Powerpoint Templates and Google slides for Attack
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
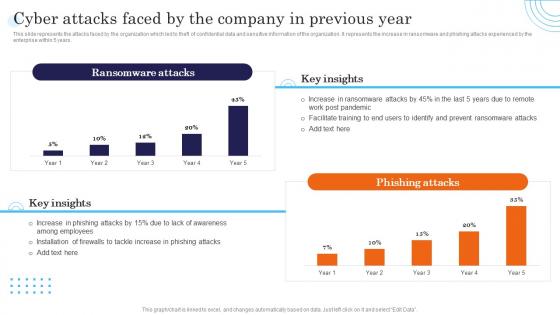 Cyber Attacks Faced By The Company In Previous Year Incident Response Strategies Deployment
Cyber Attacks Faced By The Company In Previous Year Incident Response Strategies DeploymentThis slide represents the attacks faced by the organization which led to theft of confidential data and sensitive information of the organization. It represents the increase in ransomware and phishing attacks experienced by the enterprise within 5 years. Deliver an outstanding presentation on the topic using this Cyber Attacks Faced By The Company In Previous Year Incident Response Strategies Deployment. Dispense information and present a thorough explanation of Ransomware, Phishing, Cyber using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
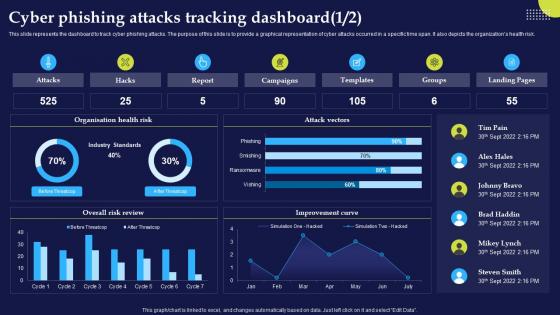 Cyber Phishing Attacks Tracking Dashboard Phishing Attacks And Strategies
Cyber Phishing Attacks Tracking Dashboard Phishing Attacks And StrategiesThis slide represents the dashboard to track cyber phishing attacks. The purpose of this slide is to provide a graphical representation of cyber attacks occurred in a specific time span. It also depicts the organizations health risk.Deliver an outstanding presentation on the topic using this Cyber Phishing Attacks Tracking Dashboard Phishing Attacks And Strategies. Dispense information and present a thorough explanation of Cyber Phishing Attacks, Tracking Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
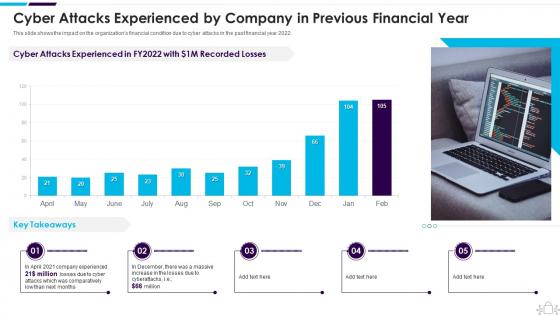 Cyber Attacks Experienced By Company In Previous Information Technology Security
Cyber Attacks Experienced By Company In Previous Information Technology SecurityThis slide shows the impact on the organizations financial condition due to cyber attacks in the past financial year 2022. Present the topic in a bit more detail with this Cyber Attacks Experienced By Company In Previous Information Technology Security. Use it as a tool for discussion and navigation on Experienced, Previous, Financial. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
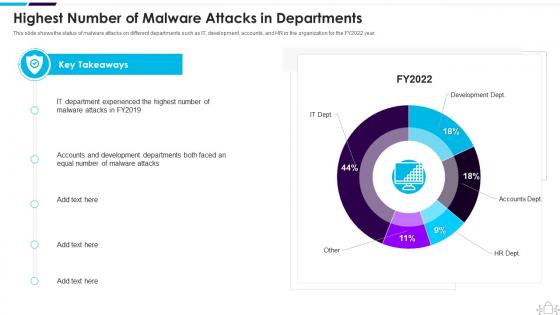 Information Technology Security Highest Number Of Malware Attacks In Departments
Information Technology Security Highest Number Of Malware Attacks In DepartmentsThis slide shows the status of malware attacks on different departments such as IT, development, accounts, and HR in the organization for the FY2022 year. Present the topic in a bit more detail with this Information Technology Security Highest Number Of Malware Attacks In Departments. Use it as a tool for discussion and navigation on Department, Experienced, Malware. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
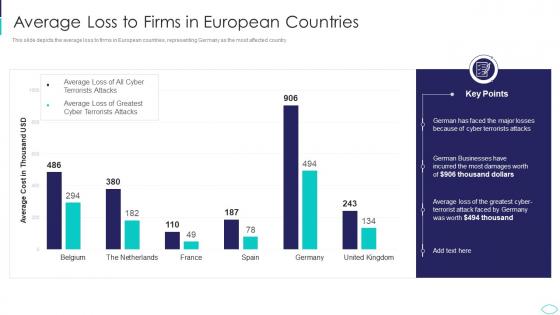 Average Loss To Firms In European Countries Cyber Terrorism Attacks
Average Loss To Firms In European Countries Cyber Terrorism AttacksThis slide depicts the average loss to firms in European countries, representing Germany as the most affected country. Present the topic in a bit more detail with this Average Loss To Firms In European Countries Cyber Terrorism Attacks. Use it as a tool for discussion and navigation on Average Loss To Firms In European Countries. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
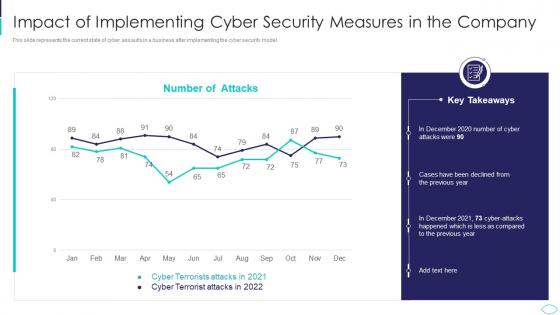 Cyber Terrorism Attacks Impact Of Implementing Cyber Security
Cyber Terrorism Attacks Impact Of Implementing Cyber SecurityThis slide represents the current state of cyber assaults in a business after implementing the cyber security model. Deliver an outstanding presentation on the topic using this Cyber Terrorism Attacks Impact Of Implementing Cyber Security. Dispense information and present a thorough explanation of Impact Of Implementing Cyber Security Measures In The Company using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Terrorism Faced By Companies In US Cyber Terrorism Attacks
Cyber Terrorism Faced By Companies In US Cyber Terrorism AttacksThis slide depicts the cyber terrorism attacks faced by the companies in the US, and the graph represents the financial losses in the last five years. Present the topic in a bit more detail with this Cyber Terrorism Faced By Companies In US Cyber Terrorism Attacks. Use it as a tool for discussion and navigation on Cyber Terrorism Faced By Companies In Us. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
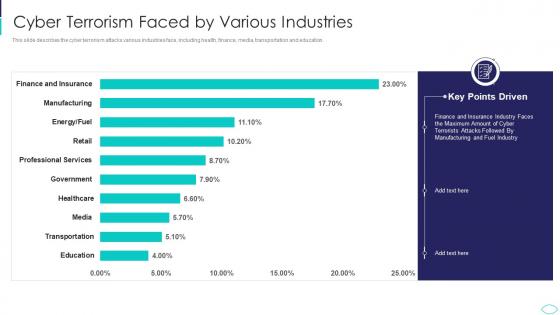 Cyber Terrorism Faced By Various Industries Cyber Terrorism Attacks
Cyber Terrorism Faced By Various Industries Cyber Terrorism AttacksThis slide describes the cyber terrorism attacks various industries face, including health, finance, media, transportation and education. Deliver an outstanding presentation on the topic using this Cyber Terrorism Faced By Various Industries Cyber Terrorism Attacks. Dispense information and present a thorough explanation of Cyber Terrorism Faced By Various Industries using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Terrorist Experienced By Company Cyber Terrorism Attacks
