Powerpoint Templates and Google slides for Malicious
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Illegal Malicious Adware Potentially Unwanted Application Training Ppt
Illegal Malicious Adware Potentially Unwanted Application Training PptPresenting Illegal Malicious Adware Potentially Unwanted Application. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
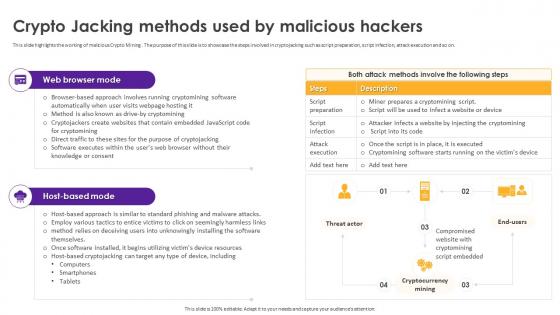 Cryptomining Innovations And Trends Crypto Jacking Methods Used By Malicious Hackers
Cryptomining Innovations And Trends Crypto Jacking Methods Used By Malicious HackersThis slide highlights the working of malicious Crypto Mining . The purpose of this slide is to showcase the steps involved in cryptojacking such as script preparation, script infection, attack execution and so on. Present the topic in a bit more detail with this Cryptomining Innovations And Trends Crypto Jacking Methods Used By Malicious Hackers. Use it as a tool for discussion and navigation on Crypto Jacking Methods, Malicious Hackers, Compromised Website, Cryptomining Script Embedded. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
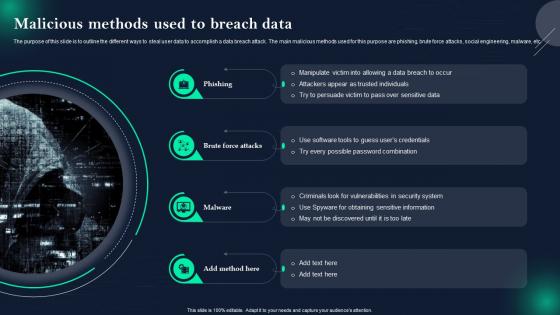 Data Breach Prevention And Mitigation Malicious Methods Used To Breach Data
Data Breach Prevention And Mitigation Malicious Methods Used To Breach DataThe purpose of this slide is to outline the different ways to steal user data to accomplish a data breach attack. The main malicious methods used for this purpose are phishing, brute force attacks, social engineering, malware, etc. Increase audience engagement and knowledge by dispensing information using Data Breach Prevention And Mitigation Malicious Methods Used To Breach Data. This template helps you present information on four stages. You can also present information on Criminals Look For Vulnerabilities, Possible Password Combination, Social Engineering, Malware using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
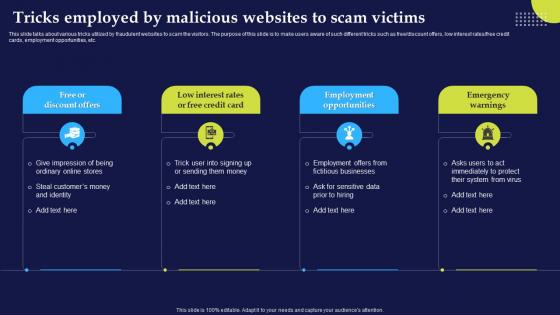 Phishing Attacks And Strategies To Mitigate Them V2 Tricks Employed By Malicious Websites To Scam
Phishing Attacks And Strategies To Mitigate Them V2 Tricks Employed By Malicious Websites To ScamThis slide talks about various tricks utilized by fraudulent websites to scam the visitors. The purpose of this slide is to make users aware of such different tricks such as free or discount offers, low interest rates or free credit cards, employment opportunities, etc. Introducing Phishing Attacks And Strategies To Mitigate Them V2 Tricks Employed By Malicious Websites To Scam to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Employment Opportunities, Emergency Warnings, Malicious Websites, Scam Victims, using this template. Grab it now to reap its full benefits.
