Powerpoint Templates and Google slides for Implementation Of Cyber Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Benefits Of Implementing Web Application Firewall Implementing Cyber Security Ppt Structure
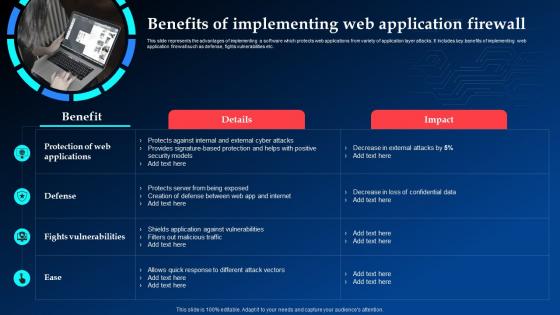
Benefits Of Implementing Web Application Firewall Implementing Cyber Security Ppt StructureThis slide represents the advantages of implementing a software which protects web applications from variety of application layer attacks. It includes key benefits of implementing web application firewall such as defense, fights vulnerabilities etc. Increase audience engagement and knowledge by dispensing information using Benefits Of Implementing Web Application Firewall Implementing Cyber Security Ppt Structure. This template helps you present information on one stage. You can also present information on Fights Vulnerabilities, Implementing, Application Firewall using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Common Sources Of Precursors And Indicators Implementing Cyber Security Ppt Inspiration
Common Sources Of Precursors And Indicators Implementing Cyber Security Ppt InspirationThis slide represents the common sources of signs which indicates that an incident may occur in the future. It includes details related to common sources of precursors and indicators such as IDPSs, SIEMs, network device logs etc. Deliver an outstanding presentation on the topic using this Common Sources Of Precursors And Indicators Implementing Cyber Security Ppt Inspiration. Dispense information and present a thorough explanation of Common Sources, Precursors And Indicators, Analytics using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Comparative Analysis Of Web Application Firewall Products Implementing Cyber Security Ppt Themes
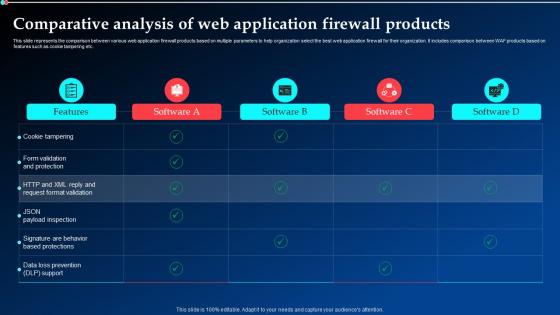
Comparative Analysis Of Web Application Firewall Products Implementing Cyber Security Ppt ThemesThis slide represents the comparison between various web application firewall products based on multiple parameters to help organization select the best web application firewall for their organization. It includes comparison between WAF products based on features such as cookie tampering etc. Present the topic in a bit more detail with this Comparative Analysis Of Web Application Firewall Products Implementing Cyber Security Ppt Themes. Use it as a tool for discussion and navigation on Cookie Tampering, Comparative Analysis, Firewall Products. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 G1 Table Of Contents For Implementing Cyber Security Incident Management Ppt Ideas
G1 Table Of Contents For Implementing Cyber Security Incident Management Ppt IdeasIncrease audience engagement and knowledge by dispensing information using G1 Table Of Contents For Implementing Cyber Security Incident Management Ppt Ideas. This template helps you present information on one stage. You can also present information on Implementing Cyber Security, Incident Management, Organization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
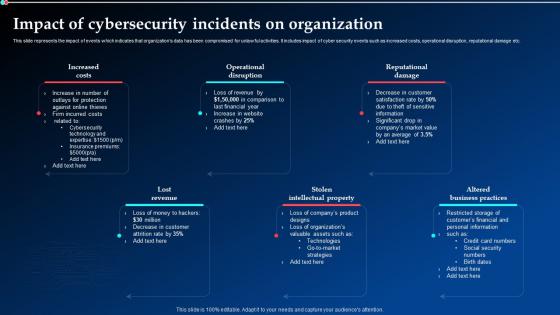 Impact Of Cybersecurity Incidents On Organization Implementing Cyber Security Ppt Topics
Impact Of Cybersecurity Incidents On Organization Implementing Cyber Security Ppt TopicsThis slide represents the impact of events which indicates that organizations data has been compromised for unlawful activities. It includes impact of cyber security events such as increased costs, operational disruption, reputational damage etc. Present the topic in a bit more detail with this Impact Of Cybersecurity Incidents On Organization Implementing Cyber Security Ppt Topics. Use it as a tool for discussion and navigation on Operational Disruption, Reputational Damage, Stolen Intellectual Property. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
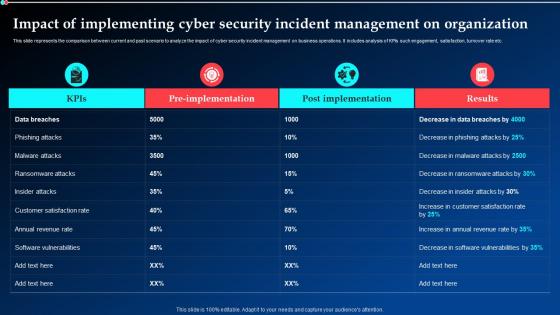 Impact Of Implementing Cyber Security Incident Management On Organization Ppt Slides
Impact Of Implementing Cyber Security Incident Management On Organization Ppt SlidesThis slide represents the comparison between current and past scenario to analyze the impact of cyber security incident management on business operations. It includes analysis of KPIs such engagement, satisfaction, turnover rate etc. Deliver an outstanding presentation on the topic using this Impact Of Implementing Cyber Security Incident Management On Organization Ppt Slides. Dispense information and present a thorough explanation of Implementing Cyber Security, Incident Management, Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
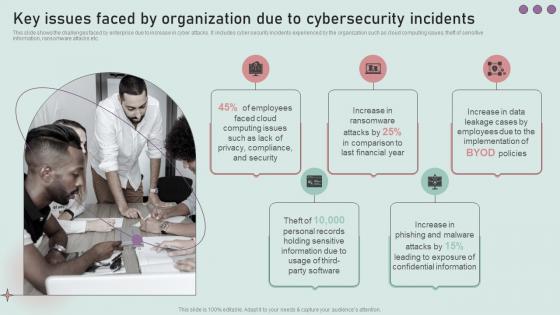 Development And Implementation Of Security Key Issues Faced By Organization Due To Cybersecurity Incidents
Development And Implementation Of Security Key Issues Faced By Organization Due To Cybersecurity IncidentsThis slide shows the challenges faced by enterprise due to increase in cyber attacks. It includes cyber security incidents experienced by the organization such as cloud computing issues, theft of sensitive information, ransomware attacks etc. Introducing Development And Implementation Of Security Key Issues Faced By Organization Due To Cybersecurity Incidents to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Employees, Privacy, Compliance, Security, using this template. Grab it now to reap its full benefits.
