Powerpoint Templates and Google slides for Hacked
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Crypto Bridge Hack In Powerpoint And Google Slides Cpb
Crypto Bridge Hack In Powerpoint And Google Slides CpbPresenting Crypto Bridge Hack In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Crypto Bridge Hack. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Credit Card Point Hacking In Powerpoint And Google Slides Cpb
Credit Card Point Hacking In Powerpoint And Google Slides CpbPresenting Credit Card Point Hacking In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase six stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Credit Card Point Hacking. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Hack Telegram Account In Powerpoint And Google Slides Cpb
Hack Telegram Account In Powerpoint And Google Slides CpbPresenting Hack Telegram Account In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Hack Telegram Account. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Blog Hacks Jobs In Powerpoint And Google Slides Cpb
Blog Hacks Jobs In Powerpoint And Google Slides CpbPresenting our Blog Hacks Jobs In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Blog Hacks Jobs. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Content Writing Hacks In Powerpoint And Google Slides Cpb
Content Writing Hacks In Powerpoint And Google Slides CpbPresenting our Content Writing Hacks In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Content Writing Hacks. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Travel Hacking Beginners In Powerpoint And Google Slides Cpb
Travel Hacking Beginners In Powerpoint And Google Slides CpbPresenting our Travel Blogging Tips In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Travel Hacking Beginners This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Writing Hack Types In Powerpoint And Google Slides Cpb
Writing Hack Types In Powerpoint And Google Slides CpbPresenting Writing Hack Types In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Writing Hack Types. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Cybercrime Hack Credit Cards Online Shopping In Powerpoint And Google Slides Cpb
Cybercrime Hack Credit Cards Online Shopping In Powerpoint And Google Slides CpbPresenting Cybercrime Hack Credit Cards Online Shopping In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Hack Credit Cards Online Shopping. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Credit Score Hack Extra Payment In Powerpoint And Google Slides Cpb
Credit Score Hack Extra Payment In Powerpoint And Google Slides CpbPresenting our Credit Score Hack Extra Payment In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Credit Score Hack Extra Payment. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Competitive Marketing Hacking Innovative Growth Marketing Techniques For Modern Businesses MKT SS
Competitive Marketing Hacking Innovative Growth Marketing Techniques For Modern Businesses MKT SSThis slide illustrates the comparison between growth marketing and growth hacking that enable marketers to analyse both strategies. It compares them based on focus, approach, objective, methodology, planning, etc. Present the topic in a bit more detail with this Competitive Marketing Hacking Innovative Growth Marketing Techniques For Modern Businesses MKT SS. Use it as a tool for discussion and navigation on Analysis, Growth, Marketing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
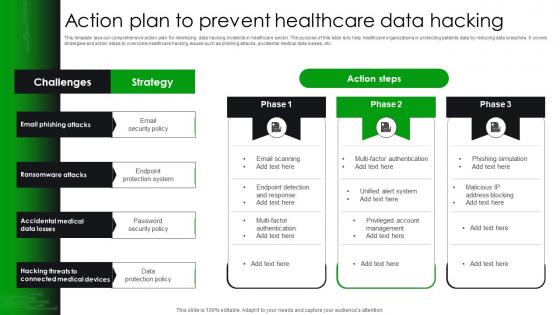 Action Plan To Prevent Healthcare Data Hacking
Action Plan To Prevent Healthcare Data HackingThis template lays out comprehensive action plan for minimizing data hacking incidents in healthcare sector. The purpose of this slide is to help healthcare organizations in protecting patients data by reducing data breaches. It covers strategies and action steps to overcome healthcare hacking issues such as phishing attacks, accidental medical data losses, etc.Introducing our Action Plan To Prevent Healthcare Data Hacking set of slides. The topics discussed in these slides are Ransomware Attacks, Accidental Medical, Connected Medical Devices This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Advanced Security Icon To Prevent Cyber Hacking
Advanced Security Icon To Prevent Cyber HackingPresenting our well structured Advanced Security Icon To Prevent Cyber Hacking The topics discussed in this slide are Advanced Security Icon, Prevent Cyber Hacking. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
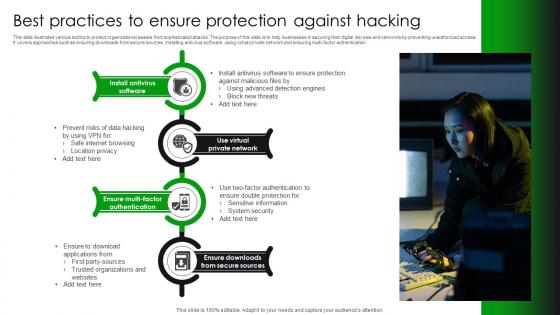 Best Practices To Ensure Protection Against Hacking
Best Practices To Ensure Protection Against HackingThis slide illustrates various tactics to protect organizational assets from sophisticated attacks. The purpose of this slide is to help businesses in securing their digital devices and networks by preventing unauthorized access. It covers approaches such as ensuring downloads from secure sources , installing antivirus software, using virtual private network and ensuring multi factor authentication.Presenting our set of slides with Best Practices To Ensure Protection Against Hacking This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Install Antivirus Software, Ensure Downloads, Secure Sources.
