Powerpoint Templates and Google slides for Asset Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Secure Your Digital Assets Major Drawbacks Of Cold Wallets In Market
Secure Your Digital Assets Major Drawbacks Of Cold Wallets In MarketThis slide discusses the disadvantages of using cold wallets in transactions of cryptocurrency. The purpose of this slide is to highlight the negatives of cold wallets, such as lack of functionality, cost, less convenience, etc. Introducing Secure Your Digital Assets Major Drawbacks Of Cold Wallets In Market to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Transactions Of Cryptocurrency, Negatives Of Cold Wallets, Lack Of Functionality, Less Convenience, using this template. Grab it now to reap its full benefits.
-
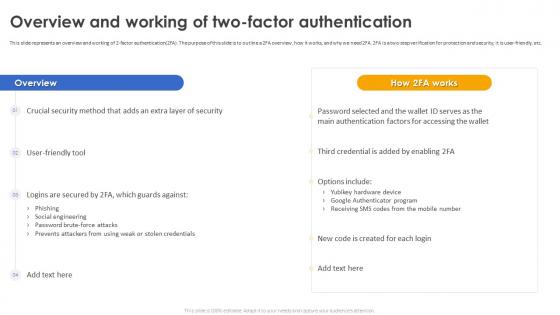 Secure Your Digital Assets Overview And Working Of Two Factor Authentication
Secure Your Digital Assets Overview And Working Of Two Factor AuthenticationThis slide represents an overview and working of 2-factor authentication 2FA. The purpose of this slide is to outline a 2FA overview, how it works, and why we need 2FA. 2FA is a two-step verification for protection and security, it is user-friendly, etc. Deliver an outstanding presentation on the topic using this Secure Your Digital Assets Overview And Working Of Two Factor Authentication. Dispense information and present a thorough explanation of Phishing, Social Engineering, Password Brute Force Attacks, Prevents Attackers, Stolen Credentials using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Secure Your Digital Assets Overview Of Cryptocurrency Awareness Training Program
Secure Your Digital Assets Overview Of Cryptocurrency Awareness Training ProgramThis slide represents the training program for cryptocurrency awareness which will help individuals. The purpose of this slide is to outline the mode, cost, agenda, and schedule for the training programs. Present the topic in a bit more detail with this Secure Your Digital Assets Overview Of Cryptocurrency Awareness Training Program. Use it as a tool for discussion and navigation on Basics Of Cryptocurrency, Blockchain Technology, Significance Of Transactions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
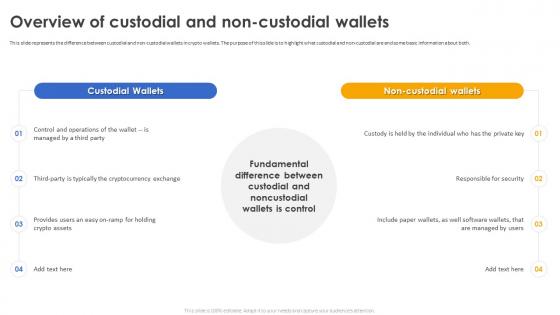 Secure Your Digital Assets Overview Of Custodial And Non Custodial Wallets
Secure Your Digital Assets Overview Of Custodial And Non Custodial WalletsThis slide represents the difference between custodial and non-custodial wallets in crypto wallets. The purpose of this slide is to highlight what custodial and non-custodial are and some basic information about both. Increase audience engagement and knowledge by dispensing information using Secure Your Digital Assets Overview Of Custodial And Non Custodial Wallets. This template helps you present information on four stages. You can also present information on Custodial Wallets, Non Custodial Wallets, Responsible For Security, Well Software Wallets using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Secure Your Digital Assets Red Flags To Be Cautious For Cryptocurrency Scams
Secure Your Digital Assets Red Flags To Be Cautious For Cryptocurrency ScamsThis slide discusses the red flags that should be considered while doing transactions in cryptocurrency. This slide aims to highlight flags such as promises of guaranteed returns, lack of project transparency, pressure to act quickly, etc. Introducing Secure Your Digital Assets Red Flags To Be Cautious For Cryptocurrency Scams to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Promises Of Guaranteed Returns, Lack Of Project Transparency, Pressure To Act Quickly, using this template. Grab it now to reap its full benefits.
-
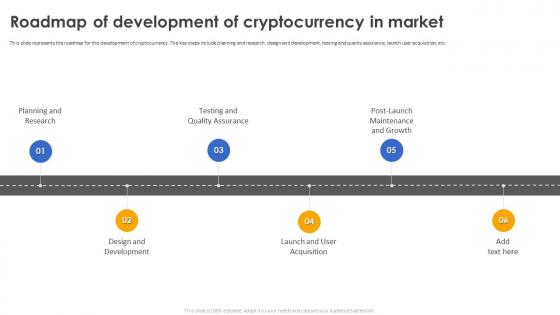 Secure Your Digital Assets Roadmap Of Development Of Cryptocurrency In Market
Secure Your Digital Assets Roadmap Of Development Of Cryptocurrency In MarketThis slide represents the roadmap for the development of cryptocurrency. The key steps include planning and research, design and development, testing and quality assurance, launch user acquisition, etc. Increase audience engagement and knowledge by dispensing information using Secure Your Digital Assets Roadmap Of Development Of Cryptocurrency In Market. This template helps you present information on six stages. You can also present information on Post Launch Maintenance And Growth, Testing And Quality Assurance, Planning And Research, Design And Development using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
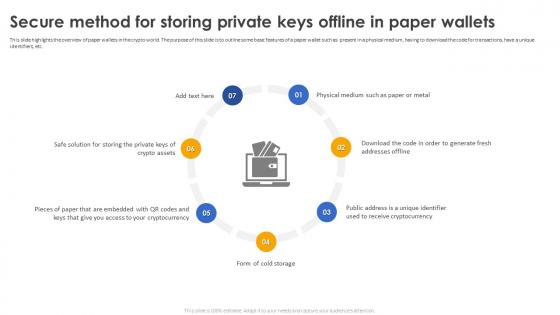 Secure Your Digital Assets Secure Method For Storing Private Keys Offline In Paper Wallets
Secure Your Digital Assets Secure Method For Storing Private Keys Offline In Paper WalletsThis slide highlights the overview of paper wallets in the crypto world. The purpose of this slide is to outline some basic features of a paper wallet such as present in a physical medium, having to download the code for transactions, have a unique identifiers, etc. Introducing Secure Your Digital Assets Secure Method For Storing Private Keys Offline In Paper Wallets to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Paper Wallets, Crypto World, Unique Identifiers, Form Of Cold Storage, using this template. Grab it now to reap its full benefits.
