Powerpoint Templates and Google slides for Data Breach Details
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Icons Slide For Data Breach Prevention And Mitigation Strategies For Businesses
Icons Slide For Data Breach Prevention And Mitigation Strategies For BusinessesPresenting our well crafted Icons Slide For Data Breach Prevention And Mitigation Strategies For Businesses set of slides. The slides include icons that are innovatively designed by our team of experts. The icons are easy to edit so you can conveniently increase or decrease their size without any loss in resolution. Therefore, grab them instantly.
-
 Table Of Contents For Data Breach Prevention And Mitigation Strategies For Businesses
Table Of Contents For Data Breach Prevention And Mitigation Strategies For BusinessesIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Data Breach Prevention And Mitigation Strategies For Businesses. This template helps you present information on ten stages. You can also present information on Data Breach Prevention Tools, Data Breach Response Plan, Prevention And Mitigation, Training And Budget using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Agenda For Data Breach Prevention And Mitigation Strategies For Businesses
Agenda For Data Breach Prevention And Mitigation Strategies For BusinessesIntroducing Agenda For Data Breach Prevention And Mitigation Strategies For Businesses to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Data Exploitation Techniques, Data Breach Prevention, Mitigation Strategies For Businesses, using this template. Grab it now to reap its full benefits.
-
 Data Breach Prevention 30 60 90 Days Plan To Secure Businesses From Data Breaches
Data Breach Prevention 30 60 90 Days Plan To Secure Businesses From Data BreachesThis slide represents 30-60-90 plan to protect companies and their employees from data breach attacks. The purpose of this slide is to illustrate the plans of the first 90 days from the start of the project including steps to be followed at interval of one month. Increase audience engagement and knowledge by dispensing information using Data Breach Prevention 30 60 90 Days Plan To Secure Businesses From Data Breaches. This template helps you present information on three stages. You can also present information on Strengthen Access Controls, Implement Continuous Monitoring, Implement Data Encryption, Continue Employee Awareness Training using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data Breach Prevention About Data Breach Introduction And Impact
Data Breach Prevention About Data Breach Introduction And ImpactThis slide represents the data breach overview, causes, and sources of data disclosure. This slide also highlights the impact of data breaches, such as financial loss, reputational damage, identity theft, legal consequences, loss of intellectual property, etc. Introducing Data Breach Prevention About Data Breach Introduction And Impact to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Cyberattacks, Human Errors, Physical Theft, Insider Threats, using this template. Grab it now to reap its full benefits.
-
 Data Breach Prevention About Identity Theft Overview And Techniques
Data Breach Prevention About Identity Theft Overview And TechniquesThis slide talks about the major crime committed by phishers, named as identity theft. The purpose of this slide is to outline the ways of stealing information, such as robbery, computer fraud, social networking sites, mail theft, and dumpster diving. Present the topic in a bit more detail with this Data Breach Prevention About Identity Theft Overview And Techniques. Use it as a tool for discussion and navigation on Drivers License, Social Security Card, Debit Or Credit Cards, Social Media Account. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
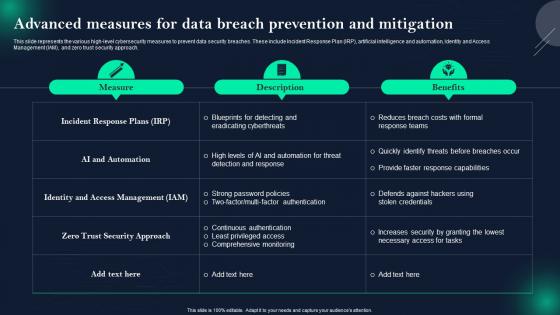 Data Breach Prevention Advanced Measures For Data Breach Prevention And Mitigation
Data Breach Prevention Advanced Measures For Data Breach Prevention And MitigationThis slide represents the various high-level cybersecurity measures to prevent data security breaches. These include Incident Response Plan IRP, artificial intelligence and automation, Identity and Access Management IAM, and zero trust security approach. Deliver an outstanding presentation on the topic using this Data Breach Prevention Advanced Measures For Data Breach Prevention And Mitigation. Dispense information and present a thorough explanation of Incident Response Plans, AI And Automation, Zero Trust Security Approach using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Breach Prevention And Mitigation Checklist For Responding To A Data Breach Attack
Data Breach Prevention And Mitigation Checklist For Responding To A Data Breach AttackThis slide represents the checklist for implementing a data breach response plan. The fundamental approaches are identify and isolate impacted systems or networks, perform a formal risk assessment, restore systems and address security flaws, notify affected parties, etc. Present the topic in a bit more detail with this Data Breach Prevention And Mitigation Checklist For Responding To A Data Breach Attack. Use it as a tool for discussion and navigation on Data Breach Response Plan, Fundamental Approaches, Systems Or Networks, Perform A Formal Risk Assessment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Breach Prevention And Mitigation Common Data Breach Attack Vectors
Data Breach Prevention And Mitigation Common Data Breach Attack VectorsThis slide represents several data breach attack vectors. The main components are stolen or compromised credentials, social engineering attacks, ransomware, system vulnerabilities, human error and IT failures, physical or site security errors, etc. Deliver an outstanding presentation on the topic using this Data Breach Prevention And Mitigation Common Data Breach Attack Vectors. Dispense information and present a thorough explanation of Brute Force Attacks, Purchasing Stolen Credentials, Phishing Scams, Fraudulent Emails, Deceptive Websites using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Breach Prevention And Mitigation Data Breach Attacks Experienced By Major Business
