Powerpoint Templates and Google slides for Follow Security Rules
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
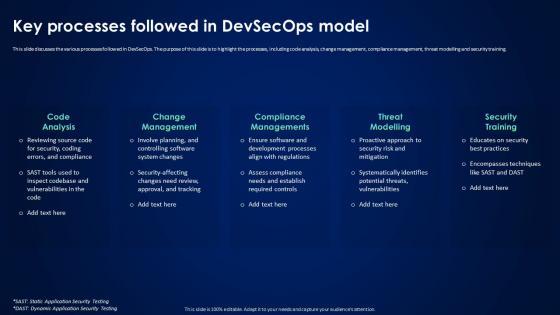 Devsecops Best Practices For Secure Key Processes Followed In Devsecops Model
Devsecops Best Practices For Secure Key Processes Followed In Devsecops ModelThis slide discusses the various processes followed in DevSecOps. The purpose of this slide is to highlight the processes, including code analysis, change management, compliance management, threat modelling and security training. Increase audience engagement and knowledge by dispensing information using Devsecops Best Practices For Secure Key Processes Followed In Devsecops Model. This template helps you present information on five stages. You can also present information on Code Analysis, Change Management, Compliance Managements, Threat Modelling using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
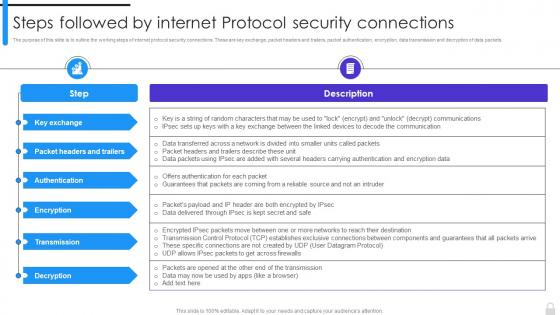 Encryption Implementation Strategies Steps Followed By Internet Protocol Security Connections
Encryption Implementation Strategies Steps Followed By Internet Protocol Security ConnectionsThe purpose of this slide is to outline the working steps of internet protocol security connections. These are key exchange, packet headers and trailers, packet authentication, encryption, data transmission and decryption of data packets. Present the topic in a bit more detail with this Encryption Implementation Strategies Steps Followed By Internet Protocol Security Connections. Use it as a tool for discussion and navigation on Protocol Security Connections, Packet Authentication, Encryption, Data Transmission, Decryption Of Data Packets. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
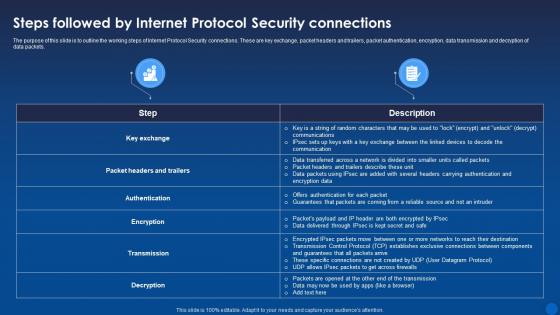 Steps Followed By Internet Protocol Security Connections Encryption For Data Privacy In Digital Age It
Steps Followed By Internet Protocol Security Connections Encryption For Data Privacy In Digital Age ItThe purpose of this slide is to outline the working steps of Internet Protocol Security connections. These are key exchange, packet headers and trailers, packet authentication, encryption, data transmission and decryption of data packets. Deliver an outstanding presentation on the topic using this Steps Followed By Internet Protocol Security Connections Encryption For Data Privacy In Digital Age It. Dispense information and present a thorough explanation of Connections, Protocol Security, Data Transmission using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Devsecops Best Practices For Secure Best Practices Followed In Organization For Devsecops
Devsecops Best Practices For Secure Best Practices Followed In Organization For DevsecopsThis slide showcases the best practices for the DevSecOps in an organization. The purpose of this slide is to highlight the best practices, these include shift security left, implementing CI or CD, obfuscation techniques, micro services architecture, and so on. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure Best Practices Followed In Organization For Devsecops. Dispense information and present a thorough explanation of Obfuscation Techniques, Cloud Native Technologies, Activity Monitoring And Logging using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Devsecops Best Practices For Secure Core Principles Followed In Devsecops Model
Devsecops Best Practices For Secure Core Principles Followed In Devsecops ModelThis slide discusses the core principle used in the DevSecOps model. The purpose of this slide is to explain the principles of DevSecOps in detail, these include automation, continuous monitoring, and collaboration across functions. Increase audience engagement and knowledge by dispensing information using Devsecops Best Practices For Secure Core Principles Followed In Devsecops Model. This template helps you present information on three stages. You can also present information on Continuous Monitoring, Collaboration Across Functions, Configuration Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Secure Your Digital Assets Immediate Actions To Undertake Following A Scam Incident
Secure Your Digital Assets Immediate Actions To Undertake Following A Scam IncidentThe purpose of this slide is to outline the steps to follow after the scam. This slide highlights the actions to be taken after the fraud, such as maintaining calm and composure, documenting the incident, and contacting the authorities. Introducing Secure Your Digital Assets Immediate Actions To Undertake Following A Scam Incident to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Documenting The Incident, Contacting The Authorities, Maintaining Calm And Composure, using this template. Grab it now to reap its full benefits.
