Powerpoint Templates and Google slides for Cloud Security Use Cases
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
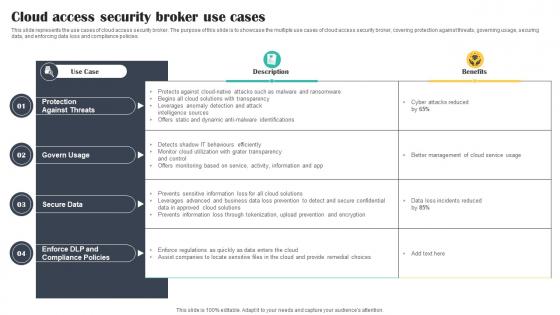
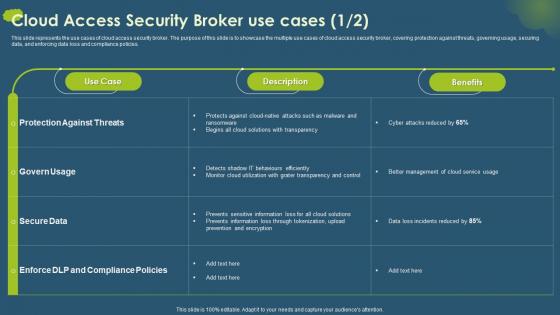 Cloud Access Security Broker CASB V2 Use Cases Ppt Ideas Graphics Download
Cloud Access Security Broker CASB V2 Use Cases Ppt Ideas Graphics DownloadThis slide represents the use cases of cloud access security broker. The purpose of this slide is to showcase the multiple use cases of cloud access security broker, covering protection against threats, governing usage, securing data, and enforcing data loss and compliance policies. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 Use Cases Ppt Ideas Graphics Download. Dispense information and present a thorough explanation of Protection Against Threats, Secure Data, Upload Prevention And Encryption, Cloud Solutions With Transparency using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
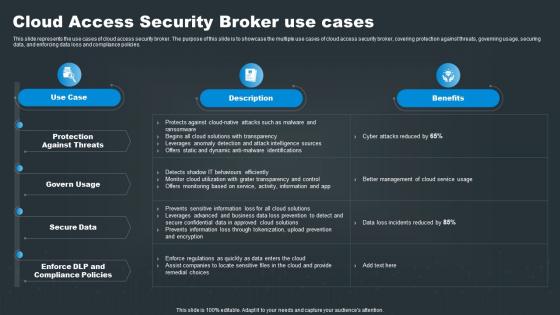
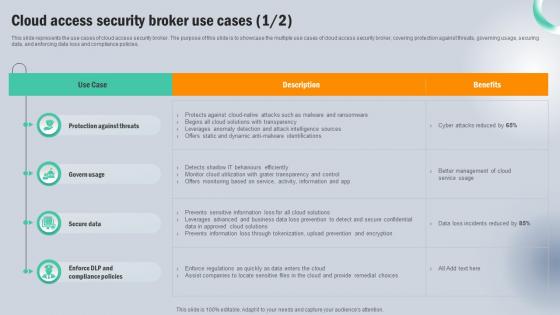 Cloud Access Security Broker Use Cases Next Generation CASB
Cloud Access Security Broker Use Cases Next Generation CASBThis slide represents the use cases of cloud access security broker. The purpose of this slide is to showcase the multiple use cases of cloud access security broker, covering protection against threats, governing usage, securing data, and enforcing data loss and compliance policies. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker Use Cases Next Generation CASB Dispense information and present a thorough explanation of Protection Against Threats, Govern Usage, Secure Data using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
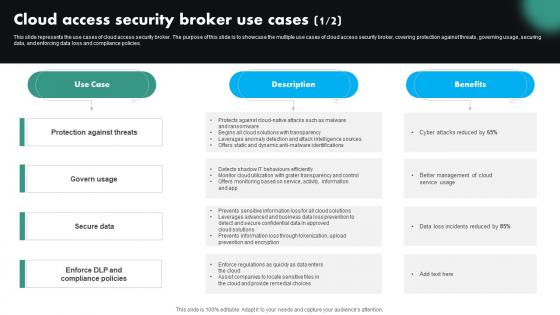 Cloud Access Security Broker Use Cases CASB Cloud Security
Cloud Access Security Broker Use Cases CASB Cloud SecurityThis slide represents the use cases of cloud access security broker. The purpose of this slide is to showcase the multiple use cases of cloud access security broker, covering protection against threats, governing usage, securing data, and enforcing data loss and compliance policies. Present the topic in a bit more detail with this Cloud Access Security Broker Use Cases CASB Cloud Security. Use it as a tool for discussion and navigation on Protection Against Threats, Compliance Policies, Cloud Access Security Broker. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
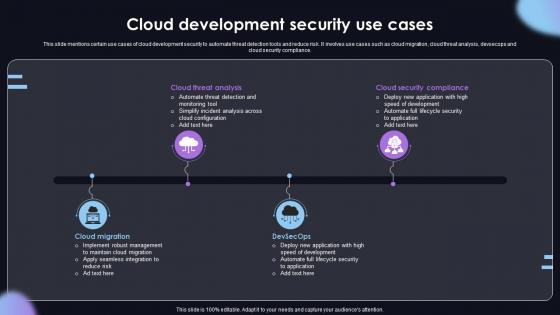 Cloud Development Security Use Cases
Cloud Development Security Use CasesThis slide mentions certain use cases of cloud development security to automate threat detection tools and reduce risk. It involves use cases such as cloud migration, cloud threat analysis, devsecops and cloud security compliance. Introducing our premium set of slides with Cloud Development Security Use Cases. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cloud Threat Analysis, Cloud Migration. So download instantly and tailor it with your information.