Cyber Terrorist Experienced By Company Cyber Terrorism AttacksThis slide describes the number of cyber terrorist attacks experienced by the company in the previous financial year 2022. Present the topic in a bit more detail with this Cyber Terrorist Experienced By Company Cyber Terrorism Attacks. Use it as a tool for discussion and navigation on Cyber Terrorist Experienced By Company In Previous Financial Year. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
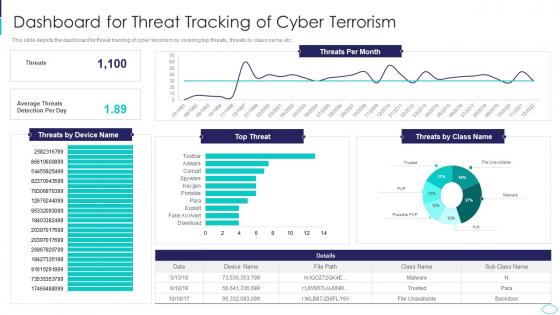 Dashboard For Threat Tracking Cyber Terrorism Attacks
Dashboard For Threat Tracking Cyber Terrorism AttacksThis slide depicts the dashboard for threat tracking of cyber terrorism by covering top threats, threats by class name, etc. Deliver an outstanding presentation on the topic using this Dashboard For Threat Tracking Cyber Terrorism Attacks. Dispense information and present a thorough explanation of Dashboard For Threat Tracking Of Cyber Terrorism using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
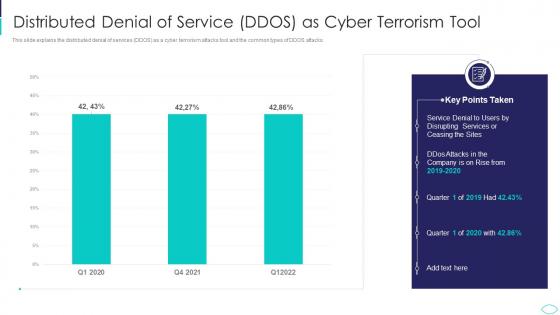 Distributed Denial Of Service DDOS Cyber Terrorism Attacks
Distributed Denial Of Service DDOS Cyber Terrorism AttacksThis slide explains the distributed denial of services DDOS as a cyber terrorism attacks tool and the common types of DDOS attacks. Present the topic in a bit more detail with this Distributed Denial Of Service DDOS Cyber Terrorism Attacks. Use it as a tool for discussion and navigation on Distributed Denial Of Service Ddos As Cyber Terrorism Tool. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Implement Strong IT Guidelines In The Company Cyber Terrorism Attacks
Implement Strong IT Guidelines In The Company Cyber Terrorism AttacksThis slide depicts the strong IT guidelines which should be implemented in the company, such as security software, backups, fraud detection. Present the topic in a bit more detail with this Implement Strong IT Guidelines In The Company Cyber Terrorism Attacks. Use it as a tool for discussion and navigation on Implement Strong It Guidelines In The Company. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
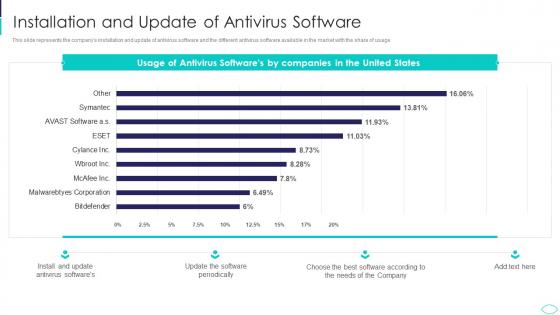 Installation And Update Of Antivirus Software Cyber Terrorism Attacks
Installation And Update Of Antivirus Software Cyber Terrorism AttacksThis slide represents the companys installation and update of antivirus software and the different antivirus software available in the market with the share of usage. Deliver an outstanding presentation on the topic using this Installation And Update Of Antivirus Software Cyber Terrorism Attacks. Dispense information and present a thorough explanation of Installation And Update Of Antivirus Software using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
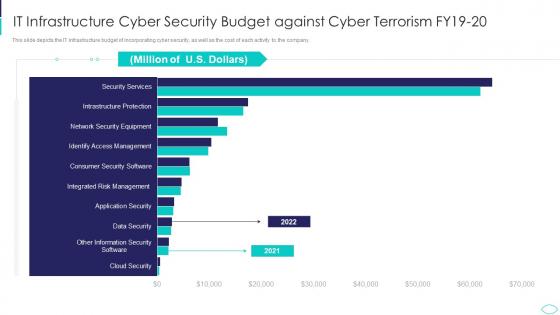 IT Infrastructure Cyber Security Budget Against Cyber Terrorism Attacks
IT Infrastructure Cyber Security Budget Against Cyber Terrorism AttacksThis slide depicts the IT infrastructure budget of incorporating cyber security, as well as the cost of each activity to the company. Present the topic in a bit more detail with this IT Infrastructure Cyber Security Budget Against Cyber Terrorism Attacks. Use it as a tool for discussion and navigation on It Infrastructure Cyber Security Budget Against Cyber Terrorism Fy19 20. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
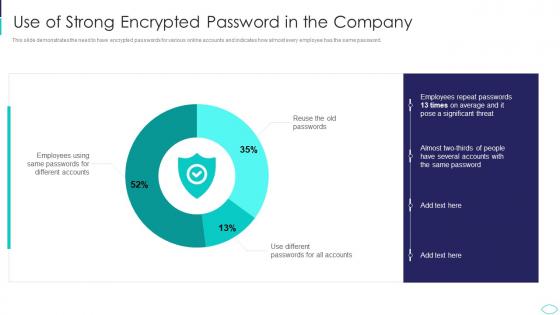 Use Of Strong Encrypted Password In The Company Cyber Terrorism Attacks
Use Of Strong Encrypted Password In The Company Cyber Terrorism AttacksThis slide demonstrates the need to have encrypted passwords for various online accounts and indicates how almost every employee has the same password. Present the topic in a bit more detail with this Use Of Strong Encrypted Password In The Company Cyber Terrorism Attacks. Use it as a tool for discussion and navigation on Use Of Strong Encrypted Password In The Company. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
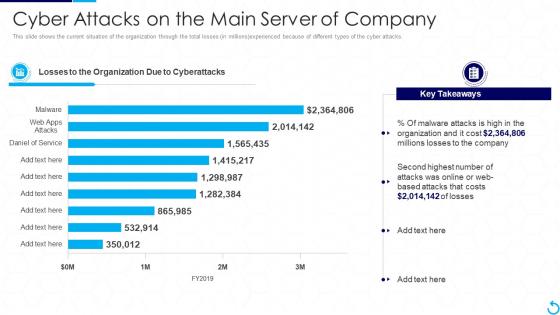 Reverse Proxy It Cyber Attacks On The Main Server Of Company
Reverse Proxy It Cyber Attacks On The Main Server Of CompanyThis slide shows the current situation of the organization through the total losses in millions experienced because of different types of the cyber attacks. Deliver an outstanding presentation on the topic using this Reverse Proxy It Cyber Attacks On The Main Server Of Company. Dispense information and present a thorough explanation of Cyber Attacks On The Main Server Of Company using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
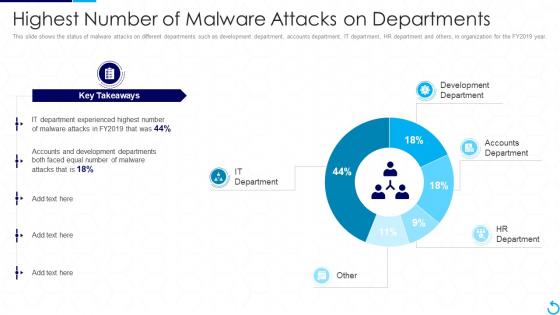 Reverse Proxy It Highest Number Of Malware Attacks On Departments
