Powerpoint Templates and Google slides for Cyber Attack For Sensitive
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Action Plan To Combat Cyber Crimes Dashboard For Tracking Cyber Attack Risk Levels
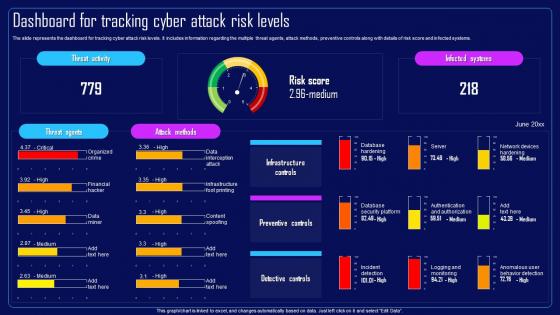
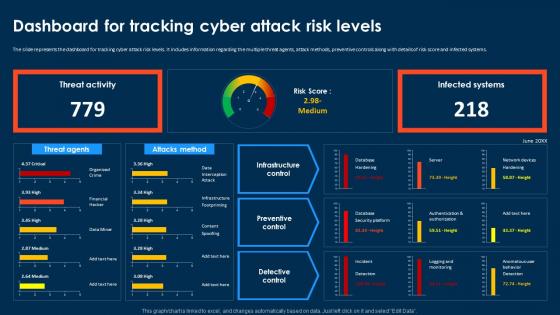
Action Plan To Combat Cyber Crimes Dashboard For Tracking Cyber Attack Risk LevelsThe slide represents the dashboard for tracking cyber attack risk levels. It includes information regarding the multiple threat agents, attack methods, preventive controls along with details of risk score and infected systems. Deliver an outstanding presentation on the topic using this Action Plan To Combat Cyber Crimes Dashboard For Tracking Cyber Attack Risk Levels. Dispense information and present a thorough explanation of Dashboard For Tracking, Cyber Attack Risk Levels, Risk Score And Infected Systems, Preventive Controls using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Compressive Planning Guide Dashboard For Tracking Cyber Attack Risk Levels
Compressive Planning Guide Dashboard For Tracking Cyber Attack Risk LevelsThe slide represents the dashboard for tracking cyber attack risk levels. It includes information regarding the multiple threat agents, attack methods, preventive controls along with details of risk score and infected systems. Deliver an outstanding presentation on the topic using this Compressive Planning Guide Dashboard For Tracking Cyber Attack Risk Levels. Dispense information and present a thorough explanation of Dashboard For Tracking, Cyber Attack Risk Levels, Preventive Controls, Risk Score And Infected Systems using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security Plan To Prevent Cyber Dashboard For Tracking Cyber Attack Risk Levels
Security Plan To Prevent Cyber Dashboard For Tracking Cyber Attack Risk LevelsThe slide represents the dashboard for tracking cyber attack risk levels. It includes information regarding the multiple threat agents, attack methods, preventive controls along with details of risk score and infected systems. Present the topic in a bit more detail with this Security Plan To Prevent Cyber Dashboard For Tracking Cyber Attack Risk Levels. Use it as a tool for discussion and navigation on Infrastructure Controls, Preventive Controls, Detective Controls. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Agenda For Security Plan To Prevent Cyber Attacks Ppt Icon Design Inspiration
Agenda For Security Plan To Prevent Cyber Attacks Ppt Icon Design InspirationIntroducing Agenda For Security Plan To Prevent Cyber Attacks Ppt Icon Design Inspiration to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Risk Assessment, Attacks Frequency, Assessment Program For Organization, using this template. Grab it now to reap its full benefits.
-
 Table Of Contents For Security Plan To Prevent Cyber Attacks
Table Of Contents For Security Plan To Prevent Cyber AttacksIntroducing Table Of Contents For Security Plan To Prevent Cyber Attacks to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Cybersecurity Risk Assessment Program, Cyber Attacks Identification, Cyber Attacks Faced By Organization, Cyber Attacks Risk Assessment, using this template. Grab it now to reap its full benefits.
-
 Prevention Techniques For Cyber Security Data Attacks
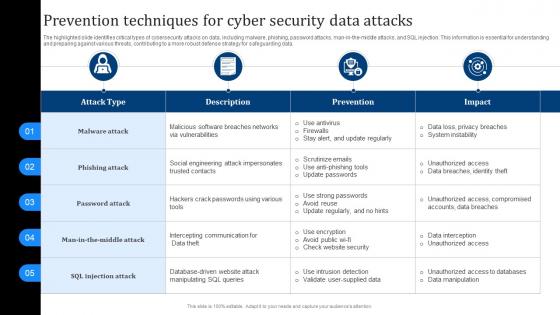
Prevention Techniques For Cyber Security Data AttacksThe highlighted slide identifies critical types of cybersecurity attacks on data, including malware, phishing, password attacks, man in the middle attacks, and SQL injection. This information is essential for understanding and preparing against various threats, contributing to a more robust defense strategy for safeguarding data. Introducing our Prevention Techniques For Cyber Security Data Attacks set of slides. The topics discussed in these slides are Malware Attack, Phishing Attack, Password Attack. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Types Of Cyber Attacks Faced By Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Types Of Cyber Attacks Faced By Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various types of cyber attacks that significantly damage the organization resources and reputation. Different types of attacks faced are Malware, Phishing, Man in middle attack, SQL injection etc. Increase audience engagement and knowledge by dispensing information using Types Of Cyber Attacks Faced By Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. This template helps you present information on five stages. You can also present information on Phishing, SQL Injection, Organization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Threats In Blockchain Methods To Avoid Sybil Attack For Protecting Tokens BCT SS V