-
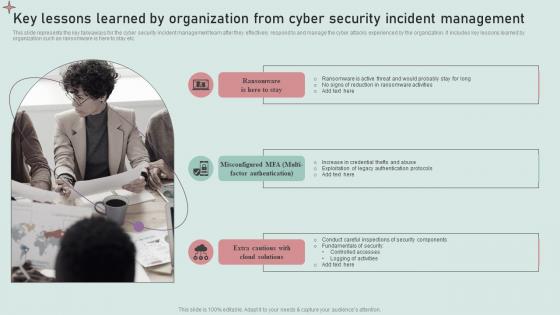 Development And Implementation Of Security Key Lessons Learned By Organization From Cyber Security Incident
Development And Implementation Of Security Key Lessons Learned By Organization From Cyber Security IncidentThis slide represents the key takeaways for the cyber security incident management team after they effectively respond to and manage the cyber attacks experienced by the organization. It includes key lessons learned by organization such as ransomware is here to stay etc. Increase audience engagement and knowledge by dispensing information using Development And Implementation Of Security Key Lessons Learned By Organization From Cyber Security Incident. This template helps you present information on three stages. You can also present information on Active, Probably Stay, No Signs Reduction Ransomware Activities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
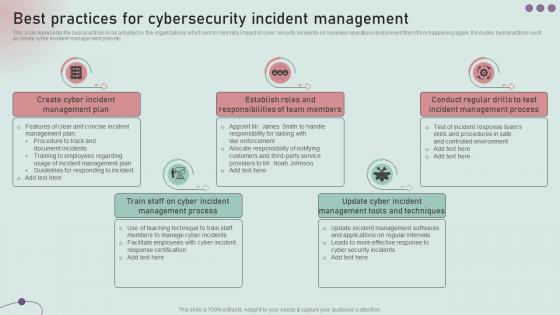 Best Practices For Cybersecurity Incident Management Development And Implementation Of Security
Best Practices For Cybersecurity Incident Management Development And Implementation Of SecurityThis slide represents the best practices to be adopted by the organizations which aim to minimize impact of cyber security incidents on business operations and prevent them from happening again. It includes best practices such as create cyber incident management plan etc. Increase audience engagement and knowledge by dispensing information using Best Practices For Cybersecurity Incident Management Development And Implementation Of Security. This template helps you present information on five stages. You can also present information on Create Cyber Incident, Management Plan, Establish Roles, Responsibilities Of Team Members using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
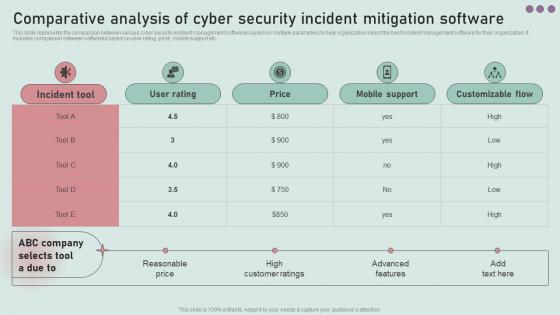 Comparative Analysis Of Cyber Security Incident Mitigation Development And Implementation Of Security
Comparative Analysis Of Cyber Security Incident Mitigation Development And Implementation Of SecurityThis slide represents the comparison between various cyber security incident management softwares based on multiple parameters to help organization select the best incident management software for their organization. It includes comparison between softwares based on user rating, price, mobile support etc. Deliver an outstanding presentation on the topic using this Comparative Analysis Of Cyber Security Incident Mitigation Development And Implementation Of Security. Dispense information and present a thorough explanation of Incident Tool, User Rating, Price using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
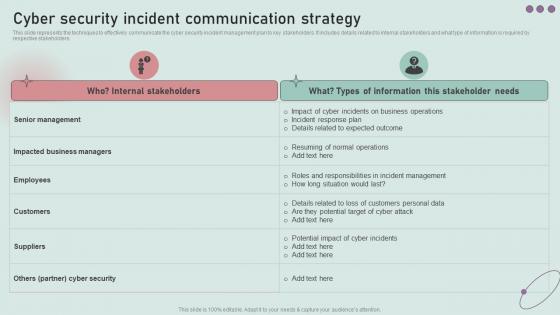 Cyber Security Incident Communication Strategy Development And Implementation Of Security
Cyber Security Incident Communication Strategy Development And Implementation Of SecurityThis slide represents the techniques to effectively communicate the cyber security incident management plan to key stakeholders. It includes details related to internal stakeholders and what type of information is required by respective stakeholders. Deliver an outstanding presentation on the topic using this Cyber Security Incident Communication Strategy Development And Implementation Of Security. Dispense information and present a thorough explanation of Senior Management, Impacted Business Managers, Employees using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
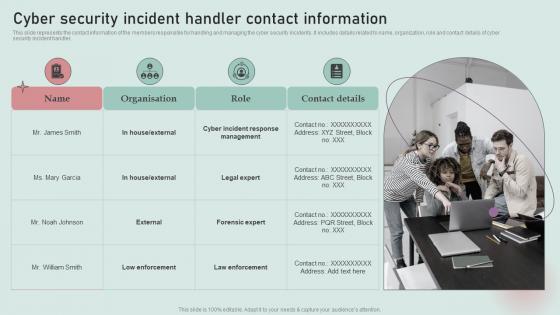 Cyber Security Incident Handler Contact Information Development And Implementation Of Security