Data Breach Prevention And Mitigation Data Breach Attacks Experienced By Major BusinessThis slide highlights the top data breach victims based on different industrial sectors. These industries include email service providers, social media websites, online auction websites, retail services, government agencies, file-sharing and hosting services, etc. Present the topic in a bit more detail with this Data Breach Prevention And Mitigation Data Breach Attacks Experienced By Major Business. Use it as a tool for discussion and navigation on Heartland Payment Systems, Email Service Provider, Social Media Website, Online Auction Website. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Breach Prevention And Mitigation Data Breach Awareness Training Program
Data Breach Prevention And Mitigation Data Breach Awareness Training ProgramThis slide represents the training program for data breach awareness which will help organizations to prevent various cyber security scams. The purpose of this slide is to outline the mode, cost, agenda, and schedule for the training programs. Deliver an outstanding presentation on the topic using this Data Breach Prevention And Mitigation Data Breach Awareness Training Program. Dispense information and present a thorough explanation of Phishing Emails And Social Engineering, Data Breaches And Cybersecurity, Data Privacy Regulations And Compliance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Breach Prevention And Mitigation Data Breach Response Plan Fix Vulnerabilities
Data Breach Prevention And Mitigation Data Breach Response Plan Fix VulnerabilitiesThis slide represents actions to be taken, the responsible team, the deadline, and tasks for fixing vulnerabilities after a data breach. The action items include assessing Service Providers access privileges, reviewing network segmentation, monitoring, etc. Deliver an outstanding presentation on the topic using this Data Breach Prevention And Mitigation Data Breach Response Plan Fix Vulnerabilities. Dispense information and present a thorough explanation of Collaborate With Forensics Experts, Review Network Segmentation, Communicate Transparently using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Breach Prevention And Mitigation Data Exploitation Methods Used By Criminals
Data Breach Prevention And Mitigation Data Exploitation Methods Used By CriminalsThis slide discusses the exploitation of data after stealing it from authorized resources. These methods include opening new credit cards, withdrawing money from accounts, filing fraudulent tax returns, medical treatment using insurance, using credit card rewards, etc. Present the topic in a bit more detail with this Data Breach Prevention And Mitigation Data Exploitation Methods Used By Criminals. Use it as a tool for discussion and navigation on File Fraudulent Tax Returns, Withdraw Money From Accounts, Medical Treatment Using Insurance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
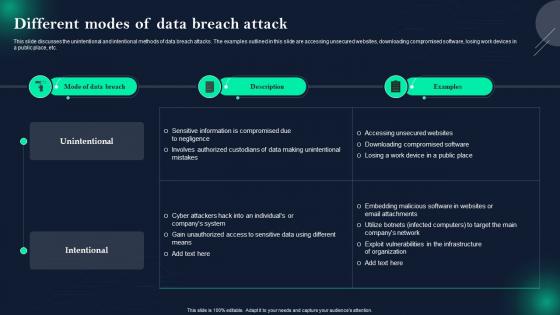 Data Breach Prevention And Mitigation Different Modes Of Data Breach Attack
Data Breach Prevention And Mitigation Different Modes Of Data Breach AttackThis slide discusses the unintentional and intentional methods of data breach attacks. The examples outlined in this slide are accessing unsecured websites, downloading compromised software, losing work devices in a public place, etc. Deliver an outstanding presentation on the topic using this Data Breach Prevention And Mitigation Different Modes Of Data Breach Attack. Dispense information and present a thorough explanation of Unintentional And Intentional Methods, Data Breach Attacks, Unsecured Websites, Downloading Compromised Software, Losing Work Devices using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Breach Prevention And Mitigation Major Types Of Data Security Breaches
Data Breach Prevention And Mitigation Major Types Of Data Security BreachesThis slide discusses the significant categories of information loss. The purpose of this slide is to describe several types of data security breaches. These include human error, device loss, cyberattacks, internal breaches, etc. Deliver an outstanding presentation on the topic using this Data Breach Prevention And Mitigation Major Types Of Data Security Breaches. Dispense information and present a thorough explanation of Social Engineering Attacks, IT Team Misconfiguring Servers, Disgruntled Employees, Gain Unauthorized Access using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
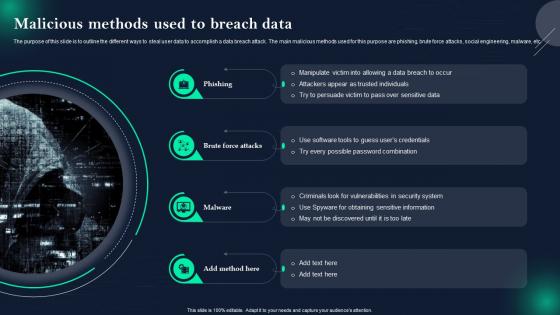 Data Breach Prevention And Mitigation Malicious Methods Used To Breach Data
Data Breach Prevention And Mitigation Malicious Methods Used To Breach DataThe purpose of this slide is to outline the different ways to steal user data to accomplish a data breach attack. The main malicious methods used for this purpose are phishing, brute force attacks, social engineering, malware, etc. Increase audience engagement and knowledge by dispensing information using Data Breach Prevention And Mitigation Malicious Methods Used To Breach Data. This template helps you present information on four stages. You can also present information on Criminals Look For Vulnerabilities, Possible Password Combination, Social Engineering, Malware using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data Breach Prevention And Mitigation Overview Of Various Targets Of Data Breach
Data Breach Prevention And Mitigation Overview Of Various Targets Of Data BreachThis slide represents information about several data breach targets and types of data compromised. These targets are organizations and businesses, government agencies, healthcare providers, financial institutions, individuals, websites, online platforms, etc. Present the topic in a bit more detail with this Data Breach Prevention And Mitigation Overview Of Various Targets Of Data Breach. Use it as a tool for discussion and navigation on Organizations And Businesses, Healthcare Providers, Educational Institutions, Websites And Online Platforms. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
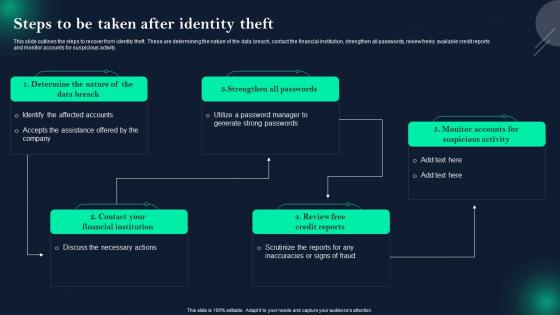 Data Breach Prevention And Mitigation Steps To Be Taken After Identity Theft
Data Breach Prevention And Mitigation Steps To Be Taken After Identity TheftThis slide outlines the steps to recover from identity theft. These are determining the nature of the data breach, contact the financial institution, strengthen all passwords, review freely available credit reports and monitor accounts for suspicious activity. Deliver an outstanding presentation on the topic using this Data Breach Prevention And Mitigation Steps To Be Taken After Identity Theft. Dispense information and present a thorough explanation of Strengthen All Passwords, Review Free Credit Reports, Contact Your Financial Institution using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
