Powerpoint Templates and Google slides for Cyber Vulnerability Assessment
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Signs That Your Business May Be Vulnerable To Cyber Threats Training Ppt
Signs That Your Business May Be Vulnerable To Cyber Threats Training PptPresenting Signs that your Business may be Vulnerable to Cyber Threats. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
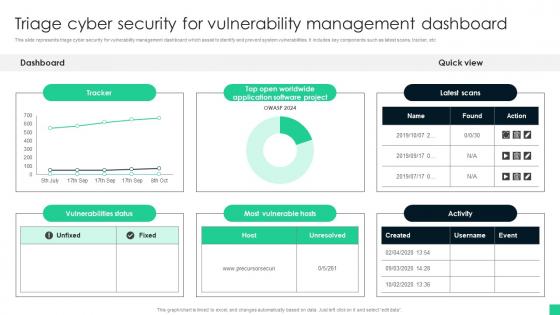 Triage Cyber Security For Vulnerability Management Dashboard
Triage Cyber Security For Vulnerability Management DashboardThis slide represents triage cyber security for vulnerability management dashboard which assist to identify and prevent system vulnerabilities. It includes key components such as latest scans, tracker, etc Introducing our Triage Cyber Security For Vulnerability Management Dashboard set of slides. The topics discussed in these slides are Most Vulnerable Hosts, Vulnerabilities Status This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Recent Cyber Security Vulnerabilities In Powerpoint And Google Slides Cpb
Recent Cyber Security Vulnerabilities In Powerpoint And Google Slides CpbPresenting our Recent Cyber Security Vulnerabilities In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Recent Cyber Security Vulnerabilities This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
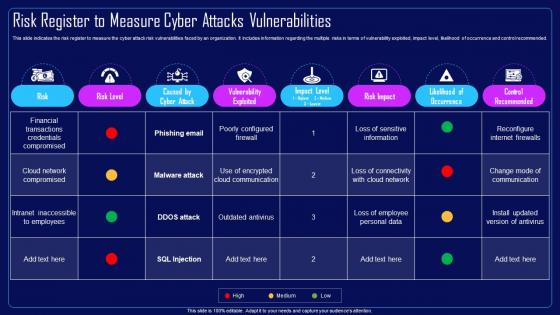 Action Plan To Combat Cyber Crimes Risk Register To Measure Cyber Attacks Vulnerabilities
Action Plan To Combat Cyber Crimes Risk Register To Measure Cyber Attacks VulnerabilitiesThis slide indicates the risk register to measure the cyber attack risk vulnerabilities faced by an organization. It includes information regarding the multiple risks in terms of vulnerability exploited, impact level, likelihood of occurrence and control recommended. Present the topic in a bit more detail with this Action Plan To Combat Cyber Crimes Risk Register To Measure Cyber Attacks Vulnerabilities. Use it as a tool for discussion and navigation on Cloud Network Compromised, Financial Transactions, Credentials Compromised. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
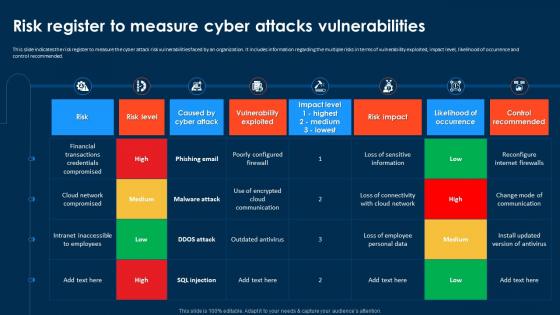 Compressive Planning Guide Risk Register To Measure Cyber Attacks Vulnerabilities
Compressive Planning Guide Risk Register To Measure Cyber Attacks VulnerabilitiesThis slide indicates the risk register to measure the cyber attack risk vulnerabilities faced by an organization. It includes information regarding the multiple risks in terms of vulnerability exploited, impact level, likelihood of occurrence and control recommended. Present the topic in a bit more detail with this Compressive Planning Guide Risk Register To Measure Cyber Attacks Vulnerabilities. Use it as a tool for discussion and navigation on Cyber Attack Risk Vulnerabilities, Vulnerability Exploited, Occurrence And Control Recommended. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
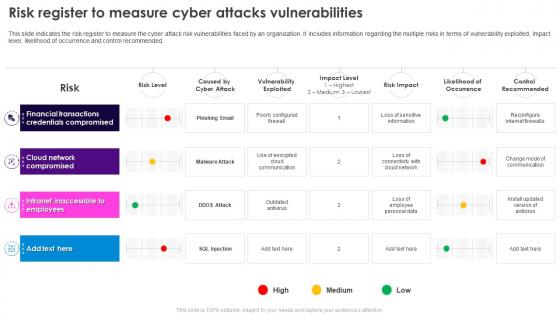 Security Plan To Prevent Cyber Risk Register To Measure Cyber Attacks Vulnerabilities
Security Plan To Prevent Cyber Risk Register To Measure Cyber Attacks VulnerabilitiesThis slide indicates the risk register to measure the cyber attack risk vulnerabilities faced by an organization. It includes information regarding the multiple risks in terms of vulnerability exploited, impact level, likelihood of occurrence and control recommended. Present the topic in a bit more detail with this Security Plan To Prevent Cyber Risk Register To Measure Cyber Attacks Vulnerabilities. Use it as a tool for discussion and navigation on Financial Transactions, Credentials Compromised, Cloud Network, Compromised. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Classify Assets Vulnerable To Cyber Attack Implementing Strategies To Mitigate Cyber Security Threats
Classify Assets Vulnerable To Cyber Attack Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts some major assets that are more prone to cyber attack. It mainly includes elements such as sales record, sales lead record, company internal database, customer and product information etc. Present the topic in a bit more detail with this Classify Assets Vulnerable To Cyber Attack Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Sales Record, Customer Database, Product Database This template is free to edit as deemed fit for your organization. Therefore download it now.