-
 Secure Your Digital Assets Steps To Follow For Creating A Crypto Wallet
Secure Your Digital Assets Steps To Follow For Creating A Crypto WalletThe purpose of this slide is to discuss the steps to follow while opening the crypto wallet. This slide highlights those steps, such as selecting the software app, downloading the wallet app, creating the account, transferring the assets, etc. Increase audience engagement and knowledge by dispensing information using Secure Your Digital Assets Steps To Follow For Creating A Crypto Wallet. This template helps you present information on five stages. You can also present information on Crypto Wallet, Transferring The Assets, Downloading The Wallet App using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Secure Your Digital Assets Steps To Follow For Creating Crypto Wallet
Secure Your Digital Assets Steps To Follow For Creating Crypto WalletThe purpose of this slide is to discuss the steps to follow while opening the crypto wallet. This slide highlights those steps, such as selecting the software app, downloading the wallet app, creating the account, transferring the assets, etc. Introducing Secure Your Digital Assets Steps To Follow For Creating Crypto Wallet to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Crypto Wallet, Software App, Downloading The Wallet App, Transferring The Assets, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Incidents Follow Up Report Ppt Powerpoint Presentation Professional Background
Cyber Security Incidents Follow Up Report Ppt Powerpoint Presentation Professional BackgroundThis slide represents the follow-up report prepared by cyber security incident management team after successfully responding to cyber incidents experienced by the organization. It includes details related to date of incident, actions taken by responsible officer. Present the topic in a bit more detail with this Cyber Security Incidents Follow Up Report Ppt Powerpoint Presentation Professional Background. Use it as a tool for discussion and navigation on Information Security, Cyber Security, Organizational Projects. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
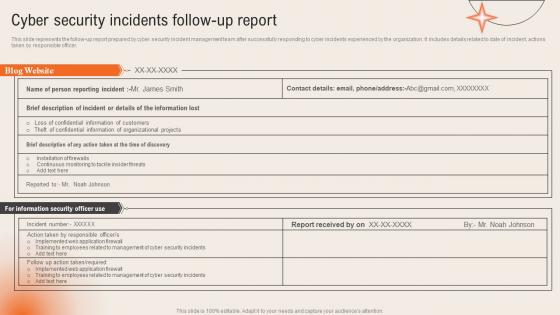 Cyber Security Incidents Follow Up Report Deploying Computer Security Incident Management
Cyber Security Incidents Follow Up Report Deploying Computer Security Incident ManagementThis slide represents the follow up report prepared by cyber security incident management team after successfully responding to cyber incidents experienced by the organization. It includes details related to date of incident, actions taken by responsible officer.Present the topic in a bit more detail with this Cyber Security Incidents Follow Up Report Deploying Computer Security Incident Management. Use it as a tool for discussion and navigation on Confidential Information, Training Employees, Organizational Projects. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Incidents Follow Up Report Development And Implementation Of Security Incident Management
Cyber Security Incidents Follow Up Report Development And Implementation Of Security Incident ManagementThis slide represents the follow up report prepared by cyber security incident management team after successfully responding to cyber incidents experienced by the organization. It includes details related to date of incident, actions taken by responsible officer. Present the topic in a bit more detail with this Cyber Security Incidents Follow Up Report Development And Implementation Of Security Incident Management. Use it as a tool for discussion and navigation on Confidential Information Customers, Theft Confidential Information, Organizational Projects. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
