Powerpoint Templates and Google slides for Data Security Management
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
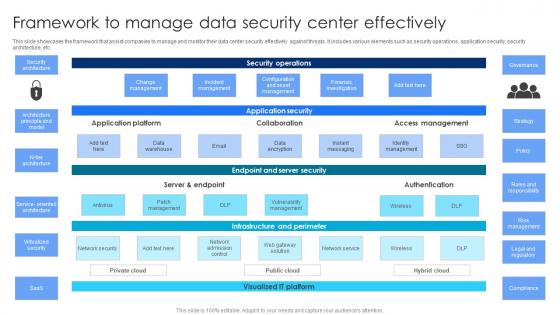 Framework To Manage Data Security Center Effectively
Framework To Manage Data Security Center EffectivelyThis slide showcases the framework that assist companies to manage and monitor their data center security effectively against threats. It includes various elements such as security operations, application security, security architecture, etc. Presenting our well structured Framework To Manage Data Security Center Effectively. The topics discussed in this slide are Application Platform, Access Management, Application Security. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
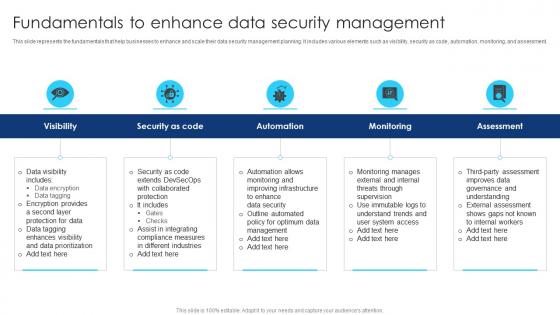 Fundamentals To Enhance Data Security Management
Fundamentals To Enhance Data Security ManagementThis slide represents the fundamentals that help businesses to enhance and scale their data security management planning. It includes various elements such as visibility, security as code, automation, monitoring, and assessment. Presenting our set of slides with Fundamentals To Enhance Data Security Management. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Collaborated Protection, Data Security, External Assessment.
-
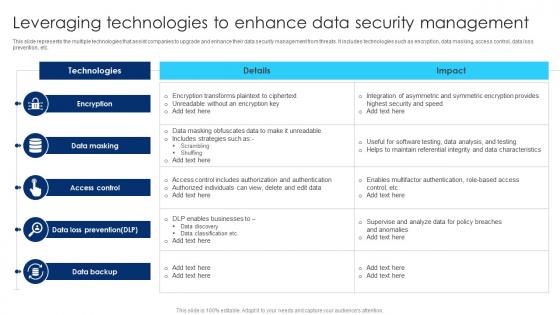 Leveraging Technologies To Enhance Data Security Management
Leveraging Technologies To Enhance Data Security ManagementThis slide represents the multiple technologies that assist companies to upgrade and enhance their data security management from threats. It includes technologies such as encryption, data masking, access control, data loss prevention, etc. Introducing our Leveraging Technologies To Enhance Data Security Management set of slides. The topics discussed in these slides are Data Loss Prevention, Access Control, Data Masking. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
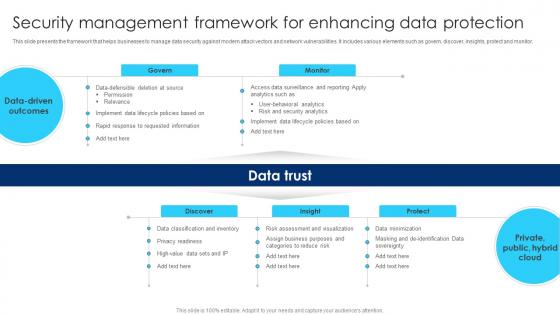 Security Management Framework For Enhancing Data Protection
Security Management Framework For Enhancing Data ProtectionThis slide presents the framework that helps businesses to manage data security against modern attack vectors and network vulnerabilities. It includes various elements such as govern, discover, insights, protect and monitor. Presenting our well structured Security Management Framework For Enhancing Data Protection. The topics discussed in this slide are Privacy Readiness, Risk And Security Analytics, Data Driven Outcomes. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
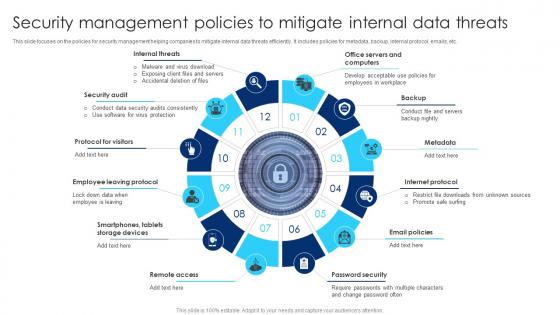 Security Management Policies To Mitigate Internal Data Threats
Security Management Policies To Mitigate Internal Data ThreatsThis slide focuses on the policies for security management helping companies to mitigate internal data threats efficiently. It includes policies for metadata, backup, internal protocol, emails, etc. Introducing our premium set of slides with Security Management Policies To Mitigate Internal Data Threats. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Protocol For Visitors, Internet Protocol, Security Audit. So download instantly and tailor it with your information.
