Powerpoint Templates and Google slides for Cybersecurity Risk Management
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Roadmap Cybersecurity Risk Analysis And Management Plan Ppt Show Graphics Example
Roadmap Cybersecurity Risk Analysis And Management Plan Ppt Show Graphics ExampleIntroducing Roadmap Cybersecurity Risk Analysis And Management Plan Ppt Show Graphics Example to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Roadmap, using this template. Grab it now to reap its full benefits.
-
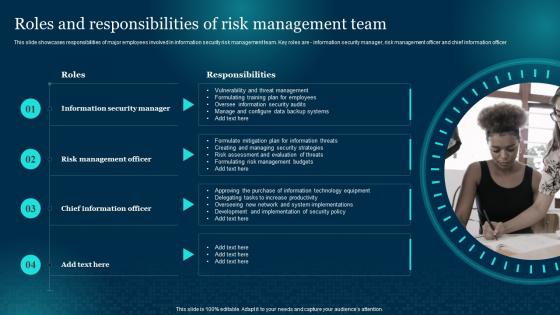 Roles And Responsibilities Of Risk Management Team Cybersecurity Risk Analysis And Management Plan
Roles And Responsibilities Of Risk Management Team Cybersecurity Risk Analysis And Management PlanThis slide showcases responsibilities of major employees involved in information security risk management team. Key roles are information security manager, risk management officer and chief information officer Deliver an outstanding presentation on the topic using this Roles And Responsibilities Of Risk Management Team Cybersecurity Risk Analysis And Management Plan. Dispense information and present a thorough explanation of Information Security Manager, Risk Management Officer, Chief Information Officer using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Selecting Suitable Software For Information Security Cybersecurity Risk Analysis And Management Plan
Selecting Suitable Software For Information Security Cybersecurity Risk Analysis And Management PlanThis slide showcases software that can help organization to monitor and manage the information security risk. It provides information about cyber risk quantification, vulnerability management, centralized repository for assets etc. Present the topic in a bit more detail with this Selecting Suitable Software For Information Security Cybersecurity Risk Analysis And Management Plan. Use it as a tool for discussion and navigation on Software, Information, Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Steps For Information Security Risk Management Cybersecurity Risk Analysis And Management Plan
Steps For Information Security Risk Management Cybersecurity Risk Analysis And Management PlanThis slide steps which can help organization to implement information security risk management program in organization. Its key steps are identify, protect, detect and respond Deliver an outstanding presentation on the topic using this Steps For Information Security Risk Management Cybersecurity Risk Analysis And Management Plan. Dispense information and present a thorough explanation of Information, Management, Awareness And Training using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Swot Analysis Cybersecurity Risk Analysis And Management Plan Ppt Show Graphics Design
Swot Analysis Cybersecurity Risk Analysis And Management Plan Ppt Show Graphics DesignIntroducing Swot Analysis Cybersecurity Risk Analysis And Management Plan Ppt Show Graphics Design to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Strengths, Weaknesses, Opportunities, using this template. Grab it now to reap its full benefits.
-
 Thanks For Watching Cybersecurity Risk Analysis And Management Plan
Thanks For Watching Cybersecurity Risk Analysis And Management PlanIntroducing Thanks For Watching Cybersecurity Risk Analysis And Management Plan to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Thanks For Watching, using this template. Grab it now to reap its full benefits.
-
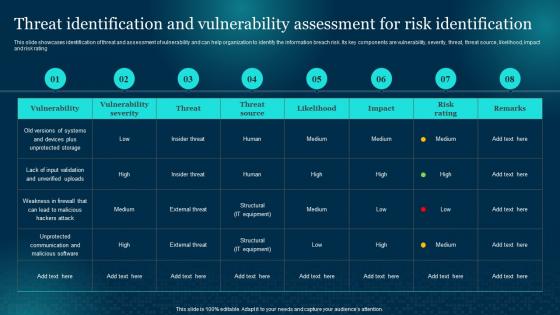 Threat Identification And Vulnerability Assessment For Cybersecurity Risk Analysis And Management Plan
Threat Identification And Vulnerability Assessment For Cybersecurity Risk Analysis And Management PlanThis slide showcases identification of threat and assessment of vulnerability and can help organization to identify the information breach risk. Its key components are vulnerability, severity, threat, threat source, likelihood, impact and risk rating Deliver an outstanding presentation on the topic using this Threat Identification And Vulnerability Assessment For Cybersecurity Risk Analysis And Management Plan. Dispense information and present a thorough explanation of Identification, Assessment, Vulnerability using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Timeline For Information Security Risk Management Cybersecurity Risk Analysis And Management Plan
Timeline For Information Security Risk Management Cybersecurity Risk Analysis And Management PlanThis slide showcases timeline that can help organization to conduct training for information security risk management programme. It also showcases weekly and step progress Present the topic in a bit more detail with this Timeline For Information Security Risk Management Cybersecurity Risk Analysis And Management Plan. Use it as a tool for discussion and navigation on Timeline, Information, Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Venn Cybersecurity Risk Analysis And Management Plan Ppt Show Example Introduction
Venn Cybersecurity Risk Analysis And Management Plan Ppt Show Example IntroductionIntroducing Venn Cybersecurity Risk Analysis And Management Plan Ppt Show Example Introduction to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Venn, using this template. Grab it now to reap its full benefits.
