Powerpoint Templates and Google slides for Cyber
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
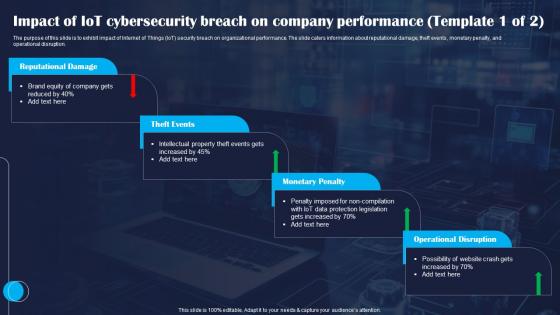 Impact Of IoT Cybersecurity Breach On Improving IoT Device Cybersecurity IoT SS
Impact Of IoT Cybersecurity Breach On Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to exhibit impact of Internet of Things IoT security breach on organizational performance. The slide caters information about reputational damage, theft events, monetary penalty, and operational disruption. Deliver an outstanding presentation on the topic using this Impact Of IoT Cybersecurity Breach On Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Reputational, Events, Penalty using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
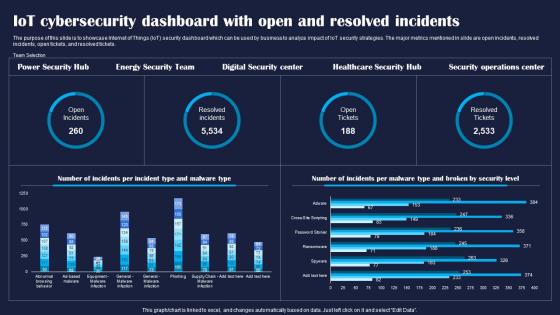 IoT Cybersecurity Dashboard With Open And Improving IoT Device Cybersecurity IoT SS
IoT Cybersecurity Dashboard With Open And Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase Internet of Things IoT security dashboard which can be used by business to analyze impact of IoT security strategies. The major metrics mentioned in slide are open incidents, resolved incidents, open tickets, and resolved tickets. Deliver an outstanding presentation on the topic using this IoT Cybersecurity Dashboard With Open And Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Cybersecurity, Resolved, Incidents using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
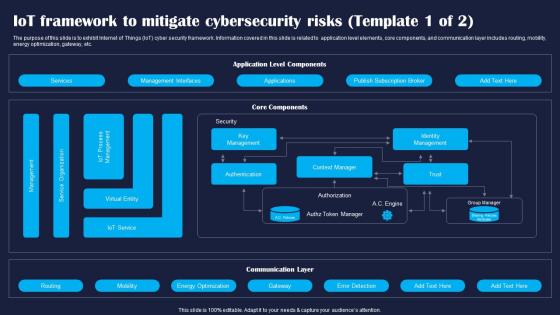 IoT Framework To Mitigate Cybersecurity Improving IoT Device Cybersecurity IoT SS
IoT Framework To Mitigate Cybersecurity Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to exhibit Internet of Things IoT cyber security framework. Information covered in this slide is related to application level elements, core components, and communication layer includes routing, mobility, energy optimization, gateway, etc. Present the topic in a bit more detail with this IoT Framework To Mitigate Cybersecurity Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Services, Management, Applications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IoT Password Attack Prevention Strategies Improving IoT Device Cybersecurity IoT SS
IoT Password Attack Prevention Strategies Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to highlight Internet of Things IoT password attack prevention measures. The techniques outlined in slide are limit public information, verifying the source, and no sharing of password. Deliver an outstanding presentation on the topic using this IoT Password Attack Prevention Strategies Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Information, Verify, Password using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 IoT Security Dashboard With User Improving IoT Device Cybersecurity IoT SS
IoT Security Dashboard With User Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to outline key performance indicator KPI metrics dashboard of IoT security. The major metrics mentioned in slide are alert severity, alert breakdown, entity breakdown, user notification, reset password, authentications request, etc. Present the topic in a bit more detail with this IoT Security Dashboard With User Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Security, Notifications, Notification. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
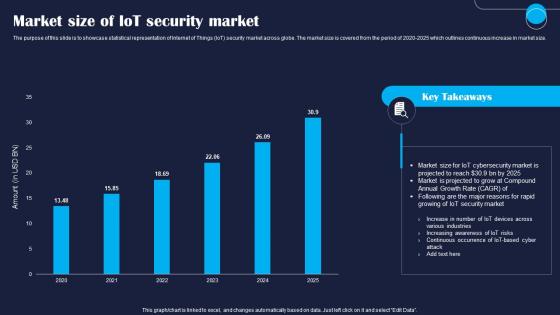 Market Size Of IoT Security Market Improving IoT Device Cybersecurity IoT SS
Market Size Of IoT Security Market Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase statistical representation of Internet of Things IoT security market across globe. The market size is covered from the period of 2020 2025 which outlines continuous increase in market size. Present the topic in a bit more detail with this Market Size Of IoT Security Market Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Market, Security, Market. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
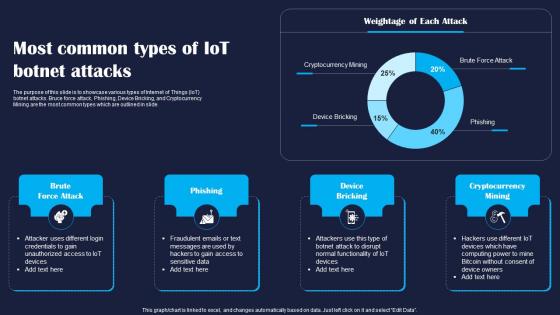 Most Common Types Of IoT Botnet Attacks Improving IoT Device Cybersecurity IoT SS
Most Common Types Of IoT Botnet Attacks Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase various types of Internet of Things IoT botnet attacks. Bruce force attack, Phishing, Device Bricking, and Cryptocurrency Mining are the most common types which are outlined in slide. Present the topic in a bit more detail with this Most Common Types Of IoT Botnet Attacks Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Phishing, Bricking, Mining. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
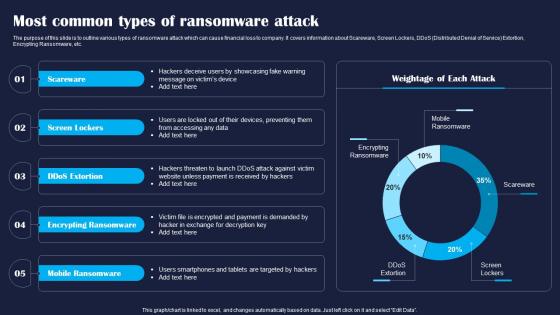 Most Common Types Of Ransomware Attack Improving IoT Device Cybersecurity IoT SS
Most Common Types Of Ransomware Attack Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to outline various types of ransomware attack which can cause financial loss to company. It covers information about Scareware, Screen Lockers, DDoS Distributed Denial of Service Extortion, Encrypting Ransomware, etc. Deliver an outstanding presentation on the topic using this Most Common Types Of Ransomware Attack Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Scareware, Lockers, Mobile using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