-
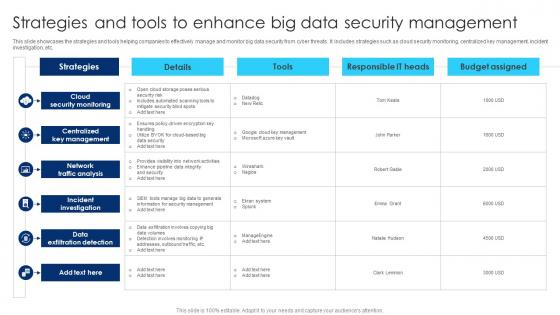 Strategies And Tools To Enhance Big Data Security Management
Strategies And Tools To Enhance Big Data Security ManagementThis slide showcases the strategies and tools helping companies to effectively manage and monitor big data security from cyber threats. It includes strategies such as cloud security monitoring, centralized key management, incident investigation, etc. Introducing our Strategies And Tools To Enhance Big Data Security Management set of slides. The topics discussed in these slides are Cloud Security Monitoring, Centralized Key Management, Network Traffic Analysis. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Security Policy Icon For Data Theft Prevention
Cyber Security Policy Icon For Data Theft PreventionIntroducing our Cyber Security Policy Icon For Data Theft Prevention set of slides. The topics discussed in these slides are Cyber Security Policy, Icon For Data Theft Prevention. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Icon For Big Data Database Security
Icon For Big Data Database SecurityPresenting our set of slides with Icon For Big Data Database Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Icon, Big Data, Database Security.
-
 Icon For Data Loss Prevention In Information Security
Icon For Data Loss Prevention In Information SecurityPresenting our set of slides with Icon For Data Loss Prevention In Information Security. This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Icon For Data Loss, Prevention In Information Security
-
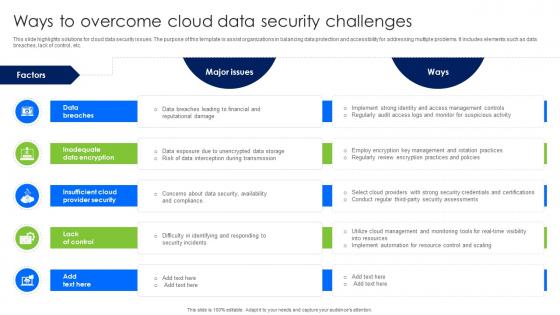 Ways To Overcome Cloud Data Security Challenges
Ways To Overcome Cloud Data Security ChallengesThis slide highlights solutions for cloud data security issues. The purpose of this template is assist organizations in balancing data protection and accessibility for addressing multiple problems. It includes elements such as data breaches, lack of control, etc. Introducing our premium set of slides with Ways To Overcome Cloud Data Security Challenges. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Breaches, Insufficient Cloud Provider Security, Lack Of Control. So download instantly and tailor it with your information.
-
 Data Privacy Training Icon For Securing Information
Data Privacy Training Icon For Securing InformationIntroducing our premium set of slides with Data Privacy Training Icon For Securing Information. Ellicudate the two stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Privacy Training, Securing Information. So download instantly and tailor it with your information.
-
 Data Analytics And Integration Security Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Data Analytics And Integration Security Colored Icon In Powerpoint Pptx Png And Editable Eps FormatEnhance your presentations with our vibrant PowerPoint icon on big data storage solutions. This eye-catching icon features a bold color scheme and represents the latest advancements in data storage technology. Perfect for showcasing your expertise in big data management and storage solutions.
-
 Data Analytics And Integration Security Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Data Analytics And Integration Security Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone powerpoint icon represents the efficient and reliable storage solutions for big data. With its sleek design and bold color, it conveys the message of simplicity and effectiveness in managing large volumes of data. Perfect for presentations on data storage and management in the modern era.
-
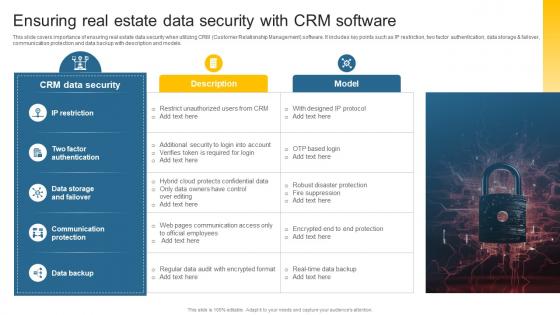 Ensuring Real Estate Data Security With CRM Leveraging Effective CRM Tool In Real Estate Company
Ensuring Real Estate Data Security With CRM Leveraging Effective CRM Tool In Real Estate CompanyThis slide covers importance of ensuring real estate data security when utilizing CRM Customer Relationship Management software. It includes key points such as IP restriction, two factor authentication, data storage and failover, communication protection and data backup with description and models. Introducing Ensuring Real Estate Data Security With CRM Leveraging Effective CRM Tool In Real Estate Company to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Data Storage And Failover, Communication Protection, Data Backup, using this template. Grab it now to reap its full benefits.
-
 Additional Blockchain Data Security Tips And Best Comprehensive Approach To Privacy BCT SS
Additional Blockchain Data Security Tips And Best Comprehensive Approach To Privacy BCT SSThis slide covers essential guidance on safeguarding blockchain data to ensure integrity and confidentiality such as keeping private key confidential, utilizing VPN, use of link checker, opting for trusted crypto wallets. Introducing Additional Blockchain Data Security Tips And Best Comprehensive Approach To Privacy BCT SS to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Private Key Confidential, Security, Blockchain, Prevent Phishing Attacks, using this template. Grab it now to reap its full benefits.