-
 Cloud Security Enhancement Using Hashing Cloud Cryptography
Cloud Security Enhancement Using Hashing Cloud CryptographyThis slide talks about the various applications of hash algorithm in cloud cryptography. The purpose of this slide is to explain how hash technique can help in providing security in cloud computing. These are password storage, data integrity, digital signatures, etc. Increase audience engagement and knowledge by dispensing information using Cloud Security Enhancement Using Hashing Cloud Cryptography. This template helps you present information on four stages. You can also present information on Data Integrity, Digital Signatures, Password Storage using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cryptographic Algorithms Used In Data Security Cloud Cryptography
Cryptographic Algorithms Used In Data Security Cloud CryptographyThis slide talks about algorithms used for implementing cryptography in data security. The purpose of this slide is to explain the different implementation steps. The techniques discussed are RSA Rivest, Shamir, Adleman cryptographic algorithm and Data Encryption Standard algorithm. Deliver an outstanding presentation on the topic using this Cryptographic Algorithms Used In Data Security Cloud Cryptography. Dispense information and present a thorough explanation of Cryptographic, Algorithms, Data Encryption Standard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Key Uses And Applications Of Cryptographic Security Cloud Cryptography
Key Uses And Applications Of Cryptographic Security Cloud CryptographyThis slide outlines the various uses of cryptography. The purpose of this slide is to elaborate the key applications of cryptography. These are computer security, digital currencies, web surfing security, electronic signatures, authentication, cryptocurrencies, etc. Increase audience engagement and knowledge by dispensing information using Key Uses And Applications Of Cryptographic Security Cloud Cryptography. This template helps you present information on nine stages. You can also present information on Computer Security, Digital Currencies, Web Surfing Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
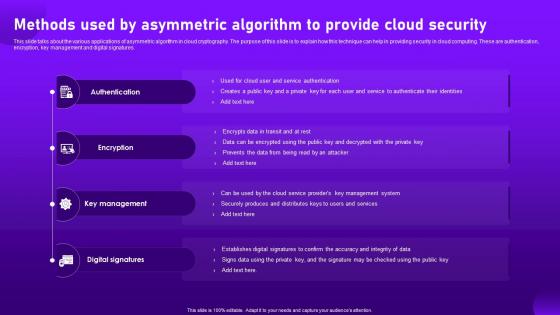 Methods Used By Asymmetric Algorithm To Provide Cloud Security Cloud Cryptography
Methods Used By Asymmetric Algorithm To Provide Cloud Security Cloud CryptographyThis slide talks about the various applications of asymmetric algorithm in cloud cryptography. The purpose of this slide is to explain how this technique can help in providing security in cloud computing. These are authentication, encryption, key management and digital signatures. Introducing Methods Used By Asymmetric Algorithm To Provide Cloud Security Cloud Cryptography to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Authentication, Key Management, Digital Signatures, using this template. Grab it now to reap its full benefits.
-
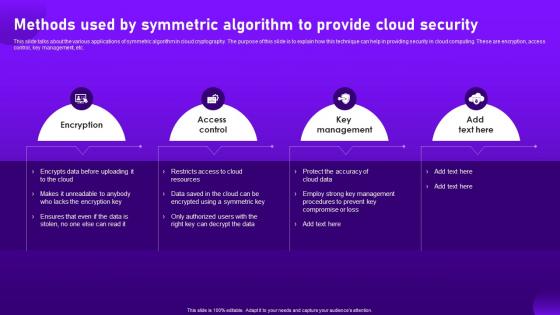 Methods Used By Symmetric Algorithm To Provide Cloud Security Cloud Cryptography
Methods Used By Symmetric Algorithm To Provide Cloud Security Cloud CryptographyThis slide talks about the various applications of symmetric algorithm in cloud cryptography. The purpose of this slide is to explain how this technique can help in providing security in cloud computing. These are encryption, access control, key management, etc. Increase audience engagement and knowledge by dispensing information using Methods Used By Symmetric Algorithm To Provide Cloud Security Cloud Cryptography. This template helps you present information on four stages. You can also present information on Encryption, Access Control, Key Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Comparison Secure Web Gateway And Cloud Network Security Using Secure Web Gateway
Comparison Secure Web Gateway And Cloud Network Security Using Secure Web GatewayThis slide demonstrates the concept of cloud security gateways and Secure Web Gateways. The purpose of this slide is to compare cloud security gateways and SWGs on the basis of various factors such as scope, deployment, architecture, features and cost. Deliver an outstanding presentation on the topic using this Comparison Secure Web Gateway And Cloud Network Security Using Secure Web Gateway. Dispense information and present a thorough explanation of Deployment, Architecture, Comparison using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Access Security Broker Use Cases Cloud Security Model
Cloud Access Security Broker Use Cases Cloud Security ModelThis slide represents the use cases of cloud access security broker. The purpose of this slide is to showcase the multiple use cases of cloud access security broker, covering protection against threats, governing usage, securing data, and enforcing data loss and compliance policies. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker Use Cases Cloud Security Model. Dispense information and present a thorough explanation of Protection, Govern, Secure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Access Security Broker Use Cases SASE Network Security
Cloud Access Security Broker Use Cases SASE Network SecurityThis slide represents the use cases of cloud access security broker. The purpose of this slide is to showcase the multiple use cases of cloud access security broker, covering protection against threats, governing usage, securing data, and enforcing data loss and compliance policies. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker Use Cases SASE Network Security. Dispense information and present a thorough explanation of Protection, Secure, Compliance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
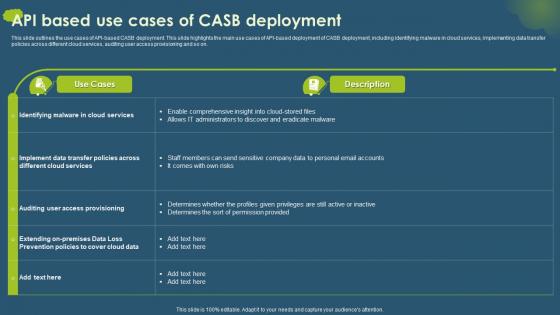 Cloud Access Security Broker CASB V2 API Based Use Cases Of CASB Deployment
Cloud Access Security Broker CASB V2 API Based Use Cases Of CASB DeploymentThis slide outlines the use cases of API-based CASB deployment. This slide highlights the main use cases of API-based deployment of CASB deployment, including identifying malware in cloud services, implementing data transfer policies across different cloud services, auditing user access provisioning and so on. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 API Based Use Cases Of CASB Deployment. Dispense information and present a thorough explanation of Malware In Cloud Services, Data Transfer Policies, Cloud Services, Auditing User Access Provisioning using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
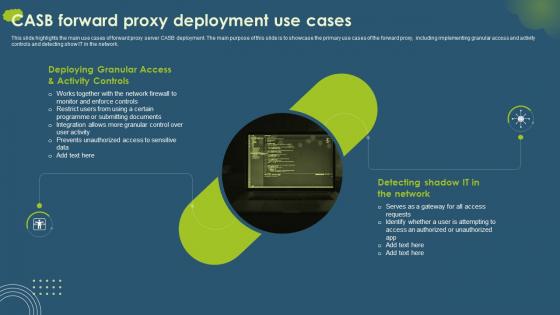 Cloud Access Security Broker CASB V2 CASB Forward Proxy Deployment Use Cases
Cloud Access Security Broker CASB V2 CASB Forward Proxy Deployment Use CasesThis slide highlights the main use cases of forward proxy server CASB deployment. The main purpose of this slide is to showcase the primary use cases of the forward proxy, including implementing granular access and activity controls and detecting show IT in the network. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker CASB V2 CASB Forward Proxy Deployment Use Cases. This template helps you present information on two stages. You can also present information on Deploying Granular Access, Activity Controls, Detecting Shadow, IT In The Network using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
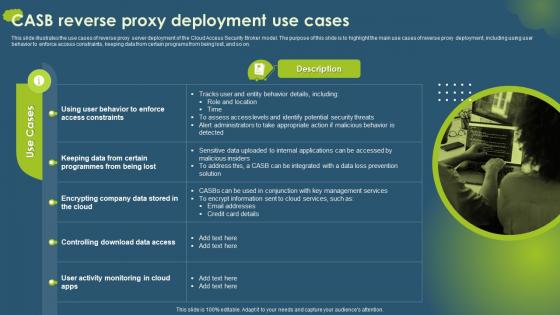 Cloud Access Security Broker CASB V2 CASB Reverse Proxy Deployment Use Cases
Cloud Access Security Broker CASB V2 CASB Reverse Proxy Deployment Use CasesThis slide illustrates the use cases of reverse proxy server deployment of the Cloud Access Security Broker model. The purpose of this slide is to highlight the main use cases of reverse proxy deployment, including using user behavior to enforce access constraints, keeping data from certain programs from being lost, and so on. Introducing Proxy to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Reverse Proxy Server Deployment, Cloud Access Security Broker, Reverse Proxy Deployment, using this template. Grab it now to reap its full benefits.
