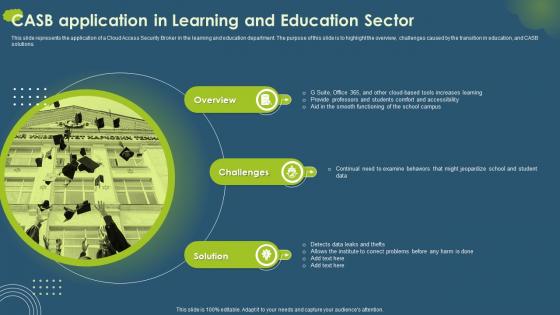 Cloud Access Security Broker CASB V2 CASB Application In Learning And Education Sector
Cloud Access Security Broker CASB V2 CASB Application In Learning And Education SectorThis slide represents the application of a Cloud Access Security Broker in the learning and education department. The purpose of this slide is to highlight the overview, challenges caused by the transition in education, and CASB solutions. Introducing Cloud Access Security Broker CASB V2 CASB Application In Learning And Education Sector to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Access Security Broker, Learning And Education Department, Transition In Education, using this template. Grab it now to reap its full benefits.
-
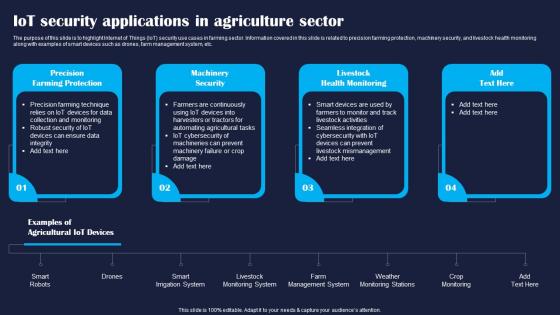 IoT Security Applications In Agriculture Sector Improving IoT Device Cybersecurity IoT SS
IoT Security Applications In Agriculture Sector Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to highlight Internet of Things IoT security use cases in farming sector. Information covered in this slide is related to precision farming protection, machinery security, and livestock health monitoring along with examples of smart devices such as drones, farm management system, etc. Increase audience engagement and knowledge by dispensing information using IoT Security Applications In Agriculture Sector Improving IoT Device Cybersecurity IoT SS. This template helps you present information on four stages. You can also present information on Protection, Security, Monitoring using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
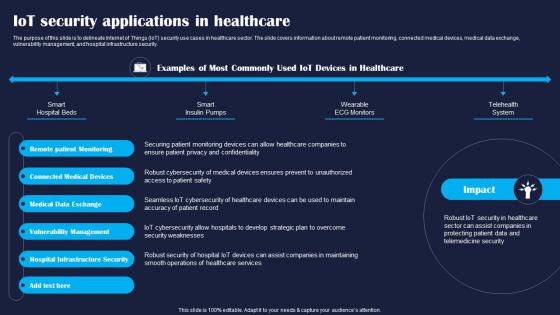 IoT Security Applications In Healthcare Improving IoT Device Cybersecurity IoT SS
IoT Security Applications In Healthcare Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to delineate Internet of Things IoT security use cases in healthcare sector. The slide covers information about remote patient monitoring, connected medical devices, medical data exchange, vulnerability management, and hospital infrastructure security. Present the topic in a bit more detail with this IoT Security Applications In Healthcare Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Exchange, Devices, Monitoring. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
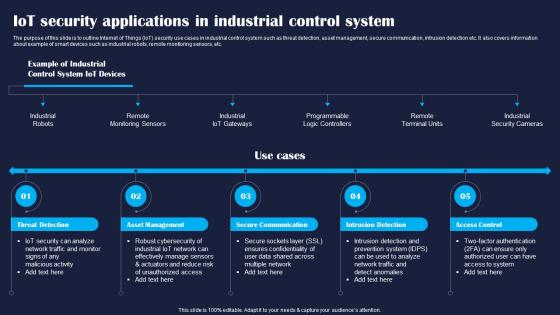 IoT Security Applications In Industrial Improving IoT Device Cybersecurity IoT SS
IoT Security Applications In Industrial Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to outline Internet of Things IoT security use cases in industrial control system such as threat detection, asset management, secure communication, intrusion detection etc. It also covers information about example of smart devices such as industrial robots, remote monitoring sensors, etc. Increase audience engagement and knowledge by dispensing information using IoT Security Applications In Industrial Improving IoT Device Cybersecurity IoT SS. This template helps you present information on five stages. You can also present information on Threat, Management, Communication using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
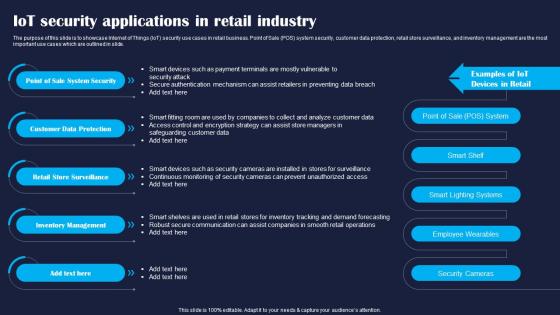 IoT Security Applications In Retail Industry Improving IoT Device Cybersecurity IoT SS
IoT Security Applications In Retail Industry Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase Internet of Things IoT security use cases in retail business. Point of Sale POS system security, customer data protection, retail store surveillance, and inventory management are the most important use cases which are outlined in slide. Introducing IoT Security Applications In Retail Industry Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Security, Protection, Retail, using this template. Grab it now to reap its full benefits.