-
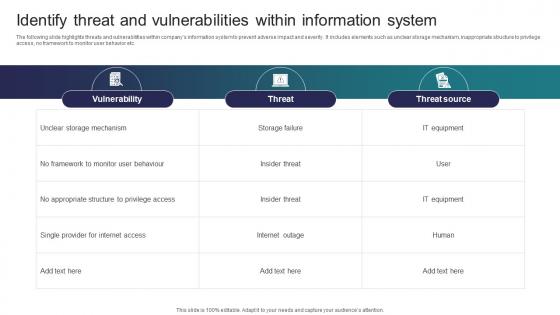 Identify Threat And Vulnerabilities Within Information System Implementing Strategies To Mitigate Cyber Security
Identify Threat And Vulnerabilities Within Information System Implementing Strategies To Mitigate Cyber SecurityThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Deliver an outstanding presentation on the topic using this Identify Threat And Vulnerabilities Within Information System Implementing Strategies To Mitigate Cyber Security Dispense information and present a thorough explanation of Vulnerability, Threat, Threat Source using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
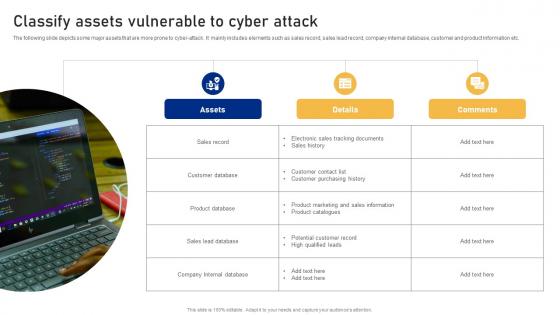 Classify Assets Vulnerable To Cyber Attack Cyber Risk Assessment
Classify Assets Vulnerable To Cyber Attack Cyber Risk AssessmentThe following slide depicts some major assets that are more prone to cyber-attack. It mainly includes elements such as sales record, sales lead record, company internal database, customer and product information etc. Introducing Classify Assets Vulnerable To Cyber Attack Cyber Risk Assessment to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Customer Database, Product Database, Sales Lead Database using this template. Grab it now to reap its full benefits.
-
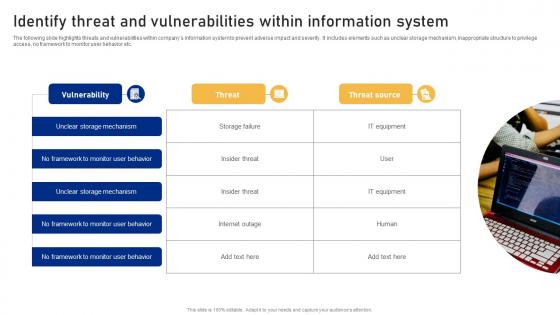 Identify Threat And Vulnerabilities Within Information System Cyber Risk Assessment
Identify Threat And Vulnerabilities Within Information System Cyber Risk AssessmentThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Introducing Identify Threat And Vulnerabilities Within Information System Cyber Risk Assessment to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on No Framework, Monitor User Behavior, Vulnerability using this template. Grab it now to reap its full benefits.
-
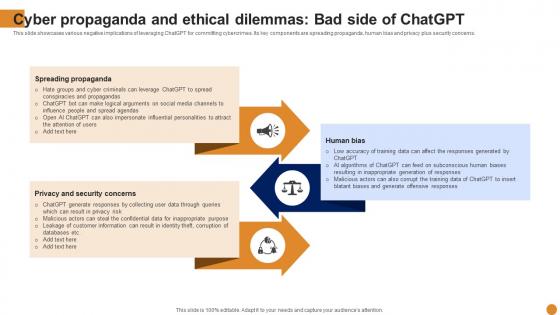 Cyber Propaganda And Ethical Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Cyber Propaganda And Ethical Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various negative implications of leveraging ChatGPT for committing cybercrimes. Its key components are spreading propaganda, human bias and privacy plus security concerns. Introducing Cyber Propaganda And Ethical Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Spreading Propaganda, Privacy And Security Concerns, Propaganda, using this template. Grab it now to reap its full benefits.
-
 Types Of Cyber Attacks Faced By Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Types Of Cyber Attacks Faced By Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various types of cyber attacks that significantly damage the organization resources and reputation. Different types of attacks faced are Malware, Phishing, Man in middle attack, SQL injection etc. Increase audience engagement and knowledge by dispensing information using Types Of Cyber Attacks Faced By Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. This template helps you present information on five stages. You can also present information on Phishing, SQL Injection, Organization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Classify Assets Vulnerable To Cyber Attack Creating Cyber Security Awareness
Classify Assets Vulnerable To Cyber Attack Creating Cyber Security AwarenessThe following slide depicts some major assets that are more prone to cyber-attack. It mainly includes elements such as sales record, sales lead record, company internal database, customer and product information etc. Introducing Classify Assets Vulnerable To Cyber Attack Creating Cyber Security Awareness to increase your presentation threshold. Encompassed with One stages, this template is a great option to educate and entice your audience. Dispence information on Sales Record, Customer Database, Product Database using this template. Grab it now to reap its full benefits.