-
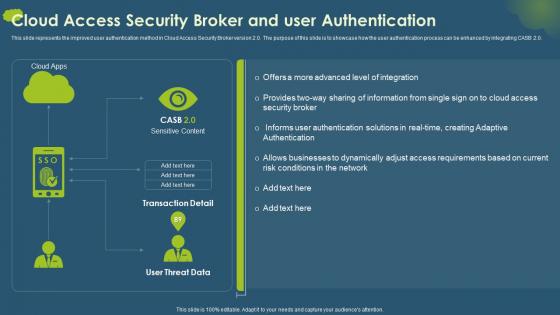 Cloud Access Security Broker CASB V2 Cloud Access Security Broker And User Authentication
Cloud Access Security Broker CASB V2 Cloud Access Security Broker And User AuthenticationThis slide represents the improved user authentication method in Cloud Access Security Broker version 2.0. The purpose of this slide is to showcase how the user authentication process can be enhanced by integrating CASB 2.0. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 Cloud Access Security Broker And User Authentication. Dispense information and present a thorough explanation of Authentication Solutions, Creating Adaptive Authentication, Businesses To Dynamically using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
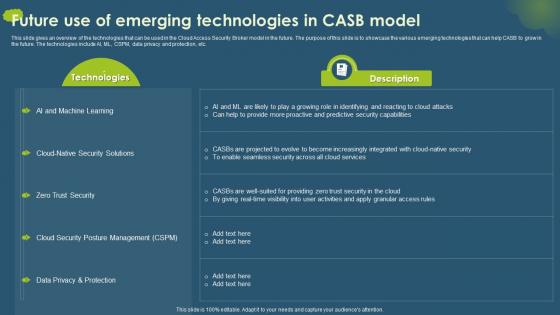 Cloud Access Security Broker CASB V2 Future Use Of Emerging Technologies In CASB Model
Cloud Access Security Broker CASB V2 Future Use Of Emerging Technologies In CASB ModelThis slide gives an overview of the technologies that can be used in the Cloud Access Security Broker model in the future. The purpose of this slide is to showcase the various emerging technologies that can help CASB to grow in the future. The technologies include AI, ML, CSPM, data privacy and protection, etc. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 Future Use Of Emerging Technologies In CASB Model. Dispense information and present a thorough explanation of Cloud Security Posture Management, Data Privacy And Protection, Zero Trust Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
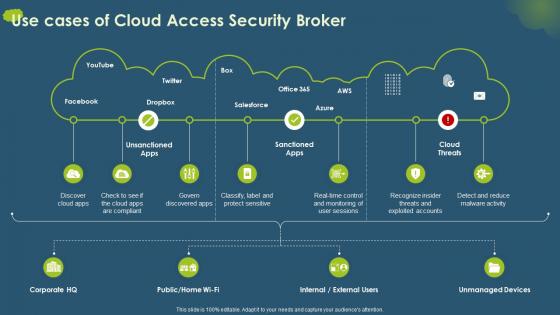 Cloud Access Security Broker CASB V2 Use Cases Of Cloud Access Security Broker
Cloud Access Security Broker CASB V2 Use Cases Of Cloud Access Security BrokerPresent the topic in a bit more detail with this Cloud Access Security Broker CASB V2 Use Cases Of Cloud Access Security Broker. Use it as a tool for discussion and navigation on Threats And Exploited Accounts, Unmanaged Devices, Label And Protect Sensitive, Cloud Access Security Broker. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
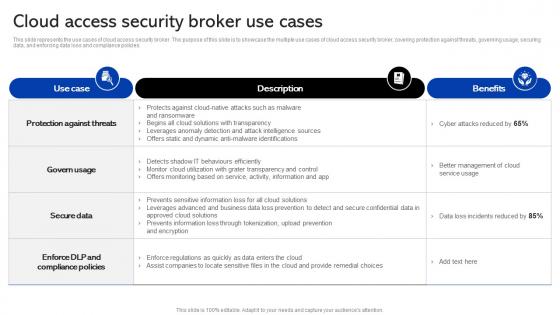 Sase Security Cloud Broker Use Cases Ppt Show Graphics Template
Sase Security Cloud Broker Use Cases Ppt Show Graphics TemplateThis slide represents the use cases of cloud access security broker. The purpose of this slide is to showcase the multiple use cases of cloud access security broker, covering protection against threats, governing usage, securing data, and enforcing data loss and compliance policies. Deliver an outstanding presentation on the topic using this Sase Security Cloud Broker Use Cases Ppt Show Graphics Template. Dispense information and present a thorough explanation of Identifications, Ransomware, Transparency using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
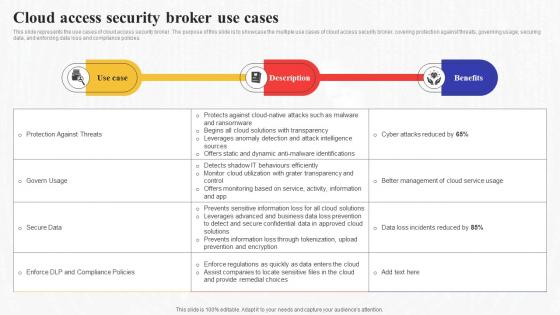 Cloud Access Broker Use Cases Secure Access Service Edge Sase
Cloud Access Broker Use Cases Secure Access Service Edge SaseThis slide represents the use cases of cloud access security broker. The purpose of this slide is to showcase the multiple use cases of cloud access security broker, covering protection against threats, governing usage, securing data, and enforcing data loss and compliance policies. Present the topic in a bit more detail with this Cloud Access Broker Use Cases Secure Access Service Edge Sase. Use it as a tool for discussion and navigation on Transparency, Intelligence, Solutions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
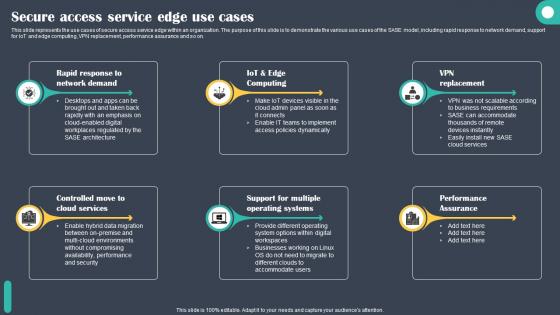 Secure Access Service Edge Use Cases Cloud Security Model
Secure Access Service Edge Use Cases Cloud Security ModelThis slide represents the use cases of secure access service edge within an organization. The purpose of this slide is to demonstrate the various use cases of the SASE model, including rapid response to network demand, support for IoT and edge computing, VPN replacement, performance assurance and so on. Increase audience engagement and knowledge by dispensing information using Secure Access Service Edge Use Cases Cloud Security Model. This template helps you present information on six stages. You can also present information on Demand, Computing, Replacement using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