-
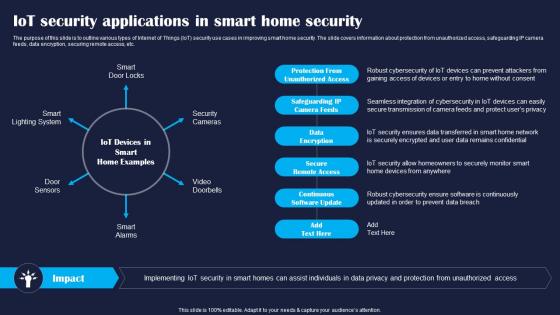 IoT Security Applications In Smart Home Improving IoT Device Cybersecurity IoT SS
IoT Security Applications In Smart Home Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to outline various types of Internet of Things IoT security use cases in improving smart home security. The slide covers information about protection from unauthorized access, safeguarding IP camera feeds, data encryption, securing remote access, etc. Increase audience engagement and knowledge by dispensing information using IoT Security Applications In Smart Home Improving IoT Device Cybersecurity IoT SS. This template helps you present information on six stages. You can also present information on Access, Encryption, Secure using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Best Maintain Security Of Comprehensive Guide To Blockchain Wallets And Applications BCT SS
Best Maintain Security Of Comprehensive Guide To Blockchain Wallets And Applications BCT SSThis slide covers tips to provide users on how to enhance the security of their desktop wallets for managing cryptocurrencies. The purpose of this template is to provide recommendations such as using a strong, unique password, ensuring desktop wallet is running on recent version, avoiding accessing desktop, making a wallet backup, using well established desktop wallet, etc. Present the topic in a bit more detail with this Best Maintain Security Of Comprehensive Guide To Blockchain Wallets And Applications BCT SS. Use it as a tool for discussion and navigation on Combination, Verification, Software. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Best Practices To Secure And Use Comprehensive Guide To Blockchain Wallets And Applications BCT SS
Best Practices To Secure And Use Comprehensive Guide To Blockchain Wallets And Applications BCT SSThis slide covers tips to increase security of paper wallets for using it effectively. The purpose of this template is to provide recommendations such as using reputable tools or websites, encrypting private keys with strong passphrase, creating multiple copies of paper wallets, testing and verifying paper wallet, etc. Present the topic in a bit more detail with this Best Practices To Secure And Use Comprehensive Guide To Blockchain Wallets And Applications BCT SS. Use it as a tool for discussion and navigation on Passphrase, Cryptocurrency, Locations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
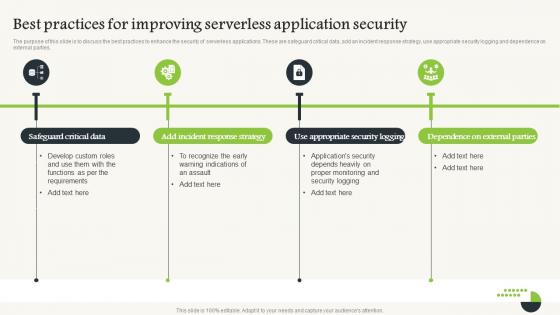 Serverless Computing V2 Best Practices For Improving Serverless Application Security
Serverless Computing V2 Best Practices For Improving Serverless Application SecurityThe purpose of this slide is to discuss the best practices to enhance the security of serverless applications. These are safeguard critical data, add an incident response strategy, use appropriate security logging and dependence on external parties. Introducing Serverless Computing V2 Best Practices For Improving Serverless Application Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Safeguard Critical Data, Incident Response Strategy, Serverless Application Security, Appropriate Security Logging, using this template. Grab it now to reap its full benefits.
-
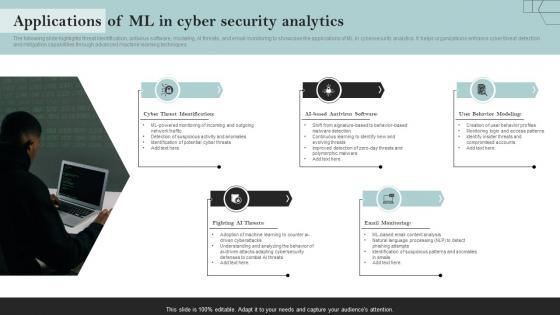 Applications Of ML In Cyber Security Analytics
Applications Of ML In Cyber Security AnalyticsThe following slide highlights threat identification, antivirus software, modeling, AI threats, and email monitoring to showcase the applications of ML in cybersecurity analytics. It helps organizations enhance cyber threat detection and mitigation capabilities through advanced machine learning techniques. Presenting our set of slides with Applications Of ML In Cyber Security Analytics. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identification, Antivirus, Behavior.