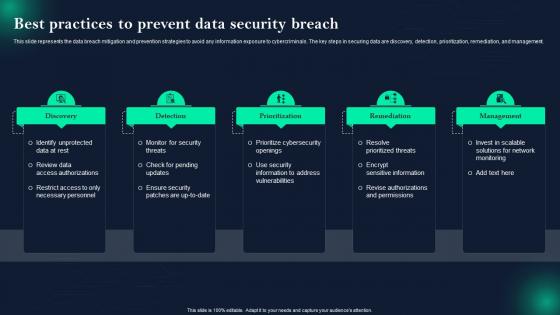 Data Breach Prevention Best Practices To Prevent Data Security Breach
Data Breach Prevention Best Practices To Prevent Data Security BreachThis slide represents the data breach mitigation and prevention strategies to avoid any information exposure to cybercriminals. The key steps in securing data are discovery, detection, prioritization, remediation, and management. Increase audience engagement and knowledge by dispensing information using Data Breach Prevention Best Practices To Prevent Data Security Breach. This template helps you present information on five stages. You can also present information on Prioritize Cybersecurity Openings, Resolve Prioritized Threats, Review Data Access Authorizations using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data Breach Prevention Comparison Between Data Breaches And Data Leaks
Data Breach Prevention Comparison Between Data Breaches And Data LeaksThe purpose of this slide is to compare the data breach and data leak based on different aspects. The factors used to differentiate data breaches and data leaks are definition, intent, potential impact, cause, and prevention. Present the topic in a bit more detail with this Data Breach Prevention Comparison Between Data Breaches And Data Leaks. Use it as a tool for discussion and navigation on Financial Losses, Reputational Damage, Legal Matters, Cyberattacks, Insider Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Casepoint Data Breach In Powerpoint And Google Slides Cpb
Casepoint Data Breach In Powerpoint And Google Slides CpbPresenting Casepoint Data Breach In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Casepoint Data Breach. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
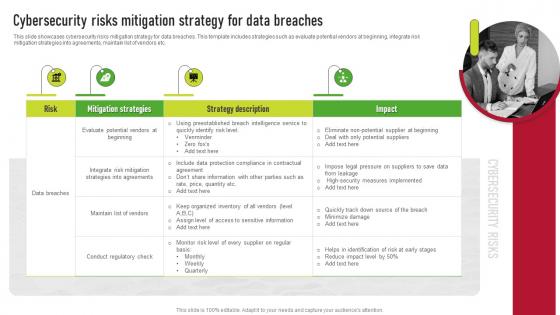 Cybersecurity Risks Mitigation Strategy For Data Breaches Supplier Risk Management
Cybersecurity Risks Mitigation Strategy For Data Breaches Supplier Risk ManagementThis slide showcases cybersecurity risks mitigation strategy for data breaches. This template includes strategies such as evaluate potential vendors at beginning, integrate risk mitigation strategies into agreements, maintain list of vendors etc. Introducing Cybersecurity Risks Mitigation Strategy For Data Breaches Supplier Risk Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Mitigation Strategies, Strategy Description, Risk, using this template. Grab it now to reap its full benefits.
-
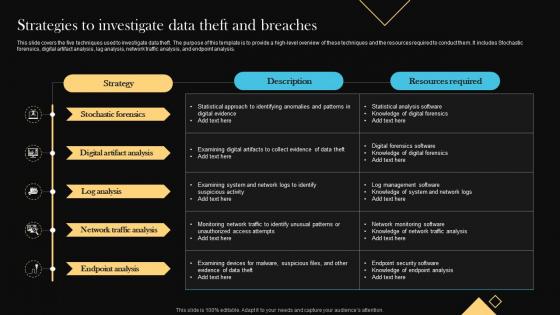 Strategies To Investigate Data Theft And Breaches
Strategies To Investigate Data Theft And BreachesThis slide covers the five techniques used to investigate data theft. The purpose of this template is to provide a high level overview of these techniques and the resources required to conduct them. It includes Stochastic forensics, digital artifact analysis, lag analysis, network traffic analysis, and endpoint analysis. Introducing our Strategies To Investigate Data Theft And Breaches set of slides. The topics discussed in these slides are Analysis, Digital, Endpoint. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Agenda Improving IoT Device Cybersecurity To Prevent Data Breaches IoT SS
Agenda Improving IoT Device Cybersecurity To Prevent Data Breaches IoT SSIntroducing Agenda Improving IoT Device Cybersecurity To Prevent Data Breaches IoT SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Provide, Business, Common, using this template. Grab it now to reap its full benefits.
-
 Icons Slide Improving IoT Device Cybersecurity To Prevent Data Breaches IoT SS
Icons Slide Improving IoT Device Cybersecurity To Prevent Data Breaches IoT SSIntroducing our well researched set of slides titled Icons Slide Improving IoT Device Cybersecurity To Prevent Data Breaches IoT SS. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
 Improving IoT Device Cybersecurity To Prevent Data Breaches Table Of Contents IoT SS
Improving IoT Device Cybersecurity To Prevent Data Breaches Table Of Contents IoT SSIntroducing Improving IoT Device Cybersecurity To Prevent Data Breaches Table Of Contents IoT SS to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on General, Strategies, Security, using this template. Grab it now to reap its full benefits.
-
 Credit Karma Data Breach In Powerpoint And Google Slides Cpb
Credit Karma Data Breach In Powerpoint And Google Slides CpbPresenting Credit Karma Data Breach In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Credit Karma Data Breach. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
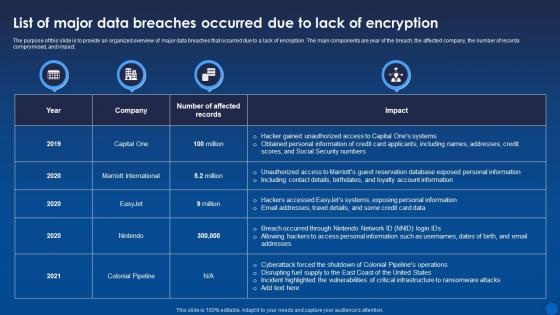 List Of Major Data Breaches Occurred Due To Lack Of Encryption Encryption For Data Privacy In Digital Age It
List Of Major Data Breaches Occurred Due To Lack Of Encryption Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to provide an organized overview of major data breaches that occurred due to a lack of encryption. The main components are year of the breach, the affected company, the number of records compromised, and impact. Present the topic in a bit more detail with this List Of Major Data Breaches Occurred Due To Lack Of Encryption Encryption For Data Privacy In Digital Age It. Use it as a tool for discussion and navigation on Compromised, Encryption, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Breach Investigations Report In Powerpoint And Google Slides Cpb
Data Breach Investigations Report In Powerpoint And Google Slides CpbPresenting our Data Breach Investigations Report In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Data Breach Investigations Report This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Agenda For Data Breach Response Plan For Businesses Ppt Ideas Background Images
Agenda For Data Breach Response Plan For Businesses Ppt Ideas Background ImagesIntroducing Agenda For Data Breach Response Plan For Businesses Ppt Ideas Background Images to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Data Breach Response Plan, Development, Post Breach Phases, Roadmap, using this template. Grab it now to reap its full benefits.
