Powerpoint Templates and Google slides for Authentic
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Recover Google Authenticator Accounts In Powerpoint And Google Slides Cpb
Recover Google Authenticator Accounts In Powerpoint And Google Slides CpbPresenting Recover Google Authenticator Accounts In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Recover Google Authenticator Accounts. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Multi Factor Authentication Gmail In Powerpoint And Google Slides Cpb
Multi Factor Authentication Gmail In Powerpoint And Google Slides CpbPresenting our Multi Factor Authentication Gmail In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Multi Factor Authentication Gmail . This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Authentic Leader Traits In Powerpoint And Google Slides Cpb
Authentic Leader Traits In Powerpoint And Google Slides CpbPresenting Authentic Leader Traits In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Authentic Leader Traits. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Examples Authentic Leadership Business In Powerpoint And Google Slides Cpb
Examples Authentic Leadership Business In Powerpoint And Google Slides CpbPresenting our Examples Authentic Leadership Business In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Examples Authentic Leadership Business This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 IoT Device Authentication Methods To Ensure Effective IoT Device Management IOT SS
IoT Device Authentication Methods To Ensure Effective IoT Device Management IOT SSThis slide showcases several IoT device authentication models for standardise and secure communication between machines. It included modules such as X.509 certificates, hardware security module, trusted platform module, and symmetric keys. Present the topic in a bit more detail with this IoT Device Authentication Methods To Ensure Effective IoT Device Management IOT SS. Use it as a tool for discussion and navigation on Hardware Security Module, Logistical Complexities, Hardware Equipment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
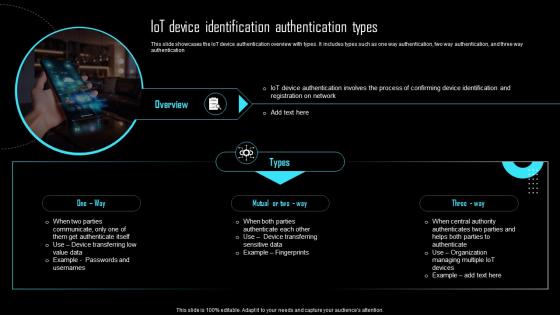 IoT Device Identification Authentication Types Effective IoT Device Management IOT SS
IoT Device Identification Authentication Types Effective IoT Device Management IOT SSThis slide showcases the IoT device authentication overview with types. It includes types such as one way authentication, two way authentication, and three way authentication.Introducing IoT Device Identification Authentication Types Effective IoT Device Management IOT SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Authentication Involves, Confirming Device Identification, Device Transferring, using this template. Grab it now to reap its full benefits.
-
 WIFI Security Network Authentication Colored Icon In Powerpoint Pptx Png And Editable Eps Format
WIFI Security Network Authentication Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon is a visual representation of WIFI security. It features a shield with a lock to represent the protection of your WIFI network. It is a great visual aid for presentations on WIFI security and can be used to highlight the importance of keeping your network secure.
-
 WIFI Security Network Authentication Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
WIFI Security Network Authentication Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone powerpoint icon is perfect for illustrating the concept of WIFI Security. It features a simple, modern design that is sure to make your presentation stand out. It is perfect for any project related to WIFI Security, from educational materials to corporate presentations.
-
 Ultimate Guide For Blockchain Adopt Two Factor Authentication To Reduce Hacking BCT SS
Ultimate Guide For Blockchain Adopt Two Factor Authentication To Reduce Hacking BCT SSThe following slide illustrates some tips and practices to ensure two factor authentication and safeguard blaockchain network. It includes elements such as restricting unauthorized access, safeguarding personal keys, sending unique codes, extending user authentication, etc. Introducing Ultimate Guide For Blockchain Adopt Two Factor Authentication To Reduce Hacking BCT SS to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Unauthorized Access, User Authentication using this template. Grab it now to reap its full benefits.
-
 Document Access Authentication Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Document Access Authentication Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon is an ideal visual aid to represent documents security. It is bright and eye-catching, making it perfect for presentations and other materials. Its simple design ensures that it is easy to understand and will be remembered by viewers.
-
 Document Access Authentication Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Document Access Authentication Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint icon is the perfect visual representation of Documents Security. It is a simple, yet powerful image that will help you communicate the importance of protecting confidential information in an effective and visually appealing way.
