Powerpoint Templates and Google slides for Cybercriminals
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
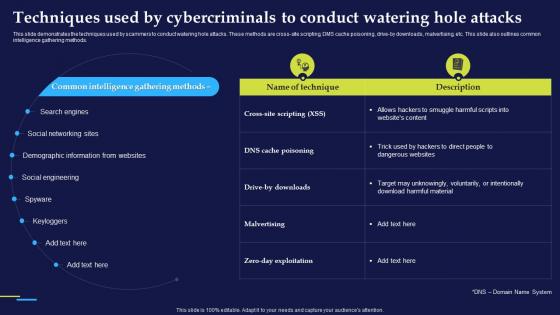 Phishing Attacks And Strategies To Mitigate Them V2 Techniques Used By Cybercriminals To Conduct
Phishing Attacks And Strategies To Mitigate Them V2 Techniques Used By Cybercriminals To ConductThis slide demonstrates the techniques used by scammers to conduct watering hole attacks. These methods are cross-site scripting, DMS cache poisoning, drive-by downloads, malvertising, etc. This slide also outlines common intelligence gathering methods. Present the topic in a bit more detail with this Phishing Attacks And Strategies To Mitigate Them V2 Techniques Used By Cybercriminals To Conduct. Use it as a tool for discussion and navigation on Social Networking Sites, Demographic Information From Websites, Social Engineering, Keyloggers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
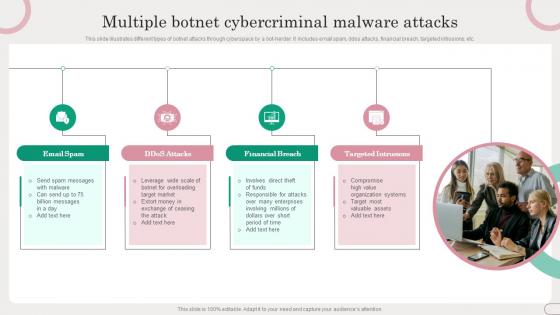 Multiple Botnet Cybercriminal Malware Attacks
Multiple Botnet Cybercriminal Malware AttacksThis slide illustrates different types of botnet attacks through cyberspace by a bot-herder. It includes email spam, ddos attacks, financial breach, targeted intrusions, etc. Presenting our set of slides with Multiple Botnet Cybercriminal Malware Attacks. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Email Spam, Financial Breach.
-
 Stages Of Botnet Malware Cybercriminal Attacks
Stages Of Botnet Malware Cybercriminal AttacksThis slide illustrates how to create a bot and orchestrating a botnet attack. It includes stages such as expose, infect and grow, activate, etc. Introducing our premium set of slides with Stages Of Botnet Malware Cybercriminal Attacks. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Expose, Infect And Grow, Activate. So download instantly and tailor it with your information.
-
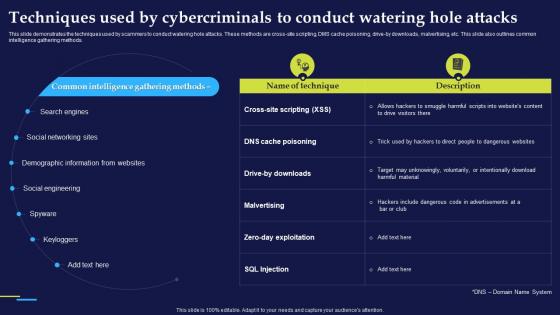 Techniques Used By Cybercriminals To Conduct Phishing Attacks And Strategies
Techniques Used By Cybercriminals To Conduct Phishing Attacks And StrategiesThis slide demonstrates the techniques used by scammers to conduct watering hole attacks. These methods are cross site scripting, DMS cache poisoning, drive by downloads, malvertising, etc. This slide also outlines common intelligence gathering methods.Deliver an outstanding presentation on the topic using this Techniques Used By Cybercriminals To Conduct Phishing Attacks And Strategies. Dispense information and present a thorough explanation of Demographic Information, Social Engineering, Include Dangerous using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.