-
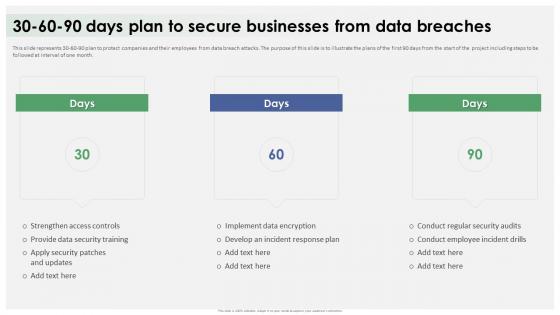 Data Breach Response Plan 30 60 90 Days Plan To Secure Businesses From Data Breaches
Data Breach Response Plan 30 60 90 Days Plan To Secure Businesses From Data BreachesThis slide represents 30-60-90 plan to protect companies and their employees from data breach attacks. The purpose of this slide is to illustrate the plans of the first 90 days from the start of the project including steps to be followed at interval of one month. Increase audience engagement and knowledge by dispensing information using Data Breach Response Plan 30 60 90 Days Plan To Secure Businesses From Data Breaches. This template helps you present information on three stages. You can also present information on Strengthen Access Controls, Conduct Regular Security Audits, Provide Data Security Training using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
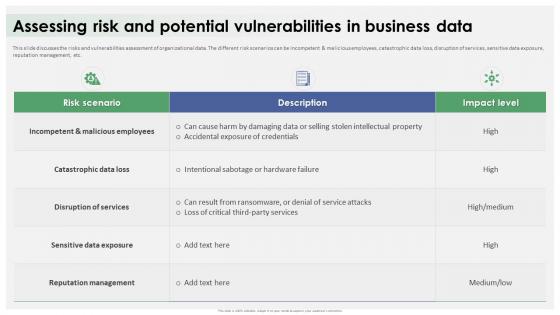 Data Breach Response Plan Assessing Risk And Potential Vulnerabilities In Business Data
Data Breach Response Plan Assessing Risk And Potential Vulnerabilities In Business DataThis slide discusses the risks and vulnerabilities assessment of organizational data. The different risk scenarios can be incompetent and malicious employees, catastrophic data loss, disruption of services, sensitive data exposure, reputation management, etc. Present the topic in a bit more detail with this Data Breach Response Plan Assessing Risk And Potential Vulnerabilities In Business Data. Use it as a tool for discussion and navigation on Incompetent And Malicious Employees, Catastrophic Data Loss, Reputation Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
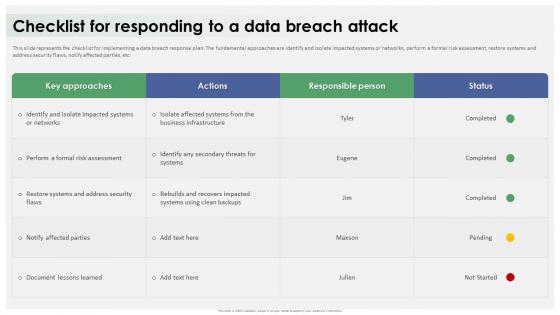 Data Breach Response Plan Checklist For Responding To A Data Breach Attack
Data Breach Response Plan Checklist For Responding To A Data Breach AttackThis slide represents the checklist for implementing a data breach response plan. The fundamental approaches are identify and isolate impacted systems or networks, perform a formal risk assessment, restore systems and address security flaws, notify affected parties, etc. Deliver an outstanding presentation on the topic using this Data Breach Response Plan Checklist For Responding To A Data Breach Attack. Dispense information and present a thorough explanation of Data Breach Response Plan, Fundamental Approaches, Formal Risk Assessment, Restore Systems using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
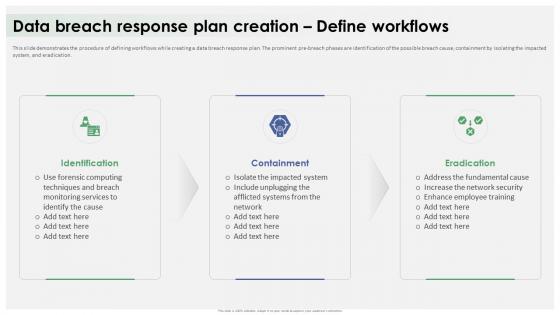 Data Breach Response Plan Creation Define Workflows Ppt Icon Design Ideas
Data Breach Response Plan Creation Define Workflows Ppt Icon Design IdeasThis slide demonstrates the procedure of defining workflows while creating a data breach response plan. The prominent pre-breach phases are identification of the possible breach cause, containment by isolating the impacted system, and eradication. Introducing Data Breach Response Plan Creation Define Workflows Ppt Icon Design Ideas to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Data Breach Response Plan, Pre Breach Phases, Possible Breach Cause, Network Security, using this template. Grab it now to reap its full benefits.