Reverse Proxy It Highest Number Of Malware Attacks On DepartmentsThis slide shows the status of malware attacks on different departments such as development department, accounts department, IT department, HR department and others, in organization for the FY2019 year. Present the topic in a bit more detail with this Reverse Proxy It Highest Number Of Malware Attacks On Departments. Use it as a tool for discussion and navigation on Departments, Development, Experienced. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
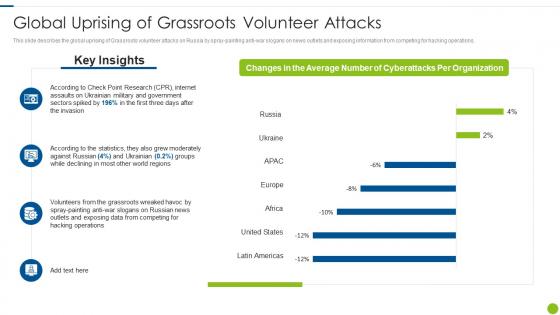 Cyber Attacks On Ukraine Global Uprising Of Grassroots Volunteer Attacks
Cyber Attacks On Ukraine Global Uprising Of Grassroots Volunteer AttacksThis slide describes the global uprising of Grassroots volunteer attacks on Russia by spray painting anti war slogans on news outlets and exposing information from competing for hacking operations. Deliver an outstanding presentation on the topic using this Cyber Attacks On Ukraine Global Uprising Of Grassroots Volunteer Attacks. Dispense information and present a thorough explanation of Global Uprising Of Grassroots Volunteer Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
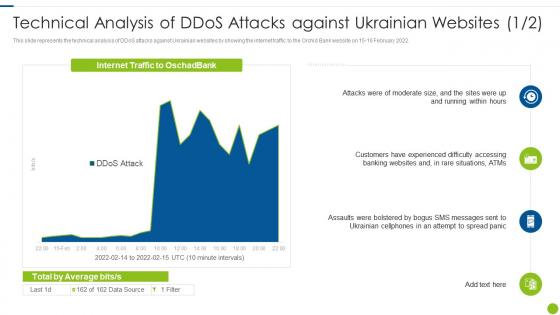 Cyber Attacks On Ukraine Technical Analysis Of DDOS Attacks Against
Cyber Attacks On Ukraine Technical Analysis Of DDOS Attacks AgainstThis slide represents the technical analysis of DDoS attacks against Ukrainian websites by showing the internet traffic to the Orchid Bank website on 15 16 February 2022. Present the topic in a bit more detail with this Cyber Attacks On Ukraine Technical Analysis Of DDOS Attacks Against. Use it as a tool for discussion and navigation on Technical Analysis Of Ddos Attacks Against Ukrainian Websites. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
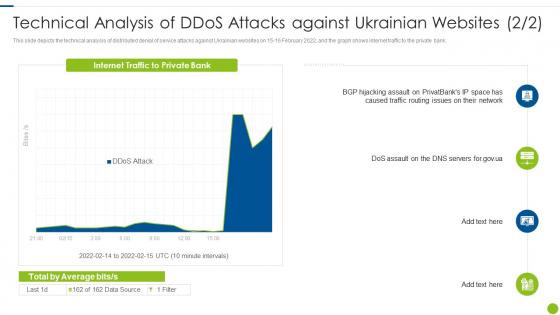 Technical Analysis Of Ddos Attacks Against Ukrainian Cyber Attacks On Ukraine
Technical Analysis Of Ddos Attacks Against Ukrainian Cyber Attacks On UkraineThis slide depicts the technical analysis of distributed denial of service attacks against Ukrainian websites on 15 16 February 2022, and the graph shows internet traffic to the private bank. Present the topic in a bit more detail with this Technical Analysis Of Ddos Attacks Against Ukrainian Cyber Attacks On Ukraine. Use it as a tool for discussion and navigation on Technical Analysis Of Ddos Attacks Against Ukrainian Websites. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
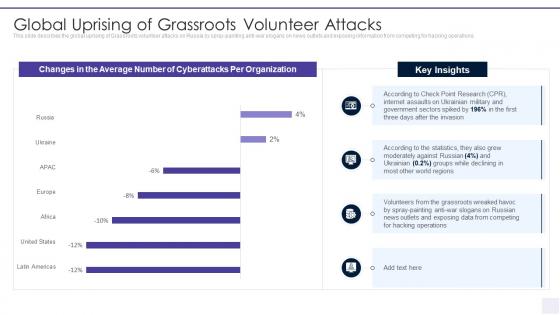 Wiper Malware Attack Global Uprising Of Grassroots Volunteer Attacks
Wiper Malware Attack Global Uprising Of Grassroots Volunteer AttacksThis slide describes the global uprising of Grassroots volunteer attacks on Russia by spray painting anti war slogans on news outlets and exposing information from competing for hacking operations. Present the topic in a bit more detail with this Wiper Malware Attack Global Uprising Of Grassroots Volunteer Attacks. Use it as a tool for discussion and navigation on Global Uprising Of Grassroots Volunteer Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
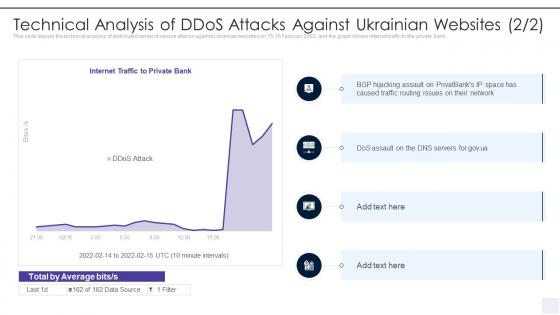 Wiper Malware Attack Technical Analysis Of DDOS Attacks Against
Wiper Malware Attack Technical Analysis Of DDOS Attacks AgainstThis slide depicts the technical analysis of distributed denial of service attacks against Ukrainian websites on 15 16 February 2022, and the graph shows internet traffic to the private bank. Deliver an outstanding presentation on the topic using this Wiper Malware Attack Technical Analysis Of DDOS Attacks Against. Dispense information and present a thorough explanation of Technical Analysis Of Ddos Attacks Against Ukrainian Websites using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
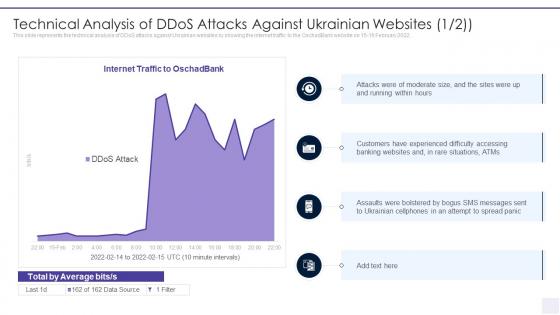 Technical Analysis Of Ddos Attacks Against Ukrainian Wiper Malware Attack
Technical Analysis Of Ddos Attacks Against Ukrainian Wiper Malware AttackThis slide represents the technical analysis of DDoS attacks against Ukrainian websites by showing the internet traffic to the OschadBank website on 15 16 February 2022. Present the topic in a bit more detail with this Technical Analysis Of Ddos Attacks Against Ukrainian Wiper Malware Attack. Use it as a tool for discussion and navigation on Technical Analysis Of Ddos Attacks Against Ukrainian Websites. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
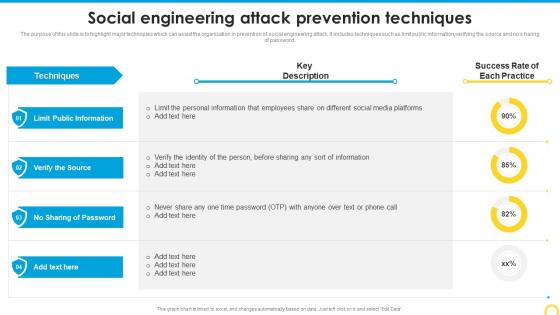 Social Engineering Attack Prevention Techniques Building A Security Awareness Program
Social Engineering Attack Prevention Techniques Building A Security Awareness ProgramThe purpose of this slide is to highlight major techniques which can assist the organization in prevention of social engineering attack. It includes techniques such as limit public information, verifying the source and no s haring of password. Deliver an outstanding presentation on the topic using this Social Engineering Attack Prevention Techniques Building A Security Awareness Program. Dispense information and present a thorough explanation of Public Information, Prevention Techniques, Social Engineering Attack using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