-
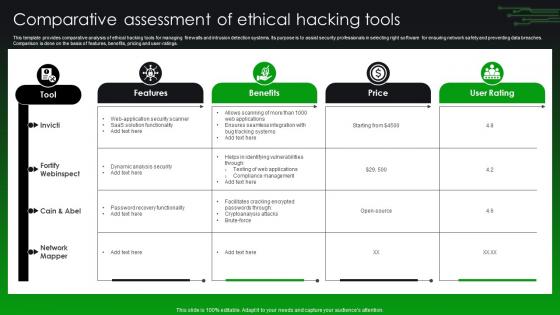 Comparative Assessment Of Ethical Hacking Tools
Comparative Assessment Of Ethical Hacking ToolsThis template provides comparative analysis of ethical hacking tools for managing firewalls and intrusion detection systems. Its purpose is to assist security professionals in selecting right software for ensuring network safety and preventing data breaches. Comparison is done on the basis of features, benefits, pricing and user ratings.Introducing our Comparative Assessment Of Ethical Hacking Tools set of slides. The topics discussed in these slides are Dynamic Analysis Security, Password Recovery, Cryptoanalysis Attacks This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
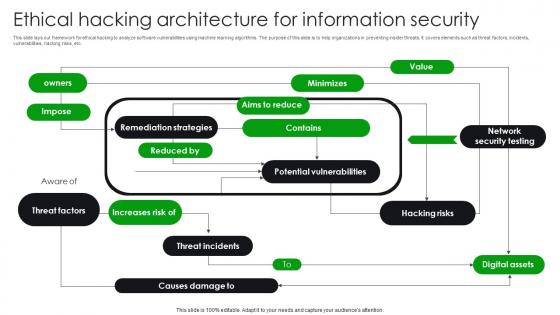 Ethical Hacking Architecture For Information Security
Ethical Hacking Architecture For Information SecurityThis slide lays out framework for ethical hacking to analyze software vulnerabilities using machine learning algorithms. The purpose of this slide is to help organizations in preventing insider threats. It covers elements such as threat factors, incidents, vulnerabilities, hacking risks, etc.Presenting our well structured Ethical Hacking Architecture For Information Security The topics discussed in this slide are Remediation Strategies, Potential Vulnerabilities, Network Security Testing. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Ethical Hacking Icon For Iot Security
Ethical Hacking Icon For Iot SecurityIntroducing our premium set of slides with Ethical Hacking Icon For Iot Security Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Ethical Hacking Icon, Iot Security. So download instantly and tailor it with your information.
-
 Ethical Hacking Icon To Prevent Banking Ransomware Attacks
Ethical Hacking Icon To Prevent Banking Ransomware AttacksIntroducing our Ethical Hacking Icon To Prevent Banking Ransomware Attacks set of slides. The topics discussed in these slides are Ethical Hacking Icon, Prevent Banking, Ransomware Attacks This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
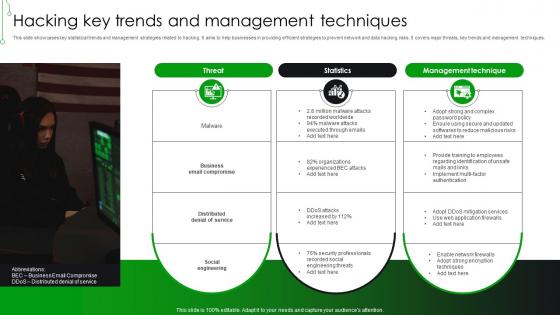 Hacking Key Trends And Management Techniques
Hacking Key Trends And Management TechniquesThis slide showcases key statistical trends and management strategies related to hacking. It aims to help businesses in providing efficient strategies to prevent network and data hacking risks. It covers major threats, key trends and management techniques. Presenting our set of slides with Hacking Key Trends And Management Techniques This exhibits information on one stage of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Business Email Compromise, Security Professionals, Management Technique.