-
 Authentication Key Management Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Authentication Key Management Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis colourful PowerPoint icon is perfect for illustrating the concept of key management. It features a key with a blue, green, and yellow background, making it a great visual aid for presentations and documents. Its easy to use and can be easily resized to fit any project.
-
 Authentication Key Management Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Authentication Key Management Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone Powerpoint Icon on Key Management is a simple yet effective visual aid for presentations. It is a great way to illustrate the importance of key management and its role in business operations. The icon can be easily inserted into any PowerPoint presentation to add a professional touch.
-
 IoT Authorization And Authentication For Cybersecurity Management
IoT Authorization And Authentication For Cybersecurity ManagementThis slide provides multiple authorization protocols that helps businesses and organizations to ensure effective and secure management of operations and data transmission. The three protocols are one way, two way, and three way authentication. Introducing our premium set of slides with IoT Authorization And Authentication For Cybersecurity Management. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Management, Cybersecurity, Authorization. So download instantly and tailor it with your information.
-
 User Authentication IoT Cybersecurity Technology
User Authentication IoT Cybersecurity TechnologyThis slide provides the application of authentication and authorization IoT technology that helps to protect systems and user information. The different types are password based, multi factor, certificate based, biometrics, and token based. Presenting our set of slides with User Authentication IoT Cybersecurity Technology. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Biometrics, Token, Technology.
-
 Data Security Encryption Authentication Illustration
Data Security Encryption Authentication IllustrationThis colourful PowerPoint Illustration is perfect for data security presentations. It features a padlock in the centre of a blue and green circle, symbolizing the protection of confidential information. Use it to emphasize the importance of data security in your presentation.
-
 Mobile Security Authentication Measures Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Mobile Security Authentication Measures Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon depicts a shield with a lock, representing security measures. Its perfect for presentations on data protection, cyber security, and other related topics. The icon is bright and vibrant, making it stand out and draw attention to your message.
-
 Mobile Security Authentication Measures Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Mobile Security Authentication Measures Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis monotone powerpoint icon is the perfect visual representation of security measures, providing a simple and effective way to communicate the importance of safety and security to any audience. It is an essential tool for any presentation on security topics.
-
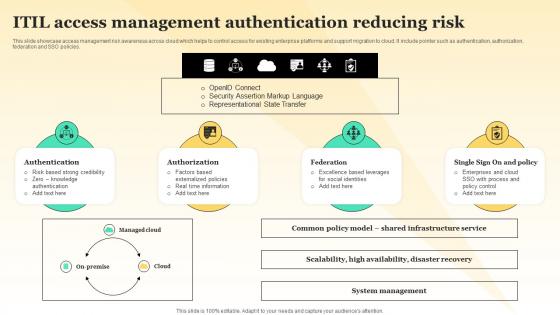 ITIL Access Management Authentication Reducing Risk
ITIL Access Management Authentication Reducing RiskThis slide showcase access management risk awareness across cloud which helps to control access for existing enterprise platforms and support migration to cloud. It include pointer such as authentication, authorization, federation and SSO policies. Introducing our ITIL Access Management Authentication Reducing Risk set of slides. The topics discussed in these slides are Authentication, Authorization. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Authenticity Workplace In Powerpoint And Google Slides Cpb
Authenticity Workplace In Powerpoint And Google Slides CpbPresenting our Authenticity Workplace In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Authenticity Workplace This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
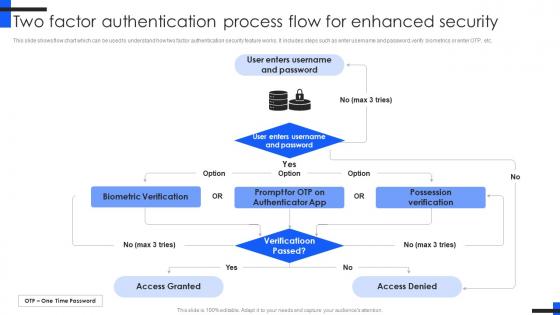 Two Factor Authentication Process Flow Comprehensive Guide For Mobile Banking Fin SS V
Two Factor Authentication Process Flow Comprehensive Guide For Mobile Banking Fin SS VThis slide shows flow chart which can be used to understand how two factor authentication security feature works. It includes steps such as enter username and password, verify biometrics or enter OTP, etc. Present the topic in a bit more detail with this Two Factor Authentication Process Flow Comprehensive Guide For Mobile Banking Fin SS V. Use it as a tool for discussion and navigation on Biometric Verification, Possession Verification. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Authentic Original Content Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Authentic Original Content Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon is perfect for creating an eye catching presentation. It is easy to use and comes in a range of vibrant colours to help your slides stand out. It is ideal for adding a professional touch to any presentation.