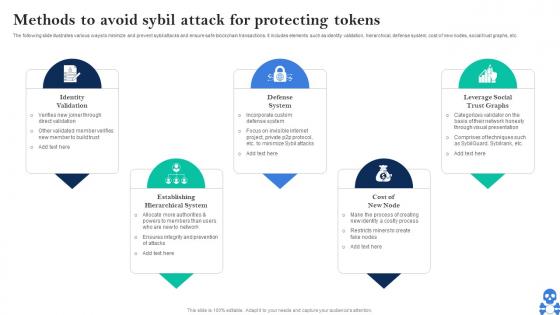
Cyber Threats In Blockchain Methods To Avoid Sybil Attack For Protecting Tokens BCT SS VThe following slide illustrates various ways to minimize and prevent sybil attacks and ensure safe blockchain transactions. It includes elements such as identity validation, hierarchical, defense system, cost of new nodes, social trust graphs, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Methods To Avoid Sybil Attack For Protecting Tokens BCT SS V This template helps you present information on Five stages. You can also present information on Identity Validation, Defense System, Cost Of New Node using this PPT design. This layout is completely editable so personaize it now
-
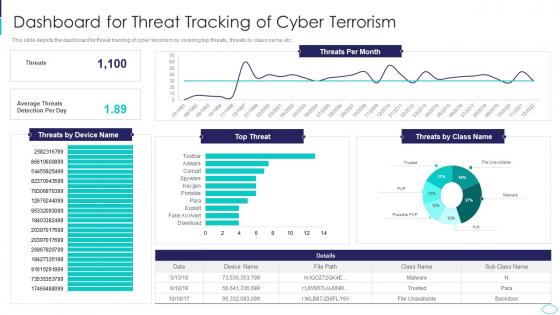 Dashboard For Threat Tracking Cyber Terrorism Attacks
Dashboard For Threat Tracking Cyber Terrorism AttacksThis slide depicts the dashboard for threat tracking of cyber terrorism by covering top threats, threats by class name, etc. Deliver an outstanding presentation on the topic using this Dashboard For Threat Tracking Cyber Terrorism Attacks. Dispense information and present a thorough explanation of Dashboard For Threat Tracking Of Cyber Terrorism using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
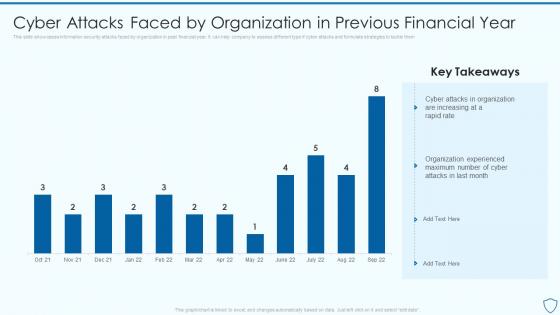 Cyber Attacks Faced By Organization In Risk Assessment And Management Plan For Information Security
Cyber Attacks Faced By Organization In Risk Assessment And Management Plan For Information SecurityThis slide showcases information security attacks faced by organization in past financial year. It can help company to assess different type if cyber attacks and formulate strategies to tackle them Present the topic in a bit more detail with this Cyber Attacks Faced By Organization In Risk Assessment And Management Plan For Information Security. Use it as a tool for discussion and navigation on Experienced, Organization, Financial. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
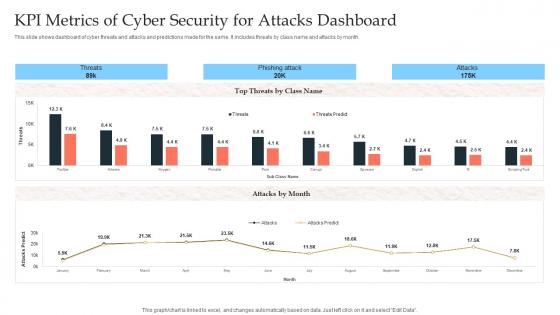 KPI Metrics Of Cyber Security For Attacks Dashboard
KPI Metrics Of Cyber Security For Attacks DashboardThis slide shows dashboard of cyber threats and attacks and predictions made for the same. It includes threats by class name and attacks by month. Introducing our KPI Metrics Of Cyber Security For Attacks Dashboard set of slides. The topics discussed in these slides are KPI Metrics, Cyber Security, Attacks Dashboard. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
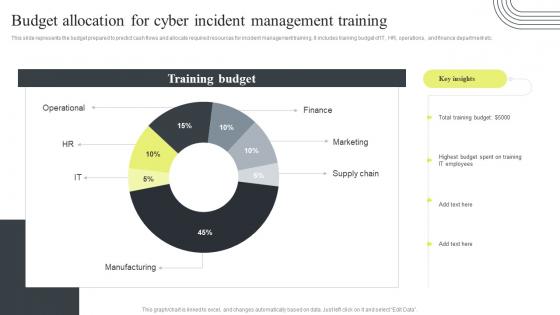 Cyber Security Attacks Response Plan Budget Allocation For Cyber Incident Management Training
Cyber Security Attacks Response Plan Budget Allocation For Cyber Incident Management TrainingThis slide represents the budget prepared to predict cash flows and allocate required resources for incident management training. It includes training budget of IT, HR, operations, and finance department etc. Deliver an outstanding presentation on the topic using this Cyber Security Attacks Response Plan Budget Allocation For Cyber Incident Management Training. Dispense information and present a thorough explanation of Budget Allocation, Cyber Incident Management, Training using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cybersecurity Risk Assessment Program Dashboard For Tracking Cyber Attack Risk Levels