-
 Crypto Tokens Unlocking Applications Of Security Tokens For Real World Assets BCT SS
Crypto Tokens Unlocking Applications Of Security Tokens For Real World Assets BCT SSThis slide covers key use cases of security tokens for real-world assets tokenization. It includes real estate tokenization, artwork ownership tokens, commodities tokenization, revenue-sharing agreements, etc. Increase audience engagement and knowledge by dispensing information using Crypto Tokens Unlocking Applications Of Security Tokens For Real World Assets BCT SS This template helps you present information on Five stages. You can also present information on Artwork Ownership Tokens, Revenue-Sharing Agreements using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
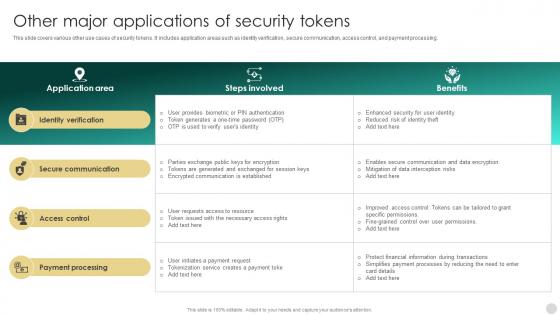 Crypto Tokens Unlocking Other Major Applications Of Security Tokens BCT SS
Crypto Tokens Unlocking Other Major Applications Of Security Tokens BCT SSThis slide covers various other use cases of security tokens. It includes application areas such as identity verification, secure communication, access control, and payment processing. Deliver an outstanding presentation on the topic using this Crypto Tokens Unlocking Other Major Applications Of Security Tokens BCT SS Dispense information and present a thorough explanation of Identity Verification, Secure Communication, Access Control using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
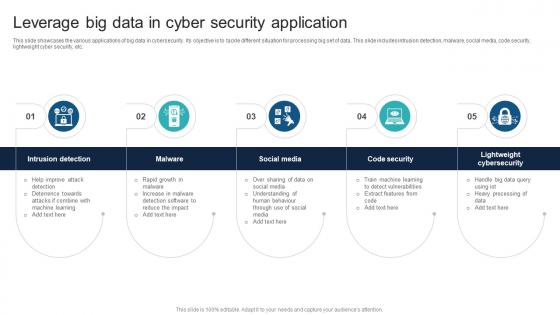 Leverage Big Data In Cyber Security Application
Leverage Big Data In Cyber Security ApplicationThis slide showcases the various applications of big data in cybersecurity. Its objective is to tackle different situation for processing big set of data. This slide includes intrusion detection, malware, social media, code security, lightweight cyber security, etc. Presenting our set of slides with Leverage Big Data In Cyber Security Application. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Detection, Social, security.
-
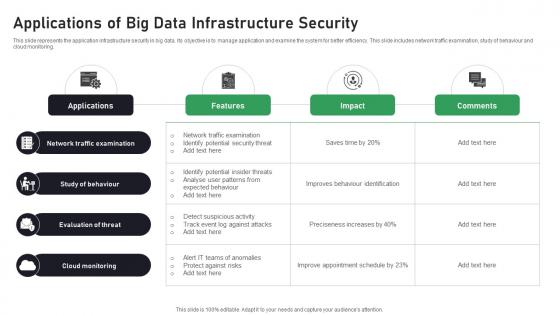 Applications Of Big Data Infrastructure Security
Applications Of Big Data Infrastructure SecurityThis slide represents the application infrastructure security in big data. Its objective is to manage application and examine the system for better efficiency. This slide includes network traffic examination, study of behaviour and cloud monitoring. Introducing our Applications Of Big Data Infrastructure Security set of slides. The topics discussed in these slides are Network, Behaviour, Evaluation. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Security Checklist To Protect Saas Applications
Cyber Security Checklist To Protect Saas ApplicationsThis slide represents cybersecurity checklist for SaaS applications to protect data. It aims to assist organizations in identifying potential vulnerabilities as well as examining security standards. It includes various elements such as backing up creation and testing, using real-time security service, etc. Introducing our Cyber Security Checklist To Protect Saas Applications set of slides. The topics discussed in these slides are Determines Data Isolation, Safeguards Against Data Theft This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Role Of Saas Applications In Cyber Security
Role Of Saas Applications In Cyber SecurityThis slide represents SaaS apps significance to cyber security. It aims to ensure continuous monitoring and updates to mitigate risks and protect sensitive data within applications. It includes various aspects such as authentication, leveraging data, etc. Introducing our premium set of slides with Role Of Saas Applications In Cyber Security Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Authentication, Enhanced Security, High Scalability, Strong Encryption. So download instantly and tailor it with your information.
-
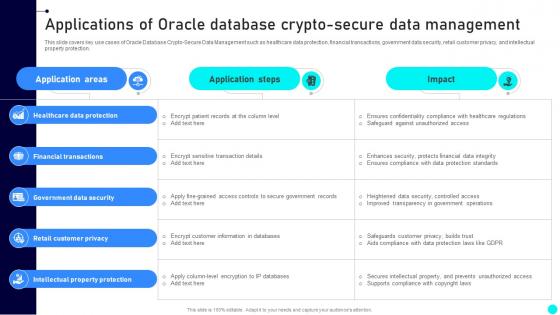 Applications Of Oracle Database Crypto Secure Exploring Diverse Blockchain BCT SS
Applications Of Oracle Database Crypto Secure Exploring Diverse Blockchain BCT SSThis slide covers key use cases of Oracle Database Crypto-Secure Data Management such as healthcare data protection, financial transactions, government data security, retail customer privacy, and intellectual property protection. Deliver an outstanding presentation on the topic using this Applications Of Oracle Database Crypto Secure Exploring Diverse Blockchain BCT SS Dispense information and present a thorough explanation of Healthcare Data, Financial Transactions, Customer Privacy using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Applications Of Digital Solution For Ensuring Data Security
Applications Of Digital Solution For Ensuring Data SecurityThis slide showcases use cases of digital solution. The main purpose of this template is to showcase methods for optimizing resources in business. This includes streamlining operations, improving decision making, enabling remote work, etc. Presenting our set of slides with Applications Of Digital Solution For Ensuring Data Security This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Streamlining Operations, Enhancing Customer Experience, Improve Decision Making
-
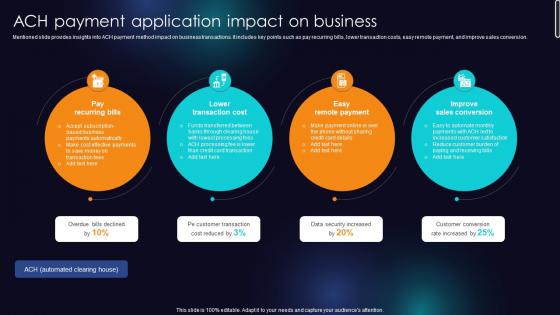 ACH Payment Application Impact On Business Enhancing Transaction Security With E Payment
ACH Payment Application Impact On Business Enhancing Transaction Security With E PaymentMentioned slide provides insights into ACH payment method impact on business transactions. It includes key points such as pay recurring bills, lower transaction costs, easy remote payment, and improve sales conversion. Introducing ACH Payment Application Impact On Business Enhancing Transaction Security With E Payment to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Pay Recurring Bills, Lower Transaction Cost, Easy Remote Payment using this template. Grab it now to reap its full benefits.