-
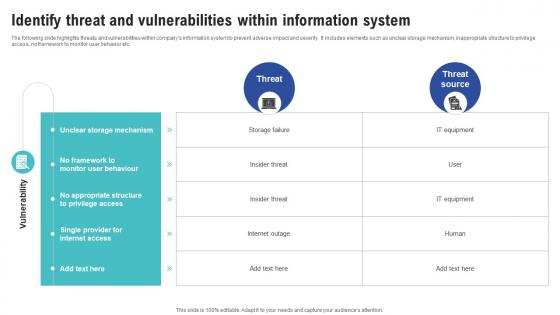 Identify Threat And Vulnerabilities Within Information System Creating Cyber Security Awareness
Identify Threat And Vulnerabilities Within Information System Creating Cyber Security AwarenessThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Deliver an outstanding presentation on the topic using this Identify Threat And Vulnerabilities Within Information System Creating Cyber Security Awareness Dispense information and present a thorough explanation of Unclear Storage Mechanism, Monitor User Behaviour, No Appropriate Structure using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
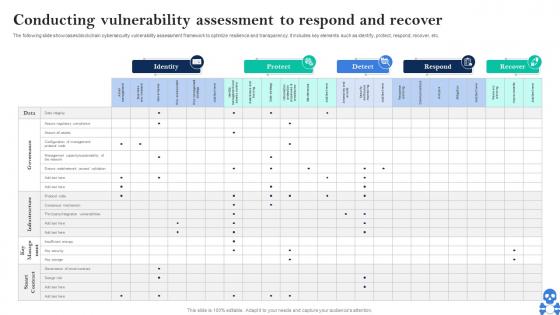 Cyber Threats In Blockchain Conducting Vulnerability Assessment To Respond And Recover BCT SS V
Cyber Threats In Blockchain Conducting Vulnerability Assessment To Respond And Recover BCT SS VThe following slide showcases blockchain cybersecurity vulnerability assessment framework to optimize resilience and transparency. It includes key elements such as identify, protect, respond, recover, etc. Present the topic in a bit more detail with this Cyber Threats In Blockchain Conducting Vulnerability Assessment To Respond And Recover BCT SS V Use it as a tool for discussion and navigation on Identity, Protect, Detect This template is free to edit as deemed fit for your organization. Therefore download it now.
-
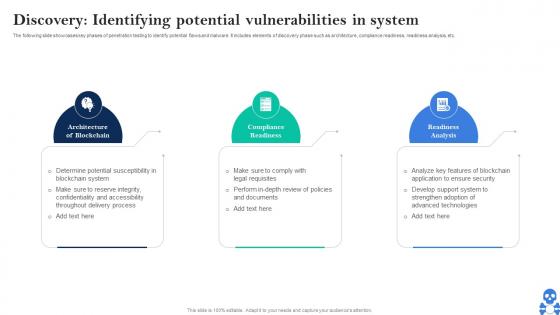 Cyber Threats In Blockchain Discovery Identifying Potential Vulnerabilities In System BCT SS V
Cyber Threats In Blockchain Discovery Identifying Potential Vulnerabilities In System BCT SS VThe following slide showcases key phases of penetration testing to identify potential flaws and malware. It includes elements of discovery phase such as architecture, compliance readiness, readiness analysis, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Discovery Identifying Potential Vulnerabilities In System BCT SS V This template helps you present information on Three stages. You can also present information on Architecture Of Blockchain, Compliance Readiness, Readiness Analysis using this PPT design. This layout is completely editable so personaize it now
-
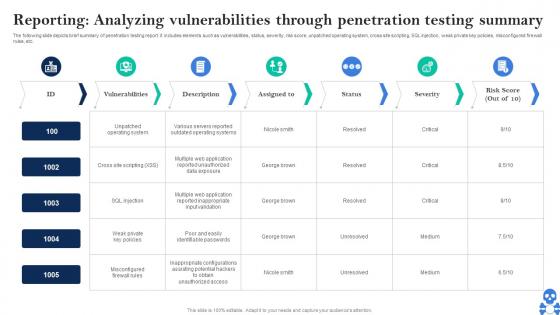 Cyber Threats In Blockchain Reporting Analyzing Vulnerabilities Through Penetration Testing Summary BCT SS V
Cyber Threats In Blockchain Reporting Analyzing Vulnerabilities Through Penetration Testing Summary BCT SS VThe following slide depicts brief summary of penetration testing report. it includes elements such as vulnerabilities, status, severity, risk score, unpatched operating system, cross site scripting, SQL injection, weak private key policies, misconfigured firewall rules, etc. Present the topic in a bit more detail with this Cyber Threats In Blockchain Reporting Analyzing Vulnerabilities Through Penetration Testing Summary BCT SS V Use it as a tool for discussion and navigation on Vulnerabilities, Description, Severity This template is free to edit as deemed fit for your organization. Therefore download it now.