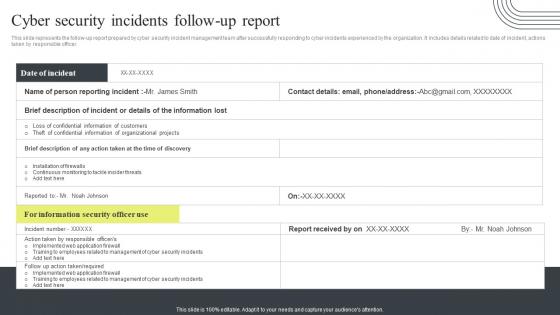 Cyber Security Attacks Response Plan Cyber Security Incidents Follow Up Report
Cyber Security Attacks Response Plan Cyber Security Incidents Follow Up ReportThis slide represents the follow up report prepared by cyber security incident management team after successfully responding to cyber incidents experienced by the organization. It includes details related to date of incident, actions taken by responsible officer. Present the topic in a bit more detail with this Cyber Security Attacks Response Plan Cyber Security Incidents Follow Up Report. Use it as a tool for discussion and navigation on Cyber Security Incidents, Follow Up Report, Management Team. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
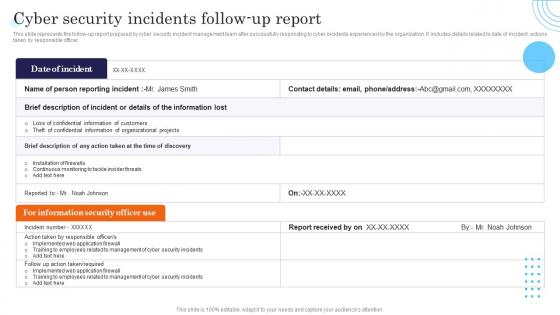 Cyber Security Incidents Follow Up Report Incident Response Strategies Deployment
Cyber Security Incidents Follow Up Report Incident Response Strategies DeploymentThis slide represents the follow up report prepared by cyber security incident management team after successfully responding to cyber incidents experienced by the organization. It includes details related to date of incident, actions taken by responsible officer. Deliver an outstanding presentation on the topic using this Cyber Security Incidents Follow Up Report Incident Response Strategies Deployment. Dispense information and present a thorough explanation of Security, Incident, Cyber using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
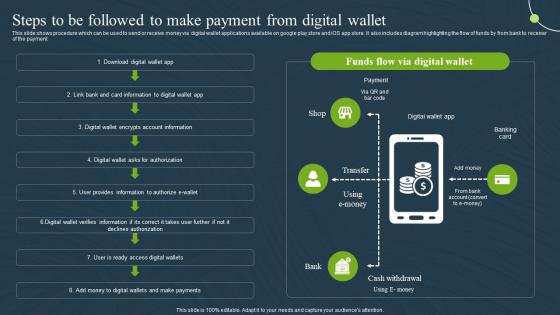 Steps To Be Followed To Make Wallet Mobile Banking For Convenient And Secure Online Payments Fin SS
Steps To Be Followed To Make Wallet Mobile Banking For Convenient And Secure Online Payments Fin SSThis slide shows procedure which can be used to send or receive money via digital wallet applications available on google play store and iOS app store. It also includes diagram highlighting the flow of funds by from bank to receiver of the payment. Deliver an outstanding presentation on the topic using this Steps To Be Followed To Make Wallet Mobile Banking For Convenient And Secure Online Payments Fin SS. Dispense information and present a thorough explanation of Information, Authorization, Applications using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 We provide the following services for your convenience in for security bid proposal
We provide the following services for your convenience in for security bid proposalPresenting this set of slides with name We Provide The Following Services For Your Convenience In For Security Bid Proposal. This is a eight stage process. The stages in this process are Management, Investigative Work, Provide Services, Team, Communication. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 We provide the following services for your convenience in security template proposal ppt slides
We provide the following services for your convenience in security template proposal ppt slidesPresenting this set of slides with name We Provide The Following Services For Your Convenience In Security Template Proposal Ppt Slides. The topics discussed in these slides are Security Services, Management, Investigation. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Manage follow security standards ppt powerpoint presentation design templates cpb
Manage follow security standards ppt powerpoint presentation design templates cpbPresenting our Manage Follow Security Standards Ppt Powerpoint Presentation Design Templates Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Manage Follow Security Standards This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.