-
 Secure Your Digital Assets Steps To Follow For Creating A Crypto Wallet
Secure Your Digital Assets Steps To Follow For Creating A Crypto WalletThe purpose of this slide is to discuss the steps to follow while opening the crypto wallet. This slide highlights those steps, such as selecting the software app, downloading the wallet app, creating the account, transferring the assets, etc. Increase audience engagement and knowledge by dispensing information using Secure Your Digital Assets Steps To Follow For Creating A Crypto Wallet. This template helps you present information on five stages. You can also present information on Crypto Wallet, Transferring The Assets, Downloading The Wallet App using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Secure Your Digital Assets Steps To Follow For Creating Crypto Wallet
Secure Your Digital Assets Steps To Follow For Creating Crypto WalletThe purpose of this slide is to discuss the steps to follow while opening the crypto wallet. This slide highlights those steps, such as selecting the software app, downloading the wallet app, creating the account, transferring the assets, etc. Introducing Secure Your Digital Assets Steps To Follow For Creating Crypto Wallet to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Crypto Wallet, Software App, Downloading The Wallet App, Transferring The Assets, using this template. Grab it now to reap its full benefits.
-
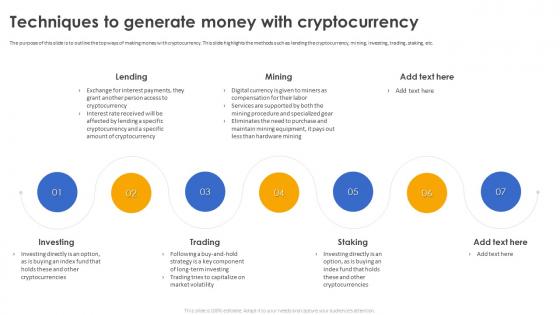 Secure Your Digital Assets Techniques To Generate Money With Cryptocurrency
Secure Your Digital Assets Techniques To Generate Money With CryptocurrencyThe purpose of this slide is to outline the top ways of making money with cryptocurrency. This slide highlights the methods such as lending the cryptocurrency, mining, investing, trading, staking, etc. Increase audience engagement and knowledge by dispensing information using Secure Your Digital Assets Techniques To Generate Money With Cryptocurrency. This template helps you present information on seven stages. You can also present information on Techniques To Generate Money, Mining, Investing, Trading, Staking using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
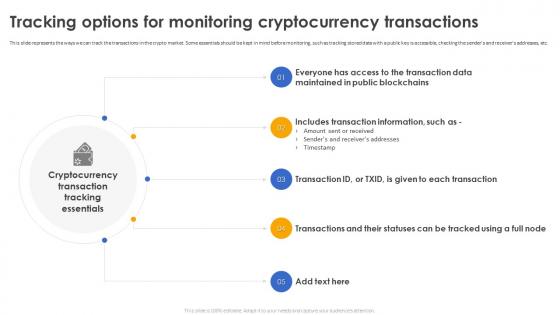 Secure Your Digital Assets Tracking Options For Monitoring Cryptocurrency Transactions
Secure Your Digital Assets Tracking Options For Monitoring Cryptocurrency TransactionsThis slide represents the ways we can track the transactions in the crypto market. Some essentials should be kept in mind before monitoring, such as tracking stored data with a public key is accessible, checking the senders and receivers addresses, etc. Introducing Secure Your Digital Assets Tracking Options For Monitoring Cryptocurrency Transactions to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Cryptocurrency Transaction, Tracking Essentials, Timestamp, Public Blockchains, using this template. Grab it now to reap its full benefits.
-
 Secure Your Digital Assets Understanding Applications And Use Cases Of Cryptography
Secure Your Digital Assets Understanding Applications And Use Cases Of CryptographyThis slide represents the application of cryptography in the market. The purpose of this slide is to outline the implements such as computer passwords, digital currencies, secure web browsing, electronic signatures, authentications, etc. Increase audience engagement and knowledge by dispensing information using Secure Your Digital Assets Understanding Applications And Use Cases Of Cryptography. This template helps you present information on six stages. You can also present information on Computer Passwords, Digital Currencies, Secure Web Browsing, Electronic Signatures, Authentication using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Secure Your Digital Assets Use Cases Of Crypto Wallets In Market
Secure Your Digital Assets Use Cases Of Crypto Wallets In MarketThis slide showcases the used cases for crypto wallets in market. The purpose of this slide is to outline uses such as boosting engagement, merchant payments, providing rewards, coupons, shared savings and pooling, investing, access to dApps, etc. Introducing Secure Your Digital Assets Use Cases Of Crypto Wallets In Market to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Merchant Payments, Boost Engagement And Personalization, Investment And Trading, Shared Savings And Pooling, using this template. Grab it now to reap its full benefits.