-
 IoT Access Points To Malicious Attackers Improving IoT Device Cybersecurity IoT SS
IoT Access Points To Malicious Attackers Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to delineate various Internet of Things IoT access points that can be accessed by hackers. The slide covers information about edge computing, communication network, and cloud computing. Increase audience engagement and knowledge by dispensing information using IoT Access Points To Malicious Attackers Improving IoT Device Cybersecurity IoT SS. This template helps you present information on four stages. You can also present information on Devices, Hardware, Commonly using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
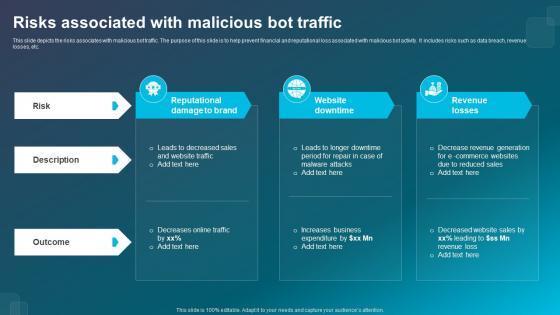 Risks Associated With Malicious Bot Traffic
Risks Associated With Malicious Bot TrafficThis slide depicts the risks associates with malicious bot traffic. The purpose of this slide is to help prevent financial and reputational loss associated with malicious bot activity. It includes risks such as data breach, revenue losses, etc. Presenting our set of slides with Risks Associated With Malicious Bot Traffic. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Reputational Damage To Brand, Website Downtime, Revenue Losses.
-
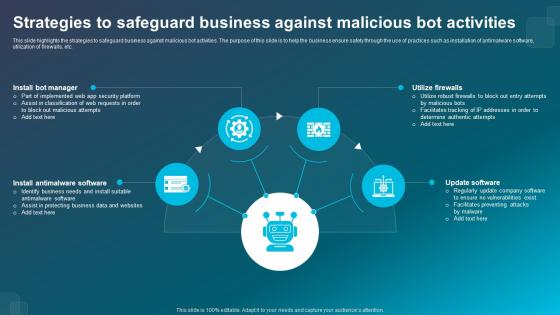 Strategies To Safeguard Business Against Malicious Bot Activities
Strategies To Safeguard Business Against Malicious Bot ActivitiesThis slide highlights the strategies to safeguard business against malicious bot activities. The purpose of this slide is to help the business ensure safety through the use of practices such as installation of antimalware software, utilization of firewalls, etc. Presenting our set of slides with Strategies To Safeguard Business Against Malicious Bot Activities. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Install Bot Manager, Install Antimalware Software, Update Software.
-
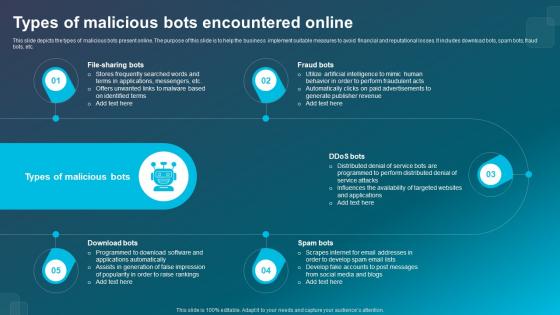 Types Of Malicious Bots Encountered Online
Types Of Malicious Bots Encountered OnlineThis slide depicts the types of malicious bots present online. The purpose of this slide is to help the business implement suitable measures to avoid financial and reputational losses. It includes download bots, spam bots, fraud bots, etc. Introducing our premium set of slides with Types Of Malicious Bots Encountered Online. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Fraud Bots, Spam Bots, Download Bots. So download instantly and tailor it with your information.