Cyber Security Incident Handler Contact Information Development And Implementation Of SecurityThis slide represents the contact information of the members responsible for handling and managing the cyber security incidents. It includes details related to name, organization, role and contact details of cyber security incident handler. Introducing Cyber Security Incident Handler Contact Information Development And Implementation Of Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Cyber Incident, Response Management, using this template. Grab it now to reap its full benefits.
-
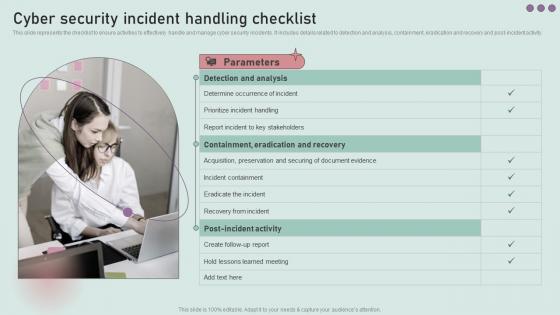 Cyber Security Incident Handling Checklist Development And Implementation Of Security
Cyber Security Incident Handling Checklist Development And Implementation Of SecurityThis slide represents the checklist to ensure activities to effectively handle and manage cyber security incidents. It includes details related to detection and analysis, containment, eradication and recovery and post incident activity. Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Handling Checklist Development And Implementation Of Security. This template helps you present information on three stages. You can also present information on Detection And Analysis, Prioritize Incident Handling, Incident Containment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
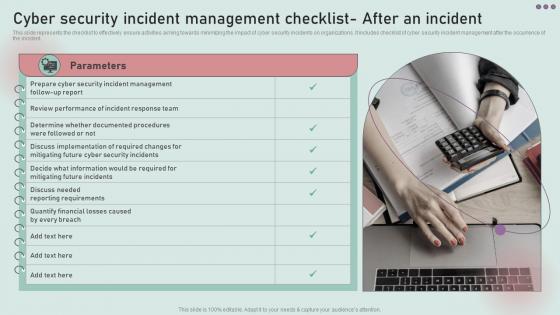 Cyber Security Incident Management Checklist After Development And Implementation Of Security
Cyber Security Incident Management Checklist After Development And Implementation Of SecurityThis slide represents the checklist to effectively ensure activities aiming towards minimizing the impact of cyber security incidents on organizations. It includes checklist of cyber security incident management after the occurrence of the incident. Introducing Cyber Security Incident Management Checklist After Development And Implementation Of Security to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Review Performance, Incident Response Team, using this template. Grab it now to reap its full benefits.
-
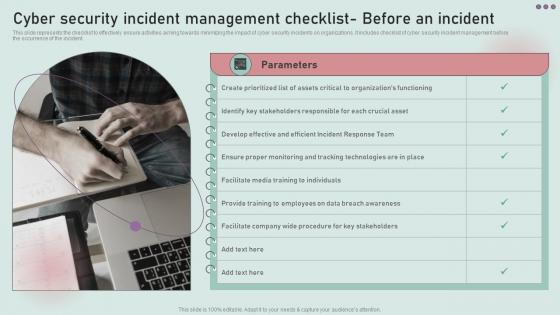 Cyber Security Incident Management Checklist Before Development And Implementation Of Security
Cyber Security Incident Management Checklist Before Development And Implementation Of SecurityThis slide represents the checklist to effectively ensure activities aiming towards minimizing the impact of cyber security incidents on organizations. It includes checklist of cyber security incident management before the occurrence of the incident. Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Management Checklist Before Development And Implementation Of Security. This template helps you present information on one stages. You can also present information on Develop Effective And Efficient, Incident Response Team using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
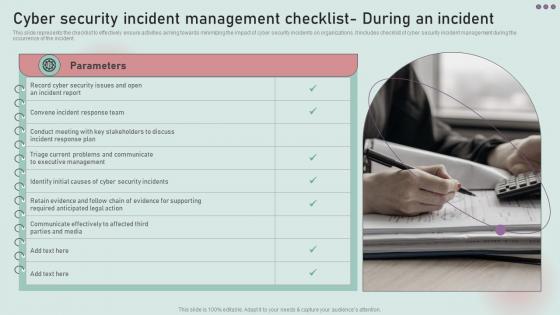 Cyber Security Incident Management Checklist During Development And Implementation Of Security
Cyber Security Incident Management Checklist During Development And Implementation Of SecurityThis slide represents the checklist to effectively ensure activities aiming towards minimizing the impact of cyber security incidents on organizations. It includes checklist of cyber security incident management during the occurrence of the incident. Introducing Cyber Security Incident Management Checklist During Development And Implementation Of Security to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Triage Current Problems, Communicate, Executive Management, using this template. Grab it now to reap its full benefits.