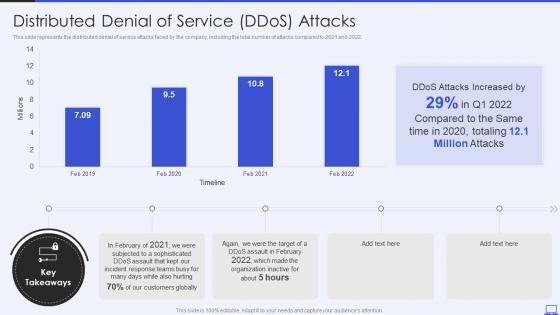 Security Hacker Distributed Denial Of Service Ddos Attacks Ppt Powerpoint Presentation Visual
Security Hacker Distributed Denial Of Service Ddos Attacks Ppt Powerpoint Presentation VisualThis slide represents the distributed denial of service attacks faced by the company, including the total number of attacks compared to 2021 and 2022. Deliver an outstanding presentation on the topic using this Security Hacker Distributed Denial Of Service Ddos Attacks Ppt Powerpoint Presentation Visual. Dispense information and present a thorough explanation of Distributed Denial Of Service, Timeline using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security Hacker Loss Due To Different Cyber Attacks Ppt Powerpoint Presentation Slides
Security Hacker Loss Due To Different Cyber Attacks Ppt Powerpoint Presentation SlidesThis slide represents the different types of cyber attacks throughout the year, including the percentage of total loss caused by these attacks. Present the topic in a bit more detail with this Security Hacker Loss Due To Different Cyber Attacks Ppt Powerpoint Presentation Slides. Use it as a tool for discussion and navigation on Different Cyber Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
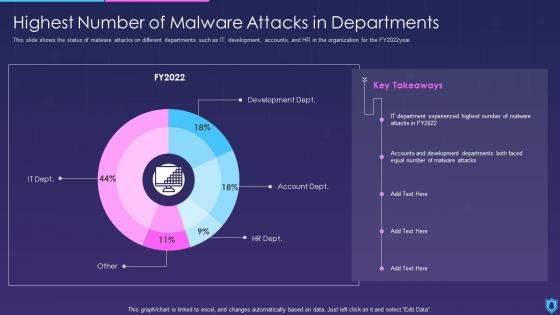 Information Security Highest Number Of Malware Attacks In Departments
Information Security Highest Number Of Malware Attacks In DepartmentsThis slide shows the status of malware attacks on different departments such as IT, development, accounts, and HR in the organization for the FY2022year. Present the topic in a bit more detail with this Information Security Highest Number Of Malware Attacks In Departments. Use it as a tool for discussion and navigation on Departments, Malware, Development. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
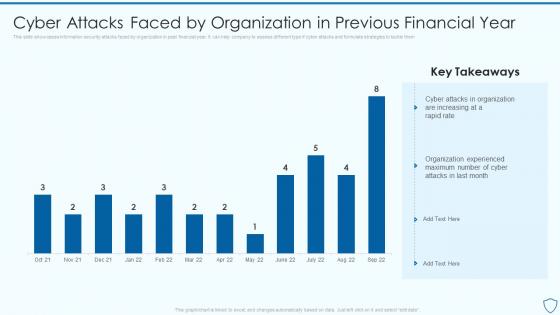 Cyber Attacks Faced By Organization In Risk Assessment And Management Plan For Information Security
Cyber Attacks Faced By Organization In Risk Assessment And Management Plan For Information SecurityThis slide showcases information security attacks faced by organization in past financial year. It can help company to assess different type if cyber attacks and formulate strategies to tackle them Present the topic in a bit more detail with this Cyber Attacks Faced By Organization In Risk Assessment And Management Plan For Information Security. Use it as a tool for discussion and navigation on Experienced, Organization, Financial. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
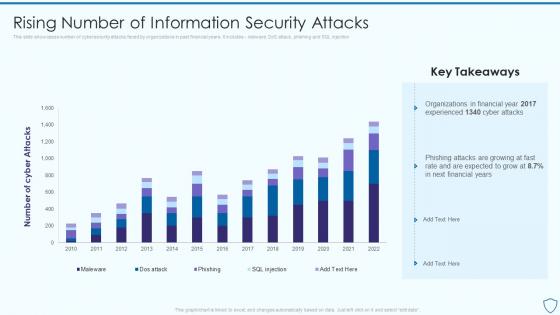 Rising Number Of Information Security Attacks Risk Assessment And Management Plan For Information Security
Rising Number Of Information Security Attacks Risk Assessment And Management Plan For Information SecurityThis slide showcases number of cybersecurity attacks faced by organizations in past financial years. It includes malware, DoS attack, phishing and SQL injection Present the topic in a bit more detail with this Rising Number Of Information Security Attacks Risk Assessment And Management Plan For Information Security. Use it as a tool for discussion and navigation on Organizations, Information, Cybersecurity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
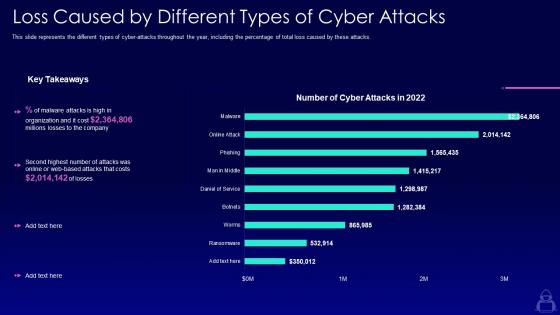 Loss caused by different types of cyber attacks ppt powerpoint presentation layouts
Loss caused by different types of cyber attacks ppt powerpoint presentation layoutsThis slide represents the different types of cyber attacks throughout the year, including the percentage of total loss caused by these attacks. Present the topic in a bit more detail with this Loss Caused By Different Types Of Cyber Attacks Ppt Powerpoint Presentation Layouts. Use it as a tool for discussion and navigation on Loss Caused By Different Types Of Cyber Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
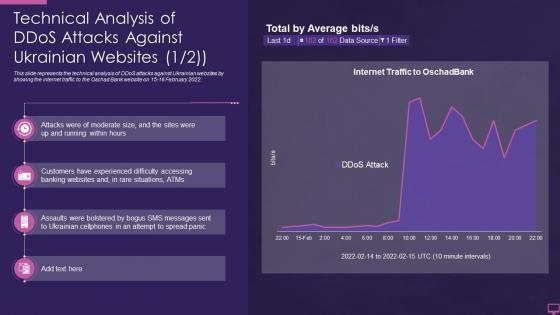 Technical analysis of ddos attacks against ukrainian websites ukraine and russia cyber warfare it
Technical analysis of ddos attacks against ukrainian websites ukraine and russia cyber warfare itThis slide represents the technical analysis of DDoS attacks against Ukrainian websites by showing the internet traffic to the Oschad Bank website on 15 16 February 2022. Present the topic in a bit more detail with this Technical Analysis Of Ddos Attacks Against Ukrainian Websites Ukraine And Russia Cyber Warfare It. Use it as a tool for discussion and navigation on Technical, Analysis, Ukrainian. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
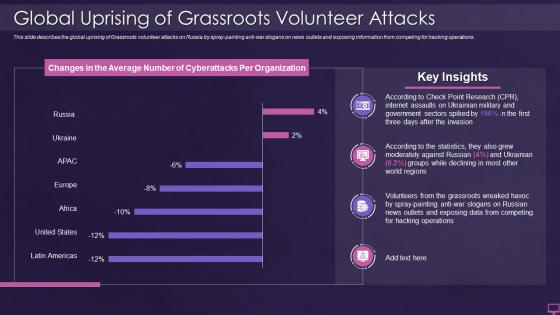 Ukraine and russia cyber warfare it global uprising of grassroots volunteer attacks
Ukraine and russia cyber warfare it global uprising of grassroots volunteer attacksThis slide describes the global uprising of Grassroots volunteer attacks on Russia by spray painting anti war slogans on news outlets and exposing information from competing for hacking operations. Deliver an outstanding presentation on the topic using this Ukraine And Russia Cyber Warfare It Global Uprising Of Grassroots Volunteer Attacks. Dispense information and present a thorough explanation of Global Uprising Of Grassroots Volunteer Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