-
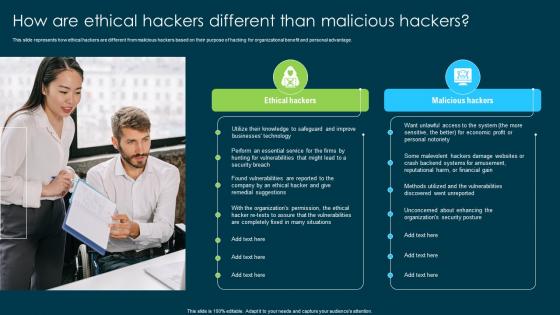 Ethical Hacking And Network Security How Are Ethical Hackers Different Than Malicious Hackers
Ethical Hacking And Network Security How Are Ethical Hackers Different Than Malicious HackersThis slide represents how ethical hackers are different from malicious hackers based on their purpose of hacking for organizational benefit and personal advantage. Increase audience engagement and knowledge by dispensing information using Ethical Hacking And Network Security How Are Ethical Hackers Different Than Malicious Hackers. This template helps you present information on two stages. You can also present information on Ethical Hackers, Malicious Hackers, Organizational Benefit, Organizations Security Posture using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cryptomining Innovations And Trends About Malicious Crypto Mining Overview And Impacts
Cryptomining Innovations And Trends About Malicious Crypto Mining Overview And ImpactsThis slide represents the Crypto Mining malware. The purpose of this slide is to showcase how it affects the victim, such as by gaining unauthorized use of computer power, impact on device owner, exploitation of web browsers and mobile apps, etc. Increase audience engagement and knowledge by dispensing information using Cryptomining Innovations And Trends About Malicious Crypto Mining Overview And Impacts. This template helps you present information on three stages. You can also present information on Unauthorized Use Of Computing Power, Impact On Device Owners, Concealed Nature Of Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cryptomining Innovations And Trends Possible Methods To Detect Malicious Crypto Mining
Cryptomining Innovations And Trends Possible Methods To Detect Malicious Crypto MiningThis slide highlights the symptoms used to detect Cryptojacking. The purpose of this slide is to showcase possible indicators, such as poor system performance, overheating, high electricity costs, sudden Central Processor Unit CPU usage spikes, and more. Deliver an outstanding presentation on the topic using this Cryptomining Innovations And Trends Possible Methods To Detect Malicious Crypto Mining. Dispense information and present a thorough explanation of Poor System Performance, Overheating, High Electricity Costs, Central Processor Unit using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
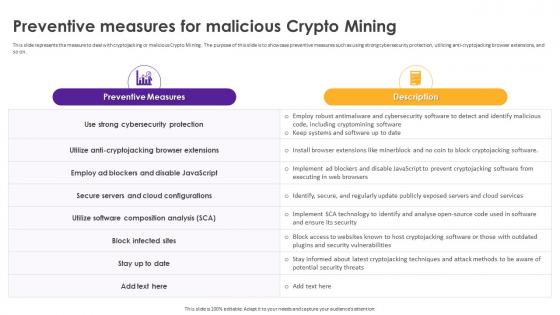 Cryptomining Innovations And Trends Preventive Measures For Malicious Crypto Mining
Cryptomining Innovations And Trends Preventive Measures For Malicious Crypto MiningThis slide represents the measure to deal with cryptojacking or malicious Crypto Mining. The purpose of this slide is to showcase preventive measures such as using strong cybersecurity protection, utilizing anti-cryptojacking browser extensions, and so on. Present the topic in a bit more detail with this Cryptomining Innovations And Trends Possible Methods To Detect Malicious Crypto Mining. Use it as a tool for discussion and navigation on Block Infected Sites, Strong Cybersecurity Protection, Secure Servers And Cloud Configurations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cryptomining Innovations And Trends Real World Examples Of Malicious Crypto Mining