-
 Authentic Original Content Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Authentic Original Content Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is a great way to add a professional touch to your presentation. It features a simple, yet powerful design that will help you stand out from the crowd. It is easy to use and can be customized to fit your needs. Perfect for any presentation.
-
 Authentic Leaders Job In Powerpoint And Google Slides Cpb
Authentic Leaders Job In Powerpoint And Google Slides CpbPresenting Authentic Leaders Job In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Authentic Leaders Job. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Digital Message Authentication Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Digital Message Authentication Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured PowerPoint icon is perfect for illustrating data tampering. It features a laptop with a red warning sign, conveying the message of caution and security. Use this icon to highlight the importance of data integrity in your presentation.
-
 Digital Message Authentication Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Digital Message Authentication Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis monotone PowerPoint icon is perfect for visually representing data tampering. It features a laptop with a red line through it, symbolizing the disruption of data integrity. Use it to illustrate the dangers of data tampering and the importance of data security.
-
 Online SMS Authentication Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Online SMS Authentication Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured PowerPoint icon is perfect for illustrating data tampering. It features a laptop with a red warning sign, conveying the message of caution and security. Use this icon to highlight the importance of data integrity in your presentation.
-
 Online SMS Authentication Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Online SMS Authentication Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis monotone PowerPoint icon is perfect for visually representing data tampering. It features a laptop with a red line through it, symbolizing the disruption of data integrity. Use it to illustrate the dangers of data tampering and the importance of data security.
-
 Signature Authentication Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Signature Authentication Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis colourful PowerPoint icon depicts a signature and is perfect for adding a personal touch to any presentation. It is available in a range of vibrant colours to suit any style or theme. Use it to add a professional and stylish look to your slides.
-
 Signature Authentication Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Signature Authentication Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon on Signature is a sleek and modern design that will add a professional touch to any presentation. It features a signature icon in a single color, perfect for adding a personal touch to any presentation.
-
 Application Access Control Authentication Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Application Access Control Authentication Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured PowerPoint icon is a visual representation of Application Security. It features a bright green shield with a white checkmark, symbolizing the protection of applications from malicious threats. Use this icon to illustrate the importance of Application Security in presentations.
-
 Application Access Control Authentication Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Application Access Control Authentication Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint icon is perfect for presentations on application security. It features a lock and key in a circular shape, representing the secure nature of applications. It is a great visual aid to emphasize the importance of security in applications.
-
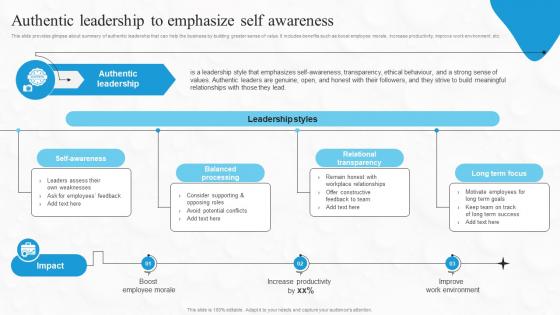 Authentic Leadership To Emphasize Self Awareness Boosting Financial Performance And Decision Strategy SS
Authentic Leadership To Emphasize Self Awareness Boosting Financial Performance And Decision Strategy SSThis slide provides glimpse about summary of authentic leadership that can help the business by building greater sense of value. It includes benefits such as boost employee morale, increase productivity, improve work environment, etc. Deliver an outstanding presentation on the topic using this Authentic Leadership To Emphasize Self Awareness Boosting Financial Performance And Decision Strategy SS. Dispense information and present a thorough explanation of Leadership, Emphasize, Awareness using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Network Authentication Wifi Password Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Network Authentication Wifi Password Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon depicts a wifi password symbol. It is a simple, yet powerful visual representation of the security of a wifi network. It is perfect for presentations, websites, or any other digital project.