-
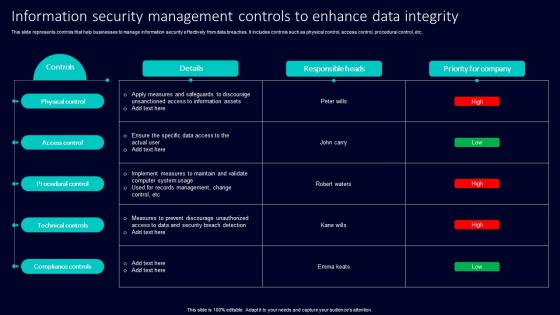 Information Security Management Controls To Enhance Data Integrity
Information Security Management Controls To Enhance Data IntegrityThis slide represents controls that help businesses to manage information security effectively from data breaches. It includes controls such as physical control, access control, procedural control, etc, Presenting our well structured Information Security Management Controls To Enhance Data Integrity. The topics discussed in this slide are Physical Control, Access Control, Procedural Control. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
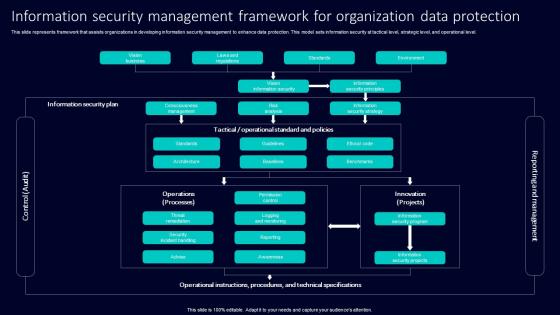 Information Security Management Framework For Organization Data Protection
Information Security Management Framework For Organization Data ProtectionThis slide represents framework that assists organizations in developing information security management to enhance data protection. This model sets information security at tactical level, strategic level, and operational level. Introducing our Information Security Management Framework For Organization Data Protection set of slides. The topics discussed in these slides are Information Security Plan, Consciousness Management, Risk Analysis. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Information Security Management Icon For Consumer Data Privacy
Information Security Management Icon For Consumer Data PrivacyIntroducing our premium set of slides with Information Security Management Icon For Consumer Data Privacy. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Information Security Management Icon, Consumer Data Privacy. So download instantly and tailor it with your information.
-
 Information Security Management Icon For Data Protection
Information Security Management Icon For Data ProtectionPresenting our set of slides with Information Security Management Icon For Data Protection. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Information Security Management Icon, Data Protection.
-
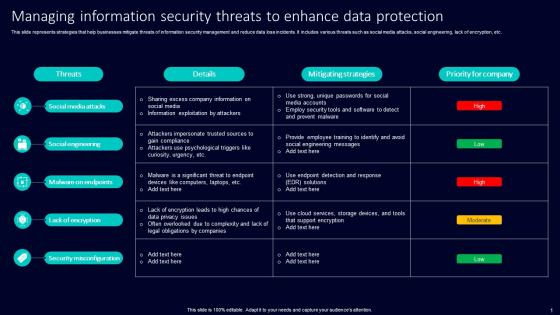 Managing Information Security Threats To Enhance Data Protection
Managing Information Security Threats To Enhance Data ProtectionThis slide represents strategies that help businesses mitigate threats of information security management and reduce data loss incidents. It includes various threats such as social media attacks, social engineering, lack of encryption, etc. Presenting our well structured Managing Information Security Threats To Enhance Data Protection. The topics discussed in this slide are Social Media Attacks, Social Engineering, Malware On Endpoints. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
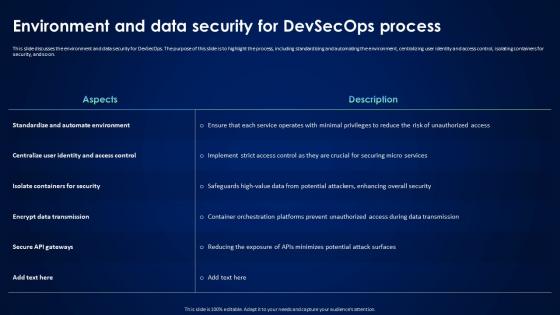 Devsecops Best Practices For Secure Environment And Data Security For Devsecops Process
Devsecops Best Practices For Secure Environment And Data Security For Devsecops ProcessThis slide discusses the environment and data security for DevSecOps. The purpose of this slide is to highlight the process, including standardizing and automating the environment, centralizing user identity and access control, isolating containers for security, and so on. Present the topic in a bit more detail with this Devsecops Best Practices For Secure Environment And Data Security For Devsecops Process. Use it as a tool for discussion and navigation on Standardize And Automate Environment, Isolate Containers For Security, Encrypt Data Transmission. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Components Of Virtual Infrastructure For Effective Data Management And Security
Components Of Virtual Infrastructure For Effective Data Management And SecurityThis slide represents key components of virtual infrastructure that help businesses with data security and disaster management. It includes various components such as virtualized computing, virtualized storage, management solutions, and virtualized security. Introducing our premium set of slides with Components Of Virtual Infrastructure For Effective Data Management And Security. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Virtualized Compute, Virtualized Networking Security, Virtualized Storage. So download instantly and tailor it with your information.
-
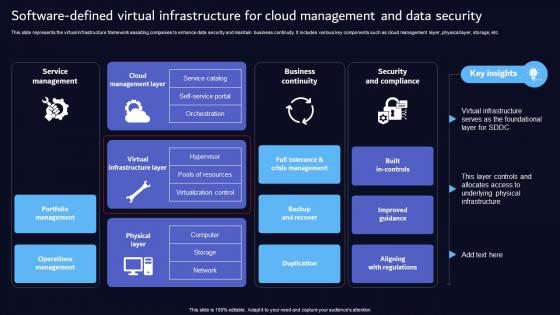 Software Defined Virtual Infrastructure For Cloud Management And Data Security
Software Defined Virtual Infrastructure For Cloud Management And Data SecurityThis slide represents the virtual infrastructure framework assisting companies to enhance data security and maintain business continuity. It includes various key components such as cloud management layer, physical layer, storage, etc. Presenting our well structured Software Defined Virtual Infrastructure For Cloud Management And Data Security. The topics discussed in this slide are Service Management, Business Continuity, Security Compliance. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Backing Up Data To Enhance Security And Efficiency Hands On Blockchain Security Risk BCT SS V
Backing Up Data To Enhance Security And Efficiency Hands On Blockchain Security Risk BCT SS VThe following slide illustrates some methods to regularly backing up data to prevent primary data failures. It includes elements such as regularly backing up, offsite, automated backup and constantly monitoring, etc. Introducing Backing Up Data To Enhance Security And Efficiency Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Regularly Backup, Offsite Backup, Automated Backup, using this template. Grab it now to reap its full benefits.