Cryptomining Innovations And Trends Real World Examples Of Malicious Crypto MiningThis slide highlights the different examples of cryptojacking. The purpose of this slide is to showcase cryptojacking examples such as Prometei, PowerGhost, Graboid, MinerGAre malware, and so on. Present the topic in a bit more detail with this Cryptomining Innovations And Trends Real World Examples Of Malicious Crypto Mining. Use it as a tool for discussion and navigation on Minergate Malware, Malicious Crypto Mining, Legitimate Windows Processes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
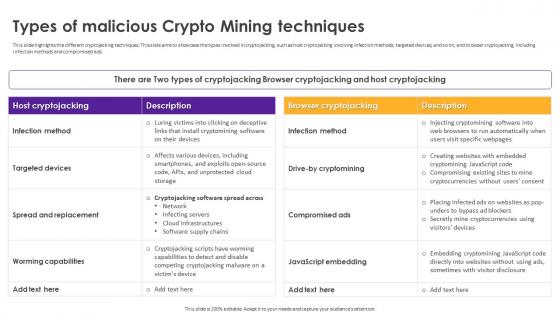 Cryptomining Innovations And Trends Types Of Malicious Crypto Mining Techniques
Cryptomining Innovations And Trends Types Of Malicious Crypto Mining TechniquesThis slide highlights the different cryptojacking techniques. This slide aims to showcase the types involved in cryptojacking, such as host cryptojacking involving infection methods, targeted devices, and so on, and browser cryptojacking, including infection methods and compromised ads. Present the topic in a bit more detail with this Cryptomining Innovations And Trends Types Of Malicious Crypto Mining Techniques. Use it as a tool for discussion and navigation on Spread And Replacement, Compromised Ads, Infection Method, Targeted Devices. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Proverbs 10 10 whoever winks maliciously causes powerpoint church sermon
Proverbs 10 10 whoever winks maliciously causes powerpoint church sermonWe are proud to present our proverbs 10 10 whoever winks maliciously causes powerpoint church sermon. Urge them to be more forgiving with our Proverbs 10.10. Get them acquainted with the Divine. Teach them forgiveness with our Sorrow PowerPoint sermon slides for pastors. Convince them of its great virtue. Proverbs 10.10 Whoever winks maliciously causes grief, and a chattering fool comes to ruin.
-
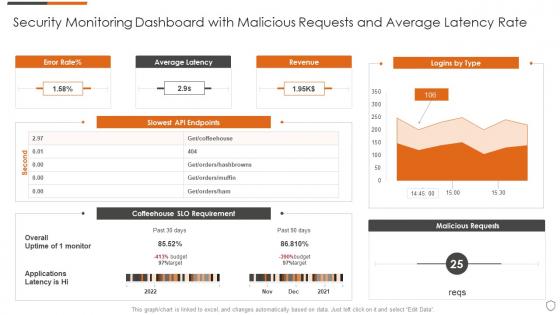 Security monitoring dashboard with malicious requests and average latency rate
Security monitoring dashboard with malicious requests and average latency rateDeliver an outstanding presentation on the topic using this Security Monitoring Dashboard With Malicious Requests And Average Latency Rate. Dispense information and present a thorough explanation of Average Latency, Revenue, Logins By Type using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
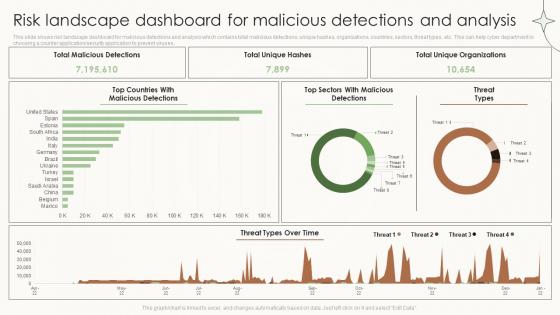 Risk Landscape Dashboard For Malicious Detections And Analysis
Risk Landscape Dashboard For Malicious Detections And AnalysisPresenting our well structured Risk Landscape Dashboard For Malicious Detections And Analysis. The topics discussed in this slide are Risk Landscape Dashboard, Cyber Attacks Analysis. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
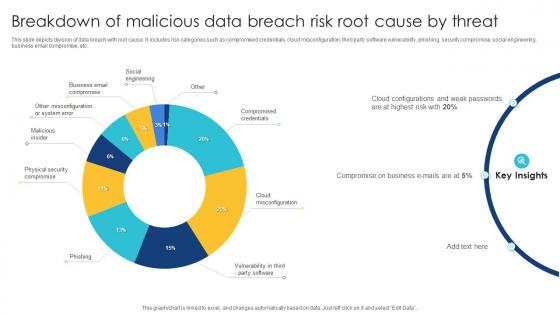 Breakdown Of Malicious Data Breach Risk Root Cause By Threat