-
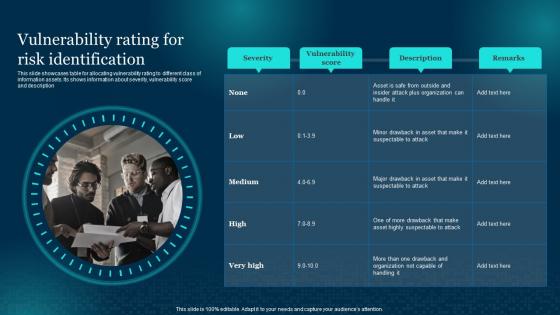 Vulnerability Rating For Risk Identification Cybersecurity Risk Analysis And Management Plan
Vulnerability Rating For Risk Identification Cybersecurity Risk Analysis And Management PlanThis slide showcases table for allocating vulnerability rating to different class of information assets. Its shows information about severity, vulnerability score and description Deliver an outstanding presentation on the topic using this Vulnerability Rating For Risk Identification Cybersecurity Risk Analysis And Management Plan. Dispense information and present a thorough explanation of Vulnerability, Identification, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Allocating Budget For Information Security Risk Management Formulating Cybersecurity Plan
Allocating Budget For Information Security Risk Management Formulating Cybersecurity PlanThis slide showcase budget to be allocated for conducting training for information security risk management. It showcases budget for areas like cybersecurity awareness, threat detection and risk management. Increase audience engagement and knowledge by dispensing information using Allocating Budget For Information Security Risk Management Formulating Cybersecurity Plan. This template helps you present information on two stages. You can also present information on Cybersecurity Awareness, Incident Management, Threat Detection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
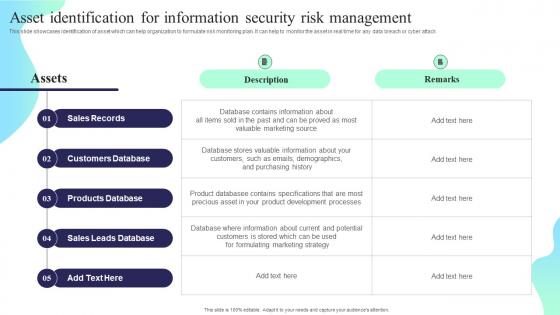 Asset Identification For Information Security Risk Management Formulating Cybersecurity Plan
Asset Identification For Information Security Risk Management Formulating Cybersecurity PlanThis slide showcases identification of asset which can help organization to formulate risk monitoring plan. It can help to monitor the asset in real time for any data breach or cyber attack. Deliver an outstanding presentation on the topic using this Asset Identification For Information Security Risk Management Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Sales Records, Customers Database, Products Database using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
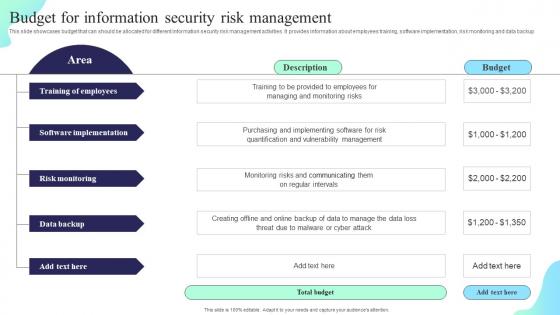 Budget For Information Security Risk Management Formulating Cybersecurity Plan
Budget For Information Security Risk Management Formulating Cybersecurity PlanThis slide showcases budget that can should be allocated for different information security risk management activities. It provides information about employees training, software implementation, risk monitoring and data backup. Deliver an outstanding presentation on the topic using this Budget For Information Security Risk Management Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Training Of Employees, Software Implementation, Risk Monitoring using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
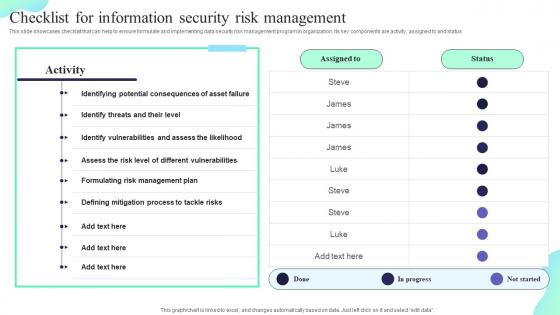 Checklist For Information Security Risk Management Formulating Cybersecurity Plan
Checklist For Information Security Risk Management Formulating Cybersecurity PlanThis slide showcases checklist that can help to ensure formulate and implementing data security risk management program in organization. Its key components are activity, assigned to and status. Present the topic in a bit more detail with this Checklist For Information Security Risk Management Formulating Cybersecurity Plan. Use it as a tool for discussion and navigation on Identifying Potential, Different Vulnerabilities, Risk Management Plan. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
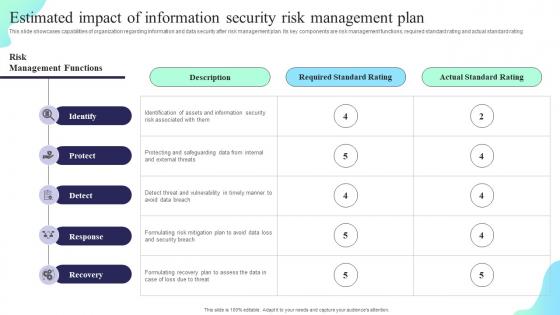 Estimated Impact Of Information Security Risk Management Plan Formulating Cybersecurity Plan
Estimated Impact Of Information Security Risk Management Plan Formulating Cybersecurity PlanThis slide showcases capabilities of organization regarding information and data security after risk management plan. Its key components are risk management functions, required standard rating and actual standard rating. Deliver an outstanding presentation on the topic using this Estimated Impact Of Information Security Risk Management Plan Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Identify, Protect, Detect, Response using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