Cybersecurity Risk Assessment Program Dashboard For Tracking Cyber Attack Risk LevelsThe slide represents the dashboard for tracking cyber attack risk levels. It includes information regarding the multiple threat agents, attack methods, preventive controls along with details of risk score and infected systems. Deliver an outstanding presentation on the topic using this Cybersecurity Risk Assessment Program Dashboard For Tracking Cyber Attack Risk Levels. Dispense information and present a thorough explanation of Infrastructure Controls, Preventive Controls, Detective Controls using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
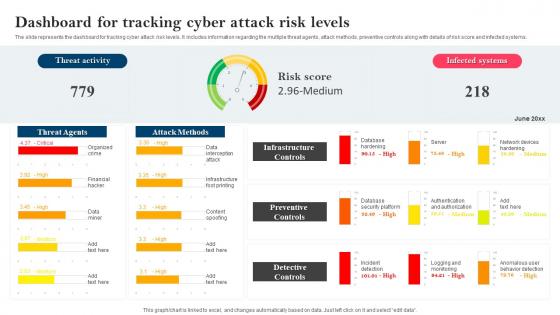 Strategy To Minimize Cyber Attacks Dashboard For Tracking Cyber Attack Risk Levels
Strategy To Minimize Cyber Attacks Dashboard For Tracking Cyber Attack Risk LevelsThe slide represents the dashboard for tracking cyber attack risk levels. It includes information regarding the multiple threat agents, attack methods, preventive controls along with details of risk score and infected systems. Present the topic in a bit more detail with this Strategy To Minimize Cyber Attacks Dashboard For Tracking Cyber Attack Risk Levels. Use it as a tool for discussion and navigation on Dashboard For Tracking, Cyber Attack Risk Levels, Infrastructure Controls, Preventive Controls, Detective Controls. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
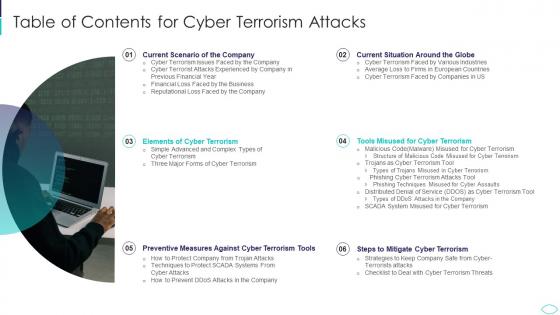 A56 Table Of Contents For Cyber Terrorism Attacks Ppt Slides Guidelines
A56 Table Of Contents For Cyber Terrorism Attacks Ppt Slides GuidelinesIntroducing A56 Table Of Contents For Cyber Terrorism Attacks Ppt Slides Guidelines to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Current Situation, Mitigate, Terrorism Tools, Cyber Terrorism, using this template. Grab it now to reap its full benefits.
-
 Agenda For Cyber Terrorism Attacks Ppt Slides Introduction
Agenda For Cyber Terrorism Attacks Ppt Slides IntroductionIncrease audience engagement and knowledge by dispensing information using Agenda For Cyber Terrorism Attacks Ppt Slides Introduction. This template helps you present information on five stages. You can also present information on Situation, Terrorism, Measures, Prevention, Demonstrate using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
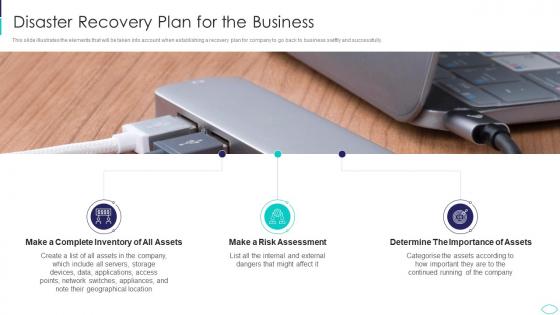 Disaster Recovery Plan For The Business Cyber Terrorism Attacks
Disaster Recovery Plan For The Business Cyber Terrorism AttacksThis slide illustrates the elements that will be taken into account when establishing a recovery plan for company to go back to business swiftly and successfully. Increase audience engagement and knowledge by dispensing information using Disaster Recovery Plan For The Business Cyber Terrorism Attacks. This template helps you present information on three stages. You can also present information on Inventory, Assets, Assessment, Importance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons Slide For Cyber Terrorism Attacks Ppt Slides Background Designs
Icons Slide For Cyber Terrorism Attacks Ppt Slides Background DesignsPresenting our well crafted Icons Slide For Cyber Terrorism Attacks Ppt Slides Background Designs set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly.
-
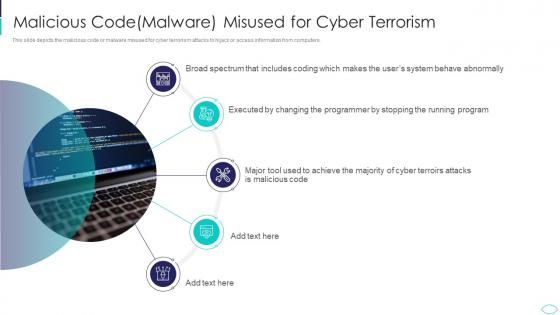 Malicious Codemalware Misused For Cyber Terrorism Cyber Terrorism Attacks
Malicious Codemalware Misused For Cyber Terrorism Cyber Terrorism AttacksThis slide depicts the malicious code or malware misused for cyber terrorism attacks to hijack or access information from computers. Increase audience engagement and knowledge by dispensing information using Malicious Codemalware Misused For Cyber Terrorism Cyber Terrorism Attacks. This template helps you present information on five stages. You can also present information on Malicious Code Malware Misused For Cyber Terrorism using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
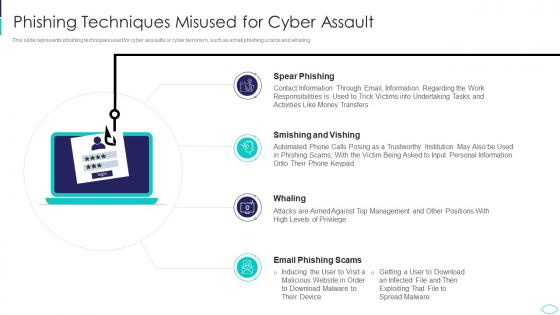 Phishing Techniques Misused For Cyber Assault Cyber Terrorism Attacks
Phishing Techniques Misused For Cyber Assault Cyber Terrorism AttacksThis slide represents phishing techniques used for cyber assaults or cyber terrorism, such as email phishing scams and whaling. Introducing Phishing Techniques Misused For Cyber Assault Cyber Terrorism Attacks to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Phishing Techniques Misused For Cyber Assault, using this template. Grab it now to reap its full benefits.