Breakdown Of Malicious Data Breach Risk Root Cause By ThreatThis slide depicts division of data breach with root cause. It includes risk categories such as compromised credentials, cloud misconfiguration, third party software vulnerability, phishing, security compromise, social engineering, business email compromise, etc. Introducing our Breakdown Of Malicious Data Breach Risk Root Cause By Threat set of slides. The topics discussed in these slides are Social Engineering, Business Email Compromise, Malicious Insider. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Malicious Binary Code Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Malicious Binary Code Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Malicious binary code colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Malicious Binary Code Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Malicious Binary Code Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Malicious binary code monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Malicious Code Danger Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Malicious Code Danger Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Malicious code danger colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Malicious Code Danger Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Malicious Code Danger Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Malicious code danger monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Malicious Code Website Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Malicious Code Website Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Malicious code website colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Malicious Code Website Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Malicious Code Website Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Malicious code website monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
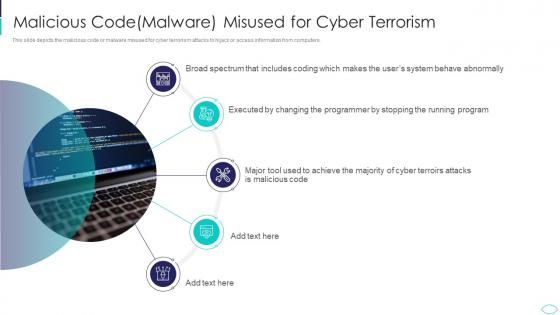 Malicious Codemalware Misused For Cyber Terrorism Cyber Terrorism Attacks
Malicious Codemalware Misused For Cyber Terrorism Cyber Terrorism AttacksThis slide depicts the malicious code or malware misused for cyber terrorism attacks to hijack or access information from computers. Increase audience engagement and knowledge by dispensing information using Malicious Codemalware Misused For Cyber Terrorism Cyber Terrorism Attacks. This template helps you present information on five stages. You can also present information on Malicious Code Malware Misused For Cyber Terrorism using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
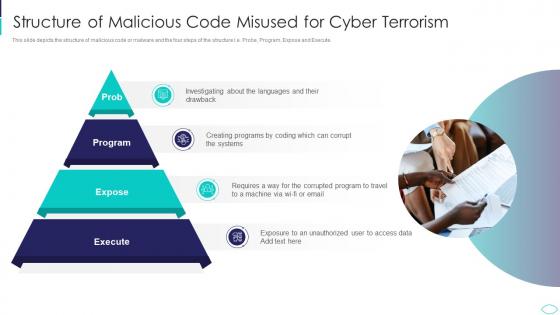 Structure Of Malicious Code Misused Cyber Terrorism Attacks
Structure Of Malicious Code Misused Cyber Terrorism AttacksThis slide depicts the structure of malicious code or malware and the four steps of the structure i.e. Probe, Program, Expose and Execute.Increase audience engagement and knowledge by dispensing information using Structure Of Malicious Code Misused Cyber Terrorism Attacks. This template helps you present information on four stages. You can also present information on Structure Of Malicious Code Misused For Cyber Terrorism using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
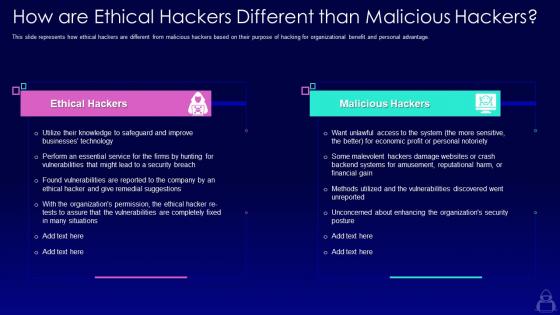 How are ethical hackers different than malicious hackers ppt inspiration templates
