Powerpoint Templates and Google slides for Defining Cyber Terrorism
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
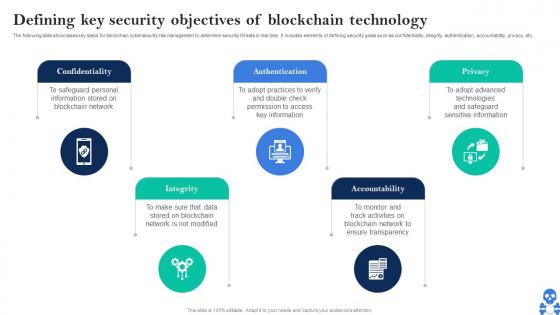 Cyber Threats In Blockchain Defining Key Security Objectives Of Blockchain Technology BCT SS V
Cyber Threats In Blockchain Defining Key Security Objectives Of Blockchain Technology BCT SS VThe following slide showcases key steps for blockchain cybersecurity risk management to determine security threats in real time. It includes elements of defining security goals such as confidentiality, integrity, authentication, accountability, privacy, etc. Introducing Cyber Threats In Blockchain Defining Key Security Objectives Of Blockchain Technology BCT SS V to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Confidentiality, Integrity, Authentication using this template. Grab it now to reap its full benefits.
-
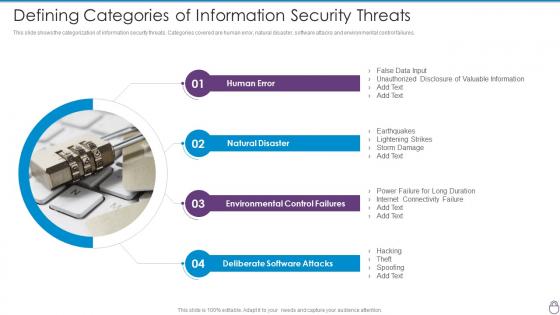 Cybersecurity Risk Management Framework Defining Categories Of Information Security
Cybersecurity Risk Management Framework Defining Categories Of Information SecurityThis slide shows the categorization of information security threats. Categories covered are human error, natural disaster, software attacks and environmental control failures. Introducing Cybersecurity Risk Management Framework Defining Categories Of Information Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Human Error, Natural Disaster, Environmental Control Failures, Deliberate Software Attacks, using this template. Grab it now to reap its full benefits.
-
 Cybersecurity Risk Management Framework Defining Risk Level
Cybersecurity Risk Management Framework Defining Risk LevelFollowing slide defines the incident risk level. It includes details about risk level, risk score and its description. Present the topic in a bit more detail with this Cybersecurity Risk Management Framework Defining Risk Level. Use it as a tool for discussion and navigation on Risk Level, Operations, Organization, Effective Mitigation Plan. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
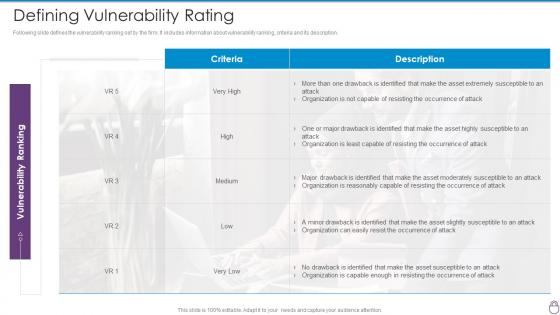 Cybersecurity Risk Management Framework Defining Vulnerability Rating
Cybersecurity Risk Management Framework Defining Vulnerability RatingFollowing slide defines the vulnerability ranking set by the firm. It includes information about vulnerability ranking, criteria and its description. Deliver an outstanding presentation on the topic using this Cybersecurity Risk Management Framework Defining Vulnerability Rating. Dispense information and present a thorough explanation of Occurrence Attack, Asset Moderately Susceptible, Asset Highly Susceptible using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Defining business priorities to ensure managing cyber risk in a digital age
Defining business priorities to ensure managing cyber risk in a digital ageThis slide illustrates the key business priorities of the organization such as efficient risk management, standardized incident management process to ensure information security. Increase audience engagement and knowledge by dispensing information using Defining Business Priorities To Ensure Managing Cyber Risk In A Digital Age. This template helps you present information on five stages. You can also present information on Management, Process, Standardized, Communication using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Defining risk events based on impact size managing cyber risk in a digital age
Defining risk events based on impact size managing cyber risk in a digital ageThis slide provides information about risk based events that company will use to define the risks based on impact size and likelihood of occurrence. Present the topic in a bit more detail with this Events Based On Impact Size Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Defining Risk Events Based On Impact Size And Likelihood Of Occurrence. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
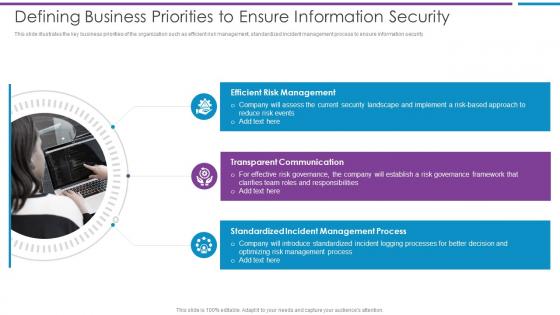 Defining Business Priorities To Ensure Information Security Risk Based Methodology To Cyber
Defining Business Priorities To Ensure Information Security Risk Based Methodology To CyberThis slide illustrates the key business priorities of the organization such as efficient risk management, standardized incident management process to ensure information security.Increase audience engagement and knowledge by dispensing information using Defining Business Priorities To Ensure Information Security Risk Based Methodology To Cyber This template helps you present information on three stages. You can also present information on Efficient Risk Management, Transparent Communication, Standardized Incident using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Defining Business Security Introducing A Risk Based Approach To Cyber Security
Defining Business Security Introducing A Risk Based Approach To Cyber SecurityThis slide illustrates the key business priorities of the organization such as efficient risk management, standardized incident management process to ensure information security.Introducing Defining Business Security Introducing A Risk Based Approach To Cyber Security to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Efficient Risk Management, Standardized Incident, Management Process using this template. Grab it now to reap its full benefits.