-
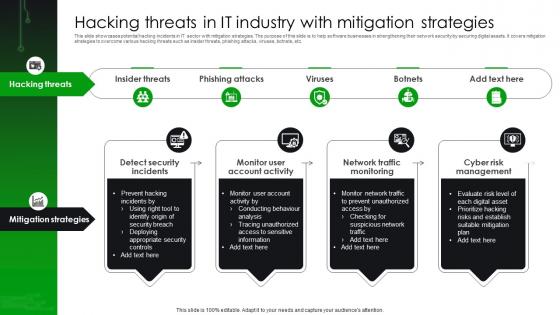 Hacking Threats In IT Industry With Mitigation Strategies
Hacking Threats In IT Industry With Mitigation StrategiesThis slide showcases potential hacking incidents in IT sector with mitigation strategies. The purpose of this slide is to help software businesses in strengthening their network security by securing digital assets. It covers mitigation strategies to overcome various hacking threats such as insider threats, phishing attacks, viruses, botnets, etc. Introducing our premium set of slides with Hacking Threats In IT Industry With Mitigation Strategies Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Insider Threats, Monitor Account Activity, Network Traffic Monitoring. So download instantly and tailor it with your information.
-
 Incident Response Strategies For Hacking Risks In Finance Sector
Incident Response Strategies For Hacking Risks In Finance SectorThis template covers challenges and solutions to ensure efficient ethical hacking. The purpose of this slide is to help businesses in implementing proactive security measures by overcoming ethical hacking issues. It covers ethical hacking challenges, description and their solutions.Presenting our set of slides with Incident Response Strategies For Hacking Risks In Finance Sector This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Threat Intelligence, External Asset Protection, Brand Abuse Scanning.
-
 List Of Devices Vulnerable To Hacking Risks
List Of Devices Vulnerable To Hacking RisksThis slide covers devices that are most vulnerable to hacking. The purpose of this slide is to help businesses in limiting chances of device hacking by providing understanding of factors causing vulnerabilities. It covers four major devices such as smart devices, webcams, email and routers.Introducing our premium set of slides with List Of Devices Vulnerable To Hacking Risks Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Inconsistent Software, Attachments Through, Access Computer. So download instantly and tailor it with your information.
-
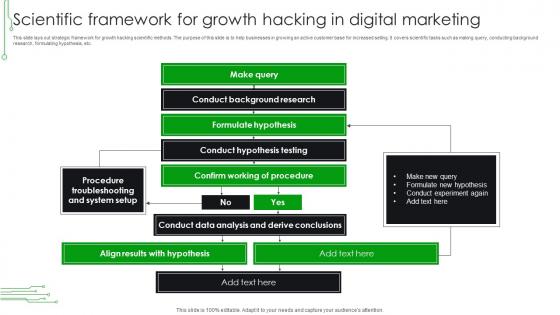 Scientific Framework For Growth Hacking In Digital Marketing
Scientific Framework For Growth Hacking In Digital MarketingThis slide lays out strategic framework for growth hacking scientific methods. The purpose of this slide is to help businesses in growing an active customer base for increased selling. It covers scientific tasks such as making query, conducting background research, formulating hypothesis, etc. Presenting our well structured Scientific Framework For Growth Hacking In Digital Marketing The topics discussed in this slide are Conduct Experiment, Formulate Hypothesis, Hypothesis Testing This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
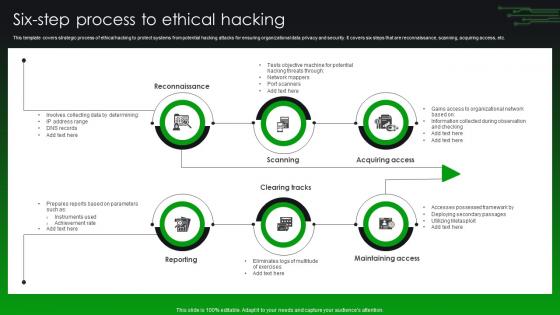 Six Step Process To Ethical Hacking
Six Step Process To Ethical HackingThis template covers strategic process of ethical hacking to protect systems from potential hacking attacks for ensuring organizational data privacy and security. It covers six steps that are reconnaissance, scanning, acquiring access, etc.Introducing our premium set of slides with Six Step Process To Ethical Hacking Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Maintaining Access, Acquiring Access, Reconnaissance. So download instantly and tailor it with your information.