-
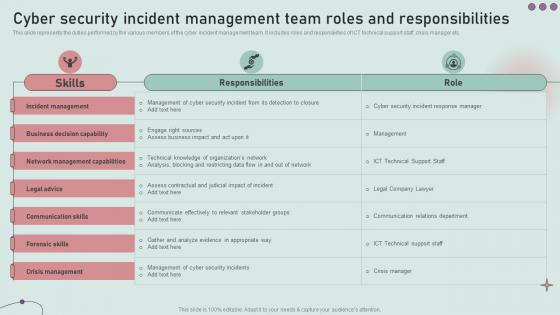 Cyber Security Incident Management Team Roles Development And Implementation Of Security
Cyber Security Incident Management Team Roles Development And Implementation Of SecurityThis slide represents the duties performed by the various members of the cyber incident management team. It includes roles and responsivities of ICT technical support staff, crisis manager etc. Present the topic in a bit more detail with this Cyber Security Incident Management Team Roles Development And Implementation Of Security. Use it as a tool for discussion and navigation on Incident Management, Business Decision Capability, Network Management Capabilities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Incident Management Team Structure Development And Implementation Of Security
Cyber Security Incident Management Team Structure Development And Implementation Of SecurityThis slide represents the org chart of team which is responsible for minimizing and managing cyber security incidents. It includes details related to team structure of cyber security incident management team Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Management Team Structure Development And Implementation Of Security. This template helps you present information on one stages. You can also present information on Human Resources, Outside Counsel, Forensics using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Incident Response Lifecycle Development And Implementation Of Security Incident Management
Cyber Security Incident Response Lifecycle Development And Implementation Of Security Incident ManagementThis slide represents the lifecycle of incident response which enables organizations to quickly detect and halt attacks, minimize damage and prevent future attacks of same type. It includes four phases of cyber security incident response such as preparation, detection and analysis etc. Introducing Cyber Security Incident Response Lifecycle Development And Implementation Of Security Incident Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Preparation, Detection Analysis, Containment Eradication Recovery, using this template. Grab it now to reap its full benefits.
-
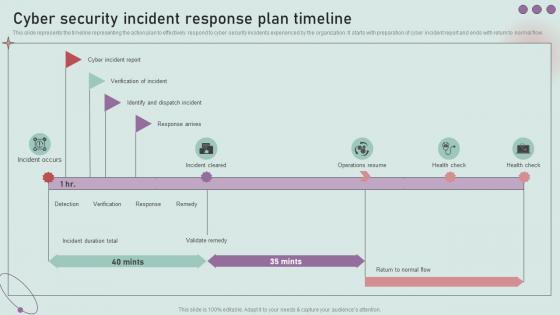 Cyber Security Incident Response Plan Timeline Development And Implementation Of Security Incident
Cyber Security Incident Response Plan Timeline Development And Implementation Of Security IncidentThis slide represents the timeline representing the action plan to effectively respond to cyber security incidents experienced by the organization. It starts with preparation of cyber incident report and ends with return to normal flow. Present the topic in a bit more detail with this Cyber Security Incident Response Plan Timeline Development And Implementation Of Security Incident. Use it as a tool for discussion and navigation on Verification Of Incident, Cyber Incident Report, Response Arrives. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Incidents Follow Up Report Development And Implementation Of Security Incident Management
Cyber Security Incidents Follow Up Report Development And Implementation Of Security Incident ManagementThis slide represents the follow up report prepared by cyber security incident management team after successfully responding to cyber incidents experienced by the organization. It includes details related to date of incident, actions taken by responsible officer. Present the topic in a bit more detail with this Cyber Security Incidents Follow Up Report Development And Implementation Of Security Incident Management. Use it as a tool for discussion and navigation on Confidential Information Customers, Theft Confidential Information, Organizational Projects. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
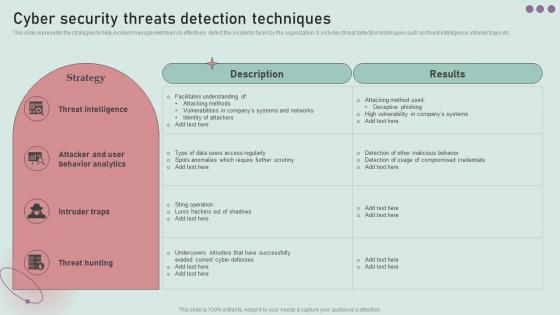 Cyber Security Threats Detection Techniques Development And Implementation Of Security Incident Management
Cyber Security Threats Detection Techniques Development And Implementation Of Security Incident ManagementThis slide represents the strategies to help incident management team to effectively detect the incidents faced by the organization. It includes threat detection techniques such as threat intelligence, intruder traps etc. Present the topic in a bit more detail with this Cyber Security Threats Detection Techniques Development And Implementation Of Security Incident Management. Use it as a tool for discussion and navigation on Intruder Traps, Attacker And User Behavior Analytics, Threat Intelligence. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
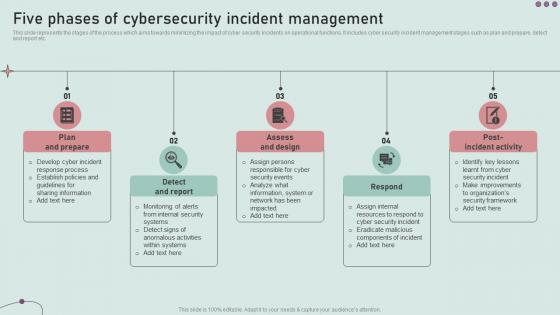 Five Phases Of Cybersecurity Incident Management Development And Implementation Of Security Incident
Five Phases Of Cybersecurity Incident Management Development And Implementation Of Security IncidentThis slide represents the stages of the process which aims towards minimizing the impact of cyber security incidents on operational functions. It includes cyber security incident management stages such as plan and prepare, detect and report etc. Introducing Five Phases Of Cybersecurity Incident Management Development And Implementation Of Security Incident to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Assess And Design, Detect And Report, Plan And Prepare, using this template. Grab it now to reap its full benefits.