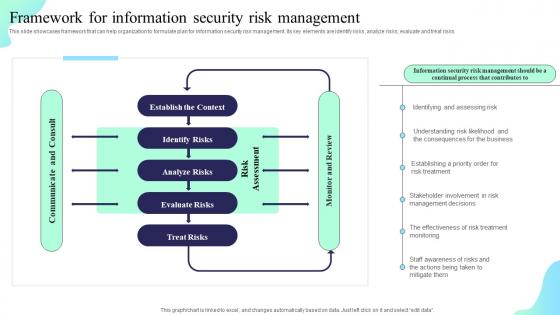 Framework For Information Security Risk Management Formulating Cybersecurity Plan
Framework For Information Security Risk Management Formulating Cybersecurity PlanThis slide showcases framework that can help organization to formulate plan for information security risk management. Its key elements are identify risks, analyze risks, evaluate and treat risks. Deliver an outstanding presentation on the topic using this Framework For Information Security Risk Management Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Establish The Context, Identify Risks, Analyze Risks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
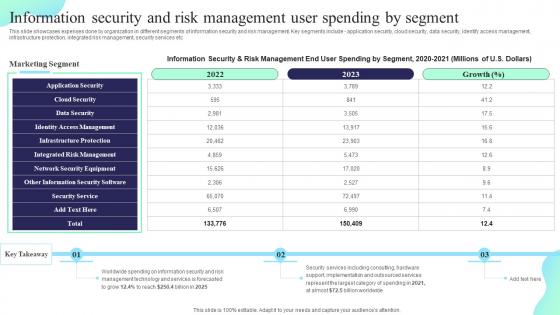 Information Security And Risk Management User Spending Formulating Cybersecurity Plan
Information Security And Risk Management User Spending Formulating Cybersecurity PlanThis slide showcases expenses done by organization in different segments of information security and risk management. Key segments include application security, cloud security, data security, identify access management, infrastructure protection, integrated risk management, security services etc. Deliver an outstanding presentation on the topic using this Information Security And Risk Management User Spending Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Application Security, Identity Access Management, Integrated Risk Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
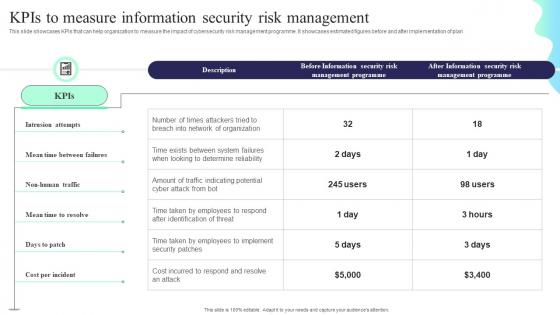 KPIS To Measure Information Security Risk Management Formulating Cybersecurity Plan
KPIS To Measure Information Security Risk Management Formulating Cybersecurity PlanThis slide showcases KPIs that can help organization to measure the impact of cybersecurity risk management programme. It showcases estimated figures before and after implementation of plan. Deliver an outstanding presentation on the topic using this KPIS To Measure Information Security Risk Management Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Intrusion Attempts, Mean Time Between Failures, Mean Time To Resolve using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Matrix For Threat Solution And Risk Management Formulating Cybersecurity Plan
Matrix For Threat Solution And Risk Management Formulating Cybersecurity PlanThis slide showcases matrix that can help organization to formulate solutions for different types of information security attacks. It can help organization to mitigate the risks and safeguard information in case of any attack. Deliver an outstanding presentation on the topic using this Matrix For Threat Solution And Risk Management Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Block Malicious, Monitor Database Activity, Validate Database Protocols using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Probability Assessment Matrix For Risk Management Formulating Cybersecurity Plan
Probability Assessment Matrix For Risk Management Formulating Cybersecurity PlanThis slide showcase matrix that can help organization to identify the probability of different information security attacks and formulate mitigation strategy in advance. It can help organization to manage the major risks and safeguard the information. Present the topic in a bit more detail with this Probability Assessment Matrix For Risk Management Formulating Cybersecurity Plan. Use it as a tool for discussion and navigation on Probability, Assessment Matrix, Risk Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
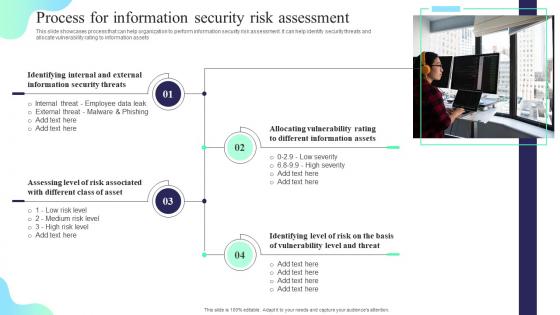 Process For Information Security Risk Assessment Formulating Cybersecurity Plan
Process For Information Security Risk Assessment Formulating Cybersecurity PlanThis slide showcases process that can help organization to perform information security risk assessment. It can help identify security threats and allocate vulnerability rating to information assets. Introducing Process For Information Security Risk Assessment Formulating Cybersecurity Plan to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Identifying Internal, Information Security Threats, Information Assets, using this template. Grab it now to reap its full benefits.