-
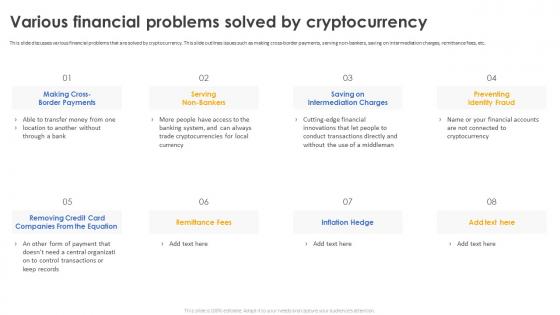 Secure Your Digital Assets Various Financial Problems Solved By Cryptocurrency
Secure Your Digital Assets Various Financial Problems Solved By CryptocurrencyThis slide discusses various financial problems that are solved by cryptocurrency. This slide outlines issues such as making cross-border payments, serving non-bankers, saving on intermediation charges, remittance fees, etc. Introducing Secure Your Digital Assets Various Financial Problems Solved By Cryptocurrency to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Saving On Intermediation Charges, Preventing Identity Fraud, Making Cross Border Payments, Serving Non Bankers, using this template. Grab it now to reap its full benefits.
-
 Secure Your Digital Assets Ways Cryptocurrency Can Alter The Global Economy
Secure Your Digital Assets Ways Cryptocurrency Can Alter The Global EconomyThis slide showcases the ways cryptocurrency can alter the global economy. The purpose of this slide is to highlight different ways of altering the global economy such as reducing inflation, giving financial stability, security, creativity, etc. Increase audience engagement and knowledge by dispensing information using Secure Your Digital Assets Ways Cryptocurrency Can Alter The Global Economy. This template helps you present information on seven stages. You can also present information on Reduces Inflation, Financial Stability, Potential To Replace Financial System, Cryptocurrencies Became using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
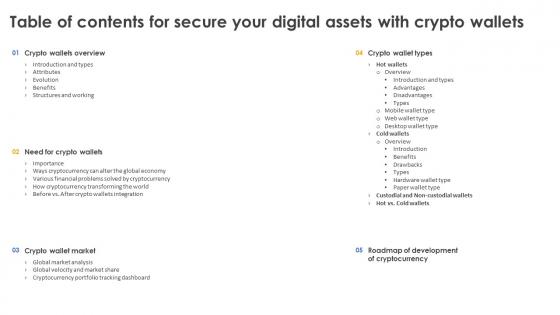 Table Of Contents For Secure Your Digital Assets With Crypto Wallets
Table Of Contents For Secure Your Digital Assets With Crypto WalletsIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Secure Your Digital Assets With Crypto Wallets. This template helps you present information on five stages. You can also present information on Roadmap Of Development Of Cryptocurrency, Crypto Wallet Market, Need For Crypto Wallets, Structures And Working using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Secure Your Digital Assets With Crypto Wallets For Table Of Content
Secure Your Digital Assets With Crypto Wallets For Table Of ContentDeliver an outstanding presentation on the topic using this Secure Your Digital Assets With Crypto Wallets For Table Of Content. Dispense information and present a thorough explanation of Ways Cryptocurrency Can Alter The Global, Various Financial Problems Solved, Cryptocurrency Transforming The World using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
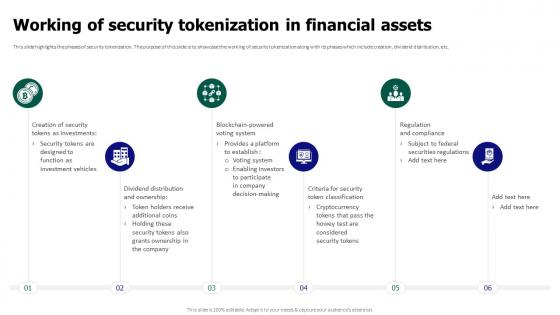 Tokenization For Improved Data Security Working Of Security Tokenization In Financial Assets
Tokenization For Improved Data Security Working Of Security Tokenization In Financial AssetsThis slide highlights the phases of security tokenization. The purpose of this slide is to showcase the working of security tokenization along with its phases which include creation, dividend distribution, etc. Introducing Tokenization For Improved Data Security Working Of Security Tokenization In Financial Assets to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Working Of Security Tokenization, Financial Assets, Dividend Distribution, Security Token Classification, using this template. Grab it now to reap its full benefits.
-
 Facility Security Icon For Asset Protection
Facility Security Icon For Asset ProtectionIntroducing our premium set of slides with name Facility Security Icon For Asset Protection. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Facility Security, Icon For Asset Protection. So download instantly and tailor it with your information.