-
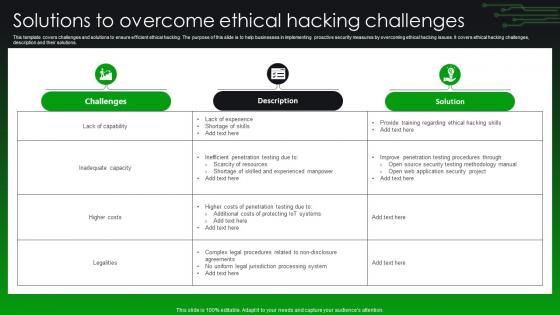 Solutions To Overcome Ethical Hacking Challenges
Solutions To Overcome Ethical Hacking ChallengesThis template covers challenges and solutions to ensure efficient ethical hacking. The purpose of this slide is to help businesses in implementing proactive security measures by overcoming ethical hacking issues. It covers ethical hacking challenges, description and their solutions.Introducing our Solutions To Overcome Ethical Hacking Challenges set of slides. The topics discussed in these slides are Inadequate Capacity, Inefficient Penetration, Penetration Testing This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
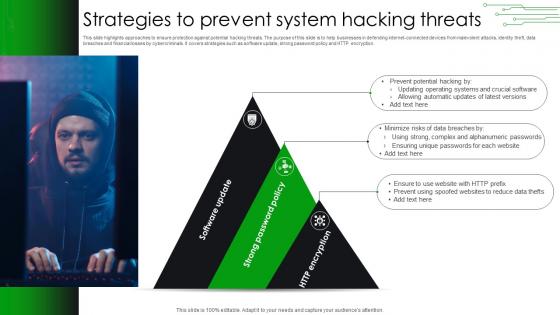 Strategies To Prevent System Hacking Threats
Strategies To Prevent System Hacking ThreatsThis slide highlights approaches to ensure protection against potential hacking threats. The purpose of this slide is to help businesses in defending internet connected devices from malevolent attacks, identity theft, data breaches and financial losses by cybercriminals. It covers strategies such as software update, strong password policy and HTTP encryption. Presenting our well structured Strategies To Prevent System Hacking Threats The topics discussed in this slide are Alphanumeric Passwords, Ensuring Unique Passwords, Updating Operating. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Techniques To Protect E Commerce Sites From Hacking
Techniques To Protect E Commerce Sites From HackingThis template presents various strategies to improve security of e commerce website. The purpose of this slide is to help online retail businesses in ensuring website security and strengthening data privacy by minimizing hacking threats. It covers techniques such as SSL monitoring, ensuring firewall safety, removing third party access, etc.Presenting our set of slides with Techniques To Protect E Commerce Sites From Hacking This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Conducting Regular, Performing Network, Ensure Chosen.
-
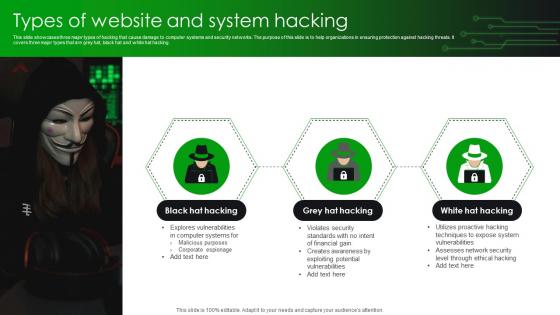 Types Of Website And System Hacking
Types Of Website And System HackingThis slide showcases three major types of hacking that cause damage to computer systems and security networks. The purpose of this slide is to help organizations in ensuring protection against hacking threats. It covers three major types that are grey hat, black hat and white hat hacking.Introducing our premium set of slides with Types Of Website And System Hacking Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Assesses Network, System Vulnerabilities, Techniques Expose So download instantly and tailor it with your information.
-
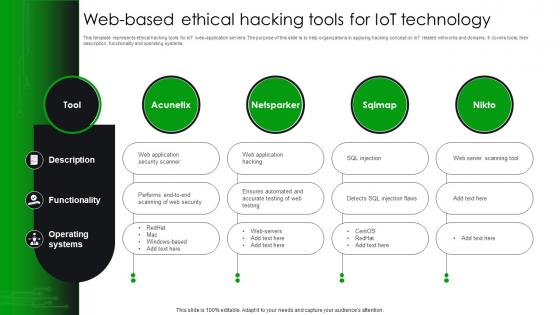 Web Based Ethical Hacking Tools For Iot Technology
Web Based Ethical Hacking Tools For Iot TechnologyThis template represents ethical hacking tools for IoT web application servers. The purpose of this slide is to help organizations in applying hacking concept on IoT related networks and domains. It covers tools, their description, functionality and operating systems.Presenting our set of slides with Web Based Ethical Hacking Tools For Iot Technology This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Ensures Automated, Injection Flaws, Server Scanning Tool.