-
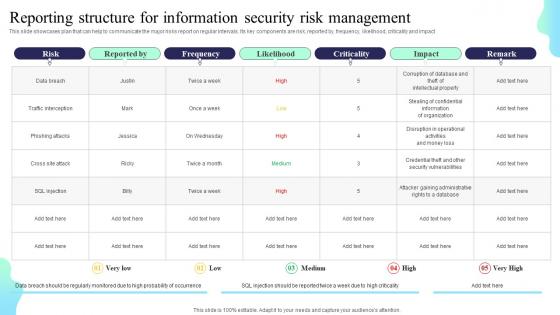 Reporting Structure For Information Security Risk Management Formulating Cybersecurity Plan
Reporting Structure For Information Security Risk Management Formulating Cybersecurity PlanThis slide showcases plan that can help to communicate the major risks report on regular intervals. Its key components are risk, reported by, frequency, likelihood, criticality and impact. Present the topic in a bit more detail with this Reporting Structure For Information Security Risk Management Formulating Cybersecurity Plan. Use it as a tool for discussion and navigation on Reporting Structure, Information Security, Risk Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
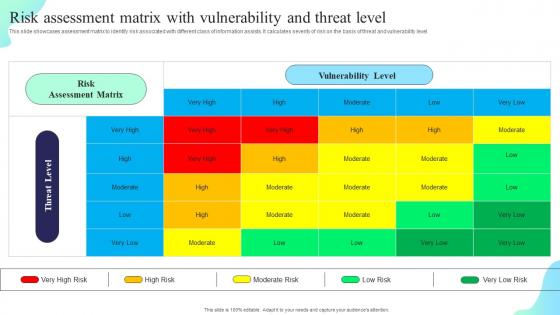 Risk Assessment Matrix With Vulnerability And Threat Level Formulating Cybersecurity Plan
Risk Assessment Matrix With Vulnerability And Threat Level Formulating Cybersecurity PlanThis slide showcases assessment matrix to identify risk associated with different class of information assists. It calculates severity of risk on the basis of threat and vulnerability level. Present the topic in a bit more detail with this Risk Assessment Matrix With Vulnerability And Threat Level Formulating Cybersecurity Plan. Use it as a tool for discussion and navigation on Risk Assessment Matrix, Vulnerability Level. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Steps For Information Security Risk Management Formulating Cybersecurity Plan
Steps For Information Security Risk Management Formulating Cybersecurity PlanThis slide showcase steps which can help organization to implement information security risk management program in organization. Its key steps are identify, protect, detect and respond. Deliver an outstanding presentation on the topic using this Steps For Information Security Risk Management Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Asset Identification, Risk Assessment, Awareness And Training using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
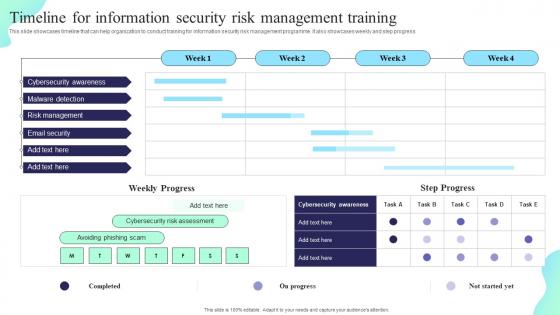 Timeline For Information Security Risk Management Training Formulating Cybersecurity Plan
Timeline For Information Security Risk Management Training Formulating Cybersecurity PlanThis slide showcases timeline that can help organization to conduct training for information security risk management programme. It also showcases weekly and step progress. Deliver an outstanding presentation on the topic using this Timeline For Information Security Risk Management Training Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Cybersecurity Awareness, Malware Detection, Risk Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Vulnerability Rating For Risk Identification Formulating Cybersecurity Plan
Vulnerability Rating For Risk Identification Formulating Cybersecurity PlanThis slide showcases table for allocating vulnerability rating to different class of information assets. It shows information about severity, vulnerability score and description. Introducing Vulnerability Rating For Risk Identification Formulating Cybersecurity Plan to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Vulnerability Score, Risk Identification, using this template. Grab it now to reap its full benefits.
-
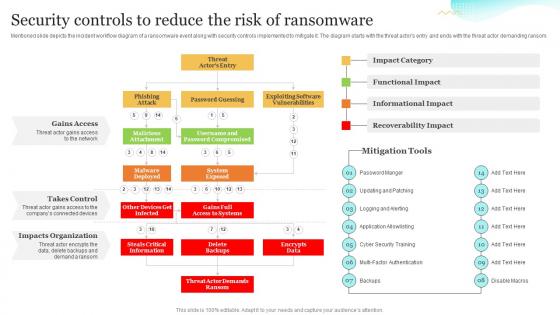 Security Controls To Reduce The Risk Of Ransomware Upgrading Cybersecurity With Incident Response Playbook
Security Controls To Reduce The Risk Of Ransomware Upgrading Cybersecurity With Incident Response PlaybookMentioned slide depicts the incident workflow diagram of a ransomware event along with security controls implemented to mitigate it. The diagram starts with the threat actors entry and ends with the threat actor demanding ransom. Present the topic in a bit more detail with this Security Controls To Reduce The Risk Of Ransomware Upgrading Cybersecurity With Incident Response Playbook. Use it as a tool for discussion and navigation on Ransomware, Informational Impact, Recoverability Impact. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cybersecurity Management Icon Showcasing Risk Assessment Checklist
Cybersecurity Management Icon Showcasing Risk Assessment ChecklistPresenting our set of slides with name Cybersecurity Management Icon Showcasing Risk Assessment Checklist. This exhibits information on three stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cybersecurity, Management, Assessment.