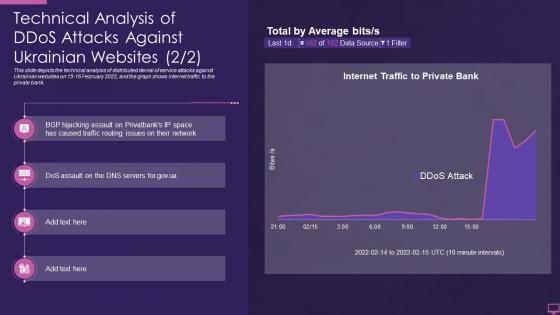 Ukraine and russia cyber warfare it technical analysis of ddos attacks against ukrainian websites
Ukraine and russia cyber warfare it technical analysis of ddos attacks against ukrainian websitesThis slide depicts the technical analysis of distributed denial of service attacks against Ukrainian websites on 15-16 February 2022, and the graph shows internet traffic to the private bank. Deliver an outstanding presentation on the topic using this Ukraine And Russia Cyber Warfare It Technical Analysis Of Ddos Attacks Against Ukrainian Websites. Dispense information and present a thorough explanation of Technical, Analysis, Websites using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
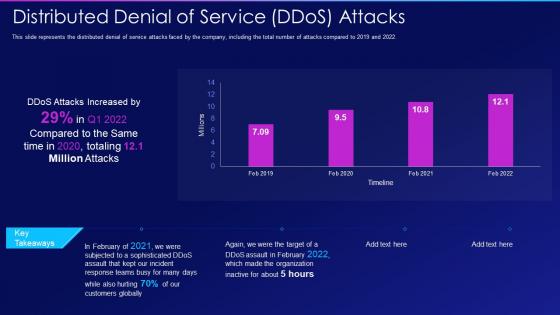 Hacking it distributed denial of service ddos attacks
Hacking it distributed denial of service ddos attacksThis slide represents the distributed denial of service attacks faced by the company, including the total number of attacks compared to 2019 and 2022. Present the topic in a bit more detail with this Hacking It Distributed Denial Of Service Ddos Attacks. Use it as a tool for discussion and navigation on Distributed Denial Of Service Ddos Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
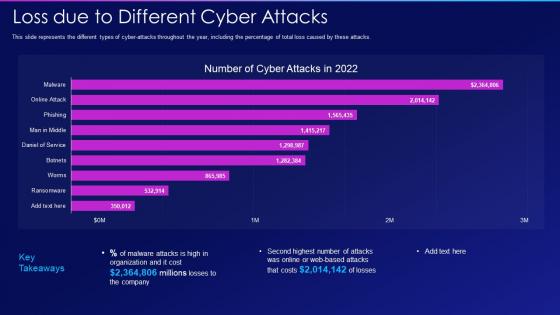 Loss due to different cyber attacks hacking it
Loss due to different cyber attacks hacking itThis slide represents the different types of cyber attacks throughout the year, including the percentage of total loss caused by these attacks. Present the topic in a bit more detail with this Loss Due To Different Cyber Attacks Hacking It. Use it as a tool for discussion and navigation on Loss Due To Different Cyber Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
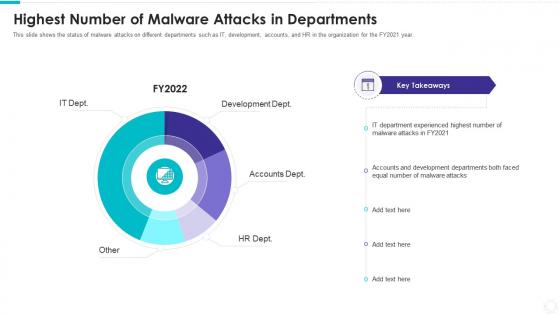 Electronic information security highest number malware attacks departments
Electronic information security highest number malware attacks departmentsThis slide shows the status of malware attacks on different departments such as IT, development, accounts, and HR in the organization for the FY2021 year. Present the topic in a bit more detail with this Electronic Information Security Highest Number Malware Attacks Departments. Use it as a tool for discussion and navigation on Development Dept, Accounts Dept, HR Dept, Other, IT Dept. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
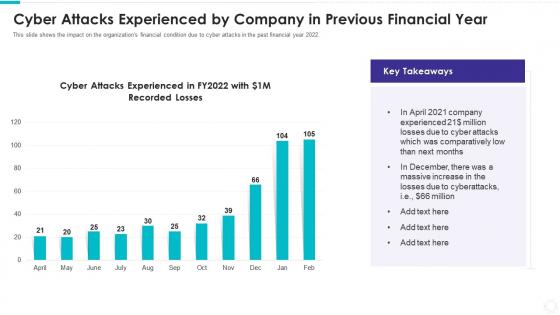 Electronic information security cyber attacks experienced company previous
Electronic information security cyber attacks experienced company previousThis slide shows the impact on the organizations financial condition due to cyber attacks in the past financial year 2022. Deliver an outstanding presentation on the topic using this Electronic Information Security Cyber Attacks Experienced Company Previous. Dispense information and present a thorough explanation of Cyber Attacks, Massive Increase using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
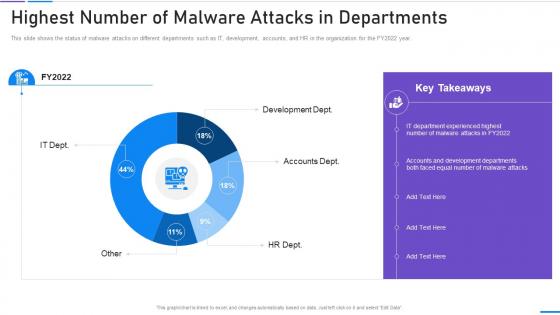 Network Security Highest Number Of Malware Attacks In Departments
Network Security Highest Number Of Malware Attacks In DepartmentsThis slide shows the status of malware attacks on different departments such as IT, development, accounts, and HR in the organization for the FY2022 year. Present the topic in a bit more detail with this Network Security Highest Number Of Malware Attacks In Departments. Use it as a tool for discussion and navigation on Highest Number Of Malware Attacks In Departments. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
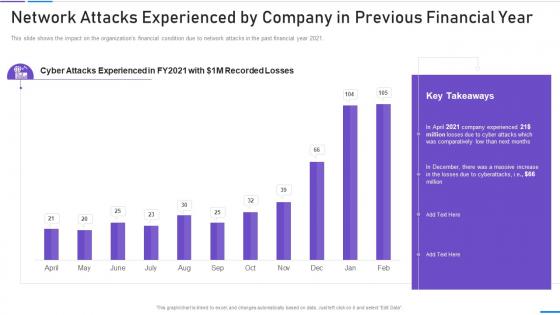 Network Security Network Attacks Experienced By Company
Network Security Network Attacks Experienced By CompanyThis slide shows the impact on the organizations financial condition due to network attacks in the past financial year 2021. Deliver an outstanding presentation on the topic using this Network Security Network Attacks Experienced By Company. Dispense information and present a thorough explanation of Network Attacks Experienced By Company In Previous Financial Year using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
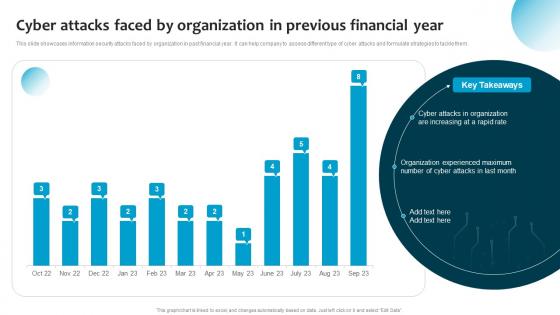 Cyber Attacks Faced By Organization Previous Financial Year Information System Security And Risk Administration
Cyber Attacks Faced By Organization Previous Financial Year Information System Security And Risk AdministrationThis slide showcases information security attacks faced by organization in past financial year. It can help company to assess different type of cyber attacks and formulate strategies to tackle them. Deliver an outstanding presentation on the topic using this Cyber Attacks Faced By Organization Previous Financial Year Information System Security And Risk Administration. Dispense information and present a thorough explanation of Organization Experienced, Increasing A Rapid Rate, Financial Year using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