-
 Network Authentication Wifi Password Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Network Authentication Wifi Password Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis monotone powerpoint icon is a great visual aid for presentations on wifi security. It features a wifi symbol with a padlock, indicating the need for a secure password to access the wifi network.
-
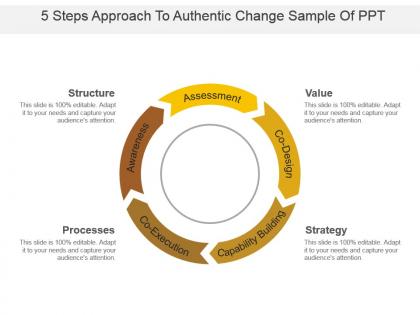 5 steps approach to authentic change sample of ppt
5 steps approach to authentic change sample of pptPresenting 5 steps approach to authentic change sample of ppt. This is a 5 steps approach to authentic change sample of ppt. This is a five stage process. The stages in this process are 5 step approach, 5 step process, 5 step plan.
-
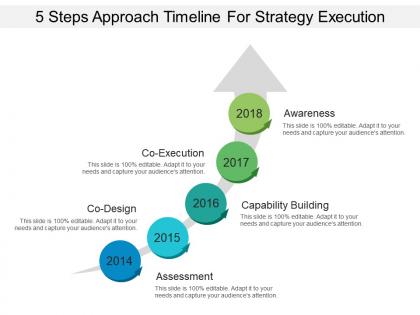 5 steps approach to authentic change ppt slide styles
5 steps approach to authentic change ppt slide stylesPresenting 5 steps approach to authentic change PPT design. This is pre-aligned PPT design template which is acceptable by corporate managers and analysts for all kind of businesses. They provide an unaffected high-quality visual PPT Design. They provide easily resizable shapes, patterns, and matters etc. They are strenuous presentation graphic having a smooth downloading process. They are well versant with Google slides and other applications.
-
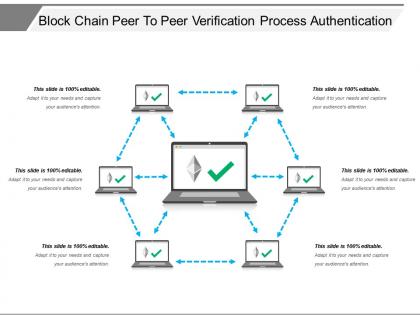 Block chain peer to peer verification process authentication
Block chain peer to peer verification process authenticationPresenting Block Chain Peer To Peer Verification Process Authentication PowerPoint slide. This PPT theme is available in both 4:3 and 16:9 aspect ratios. This PowerPoint template is customizable so you can modify the font size, font type, color and shapes as per your requirements. This PPT presentation is Google Slides compatible hence it is easily accessible. You can download and save this PowerPoint layout in different formats like PDF, PNG, and JPG.
-
 Industry dynamics institutional factors marketing mix user authentication
Industry dynamics institutional factors marketing mix user authenticationPresenting this set of slides with name - Industry Dynamics Institutional Factors Marketing Mix User Authentication. This is an editable six stages graphic that deals with topics like Industry Dynamics, Institutional Factors, Marketing Mix, User Authentication to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
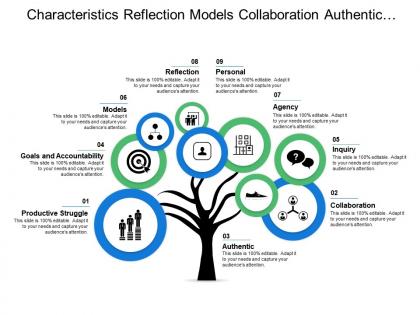 Characteristics reflection models collaboration authentic goals and accountability
Characteristics reflection models collaboration authentic goals and accountabilityPresenting this set of slides with name - Characteristics Reflection Models Collaboration Authentic Goals And Accountability. This is a nine stage process. The stages in this process are Characteristics, Feature, Quality.