-
 Wireless Lan Network Icon For Data Security
Wireless Lan Network Icon For Data SecurityPresenting our well structured Wireless Lan Network Icon For Data Security. The topics discussed in this slide are Wireless, Data Security . This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
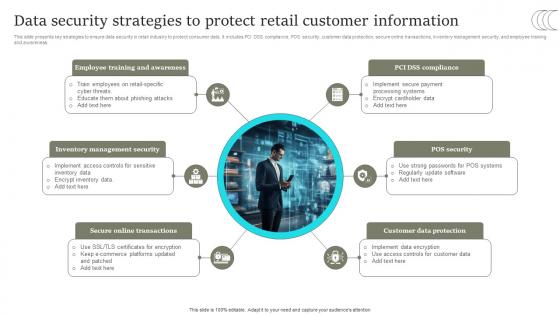 Data Security Strategies To Protect Retail Customer Comprehensive Retail Transformation DT SS
Data Security Strategies To Protect Retail Customer Comprehensive Retail Transformation DT SSThis slide presents key strategies to ensure data security in retail industry to protect consumer data. It includes PCI DSS compliance, POS security, customer data protection, secure online transactions, inventory management security, and employee training and awareness. Present the topic in a bit more detail with this Data Security Strategies To Protect Retail Customer Comprehensive Retail Transformation DT SS. Use it as a tool for discussion and navigation on Online Transactions, Customer Data Protection, POS Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
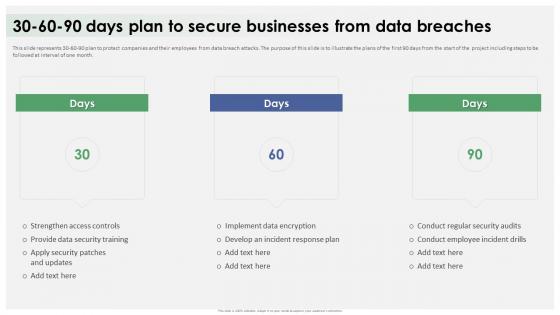 Data Breach Response Plan 30 60 90 Days Plan To Secure Businesses From Data Breaches
Data Breach Response Plan 30 60 90 Days Plan To Secure Businesses From Data BreachesThis slide represents 30-60-90 plan to protect companies and their employees from data breach attacks. The purpose of this slide is to illustrate the plans of the first 90 days from the start of the project including steps to be followed at interval of one month. Increase audience engagement and knowledge by dispensing information using Data Breach Response Plan 30 60 90 Days Plan To Secure Businesses From Data Breaches. This template helps you present information on three stages. You can also present information on Strengthen Access Controls, Conduct Regular Security Audits, Provide Data Security Training using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
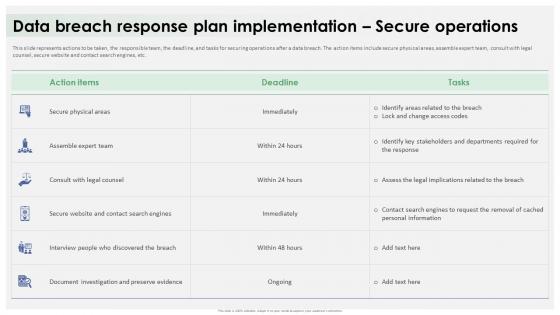 Data Breach Response Plan Implementation Secure Operations
Data Breach Response Plan Implementation Secure OperationsThis slide represents actions to be taken, the responsible team, the deadline, and tasks for securing operations after a data breach. The action items include secure physical areas, assemble expert team, consult with legal counsel, secure website and contact search engines, etc. Present the topic in a bit more detail with this Data Breach Response Plan Implementation Secure Operations. Use it as a tool for discussion and navigation on Secure Physical Areas, Assemble Expert Team, Consult With Legal Counsel, Secure Website. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
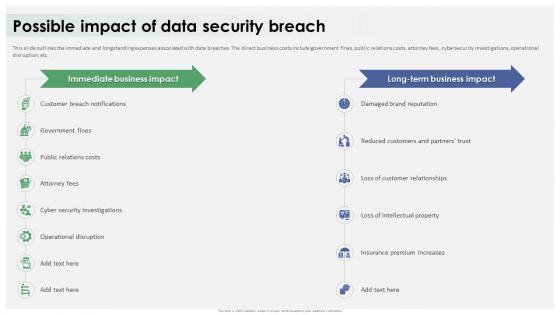 Data Breach Response Plan Possible Impact Of Data Security Breach
Data Breach Response Plan Possible Impact Of Data Security BreachThis slide outlines the immediate and longstanding expenses associated with data breaches. The direct business costs include government fines, public relations costs, attorney fees, cybersecurity investigations, operational disruption, etc. Present the topic in a bit more detail with this Data Breach Response Plan Possible Impact Of Data Security Breach. Use it as a tool for discussion and navigation on Customer Breach Notifications, Loss Of Customer Relationships, Operational Disruption, Damaged Brand Reputation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
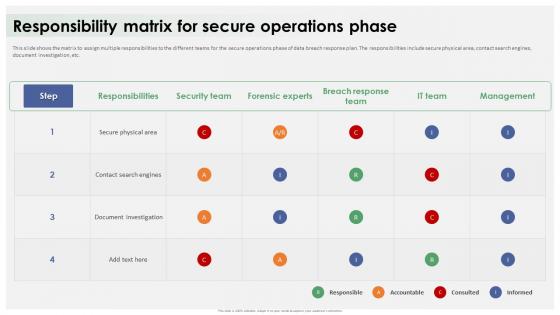 Data Breach Response Plan Responsibility Matrix For Secure Operations Phase
Data Breach Response Plan Responsibility Matrix For Secure Operations PhaseThis slide shows the matrix to assign multiple responsibilities to the different teams for the secure operations phase of data breach response plan. The responsibilities include secure physical area, contact search engines, document investigation, etc. Present the topic in a bit more detail with this Data Breach Response Plan Responsibility Matrix For Secure Operations Phase. Use it as a tool for discussion and navigation on Secure Physical Area, Contact Search Engines, Document Investigation, Responsibility Matrix. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