-
 Cybersecurity Risk Management Implementation Process
Cybersecurity Risk Management Implementation ProcessThe following slide explains implementation method for cybersecurity risk management for the organization to ensure protection of key business data. It includes steps such as categorize, security controls, implementation, assess, etc. Presenting our set of slides with name Cybersecurity Risk Management Implementation Process. This exhibits information on six stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Categorize System, Security Controls, Implementation .
-
 Cybersecurity Risk Management Plan Implementation Stages
Cybersecurity Risk Management Plan Implementation StagesThis slide explains various steps for implementation of cybersecurity risk management plan in the organization to ensure time and budget compliance. It includes elements such as current state analysis, assessment, target state, etc. Presenting our set of slides with name Cybersecurity Risk Management Plan Implementation Stages. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Current State Analysis, Assessment, Target State .
-
 Cybersecurity Risk Management Process For Organization
Cybersecurity Risk Management Process For OrganizationThis slide displays flow diagram to illustrate cybersecurity risk management process to ensure continuous monitoring. It includes components such as threats, vulnerabilities, impacts, intelligence, etc. Introducing our Cybersecurity Risk Management Process For Organization set of slides. The topics discussed in these slides are Cybersecurity, Management, Process. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Icon Showcasing Cybersecurity Management And Risk Analysis
Icon Showcasing Cybersecurity Management And Risk AnalysisPresenting our set of slides with name Icon Showcasing Cybersecurity Management And Risk Analysis. This exhibits information on three stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cybersecurity, Management, Analysis.
-
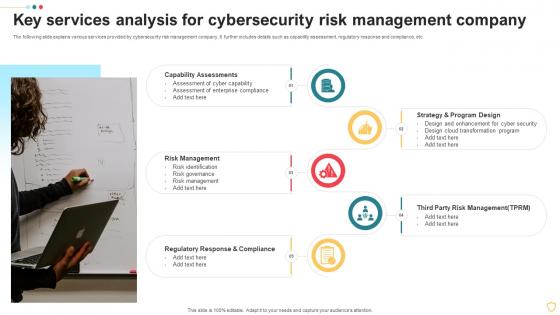 Key Services Analysis For Cybersecurity Risk Management Company
Key Services Analysis For Cybersecurity Risk Management CompanyThe following slide explains various services provided by cybersecurity risk management company. It further includes details such as capability assessment, regulatory response and compliance, etc. Presenting our set of slides with name Key Services Analysis For Cybersecurity Risk Management Company. This exhibits information on five stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Capability Assessments, Risk Management, Strategy Program Design.
-
 Strategic Risk Assessment Framework For Cybersecurity Management
Strategic Risk Assessment Framework For Cybersecurity ManagementThis slide showcases flow diagram to plan efficient management of cybersecurity risks for the organization for threat reduction. It includes steps such as understanding company strategies, data gathering, preliminary risk profiling, action plan, etc. Presenting our set of slides with name Strategic Risk Assessment Framework For Cybersecurity Management. This exhibits information on seven stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Strategic, Assessment, Framework.
-
 Cybersecurity Risk In Powerpoint And Google Slides Cpb
Cybersecurity Risk In Powerpoint And Google Slides CpbPresenting our Cybersecurity Risk In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Cybersecurity Risk. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
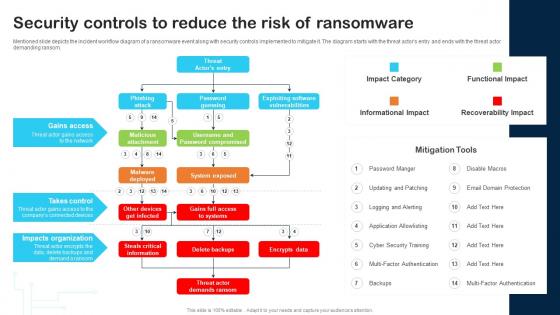 Security Controls To Reduce The Risk Of Ransomware Cybersecurity Incident And Vulnerability
Security Controls To Reduce The Risk Of Ransomware Cybersecurity Incident And VulnerabilityMentioned slide depicts the incident workflow diagram of a ransomware event along with security controls implemented to mitigate it. The diagram starts with the threat actors entry and ends with the threat actor demanding ransom. Deliver an outstanding presentation on the topic using this Security Controls To Reduce The Risk Of Ransomware Cybersecurity Incident And Vulnerability. Dispense information and present a thorough explanation of Gains Access, Takes Control, Impacts Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Approaches To Overcome Cybersecurity Risk Faced By Real Estate Company Managing Various Risks
Approaches To Overcome Cybersecurity Risk Faced By Real Estate Company Managing Various RisksThe following slide exhibits various approaches which can be used to prevent cybersecurity risk faced by the real estate enterprise. The key approaches highlighted in the slide are updating the security system, installing anti-phishing add ons, using a customized web application firewall etc. Deliver an outstanding presentation on the topic using this Approaches To Overcome Cybersecurity Risk Faced By Real Estate Company Managing Various Risks. Dispense information and present a thorough explanation of Ransomware, Business Email Compromise, Goal using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
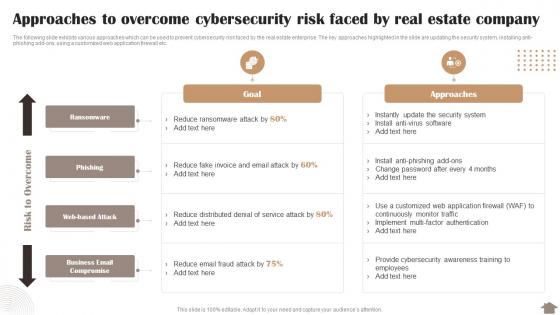 Risk Reduction Strategies Stakeholders Approaches To Overcome Cybersecurity Risk Faced By Real Estate Company
Risk Reduction Strategies Stakeholders Approaches To Overcome Cybersecurity Risk Faced By Real Estate CompanyThe following slide exhibits various approaches which can be used to prevent cybersecurity risk faced by the real estate enterprise. The key approaches highlighted in the slide are updating the security system, installing anti-phishing add-ons, using a customized web application firewall etc. Deliver an outstanding presentation on the topic using this Risk Reduction Strategies Stakeholders Approaches To Overcome Cybersecurity Risk Faced By Real Estate Company. Dispense information and present a thorough explanation of Approaches, Cybersecurity, Ransomware using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cybersecurity Risks Of An Escalating Russia Ukraine Conflict String Of Cyber Attacks Against
Cybersecurity Risks Of An Escalating Russia Ukraine Conflict String Of Cyber Attacks AgainstThis slide represents the cybersecurity risks associated with russia and ukraine conflict that are the most serious cyber threat, and many organizations are advised to take precautions. Introducing Cybersecurity Risks Of An Escalating Russia Ukraine Conflict String Of Cyber Attacks Against to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Cyber Capabilities, Economic Warfare, Cybersecurity, using this template. Grab it now to reap its full benefits.