-
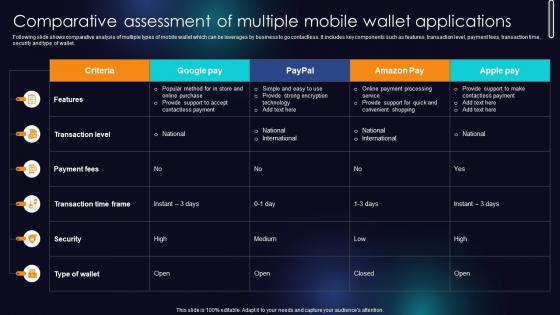 Comparative Assessment Of Multiple Mobile Wallet Applications Enhancing Transaction Security With E Payment
Comparative Assessment Of Multiple Mobile Wallet Applications Enhancing Transaction Security With E PaymentFollowing slide shows comparative analysis of multiple types of mobile wallet which can be leverages by business to go contactless. It includes key components such as features, transaction level, payment fees, transaction time, security and type of wallet. Present the topic in a bit more detail with this Comparative Assessment Of Multiple Mobile Wallet Applications Enhancing Transaction Security With E Payment Use it as a tool for discussion and navigation on Features, Transaction Level, Payment Fees This template is free to edit as deemed fit for your organization. Therefore download it now.
-
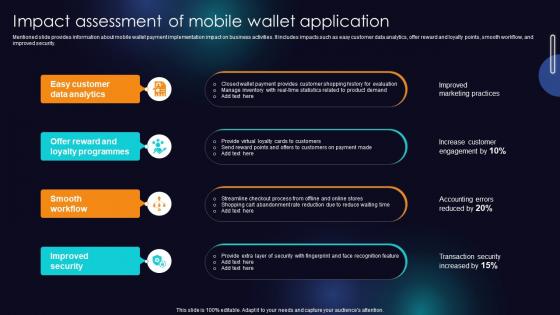 Impact Assessment Of Mobile Wallet Application Enhancing Transaction Security With E Payment
Impact Assessment Of Mobile Wallet Application Enhancing Transaction Security With E PaymentMentioned slide provides information about mobile wallet payment implementation impact on business activities. It includes impacts such as easy customer data analytics, offer reward and loyalty points, smooth workflow, and improved security. Increase audience engagement and knowledge by dispensing information using Impact Assessment Of Mobile Wallet Application Enhancing Transaction Security With E Payment This template helps you present information on four stages. You can also present information on Easy Customer Data Analytics, Smooth Workflow, Improved Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
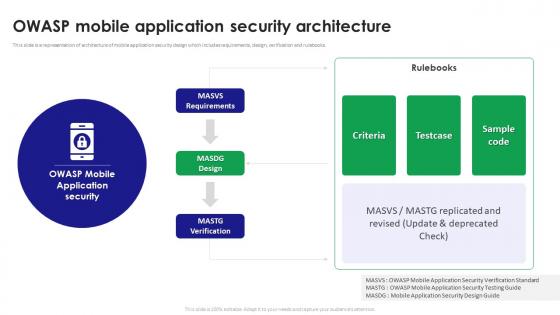 Owasp Mobile Application Security Architecture
Owasp Mobile Application Security ArchitectureThis slide is a representation of architecture of mobile application security design which includes requirements, design, verification and rulebooks. Presenting our well structured Owasp Mobile Application Security Architecture. The topics discussed in this slide are Mobile Application, Security Architecture, Verification And Rulebooks. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
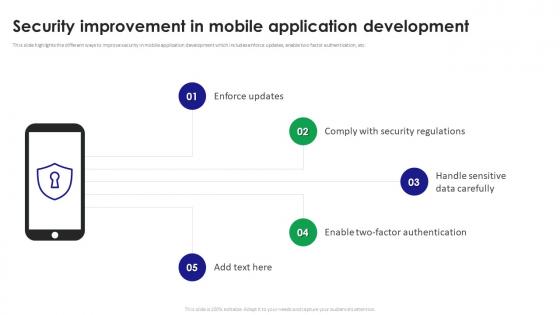 Security Improvement In Mobile Application Development
Security Improvement In Mobile Application DevelopmentThis slide highlights the different ways to improve security in mobile application development which includes enforce updates, enable two factor authentication, etc. Introducing our premium set of slides with name Security Improvement In Mobile Application Development. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Security Improvement, Mobile Application Development, Handle Sensitive Data Carefully. So download instantly and tailor it with your information.