-
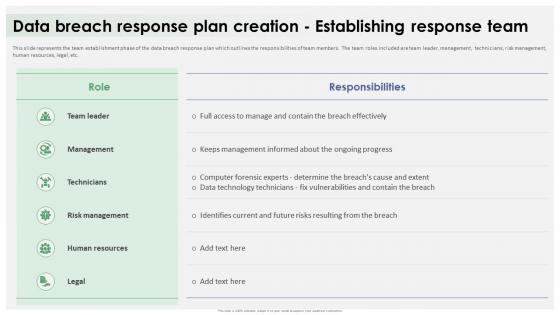 Data Breach Response Plan Creation Establishing Response Team
Data Breach Response Plan Creation Establishing Response TeamThis slide represents the team establishment phase of the data breach response plan which outlines the responsibilities of team members. The team roles included are team leader, management, technicians, risk management, human resources, legal, etc. Present the topic in a bit more detail with this Data Breach Response Plan Creation Establishing Response Team. Use it as a tool for discussion and navigation on Management, Technicians, Risk Management, Establishing Response Team. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
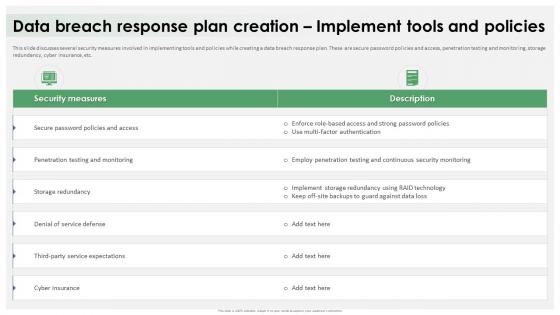 Data Breach Response Plan Creation Implement Tools And Policies
Data Breach Response Plan Creation Implement Tools And PoliciesThis slide discusses several security measures involved in implementing tools and policies while creating a data breach response plan. These are secure password policies and access, penetration testing and monitoring, storage redundancy, cyber insurance, etc. Deliver an outstanding presentation on the topic using this Data Breach Response Plan Creation Implement Tools And Policies. Dispense information and present a thorough explanation of Several Security, Data Breach Response Plan, Password Policies And Access, Penetration Testing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
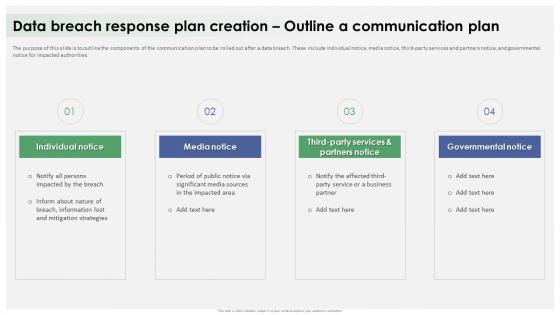 Data Breach Response Plan Creation Outline A Communication Plan
Data Breach Response Plan Creation Outline A Communication PlanThe purpose of this slide is to outline the components of the communication plan to be rolled out after a data breach. These include individual notice, media notice, third-party services and partners notice, and governmental notice for impacted authorities. Increase audience engagement and knowledge by dispensing information using Data Breach Response Plan Creation Outline A Communication Plan. This template helps you present information on four stages. You can also present information on Individual Notice, Media Notice, Third Party Services, Governmental Notice using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
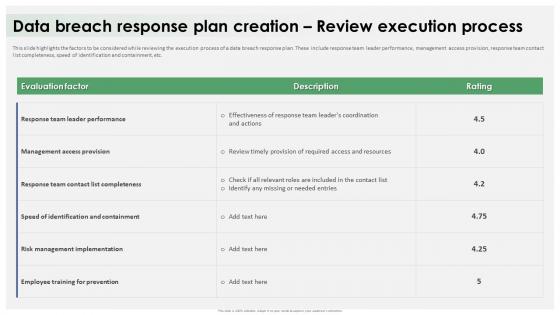 Data Breach Response Plan Creation Review Execution Process
Data Breach Response Plan Creation Review Execution ProcessThis slide highlights the factors to be considered while reviewing the execution process of a data breach response plan. These include response team leader performance, management access provision, response team contact list completeness, speed of identification and containment, etc. Present the topic in a bit more detail with this Data Breach Response Plan Creation Review Execution Process. Use it as a tool for discussion and navigation on Response Team Leader Performance, Management Access Provision, Risk Management Implementation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
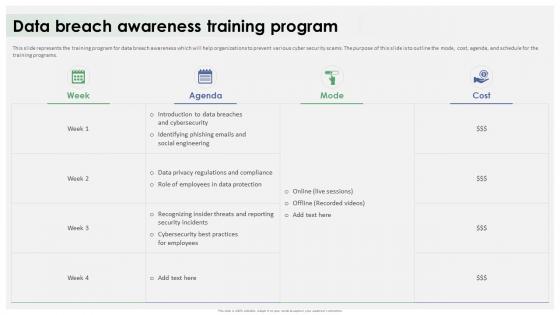 Data Breach Response Plan Data Breach Awareness Training Program
Data Breach Response Plan Data Breach Awareness Training ProgramThis slide represents the training program for data breach awareness which will help organizations to prevent various cyber security scams. The purpose of this slide is to outline the mode, cost, agenda, and schedule for the training programs. Deliver an outstanding presentation on the topic using this Data Breach Response Plan Data Breach Awareness Training Program. Dispense information and present a thorough explanation of Training Program, Data Breach Awareness, Cyber Security Scams, Data Privacy Regulations And Compliance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
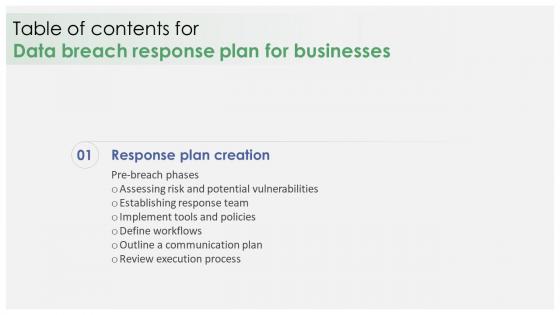 Data Breach Response Plan For Businesses For Table Of Contents
Data Breach Response Plan For Businesses For Table Of ContentsPresent the topic in a bit more detail with this Data Breach Response Plan For Businesses For Table Of Contents. Use it as a tool for discussion and navigation on Establishing Response Team, Implement Tools And Policies, Define Workflows, Outline A Communication Plan. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
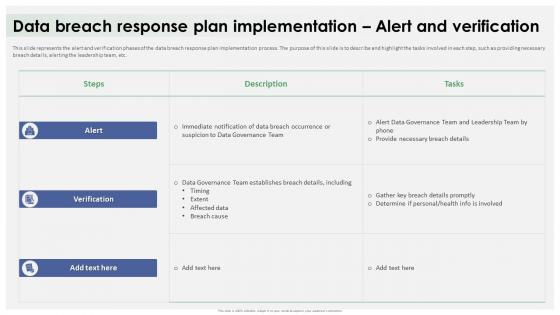 Data Breach Response Plan Implementation Alert And Verification
Data Breach Response Plan Implementation Alert And VerificationThis slide represents the alert and verification phases of the data breach response plan implementation process. The purpose of this slide is to describe and highlight the tasks involved in each step, such as providing necessary breach details, alerting the leadership team, etc. Deliver an outstanding presentation on the topic using this Data Breach Response Plan Implementation Alert And Verification. Dispense information and present a thorough explanation of Alert And Verification Phases, Data Breach Response Plan, Alerting The Leadership Team using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