-
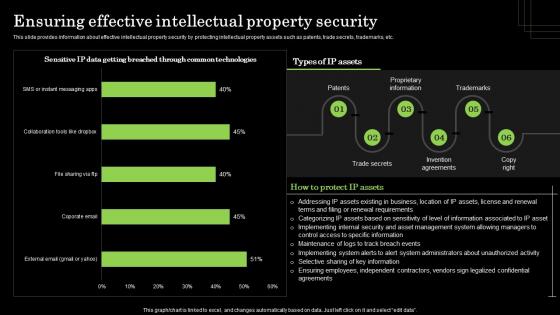 Ensuring Effective Intellectual Property Security Defense Plan To Protect Firm Assets
Ensuring Effective Intellectual Property Security Defense Plan To Protect Firm AssetsThis slide provides information about effective intellectual property security by protecting intellectual property assets such as patents, trade secrets, trademarks, etc. Present the topic in a bit more detail with this Ensuring Effective Intellectual Property Security Defense Plan To Protect Firm Assets. Use it as a tool for discussion and navigation on Proprietary Information, Trademarks, Invention Agreements. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
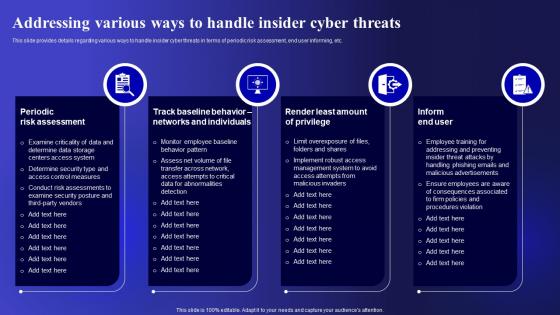 Addressing Various Ways To Handle Cyber Threats Management To Enable Digital Assets Security
Addressing Various Ways To Handle Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding various ways to handle insider cyber threats in terms of periodic risk assessment, end user informing, etc. Present the topic in a bit more detail with this Addressing Various Ways To Handle Cyber Threats Management To Enable Digital Assets Security. Use it as a tool for discussion and navigation on Periodic Risk Assessment, Individuals, Implement. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
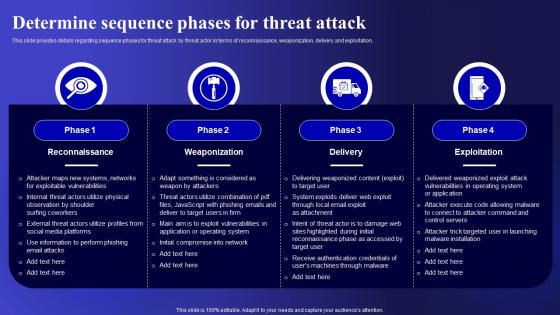 Determine Sequence Phases For Cyber Threats Management To Enable Digital Assets Security
Determine Sequence Phases For Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding sequence phases for threat attack by threat actor in terms of reconnaissance, weaponization, delivery and exploitation. Deliver an outstanding presentation on the topic using this Determine Sequence Phases For Cyber Threats Management To Enable Digital Assets Security. Dispense information and present a thorough explanation of Reconnaissance, Weaponization, Exploitation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Checklist For Effectively Managing Asset Security Risk Based Methodology To Cyber
Checklist For Effectively Managing Asset Security Risk Based Methodology To CyberFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them.Increase audience engagement and knowledge by dispensing information using Checklist For Effectively Managing Asset Security Risk Based Methodology To Cyber This template helps you present information on one stage. You can also present information on System Monitoring, Data Backup, Security Patches using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Checklist For Effectively Managing Asset Security Introducing A Risk Based Approach
Checklist For Effectively Managing Asset Security Introducing A Risk Based ApproachFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them.Introducing Checklist For Effectively Managing Asset Security Introducing A Risk Based Approach to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on System Monitoring, Virus Scanning, System Monitoring using this template. Grab it now to reap its full benefits.
-
 Criticality Assessment Of Identified Assets Introducing A Risk Based Approach To Cyber Security
Criticality Assessment Of Identified Assets Introducing A Risk Based Approach To Cyber SecurityFollowing slide demonstrates the asset criticality of identified system components. It covers details such as major components used along with criticality rating and failure cost.Deliver an outstanding presentation on the topic using this Criticality Assessment Of Identified Assets Introducing A Risk Based Approach To Cyber Security Dispense information and present a thorough explanation of Infrastructure Hardware, Routers And Switches, Server Computers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
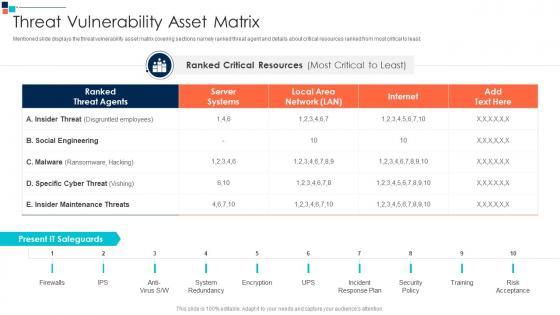 Threat Vulnerability Asset Matrix Introducing A Risk Based Approach To Cyber Security
Threat Vulnerability Asset Matrix Introducing A Risk Based Approach To Cyber SecurityMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least.Present the topic in a bit more detail with this Threat Vulnerability Asset Matrix Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on System Redundancy, Incident Response Plan, Security Policy This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Line Credit Secured Assets Ppt Powerpoint Presentation Layouts Graphics Cpb