-
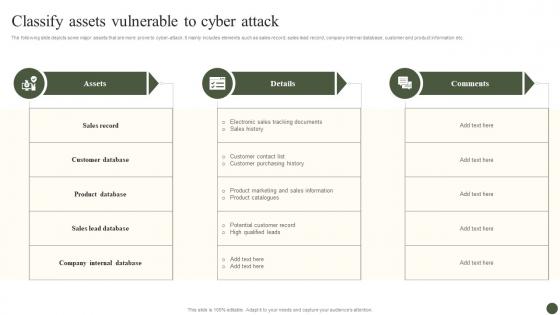 Classify Assets Vulnerable To Cyber Attack Implementing Cyber Risk Management Process
Classify Assets Vulnerable To Cyber Attack Implementing Cyber Risk Management ProcessThe following slide depicts some major assets that are more prone to cyber-attack. It mainly includes elements such as sales record, sales lead record, company internal database, customer and product information etc. Present the topic in a bit more detail with this Classify Assets Vulnerable To Cyber Attack Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Assets, Details, Comments. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
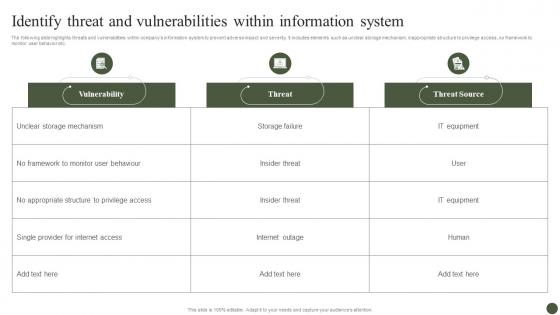 Identify Threat And Vulnerabilities Within Information Implementing Cyber Risk Management Process
Identify Threat And Vulnerabilities Within Information Implementing Cyber Risk Management ProcessThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Present the topic in a bit more detail with this Identify Threat And Vulnerabilities Within Information Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Vulnerability, Threat, Threat Source. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vulnerability Administration At Workplace Cyber Threats Management Dashboard
Vulnerability Administration At Workplace Cyber Threats Management DashboardThis slide portrays information regarding the dashboard that firm will use to manage cyber threats. The dashboard will provide clear picture of threats risks prevailing and how they are treated to technical engineers and board level executives. Deliver an outstanding presentation on the topic using this Vulnerability Administration At Workplace Cyber Threats Management Dashboard. Dispense information and present a thorough explanation of Management, Dashboard, Portrays Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
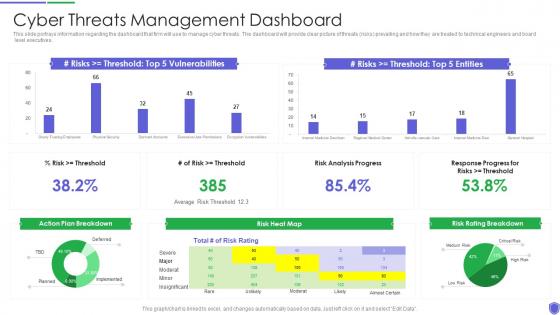 Cyber threats management managing critical threat vulnerabilities and security threats
Cyber threats management managing critical threat vulnerabilities and security threatsThis slide portrays information regarding the dashboard that firm will use to manage cyber threats. The dashboard will provide clear picture of threats risks prevailing and how they are treated to technical engineers and board level executives. Present the topic in a bit more detail with this Cyber Threats Management Managing Critical Threat Vulnerabilities And Security Threats. Use it as a tool for discussion and navigation on Cyber Threats Management Dashboard. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
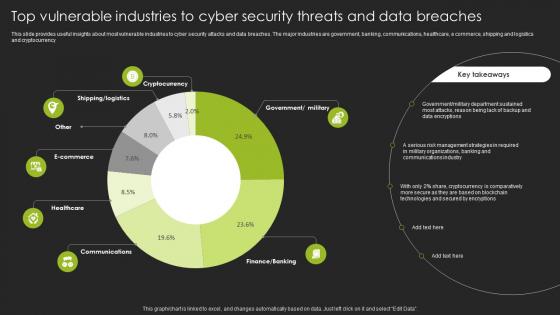 Top Vulnerable Industries To Cyber Security Threats And Data Breaches
Top Vulnerable Industries To Cyber Security Threats And Data BreachesThis slide provides useful insights about most vulnerable industries to cyber security attacks and data breaches. The major industries are government, banking, communications, healthcare, e commerce, shipping and logistics and cryptocurrency Introducing our Top Vulnerable Industries To Cyber Security Threats And Data Breaches set of slides. The topics discussed in these slides are Government, Department. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
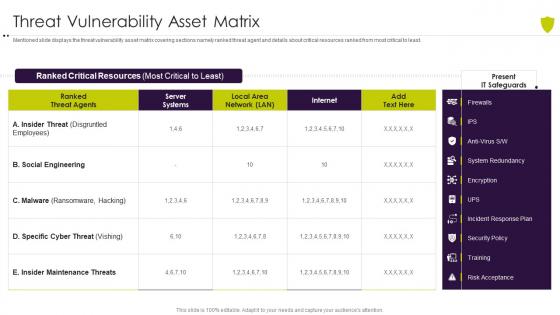 Threat vulnerability asset matrix managing cyber risk in a digital age
Threat vulnerability asset matrix managing cyber risk in a digital ageMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least. Present the topic in a bit more detail with this Threat Vulnerability Asset Matrix Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Threat Vulnerability Asset Matrix. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
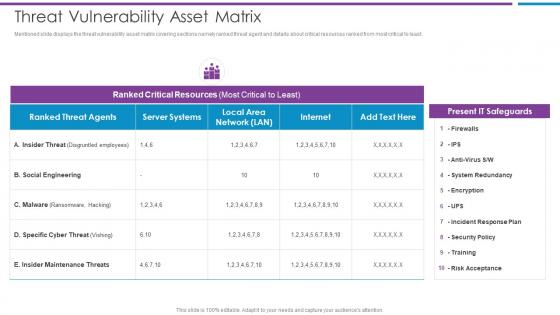 Threat Vulnerability Asset Matrix Risk Based Methodology To Cyber
Threat Vulnerability Asset Matrix Risk Based Methodology To CyberMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least.Present the topic in a bit more detail with this Threat Vulnerability Asset Matrix Risk Based Methodology To Cyber Use it as a tool for discussion and navigation on Social Engineering, Ranked Critical Resources, Present IT Safeguards This template is free to edit as deemed fit for your organization. Therefore download it now.