-
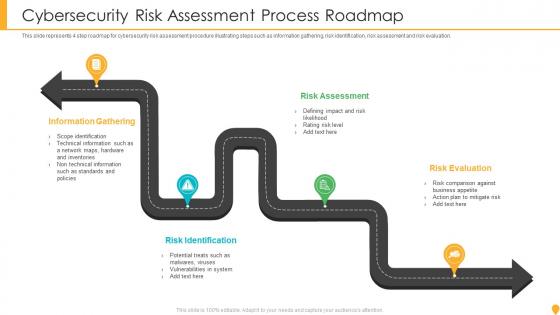 Cybersecurity Risk Assessment Process Roadmap
Cybersecurity Risk Assessment Process RoadmapThis slide represents 4 step roadmap for cybersecurity risk assessment procedure illustrating steps such as information gathering, risk identification, risk assessment and risk evaluation. Presenting our set of slides with name Cybersecurity Risk Assessment Process Roadmap. This exhibits information on four stages of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Information Gathering, Risk Assessment, Risk Identification, Risk Evaluation.
-
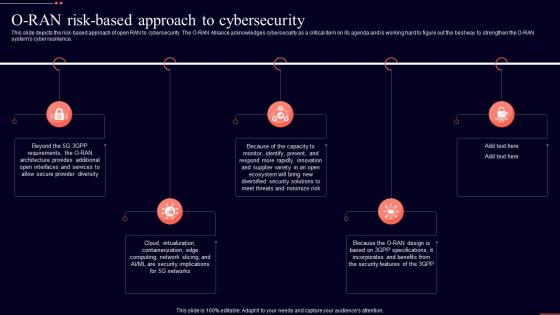 O Ran Risk Based Approach To Cybersecurity Open Ran It Ppt Show Graphics Download
O Ran Risk Based Approach To Cybersecurity Open Ran It Ppt Show Graphics DownloadThis slide depicts the risk-based approach of open RAN to cybersecurity. The O-RAN Alliance acknowledges cybersecurity as a critical item on its agenda and is working hard to figure out the best way to strengthen the O-RAN systems cyber resilience. Introducing O Ran Risk Based Approach To Cybersecurity Open Ran It Ppt Show Graphics Download to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Approach, Cybersecurity, Incorporates, using this template. Grab it now to reap its full benefits.
-
 Cybersecurity Risk Assessment And Strategic Mitigation Plan
Cybersecurity Risk Assessment And Strategic Mitigation PlanThis slide represents the identified cyber security risks to help the organizations in identifying and prioritizing areas to improve cybersecurity program. It includes details related to cyber security threats, risks, risk priority, mitigation plan, risk owner and risk deduction timeline. Presenting our well structured Cybersecurity Risk Assessment And Strategic Mitigation Plan. The topics discussed in this slide are Risk, Risk Priority, Risk Mitigation Plan . This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
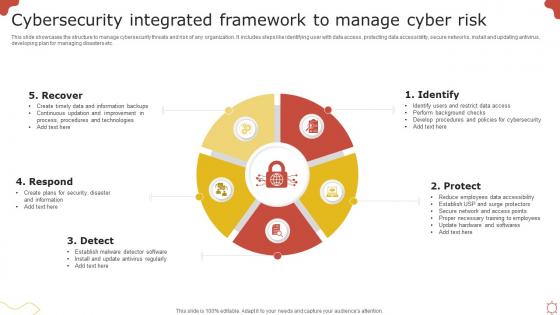 Cybersecurity Integrated Framework To Manage Cyber Risk
Cybersecurity Integrated Framework To Manage Cyber RiskThis slide showcases the structure to manage cybersecurity threats and risk of any organization. It includes steps like identifying user with data access, protecting data accessibility, secure networks, install and updating antivirus, developing plan for managing disasters etc. Introducing our premium set of slides with Cybersecurity Integrated Framework To Manage Cyber Risk. Elucidate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Recover, Respond, Detect, Protect, Identify. So download instantly and tailor it with your information.