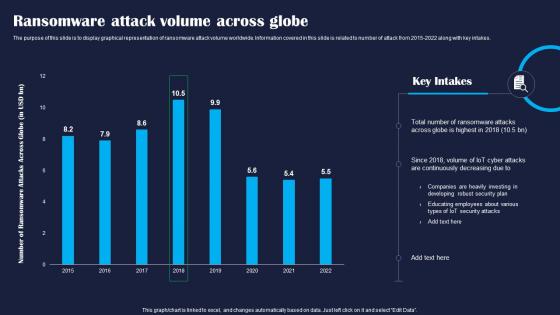 Ransomware Attack Volume Across Globe Improving IoT Device Cybersecurity IoT SS
Ransomware Attack Volume Across Globe Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to display graphical representation of ransomware attack volume worldwide. Information covered in this slide is related to number of attack from 2015 2022 along with key intakes. Deliver an outstanding presentation on the topic using this Ransomware Attack Volume Across Globe Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Globe, Attacks, Developing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
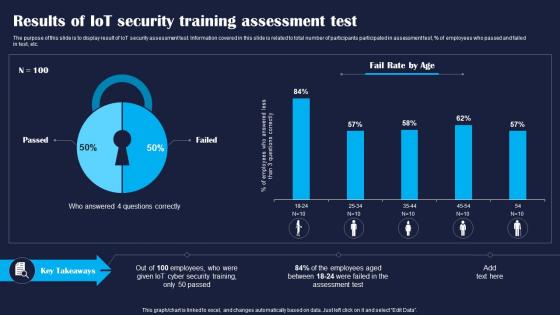 Results Of IoT Security Training Improving IoT Device Cybersecurity IoT SS
Results Of IoT Security Training Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to display result of IoT security assessment test. Information covered in this slide is related to total number of participants participated in assessment test, percentage of employees who passed and failed in test, etc. Present the topic in a bit more detail with this Results Of IoT Security Training Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Assessment, Training, Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
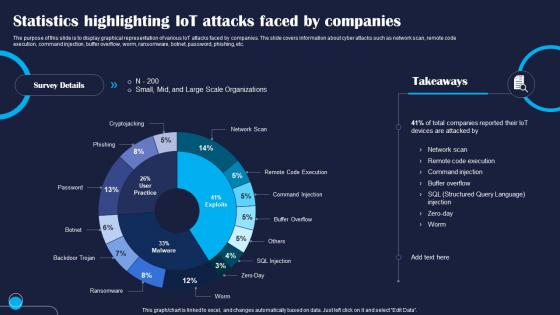 Statistics Highlighting IoT Attacks Faced Improving IoT Device Cybersecurity IoT SS
Statistics Highlighting IoT Attacks Faced Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to display graphical representation of various IoT attacks faced by companies. The slide covers information about cyber attacks such as network scan, remote code execution, command injection, buffer overflow, worm, ransomware, botnet, password, phishing, etc. Present the topic in a bit more detail with this Statistics Highlighting IoT Attacks Faced Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Statistics, Injection, Execution. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
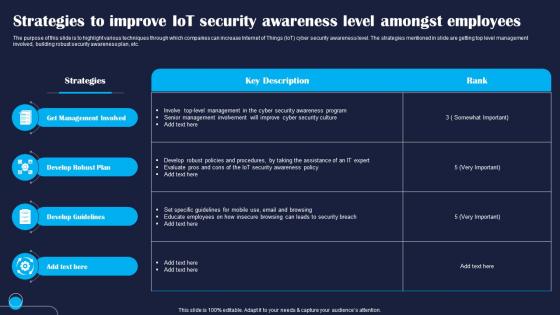 Strategies To Improve IoT Security Improving IoT Device Cybersecurity IoT SS
Strategies To Improve IoT Security Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to highlight various techniques through which companies can increase Internet of Things IoT cyber security awareness level. The strategies mentioned in slide are getting top level management involved, building robust security awareness plan, etc. Present the topic in a bit more detail with this Strategies To Improve IoT Security Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Management, Develop, Guidelines. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table Of Contents Improving IoT Device Cybersecurity To Prevent Data Breaches IoT SS
Table Of Contents Improving IoT Device Cybersecurity To Prevent Data Breaches IoT SSIncrease audience engagement and knowledge by dispensing information using Table Of Contents Improving IoT Device Cybersecurity To Prevent Data Breaches IoT SS. This template helps you present information on six stages. You can also present information on Security, Strategies, Budget using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
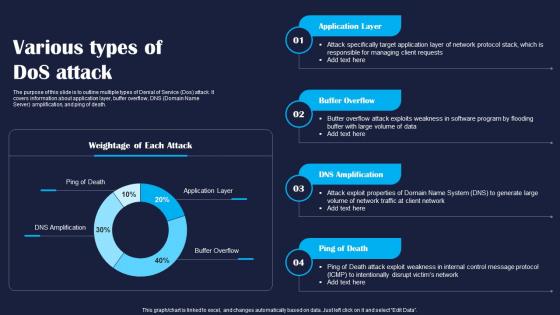 Various Types Of Dos Attack Improving IoT Device Cybersecurity IoT SS
Various Types Of Dos Attack Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to outline multiple types of Denial of Service Dos attack. It covers information about application layer, buffer overflow, DNS Domain Name Server amplification, and ping of death. Deliver an outstanding presentation on the topic using this Various Types Of Dos Attack Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Application, Layer, Death using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
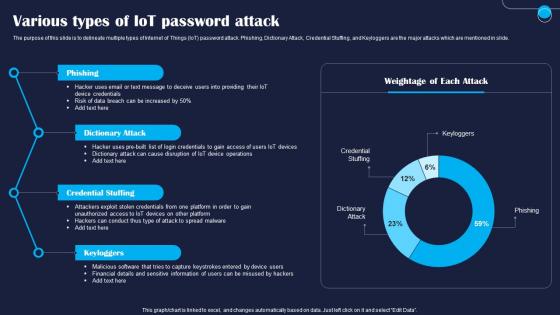 Various Types Of IoT Password Attack Improving IoT Device Cybersecurity IoT SS
Various Types Of IoT Password Attack Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to delineate multiple types of Internet of Things IoT password attack. Phishing, Dictionary Attack, Credential Stuffing, and Keyloggers are the major attacks which are mentioned in slide. Present the topic in a bit more detail with this Various Types Of IoT Password Attack Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Phishing, Dictionary, Credential. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
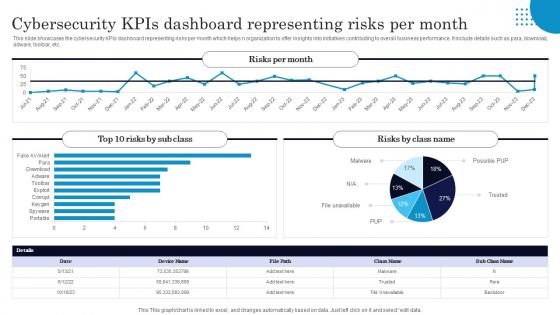 Cybersecurity Kpis Dashboard Representing Risks Per Month
Cybersecurity Kpis Dashboard Representing Risks Per MonthThis slide showcases the cybersecurity KPIs dashboard representing risks per month which helps n organization to offer insights into initiatives contributing to overall business performance. It include details such as para, download, adware, toolbar, etc. Presenting our well structured Cybersecurity Kpis Dashboard Representing Risks Per Month. The topics discussed in this slide are Risks Per Month, Risks By Class Name.This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