-
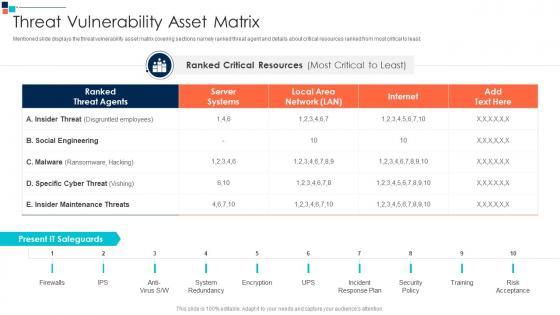 Threat Vulnerability Asset Matrix Introducing A Risk Based Approach To Cyber Security
Threat Vulnerability Asset Matrix Introducing A Risk Based Approach To Cyber SecurityMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least.Present the topic in a bit more detail with this Threat Vulnerability Asset Matrix Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on System Redundancy, Incident Response Plan, Security Policy This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vulnerability Cyber Security Ppt Powerpoint Presentation Icon Clipart Images Cpb
Vulnerability Cyber Security Ppt Powerpoint Presentation Icon Clipart Images CpbPresenting Vulnerability Cyber Security Ppt Powerpoint Presentation Icon Clipart Images Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Vulnerability Cyber Security. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
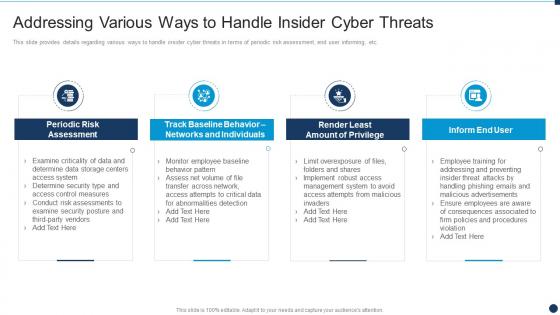 Various Ways To Handle Insider Cyber Threats Vulnerability Administration At Workplace
Various Ways To Handle Insider Cyber Threats Vulnerability Administration At WorkplaceThis slide provides details regarding various ways to handle insider cyber threats in terms of periodic risk assessment, end user informing, etc. Present the topic in a bit more detail with this Various Ways To Handle Insider Cyber Threats Vulnerability Administration At Workplace. Use it as a tool for discussion and navigation on Assessment, Individuals, Management This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vulnerability Administration At Workplace Contingency Plan For Cyber Threat Handling
Vulnerability Administration At Workplace Contingency Plan For Cyber Threat HandlingThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations Deliver an outstanding presentation on the topic using this Vulnerability Administration At Workplace Contingency Plan For Cyber Threat Handling. Dispense information and present a thorough explanation of Contingency Plan For Cyber Threat Handling using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Vulnerability Administration At Workplace Cyber Threats In Various Industries
Vulnerability Administration At Workplace Cyber Threats In Various IndustriesThis slide provides details regarding insider threats identified in various industries such as healthcare, manufacturing, government, energy, etc. Present the topic in a bit more detail with this Vulnerability Administration At Workplace Cyber Threats In Various Industries. Use it as a tool for discussion and navigation on Healthcare, Manufacturing, Government. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
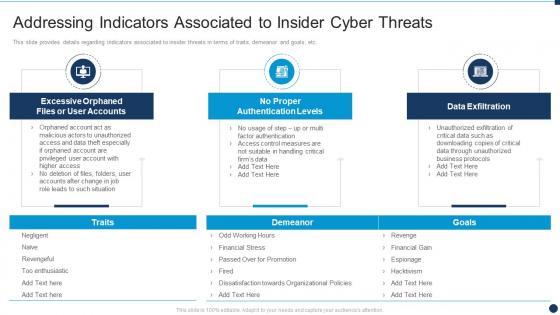 Vulnerability Administration At Workplace Indicators Associated To Insider Cyber Threats
Vulnerability Administration At Workplace Indicators Associated To Insider Cyber ThreatsThis slide provides details regarding indicators associated to insider threats in terms of traits, demeanor and goals, etc. Present the topic in a bit more detail with this Vulnerability Administration At Workplace Indicators Associated To Insider Cyber Threats. Use it as a tool for discussion and navigation on Associated, Authentication, Data Exfiltration . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
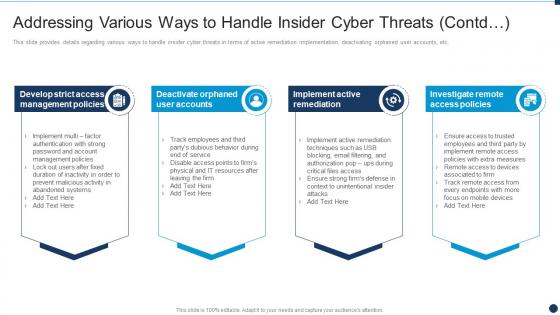 Vulnerability Administration At Workplace Various Ways To Handle Insider Cyber Threats Contd
Vulnerability Administration At Workplace Various Ways To Handle Insider Cyber Threats ContdThis slide provides details regarding various ways to handle insider cyber threats in terms of active remediation implementation, deactivating orphaned user accounts, etc. Increase audience engagement and knowledge by dispensing information using Vulnerability Administration At Workplace Various Ways To Handle Insider Cyber Threats Contd. This template helps you present information on four stages. You can also present information on Management Policies, Remediation, Investigate Remote using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Vulnerability Management Cyber Security In Powerpoint And Google Slides Cpb