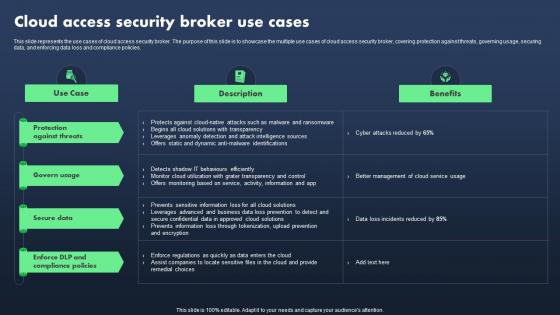 Sase Model Cloud Access Security Broker Use Cases
Sase Model Cloud Access Security Broker Use CasesThis slide represents the use cases of cloud access security broker. The purpose of this slide is to showcase the multiple use cases of cloud access security broker, covering protection against threats, governing usage, securing data, and enforcing data loss and compliance policies. Present the topic in a bit more detail with this Sase Model Cloud Access Security Broker Use Cases. Use it as a tool for discussion and navigation on Protection Against Threats, Govern Usage, Secure Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
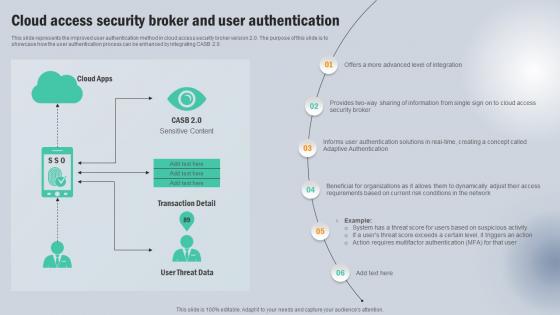 Cloud Access Security Broker And User Authentication Next Generation CASB
Cloud Access Security Broker And User Authentication Next Generation CASBThis slide represents the improved user authentication method in cloud access security broker version 2.0. The purpose of this slide is to showcase how the user authentication process can be enhanced by integrating CASB 2.0. Present the topic in a bit more detail with this Cloud Access Security Broker And User Authentication Next Generation CASB Use it as a tool for discussion and navigation on Cloud Apps, Transaction Detail, User Threat Data This template is free to edit as deemed fit for your organization. Therefore download it now.
-
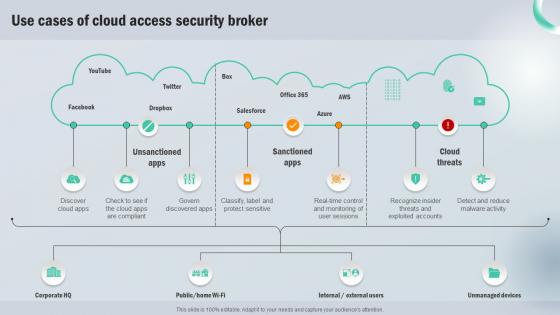 Use Cases Of Cloud Access Security Broker Next Generation CASB
Use Cases Of Cloud Access Security Broker Next Generation CASBPresent the topic in a bit more detail with this Use Cases Of Cloud Access Security Broker Next Generation CASB Use it as a tool for discussion and navigation on Unsanctioned Apps, Sanctioned Apps, Cloud Threats This template is free to edit as deemed fit for your organization. Therefore download it now.
-
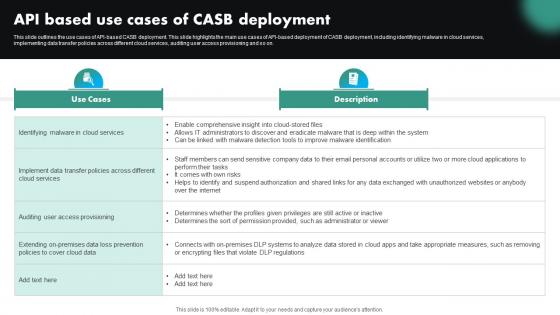 Api Based Use Cases Of CASB Deployment CASB Cloud Security
Api Based Use Cases Of CASB Deployment CASB Cloud SecurityThis slide outlines the use cases of API-based CASB deployment. This slide highlights the main use cases of API-based deployment of CASB deployment, including identifying malware in cloud services, implementing data transfer policies across different cloud services, auditing user access provisioning and so on. Present the topic in a bit more detail with this Api Based Use Cases Of CASB Deployment CASB Cloud Security. Use it as a tool for discussion and navigation on Cloud Services, Data Transfer Policies, Auditing User Access Provisioning. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
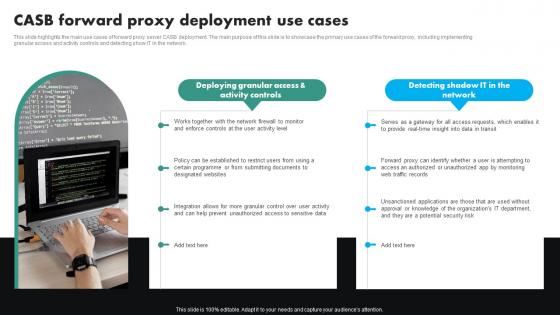 CASB Forward Proxy Deployment Use Cases CASB Cloud Security
CASB Forward Proxy Deployment Use Cases CASB Cloud SecurityThis slide highlights the main use cases of forward proxy server CASB deployment. The main purpose of this slide is to showcase the primary use cases of the forward proxy, including implementing granular access and activity controls and detecting show IT in the network. Increase audience engagement and knowledge by dispensing information using CASB Forward Proxy Deployment Use Cases CASB Cloud Security. This template helps you present information on two stages. You can also present information on Deploying Granular Access, Proxy Deployment Use Cases, Potential Security Risk using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 CASB Reverse Proxy Deployment Use Cases CASB Cloud Security
CASB Reverse Proxy Deployment Use Cases CASB Cloud SecurityThis slide illustrates the use cases of reverse proxy server deployment of the cloud access security broker model. The purpose of this slide is to highlight the main use cases of reverse proxy deployment, including using user behavior to enforce access constraints, keeping data from certain programs from being lost, and so on. Deliver an outstanding presentation on the topic using this CASB Reverse Proxy Deployment Use Cases CASB Cloud Security. Dispense information and present a thorough explanation of Enforce Access Constraints, Controlling Download Data Access, Prevent Data Exfiltration using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cloud Access Security Broker And User Authentication CASB Cloud Security