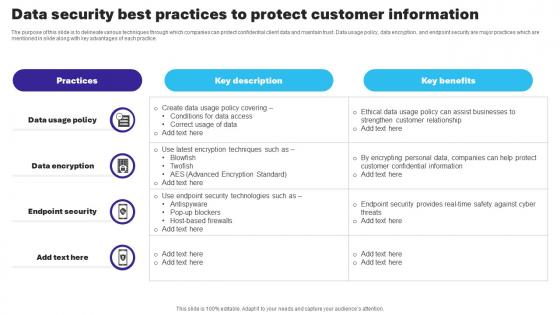 Essential Guide To Database Marketing Data Security Best Practices To Protect Customer Information MKT SS V
Essential Guide To Database Marketing Data Security Best Practices To Protect Customer Information MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Deliver an outstanding presentation on the topic using this Essential Guide To Database Marketing Data Security Best Practices To Protect Customer Information MKT SS V Dispense information and present a thorough explanation of Data Usage Policy, Data Encryption, Endpoint Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
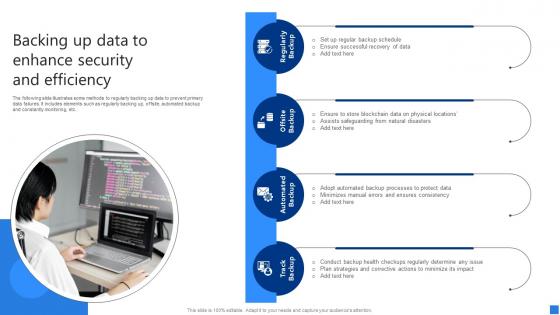 Backing Up Data To Enhance Securing Blockchain Transactions A Beginners Guide BCT SS V
Backing Up Data To Enhance Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide illustrates some methods to regularly backing up data to prevent primary data failures. It includes elements such as regularly backing up, offsite, automated backup and constantly monitoring, etc. Introducing Backing Up Data To Enhance Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Regularly Backup, Offsite Backup, Automated Backup, using this template. Grab it now to reap its full benefits.
-
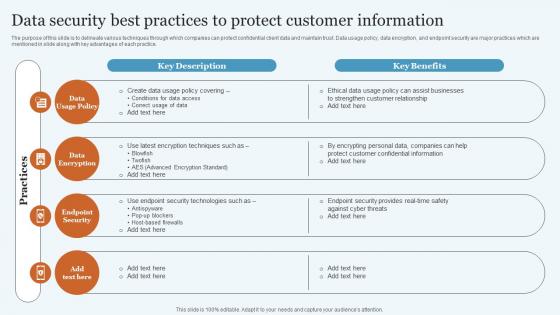 Data Security Best Practices To Protect Database Marketing Practices To Increase MKT SS V
Data Security Best Practices To Protect Database Marketing Practices To Increase MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Increase audience engagement and knowledge by dispensing information using Data Security Best Practices To Protect Database Marketing Practices To Increase MKT SS V. This template helps you present information on four stages. You can also present information on Policy, Encryption, Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data Highlighting Cyber Security Unawareness Among Employees Creating Cyber Security Awareness
Data Highlighting Cyber Security Unawareness Among Employees Creating Cyber Security AwarenessThe following slide depicts some figures to analyse the awareness gap among staff regarding cyber safety. It includes statistics such as clicking suspicious links, transferring data over personal cloud, securing systems with weak passwords etc. Increase audience engagement and knowledge by dispensing information using Data Highlighting Cyber Security Unawareness Among Employees Creating Cyber Security Awareness This template helps you present information on Five stages. You can also present information on Future Goal Analysis, Business Unit, Risk Category using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
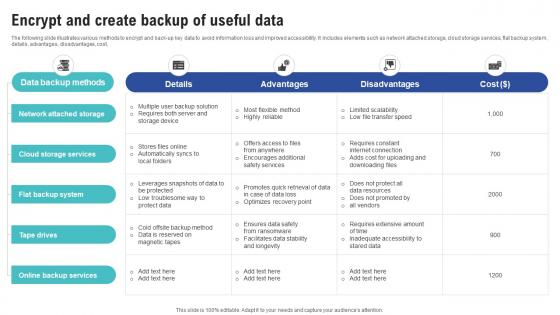 Encrypt And Create Backup Of Useful Data Creating Cyber Security Awareness
Encrypt And Create Backup Of Useful Data Creating Cyber Security AwarenessThe following slide illustrates various methods to encrypt and back-up key data to avoid information loss and improved accessibility. It includes elements such as network attached storage, cloud storage services, flat backup system, details, advantages, disadvantages, cost,. Present the topic in a bit more detail with this Encrypt And Create Backup Of Useful Data Creating Cyber Security Awareness Use it as a tool for discussion and navigation on Accountable, Consulted, Responsible This template is free to edit as deemed fit for your organization. Therefore download it now.
-
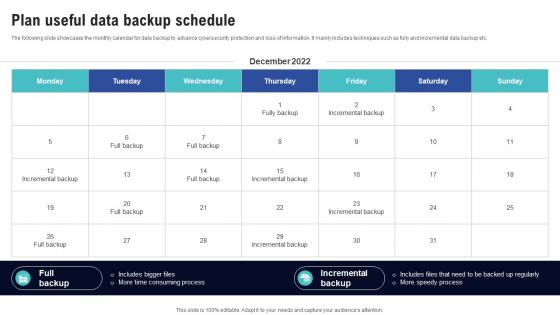 Plan Useful Data Backup Schedule Creating Cyber Security Awareness
Plan Useful Data Backup Schedule Creating Cyber Security AwarenessThe following slide showcases the monthly calendar for data backup to advance cybersecurity protection and loss of information. It mainly includes techniques such as fully and incremental data backup etc. Deliver an outstanding presentation on the topic using this Plan Useful Data Backup Schedule Creating Cyber Security Awareness Dispense information and present a thorough explanation of Security And Privacy, Web Application Security, Infrastructure Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Icon For Insurancing Data Breaches
Cyber Security Icon For Insurancing Data BreachesPresenting our set of slides with Cyber Security Icon For Insurancing Data Breaches. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security Icon, Insurancing Data Breaches.