-
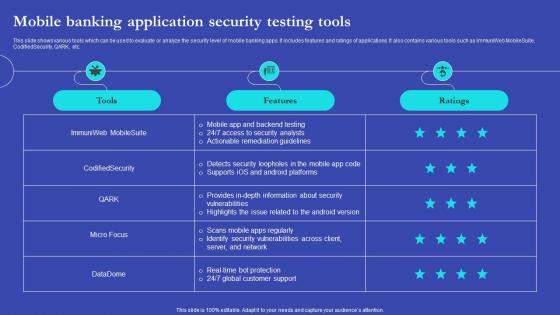 NEO Banks For Digital Funds Mobile Banking Application Security Testing Tools Fin SS V
NEO Banks For Digital Funds Mobile Banking Application Security Testing Tools Fin SS VThis slide shows various tools which can be used to evaluate or analyze the security level of mobile banking apps. It includes features and ratings of applications. It also contains various tools such as ImmuniWeb MobileSuite, CodifiedSecurity, QARK, etc. Present the topic in a bit more detail with this NEO Banks For Digital Funds Mobile Banking Application Security Testing Tools Fin SS V. Use it as a tool for discussion and navigation on Mobile Banking Application, Security Testing Tools, Ratings Of Applications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
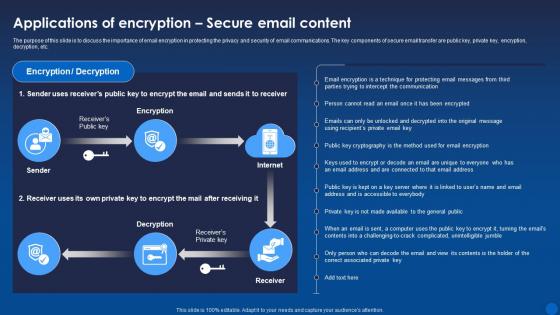 Applications Secure Email Content Encryption For Data Privacy In Digital Age It
Applications Secure Email Content Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to discuss the importance of email encryption in protecting the privacy and security of email communications. The key components of secure email transfer are public key, private key, encryption, decryption, etc. Present the topic in a bit more detail with this Applications Secure Email Content Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Applications, Encryption, Decryption. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
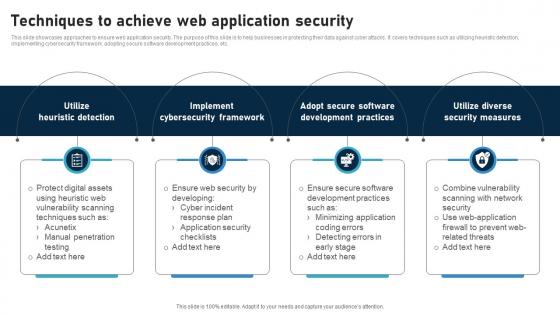 Techniques To Achieve Web Application Security
Techniques To Achieve Web Application SecurityThis slide showcases approaches to ensure web application security. The purpose of this slide is to help businesses in protecting their data against cyber attacks. It covers techniques such as utilizing heuristic detection, implementing cybersecurity framework, adopting secure software development practices, etc. Introducing our premium set of slides with Techniques To Achieve Web Application Security Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Utilize Heuristic Detection, Implement Cybersecurity Framework, Security Measures So download instantly and tailor it with your information.
-
 Web Application Firewall Icon For Application Security
Web Application Firewall Icon For Application SecurityPresenting our well structured Web Application Firewall Icon For Application Security The topics discussed in this slide are Web Application Firewall Icon, Application Security This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Web Application Security Checklist Icon
Web Application Security Checklist IconIntroducing our premium set of slides with Web Application Security Checklist Icon Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Web Application Security Checklist Icon So download instantly and tailor it with your information.
-
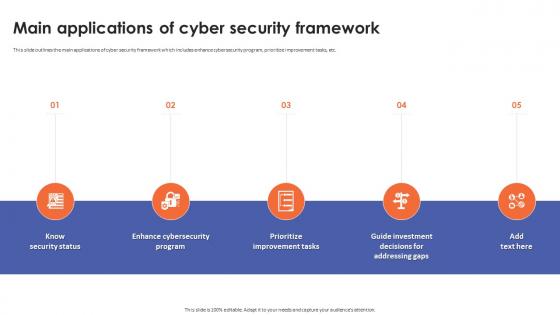 Main Applications Of Cyber Security Framework
Main Applications Of Cyber Security FrameworkThis slide outlines the main applications of cyber security framework which includes enhance cybersecurity program, prioritize improvement tasks, etc. Introducing Main Applications Of Cyber Security Framework to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Enhance Cybersecurity Program, Prioritize Improvement Tasks, Know Security Status, Guide Investment Decisions, using this template. Grab it now to reap its full benefits.