How are ethical hackers different than malicious hackers ppt inspiration templatesThis slide represents how ethical hackers are different from malicious hackers based on their purpose of hacking for organizational benefit and personal advantage. Increase audience engagement and knowledge by dispensing information using How Are Ethical Hackers Different Than Malicious Hackers Ppt Inspiration Templates. This template helps you present information on two stages. You can also present information on Ethical Hackers, Malicious Hackers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
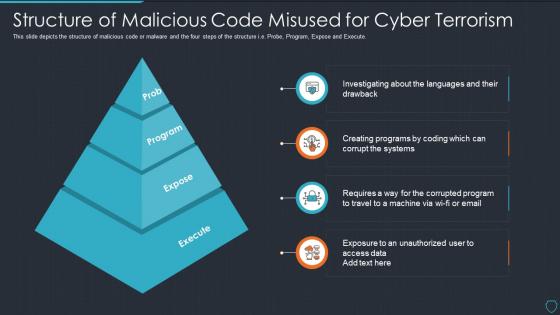 Cyberterrorism it structure of malicious code misused for cyber terrorism
Cyberterrorism it structure of malicious code misused for cyber terrorismThis slide depicts the structure of malicious code or malware and the four steps of the structure i.e. Probe, Program, Expose and Execute. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Structure Of Malicious Code Misused For Cyber Terrorism. This template helps you present information on four stages. You can also present information on Prob, Program, Expose, Execute using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Malicious Software Includes In Powerpoint And Google Slides Cpb
Malicious Software Includes In Powerpoint And Google Slides CpbPresenting our Malicious Software Includes In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases Five stages. It is useful to share insightful information on Malicious Software Includes This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Indication Malicious Code Running System In Powerpoint And Google Slides Cpb
Indication Malicious Code Running System In Powerpoint And Google Slides CpbPresenting our Indication Malicious Code Running System In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Indication Malicious Code Running System This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
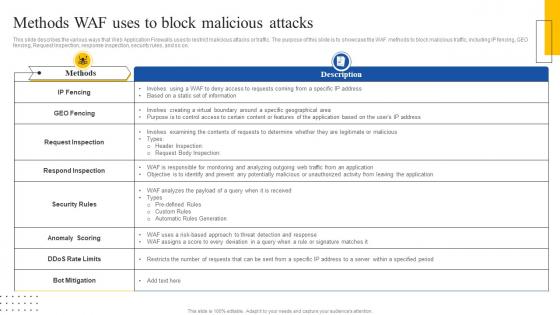 Web Application Firewall Introduction It Methods Waf Uses To Block Malicious Attacks
Web Application Firewall Introduction It Methods Waf Uses To Block Malicious AttacksThis slide describes the various ways that Web Application Firewalls uses to restrict malicious attacks or traffic. The purpose of this slide is to showcase the WAF methods to block malicious traffic, including IP fencing, GEO fencing, Request Inspection, response inspection, security rules, and so on. Present the topic in a bit more detail with this Web Application Firewall Introduction It Methods Waf Uses To Block Malicious Attacks. Use it as a tool for discussion and navigation on Ip Fencing, Geo Fencing, Request Inspection. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Tricks Employed By Malicious Websites To Phishing Attacks And Strategies
Tricks Employed By Malicious Websites To Phishing Attacks And StrategiesThis slide talks about various tricks utilized by fraudulent websites to scam the visitors. The purpose of this slide is to make users aware of such different tricks such as freeordiscount offers, low interest ratesorfree credit cards, employment opportunities, etc.Introducing Tricks Employed By Malicious Websites To Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Fictitious Businesses, Feel Emergency, Emergency Warnings, using this template. Grab it now to reap its full benefits.