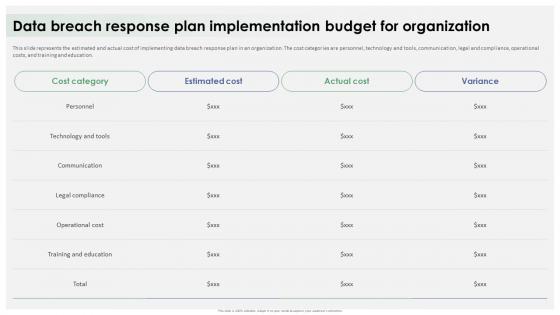 Data Breach Response Plan Implementation Budget For Organization
Data Breach Response Plan Implementation Budget For OrganizationThis slide represents the estimated and actual cost of implementing data breach response plan in an organization. The cost categories are personnel, technology and tools, communication, legal and compliance, operational costs, and training and education. Present the topic in a bit more detail with this Data Breach Response Plan Implementation Budget For Organization. Use it as a tool for discussion and navigation on Technology And Tools, Communication, Legal Compliance, Operational Cost, Training And Education. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
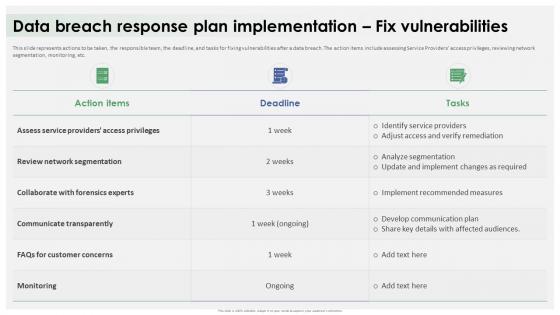 Data Breach Response Plan Implementation Fix Vulnerabilities
Data Breach Response Plan Implementation Fix VulnerabilitiesThis slide represents actions to be taken, the responsible team, the deadline, and tasks for fixing vulnerabilities after a data breach. The action items include assessing Service Providers access privileges, reviewing network segmentation, monitoring, etc. Deliver an outstanding presentation on the topic using this Data Breach Response Plan Implementation Fix Vulnerabilities. Dispense information and present a thorough explanation of Review Network Segmentation, Communicate Transparently, Collaborate With Forensics Experts using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
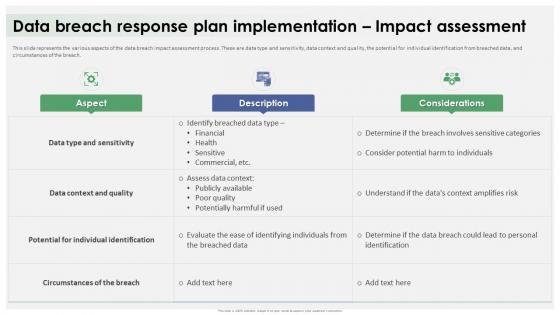 Data Breach Response Plan Implementation Impact Assessment
Data Breach Response Plan Implementation Impact AssessmentThis slide represents the various aspects of the data breach impact assessment process. These are data type and sensitivity, data context and quality, the potential for individual identification from breached data, and circumstances of the breach. Present the topic in a bit more detail with this Data Breach Response Plan Implementation Impact Assessment. Use it as a tool for discussion and navigation on Data Type And Sensitivity, Data Context And Quality, Potential For Individual Identification. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
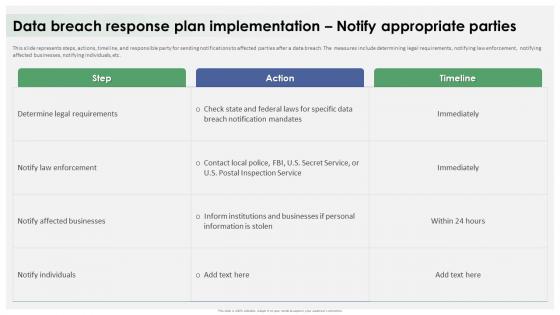 Data Breach Response Plan Implementation Notify Appropriate Parties
Data Breach Response Plan Implementation Notify Appropriate PartiesThis slide represents steps, actions, timeline, and responsible party for sending notifications to affected parties after a data breach. The measures include determining legal requirements, notifying law enforcement, notifying affected businesses, notifying individuals, etc. Deliver an outstanding presentation on the topic using this Data Breach Response Plan Implementation Notify Appropriate Parties. Dispense information and present a thorough explanation of Determine Legal Requirements, Notify Law Enforcement, Notify Affected Businesses using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
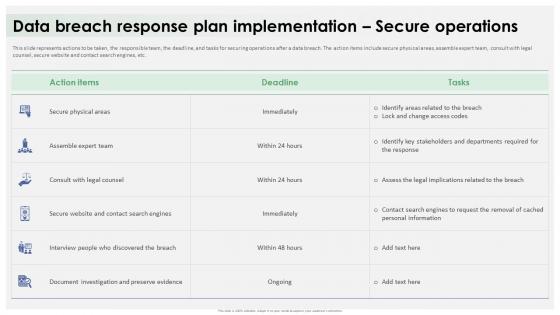 Data Breach Response Plan Implementation Secure Operations
Data Breach Response Plan Implementation Secure OperationsThis slide represents actions to be taken, the responsible team, the deadline, and tasks for securing operations after a data breach. The action items include secure physical areas, assemble expert team, consult with legal counsel, secure website and contact search engines, etc. Present the topic in a bit more detail with this Data Breach Response Plan Implementation Secure Operations. Use it as a tool for discussion and navigation on Secure Physical Areas, Assemble Expert Team, Consult With Legal Counsel, Secure Website. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
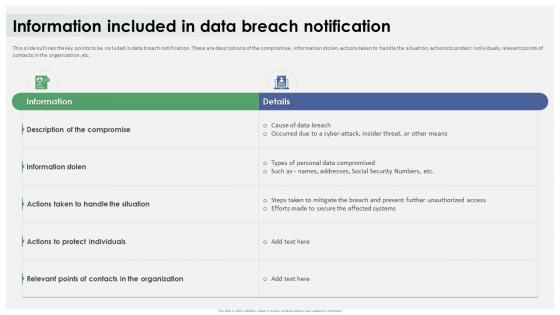 Data Breach Response Plan Information Included In Data Breach Notification
Data Breach Response Plan Information Included In Data Breach NotificationThis slide outlines the key points to be included in data breach notification. These are descriptions of the compromise, information stolen, actions taken to handle the situation, actions to protect individuals, relevant points of contacts in the organization, etc. Deliver an outstanding presentation on the topic using this Data Breach Response Plan Information Included In Data Breach Notification. Dispense information and present a thorough explanation of Actions To Protect Individuals, Data Breach Notification, Personal Data Compromised using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