-
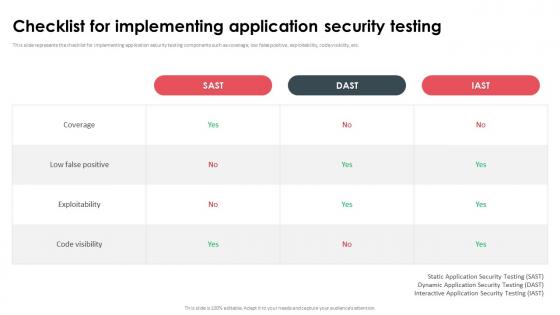 Checklist For Implementing Application Security Testing
Checklist For Implementing Application Security TestingThis slide represents the checklist for implementing application security testing components such as coverage, low false positive, exploitability, code visibility, etc. Deliver an outstanding presentation on the topic using this Checklist For Implementing Application Security Testing. Dispense information and present a thorough explanation of Static Application Security Testing, Dynamic Application Security Testing, Interactive Application Security Testing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
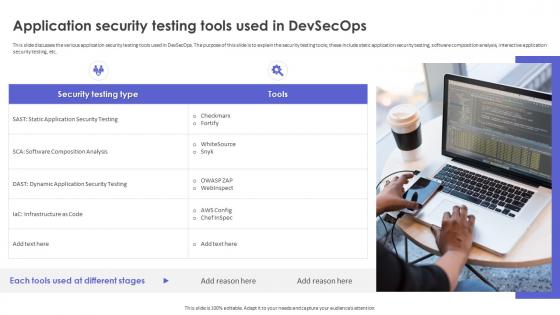 Strategic Roadmap To Implement DevSecOps Application Security Testing Tools Used In DevSecOps
Strategic Roadmap To Implement DevSecOps Application Security Testing Tools Used In DevSecOpsThis slide discusses the various application security testing tools used in DevSecOps. The purpose of this slide is to explain the security testing tools these include static application security testing, software composition analysis, interactive application security testing, etc. Increase audience engagement and knowledge by dispensing information using Strategic Roadmap To Implement DevSecOps Application Security Testing Tools Used In DevSecOps. This template helps you present information on one stages. You can also present information on Application Security Testing, Software Composition Analysis, Interactive Application Security Testing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
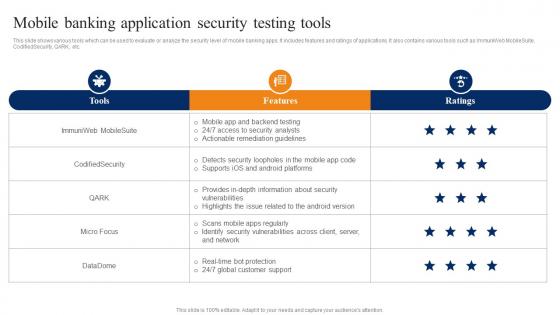 Mobile Banking Application Security Smartphone Banking For Transferring Funds Digitally Fin SS V
Mobile Banking Application Security Smartphone Banking For Transferring Funds Digitally Fin SS VThis slide shows various tools which can be used to evaluate or analyze the security level of mobile banking apps. It includes features and ratings of applications. It also contains various tools such as ImmuniWeb MobileSuite, CodifiedSecurity, QARK, etc. Present the topic in a bit more detail with this Mobile Banking Application Security Smartphone Banking For Transferring Funds Digitally Fin SS V. Use it as a tool for discussion and navigation on Mobile App Backend Testing, Access Security Analysts, Actionable Remediation Guidelines. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Agenda For Devsecops Best Practices For Secure Applications
Agenda For Devsecops Best Practices For Secure ApplicationsIncrease audience engagement and knowledge by dispensing information using Agenda For Devsecops Best Practices For Secure Applications. This template helps you present information on six stages. You can also present information on Driving Digital Transformation, Devsecops Best Practices, Secure Applications using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
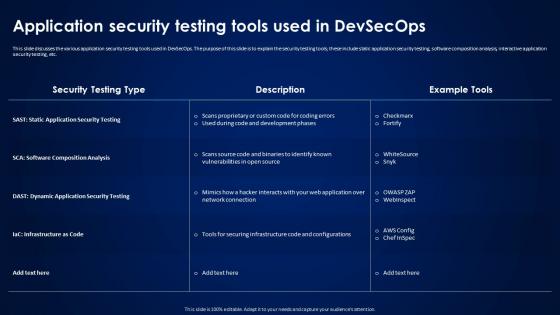 Devsecops Best Practices For Secure Application Security Testing Tools Used In Devsecops
Devsecops Best Practices For Secure Application Security Testing Tools Used In DevsecopsThis slide discusses the various application security testing tools used in DevSecOps. The purpose of this slide is to explain the security testing tools, these include static application security testing, software composition analysis, interactive application security testing, etc. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure Application Security Testing Tools Used In Devsecops. Dispense information and present a thorough explanation of Application Security Testing, Dynamic Application Security Testing, Infrastructure As Code using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Devsecops Best Practices For Secure Applications For Table Of Content
Devsecops Best Practices For Secure Applications For Table Of ContentThis slide showcases the comparative analysis of the before versus after DevSecOps implementation. The purpose of this slide is to discuss the different performance aspects and how DevSecOps has proved beneficial for these aspects. Present the topic in a bit more detail with this Devsecops Best Practices For Secure Applications For Table Of Content. Use it as a tool for discussion and navigation on Pipeline Security, Development Pre Commit Stage, Continuous Integration Commit Stage. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Icons Slide For Devsecops Best Practices For Secure Applications
Icons Slide For Devsecops Best Practices For Secure ApplicationsIntroducing our well researched set of slides titled Icons Slide For Devsecops Best Practices For Secure Applications. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
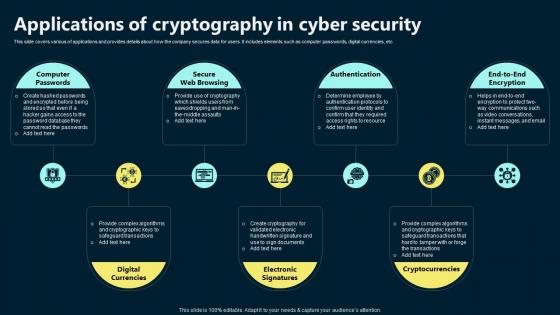 Applications Of Cryptography In Cyber Security
Applications Of Cryptography In Cyber SecurityThis slide covers various of applications and provides details about how the company secures data for users. It includes elements such as computer passwords, digital currencies, etc. Presenting our set of slides with Applications Of Cryptography In Cyber Security. This exhibits information on seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Computer Passwords, Secure Web Browsing, Authentication.