-
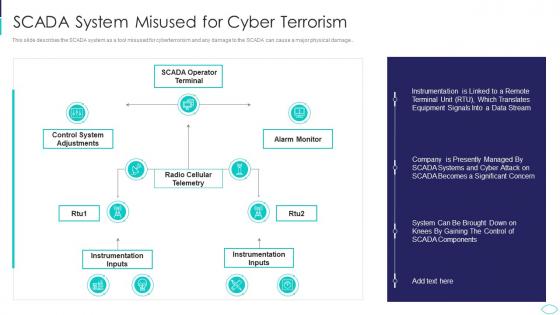 SCADA System Misused For Cyber Terrorism Cyber Terrorism Attacks
SCADA System Misused For Cyber Terrorism Cyber Terrorism AttacksThis slide describes the SCADA system as a tool misused for cyberterrorism and any damage to the SCADA can cause a major physical damage.. Present the topic in a bit more detail with this SCADA System Misused For Cyber Terrorism Cyber Terrorism Attacks. Use it as a tool for discussion and navigation on Scada System Misused For Cyber Terrorism. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table Of Contents For Cyber Terrorism Attacks Mitigate
Table Of Contents For Cyber Terrorism Attacks MitigateIntroducing Table Of Contents For Cyber Terrorism Attacks Mitigate to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Assessment Matrix, Security Budget, Security Measures, using this template. Grab it now to reap its full benefits.
-
 Three Major Forms Of Cyber Terrorism Attacks Ppt Slides Designs Download
Three Major Forms Of Cyber Terrorism Attacks Ppt Slides Designs DownloadThis slide describes the three major forms of cyber terrorism attacks such as privacy violation, networks damage, and disruptions, and distribution denial of service attack. Introducing Three Major Forms Of Cyber Terrorism Attacks Ppt Slides Designs Download to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Privacy Violation, Damage Disruptions, Distributed Denial, using this template. Grab it now to reap its full benefits.
-
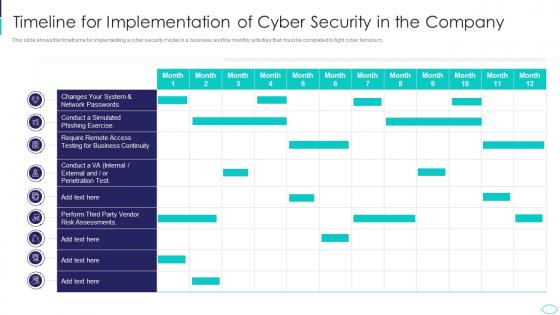 Timeline For Implementation Cyber Terrorism Attacks
Timeline For Implementation Cyber Terrorism AttacksThis slide shows the timeframe for implementing a cyber security model in a business and the monthly activities that must be completed to fight cyber terrorism. Deliver an outstanding presentation on the topic using this Timeline For Implementation Cyber Terrorism Attacks. Dispense information and present a thorough explanation of Timeline For Implementation Of Cyber Security In The Company using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Incident Response Plan For Attack
Cyber Security Incident Response Plan For AttackThe following slide highlights the cyber security incident response plan for attack illustrating objective, planning and action, which helps the management to take decision for risk mitigation strategy and allocation of budget and resources depending on criticality of cyber attack. Presenting our set of slides with name Cyber Security Incident Response Plan For Attack. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Objective, Planning, Action.
-
 Agenda For Cyber Attacks On Ukraine Ppt Slides Portfolio
Agenda For Cyber Attacks On Ukraine Ppt Slides PortfolioIntroducing Agenda For Cyber Attacks On Ukraine Ppt Slides Portfolio to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Reasons, Demonstrate, Technical, Analysis, Mitigate, Cyberattacks, using this template. Grab it now to reap its full benefits.
-
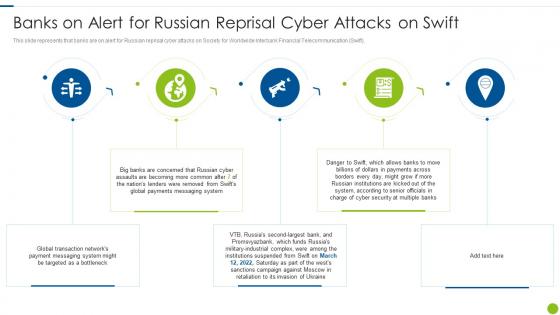 Cyber Attacks On Ukraine Banks On Alert For Russian Reprisal Cyber Attacks On Swift
Cyber Attacks On Ukraine Banks On Alert For Russian Reprisal Cyber Attacks On SwiftThis slide represents that banks are on alert for Russian reprisal cyber attacks on Society for Worldwide Interbank Financial Telecommunication Swift. Introducing Cyber Attacks On Ukraine Banks On Alert For Russian Reprisal Cyber Attacks On Swift to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Concerned, Lenders, Payments, Security, System, using this template. Grab it now to reap its full benefits.