-
 Characteristics showing active collaborative constructive and authentic
Characteristics showing active collaborative constructive and authenticPresenting this set of slides with name - Characteristics Showing Active Collaborative Constructive And Authentic. This is a five stage process. The stages in this process are Characteristics, Feature, Quality.
-
 Access management identity authentication overview
Access management identity authentication overviewPresenting this set of slides with name - Access Management Identity Authentication Overview. This is a five stage process. The stages in this process are Access Management, Identity Management, Authentication Management.
-
 Work environment contains authentic leadership appropriate staffing and collaboration
Work environment contains authentic leadership appropriate staffing and collaborationPresenting this set of slides with name - Work Environment Contains Authentic Leadership Appropriate Staffing And Collaboration. This is a seven stage process. The stages in this process are Work Environment, Workplace Ethics, Company Environment.
-
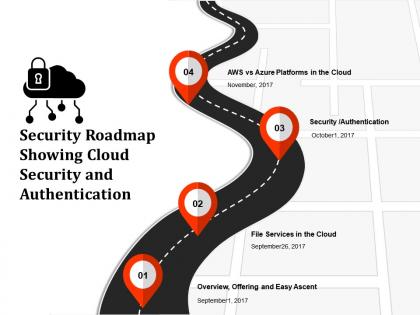 Security roadmap showing cloud security and authentication
Security roadmap showing cloud security and authenticationPresenting this set of slides with name - Security Roadmap Showing Cloud Security And Authentication. This is a four stage process. The stages in this process are Security Roadmap, Security Timeline, Safer Roadmap.
-
 Adapted localized tools personality addition authenticity boosted positive
Adapted localized tools personality addition authenticity boosted positivePresenting this set of slides with name - Adapted Localized Tools Personality Addition Authenticity Boosted Positive. This is an editable six stages graphic that deals with topics like Adapted Localized Tools, Personality Addition, Authenticity Boosted Positive to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
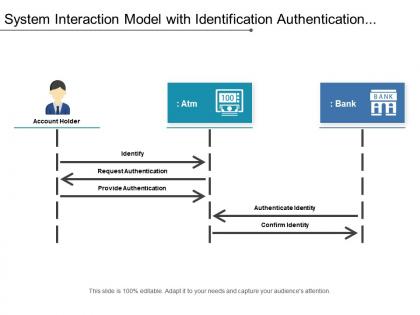 System interaction model with identification authentication and identity
System interaction model with identification authentication and identityPresenting this set of slides with name - System Interaction Model With Identification Authentication And Identity. This is a two stage process. The stages in this process are System Interaction, User System, Usi.
-
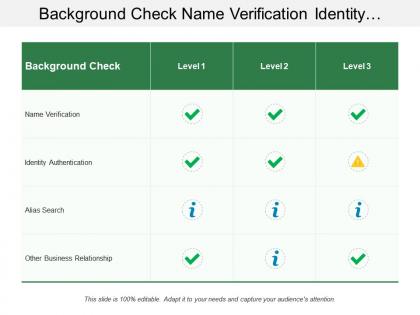 Background check name verification identity authentication
Background check name verification identity authenticationPresenting this set of slides with name - Background Check Name Verification Identity Authentication. This is a three stage process. The stages in this process are Background Check, Background Verification, Employment History.
-
 Core values showing authenticity responsibility and integrity
Core values showing authenticity responsibility and integrityPresenting this set of slides with name - Core Values Showing Authenticity Responsibility And Integrity. This is a three stage process. The stages in this process are Core Values, Our Values, Our Goals, Company Philosophy.
-
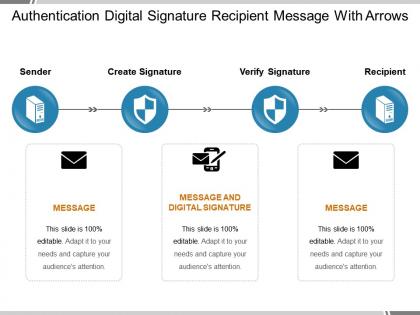 Authentication digital signature recipient message with arrows
Authentication digital signature recipient message with arrowsPresenting authentication digital signature recipient message with arrows. This is a authentication digital signature recipient message with arrows. This is a three stage process. The stages in this process are password, authentication, access approval.