-
 Cyber Security Hack In Powerpoint And Google Slides Cpb
Cyber Security Hack In Powerpoint And Google Slides CpbPresenting Cyber Security Hack In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cyber Security Hack This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Mobile Performance Meter Hack In Powerpoint And Google Slides Cpb
Mobile Performance Meter Hack In Powerpoint And Google Slides CpbPresenting Mobile Performance Meter Hack In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Mobile Performance Meter Hack. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Crypto Wallet Hack In Powerpoint And Google Slides Cpb
Crypto Wallet Hack In Powerpoint And Google Slides CpbPresenting our Crypto Wallet Hack In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Crypto Wallet Hack. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Wealth Building Hacks Leverage In Powerpoint And Google Slides Cpb
Wealth Building Hacks Leverage In Powerpoint And Google Slides CpbPresenting Wealth Building Hacks Leverage In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase six stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Wealth Building Hacks Leverage. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Ethereum Hacked In Powerpoint And Google Slides Cpb
Ethereum Hacked In Powerpoint And Google Slides CpbPresenting Ethereum Hacked In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Ethereum Hacked. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Banks Responsible Hacked Accounts In Powerpoint And Google Slides Cpb
Banks Responsible Hacked Accounts In Powerpoint And Google Slides CpbPresenting our Banks Responsible Hacked Accounts In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Banks Responsible Hacked Accounts This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Parity Wallet Hack In Powerpoint And Google Slides Cpb
Parity Wallet Hack In Powerpoint And Google Slides CpbPresenting our Parity Wallet Hack In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Parity Wallet Hack This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Unlimited Data Hack Smart In Powerpoint And Google Slides Cpb
Unlimited Data Hack Smart In Powerpoint And Google Slides CpbPresenting Unlimited Data Hack Smart In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Unlimited Data Hack Smart This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Western Digital Hack In Powerpoint And Google Slides Cpb
Western Digital Hack In Powerpoint And Google Slides CpbPresenting our Western Digital Hack In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases two stages. It is useful to share insightful information on Western Digital Hack This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Hacking Exposed Model In Powerpoint And Google Slides Cpb
Hacking Exposed Model In Powerpoint And Google Slides CpbPresenting our Hacking Exposed Model In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Hacking Exposed Model This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Adopt Two Factor Authentication To Reduce Hacking Hands On Blockchain Security Risk BCT SS V
Adopt Two Factor Authentication To Reduce Hacking Hands On Blockchain Security Risk BCT SS VThe following slide illustrates some tips and practices to ensure two factor authentication and safeguard blockchain network. It includes elements such as restricting unauthorized access, safeguarding personal keys, sending unique codes, extending user authentication, etc. Increase audience engagement and knowledge by dispensing information using Adopt Two Factor Authentication To Reduce Hacking Hands On Blockchain Security Risk BCT SS V. This template helps you present information on four stages. You can also present information on Restricts Unauthorized Access, Extends User Authentication, Safeguards Personal Key using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Hack Explained In Powerpoint And Google Slides Cpb
Hack Explained In Powerpoint And Google Slides CpbPresenting Hack Explained In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Hack Explained. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Considered Hacking In Powerpoint And Google Slides Cpb
Considered Hacking In Powerpoint And Google Slides CpbPresenting our Considered Hacking In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Considered Hacking This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Recent Hacking Attacks In Powerpoint And Google Slides Cpb
Recent Hacking Attacks In Powerpoint And Google Slides CpbPresenting Recent Hacking Attacks In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase six stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Recent Hacking Attacks. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Hacking Cough Sound Effect In Powerpoint And Google Slides Cpb
Hacking Cough Sound Effect In Powerpoint And Google Slides CpbPresenting our Hacking Cough Sound Effect In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Hacking Cough Sound Effect. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Advertising Account Hacked In Powerpoint And Google Slides Cpb
Advertising Account Hacked In Powerpoint And Google Slides CpbPresenting Advertising Account Hacked In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Advertising Account Hacked. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Adopt Two Factor Authentication To Reduce Hacking Guide For Blockchain BCT SS V
Adopt Two Factor Authentication To Reduce Hacking Guide For Blockchain BCT SS VThe following slide illustrates some tips and practices to ensure two factor authentication and safeguard blaockchain network. It includes elements such as restricting unauthorized access, safeguarding personal keys, sending unique codes, extending user authentication, etc. Introducing Adopt Two Factor Authentication To Reduce Hacking Guide For Blockchain BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Unauthorized Access, User Authentication, Safeguards Personal using this template. Grab it now to reap its full benefits.