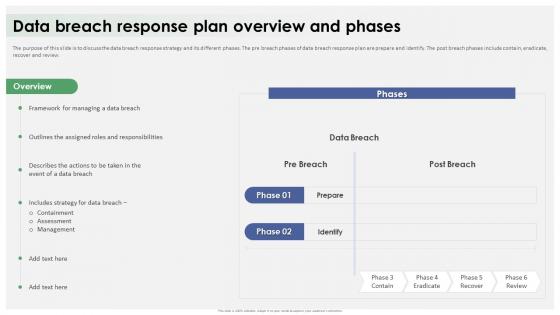 Data Breach Response Plan Overview And Phases Ppt Ideas Example File
Data Breach Response Plan Overview And Phases Ppt Ideas Example FileThe purpose of this slide is to discuss the data breach response strategy and its different phases. The pre breach phases of data breach response plan are prepare and identify. The post breach phases include contain, eradicate, recover and review. Present the topic in a bit more detail with this Data Breach Response Plan Overview And Phases Ppt Ideas Example File. Use it as a tool for discussion and navigation on Containment, Assessment, Management, Data Breach Response Plan. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data Breach Response Plan Possible Causes Of Data Breach Attack
Data Breach Response Plan Possible Causes Of Data Breach AttackThis slide highlights the reasons behind the success of data breach attack. These include phishing attacks, unpatched software, malware, insider threats, third-party vulnerabilities, SQL Structured Query Language injections, unsecured APIs, etc. Deliver an outstanding presentation on the topic using this Data Breach Response Plan Possible Causes Of Data Breach Attack. Dispense information and present a thorough explanation of Phishing Attacks, Unpatched Software, Third Party Vulnerabilities, Structured Query Language using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
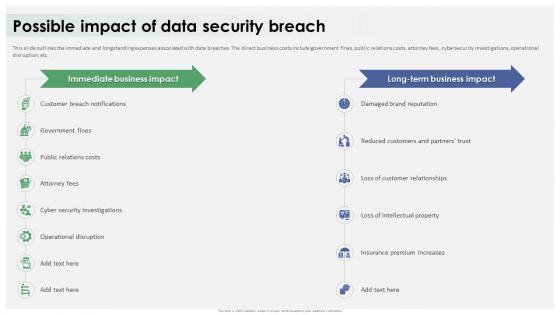 Data Breach Response Plan Possible Impact Of Data Security Breach
Data Breach Response Plan Possible Impact Of Data Security BreachThis slide outlines the immediate and longstanding expenses associated with data breaches. The direct business costs include government fines, public relations costs, attorney fees, cybersecurity investigations, operational disruption, etc. Present the topic in a bit more detail with this Data Breach Response Plan Possible Impact Of Data Security Breach. Use it as a tool for discussion and navigation on Customer Breach Notifications, Loss Of Customer Relationships, Operational Disruption, Damaged Brand Reputation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
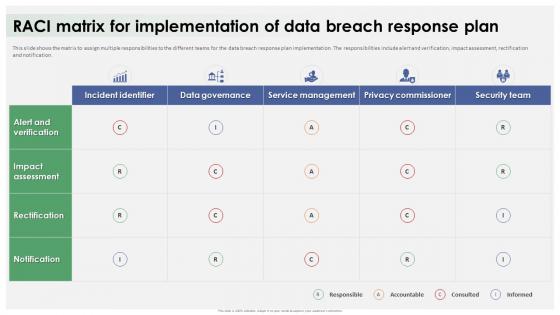 Data Breach Response Plan Raci Matrix For Implementation Of Data Breach Response Plan
Data Breach Response Plan Raci Matrix For Implementation Of Data Breach Response PlanThis slide shows the matrix to assign multiple responsibilities to the different teams for the data breach response plan implementation. The responsibilities include alert and verification, impact assessment, rectification and notification. Deliver an outstanding presentation on the topic using this Data Breach Response Plan Raci Matrix For Implementation Of Data Breach Response Plan. Dispense information and present a thorough explanation of Assign Multiple Responsibilities, Data Breach Response Plan, Rectification And Notification using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
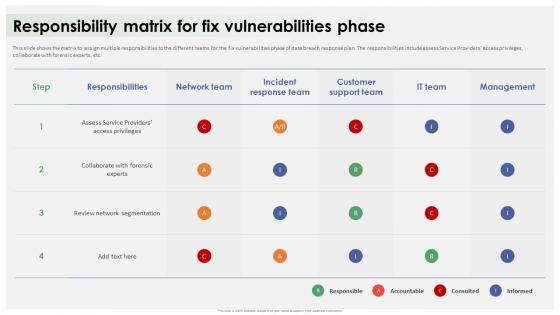 Data Breach Response Plan Responsibility Matrix For Fix Vulnerabilities Phase
Data Breach Response Plan Responsibility Matrix For Fix Vulnerabilities PhaseThis slide shows the matrix to assign multiple responsibilities to the different teams for the fix vulnerabilities phase of data breach response plan. The responsibilities include assess Service Providers access privileges, collaborate with forensic experts, etc. Present the topic in a bit more detail with this Data Breach Response Plan Responsibility Matrix For Fix Vulnerabilities Phase. Use it as a tool for discussion and navigation on Responsibilities, Customer Support Team, Review Network Segmentation, Fix Vulnerabilities Phase. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
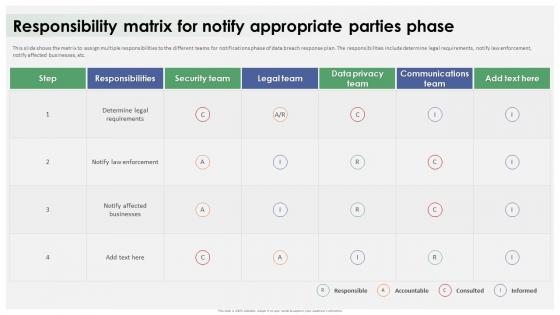 Data Breach Response Plan Responsibility Matrix For Notify Appropriate Parties Phase
Data Breach Response Plan Responsibility Matrix For Notify Appropriate Parties PhaseThis slide shows the matrix to assign multiple responsibilities to the different teams for notifications phase of data breach response plan. The responsibilities include determine legal requirements, notify law enforcement, notify affected businesses, etc. Deliver an outstanding presentation on the topic using this Data Breach Response Plan Responsibility Matrix For Notify Appropriate Parties Phase. Dispense information and present a thorough explanation of Responsibility Matrix, Legal Requirements, Notify Law Enforcement, Notify Affected Businesses using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
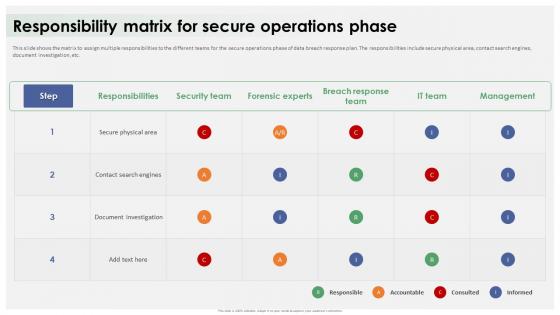 Data Breach Response Plan Responsibility Matrix For Secure Operations Phase