-
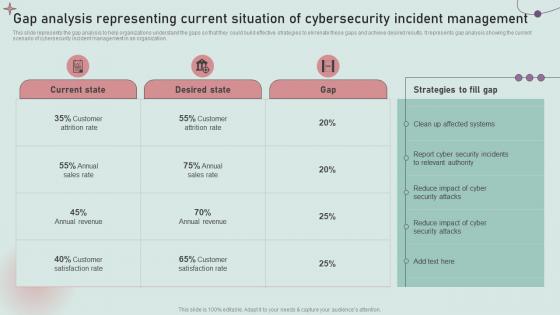 Gap Analysis Representing Current Situation Of Cybersecurity Development And Implementation Of Security
Gap Analysis Representing Current Situation Of Cybersecurity Development And Implementation Of SecurityThis slide represents the gap analysis to help organizations understand the gaps so that they could build effective strategies to eliminate these gaps and achieve desired results. It represents gap analysis showing the current scenario of cybersecurity incident management in an organization. Deliver an outstanding presentation on the topic using this Gap Analysis Representing Current Situation Of Cybersecurity Development And Implementation Of Security. Dispense information and present a thorough explanation of Report Cyber Security Incidents, Relevant Authority using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
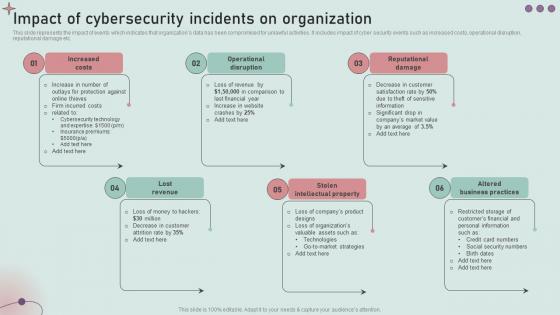 Impact Of Cybersecurity Incidents On Organization Development And Implementation Of Security Incident
Impact Of Cybersecurity Incidents On Organization Development And Implementation Of Security IncidentThis slide represents the impact of events which indicates that organizations data has been compromised for unlawful activities. It includes impact of cyber security events such as increased costs, operational disruption, reputational damage etc. Increase audience engagement and knowledge by dispensing information using Impact Of Cybersecurity Incidents On Organization Development And Implementation Of Security Incident. This template helps you present information on five stages. You can also present information on Increased Costs, Operational Disruption, Reputational Damage using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
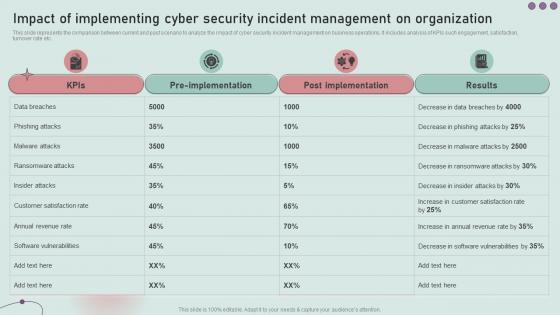 Impact Of Implementing Cyber Security Incident Management Development And Implementation Of Security
Impact Of Implementing Cyber Security Incident Management Development And Implementation Of SecurityThis slide represents the comparison between current and past scenario to analyze the impact of cyber security incident management on business operations. It includes analysis of KPIs such engagement, satisfaction, turnover rate etc. Present the topic in a bit more detail with this Impact Of Implementing Cyber Security Incident Management Development And Implementation Of Security. Use it as a tool for discussion and navigation on Results, Post Implementation, Pre Implementation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Key Parameters To Select Cyber Security Containment Strategy Development And Implementation Of Security
Key Parameters To Select Cyber Security Containment Strategy Development And Implementation Of SecurityThis slide represents the various parameters to look for before choosing an effective and efficient cyber security containment strategy. It includes key parameters such as higher potential damages and theft of organizational resources etc. Introducing Key Parameters To Select Cyber Security Containment Strategy Development And Implementation Of Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Organizational Resources, Potential Damages, Strategy, using this template. Grab it now to reap its full benefits.