Vulnerability Management Cyber Security In Powerpoint And Google Slides CpbPresenting Vulnerability Management Cyber Security In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Vulnerability Management Cyber Security. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Addressing cyber threats in managing critical threat vulnerabilities and security threats
Addressing cyber threats in managing critical threat vulnerabilities and security threatsThis slide provides details regarding insider threats identified in various industries such as healthcare, manufacturing, government, energy, etc. Increase audience engagement and knowledge by dispensing information using Addressing Cyber Threats In Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on four stages. You can also present information on Healthcare, Manufacturing, Government, Energy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Contingency plan for cyber managing critical threat vulnerabilities and security threats
Contingency plan for cyber managing critical threat vulnerabilities and security threatsThis slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Introducing Contingency Plan For Cyber Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Contingency Solutions, Contingency Considerations, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Environment Vulnerability Assessment In Powerpoint And Google Slides Cpb
Cyber Security Environment Vulnerability Assessment In Powerpoint And Google Slides CpbPresenting our Cyber Security Environment Vulnerability Assessment In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases eight stages. It is useful to share insightful information on Cyber Security Environment Vulnerability Assessment. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
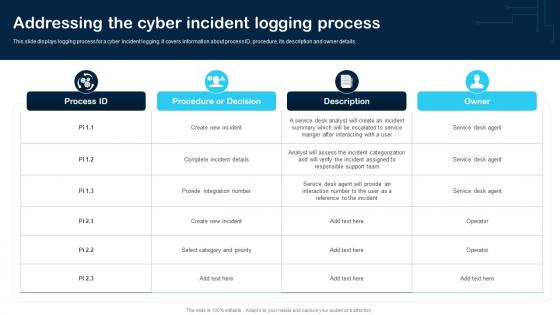 Addressing The Cyber Incident Logging Process Cybersecurity Incident And Vulnerability
Addressing The Cyber Incident Logging Process Cybersecurity Incident And VulnerabilityThis slide displays logging process for a cyber incident logging. It covers information about process ID, procedure, its description and owner details. Present the topic in a bit more detail with this Addressing The Cyber Incident Logging Process Cybersecurity Incident And Vulnerability. Use it as a tool for discussion and navigation on Create New Incident, Complete Incident Details, Category And Priority. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
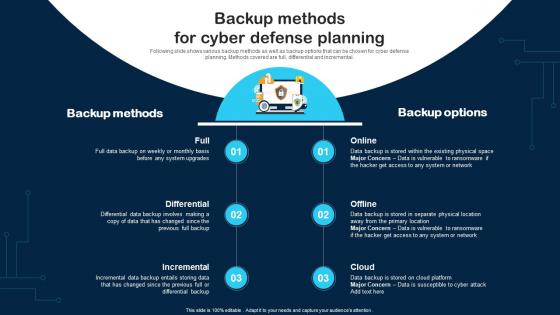 Backup Methods For Cyber Defense Planning Cybersecurity Incident And Vulnerability
Backup Methods For Cyber Defense Planning Cybersecurity Incident And VulnerabilityFollowing slide shows various backup methods as well as backup options that can be chosen for cyber defense planning. Methods covered are full, differential and incremental. Increase audience engagement and knowledge by dispensing information using Backup Methods For Cyber Defense Planning Cybersecurity Incident And Vulnerability. This template helps you present information on three stages. You can also present information on Backup Methods, Backup Options, Incremental using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Awareness Training Program Cybersecurity Incident And Vulnerability
Cyber Security Awareness Training Program Cybersecurity Incident And VulnerabilityPurpose of this slide is to provide information about the cyber security awareness training program to be conducted for in house team. It also provides the details about training types, content types and audience. Present the topic in a bit more detail with this Cyber Security Awareness Training Program Cybersecurity Incident And Vulnerability. Use it as a tool for discussion and navigation on Policy Based, Industry Specific Content, Generic Security Awareness. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
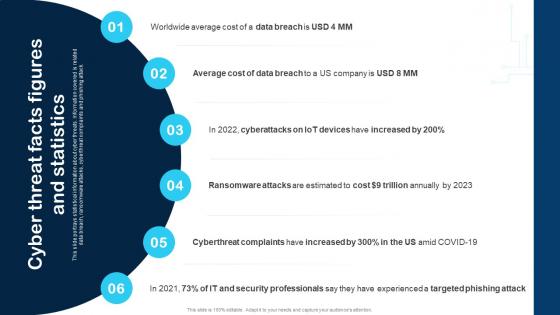 Cyber Threat Facts Figures And Statistics Cybersecurity Incident And Vulnerability