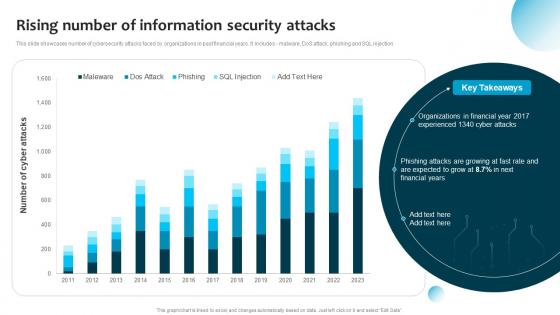 Rising Number Of Information Security Attacks Information System Security And Risk Administration Plan
Rising Number Of Information Security Attacks Information System Security And Risk Administration PlanThis slide showcases number of cybersecurity attacks faced by organizations in past financial years. It includes malware, DoS attack, phishing and SQL injection. Deliver an outstanding presentation on the topic using thisRising Number Of Information Security Attacks Information System Security And Risk Administration Plan. Dispense information and present a thorough explanation of Financial Years, Cyber Attacks, Information Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Social Engineering Attack Prevention Techniques Implementing Security Awareness Training
Social Engineering Attack Prevention Techniques Implementing Security Awareness TrainingThe purpose of this slide is to highlight major techniques which can assist the organization in prevention of social engineering attack. It includes techniques such as limit public information, verifying the source and no s haring of password. Present the topic in a bit more detail with this Social Engineering Attack Prevention Techniques Implementing Security Awareness Training. Use it as a tool for discussion and navigation on Limit Public Information, Verify The Source, No Sharing Of Password. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Attacks Faced By Organization Previous Cybersecurity Risk Analysis And Management Plan
Cyber Attacks Faced By Organization Previous Cybersecurity Risk Analysis And Management PlanThis slide showcases information security attacks faced by organization in past financial year. It can help company to assess different type of cyber attacks and formulate strategies to tackle them. Deliver an outstanding presentation on the topic using this Cyber Attacks Faced By Organization Previous Cybersecurity Risk Analysis And Management Plan. Dispense information and present a thorough explanation of Organization, Financial Year, Experienced using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Rising Number Of Information Security Attacks Cybersecurity Risk Analysis And Management Plan
Rising Number Of Information Security Attacks Cybersecurity Risk Analysis And Management PlanThis slide showcases number of cybersecurity attacks faced by organizations in past financial years. It includes malware, DoS attack, phishing and SQL injection Present the topic in a bit more detail with this Rising Number Of Information Security Attacks Cybersecurity Risk Analysis And Management Plan. Use it as a tool for discussion and navigation on Information, Security Attacks, Organizations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Attacks Faced By Organization In Previous Financial Year Formulating Cybersecurity Plan
Cyber Attacks Faced By Organization In Previous Financial Year Formulating Cybersecurity PlanThis slide showcases information security attacks faced by organization in past financial year. It can help company to assess different type of cyber attacks and formulate strategies to tackle them. Deliver an outstanding presentation on the topic using this Cyber Attacks Faced By Organization In Previous Financial Year Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Cyber Attacks, Organization, Financial Year using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
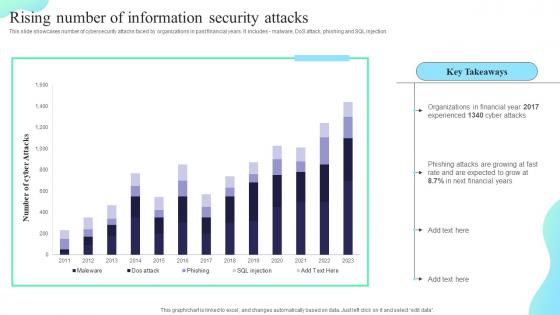 Rising Number Of Information Security Attacks Formulating Cybersecurity Plan
Rising Number Of Information Security Attacks Formulating Cybersecurity PlanThis slide showcases number of cybersecurity attacks faced by organizations in past financial years. It includes malware, DoS attack, phishing and SQL injection. Deliver an outstanding presentation on the topic using this Rising Number Of Information Security Attacks Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Rising Number, Information Security, Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
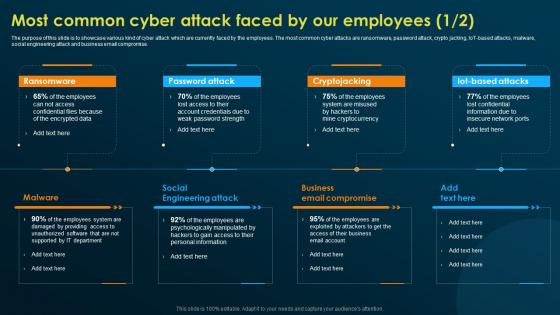 Most Common Cyber Attack Faced By Our Employees Implementing Security Awareness Training
Most Common Cyber Attack Faced By Our Employees Implementing Security Awareness TrainingThe purpose of this slide is to showcase various kind of cyber attack which are currently faced by the employees. The most common cyber attacks are ransomware, password attack, crypto jacking, IoT based attacks, malware, social engineering attack and business email compromise. Introducing Most Common Cyber Attack Faced By Our Employees Implementing Security Awareness Training to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Ransomware, Password Attack, Cryptojacking, Malware, using this template. Grab it now to reap its full benefits.