-
 Crypto Wallets Types And Applications Best Practices For The Security Of Crypto Wallets In Market
Crypto Wallets Types And Applications Best Practices For The Security Of Crypto Wallets In MarketThis slide aims to highlight some broad security aspects of crypto wallets. This slide outlines the general security purposes such as passwords, 2FA accounts, phrases for secure passwords, secure hardware, keeping the seed phrase off devices as well, etc. Deliver an outstanding presentation on the topic using this Crypto Wallets Types And Applications Best Practices For The Security Of Crypto Wallets In Market. Dispense information and present a thorough explanation of Storage Mechanism, Network, Crypto Wallets In Market, Multisignature Wallets using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
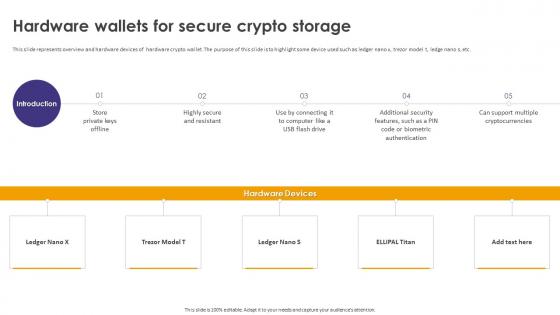 Crypto Wallets Types And Applications Hardware Wallets For Secure Crypto Storage
Crypto Wallets Types And Applications Hardware Wallets For Secure Crypto StorageThis slide represents overview and hardware devices of hardware crypto wallet. The purpose of this slide is to highlight some device used such as ledger nano x, trezor model t, ledge nano s, etc. Increase audience engagement and knowledge by dispensing information using Crypto Wallets Types And Applications Hardware Wallets For Secure Crypto Storage. This template helps you present information on five stages. You can also present information on Hardware Wallets, Secure Crypto Storage, Hardware Devices, Biometric Authentication using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
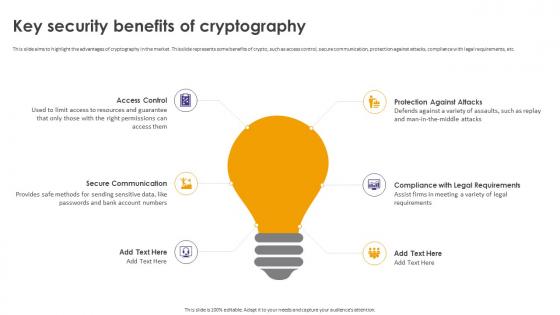 Crypto Wallets Types And Applications Key Security Benefits Of Cryptography
Crypto Wallets Types And Applications Key Security Benefits Of CryptographyThis slide aims to highlight the advantages of cryptography in the market. This slide represents some benefits of crypto, such as access control, secure communication, protection against attacks, compliance with legal requirements, etc. Introducing Crypto Wallets Types And Applications Key Security Benefits Of Cryptography to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Protection Against Attacks, Compliance With Legal Requirements, Secure Communication, using this template. Grab it now to reap its full benefits.
-
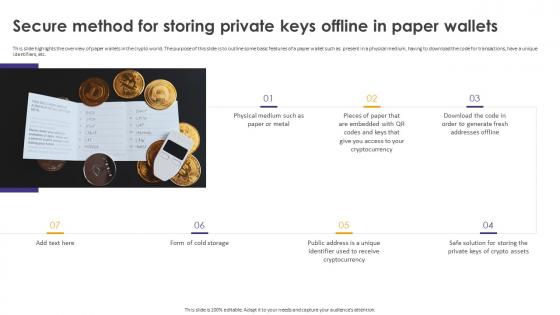 Crypto Wallets Types And Applications Secure Method For Storing Private Keys Offline In Paper Wallets
Crypto Wallets Types And Applications Secure Method For Storing Private Keys Offline In Paper WalletsThis slide highlights the overview of paper wallets in the crypto world. The purpose of this slide is to outline some basic features of a paper wallet such as present in a physical medium, having to download the code for transactions, have a unique identifiers, etc. Increase audience engagement and knowledge by dispensing information using Crypto Wallets Types And Applications Secure Method For Storing Private Keys Offline In Paper Wallets. This template helps you present information on seven stages. You can also present information on Paper Wallets, Code For Transactions, Form Of Cold Storage, Fresh Addresses Offline using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
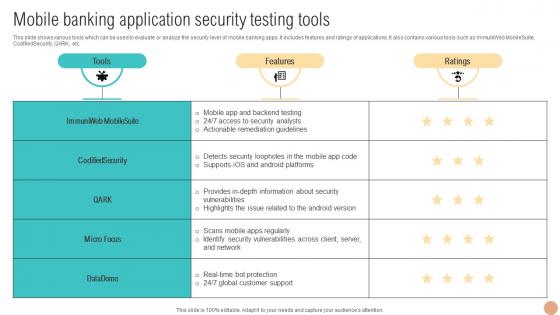 Mobile Banking Application Security Testing Digital Wallets For Making Hassle Fin SS V
Mobile Banking Application Security Testing Digital Wallets For Making Hassle Fin SS VThis slide shows various tools which can be used to evaluate or analyze the security level of mobile banking apps. It includes features and ratings of applications. It also contains various tools such as ImmuniWeb MobileSuite, CodifiedSecurity, QARK, etc. Deliver an outstanding presentation on the topic using this Mobile Banking Application Security Testing Digital Wallets For Making Hassle Fin SS V. Dispense information and present a thorough explanation of Banking, Mobile, Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Banking Solutions For Improving Customer Mobile Banking Application Security Testing Tools Fin SS V
Banking Solutions For Improving Customer Mobile Banking Application Security Testing Tools Fin SS VThis slide shows various tools which can be used to evaluate or analyze the security level of mobile banking apps. It includes features and ratings of applications. It also contains various tools such as ImmuniWeb MobileSuite, CodifiedSecurity, QARK, etc. Present the topic in a bit more detail with this Banking Solutions For Improving Customer Mobile Banking Application Security Testing Tools Fin SS V. Use it as a tool for discussion and navigation on Mobile Banking Application, Security Testing Tools, Mobile Banking Apps, Real Time Bot Protection. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
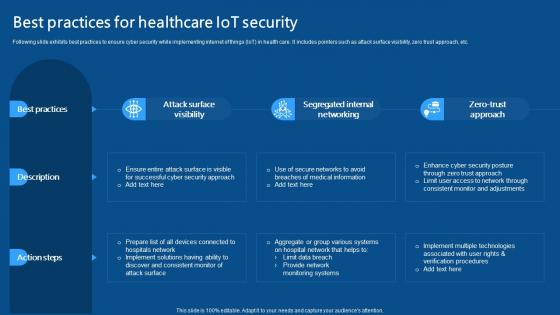 Best Practices For Healthcare IoT Security IoMT Applications In Medical Industry IoT SS V
Best Practices For Healthcare IoT Security IoMT Applications In Medical Industry IoT SS VFollowing slide exhibits best practices to ensure cyber security while implementing internet of things IoT in health care. It includes pointers such as attack surface visibility, zero trust approach, etc. Introducing Best Practices For Healthcare IoT Security IoMT Applications In Medical Industry IoT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Attack Surface Visibility, Segregated Internal Networking, Zero Trust Approach, using this template. Grab it now to reap its full benefits.