Line Credit Secured Assets Ppt Powerpoint Presentation Layouts Graphics CpbPresenting Line Credit Secured Assets Ppt Powerpoint Presentation Layouts Graphics Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Line Credit Secured Assets. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Addressing Asset Security Categorization Vulnerability Administration At Workplace
Addressing Asset Security Categorization Vulnerability Administration At WorkplaceThis slide provides details regarding asset security categorization on certain parameters such as ownership, location, confidentiality, integrity and availability. Present the topic in a bit more detail with this Addressing Asset Security Categorization Vulnerability Administration At Workplace. Use it as a tool for discussion and navigation on Location, Availability, Categorization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
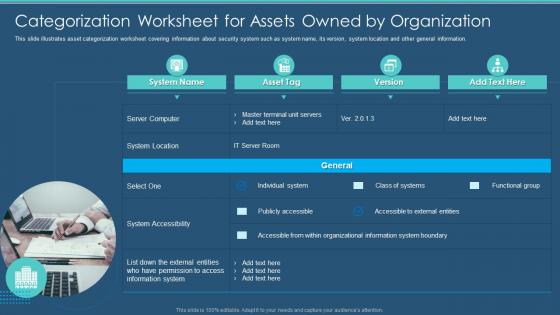 Information Security Program Categorization Worksheet For Assets Owned Organization
Information Security Program Categorization Worksheet For Assets Owned OrganizationThis slide illustrates asset categorization worksheet covering information about security system such as system name, its version, system location and other general information. Present the topic in a bit more detail with this Information Security Program Categorization Worksheet For Assets Owned Organization. Use it as a tool for discussion and navigation on Categorization, Worksheet, Organization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Security Program Cybersecurity Checklist Effectively Managing Asset Security
Information Security Program Cybersecurity Checklist Effectively Managing Asset SecurityFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them. Present the topic in a bit more detail with this Information Security Program Cybersecurity Checklist Effectively Managing Asset Security. Use it as a tool for discussion and navigation on Checklist For Effectively Managing Asset Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Information Security Program Cybersecurity Management Threat Vulnerability Asset Matrix
Information Security Program Cybersecurity Management Threat Vulnerability Asset MatrixMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least. Deliver an outstanding presentation on the topic using this Information Security Program Cybersecurity Management Threat Vulnerability Asset Matrix. Dispense information and present a thorough explanation of Threat Vulnerability Asset Matrix using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
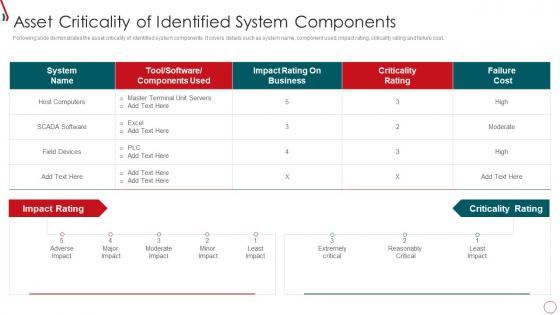 Risk Management Framework For Information Security Asset Criticality Of Identified System
Risk Management Framework For Information Security Asset Criticality Of Identified SystemFollowing slide demonstrates the asset criticality of identified system components. It covers details such as system name, component used, impact rating, criticality rating and failure cost. Present the topic in a bit more detail with this Risk Management Framework For Information Security Asset Criticality Of Identified System. Use it as a tool for discussion and navigation on Host Computers, Impact Rating, Criticality Rating, Failure Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
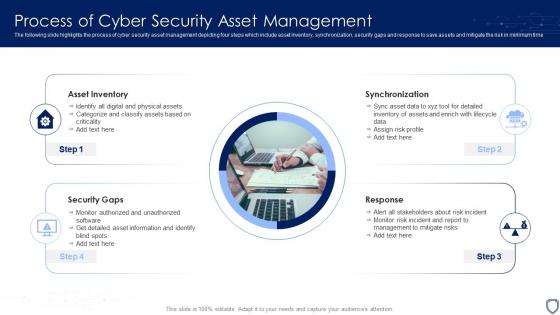 Process Of Cyber Security Asset Management
Process Of Cyber Security Asset ManagementThe following slide highlights the process of cyber security asset management depicting four steps which include asset inventory, synchronization, security gaps and response to save assets and mitigate the risk in minimum time. Introducing our premium set of slides with name Process Of Cyber Security Asset Management. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Asset Inventory, Synchronization, Response, Security Gaps. So download instantly and tailor it with your information.
-
 Roadmap Of Cyber Security Asset Assessment And Security Policy Development
Roadmap Of Cyber Security Asset Assessment And Security Policy DevelopmentThe following slide highlights the roadmap of cyber security asset assessment and security policy development for organisation to draft system security policy which describes assessment, build, select, deployment, awareness and audit. Presenting our set of slides with name Roadmap Of Cyber Security Asset Assessment And Security Policy Development. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Audit, Awareness, Assessment, Build, Deployment.