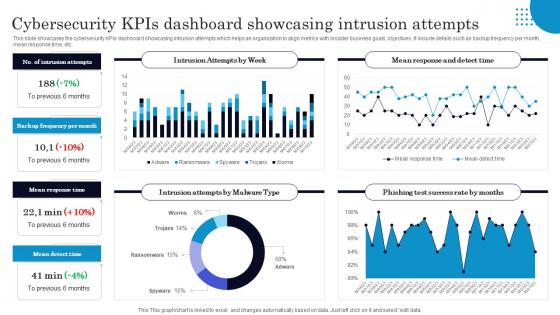 Cybersecurity Kpis Dashboard Showcasing Intrusion Attempts
Cybersecurity Kpis Dashboard Showcasing Intrusion AttemptsThis slide showcases the cybersecurity KPIs dashboard showcasing intrusion attempts which helps an organization to align metrics with broader business goals, objectives. It include details such as backup frequency per month, mean response time, etc. Introducing our Cybersecurity Kpis Dashboard Showcasing Intrusion Attempts set of slides. The topics discussed in these slides are Intrusion Attempts By Week, Mean Response Time. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
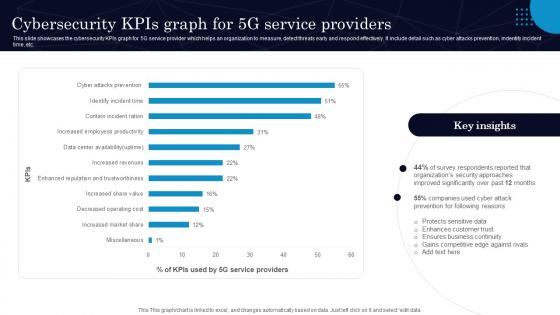 Cybersecurity Kpis Graph For 5g Service Providers
Cybersecurity Kpis Graph For 5g Service ProvidersThis slide showcases the cybersecurity KPIs graph for 5G service provider which helps an organization to measure, detect threats early and respond effectively. It include detail such as cyber attacks prevention, indentify incident time, etc. Presenting our well structured Cybersecurity Kpis Graph For 5g Service Providers. The topics discussed in this slide are Survey Respondents, Companies Used.This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
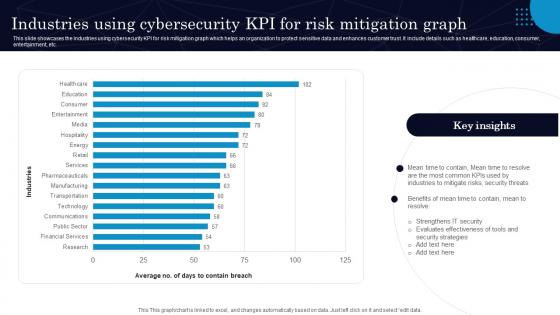 Industries Using Cybersecurity Kpi For Risk Mitigation Graph
Industries Using Cybersecurity Kpi For Risk Mitigation GraphThis slide showcases the industries using cybersecurity KPI for risk mitigation graph which helps an organization to protect sensitive data and enhances customer trust. It include details such as healthcare, education, consumer, entertainment, etc. Presenting our well structured Industries Using Cybersecurity Kpi For Risk Mitigation Graph. The topics discussed in this slide are Mitigate Risks, Security Threats.This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
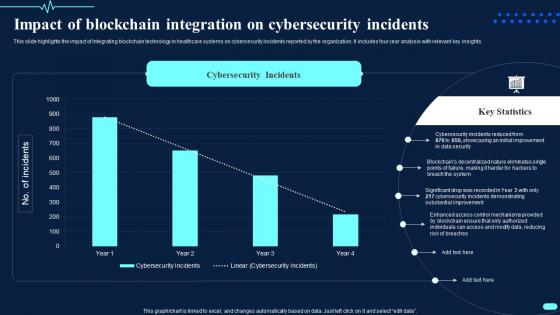 Impact Of Blockchain Integration On Cybersecurity Transforming Healthcare BCT SS
Impact Of Blockchain Integration On Cybersecurity Transforming Healthcare BCT SSThis slide highlights the impact of integrating blockchain technology in healthcare systems on cybersecurity incidents reported by the organization. It includes four year analysis with relevant key insights. Deliver an outstanding presentation on the topic using this Impact Of Blockchain Integration On Cybersecurity Transforming Healthcare BCT SS. Dispense information and present a thorough explanation of Cybersecurity Incidents using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
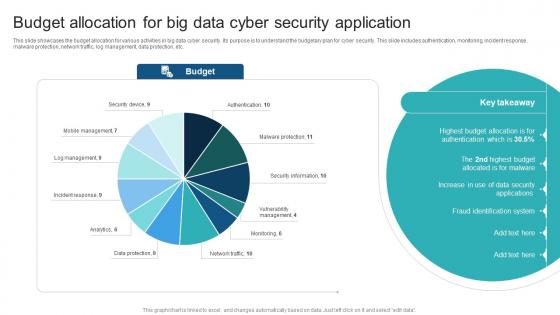 Budget Allocation For Big Data Cyber Security Application
Budget Allocation For Big Data Cyber Security ApplicationThis slide showcases the budget allocation for various activities in big data cyber security. Its purpose is to understand the budgetary plan for cyber security. This slide includes authentication, monitoring, incident response, malware protection, network traffic, log management, data protection, etc. Introducing our Budget Allocation For Big Data Cyber Security Application set of slides. The topics discussed in these slides are Allocation, Cyber, Security. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
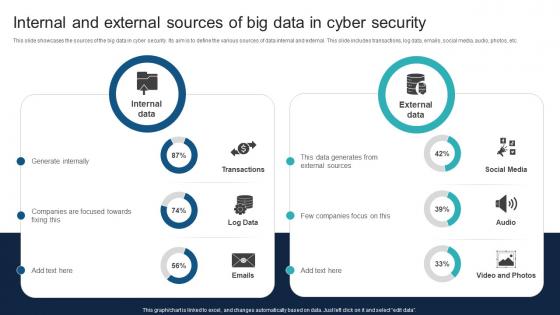 Internal And External Sources Of Big Data In Cyber Security
Internal And External Sources Of Big Data In Cyber SecurityThis slide showcases the sources of the big data in cyber security. Its aim is to define the various sources of data internal and external. This slide includes transactions, log data, emails, social media, audio, photos, etc. Introducing our Internal And External Sources Of Big Data In Cyber Security set of slides. The topics discussed in these slides are Generate, Focused, Companies. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
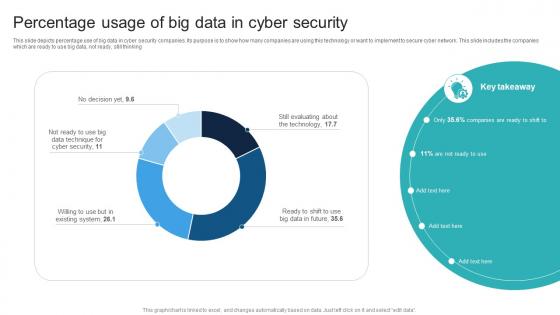 Percentage Usage Of Big Data In Cyber Security
Percentage Usage Of Big Data In Cyber SecurityThis slide depicts percentage use of big data in cyber security companies. Its purpose is to show how many companies are using this technology or want to implement to secure cyber network. This slide includes the companies which are ready to use big data, not ready, still thinking Introducing our Percentage Usage Of Big Data In Cyber Security set of slides. The topics discussed in these slides are Security, Cyber, Percentage. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
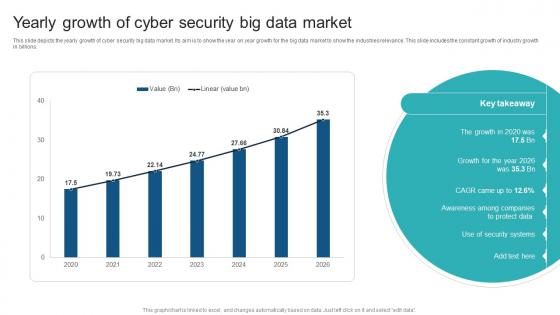 Yearly Growth Of Cyber Security Big Data Market
Yearly Growth Of Cyber Security Big Data MarketThis slide depicts the yearly growth of cyber security big data market. Its aim is to show the year on year growth for the big data market to show the industries relevance. This slide includes the constant growth of industry growth in billions. Introducing our Yearly Growth Of Cyber Security Big Data Market set of slides. The topics discussed in these slides are Growth, Security, Market. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Security Dashboard For Tracking Data Breach Intelligence