Data Breach Response Plan Responsibility Matrix For Secure Operations PhaseThis slide shows the matrix to assign multiple responsibilities to the different teams for the secure operations phase of data breach response plan. The responsibilities include secure physical area, contact search engines, document investigation, etc. Present the topic in a bit more detail with this Data Breach Response Plan Responsibility Matrix For Secure Operations Phase. Use it as a tool for discussion and navigation on Secure Physical Area, Contact Search Engines, Document Investigation, Responsibility Matrix. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
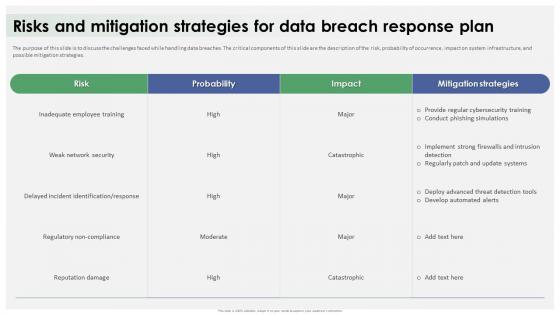 Data Breach Response Plan Risks And Mitigation Strategies For Data Breach Response Plan
Data Breach Response Plan Risks And Mitigation Strategies For Data Breach Response PlanThe purpose of this slide is to discuss the challenges faced while handling data breaches. The critical components of this slide are the description of the risk, probability of occurrence, impact on system infrastructure, and possible mitigation strategies. Deliver an outstanding presentation on the topic using this Data Breach Response Plan Risks And Mitigation Strategies For Data Breach Response Plan. Dispense information and present a thorough explanation of Inadequate Employee Training, Weak Network Security, Regulatory Non Compliance using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
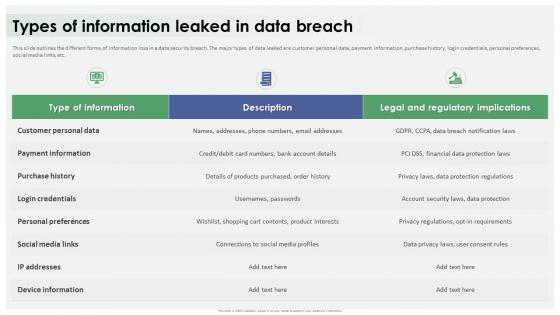 Data Breach Response Plan Types Of Information Leaked In Data Breach
Data Breach Response Plan Types Of Information Leaked In Data BreachThis slide outlines the different forms of information loss in a data security breach. The major types of data leaked are customer personal data, payment information, purchase history, login credentials, personal preferences, social media links, etc. Deliver an outstanding presentation on the topic using this Data Breach Response Plan Types Of Information Leaked In Data Breach. Dispense information and present a thorough explanation of Customer Personal Data, Payment Information, Personal Preferences, Social Media Links using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
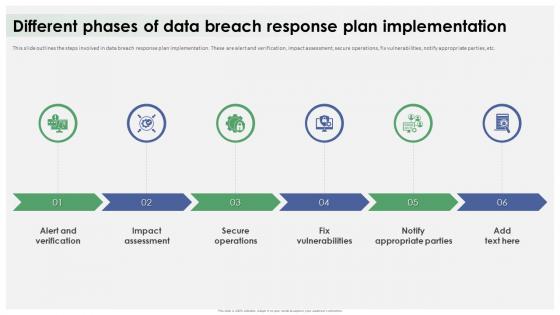 Different Phases Of Data Breach Response Plan Implementation
Different Phases Of Data Breach Response Plan ImplementationThis slide outlines the steps involved in data breach response plan implementation. These are alert and verification, impact assessment, secure operations, fix vulnerabilities, notify appropriate parties, etc. Introducing Different Phases Of Data Breach Response Plan Implementation to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Alert And Verification, Impact Assessment, Secure Operations, Fix Vulnerabilities, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Data Breach Response Plan For Businesses Ppt Icon Microsoft
Icons Slide For Data Breach Response Plan For Businesses Ppt Icon MicrosoftIntroducing our well researched set of slides titled Icons Slide For Data Breach Response Plan For Businesses Ppt Icon Microsoft. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
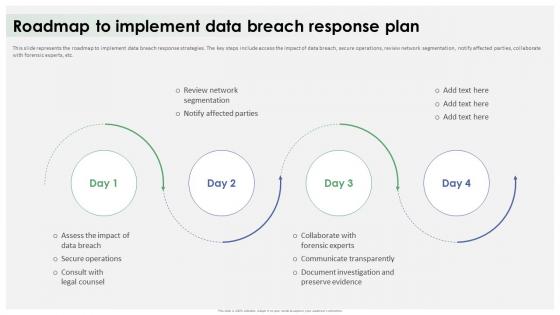 Roadmap To Implement Data Breach Response Plan Ppt Icon Information
Roadmap To Implement Data Breach Response Plan Ppt Icon InformationThis slide represents the roadmap to implement data breach response strategies. The key steps include access the impact of data breach, secure operations, review network segmentation, notify affected parties, collaborate with forensic experts, etc. Increase audience engagement and knowledge by dispensing information using Roadmap To Implement Data Breach Response Plan Ppt Icon Information. This template helps you present information on four stages. You can also present information on Data Breach Response Strategies, Secure Operations, Review Network Segmentation, Collaborate With Forensic Experts using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
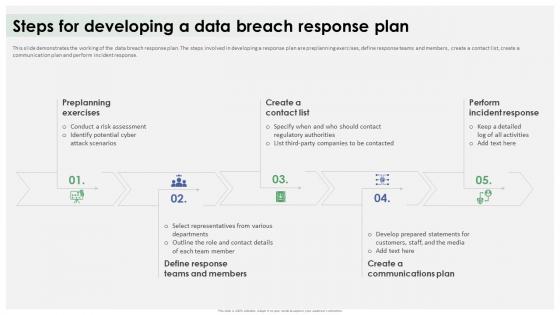 Steps For Developing A Data Breach Response Plan Ppt Icon Graphics Design
Steps For Developing A Data Breach Response Plan Ppt Icon Graphics DesignThis slide demonstrates the working of the data breach response plan. The steps involved in developing a response plan are preplanning exercises, define response teams and members, create a contact list, create a communication plan and perform incident response. Introducing Steps For Developing A Data Breach Response Plan Ppt Icon Graphics Design to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Preplanning Exercises, Perform Incident Response, Data Breach Response Plan, Create A Communications Plan, using this template. Grab it now to reap its full benefits.