-
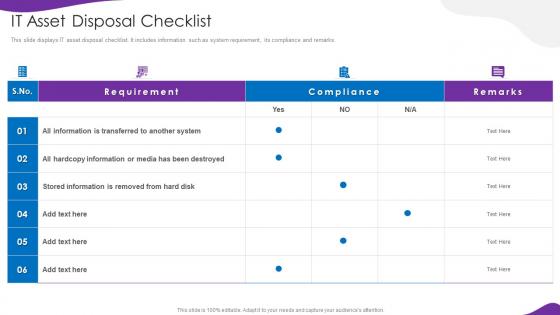 Information Security And Iso 27001 It Asset Disposal Checklist
Information Security And Iso 27001 It Asset Disposal ChecklistThis slide displays IT asset disposal checklist. It includes information such as system requirement, its compliance and remarks. Deliver an outstanding presentation on the topic using this Information Security And Iso 27001 It Asset Disposal Checklist. Dispense information and present a thorough explanation of It Asset Disposal Checklist using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
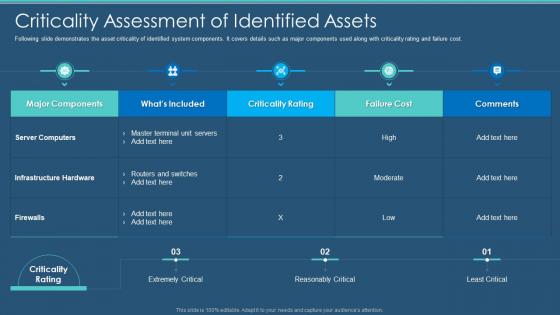 Cybersecurity Criticality Assessment Of Identified Assets Information Security Program
Cybersecurity Criticality Assessment Of Identified Assets Information Security ProgramFollowing slide demonstrates the asset criticality of identified system components. It covers details such as major components used along with criticality rating and failure cost. Present the topic in a bit more detail with this Cybersecurity Criticality Assessment Of Identified Assets Information Security Program. Use it as a tool for discussion and navigation on Criticality Assessment Of Identified Assets. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Marketable Securities Assets Liabilities Ppt Powerpoint Presentation Styles Graphic Images Cpb
Marketable Securities Assets Liabilities Ppt Powerpoint Presentation Styles Graphic Images CpbPresenting Marketable Securities Assets Liabilities Ppt Powerpoint Presentation Styles Graphic Images Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase eight stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Marketable Securities Assets Liabilities. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
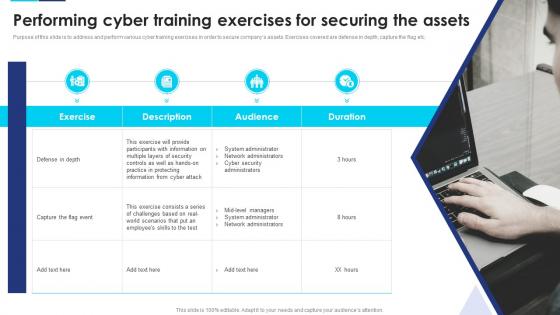 Incident Response Playbook Performing Cyber Training Exercises For Securing The Assets
Incident Response Playbook Performing Cyber Training Exercises For Securing The AssetsPurpose of this slide is to address and perform various cyber training exercises in order to secure companys assets. Exercises covered are defense in depth, capture the flag etc. Increase audience engagement and knowledge by dispensing information using Incident Response Playbook Performing Cyber Training Exercises For Securing The Assets. This template helps you present information on four stages. You can also present information on Network Administrators, Security Controls, Mid Level Managers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
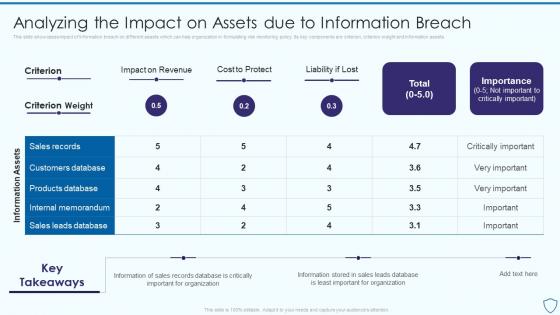 Analyzing The Impact On Assets Due To Risk Assessment And Management Plan For Information Security
Analyzing The Impact On Assets Due To Risk Assessment And Management Plan For Information SecurityThis slide showcases impact of information breach on different assets which can help organization in formulating risk monitoring policy. Its key components are criterion, criterion weight and information assets Deliver an outstanding presentation on the topic using this Analyzing The Impact On Assets Due To Risk Assessment And Management Plan For Information Security. Dispense information and present a thorough explanation of Revenue, Information, Importance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
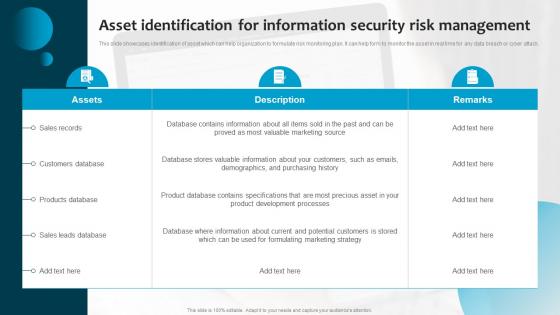
 Asset Identification For Information Risk Assessment And Management Plan For Information Security
Asset Identification For Information Risk Assessment And Management Plan For Information SecurityThis slide showcases identification of asset which can help organization to formulate risk monitoring plan. It can help to monitor the asset in real time for any data breach or cyber attack Deliver an outstanding presentation on the topic using this Asset Identification For Information Risk Assessment And Management Plan For Information Security. Dispense information and present a thorough explanation of Sales Records, Customers Database, Products Database using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Investment Securities Current Assets In Powerpoint And Google Slides Cpb
Investment Securities Current Assets In Powerpoint And Google Slides CpbPresenting our Investment Securities Current Assets In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Investment Securities Current Assets. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
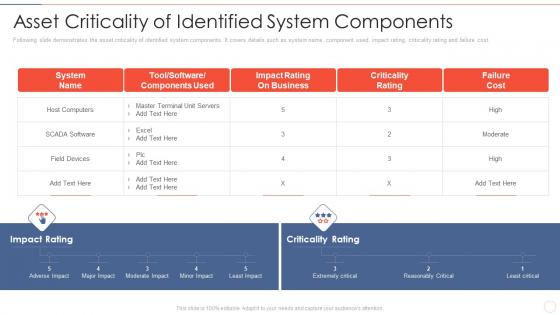 Effective information security asset criticality of identified system components
Effective information security asset criticality of identified system componentsFollowing slide demonstrates the asset criticality of identified system components. It covers details such as system name, component used, impact rating, criticality rating and failure cost. Deliver an outstanding presentation on the topic using this Effective Information Security Asset Criticality Of Identified System Components. Dispense information and present a thorough explanation of Host Computers, Impact Rating, Business, Criticality Rating using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Addressing asset security managing critical threat vulnerabilities and security threats
Addressing asset security managing critical threat vulnerabilities and security threatsThis slide provides details regarding asset security categorization on certain parameters such as ownership, location, confidentiality, integrity and availability. Introducing Addressing Asset Security Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Ownership, Location, Confidentiality, Integrity, using this template. Grab it now to reap its full benefits.