-
 Agenda For Ethical Hacking And Network Security Ppt Icon Master Slide
Agenda For Ethical Hacking And Network Security Ppt Icon Master SlideIntroducing Agenda For Ethical Hacking And Network Security Ppt Icon Master Slide to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Ethical Hacking, Network Security, Ethical Hacking Training Program, using this template. Grab it now to reap its full benefits.
-
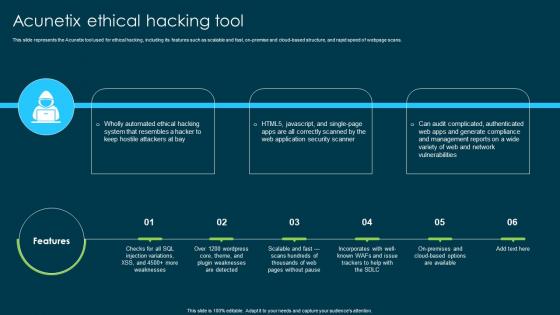 Ethical Hacking And Network Security Acunetix Ethical Hacking Tool
Ethical Hacking And Network Security Acunetix Ethical Hacking ToolThis slide represents the Acunetix tool used for ethical hacking, including its features such as scalable and fast, on-premise and cloud-based structure, and rapid speed of webpage scans. Increase audience engagement and knowledge by dispensing information using Ethical Hacking And Network Security Acunetix Ethical Hacking Tool. This template helps you present information on three stages. You can also present information on Acunetix Ethical Hacking Tool, Cloud Based Structure, Web Application Security Scanner using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
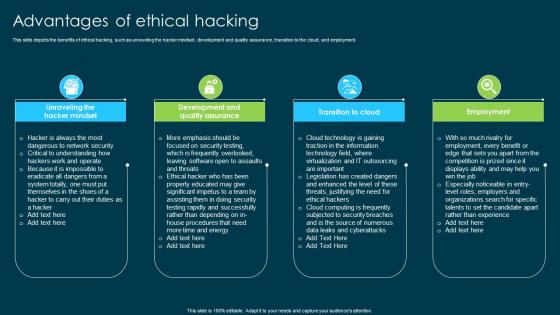 Ethical Hacking And Network Security Advantages Of Ethical Hacking
Ethical Hacking And Network Security Advantages Of Ethical HackingThis slide depicts the benefits of ethical hacking, such as unraveling the hacker mindset, development and quality assurance, transition to the cloud, and employment. Introducing Ethical Hacking And Network Security Advantages Of Ethical Hacking to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Unraveling The Hacker Mindset, Development And Quality Assurance, Transition To Cloud, Employment, using this template. Grab it now to reap its full benefits.
-
 Ethical Hacking And Network Security Benefits Of Ethical Hacking To Companies
Ethical Hacking And Network Security Benefits Of Ethical Hacking To CompaniesThis slide represents the benefits of ethical hacking to the companies, including testing security, identifying weaknesses, understanding hacker methods, and being ready for a hacker attack. Increase audience engagement and knowledge by dispensing information using Ethical Hacking And Network Security Benefits Of Ethical Hacking To Companies. This template helps you present information on four stages. You can also present information on Security Measures Testing, Identifying Weaknesses, Ethical Hacking, Understanding Hacker Methods using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ethical Hacking And Network Security Black Hat Hackers Crackers
Ethical Hacking And Network Security Black Hat Hackers CrackersThis slide describes the black hat hackers and how they can take advantage of a vulnerability in a software, network, and computer system. Introducing Ethical Hacking And Network Security Black Hat Hackers Crackers to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Weakness For Illegal Purposes, Black Hat Hackers, Computer System, Network, using this template. Grab it now to reap its full benefits.