-
 Online Data Cyber Security Services
Online Data Cyber Security ServicesThis slide showcases data cyber security services that protect personal data and help to preserve reputation. It includes elements such as firewall, antivirus, email filtering, device control and content filtering. Presenting our set of slides with Online Data Cyber Security Services. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Firewall, Antivirus, Device Control.
-
 Backing Up Data To Enhance Security And Efficiency Guide For Blockchain BCT SS V
Backing Up Data To Enhance Security And Efficiency Guide For Blockchain BCT SS VThe following slide illustrates some methods to regularly backing up data to prevent primary data failures. It includes elements such as regularly backing up, offsite, automated backup and constantly monitoring, etc. Introducing Backing Up Data To Enhance Security And Efficiency Guide For Blockchain BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Regularly Backup, Offsite Backup, Automated Backup using this template. Grab it now to reap its full benefits.
-
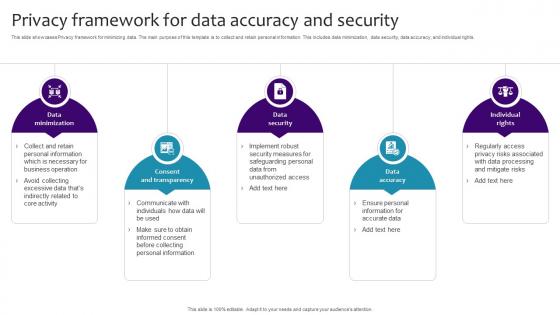 Privacy Framework For Data Accuracy And Security
Privacy Framework For Data Accuracy And SecurityThis slide showcases Privacy framework for minimizing data. The main purpose of this template is to collect and retain personal information. This includes data minimization, data security, data accuracy, and individual rights.Introducing our premium set of slides with Privacy Framework For Data Accuracy And Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Data Minimization, Consent Transparency, Data Accuracy. So download instantly and tailor it with your information.
-
 Privacy Framework Icon For Securing Business Data
Privacy Framework Icon For Securing Business DataPresenting our well structured Privacy Framework Icon For Securing Business Data. The topics discussed in this slide are Privacy Framework Icon, Securing Business Data. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Icon For Ensuring Data Security In Onboarding Procedure
Icon For Ensuring Data Security In Onboarding ProcedureIntroducing our premium set of slides with Icon For Ensuring Data Security In Onboarding Procedure. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Icon, Data Onboarding, Digital Transformation. So download instantly and tailor it with your information.
-
 Blockchain Approaches To Enhance IoT Data Security IoT Security And Privacy Safeguarding IoT SS
Blockchain Approaches To Enhance IoT Data Security IoT Security And Privacy Safeguarding IoT SSThis slide encompasses blockchain technical applications to the IoT ecosystem aimed at enhancing data privacy and security. It includes decentralized system, an immutable ledger, and smart contracts. Increase audience engagement and knowledge by dispensing information using Blockchain Approaches To Enhance IoT Data Security IoT Security And Privacy Safeguarding IoT SS. This template helps you present information on three stages. You can also present information on Decentralized System, Immutable Ledger, Smart Contracts using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
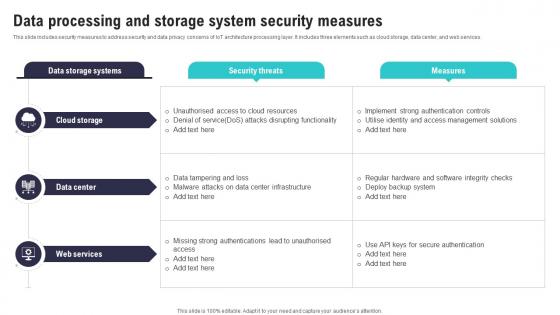 Data Processing And Storage System Security Measures IoT Security And Privacy Safeguarding IoT SS
Data Processing And Storage System Security Measures IoT Security And Privacy Safeguarding IoT SSThis slide includes security measures to address security and data privacy concerns of IoT architecture processing layer. It includes three elements such as cloud storage, data center, and web services. Deliver an outstanding presentation on the topic using this Data Processing And Storage System Security Measures IoT Security And Privacy Safeguarding IoT SS. Dispense information and present a thorough explanation of Data Tampering, Strong Authentications, Regular Hardware using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Edge Computing Role In Securing IoT Data IoT Security And Privacy Safeguarding IoT SS
Edge Computing Role In Securing IoT Data IoT Security And Privacy Safeguarding IoT SSThis slide showcases the significant role of edge computing in enhancing IoT data security and privacy. It include role such as data filtering and processing, localised threat identification, and reduce attack surface. Introducing Edge Computing Role In Securing IoT Data IoT Security And Privacy Safeguarding IoT SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Data Filtering Processing, Reduce Attack Surface, Trusted Entities Interacting, using this template. Grab it now to reap its full benefits.