-
 Addressing asset security categorization corporate security management
Addressing asset security categorization corporate security managementThis slide provides details regarding asset security categorization on certain parameters such as ownership, location, confidentiality, integrity and availability. Present the topic in a bit more detail with this Addressing Asset Security Categorization Corporate Security Management. Use it as a tool for discussion and navigation on Ownership, Location, Confidentiality, Integrity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Asset management information security ppt powerpoint presentation inspiration outfit cpb
Asset management information security ppt powerpoint presentation inspiration outfit cpbPresenting our Asset Management Information Security Ppt Powerpoint Presentation Inspiration Outfit Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Asset Management Information Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
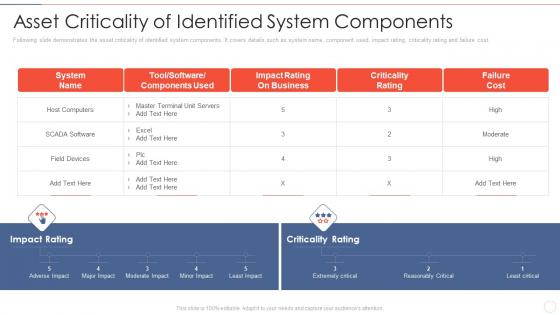 Asset components effective information security risk management process
Asset components effective information security risk management processFollowing slide demonstrates the asset criticality of identified system components. It covers details such as system name, component used, impact rating, criticality rating and failure cost.Present the topic in a bit more detail with this Asset Components Effective Information Security Risk Management Process. Use it as a tool for discussion and navigation on Impact Rating On Business, Criticality Rating, Failure Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
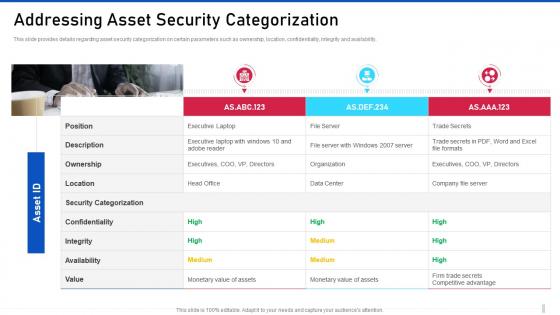 Threat management for organization critical addressing asset security categorization
Threat management for organization critical addressing asset security categorizationThis slide provides details regarding asset security categorization on certain parameters such as ownership, location, confidentiality, integrity and availability. Present the topic in a bit more detail with this Threat Management For Organization Critical Addressing Asset Security Categorization. Use it as a tool for discussion and navigation on Security Categorization, Confidentiality, Executive Laptop. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber security risk management addressing asset security categorization
Cyber security risk management addressing asset security categorizationThis slide provides details regarding asset security categorization on certain parameters such as ownership, location, confidentiality, integrity and availability. Introducing Cyber Security Risk Management Addressing Asset Security Categorization to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Position, Ownership, Location, Security Categorization, Integrity, Confidentiality, Availability, Value , using this template. Grab it now to reap its full benefits.
-
 Introducing security at workplace to ensure assets safety building organizational security strategy plan
Introducing security at workplace to ensure assets safety building organizational security strategy planThis slide provides information about introducing security at workplace in order to ensure assets safety and details regarding security mission statement and objectives. Introducing Introducing Security At Workplace To Ensure Assets Safety Building Organizational Security Strategy Plan to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Information, Organizational, Strategy, using this template. Grab it now to reap its full benefits.
-
 Cybersecurity and digital business risk management checklist for effectively managing asset security
Cybersecurity and digital business risk management checklist for effectively managing asset securityFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them. Present the topic in a bit more detail with this Cybersecurity And Digital Business Risk Management Checklist For Effectively Managing Asset Security. Use it as a tool for discussion and navigation on System Monitoring, Data Backup, Security Patches . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
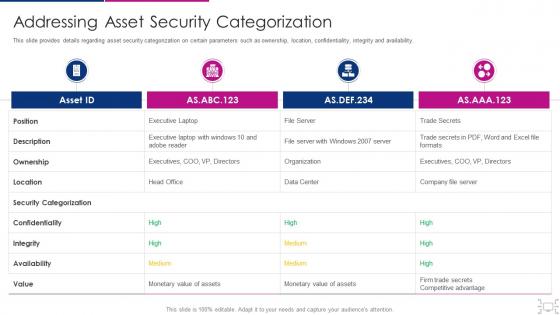 Cyber threat management workplace addressing asset security categorization
Cyber threat management workplace addressing asset security categorizationThis slide provides details regarding comparative assessment of different threat agents on various parameters such as data loss impact, skills required to handle threat, etc. Deliver an outstanding presentation on the topic using this Cyber Threat Management Workplace Addressing Asset Security Categorization. Dispense information and present a thorough explanation of Position, Ownership, Location, Security Categorization, Confidentiality using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
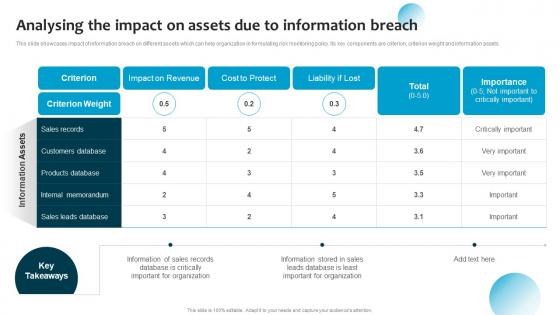 Analysing The Impact On Assets Information Breach Information System Security And Risk Administration