Cyber Security Dashboard For Tracking Data Breach IntelligenceThe highlighted slide focuses on key elements such as threat intelligence, activity trends, malware sightings, and the identification of active and most active vulnerabilities. This data is essential for a cybersecurity dashboard, providing valuable insights and intelligence to proactively address and mitigate potential data breaches. Presenting our well structured Cyber Security Dashboard For Tracking Data Breach Intelligence. The topics discussed in this slide are Digital Threat Monitoring, File Analysis, Threat Intelligence. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
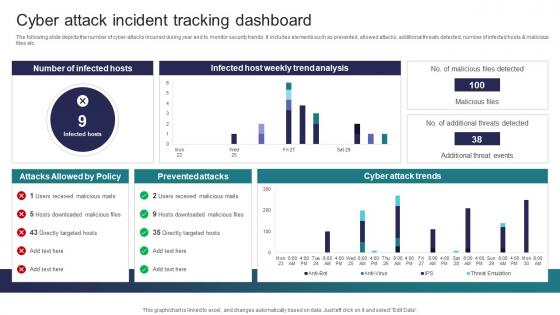 Cyber Attack Incident Tracking Dashboard Implementing Strategies To Mitigate Cyber Security Threats
Cyber Attack Incident Tracking Dashboard Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts the number of cyber attacks incurred during year end to monitor security trends. It includes elements such as prevented, allowed attacks, additional threats detected, number of infected hosts and malicious files etc. Present the topic in a bit more detail with this Cyber Attack Incident Tracking Dashboard Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Prevented Attacks, Cyber Attack Trends This template is free to edit as deemed fit for your organization. Therefore download it now.
-
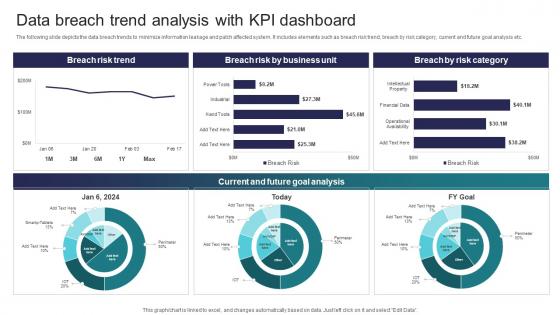 Data Breach Trend Analysis With KPI Dashboard Implementing Strategies To Mitigate Cyber Security Threats
Data Breach Trend Analysis With KPI Dashboard Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts the data breach trends to minimize information leakage and patch affected system. It includes elements such as breach risk trend, breach by risk category, current and future goal analysis etc. Present the topic in a bit more detail with this Data Breach Trend Analysis With KPI Dashboard Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Current And Future Goal Analysis, Breach Risk Trend This template is free to edit as deemed fit for your organization. Therefore download it now.
-
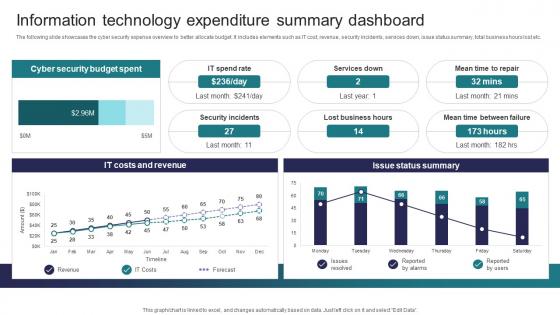 Information Technology Expenditure Summary Implementing Strategies To Mitigate Cyber Security Threats
Information Technology Expenditure Summary Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases the cyber security expense overview to better allocate budget. It includes elements such as IT cost, revenue, security incidents, services down, issue status summary, total business hours lost etc. Deliver an outstanding presentation on the topic using this Information Technology Expenditure Summary Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Cyber Security Budget Spent, It Costs And Revenue, Issue Status Summary using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
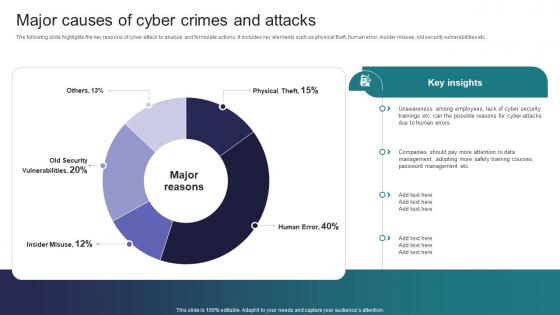 Major Causes Of Cyber Crimes And Attacks Implementing Strategies To Mitigate Cyber Security Threats
Major Causes Of Cyber Crimes And Attacks Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide highlights the key reasons of cyber attack to analyze and formulate actions. It includes key elements such as physical theft, human error, insider misuse, old security vulnerabilities etc. Deliver an outstanding presentation on the topic using this Major Causes Of Cyber Crimes And Attacks Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Employees, Management, Training Courses using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
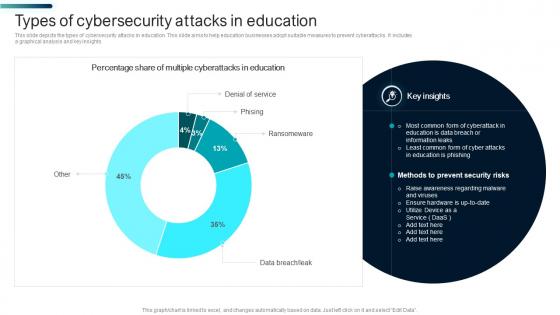 Types Of Cybersecurity Attacks In Education
Types Of Cybersecurity Attacks In EducationThis slide depicts the types of cybersecurity attacks in education. This slide aims to help education businesses adopt suitable measures to prevent cyberattacks. It includes a graphical analysis and key insights Introducing our Types Of Cybersecurity Attacks In Education set of slides. The topics discussed in these slides are Cyberattacks In Education, Education Is Phishing. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
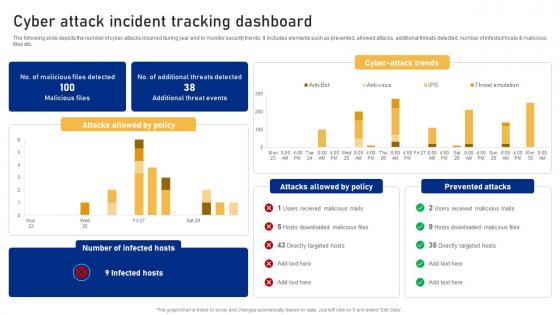 Cyber Attack Incident Tracking Dashboard Cyber Risk Assessment
Cyber Attack Incident Tracking Dashboard Cyber Risk AssessmentThe following slide depicts the number of cyber-attacks incurred during year end to monitor security trends. It includes elements such as prevented, allowed attacks, additional threats detected, number of infected hosts and malicious files etc. Present the topic in a bit more detail with this Cyber Attack Incident Tracking Dashboard Cyber Risk Assessment Use it as a tool for discussion and navigation on Cyber Attack Incident, Tracking Dashboard This template is free to edit as deemed fit for your organization. Therefore download it now.