-
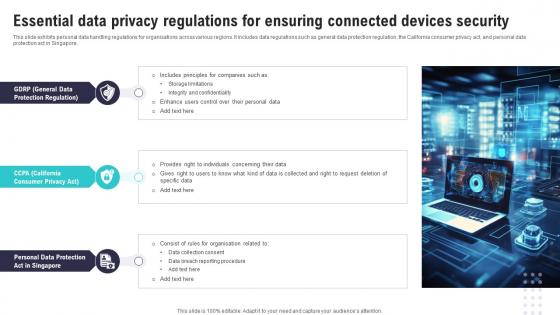 Essential Data Privacy Regulations For Ensuring IoT Security And Privacy Safeguarding IoT SS
Essential Data Privacy Regulations For Ensuring IoT Security And Privacy Safeguarding IoT SSThis slide exhibits personal data handling regulations for organisations across various regions. It includes data regulations such as general data protection regulation, the California consumer privacy act, and personal data protection act in Singapore. Increase audience engagement and knowledge by dispensing information using Essential Data Privacy Regulations For Ensuring IoT Security And Privacy Safeguarding IoT SS. This template helps you present information on three stages. You can also present information on Protection Regulation, Data Collection Consent, Data Breach using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 IoT Data Security Vulnerabilities And Privacy Concerns IoT Security And Privacy Safeguarding IoT SS
IoT Data Security Vulnerabilities And Privacy Concerns IoT Security And Privacy Safeguarding IoT SSThis slide includes common IoT security vulnerabilities and risk that helps organization implement security measures. It includes vulnerabilities such as lack of privacy protection, improper device management approach, default settings, weak credentials, etc. Increase audience engagement and knowledge by dispensing information using IoT Data Security Vulnerabilities And Privacy Concerns IoT Security And Privacy Safeguarding IoT SS. This template helps you present information on six stages. You can also present information on Insecure Data Transfer, Weak Credentials, Insecure Default Settings using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Transforming From Traditional Ethical And Data Security Considerations For Digital Innovation DT SS
Transforming From Traditional Ethical And Data Security Considerations For Digital Innovation DT SSThis slide presents important ethical and legal considerations in the digital landscape. It mentions description, laws necessary for maintaining regulations including data privacy, cybersecurity and intellectual property. Introducing Transforming From Traditional Ethical And Data Security Considerations For Digital Innovation DT SS to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Data Privacy, Cybersecurity, Intellectual Property using this template. Grab it now to reap its full benefits.
-
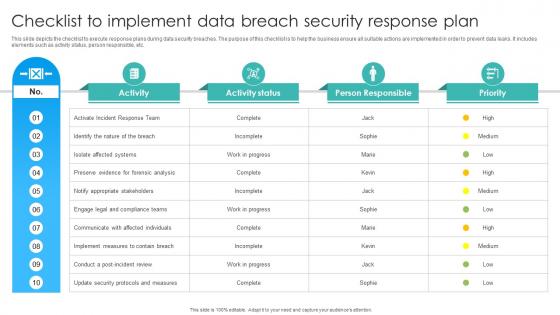 Checklist To Implement Data Breach Security Response Plan
Checklist To Implement Data Breach Security Response PlanThis slide depicts the checklist to execute response plans during data security breaches. The purpose of this checklist is to help the business ensure all suitable actions are implemented in order to prevent data leaks. It includes elements such as activity status, person responsible, etc. Presenting our well structured Checklist To Implement Data Breach Security Response Plan. The topics discussed in this slide are Isolate Affected Systems, Notify Appropriate Stakeholders, Identify The Nature. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Devops Automation Icon For Data Security
Devops Automation Icon For Data SecurityPresenting our set of slides with Devops Automation Icon For Data Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Devops Automation, Icon, Data Security .
-
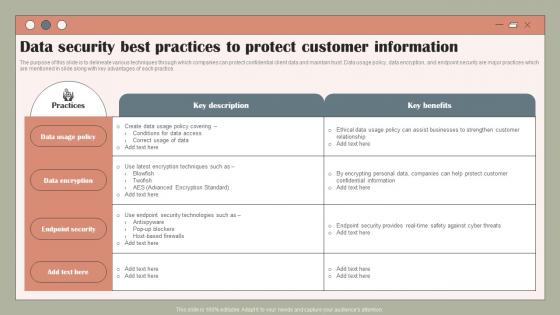 Data Security Best Practices To Protect Using Customer Data To Improve MKT SS V
Data Security Best Practices To Protect Using Customer Data To Improve MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Deliver an outstanding presentation on the topic using this Data Security Best Practices To Protect Using Customer Data To Improve MKT SS V. Dispense information and present a thorough explanation of Policy, Data, Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data Security Strategies To Protect Retail Customer Digital Transformation Of Retail DT SS
Data Security Strategies To Protect Retail Customer Digital Transformation Of Retail DT SSThis slide presents key strategies to ensure data security in retail industry to protect consumer data. It includes PCI DSS compliance, POS security, customer data protection, secure online transactions, inventory management security, and employee training and awareness. Increase audience engagement and knowledge by dispensing information using Data Security Strategies To Protect Retail Customer Digital Transformation Of Retail DT SS This template helps you present information on six stages. You can also present information on Customer Data Protection, Online Transactions, Management Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Overview Need For Implementing Data Security Across Retail Digital Transformation Of Retail DT SS
Overview Need For Implementing Data Security Across Retail Digital Transformation Of Retail DT SSThis slide analyses the need of implementing data security initiatives to address key customer data challenges in retail industry. It also mentions types of customer data collected such as account, location, browsing, and profile. Deliver an outstanding presentation on the topic using this Overview Need For Implementing Data Security Across Retail Digital Transformation Of Retail DT SS Dispense information and present a thorough explanation of Customer Trust, Sensitive Information, Balancing Personalization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Threats In Blockchain Backing Up Data To Enhance Security And Efficiency BCT SS V
Cyber Threats In Blockchain Backing Up Data To Enhance Security And Efficiency BCT SS VThe following slide illustrates some methods to regularly backing up data to prevent primary data failures. It includes elements such as regularly backing up, offsite, automated backup and constantly monitoring, etc. Introducing Cyber Threats In Blockchain Backing Up Data To Enhance Security And Efficiency BCT SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Regularly Backup, Automated Backup, Track Backup using this template. Grab it now to reap its full benefits.