-
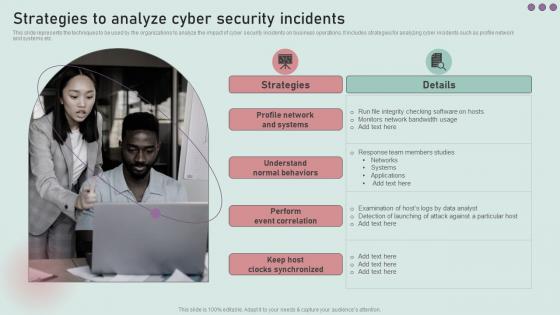 Strategies To Analyze Cyber Security Incidents Development And Implementation Of Security Incident Management
Strategies To Analyze Cyber Security Incidents Development And Implementation Of Security Incident ManagementThis slide represents the techniques to be used by the organizations to analyze the impact of cyber security incidents on business operations. It includes strategies for analyzing cyber incidents such as profile network and systems etc. Increase audience engagement and knowledge by dispensing information using Strategies To Analyze Cyber Security Incidents Development And Implementation Of Security Incident Management. This template helps you present information on two stages. You can also present information on Profile Network And Systems, Understand Normal Behaviors, Perform Event Correlation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
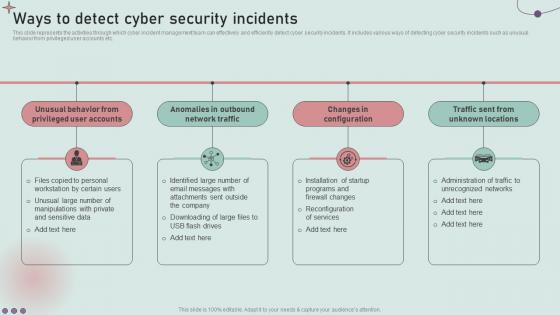 Ways To Detect Cyber Security Incidents Development And Implementation Of Security Incident Management
Ways To Detect Cyber Security Incidents Development And Implementation Of Security Incident ManagementThis slide represents the activities through which cyber incident management team can effectively and efficiently detect cyber security incidents. It includes various ways of detecting cyber security incidents such as unusual behavior from privileged user accounts etc. Introducing Ways To Detect Cyber Security Incidents Development And Implementation Of Security Incident Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Privileged User Accounts, Unusual Behavior, Network Traffic, using this template. Grab it now to reap its full benefits.
-
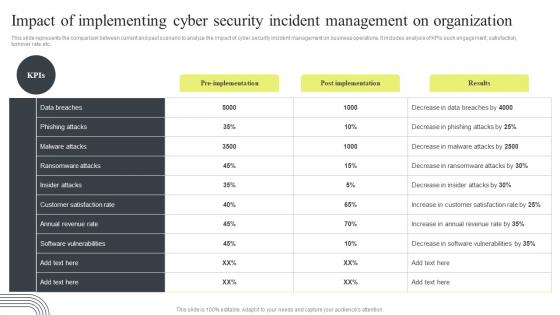 Cyber Security Attacks Response Impact Of Implementing Cyber Security Incident Management
Cyber Security Attacks Response Impact Of Implementing Cyber Security Incident ManagementThis slide represents the comparison between current and past scenario to analyze the impact of cyber security incident management on business operations. It includes analysis of KPIs such engagement, satisfaction, turnover rate etc. Deliver an outstanding presentation on the topic using this Cyber Security Attacks Response Impact Of Implementing Cyber Security Incident Management. Dispense information and present a thorough explanation of Cyber Security Incident, Management On Organization, Software Vulnerabilities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
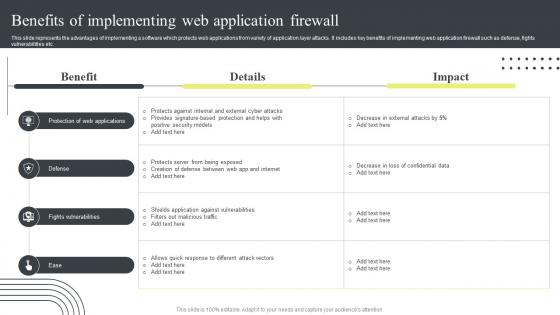 Cyber Security Attacks Response Plan Benefits Of Implementing Web Application Firewall
Cyber Security Attacks Response Plan Benefits Of Implementing Web Application FirewallThis slide represents the advantages of implementing a software which protects web applications from variety of application layer attacks. It includes key benefits of implementing web application firewall such as defense, fights vulnerabilities etc. Present the topic in a bit more detail with this Cyber Security Attacks Response Plan Benefits Of Implementing Web Application Firewall. Use it as a tool for discussion and navigation on Fights Vulnerabilities, Application Firewall, Confidential Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
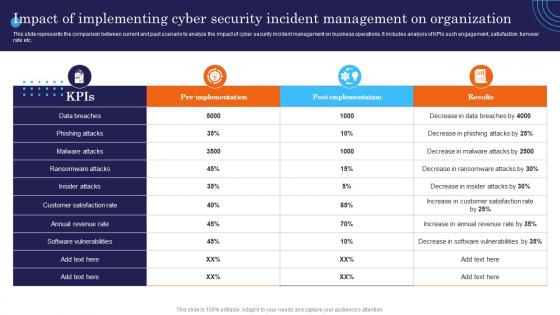 Impact Of Implementing Cyber Security Management Incident Response Strategies Deployment
Impact Of Implementing Cyber Security Management Incident Response Strategies DeploymentThis slide represents the comparison between current and past scenario to analyze the impact of cyber security incident management on business operations. It includes analysis of KPIs such engagement, satisfaction, turnover rate etc. Present the topic in a bit more detail with this Impact Of Implementing Cyber Security Management Incident Response Strategies Deployment. Use it as a tool for discussion and navigation on Implementing, Security, Organization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Impact Of Implementing Cyber Deploying Computer
Impact Of Implementing Cyber Deploying ComputerThis slide represents the comparison between current and past scenario to analyze the impact of cyber security incident management on business operations. It includes analysis of KPIs such engagement, satisfaction, turnover rate etc.Deliver an outstanding presentation on the topic using this Impact Of Implementing Cyber Deploying Computer. Dispense information and present a thorough explanation of Ransomware Attacks, Software Vulnerabilities, Ransomware Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Implementation Of Cyber Security Risk Management Action Plan