-
 Risk And Threats Landscape In Business Cybersecurity
Risk And Threats Landscape In Business CybersecurityThis slide showcases risk and threats landscape which can be referred by businesses to be aware of cybersecurity issues and attacks. It contains information about phishing, malware and blackmail hacking. Presenting our set of slides with Risk And Threats Landscape In Business Cybersecurity. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Phishing, Malware, Blackmail Hacking.
-
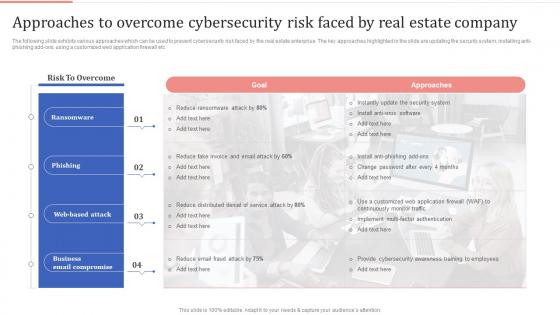 Approaches To Overcome Cybersecurity Risk Faced By Real Estate Optimizing Process Improvement
Approaches To Overcome Cybersecurity Risk Faced By Real Estate Optimizing Process ImprovementThe following slide exhibits various approaches which can be used to prevent cybersecurity risk faced by the real estate enterprise. The key approaches highlighted in the slide are updating the security system, installing anti-phishing add ons, using a customized web application firewall etc. Present the topic in a bit more detail with this Approaches To Overcome Cybersecurity Risk Faced By Real Estate Optimizing Process Improvement. Use it as a tool for discussion and navigation on Ransomware, Phishing, Business Email Compromise. This template is free to edit as deemed fit for your organization. Therefore download it now
-
 Cybersecurity Risks In Powerpoint And Google Slides Cpb
Cybersecurity Risks In Powerpoint And Google Slides CpbPresenting Cybersecurity Risks In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cybersecurity Risks. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
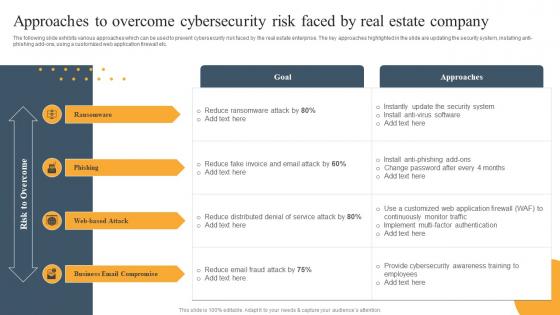 Approaches To Overcome Cybersecurity Risk Mitigation Techniques For Real Estate Firm
Approaches To Overcome Cybersecurity Risk Mitigation Techniques For Real Estate FirmThe following slide exhibits various approaches which can be used to prevent cybersecurity risk faced by the real estate enterprise. The key approaches highlighted in the slide are updating the security system, installing anti phishing add ons, using a customized web application firewall etc. Present the topic in a bit more detail with this Approaches To Overcome Cybersecurity Risk Mitigation Techniques For Real Estate Firm. Use it as a tool for discussion and navigation on Risk To Overcome, Web Based Attack, Business Email Compromise. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
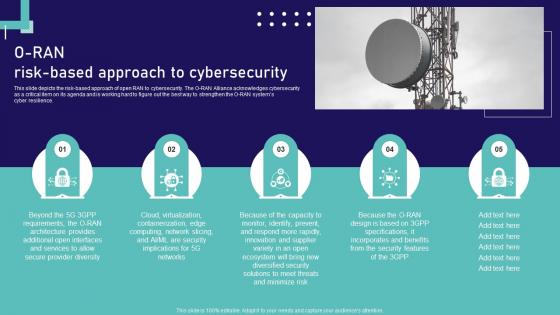 Open Ran Technology O Ran Risk Based Approach To Cybersecurity Ppt Professional Shapes
Open Ran Technology O Ran Risk Based Approach To Cybersecurity Ppt Professional ShapesThis slide depicts the risk-based approach of open RAN to cybersecurity. The O-RAN Alliance acknowledges cybersecurity as a critical item on its agenda and is working hard to figure out the best way to strengthen the O-RAN systems cyber resilience. Increase audience engagement and knowledge by dispensing information using Open Ran Technology O Ran Risk Based Approach To Cybersecurity Ppt Professional Shapes. This template helps you present information on five stages. You can also present information on Cybersecurity, Approach, Containerization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cybersecurity Framework To Manage Cyber Risk
Cybersecurity Framework To Manage Cyber RiskThis slide showcases structure to manage cybersecurity threats and risk of any organization. It includes steps like identifying user with data access, protecting data accessibility, secure networks, install and updating antivirus, developing plan for managing disasters etc Introducing our premium set of slides with Cybersecurity Framework To Manage Cyber Risk. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Recover, Respond, Identify. So download instantly and tailor it with your information.
-
 Strategic Management Plan For Cybersecurity Risk
Strategic Management Plan For Cybersecurity RiskThis slide deals with the formation of cyber security risk management program to identify, eliminate and minimize cyber threat. The steps involved are business alignment, defining program, program development, metrics, monitoring Presenting our set of slides with Strategic Management Plan For Cybersecurity Risk. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Business, Program, Development.