-
 Table Of Contents Implementing Security Awareness Training To Prevent Cyber Attacks
Table Of Contents Implementing Security Awareness Training To Prevent Cyber AttacksPresent the topic in a bit more detail with this Table Of Contents Implementing Security Awareness Training To Prevent Cyber Attacks. Use it as a tool for discussion and navigation on Security Awareness, Current Assessment, Organization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Attack Analytics Dashboard With Level Of Security
Cyber Attack Analytics Dashboard With Level Of SecurityThe given slide depicts the cyber threat analytics to track the attacks. It includes the no. of incidents, open and solved tickets, category wise no. of incidents along with malware type etc. Introducing our Cyber Attack Analytics Dashboard With Level Of Security set of slides. The topics discussed in these slides are Cyber Attack Analytics, Dashboard, Level Security. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
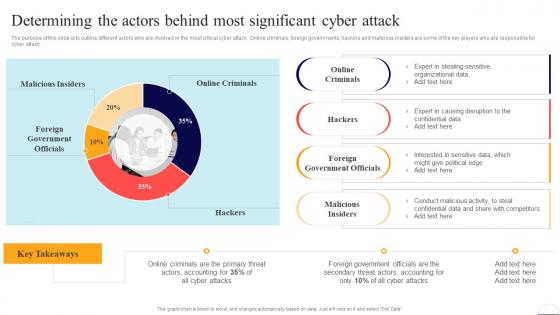 Determining The Actors Behind Most Significant Cyber Attack Preventing Data Breaches Through Cyber Security
Determining The Actors Behind Most Significant Cyber Attack Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to outline different actors who are involved in the most critical cyber attack. Online criminals, foreign governments, hackers and malicious insiders are some of the key players who are responsible for cyber attack. Present the topic in a bit more detail with this Determining The Actors Behind Most Significant Cyber Attack Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Online Criminals, Foreign Government Officials, Malicious Insiders. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
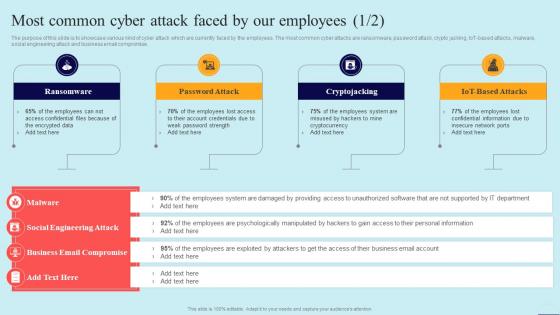 Most Common Cyber Attack Faced By Our Employees Preventing Data Breaches Through Cyber Security
Most Common Cyber Attack Faced By Our Employees Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to showcase various kind of cyber attack which are currently faced by the employees. The most common cyber attacks are ransomware, password attack, crypto jacking, IoT-based attacks, malware, social engineering attack and business email compromise. Introducing Most Common Cyber Attack Faced By Our Employees Preventing Data Breaches Through Cyber Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Ransomware, Password Attack, Cryptojacking, using this template. Grab it now to reap its full benefits.
-
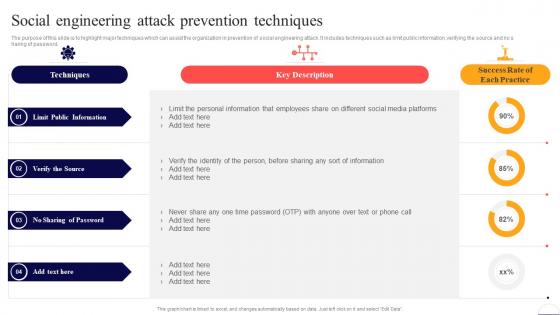 Social Engineering Attack Prevention Techniques Preventing Data Breaches Through Cyber Security
Social Engineering Attack Prevention Techniques Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to highlight major techniques which can assist the organization in prevention of social engineering attack. It includes techniques such as limit public information, verifying the source and no sharing of password. Present the topic in a bit more detail with this Social Engineering Attack Prevention Techniques Preventing Data Breaches Through Cyber Security. Use it as a tool for discussion and navigation on Limit Public Information, Verify The Source, No Sharing Of Password. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
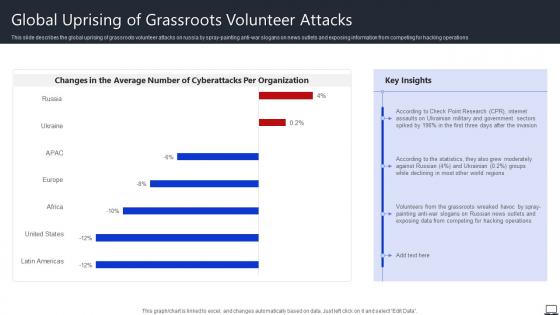 Global Uprising Of Grassroots Volunteer Attacks String Of Cyber Attacks Against Ukraine 2022
Global Uprising Of Grassroots Volunteer Attacks String Of Cyber Attacks Against Ukraine 2022This slide describes the global uprising of grassroots volunteer attacks on russia by spray painting anti war slogans on news outlets and exposing information from competing for hacking operations Present the topic in a bit more detail with this Global Uprising Of Grassroots Volunteer Attacks String Of Cyber Attacks Against Ukraine 2022. Use it as a tool for discussion and navigation on Government, Exposing Data, Hacking Operations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
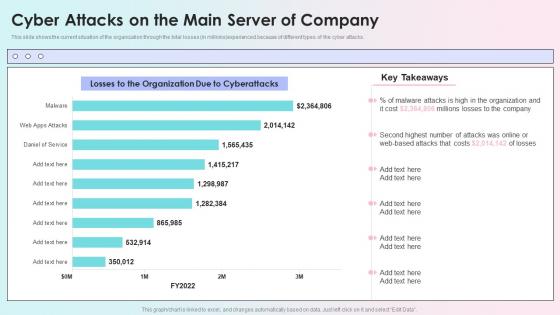 Cyber Attacks On The Main Server Of Company Reverse Proxy Load Balancer Ppt Template
Cyber Attacks On The Main Server Of Company Reverse Proxy Load Balancer Ppt TemplateThis slide shows the current situation of the organization through the total losses in millions experienced because of different types of the cyber attacks. Present the topic in a bit more detail with this Cyber Attacks On The Main Server Of Company Reverse Proxy Load Balancer Ppt Template. Use it as a tool for discussion and navigation on Organization, Cyberattacks, Company, Main Server. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