-
 Cyber Attacks On Ukraine For The First Time In History Anyone Can Join A War
Cyber Attacks On Ukraine For The First Time In History Anyone Can Join A WarThis slide represents the official announcement from Lotte Finkelstein, head of threat intelligence at Check Point Software, that anyone can join Ukraine and Russia cyber warfare. Increase audience engagement and knowledge by dispensing information using Cyber Attacks On Ukraine For The First Time In History Anyone Can Join A War. This template helps you present information on six stages. You can also present information on Conflict Grows, Volunteers, Technologies, Cyberattacks, Organizations using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
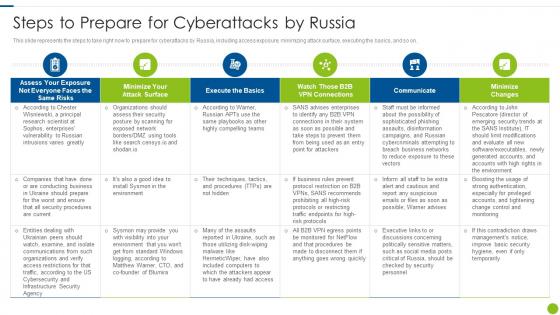 Cyber Attacks On Ukraine Steps To Prepare For Cyberattacks By Russia
Cyber Attacks On Ukraine Steps To Prepare For Cyberattacks By RussiaThis slide represents the steps to take right now to prepare for cyberattacks by Russia, including access exposure, minimizing attack surface, executing the basics, and so on. Deliver an outstanding presentation on the topic using this Cyber Attacks On Ukraine Steps To Prepare For Cyberattacks By Russia. Dispense information and present a thorough explanation of Steps To Prepare For Cyberattacks By Russia using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Icons Slide For Cyber Attacks On Ukraine Ppt Slides Background Image
Icons Slide For Cyber Attacks On Ukraine Ppt Slides Background ImageIntroducing our Icons Slide For Cyber Attacks On Ukraine Ppt Slides Background Image template to enhance your presentation. The slide displays eye catching icons that can be incorporated into any business presentation. Download it instantly and edit as per your knowledge.
-
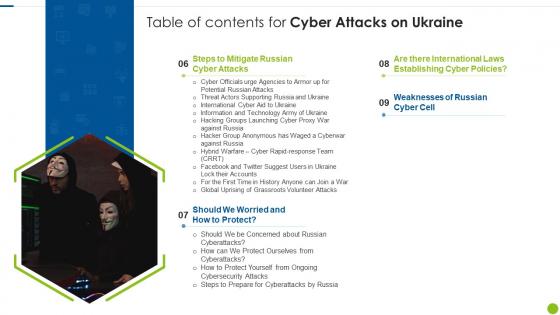 Table Of Contents For Cyber Attacks On Ukraine Ppt Slides Inspiration
Table Of Contents For Cyber Attacks On Ukraine Ppt Slides InspirationPresent the topic in a bit more detail with this Table Of Contents For Cyber Attacks On Ukraine Ppt Slides Inspiration. Use it as a tool for discussion and navigation on Protect, Cyber Attacks, Weaknesses, Establishing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
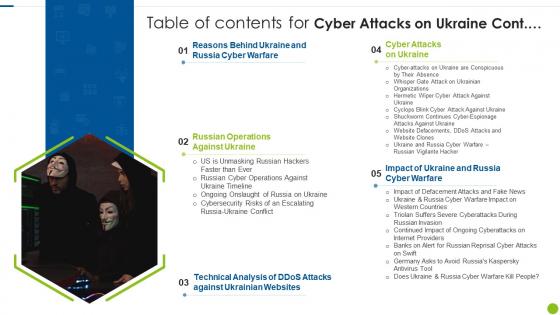 Table Of Contents For Cyber Attacks On Ukraine Technical
Table Of Contents For Cyber Attacks On Ukraine TechnicalDeliver an outstanding presentation on the topic using this Table Of Contents For Cyber Attacks On Ukraine Technical. Dispense information and present a thorough explanation of Cyber Warfare, Operations, Technical, Analysis using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Wiper Malware Attack Banks On Alert For Russian Reprisal Cyber Attacks On Swift
Wiper Malware Attack Banks On Alert For Russian Reprisal Cyber Attacks On SwiftThis slide represents that banks are on alert for Russian reprisal cyber attacks on Society for Worldwide Interbank Financial Telecommunication Swift. Introducing Wiper Malware Attack Banks On Alert For Russian Reprisal Cyber Attacks On Swift to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Transaction, Payment, Targeted, Payments, Institutions, using this template. Grab it now to reap its full benefits.