Cyber Threat Facts Figures And Statistics Cybersecurity Incident And VulnerabilityThis slide portrays statistical information about cyber threats. Information covered is related data breach, ransomware attacks, cyberthreat complaints and phishing attack. Increase audience engagement and knowledge by dispensing information using Cyber Threat Facts Figures And Statistics Cybersecurity Incident And Vulnerability. This template helps you present information on six stages. You can also present information on Data Breach, Cost, Security Professionals using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
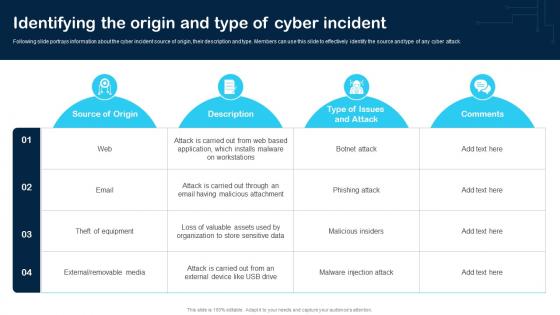 Identifying The Origin And Type Of Cyber Incident Cybersecurity Incident And Vulnerability
Identifying The Origin And Type Of Cyber Incident Cybersecurity Incident And VulnerabilityFollowing slide portrays information about the cyber incident source of origin, their description and type. Members can use this slide to effectively identify the source and type of any cyber attack. Deliver an outstanding presentation on the topic using this Identifying The Origin And Type Of Cyber Incident Cybersecurity Incident And Vulnerability. Dispense information and present a thorough explanation of Web, Email, Removable Media using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
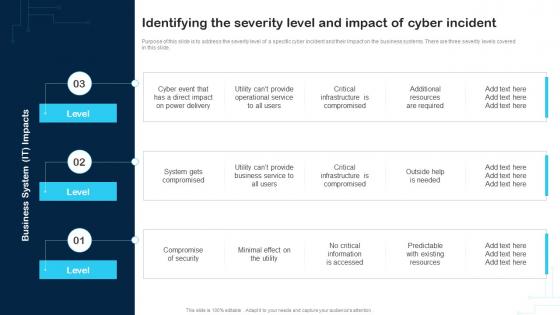 Identifying The Severity Level And Impact Of Cyber Incident Cybersecurity Incident And Vulnerability
Identifying The Severity Level And Impact Of Cyber Incident Cybersecurity Incident And VulnerabilityPurpose of this slide is to address the severity level of a specific cyber incident and their impact on the business systems. There are three severity levels covered in this slide. Introducing Identifying The Severity Level And Impact Of Cyber Incident Cybersecurity Incident And Vulnerability to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Compromise Of Security, Service, Business System, using this template. Grab it now to reap its full benefits.
-
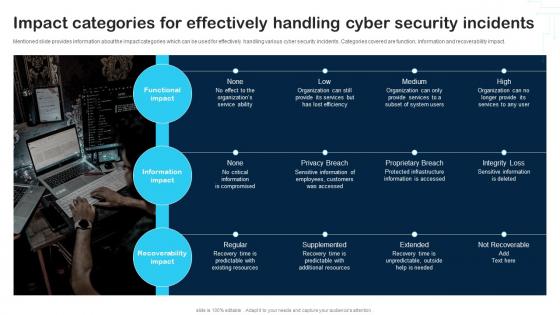 Impact Categories For Effectively Handling Cyber Security Incidents Cybersecurity Incident And Vulnerability
Impact Categories For Effectively Handling Cyber Security Incidents Cybersecurity Incident And VulnerabilityMentioned slide provides information about the impact categories which can be used for effectively handling various cyber security incidents. Categories covered are function, information and recoverability impact. Increase audience engagement and knowledge by dispensing information using Impact Categories For Effectively Handling Cyber Security Incidents Cybersecurity Incident And Vulnerability. This template helps you present information on three stages. You can also present information on Functional Impact, Information Impact, Recoverability Impact using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Performing Cyber Training Exercises For Securing The Assets Cybersecurity Incident And Vulnerability
Performing Cyber Training Exercises For Securing The Assets Cybersecurity Incident And VulnerabilityPurpose of this slide is to address and perform various cyber training exercises in order to secure companys assets. Exercises covered are defense in depth, capture the flag etc. Deliver an outstanding presentation on the topic using this Performing Cyber Training Exercises For Securing The Assets Cybersecurity Incident And Vulnerability. Dispense information and present a thorough explanation of Capture The Flag Event, Training, System Administrator using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
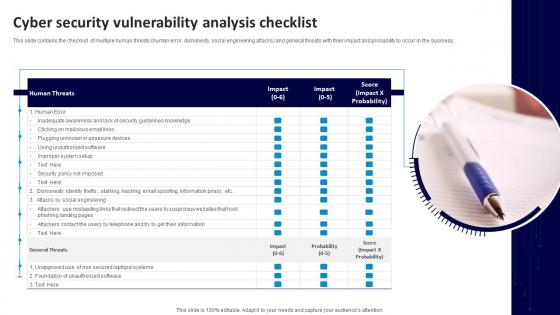 Cyber Security Vulnerability Analysis Checklist
Cyber Security Vulnerability Analysis ChecklistThis slide contains the checklist of multiple human threats human error, dishonesty, social engineering attacks and general threats with their impact and probability to occur in the business. Introducing our premium set of slides with Cyber Security Vulnerability Analysis Checklist. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Human Threats, General Threats, Unsecure Devices. So download instantly and tailor it with your information.