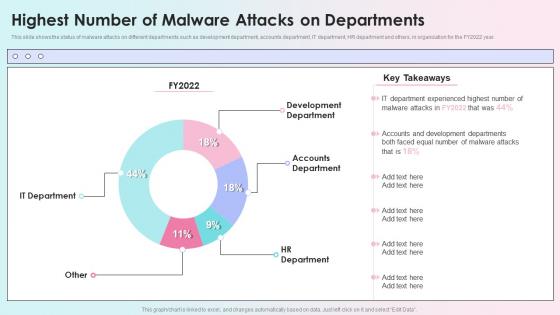 Highest Number Of Malware Attacks On Departments Reverse Proxy Load Balancer Ppt Infographics
Highest Number Of Malware Attacks On Departments Reverse Proxy Load Balancer Ppt InfographicsThis slide shows the status of malware attacks on different departments such as development department, accounts department, IT department, HR department and others, in organization for the FY2022 year. Present the topic in a bit more detail with this Highest Number Of Malware Attacks On Departments Reverse Proxy Load Balancer Ppt Infographics. Use it as a tool for discussion and navigation on Development Department, Accounts Department, Hr Department. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
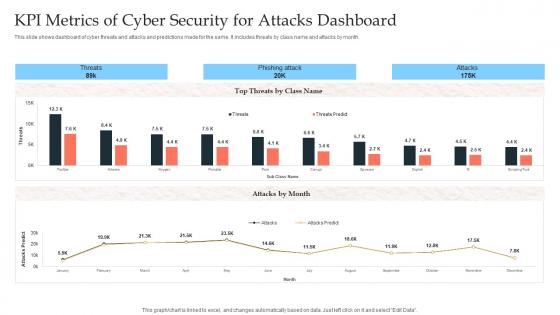 KPI Metrics Of Cyber Security For Attacks Dashboard
KPI Metrics Of Cyber Security For Attacks DashboardThis slide shows dashboard of cyber threats and attacks and predictions made for the same. It includes threats by class name and attacks by month. Introducing our KPI Metrics Of Cyber Security For Attacks Dashboard set of slides. The topics discussed in these slides are KPI Metrics, Cyber Security, Attacks Dashboard. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
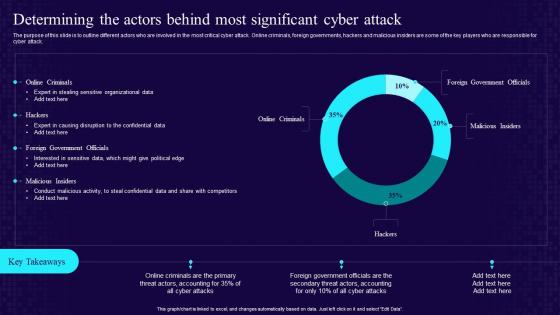 Determining The Actors Behind Most Significant Cyber Attack Developing Cyber Security Awareness
Determining The Actors Behind Most Significant Cyber Attack Developing Cyber Security AwarenessThe purpose of this slide is to outline different actors who are involved in the most critical cyber attack. Online criminals, foreign governments, hackers and malicious insiders are some of the key players who are responsible for cyber attack. Present the topic in a bit more detail with this Determining The Actors Behind Most Significant Cyber Attack Developing Cyber Security Awareness. Use it as a tool for discussion and navigation on Determining The Actors, Behind Most Significant, Cyber Attack. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
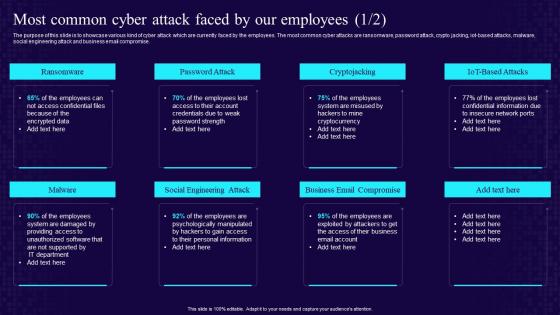 Most Common Cyber Attack Faced By Our Employees Developing Cyber Security Awareness Training Program
Most Common Cyber Attack Faced By Our Employees Developing Cyber Security Awareness Training ProgramThe purpose of this slide is to showcase various kind of cyber attack which are currently faced by the employees. The most common cyber attacks are ransomware, password attack, crypto jacking, iot based attacks, malware, social engineering attack and business email compromise. Increase audience engagement and knowledge by dispensing information using Most Common Cyber Attack Faced By Our Employees Developing Cyber Security Awareness Training Program. This template helps you present information on eight stages. You can also present information on Ransomware, Password Attack, Social Engineering Attack, Business Email Compromise using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
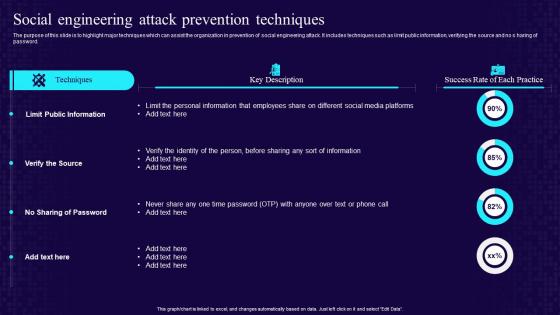 Social Engineering Attack Prevention Techniques Developing Cyber Security Awareness Training
Social Engineering Attack Prevention Techniques Developing Cyber Security Awareness TrainingThe purpose of this slide is to highlight major techniques which can assist the organization in prevention of social engineering attack. It includes techniques such as limit public information, verifying the source and no s haring of password. Deliver an outstanding presentation on the topic using this Social Engineering Attack Prevention Techniques Developing Cyber Security Awareness Training. Dispense information and present a thorough explanation of Limit Public Information, Verify The Source, No Sharing Of Password using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
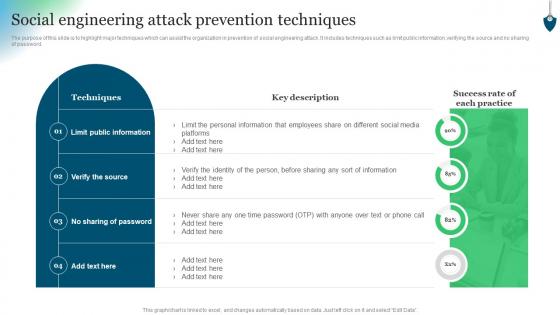 Social Engineering Attack Prevention Techniques Conducting Security Awareness
Social Engineering Attack Prevention Techniques Conducting Security AwarenessThe purpose of this slide is to highlight major techniques which can assist the organization in prevention of social engineering attack. It includes techniques such as limit public information, verifying the source and no sharing of password. Present the topic in a bit more detail with this Social Engineering Attack Prevention Techniques Conducting Security Awareness. Use it as a tool for discussion and navigation on Techniques, Limit Public Information, Verify Source. This template is free to edit as deemed fit for your organization. Therefore download it now.