-
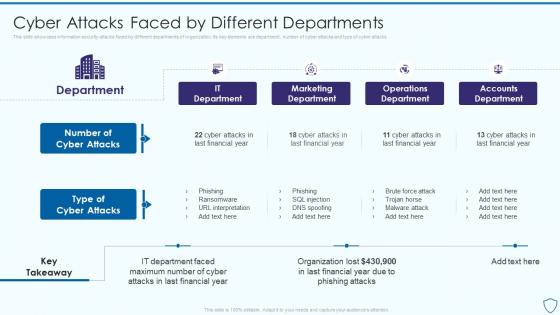 Risk Assessment And Management Plan For Information Security Cyber Attacks Faced By Different
Risk Assessment And Management Plan For Information Security Cyber Attacks Faced By DifferentThis slide showcase information security attacks faced by different departments of organization. Its key elements are department, number of cyber attacks and type of cyber attacks Deliver an outstanding presentation on the topic using this Risk Assessment And Management Plan For Information Security Cyber Attacks Faced By Different. Dispense information and present a thorough explanation of Marketing Department, Operations Department, Accounts Department using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Ukraine and russia cyber warfare it banks on alert for russian reprisal cyber attacks on swift
Ukraine and russia cyber warfare it banks on alert for russian reprisal cyber attacks on swiftThis slide represents that banks are on alert for Russian reprisal cyber attacks on Society for Worldwide Interbank Financial Telecommunication Swift. Deliver an outstanding presentation on the topic using this Ukraine And Russia Cyber Warfare It Banks On Alert For Russian Reprisal Cyber Attacks On Swift. Dispense information and present a thorough explanation of Banks On Alert For Russian Reprisal Cyber Attacks On Swift using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
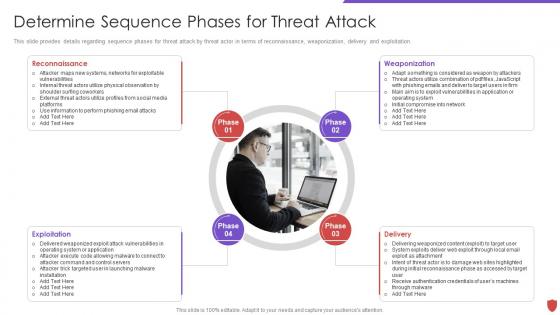 Cyber security risk management determine sequence phases for threat attack
Cyber security risk management determine sequence phases for threat attackThis slide provides details regarding sequence phases for threat attack by threat actor in terms of reconnaissance, weaponization, delivery and exploitation. Increase audience engagement and knowledge by dispensing information using Cyber Security Risk Management Determine Sequence Phases For Threat Attack. This template helps you present information on four stages. You can also present information on Reconnaissance, Weaponization, Exploitation, Delivery using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
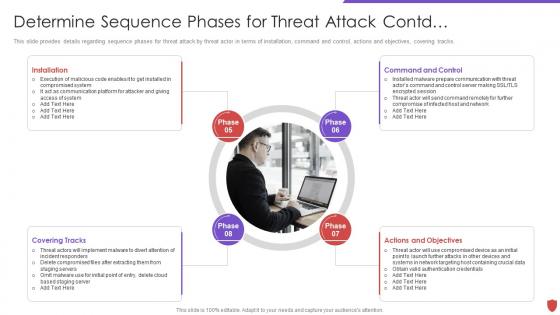 Determine sequence phases for threat attack contd cyber security risk management
Determine sequence phases for threat attack contd cyber security risk managementThis slide provides details regarding sequence phases for threat attack by threat actor in terms of installation, command and control, actions and objectives, covering tracks. Introducing Determine Sequence Phases For Threat Attack Contd Cyber Security Risk Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Installation, Command And Control, Actions And Objectives, Covering Tracks, using this template. Grab it now to reap its full benefits.
-
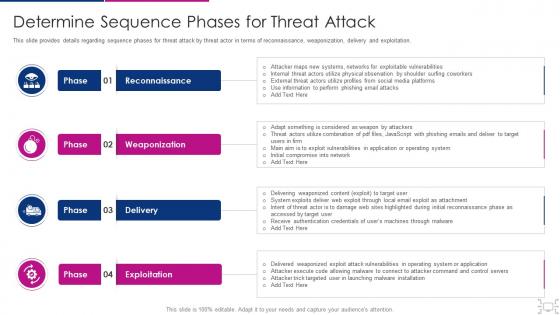 Cyber threat management workplace determine sequence phases for attack
Cyber threat management workplace determine sequence phases for attackThis slide provides details regarding sequence phases for threat attack by threat actor in terms of reconnaissance, weaponization, delivery and exploitation. Increase audience engagement and knowledge by dispensing information using Cyber Threat Management Workplace Determine Sequence Phases For Attack. This template helps you present information on four stages. You can also present information on Reconnaissance, Weaponization, Delivery, Exploitation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Agenda For Implementing Security Awareness Training To Prevent Cyber Attacks
Agenda For Implementing Security Awareness Training To Prevent Cyber AttacksIntroducing Agenda For Implementing Security Awareness Training To Prevent Cyber Attacks to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Awareness Campaign, Cyber Security, Awareness Training, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Implementing Security Awareness Training To Prevent Cyber Attacks
Icons Slide For Implementing Security Awareness Training To Prevent Cyber AttacksIntroducing our well researched set of slides titled Icons Slide For Implementing Security Awareness Training To Prevent Cyber Attacks. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
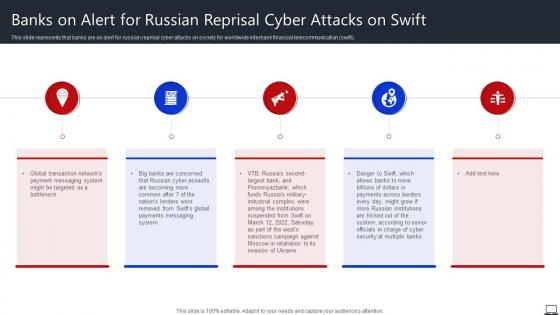 Banks On Alert For Russian Reprisal Cyber Attacks On Swift String Of Cyber Attacks
Banks On Alert For Russian Reprisal Cyber Attacks On Swift String Of Cyber AttacksThis slide represents that banks are on alert for russian reprisal cyber attacks on society for worldwide interbank financial telecommunication swift. Introducing Banks On Alert For Russian Reprisal Cyber Attacks On Swift String Of Cyber Attacks to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Global Transaction, Payment Messaging, Cyber Assaults, using this template. Grab it now to reap its full benefits.