Cloud Access Security Broker And User Authentication CASB Cloud SecurityThis slide represents the improved user authentication method in cloud access security broker version 2.0. The purpose of this slide is to showcase how the user authentication process can be enhanced by integrating CASB 2.0. Present the topic in a bit more detail with this Cloud Access Security Broker And User Authentication CASB Cloud Security. Use it as a tool for discussion and navigation on Cloud Access Security Broker, User Authentication, Multifactor Authentication. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
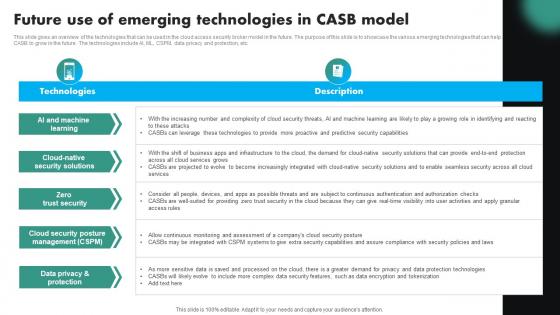 Future Use Of Emerging Technologies In CASB Model CASB Cloud Security
Future Use Of Emerging Technologies In CASB Model CASB Cloud SecurityThis slide gives an overview of the technologies that can be used in the cloud access security broker model in the future. The purpose of this slide is to showcase the various emerging technologies that can help CASB to grow in the future. The technologies include AI, ML, CSPM, data privacy and protection, etc. Deliver an outstanding presentation on the topic using this Future Use Of Emerging Technologies In CASB Model CASB Cloud Security. Dispense information and present a thorough explanation of Cloud Native Security Solutions, Cloud Security Posture Management, Data Privacy And Protection using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Use Cases Of Cloud Access Security Broker CASB Cloud Security
Use Cases Of Cloud Access Security Broker CASB Cloud SecurityDeliver an outstanding presentation on the topic using this Use Cases Of Cloud Access Security Broker CASB Cloud Security. Dispense information and present a thorough explanation of Cloud Access Security Broker, Reduce Malware Activity, Real Time Control using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
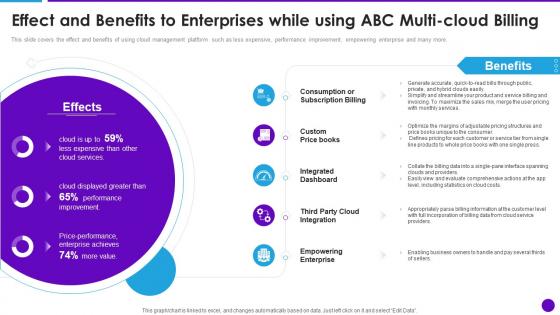 Cloud Architecture And Security Review Effect And Benefits To Enterprises While Using Abc Multi Cloud
Cloud Architecture And Security Review Effect And Benefits To Enterprises While Using Abc Multi CloudThis slide covers the effect and benefits of using cloud management platform such as less expensive, performance improvement, empowering enterprise and many more. Present the topic in a bit more detail with this Cloud Architecture And Security Review Effect And Benefits To Enterprises While Using Abc Multi Cloud. Use it as a tool for discussion and navigation on Consumption Or Subscription Billing, Integrated Dashboard, Empowering Enterprise. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
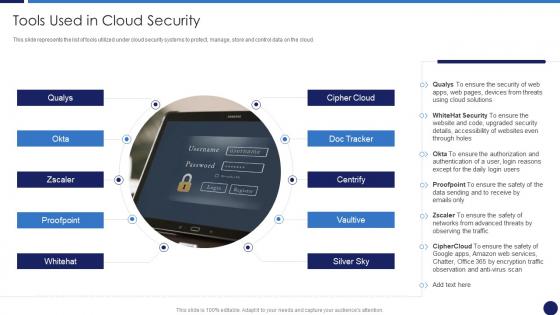 Cloud Data Protection Tools Used In Cloud Security
Cloud Data Protection Tools Used In Cloud SecurityThis slide represents the list of tools utilized under cloud security systems to protect, manage, store and control data on the cloud. Increase audience engagement and knowledge by dispensing information using Cloud Data Protection Tools Used In Cloud Security. This template helps you present information on one stage. You can also present information on Cloud Solutions, Security, Networks using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
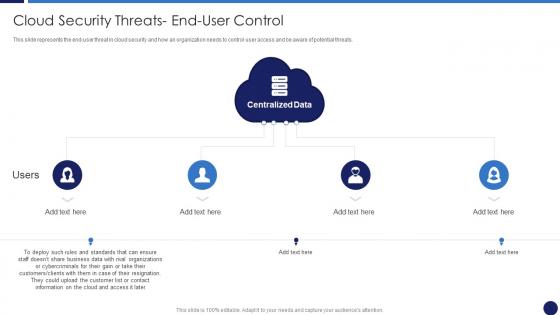 Cloud Security Threats End User Control Cloud Data Protection
Cloud Security Threats End User Control Cloud Data ProtectionThis slide represents the end-user threat in cloud security and how an organization needs to control user access and be aware of potential threats. Introducing Cloud Security Threats End User Control Cloud Data Protection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Business Data, Customers, Centralized Data, using this template. Grab it now to reap its full benefits.