-
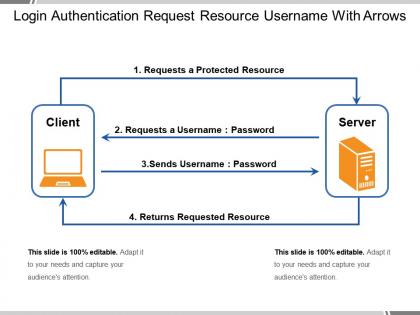 Login authentication request resource username with arrows
Login authentication request resource username with arrowsPresenting login authentication request resource username with arrows. This is a login authentication request resource username with arrows. This is a two stage process. The stages in this process are password, authentication, access approval.
-
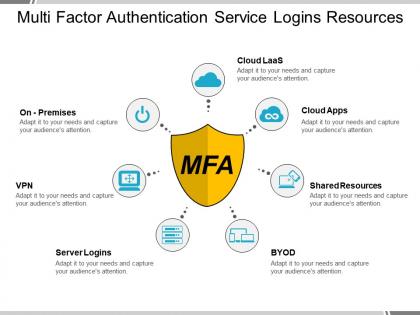 Multi factor authentication service logins resources
Multi factor authentication service logins resourcesPresenting multi factor authentication service logins resources. This is a multi factor authentication service logins resources. This is a seven stage process. The stages in this process are password, authentication, access approval.
-
 Medium term planning authentic leadership relational leadership model
Medium term planning authentic leadership relational leadership modelPresenting this set of slides with name - Medium Term Planning Authentic Leadership Relational Leadership Model. This is an editable five stages graphic that deals with topics like medium term planning, authentic leadership, relational leadership model to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Concrete model organic farming authentic content unstructured communication
Concrete model organic farming authentic content unstructured communicationPresenting this set of slides with name - Concrete Model Organic Farming Authentic Content Unstructured Communication. This is an editable four stages graphic that deals with topics like Concrete Model, Organic Farming, Authentic Content, Unstructured Communication to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
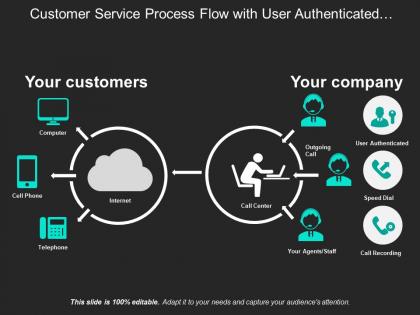 Customer service process flow with user authenticated agent and call recording
Customer service process flow with user authenticated agent and call recordingPresenting this set of slides with name - Customer Service Process Flow With User Authenticated Agent And Call Recording. This is a two stage process. The stages in this process are Customer Service Process Flow, Customer Service Management, Customer Service Flow Chart.
-
 Authentication icon displaying secured connection
Authentication icon displaying secured connectionPresenting this set of slides with name - Authentication Icon Displaying Secured Connection. This is a three stages process. The stages in this process are Password, Authentication Icon, Access Approval.
-
 Authentication icon displaying secured network
Authentication icon displaying secured networkPresenting this set of slides with name - Authentication Icon Displaying Secured Network. This is a four stages process. The stages in this process are Password, Authentication Icon, Access Approval.
-
 Authentication icon showing secured email
Authentication icon showing secured emailPresenting this set of slides with name - Authentication Icon Showing Secured Email. This is a three stages process. The stages in this process arePassword, Authentication Icon, Access Approval.
-
 Authentication icon showing secured network
Authentication icon showing secured networkPresenting this set of slides with name - Authentication Icon Showing Secured Network. This is a four stages process. The stages in this process are Password, Authentication Icon, Access Approval.
-
 Authentication icon with fingerprint
Authentication icon with fingerprintPresenting this set of slides with name - Authentication Icon With Fingerprint. This is a four stages process. The stages in this process are Password, Authentication Icon, Access Approval.
-
 Authentication icon with user authentication
Authentication icon with user authenticationPresenting this set of slides with name - Authentication Icon With User Authentication. This is a four stages process. The stages in this process are Password, Authentication Icon, Access Approval.