-
 Types Malicious Software In Powerpoint And Google Slides Cpb
Types Malicious Software In Powerpoint And Google Slides CpbPresenting Types Malicious Software In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Types Malicious Software. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Malware Attack Icon Sending Malicious Emails
Malware Attack Icon Sending Malicious EmailsIntroducing our Malware Attack Icon Sending Malicious Emails set of slides. The topics discussed in these slides are Malware Attack Icon, Sending Malicious Emails. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Malware Device Icon To Prevent Form Malicious Attacks
Malware Device Icon To Prevent Form Malicious AttacksPresenting our well structured Malware Device Icon To Prevent Form Malicious Attacks. The topics discussed in this slide are Malware Device Icon, Prevent Form Malicious Attacks. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
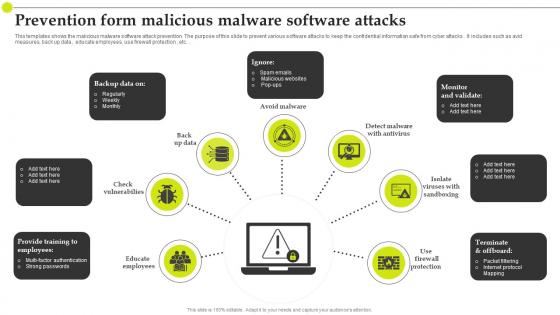 Prevention Form Malicious Malware Software Attacks
Prevention Form Malicious Malware Software AttacksThis templates shows the malicious malware software attack prevention. The purpose of this slide to prevent various software attacks to keep the confidential information safe from cyber attacks . It includes such as avid measures, back up data , educate employees, use firewall protection , etc.Introducing our premium set of slides with Prevention Form Malicious Malware Software Attacks. Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Packet Filtering, Internet Protocol, Educate Employees. So download instantly and tailor it with your information.
-
 Application security effectiveness change management configuration management malicious software
Application security effectiveness change management configuration management malicious softwarePresenting this set of slides with name - Application Security Effectiveness Change Management Configuration Management Malicious Software. This is an editable four stages graphic that deals with topics like Application Security Effectiveness, Change Management, Configuration Management, Malicious Software to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Application environment security controls configuration management malicious software
Application environment security controls configuration management malicious softwarePresenting this set of slides with name - Application Environment Security Controls Configuration Management Malicious Software. This is an editable three stages graphic that deals with topics like Application Environment Security Controls, Configuration Management, Malicious Software to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Social engineering attack icon for malicious activities
Social engineering attack icon for malicious activitiesPresenting this set of slides with name - Social Engineering Attack Icon For Malicious Activities. This is a three stage process. The stages in this process are Social Engineering, Social Network, Technology.
-
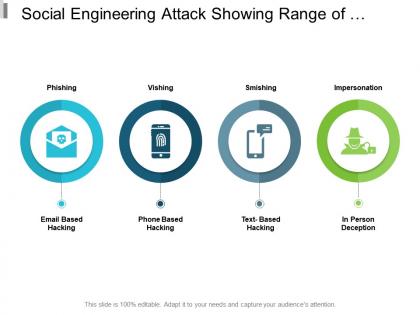 Social engineering attack showing range of malicious activities
Social engineering attack showing range of malicious activitiesPresenting this set of slides with name - Social Engineering Attack Showing Range Of Malicious Activities. This is a four stage process. The stages in this process are Social Engineering, Social Network, Technology.
-
 Social engineering icon showing malicious activities
Social engineering icon showing malicious activitiesPresenting this set of slides with name - Social Engineering Icon Showing Malicious Activities. This is a three stage process. The stages in this process are Social Engineering, Social Network, Technology.