-
 Secure Your Digital Assets Understanding Applications And Use Cases Of Cryptography
Secure Your Digital Assets Understanding Applications And Use Cases Of CryptographyThis slide represents the application of cryptography in the market. The purpose of this slide is to outline the implements such as computer passwords, digital currencies, secure web browsing, electronic signatures, authentications, etc. Increase audience engagement and knowledge by dispensing information using Secure Your Digital Assets Understanding Applications And Use Cases Of Cryptography. This template helps you present information on six stages. You can also present information on Computer Passwords, Digital Currencies, Secure Web Browsing, Electronic Signatures, Authentication using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
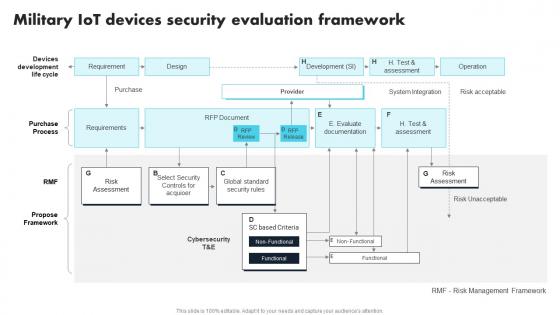 Military IoT Devices Security Evaluation Framework Comprehensive Guide For Applications IoT SS
Military IoT Devices Security Evaluation Framework Comprehensive Guide For Applications IoT SSPresent the topic in a bit more detail with this Military IoT Devices Security Evaluation Framework Comprehensive Guide For Applications IoT SS. Use it as a tool for discussion and navigation on Devices Development Life Cycle, Purchase Process, Propose Framework. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
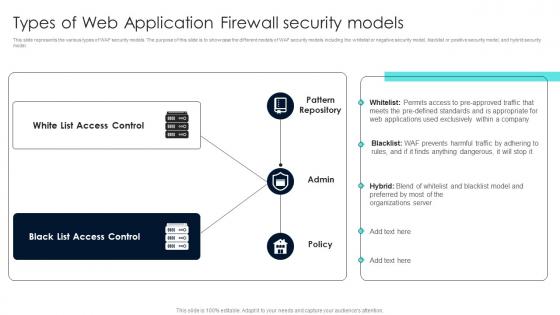 Firewall Network Security Types Of Web Application Firewall Security Models
Firewall Network Security Types Of Web Application Firewall Security ModelsThis slide represents the various types of WAF security models. The purpose of this slide is to showcase the different models of WAF security models including the whitelist or negative security model, blacklist or positive security model, and hybrid security model. Present the topic in a bit more detail with this Firewall Network Security Types Of Web Application Firewall Security Models Use it as a tool for discussion and navigation on Black List Access Control, White List Access Control This template is free to edit as deemed fit for your organization. Therefore download it now.
-
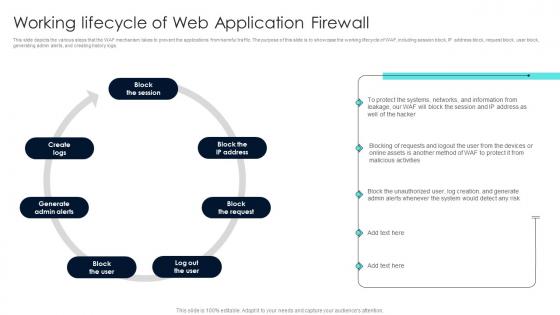 Firewall Network Security Working Lifecycle Of Web Application Firewall
Firewall Network Security Working Lifecycle Of Web Application FirewallThis slide depicts the various steps that the WAF mechanism takes to prevent the applications from harmful traffic. The purpose of this slide is to showcase the working lifecycle of WAF, including session block, IP address block, request block, user block, generating admin alerts, and creating history logs. Increase audience engagement and knowledge by dispensing information using Firewall Network Security Working Lifecycle Of Web Application Firewall This template helps you present information on Seven stages. You can also present information on Log Out The User, Block The User, Generate Admin Alerts using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.