Implementation Of Cyber Security Risk Management Action PlanThis slide represents implementation process of cyber security risk management action plan. It further includes steps such as evaluate cyber security risks, prioritize cyber risks Presenting our well structured Implementation Of Cyber Security Risk Management Action Plan. The topics discussed in this slide are Security, Management, Plan. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
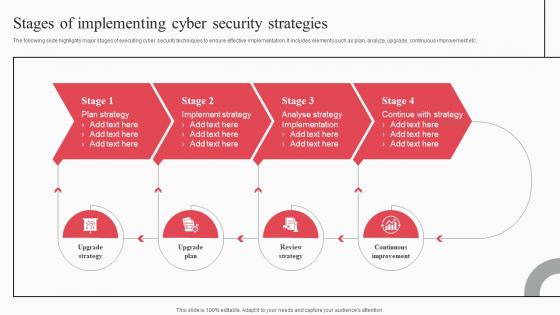 Stages Of Implementing Cyber Security Strategies Cyber Attack Risks Mitigation
Stages Of Implementing Cyber Security Strategies Cyber Attack Risks MitigationThe following slide highlights major stages of executing cyber security techniques to ensure effective implementation. It includes elements such as plan, analyze, upgrade, continuous improvement etc. Increase audience engagement and knowledge by dispensing information using Stages Of Implementing Cyber Security Strategies Cyber Attack Risks Mitigation. This template helps you present information on four stages. You can also present information on Plan Strategy, Implement Strategy, Analyse Strategy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber security it implementation of strong password policy ppt powerpoint ideas example
Cyber security it implementation of strong password policy ppt powerpoint ideas exampleThis slide depicts the importance of having strong passwords for different online accounts. It also shows the number of users who use the same password across other accounts. Increase audience engagement and knowledge by dispensing information using Cyber Security IT Implementation Of Strong Password Policy Ppt Powerpoint Ideas Example. This template helps you present information on four stages. You can also present information on Implementation Of Strong Password Policy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
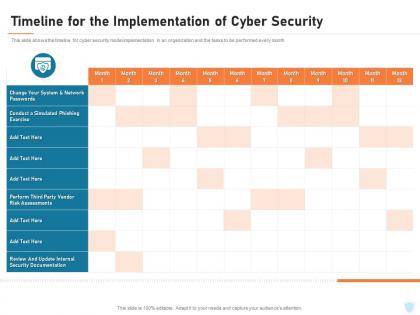 Cyber security it timeline for the implementation of cyber security ppt icon slide portrait
Cyber security it timeline for the implementation of cyber security ppt icon slide portraitThis slide shows the timeline for cyber security model implementation in an organization and the tasks to be performed every month. Present the topic in a bit more detail with this Cyber Security IT Timeline For The Implementation Of Cyber Security Ppt Icon Slide Portrait. Use it as a tool for discussion and navigation on Internal Security Documentation, Network Passwords, Risk Assessments, Perform. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Firewall Implementation For Cyber Security Department Wise Incident Analysis Of Malware Attacks
Firewall Implementation For Cyber Security Department Wise Incident Analysis Of Malware AttacksThis slide represents the number of attacks on each department in an organization. The purpose of this slide is to showcase the department-wise incident analysis of cyber-attacks on different departments such as finance, R and D, sales and marketing HR, IT, and others. Deliver an outstanding presentation on the topic using this Firewall Implementation For Cyber Security Department Wise Incident Analysis Of Malware Attacks. Dispense information and present a thorough explanation of Research And Development, Sales And Marketing, Incident Analysis, Malware Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
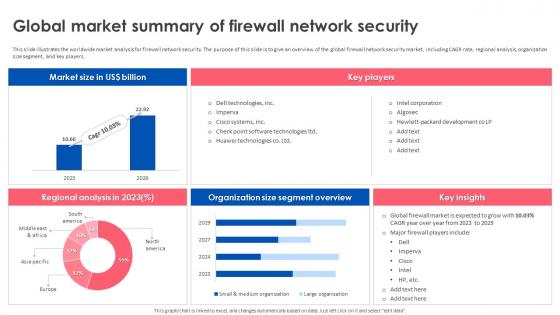 Firewall Implementation For Cyber Security Global Market Summary Of Firewall Network Security
Firewall Implementation For Cyber Security Global Market Summary Of Firewall Network SecurityThis slide illustrates the worldwide market analysis for firewall network security. The purpose of this slide is to give an overview of the global firewall network security market, including CAGR rate, regional analysis, organization size segment, and key players. Deliver an outstanding presentation on the topic using this Firewall Implementation For Cyber Security Global Market Summary Of Firewall Network Security. Dispense information and present a thorough explanation of Worldwide Market Analysis, Firewall Network Security, Global Firewall Network Security Market using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
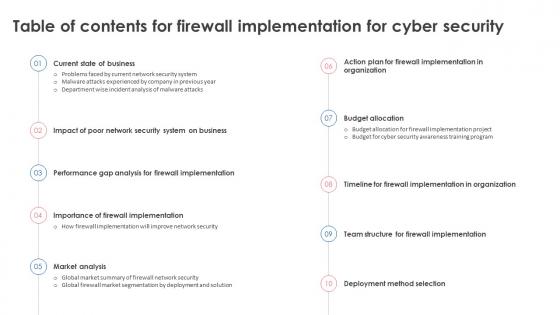 Table Of Contents For Firewall Implementation For Cyber Security Ppt Icon Slide Portrait
Table Of Contents For Firewall Implementation For Cyber Security Ppt Icon Slide PortraitIntroducing Table Of Contents For Firewall Implementation For Cyber Security Ppt Icon Slide Portrait to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Deployment Method Selection, Budget Allocation, Importance Of Firewall Implementation, using this template. Grab it now to reap its full benefits.