-
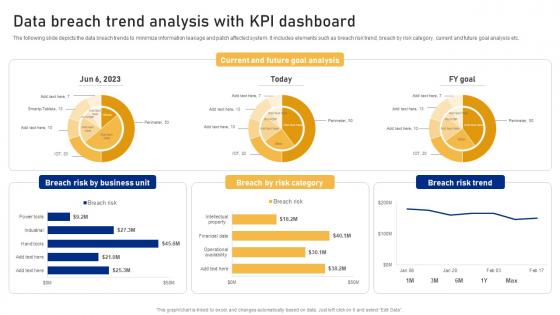 Data Breach Trend Analysis With KPI Dashboard Cyber Risk Assessment
Data Breach Trend Analysis With KPI Dashboard Cyber Risk AssessmentThe following slide depicts the data breach trends to minimize information leakage and patch affected system. It includes elements such as breach risk trend, breach by risk category, current and future goal analysis etc. Present the topic in a bit more detail with this Data Breach Trend Analysis With KPI Dashboard Cyber Risk Assessment Use it as a tool for discussion and navigation on Breach Risk, Business Unit, Risk Category This template is free to edit as deemed fit for your organization. Therefore download it now.
-
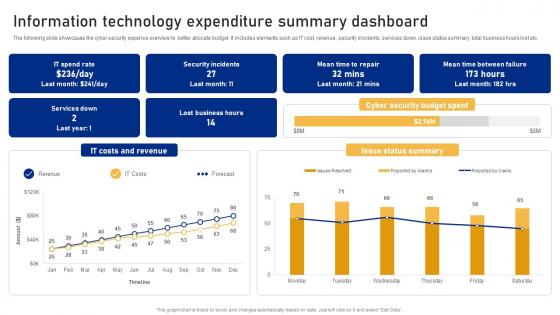 Information Technology Expenditure Summary Dashboard Cyber Risk Assessment
Information Technology Expenditure Summary Dashboard Cyber Risk AssessmentThe following slide showcases the cyber security expense overview to better allocate budget. It includes elements such as IT cost, revenue, security incidents, services down, issue status summary, total business hours lost etc. Deliver an outstanding presentation on the topic using this Information Technology Expenditure Summary Dashboard Cyber Risk Assessment Dispense information and present a thorough explanation of Security Incidents, Costs And Revenue, Issue Status Summary using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
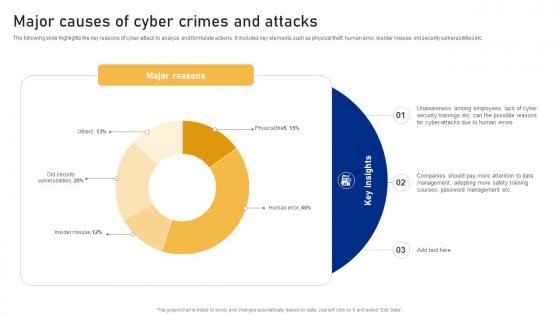 Major Causes Of Cyber Crimes And Attacks Cyber Risk Assessment
Major Causes Of Cyber Crimes And Attacks Cyber Risk AssessmentThe following slide highlights the key reasons of cyber-attack to analyze and formulate actions. It includes key elements such as physical theft, human error, insider misuse, old security vulnerabilities etc. Present the topic in a bit more detail with this Major Causes Of Cyber Crimes And Attacks Cyber Risk Assessment Use it as a tool for discussion and navigation on Major Reasons, Major Causes, Cyber Crimes And Attacks This template is free to edit as deemed fit for your organization. Therefore download it now.
-
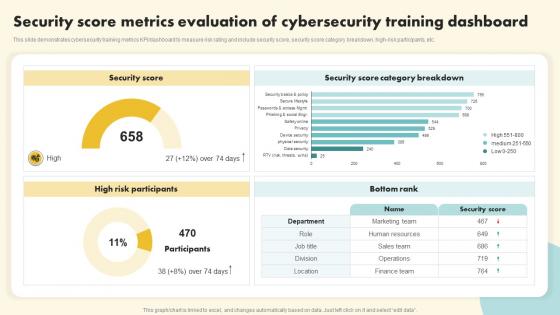 Security Score Metrics Evaluation Of Cybersecurity Training Dashboard
Security Score Metrics Evaluation Of Cybersecurity Training DashboardThis slide demonstrates cybersecurity training metrics KPI dashboard to measure risk rating and include security score, security score category breakdown, high risk participants, etc. Introducing our Security Score Metrics Evaluation Of Cybersecurity Training Dashboard set of slides. The topics discussed in these slides are Security Score Metrics Evaluation, Cybersecurity Training Dashboard This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Security Attack Control Dashboard
Cyber Security Attack Control DashboardThis slide highlights the data to track cyber attack attempted on the company to analyze and make strategies to prevent from these attacks and protect sensitive data. It includes various KPIs such as malicious emails, malicious files, malicious websites, etc. Introducing our Cyber Security Attack Control Dashboard set of slides. The topics discussed in these slides are Malicious Emails, Malicious Files, Malicious Websites This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
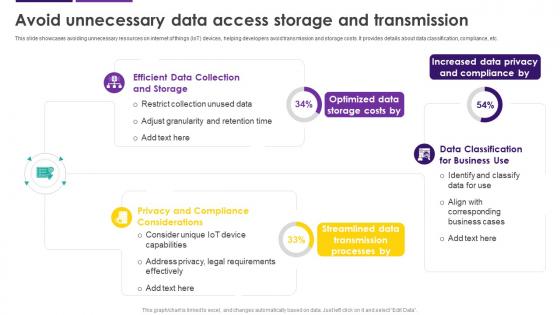 Avoid Unnecessary Data Access Storage And Transmission Internet Of Things IoT Security Cybersecurity SS
Avoid Unnecessary Data Access Storage And Transmission Internet Of Things IoT Security Cybersecurity SSThis slide showcases avoiding unnecessary resources on internet of things IoT devices, helping developers avoid transmission and storage costs. It provides details about data classification, compliance, etc. Deliver an outstanding presentation on the topic using this Avoid Unnecessary Data Access Storage And Transmission Internet Of Things IoT Security Cybersecurity SS. Dispense information and present a thorough explanation of Privacy And Compliance Considerations, Data Privacy And Compliance, Data Access Storage using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
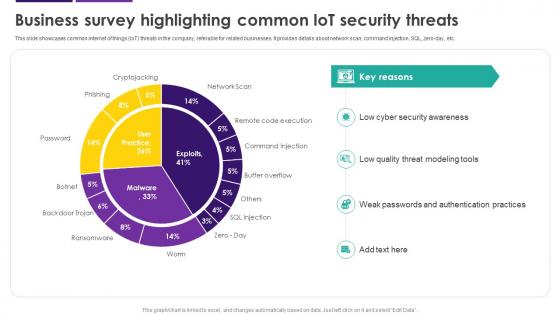 Business Survey Highlighting Common IoT Security Threats Internet Of Things IoT Security Cybersecurity SS
Business Survey Highlighting Common IoT Security Threats Internet Of Things IoT Security Cybersecurity SSThis slide showcases common internet of things IoT threats in the company, referable for related businesses. It provides details about network scan, command injection, SQL, zero-day, etc. Present the topic in a bit more detail with this Business Survey Highlighting Common IoT Security Threats Internet Of Things IoT Security Cybersecurity SS. Use it as a tool for discussion and navigation on Cyber Security Awareness, Quality Threat Modeling Tools, Weak Passwords, Authentication Practices. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
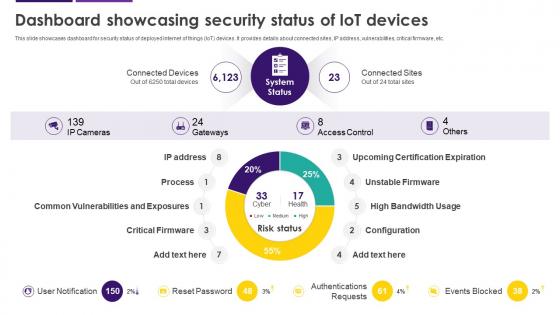 Dashboard Showcasing Security Status Of IoT Devices Internet Of Things IoT Security Cybersecurity SS