Analysing The Impact On Assets Information Breach Information System Security And Risk AdministrationThis slide showcases impact of information breach on different assets which can help organization in formulating risk monitoring policy. Its key components are criterion, criterion weight and information assets. Deliver an outstanding presentation on the topic using this Analysing The Impact On Assets Information Breach Information System Security And Risk Administration. Dispense information and present a thorough explanation of Cost To Protect, Sales Records, Products Database using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
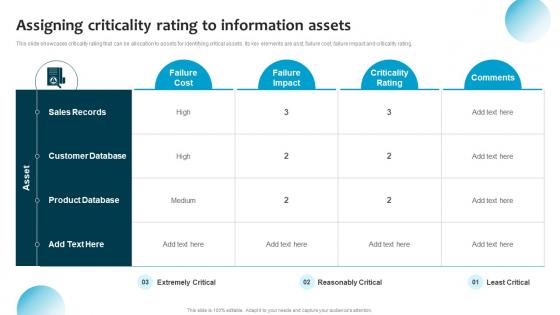 Assigning Criticality Rating To Assets Information System Security And Risk Administration Plan
Assigning Criticality Rating To Assets Information System Security And Risk Administration PlanThis slide showcases criticality rating that can be allocation to assets for identifying critical assets. Its key elements are asst, failure cost, failure impact and criticality rating. Deliver an outstanding presentation on the topic using this Assigning Criticality Rating To Assets Information System Security And Risk Administration Plan. Dispense information and present a thorough explanation of Failure Cost, Criticality Rating, Product Database using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 C12 Asset Identification For Information Security Risk Management Ppt Powerpoint Presentation File Grid
C12 Asset Identification For Information Security Risk Management Ppt Powerpoint Presentation File GridThis slide showcases identification of asset which can help organization to formulate risk monitoring plan. It can help form to monitor the asset in real time for any data breach or cyber attack. Deliver an outstanding presentation on the topic using this C12 Asset Identification For Information Security Risk Management Ppt Powerpoint Presentation File Grid. Dispense information and present a thorough explanation of Customers Database, Sales Records, Products Database using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Digital Asset Security In Powerpoint And Google Slides Cpb
Digital Asset Security In Powerpoint And Google Slides CpbPresenting Digital Asset Security In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Digital Asset Security. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Security Assets In Powerpoint And Google Slides Cpb
Security Assets In Powerpoint And Google Slides CpbPresenting our Security Assets In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Security Assets This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Asset Identification For Information Security Cybersecurity Risk Analysis And Management Plan
Asset Identification For Information Security Cybersecurity Risk Analysis And Management PlanThis slide showcases identification of asset which can help organization to formulate risk monitoring plan. It can help form to monitor the asset in real time for any data breach or cyber attack Introducing Asset Identification For Information Security Cybersecurity Risk Analysis And Management Plan to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Identification, Information, Management, using this template. Grab it now to reap its full benefits.
-
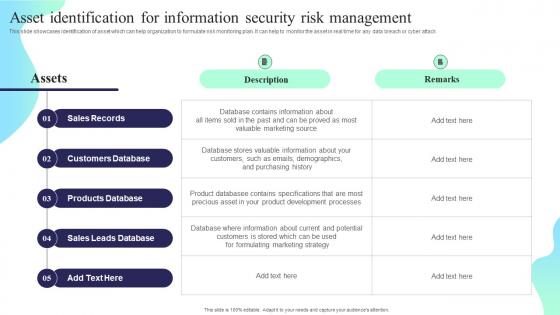 Asset Identification For Information Security Risk Management Formulating Cybersecurity Plan
Asset Identification For Information Security Risk Management Formulating Cybersecurity PlanThis slide showcases identification of asset which can help organization to formulate risk monitoring plan. It can help to monitor the asset in real time for any data breach or cyber attack. Deliver an outstanding presentation on the topic using this Asset Identification For Information Security Risk Management Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Sales Records, Customers Database, Products Database using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
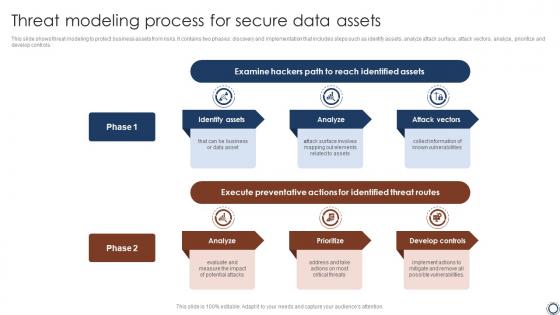 Threat Modeling Process For Secure Data Assets
Threat Modeling Process For Secure Data AssetsThis slide shows threat modeling to protect business assets from risks. It contains two phases discovery and implementation that includes steps such as identify assets, analyze attack surface, attack vectors, analyze, prioritize and develop controls. Introducing our premium set of slides with name Threat Modeling Process For Secure Data Assets. Ellicudate the two stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Hackers Path, Identified Assets, Threat Routes. So download instantly and tailor it with your information.
-
 Performing Cyber Training Exercises For Securing The Assets Cybersecurity Incident And Vulnerability
Performing Cyber Training Exercises For Securing The Assets Cybersecurity Incident And VulnerabilityPurpose of this slide is to address and perform various cyber training exercises in order to secure companys assets. Exercises covered are defense in depth, capture the flag etc. Deliver an outstanding presentation on the topic using this Performing Cyber Training Exercises For Securing The Assets Cybersecurity Incident And Vulnerability. Dispense information and present a thorough explanation of Capture The Flag Event, Training, System Administrator using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.