-
 Cyber Officials Urge Agencies To Armor Up For Potential Russian Attacks String Of Cyber Attacks
Cyber Officials Urge Agencies To Armor Up For Potential Russian Attacks String Of Cyber AttacksThis slide represents that officials from the department of homeland security have urged agencies to prepare for possible russian cyberattacks, and CISA has amended its shields up guidelines. Increase audience engagement and knowledge by dispensing information using Cyber Officials Urge Agencies To Armor Up For Potential Russian Attacks String Of Cyber Attacks. This template helps you present information on five stages. You can also present information on Cyberattacks, Enterprises, Advising Managers, Cybersecurity using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons Slide For String Of Cyber Attacks Against Ukraine 2022
Icons Slide For String Of Cyber Attacks Against Ukraine 2022Introducing our well researched set of slides titled Icons Slide For String Of Cyber Attacks Against Ukraine 2022. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
 Steps To Prepare For Cyberattacks By Russia String Of Cyber Attacks Against Ukraine 2022
Steps To Prepare For Cyberattacks By Russia String Of Cyber Attacks Against Ukraine 2022This slide represents the steps to take right now to prepare for cyberattacks by russia, including access exposure, minimizing attack surface, executing the basics, and so on. Present the topic in a bit more detail with this Steps To Prepare For Cyberattacks By Russia String Of Cyber Attacks Against Ukraine 2022. Use it as a tool for discussion and navigation on Minimize Your Attack Surface, Execute The Basics, Communicate. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 General Outlook Of Ransomware Attack Developing Cyber Security Awareness Training Program For Staff
General Outlook Of Ransomware Attack Developing Cyber Security Awareness Training Program For StaffThe purpose of this slide is to outline an example of ransomware attack. The slide provides information about the working of ransomware attack work and how it can encrypts the victims data. Introducing General Outlook Of Ransomware Attack Developing Cyber Security Awareness Training Program For Staff to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Files Are Encrypted, Ransomware Works, General Outlook, using this template. Grab it now to reap its full benefits.
-
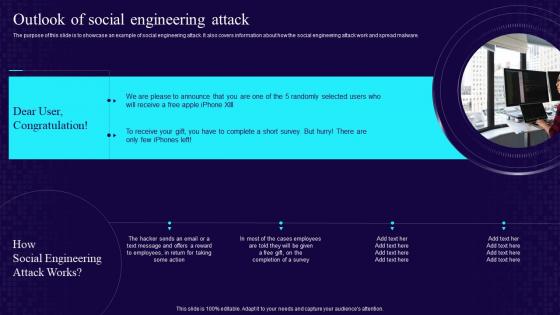 Outlook Of Social Engineering Attack Developing Cyber Security Awareness Training Program For Staff
Outlook Of Social Engineering Attack Developing Cyber Security Awareness Training Program For StaffThe purpose of this slide is to showcase an example of social engineering attack. It also covers information about how the social engineering attack work and spread malware. Increase audience engagement and knowledge by dispensing information using Outlook Of Social Engineering Attack Developing Cyber Security Awareness Training Program For Staff. This template helps you present information on one stages. You can also present information on Social Engineering, Attack Works, Completion Of A Survey using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Phishing Attack Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Cyber Phishing Attack Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Cyber phishing attack colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Cyber Phishing Attack Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Cyber Phishing Attack Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Cyber phishing attack monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
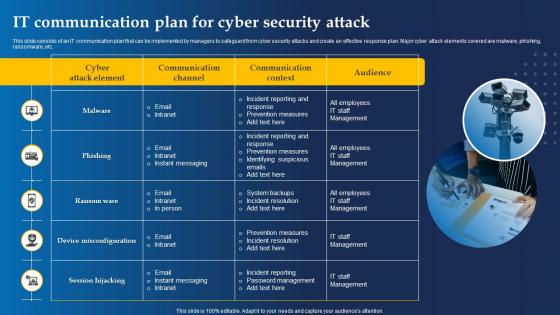 It Communication Plan For Cyber Security Attack
It Communication Plan For Cyber Security AttackThis slide consists of an IT communication plan that can be implemented by managers to safeguard from cyber security attacks and create an effective response plan. Major cyber attack elements covered are malware, phishing, ransomware, etc. Presenting our set of slides with It Communication Plan For Cyber Security Attack This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Malware, Phishing
-
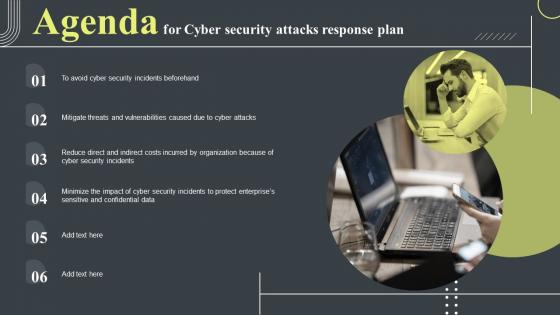 Agenda For Cyber Security Attacks Response Plan Ppt Infographic Template Background Images
Agenda For Cyber Security Attacks Response Plan Ppt Infographic Template Background ImagesIntroducing Agenda For Cyber Security Attacks Response Plan Ppt Infographic Template Background Images to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Cyber Security, Attacks Response Plan, Security Incidents, using this template. Grab it now to reap its full benefits.