Dashboard Showcasing Security Status Of IoT Devices Internet Of Things IoT Security Cybersecurity SSThis slide showcases dashboard for security status of deployed internet of things IoT devices. It provides details about connected sites, IP address, vulnerabilities, critical firmware, etc. Deliver an outstanding presentation on the topic using this Dashboard Showcasing Security Status Of IoT Devices Internet Of Things IoT Security Cybersecurity SS. Dispense information and present a thorough explanation of Dashboard, Security Status, IoT Devices, Vulnerabilities, Critical Firmware using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
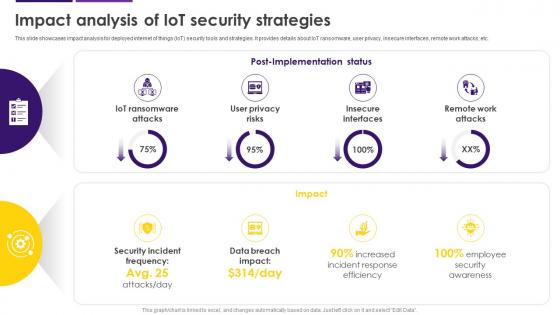 Impact Analysis Of IoT Security Strategies Internet Of Things IoT Security Cybersecurity SS
Impact Analysis Of IoT Security Strategies Internet Of Things IoT Security Cybersecurity SSThis slide showcases impact analysis for deployed internet of things IoT security tools and strategies. It provides details about IoT ransomware, user privacy, insecure interfaces, remote work attacks, etc. Present the topic in a bit more detail with this Impact Analysis Of IoT Security Strategies Internet Of Things IoT Security Cybersecurity SS. Use it as a tool for discussion and navigation on Internet Of Things, Security Tools And Strategies, IoT Ransomware, Remote Work Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 IoT Cyber Security Budget Plan Internet Of Things IoT Security Cybersecurity SS
IoT Cyber Security Budget Plan Internet Of Things IoT Security Cybersecurity SSThis slide showcases security budget plan for internet of things IoT operations. It provides details about secure data transmission, reduce attack surface, add features from gateways, understand data, etc. Present the topic in a bit more detail with this IoT Cyber Security Budget Plan Internet Of Things IoT Security Cybersecurity SS. Use it as a tool for discussion and navigation on IoT Cyber Security, Budget Plan, Reduce Attack Surface, Internet Of Things. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
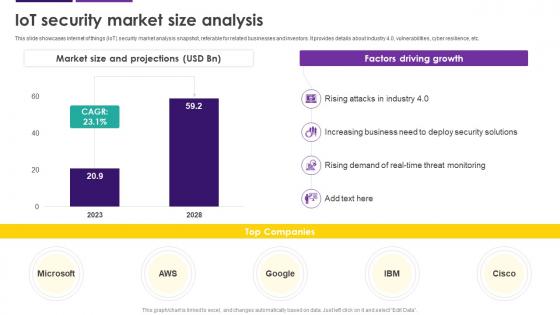 IoT Security Market Size Analysis Internet Of Things IoT Security Cybersecurity SS
IoT Security Market Size Analysis Internet Of Things IoT Security Cybersecurity SSThis slide showcases internet of things IoT security market analysis snapshot, referable for related businesses and investors. It provides details about industry 4.0, vulnerabilities, cyber resilience, etc. Present the topic in a bit more detail with this IoT Security Market Size Analysis Internet Of Things IoT Security Cybersecurity SS. Use it as a tool for discussion and navigation on IoT Security, Market Size Analysis, Internet Of Things, Vulnerabilities, Cyber Resilience. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
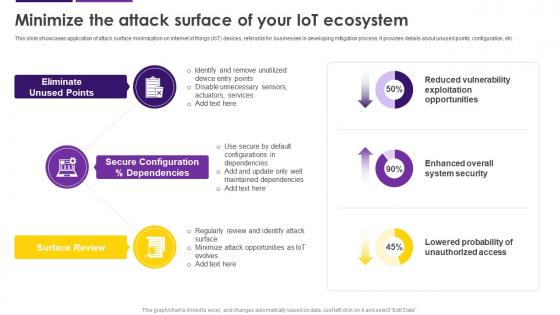 Minimize The Attack Surface Of Your IoT Ecosystem Internet Of Things IoT Security Cybersecurity SS
Minimize The Attack Surface Of Your IoT Ecosystem Internet Of Things IoT Security Cybersecurity SSThis slide showcases application of attack surface minimization on internet of things IoT devices, referable for businesses in developing mitigation process. It provides details about unused points, configuration, etc. Deliver an outstanding presentation on the topic using this Minimize The Attack Surface Of Your IoT Ecosystem Internet Of Things IoT Security Cybersecurity SS. Dispense information and present a thorough explanation of Eliminate Unused Points, System Security, Exploitation Opportunities, Probability Of Unauthorized Access using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
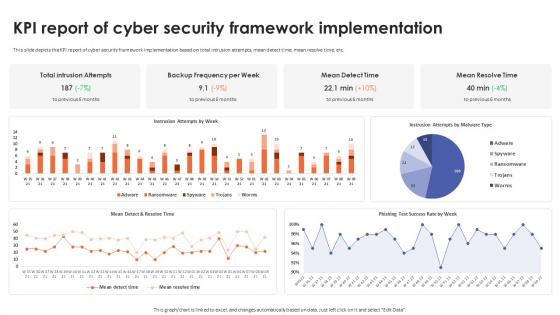 KPI Report Of Cyber Security Framework Implementation
KPI Report Of Cyber Security Framework ImplementationThis slide depicts the KPI report of cyber security framework implementation based on total intrusion attempts, mean detect time, mean resolve time, etc. Deliver an outstanding presentation on the topic using this KPI Report Of Cyber Security Framework Implementation. Dispense information and present a thorough explanation of KPI Report Of Cyber Security, Framework Implementation, Mean Detect Time, Mean Resolve Time using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
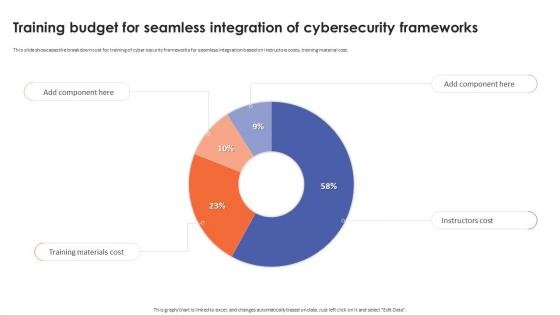 Training Budget For Seamless Integration Of Cybersecurity Frameworks
Training Budget For Seamless Integration Of Cybersecurity FrameworksThis slide showcases the breakdown cost for training of cyber security frameworks for seamless integration based on instructors costs, training material cost. Present the topic in a bit more detail with this Training Budget For Seamless Integration Of Cybersecurity Frameworks. Use it as a tool for discussion and navigation on Training Budget, Seamless Integration, Cybersecurity Frameworks, Training Material Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Forecasting Of Quantum Cryptography In Cybersecurity
Forecasting Of Quantum Cryptography In CybersecurityThis slide depicts about future of quantum cryptography and provides details about forecasting cybersecurity in global market. It includes elements such as network technology , funding, etc. Presenting our well structured Forecasting Of Quantum Cryptography In Cybersecurity. The topics discussed in this slide are Forecasting, Cryptography, Cybersecurity. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