-
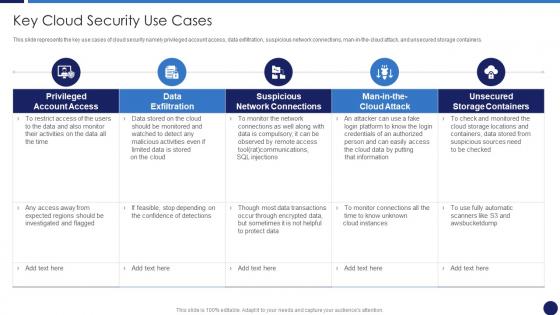 Key Cloud Security Use Cases Cloud Data Protection
Key Cloud Security Use Cases Cloud Data ProtectionThis slide represents the key use cases of cloud security namely privileged account access, data exfiltration, suspicious network connections, man-in-the-cloud attack, and unsecured storage containers. Present the topic in a bit more detail with this Key Cloud Security Use Cases Cloud Data Protection. Use it as a tool for discussion and navigation on Suspicious Network Connections, Data Exfiltration, Unsecured Storage Containers. This template is free to edit as deemed fit for your organization. Therefore download it now
-
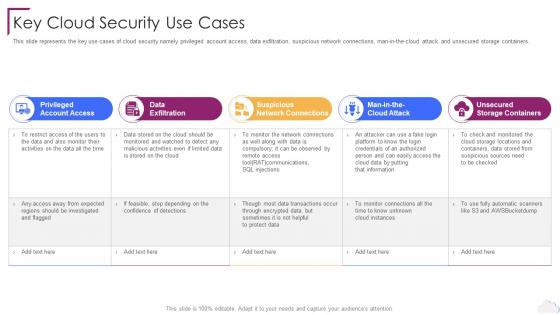 Cloud Computing Security Key Cloud Security Use Cases Ppt Background
Cloud Computing Security Key Cloud Security Use Cases Ppt BackgroundThis slide represents the key use cases of cloud security namely privileged account access, data exfiltration, suspicious network connections, man in the cloud attack, and unsecured storage containers. Increase audience engagement and knowledge by dispensing information using Cloud Computing Security Key Cloud Security Use Cases Ppt Background. This template helps you present information on five stages. You can also present information on Privileged Account Access, Data Exfiltration, Suspicious Network Connections, Unsecured Storage Containers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cloud Computing Security Tools Used In Cloud Security Ppt Infographics
Cloud Computing Security Tools Used In Cloud Security Ppt InfographicsThis slide represents the list of tools utilized under cloud security systems to protect, manage, store and control data on the cloud. Increase audience engagement and knowledge by dispensing information using Cloud Computing Security Tools Used In Cloud Security Ppt Infographics. This template helps you present information on ten stages. You can also present information on Cloud Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
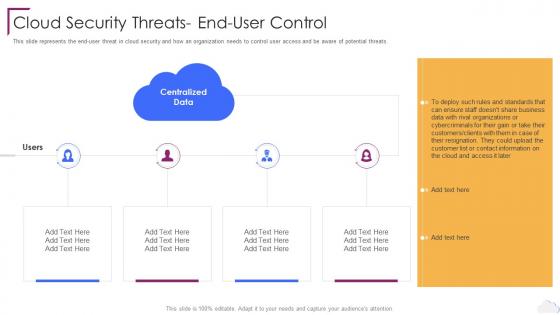 Cloud Security Threats End User Control Cloud Computing Security
Cloud Security Threats End User Control Cloud Computing SecurityThis slide represents the end user threat in cloud security and how an organization needs to control user access and be aware of potential threats. Introducing Cloud Security Threats End User Control Cloud Computing Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Centralized Data, Cloud Security Threats, End User Control, using this template. Grab it now to reap its full benefits.
-
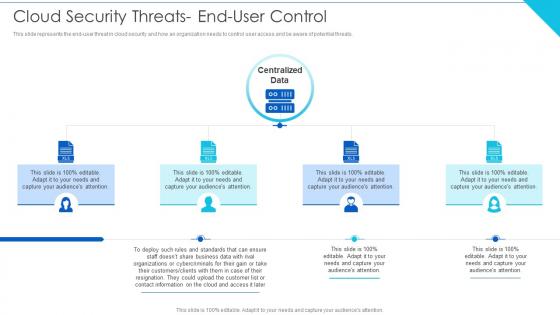 Cloud Security Threats End User Control Cloud Information Security
Cloud Security Threats End User Control Cloud Information SecurityThis slide represents the end user threat in cloud security and how an organization needs to control user access and be aware of potential threats.Introducing Cloud Security Threats End User Control Cloud Information Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Wisely Considering, Storage Location, Procedures Strategies using this template. Grab it now to reap its full benefits.
-
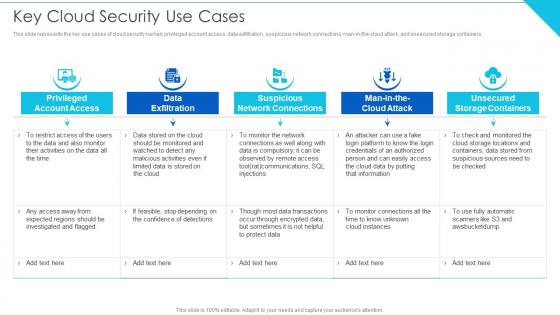 Key Cloud Security Use Cases Cloud Information Security
Key Cloud Security Use Cases Cloud Information SecurityThis slide represents the key use cases of cloud security namely privileged account access, data exfiltration, suspicious network connections, man in the cloud attack, and unsecured storage containers.Present the topic in a bit more detail with this Key Cloud Security Use Cases Cloud Information Security Use it as a tool for discussion and navigation on Review Specifications, Discover Malicious, Vulnerabilities This template is free to edit as deemed fit for your organization. Therefore download it now.
-
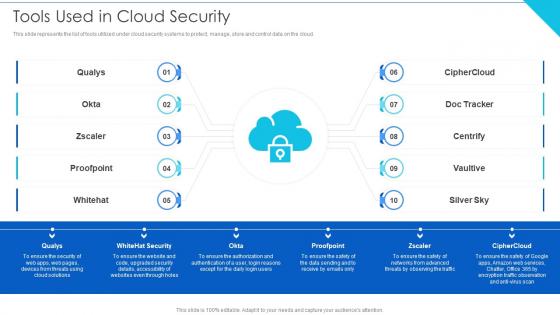 Tools Used In Cloud Security Cloud Information Security
Tools Used In Cloud Security Cloud Information SecurityThis slide represents the list of tools utilized under cloud security systems to protect, manage, store and control data on the cloud.Introducing Tools Used In Cloud Security Cloud Information Security to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Security, Access Control, Threat Detection using this template. Grab it now to reap its full benefits.