-
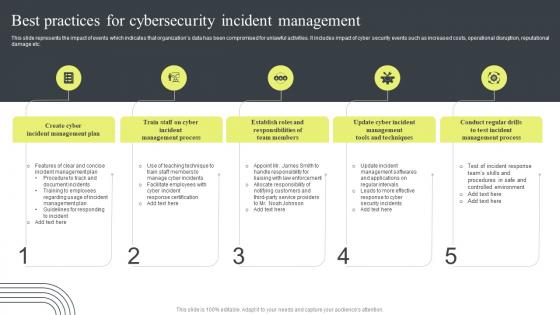 Cyber Security Attacks Response Plan Best Practices For Cybersecurity Incident Management
Cyber Security Attacks Response Plan Best Practices For Cybersecurity Incident ManagementThis slide represents the impact of events which indicates that organizations data has been compromised for unlawful activities. It includes impact of cyber security events such as increased costs, operational disruption, reputational damage etc. Introducing Cyber Security Attacks Response Plan Best Practices For Cybersecurity Incident Management to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Incident Management Process, Incident Management Plan, Responsibilities, Team Members, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Attacks Response Plan Cyber Security Attacks Response Plan For Table Of Contents
Cyber Security Attacks Response Plan Cyber Security Attacks Response Plan For Table Of ContentsIncrease audience engagement and knowledge by dispensing information using Cyber Security Attacks Response Plan Cyber Security Attacks Response Plan For Table Of Contents. This template helps you present information on one stages. You can also present information on Cyber Security Attacks, Response Plan, Incident Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons Slide For Cyber Security Attacks Response Plan Ppt Infographic Template Backgrounds
Icons Slide For Cyber Security Attacks Response Plan Ppt Infographic Template BackgroundsIntroducing our well researched set of slides titled Icons Slide For Cyber Security Attacks Response Plan Ppt Infographic Template Backgrounds. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
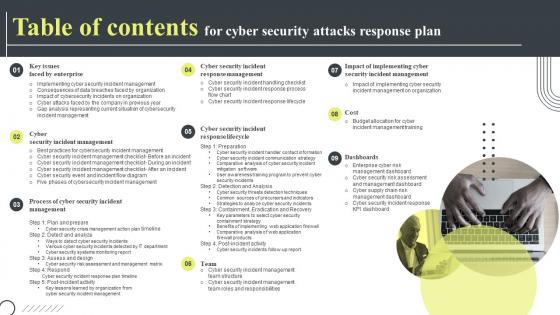 Table Of Contents For Cyber Security Attacks Response Plan Ppt Infographic Template Deck
Table Of Contents For Cyber Security Attacks Response Plan Ppt Infographic Template DeckIntroducing Table Of Contents For Cyber Security Attacks Response Plan Ppt Infographic Template Deck to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Dashboards, Cyber Security, Incident Management, Incident Response Management, using this template. Grab it now to reap its full benefits.
-
 Agenda For Strategy To Minimize Cyber Attacks Risks Ppt Icon Clipart Images
Agenda For Strategy To Minimize Cyber Attacks Risks Ppt Icon Clipart ImagesIntroducing Agenda For Strategy To Minimize Cyber Attacks Risks Ppt Icon Clipart Images to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Risk Assessment, Cyber Attacks Risks, Attacks Frequency, Cybersecurity Risk, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Strategy To Minimize Cyber Attacks Risks Ppt Icon Templates
Icons Slide For Strategy To Minimize Cyber Attacks Risks Ppt Icon TemplatesPresenting our premium Icons Slide For Strategy To Minimize Cyber Attacks Risks Ppt Icon Templates set of slides with flexible icons. The icons are designed by our group of professionals. Add these Icons Slide For Strategy To Minimize Cyber Attacks Risks Ppt Icon Templates to your presentation to make it visually appealing. Also, edit them according to your requirement. Download it and captive your audience.
-
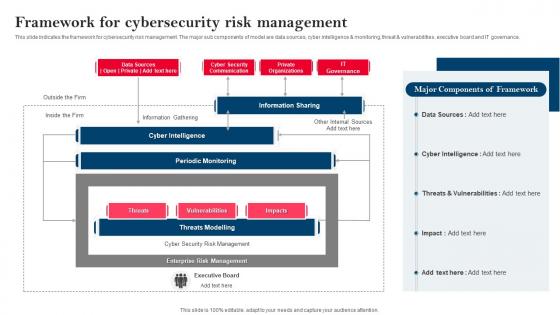 Strategy To Minimize Cyber Attacks Framework For Cybersecurity Risk Management
Strategy To Minimize Cyber Attacks Framework For Cybersecurity Risk ManagementThis slide indicates the framework for cybersecurity risk management. The major sub components of model are data sources, cyber intelligence and monitoring, threat and vulnerabilities, executive board and IT governance. Present the topic in a bit more detail with this Strategy To Minimize Cyber Attacks Framework For Cybersecurity Risk Management. Use it as a tool for discussion and navigation on Information Sharing, Components Of Framework, Framework For Cybersecurity, Risk Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Strategy To Minimize Cyber Attacks Need Of Cybersecurity Program For Organization
Strategy To Minimize Cyber Attacks Need Of Cybersecurity Program For OrganizationThis slide depicts the value that a cybersecurity program with risk assessment module add to organization in terms of increased awareness of organization security landscape, identification of system vulnerabilities, actionable and prioritized list of cybersecurity risks and mitigation plan to tackle future threats. Increase audience engagement and knowledge by dispensing information using Strategy To Minimize Cyber Attacks Need Of Cybersecurity Program For Organization. This template helps you present information on four stages. You can also present information on Organization Security Landscape, Actionable And Prioritized, List Of Cybersecurity Risks, Identification Of System Vulnerabilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Strategy To Minimize Cyber Attacks Risks For Table Of Content Ppt Icon Elements
Strategy To Minimize Cyber Attacks Risks For Table Of Content Ppt Icon ElementsIncrease audience engagement and knowledge by dispensing information using Strategy To Minimize Cyber Attacks Risks For Table Of Content Ppt Icon Elements. This template helps you present information on one stages. You can also present information on Cyber Attacks Risks, Cyber Attacks Risk Mitigation, Mitigation Plan using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table Of Contents For Strategy To Minimize Cyber Attacks Risks
Table Of Contents For Strategy To Minimize Cyber Attacks RisksIntroducing Table Of Contents For Strategy To Minimize Cyber Attacks Risks to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Cyber Attacks Faced By Organization, Risk Heatmap, Risk Register, Mitigation Plan, Cybersecurity Risk Assessment Program, using this template. Grab it now to reap its full benefits.