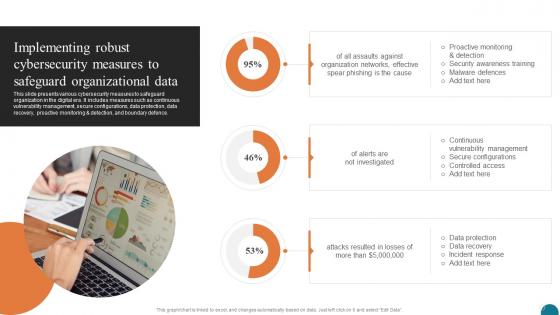 Implementing Robust Cybersecurity Elevating Small And Medium Enterprises Digital Transformation DT SS
Implementing Robust Cybersecurity Elevating Small And Medium Enterprises Digital Transformation DT SSThis slide presents various cybersecurity measures to safeguard organization in the digital era. It includes measures such as continuous vulnerability management, secure configurations, data protection, data recovery, proactive monitoring and detection, and boundary defence. Present the topic in a bit more detail with this Implementing Robust Cybersecurity Elevating Small And Medium Enterprises Digital Transformation DT SS. Use it as a tool for discussion and navigation on Organization Networks, Data Protection, Controlled Access. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Overview Cybersecurity And Data Protection Elevating Small And Medium Enterprises Digital Transformation DT SS
Overview Cybersecurity And Data Protection Elevating Small And Medium Enterprises Digital Transformation DT SSThis slide presents an overview into the landscape of cybersecurity and data protection with its advantages. It also presents a survey analysis on share of SMEs that have implemented essential and basic IT security initiatives. Deliver an outstanding presentation on the topic using this Overview Cybersecurity And Data Protection Elevating Small And Medium Enterprises Digital Transformation DT SS. Dispense information and present a thorough explanation of Digital Technologies, Organizations Digital, Digital Transformation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
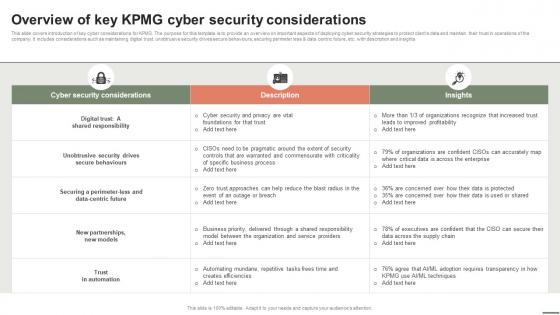 Extensive Business Strategy Overview Of Key KPMG Cyber Security Considerations Strategy SS V
Extensive Business Strategy Overview Of Key KPMG Cyber Security Considerations Strategy SS VThis slide covers introduction of key cyber considerations for KPMG. The purpose for this template is to provide an overview on important aspects of deploying cyber security strategies to protect clients data and maintain their trust in operations of the company. It includes considerations such as maintaining digital trust, unobtrusive security drives secure behaviours, securing perimeter less and data centric future, etc. with description and insights Present the topic in a bit more detail with this Extensive Business Strategy Overview Of Key KPMG Cyber Security Considerations Strategy SS V. Use it as a tool for discussion and navigation on Cyber Security Considerations, Description, Insights. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
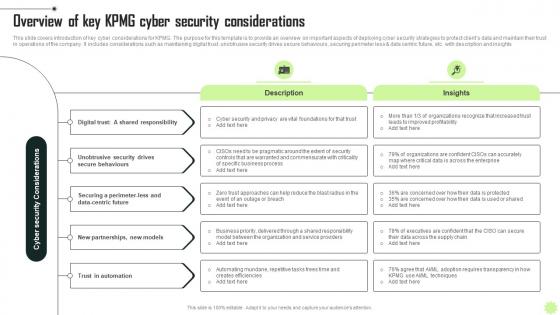 Overview Of Key KPMG Cyber Security KPMG Operational And Marketing Strategy SS V
Overview Of Key KPMG Cyber Security KPMG Operational And Marketing Strategy SS VThis slide covers introduction of key cyber considerations for KPMG. The purpose for this template is to provide an overview on important aspects of deploying cyber security strategies to protect clients data and maintain their trust in operations of the company. It includes considerations such as maintaining digital trust, unobtrusive security drives secure behaviours, securing perimeter less and data centric future, etc. with description and insights Increase audience engagement and knowledge by dispensing information using Overview Of Key KPMG Cyber Security KPMG Operational And Marketing Strategy SS V. This template helps you present information on five stages. You can also present information on Digital, Security, Automation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
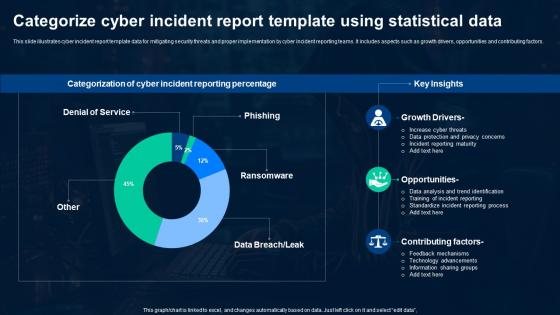 Categorize Cyber Incident Report Template Using Statistical Data
Categorize Cyber Incident Report Template Using Statistical DataThis slide illustrates cyber incident report template data for mitigating security threats and proper implementation by cyber incident reporting teams. It includes aspects such as growth drivers, opportunities and contributing factors. Introducing our Categorize Cyber Incident Report Template Using Statistical Data set of slides. The topics discussed in these slides are Growth Drivers, Opportunities, Contributing Factors. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
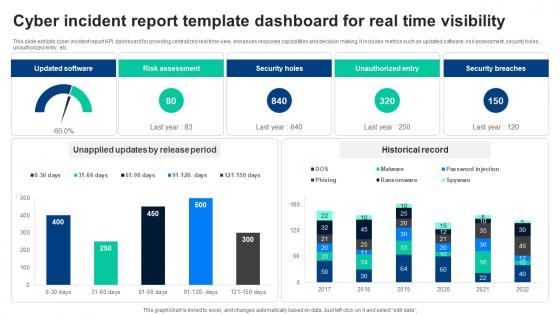 Cyber Incident Report Template Dashboard For Real Time Visibility
Cyber Incident Report Template Dashboard For Real Time VisibilityThis slide exhibits cyber incident report KPI dashboard for providing centralized real time view, enhances response capabilities and decision making. It includes metrics such as updated software, risk assessment, security holes, unauthorized entry, etc. Presenting our well structured Cyber Incident Report Template Dashboard For Real Time Visibility. The topics discussed in this slide are Dashboard, Unauthorized Entry, Security Breaches. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