-
 About Us It Consulting Firm Introduction Cloud Architecture And Security Review
About Us It Consulting Firm Introduction Cloud Architecture And Security ReviewThis slide covers the introduction for IT consultancy firm including a brief about company and the major clients they have captured. Present the topic in a bit more detail with this About Us It Consulting Firm Introduction Cloud Architecture And Security Review. Use it as a tool for discussion and navigation on Meeting And Surpassing, Reviewing And Evaluating, Return On Investment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
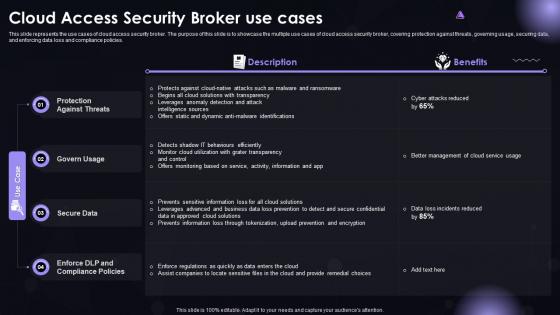 SASE IT Cloud Access Security Broker Use Cases Ppt Powerpoint Diagrams
SASE IT Cloud Access Security Broker Use Cases Ppt Powerpoint DiagramsThis slide represents the use cases of cloud access security broker. The purpose of this slide is to showcase the multiple use cases of cloud access security broker, covering protection against threats, governing usage, securing data, and enforcing data loss and compliance policies. Present the topic in a bit more detail with this SASE IT Cloud Access Security Broker Use Cases Ppt Powerpoint Diagrams. Use it as a tool for discussion and navigation on Protection Against Threats, Govern Usage, Secure Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
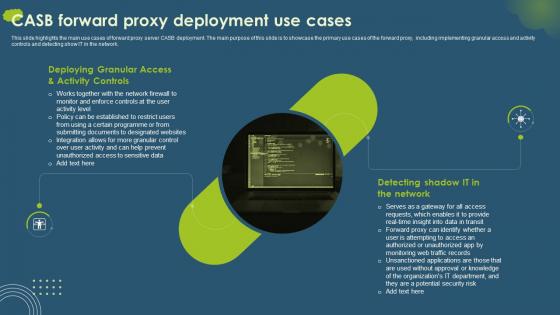 CASB Forward Proxy Deployment Use Cases Cloud Access Security Broker CASB
CASB Forward Proxy Deployment Use Cases Cloud Access Security Broker CASBThis slide highlights the main use cases of forward proxy server CASB deployment. The main purpose of this slide is to showcase the primary use cases of the forward proxy, including implementing granular access and activity controls and detecting show IT in the network. Increase audience engagement and knowledge by dispensing information using CASB Forward Proxy Deployment Use Cases Cloud Access Security Broker CASB. This template helps you present information on two stages. You can also present information on Deploying Granular, Detecting Shadow, Activity Controls using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
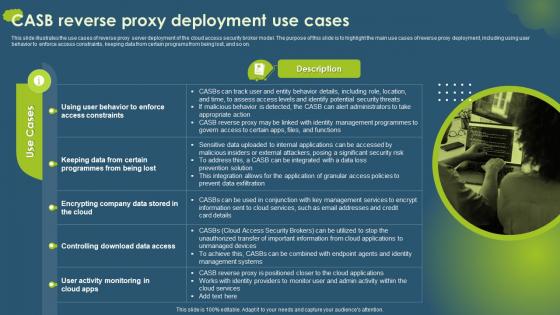 CASB Reverse Proxy Deployment Use Cases Cloud Access Security Broker CASB
CASB Reverse Proxy Deployment Use Cases Cloud Access Security Broker CASBThis slide illustrates the use cases of reverse proxy server deployment of the cloud access security broker model. The purpose of this slide is to highlight the main use cases of reverse proxy deployment, including using user behavior to enforce access constraints, keeping data from certain programs from being lost, and so on. Introducing CASB Reverse Proxy Deployment Use Cases Cloud Access Security Broker CASB. to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Use Cases, Description, Access Constraints, using this template. Grab it now to reap its full benefits.
-
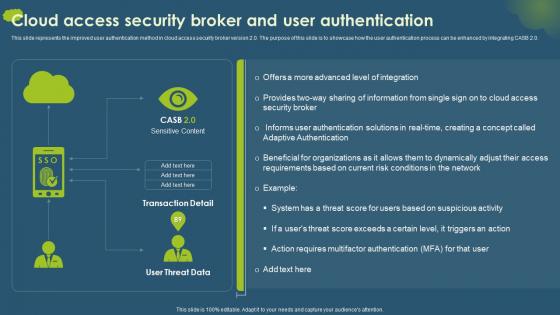 Cloud Access Security Broker And User Authentication Ppt Ideas Infographic Template
Cloud Access Security Broker And User Authentication Ppt Ideas Infographic TemplateThis slide represents the improved user authentication method in cloud access security broker version 2.0. The purpose of this slide is to showcase how the user authentication process can be enhanced by integrating CASB 2.0. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker And User Authentication Ppt Ideas Infographic Template. Dispense information and present a thorough explanation of Sensitive Content, Transaction Detail, User Threat Data using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
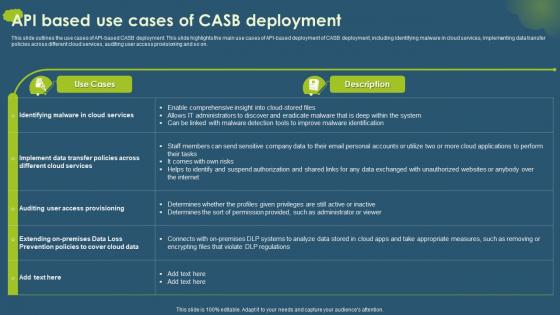 Cloud Access Security Broker CASB API Based Use Cases Of CASB Deployment
Cloud Access Security Broker CASB API Based Use Cases Of CASB DeploymentThis slide outlines the use cases of API based CASB deployment. This slide highlights the main use cases of API based deployment of CASB deployment, including identifying malware in cloud services, implementing data transfer policies across different cloud services, auditing user access provisioning and so on. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB API Based Use Cases Of CASB Deployment. Dispense information and present a thorough explanation of Use Cases, Description, Casb Deployment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
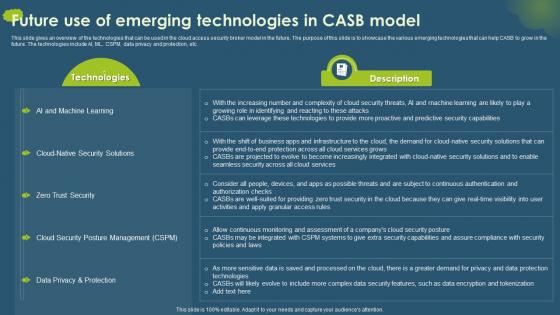 Cloud Access Security Broker CASB Future Use Of Emerging Technologies In CASB Model
Cloud Access Security Broker CASB Future Use Of Emerging Technologies In CASB ModelThis slide gives an overview of the technologies that can be used in the cloud access security broker model in the future. The purpose of this slide is to showcase the various emerging technologies that can help CASB to grow in the future. The technologies include AI, ML, CSPM, data privacy and protection, etc. Present the topic in a bit more detail with this Cloud Access Security Broker CASB Future Use Of Emerging Technologies In CASB Model. Use it as a tool for discussion and navigation on Technologies, Description, Zero Trust Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
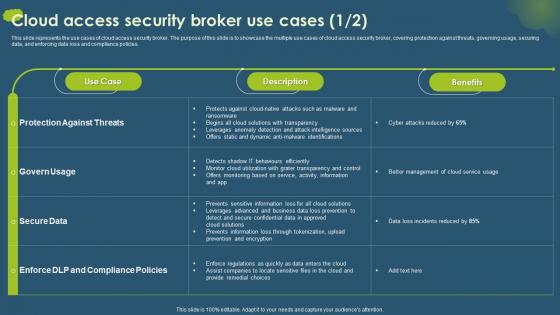 Cloud Access Security Broker Use Cases Ppt Styles Master Slide