-
 Data Centre Colocations Icon For Securing Information
Data Centre Colocations Icon For Securing InformationPresenting our set of slides with Data Centre Colocations Icon For Securing Information This exhibits information on Three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Centre Colocations Icon, For Securing Information
-
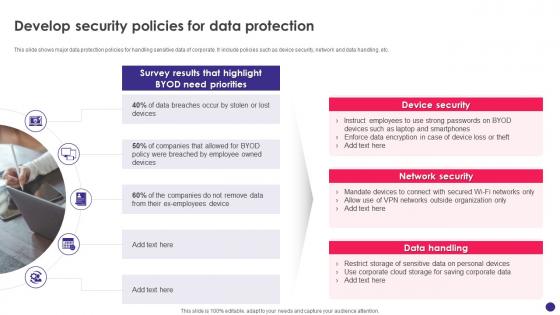 Implementing Byod Policy To Enhance Develop Security Policies For Data Protection
Implementing Byod Policy To Enhance Develop Security Policies For Data ProtectionThis slide shows major data protection policies for handling sensitive data of corporate. It include policies such as device security, network and data handling, etc. Introducing Implementing Byod Policy To Enhance Develop Security Policies For Data Protection to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Network Security, Data Handling, Device Security, Data Protection, using this template. Grab it now to reap its full benefits.
-
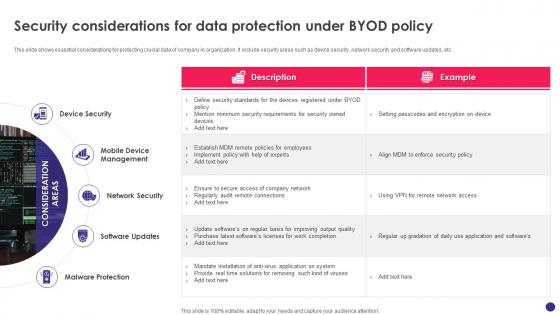 Implementing Byod Policy To Enhance Security Considerations For Data Protection Under Byod Policy
Implementing Byod Policy To Enhance Security Considerations For Data Protection Under Byod PolicyThis slide shows essential considerations for protecting crucial data of company in organization. It include security areas such as device security, network security and software updates, etc. Increase audience engagement and knowledge by dispensing information using Implementing Byod Policy To Enhance Security Considerations For Data Protection Under Byod Policy. This template helps you present information on five stages. You can also present information on Device Security, Mobile Device Management, Network Security, Malware Protection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
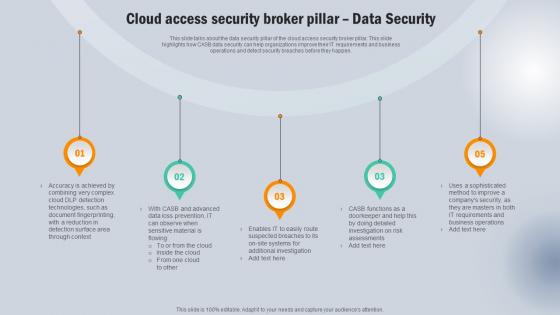 Cloud Access Security Broker Pillar Data Security Next Generation CASB
Cloud Access Security Broker Pillar Data Security Next Generation CASBThis slide talks about the data security pillar of the cloud access security broker pillar. This slide highlights how CASB data security can help organizations improve their IT requirements and business operations and detect security breaches before they happen. Increase audience engagement and knowledge by dispensing information using Cloud Access Security Broker Pillar Data Security Next Generation CASB This template helps you present information on five stages. You can also present information on Complex Cloud, Sensitive Material, Risk Assessments using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
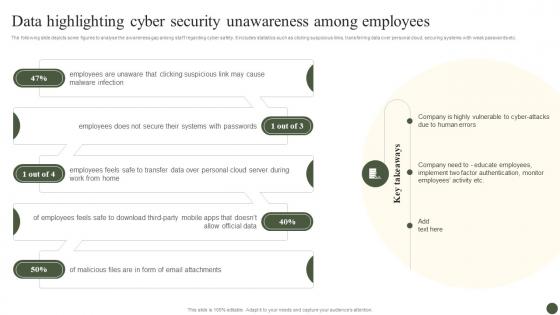 Data Highlighting Cyber Security Unawareness Among Implementing Cyber Risk Management Process
Data Highlighting Cyber Security Unawareness Among Implementing Cyber Risk Management ProcessThe following slide depicts some figures to analyse the awareness gap among staff regarding cyber safety. It includes statistics such as clicking suspicious links, transferring data over personal cloud, securing systems with weak passwords etc. Increase audience engagement and knowledge by dispensing information using Data Highlighting Cyber Security Unawareness Among Implementing Cyber Risk Management Process. This template helps you present information on five stages. You can also present information on Malware Infection, Systems With Passwords, Employees Feels, Allow Official Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
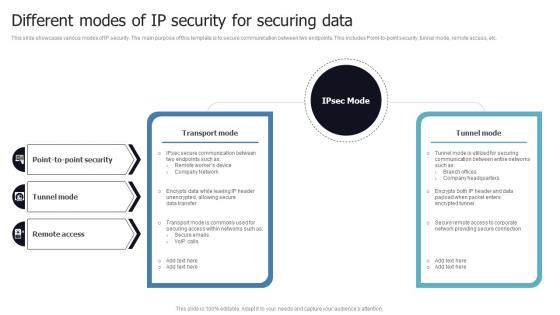 Different Modes Of IP Security For Securing Data
Different Modes Of IP Security For Securing DataThis slide showcases various modes of IP security. The main purpose of this template is to secure communication between two endpoints. This includes Point-to-point security, tunnel mode, remote access, etc. Introducing our Different Modes Of IP Security For Securing Data set of slides. The topics discussed in these slides are IP Security, Secure Communication, Point To Point Security, Tunnel Mode. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.