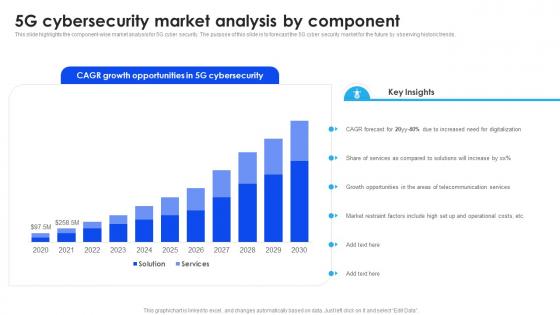 5G Cybersecurity Market Analysis By Component
5G Cybersecurity Market Analysis By ComponentThis slide highlights the component wise market analysis for 5G cyber security. The purpose of this slide is to forecast the 5G cyber security market for the future by observing historic trends. Introducing our 5G Cybersecurity Market Analysis By Component set of slides. The topics discussed in these slides are Increased, Solutions, Services. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Global 5G Cybersecurity Market Forecast
Global 5G Cybersecurity Market ForecastThis slide depicts the global 5G cybersecurity market forecast. The purpose of this slide is to help the business observe historic trends and adopt suitable techniques in order to safeguard its 5G network. Presenting our well structured Global 5G Cybersecurity Market Forecast. The topics discussed in this slide are Increased, Digital, Market. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cyber Attack Incident Tracking Dashboard Creating Cyber Security Awareness
Cyber Attack Incident Tracking Dashboard Creating Cyber Security AwarenessThe following slide depicts the number of cyber-attacks incurred during year end to monitor security trends. It includes elements such as prevented, allowed attacks, additional threats detected, number of infected hosts and malicious files etc. Present the topic in a bit more detail with this Cyber Attack Incident Tracking Dashboard Creating Cyber Security Awareness Use it as a tool for discussion and navigation on Infected Hosts, Cyber Attack Trends This template is free to edit as deemed fit for your organization. Therefore download it now.
-
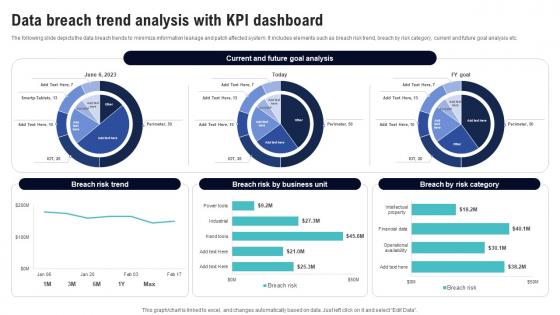 Data Breach Trend Analysis With Kpi Dashboard Creating Cyber Security Awareness
Data Breach Trend Analysis With Kpi Dashboard Creating Cyber Security AwarenessThe following slide depicts the data breach trends to minimize information leakage and patch affected system. It includes elements such as breach risk trend, breach by risk category, current and future goal analysis etc. Deliver an outstanding presentation on the topic using this Data Breach Trend Analysis With Kpi Dashboard Creating Cyber Security Awareness Dispense information and present a thorough explanation of Systems And Passwords, Phishing Exercise, Penetration Test using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Information Technology Expenditure Summary Dashboard Creating Cyber Security Awareness
Information Technology Expenditure Summary Dashboard Creating Cyber Security AwarenessThe following slide showcases the cyber security expense overview to better allocate budget. It includes elements such as IT cost, revenue, security incidents, services down, issue status summary, total business hours lost etc. Deliver an outstanding presentation on the topic using this Information Technology Expenditure Summary Dashboard Creating Cyber Security Awareness Dispense information and present a thorough explanation of Inadequate Security Guidelines, Inappropriate Privacy Policies, Insufficient Security Failure By Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
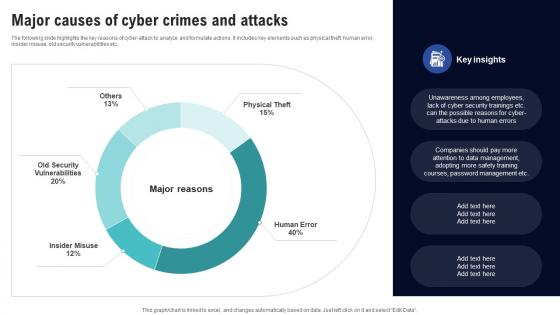 Major Causes Of Cyber Crimes And Attacks Creating Cyber Security Awareness
Major Causes Of Cyber Crimes And Attacks Creating Cyber Security AwarenessThe following slide highlights the key reasons of cyber-attack to analyze and formulate actions. It includes key elements such as physical theft, human error, insider misuse, old security vulnerabilities etc. Present the topic in a bit more detail with this Major Causes Of Cyber Crimes And Attacks Creating Cyber Security Awareness Use it as a tool for discussion and navigation on Mean Time To Detect, Mean Time To Resolve This template is free to edit as deemed fit for your organization. Therefore download it now.
-
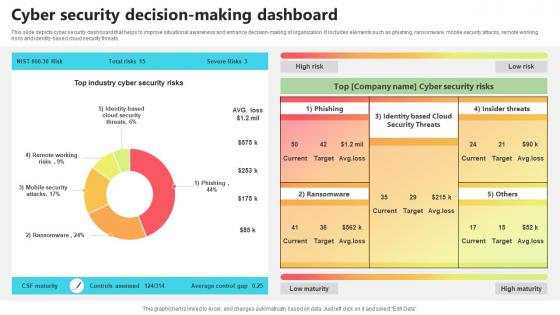 Cyber Security Decision Making Dashboard
Cyber Security Decision Making DashboardThis slide depicts cyber security dashboard that helps to improve situational awareness and enhance decision-making of organization. It includes elements such as phishing, ransomware, mobile security attacks, remote working risks and identity-based cloud security threats. Introducing our Cyber Security Decision Making Dashboard set of slides. The topics discussed in these slides are Cyber Security, Decision Making Dashboard. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
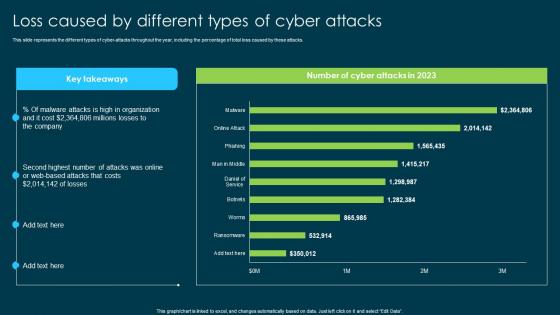 Ethical Hacking And Network Security Loss Caused By Different Types Of Cyber Attacks
Ethical Hacking And Network Security Loss Caused By Different Types Of Cyber AttacksThis slide represents the different types of cyber-attacks throughout the year, including the percentage of total loss caused by these attacks. Present the topic in a bit more detail with this Ethical Hacking And Network Security Loss Caused By Different Types Of Cyber Attacks. Use it as a tool for discussion and navigation on Cyber Attacks Throughout, Online Or Web Based Attacks, Malware Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.