Cloud Access Security Broker Use Cases Ppt Styles Master SlideThis slide represents the use cases of cloud access security broker. The purpose of this slide is to showcase the multiple use cases of cloud access security broker, covering protection against threats, governing usage, securing data, and enforcing data loss and compliance policies. Present the topic in a bit more detail with this Cloud Access Security Broker Use Cases Ppt Styles Master Slide. Use it as a tool for discussion and navigation on Use Case, Description, Benefits. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
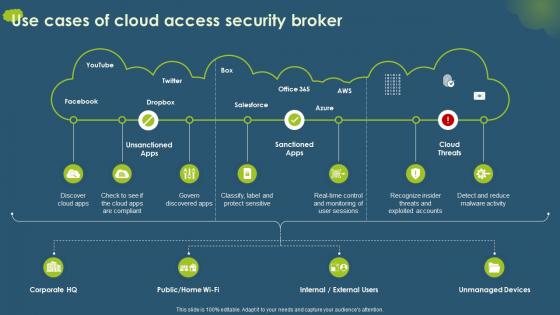 Use Cases Of Cloud Access Security Broker Ppt Ideas Influencers
Use Cases Of Cloud Access Security Broker Ppt Ideas InfluencersPresent the topic in a bit more detail with this Use Cases Of Cloud Access Security Broker Ppt Ideas Influencers. Use it as a tool for discussion and navigation on Unsanctioned Apps, Sanctioned Apps, Cloud Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Determine your cloud journey with us secure ppt layouts format ideas
Determine your cloud journey with us secure ppt layouts format ideasThis slide covers the steps considered by our company such as exit the data center determine the right cloud strategy, secure everything outsource IT management control IT spend and modernize application etc. Presenting this set of slides with name Determine Your Cloud Journey With Us Secure Ppt Layouts Format Ideas. This is a six stage process. The stages in this process are Exit The Data Center, Determine Right Cloud Strategy, Secure Everything, Modernize Applications, Outsource IT Management. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Cloud service providers determine your cloud journey with us secure everything ppt portfolio
Cloud service providers determine your cloud journey with us secure everything ppt portfolioThis slide covers the steps considered by our company such as exit the data center, determine the right cloud strategy, secure everything, outsource IT management, control IT spend, and modernize application, etc. Presenting this set of slides with name Cloud Service Providers Determine Your Cloud Journey With Us Secure Everything Ppt Portfolio. The topics discussed in these slides are Determine Cloud, Journey, Secure Everything. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
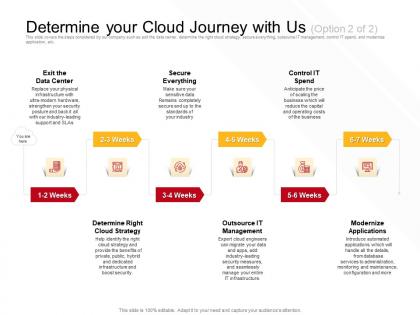 Determine your cloud journey with us boost security ppt powerpoint presentation portfolio
Determine your cloud journey with us boost security ppt powerpoint presentation portfolioThis slide covers the steps considered by our company such as exit the data center, determine the right cloud strategy, secure everything, outsource IT management, control IT spend, and modernize application, etc. Presenting this set of slides with name Determine Your Cloud Journey With Us Boost Security Ppt Powerpoint Presentation Portfolio. This is a six stage process. The stages in this process are Data Center, Management, Applications, Cloud Strategy, Secure Everything. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Cloud security monitoring use cases ppt powerpoint presentation slides example cpb
Cloud security monitoring use cases ppt powerpoint presentation slides example cpbPresenting this set of slides with name Cloud Security Monitoring Use Cases Ppt Powerpoint Presentation Slides Example Cpb. This is an editable Powerpoint graphic that deals with topics like Cloud Security Monitoring Use Cases to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cloud security threats end user control cloud security it ppt graphics
Cloud security threats end user control cloud security it ppt graphicsThis slide represents the end-user threat in cloud security and how an organization needs to control user access and be aware of potential threats.Increase audience engagement and knowledge by dispensing information using Cloud Security Threats End user Control Cloud Security IT Ppt Graphics. This template helps you present information on four stages. You can also present information on Organizations Or Cybercriminals, Contact Information, Rules And Standards using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
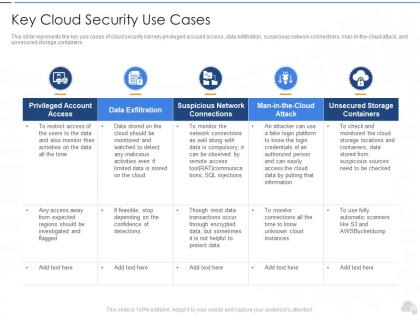 Key cloud security use cases cloud security it ppt summary
Key cloud security use cases cloud security it ppt summaryThis slide represents the key use cases of cloud security namely privileged account access, data exfiltration, suspicious network connections, man-in-the-cloud attack, and unsecured storage containers.Deliver an outstanding presentation on the topic using this Key Cloud Security Use Cases Cloud Security IT Ppt Summary. Dispense information and present a thorough explanation of Privileged Account Access, Data Exfiltration, Suspicious Network Connections using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
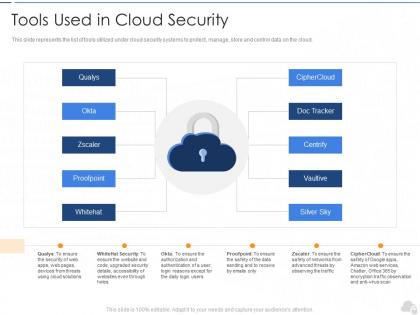 Tools used in cloud security cloud security it ppt inspiration
Tools used in cloud security cloud security it ppt inspirationThis slide represents the list of tools utilized under cloud security systems to protect, manage, store and control data on the cloud.Introducing Tools Used In Cloud Security Cloud Security It Ppt Inspiration to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Tools Used In Cloud Security, using this template. Grab it now to reap its full benefits.