-
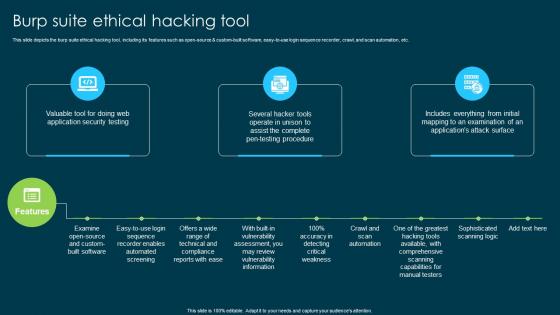 Ethical Hacking And Network Security Burp Suite Ethical Hacking Tool
Ethical Hacking And Network Security Burp Suite Ethical Hacking ToolThis slide depicts the burp suite ethical hacking tool, including its features such as open-source and custom-built software, easy-to-use login sequence recorder, crawl, and scan automation, etc. Increase audience engagement and knowledge by dispensing information using Ethical Hacking And Network Security Burp Suite Ethical Hacking Tool. This template helps you present information on three stages. You can also present information on Sophisticated Scanning Logic, Crawl And Scan Automation, Custom Built Software, Comprehensive Scanning Capabilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ethical Hacking And Network Security Common Types Of Cyber Crime
Ethical Hacking And Network Security Common Types Of Cyber CrimeThis slide describes the common types of cybercrime such as identity theft, computer fraud, privacy breach, electronic money laundering, electronic funds transfer, and so on. Introducing Ethical Hacking And Network Security Common Types Of Cyber Crime to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Electronic Money Laundering, Electronic Funds Transfer, Denial Of Service Attacks, Sharing Copyrighted Files Or Data, using this template. Grab it now to reap its full benefits.
-
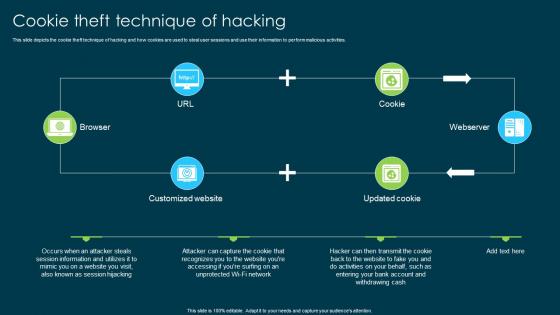 Ethical Hacking And Network Security Cookie Theft Technique Of Hacking
Ethical Hacking And Network Security Cookie Theft Technique Of HackingThis slide depicts the cookie theft technique of hacking and how cookies are used to steal user sessions and use their information to perform malicious activities. Increase audience engagement and knowledge by dispensing information using Ethical Hacking And Network Security Cookie Theft Technique Of Hacking. This template helps you present information on four stages. You can also present information on Technique Of Hacking, Perform Malicious Activities, Customized Website, Session Hijacking using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
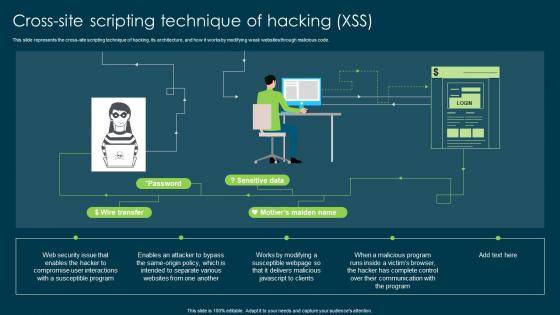 Ethical Hacking And Network Security Crosssite Scripting Technique Of Hacking Xss
Ethical Hacking And Network Security Crosssite Scripting Technique Of Hacking XssThis slide represents the cross-site scripting technique of hacking, its architecture, and how it works by modifying weak websites through malicious code. Deliver an outstanding presentation on the topic using this Ethical Hacking And Network Security Crosssite Scripting Technique Of Hacking Xss. Dispense information and present a thorough explanation of Cross Site Scripting, Technique Of Hacking, Modifying Weak Websites, Susceptible Program using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
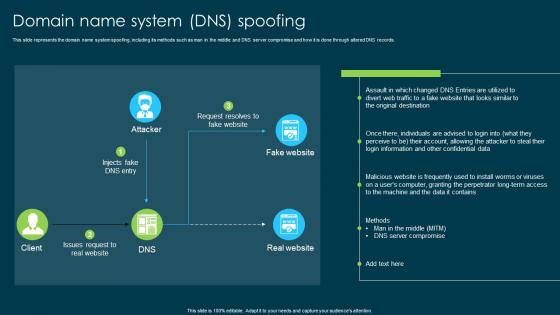 Ethical Hacking And Network Security Domain Name System Dns Spoofing
Ethical Hacking And Network Security Domain Name System Dns SpoofingThis slide represents the domain name system spoofing, including its methods such as man in the middle and DNS server compromise and how it is done through altered DNS records. Deliver an outstanding presentation on the topic using this Ethical Hacking And Network Security Domain Name System Dns Spoofing. Dispense information and present a thorough explanation of Domain Name System Spoofing, Server Compromise, Confidential Data, Technique For Gathering Data using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
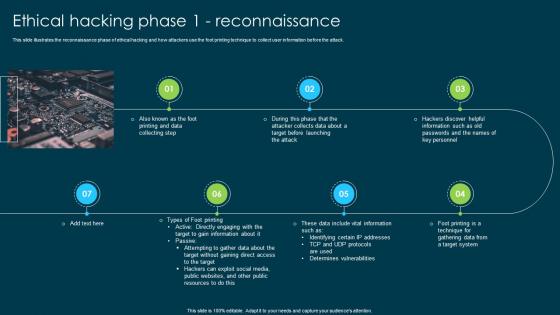 Ethical Hacking And Network Security Ethical Hacking Phase 1 Reconnaissance
Ethical Hacking And Network Security Ethical Hacking Phase 1 ReconnaissanceThis slide illustrates the reconnaissance phase of ethical hacking and how attackers use the foot printing technique to collect user information before the attack. Introducing Ethical Hacking And Network Security Ethical Hacking Phase 1 Reconnaissance to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Target To Gain Information, Hackers Can Exploit Social Media, Public Websites, Public Resources, using this template. Grab it now to reap its full benefits.