-
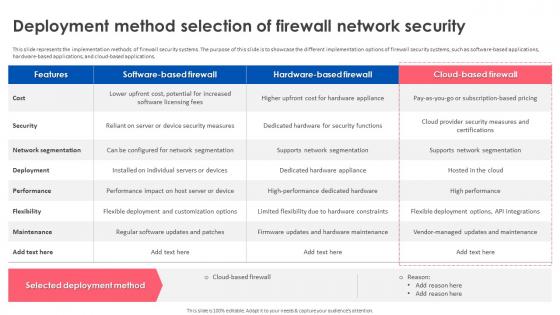 Firewall Implementation For Cyber Security Deployment Method Selection Of Firewall Network Security
Firewall Implementation For Cyber Security Deployment Method Selection Of Firewall Network SecurityThis slide represents the implementation methods of firewall security systems. The purpose of this slide is to showcase the different implementation options of firewall security systems, such as software-based applications, hardware-based applications, and cloud-based applications. Present the topic in a bit more detail with this Firewall Implementation For Cyber Security Deployment Method Selection Of Firewall Network Security. Use it as a tool for discussion and navigation on Network Segmentation, Supports Network Segmentation, Hardware For Security Functions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Firewall Implementation For Cyber Security For Table Of Contents Ppt Ideas Inspiration
Firewall Implementation For Cyber Security For Table Of Contents Ppt Ideas InspirationDeliver an outstanding presentation on the topic using this Firewall Implementation For Cyber Security For Table Of Contents Ppt Ideas Inspiration. Dispense information and present a thorough explanation of Firewall Implementation, Cyber Security, Firewall Network Performance, Tracking Dashboard using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
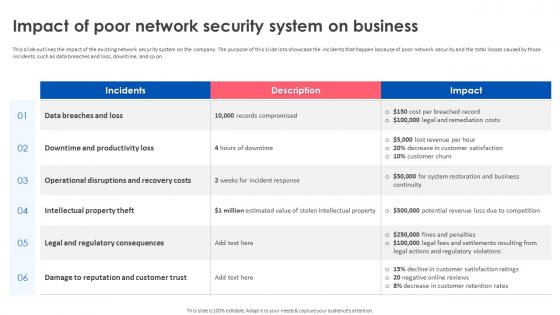 Firewall Implementation For Cyber Security Impact Of Poor Network Security System On Business
Firewall Implementation For Cyber Security Impact Of Poor Network Security System On BusinessThis slide outlines the impact of the existing network security system on the company. The purpose of this slide is to showcase the incidents that happen because of poor network security and the total losses caused by those incidents, such as data breaches and loss, downtime, and so on. Deliver an outstanding presentation on the topic using this Firewall Implementation For Cyber Security Impact Of Poor Network Security System On Business. Dispense information and present a thorough explanation of Downtime And Productivity Loss, Intellectual Property Theft, Legal And Regulatory Consequences using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
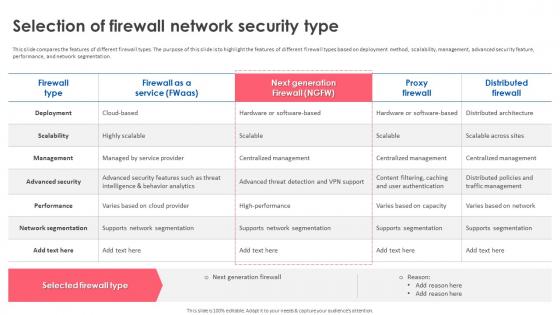 Firewall Implementation For Cyber Security Selection Of Firewall Network Security Type
Firewall Implementation For Cyber Security Selection Of Firewall Network Security TypeThis slide compares the features of different firewall types. The purpose of this slide is to highlight the features of different firewall types based on deployment method, scalability, management, advanced security feature, performance, and network segmentation. Present the topic in a bit more detail with this Firewall Implementation For Cyber Security Selection Of Firewall Network Security Type. Use it as a tool for discussion and navigation on Advanced Security, Network Segmentation, Supports Network Segmentation, Centralized Management. This template is free to edit as deemed fit for your organization. Therefore download it now.