-
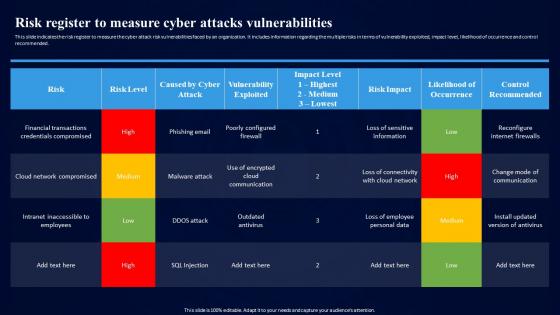 Cybersecurity Risk Assessment Program Risk Register To Measure Cyber Attacks Vulnerabilities
Cybersecurity Risk Assessment Program Risk Register To Measure Cyber Attacks VulnerabilitiesThis slide indicates the risk register to measure the cyber attack risk vulnerabilities faced by an organization. It includes information regarding the multiple risks in terms of vulnerability exploited, impact level, likelihood of occurrence and control recommended. Present the topic in a bit more detail with this Cybersecurity Risk Assessment Program Risk Register To Measure Cyber Attacks Vulnerabilities. Use it as a tool for discussion and navigation on Cyber Attacks, Vulnerabilities, Cloud Network Compromised, Outdated Antivirus. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Vulnerability In Powerpoint And Google Slides Cpb
Cyber Security Vulnerability In Powerpoint And Google Slides CpbPresenting our Cyber Security Vulnerability In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Cyber Security Vulnerability This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
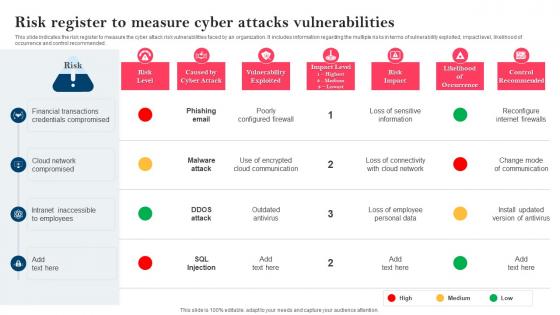 Strategy To Minimize Cyber Attacks Risk Register To Measure Cyber Attacks Vulnerabilities
Strategy To Minimize Cyber Attacks Risk Register To Measure Cyber Attacks VulnerabilitiesThis slide indicates the risk register to measure the cyber attack risk vulnerabilities faced by an organization. It includes information regarding the multiple risks in terms of vulnerability exploited, impact level, likelihood of occurrence and control recommended. Deliver an outstanding presentation on the topic using this Strategy To Minimize Cyber Attacks Risk Register To Measure Cyber Attacks Vulnerabilities. Dispense information and present a thorough explanation of Financial Transactions, Credentials Compromised, Cloud Network Compromised using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Reputational management organizational design methodology cyber vulnerability assessment cpb
Reputational management organizational design methodology cyber vulnerability assessment cpbPresenting this set of slides with name - Reputational Management Organizational Design Methodology Cyber Vulnerability Assessment Cpb. This is an editable three stages graphic that deals with topics like Reputational Management, Organizational Design Methodology, Cyber Vulnerability Assessment to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Cyber database security issues vulnerabilities ppt powerpoint presentation outline ideas cpb
Cyber database security issues vulnerabilities ppt powerpoint presentation outline ideas cpbPresenting this set of slides with name Cyber Database Security Issues Vulnerabilities Ppt Powerpoint Presentation Outline Ideas Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Cyber Database Security Issues Vulnerabilities to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
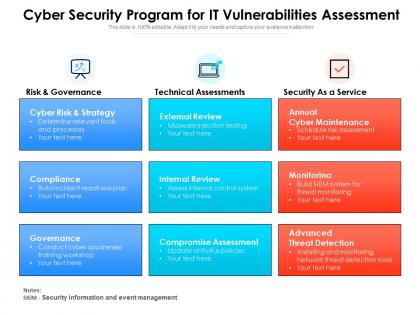 Cyber security program for it vulnerabilities assessment
Cyber security program for it vulnerabilities assessmentPresenting this set of slides with name Cyber Security Program For It Vulnerabilities Assessment. This is a three stage process. The stages in this process are Risk And Governance, Technical Assessments, Security As A Service. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Scanning system for vulnerability to cyber attack
Scanning system for vulnerability to cyber attackPresenting this set of slides with name Scanning System For Vulnerability To Cyber Attack. This is a three stage process. The stages in this process are Scanning System For Vulnerability To Cyber Attack. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 System vulnerability scanning for potential cyber attack
System vulnerability scanning for potential cyber attackPresenting this set of slides with name System Vulnerability Scanning For Potential Cyber Attack. This is a three stage process. The stages in this process are System Vulnerability Scanning For Potential Cyber Attack. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.