-
 O RAN Risk based Approach To Cybersecurity Open RAN Alliance
O RAN Risk based Approach To Cybersecurity Open RAN AllianceThis slide depicts the risk-based approach of open RAN to cybersecurity. The O-RAN Alliance acknowledges cybersecurity as a critical item on its agenda and is working hard to figure out the best way to strengthen the O-RAN systems cyber resilience.Increase audience engagement and knowledge by dispensing information using O RAN Risk based Approach To Cybersecurity Open RAN Alliance. This template helps you present information onfive stages. You can also present information on Secure Provider Diversity, Open Interfaces, Architecture Provides using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cybersecurity Risk Management Program Framework
Cybersecurity Risk Management Program FrameworkThis slide showcases a cyber security risk management framework to increase system capability to protect, detect and react under uncertain security threats. It includes steps such as categorize system, select security control, apply security controls, evaluate security controls, etc. Presenting our set of slides with Cybersecurity Risk Management Program Framework. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Categorise System, Select Security Controls, Apply Security Controls.
-
 O RAN Risk Based Approach To Cybersecurity
O RAN Risk Based Approach To CybersecurityThis slide depicts the risk-based approach of open RAN to cybersecurity. The O-RAN Alliance acknowledges cybersecurity as a critical item on its agenda and is working hard to figure out the best way to strengthen the O-RAN systems cyber resilience. Introducing O Ran Risk Based Approach To Cybersecurity to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Provider Diversity, Security Implications, Incorporates using this template. Grab it now to reap its full benefits.
-
 Core Operations Of Cybersecurity Risk Management System
Core Operations Of Cybersecurity Risk Management SystemThe following slide illustrates major functions of cyber security risk administration to address and respond organizational threats. It includes elements such as identify, protect, detect, respond and recover etc. Presenting our set of slides with Core Operations Of Cybersecurity Risk Management System. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identify, Protect, Respond.
-
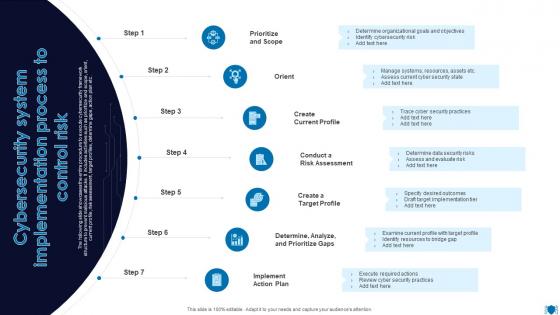 Cybersecurity System Implementation Process To Control Risk
Cybersecurity System Implementation Process To Control RiskThe following slide showcases the entire procedure to execute cybersecurity framework structure to prevent malicious attacks. It includes activities such as prioritize and scope, orient, current profile, risk assessment, target profiles, determine gaps, action plan etc. Presenting our set of slides with Cybersecurity System Implementation Process To Control Risk. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Create Current Profile, Determine, Analyze, Prioritize Gaps.
-
 Cybersecurity Risk Assessment System Icon
Cybersecurity Risk Assessment System IconPresenting our set of slides with Cybersecurity Risk Assessment System Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cybersecurity, Risk Assessment, Framework Icon.
-
 Elements Of Cybersecurity Risk Administration System
Elements Of Cybersecurity Risk Administration SystemThe following slide showcases the components of cybersecurity framework to assess industry standards and manage risks. It includes elements namely, core, tiers and profile etc. Introducing our premium set of slides with Elements Of Elements Of Cybersecurity Risk Administration System. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Framework Core, Framework Tiers, Framework Profile. So download instantly and tailor it with your information.
-
 K56 Cybersecurity Risk Assessment Program To Strengthen Organization Security For Table Of Contents
K56 Cybersecurity Risk Assessment Program To Strengthen Organization Security For Table Of ContentsIntroducing K56 Cybersecurity Risk Assessment Program To Strengthen Organization Security For Table Of Contents to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Cybersecurity, Risk Assessment Program, Strengthen Organization Security, using this template. Grab it now to reap its full benefits.
-
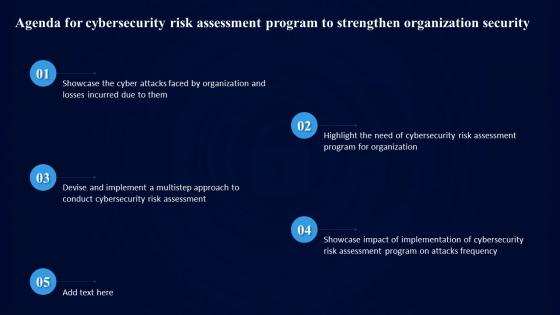 Agenda For Cybersecurity Risk Assessment Program To Strengthen Organization Security
Agenda For Cybersecurity Risk Assessment Program To Strengthen Organization SecurityIntroducing Agenda For Cybersecurity Risk Assessment Program To Strengthen Organization Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Cybersecurity, Risk Assessment Program, Strengthen Organization Security, using this template. Grab it now to reap its full benefits.
-
 Cybersecurity Risk Assessment Cyber Security Risk Assessment Program Implementation Impact
Cybersecurity Risk Assessment Cyber Security Risk Assessment Program Implementation ImpactThe purpose of the following slide is to highlight the impact of impact of risk assessment on cyber crime attacks. It compares the number of security incident occurred in two consecutive months and highlight the prevailing trend in terms of going up, remaining same or going down. Present the topic in a bit more detail with this Cybersecurity Risk Assessment Cyber Security Risk Assessment Program Implementation Impact. Use it as a tool for discussion and navigation on Cyber Security, Risk Assessment, Program Implementation, Impact On Attacks Frequency. This template is free to edit as deemed fit for your organization. Therefore download it now.