-
 Ethical Hacking And Network Security Ethical Hacking Phase 2 Scanning
Ethical Hacking And Network Security Ethical Hacking Phase 2 ScanningThis slide describes the scanning phase of ethical hacking, and the four types of scans are running in this phase such as pre-attack, port scanning, vulnerability scanning, and data extraction. Increase audience engagement and knowledge by dispensing information using Ethical Hacking And Network Security Ethical Hacking Phase 2 Scanning. This template helps you present information on five stages. You can also present information on Scanning Phase Of Ethical Hacking, Port Scanning, Vulnerability Scanning, Data Extraction using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
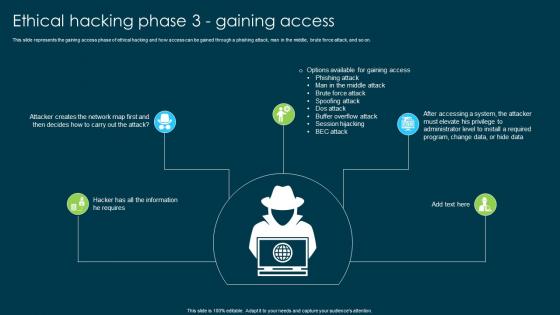 Ethical Hacking And Network Security Ethical Hacking Phase 3 Gaining Access
Ethical Hacking And Network Security Ethical Hacking Phase 3 Gaining AccessThis slide represents the gaining access phase of ethical hacking and how access can be gained through a phishing attack, man in the middle, brute force attack, and so on. Introducing Ethical Hacking And Network Security Ethical Hacking Phase 3 Gaining Access to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Phishing Attack, Brute Force Attack, Spoofing Attack, Dos Attack, Buffer Overflow Attack, using this template. Grab it now to reap its full benefits.
-
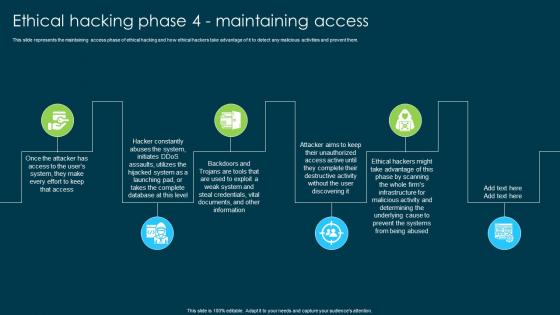 Ethical Hacking And Network Security Ethical Hacking Phase 4 Maintaining Access
Ethical Hacking And Network Security Ethical Hacking Phase 4 Maintaining AccessThis slide represents the maintaining access phase of ethical hacking and how ethical hackers take advantage of it to detect any malicious activities and prevent them. Increase audience engagement and knowledge by dispensing information using Ethical Hacking And Network Security Ethical Hacking Phase 4 Maintaining Access. This template helps you present information on six stages. You can also present information on Whole Firms Infrastructure, Malicious Activity, Prevent The Systems, Ethical Hacking using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Ethical Hacking And Network Security Ethical Hacking Phase 5 Clearing Tracks
Ethical Hacking And Network Security Ethical Hacking Phase 5 Clearing TracksThis slide depicts the clearing tracks phase of ethical hacking and how experienced hackers remove their traces from the system so that no one can follow them. Introducing Ethical Hacking And Network Security Ethical Hacking Phase 5 Clearing Tracks to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Delete The Cache And Cookies, Changing Registry Values, Getting Rid Of Sent Emails, using this template. Grab it now to reap its full benefits.