-
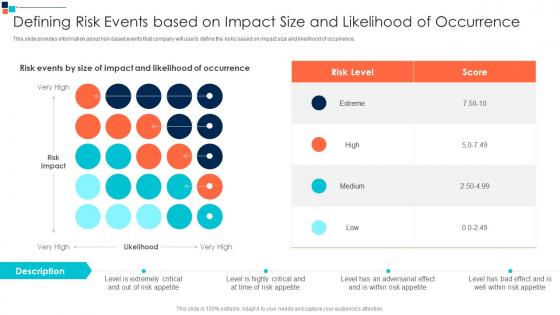 Defining Risk Events Based On Introducing A Risk Based Approach To Cyber Security
Defining Risk Events Based On Introducing A Risk Based Approach To Cyber SecurityThis slide provides information about risk based events that company will use to define the risks based on impact size and likelihood of occurrence.Present the topic in a bit more detail with this Defining Risk Events Based On Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on Defining Risk Events Based On Impact Size And Likelihood Of Occurrence This template is free to edit as deemed fit for your organization. Therefore download it now.
-
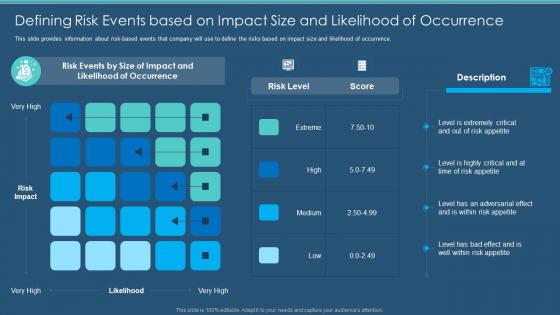 Information Security Program Cybersecurity Defining Risk Events Based On Impact Size
Information Security Program Cybersecurity Defining Risk Events Based On Impact SizeThis slide provides information about risk based events that company will use to define the risks based on impact size and likelihood of occurrence. Deliver an outstanding presentation on the topic using this Information Security Program Cybersecurity Defining Risk Events Based On Impact Size. Dispense information and present a thorough explanation of Occurrence, Likelihood, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cybersecurity and digital business risk management defining business priorities
Cybersecurity and digital business risk management defining business prioritiesThis slide illustrates the key business priorities of the organization such as efficient risk management, standardized incident management process to ensure information security. Introducing Cybersecurity And Digital Business Risk Management Defining Business Priorities to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Management, Communication, Process, using this template. Grab it now to reap its full benefits.
-
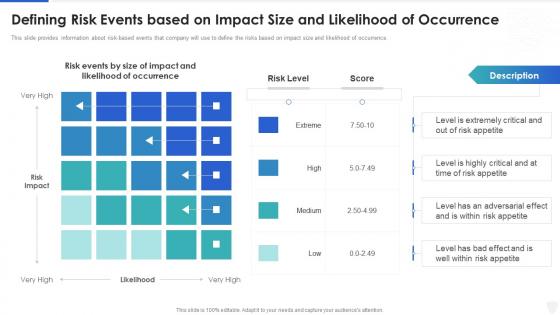 Cybersecurity and digital business risk management defining risk events based on impact
Cybersecurity and digital business risk management defining risk events based on impactThis slide provides information about risk-based events that company will use to define the risks based on impact size and likelihood of occurrence. Present the topic in a bit more detail with this Cybersecurity And Digital Business Risk Management Defining Risk Events Based On Impact. Use it as a tool for discussion and navigation on Defining Risk Events Based On Impact Size And Likelihood Of Occurrence. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Define access control measures for employees cyber security it ppt powerpoint pictures
Define access control measures for employees cyber security it ppt powerpoint picturesThis slide represents how it is essential to minimize the rights or access of employees in an organization to keep data safe and prevent it from deletion, manipulation. Introducing Define Access Control Measures For Employees Cyber Security IT Ppt Powerpoint Pictures to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Responsibilities, Access Data, Organization, Staff Duties, using this template. Grab it now to reap its full benefits.

