Powerpoint Templates and Google slides for Methodical
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
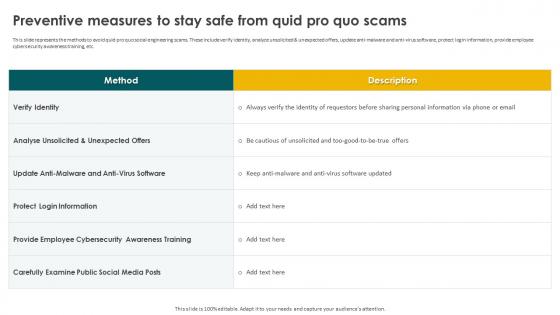 Preventive Measures To Stay Safe From Quid Pro Quo Scams Social Engineering Methods And Mitigation
Preventive Measures To Stay Safe From Quid Pro Quo Scams Social Engineering Methods And MitigationThis slide represents the methods to avoid quid pro quo social engineering scams. These include verify identity, analyze unsolicited and unexpected offers, update anti-malware and anti-virus software, protect login information, provide employee cybersecurity awareness training, etc. Present the topic in a bit more detail with this Preventive Measures To Stay Safe From Quid Pro Quo Scams Social Engineering Methods And Mitigation. Use it as a tool for discussion and navigation on Protect Login Information, Anti Virus Software, Quid Pro Quo Scams. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Social Engineering Methods And Mitigation 30 60 90 Days Plan To Implement Social Engineering Prevention
Social Engineering Methods And Mitigation 30 60 90 Days Plan To Implement Social Engineering PreventionThis slide represents 30-60-90 plan to protect companies and their employees from social engineering attacks. The purpose of this slide is to illustrate the plans of the first 90 days from the start of the project including steps to be followed at interval of one month. Introducing Social Engineering Methods And Mitigation 30 60 90 Days Plan To Implement Social Engineering Prevention to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Social Engineering, Prevention Strategies, Protect Companies, Social Engineering Attacks, using this template. Grab it now to reap its full benefits.
-
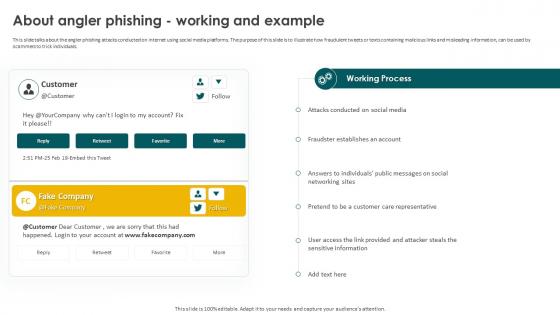 Social Engineering Methods And Mitigation About Angler Phishing Working And Example
Social Engineering Methods And Mitigation About Angler Phishing Working And ExampleThis slide talks about the angler phishing attacks conducted on internet using social media platforms. The purpose of this slide is to illustrate how fraudulent tweets or texts containing malicious links and misleading information, can be used by scammers to trick individuals. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation About Angler Phishing Working And Example. Dispense information and present a thorough explanation of Angler Phishing Attacks, Social Media Platforms, Fraudulent Tweets, Texts Containing Malicious using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
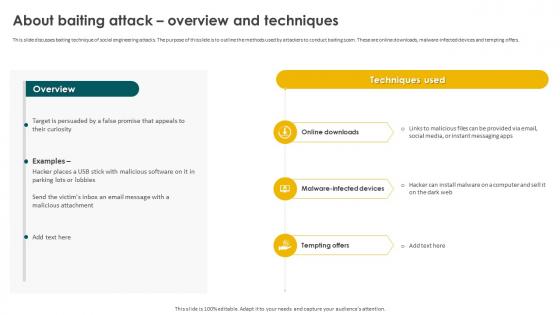 Social Engineering Methods And Mitigation About Baiting Attack Overview And Techniques
Social Engineering Methods And Mitigation About Baiting Attack Overview And TechniquesThis slide discusses baiting technique of social engineering attacks. The purpose of this slide is to outline the methods used by attackers to conduct baiting scam. These are online downloads, malware-infected devices and tempting offers. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation About Baiting Attack Overview And Techniques. Use it as a tool for discussion and navigation on Online Downloads, Malware Infected Devices, Baiting Attack, Malicious Attachment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
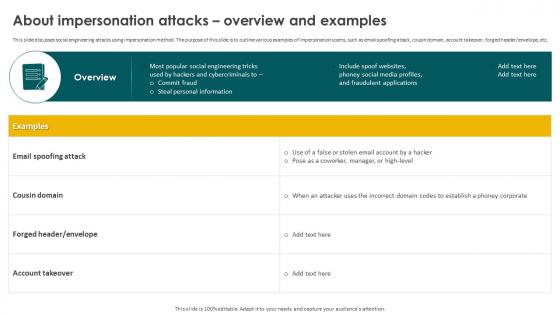 Social Engineering Methods And Mitigation About Impersonation Attacks Overview And Examples
Social Engineering Methods And Mitigation About Impersonation Attacks Overview And ExamplesThis slide discusses social engineering attacks using impersonation method. The purpose of this slide is to outline various examples of impersonation scams, such as email spoofing attack, cousin domain, account takeover, forged header or envelope, etc. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation About Impersonation Attacks Overview And Examples. Dispense information and present a thorough explanation of Email Spoofing Attack, Cousin Domain, Fraudulent Applications, Impersonation Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
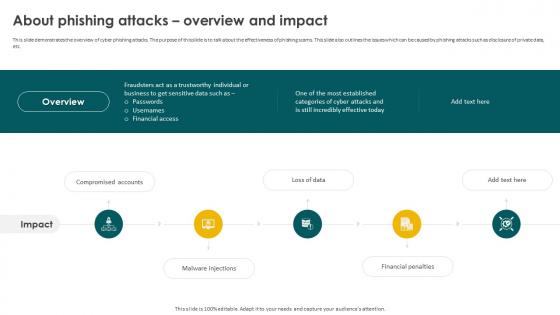 Social Engineering Methods And Mitigation About Phishing Attacks Overview And Impact
Social Engineering Methods And Mitigation About Phishing Attacks Overview And ImpactThis slide demonstrates the overview of cyber phishing attacks. The purpose of this slide is to talk about the effectiveness of phishing scams. This slide also outlines the issues which can be caused by phishing attacks such as disclosure of private data, etc. Increase audience engagement and knowledge by dispensing information using Social Engineering Methods And Mitigation About Phishing Attacks Overview And Impact. This template helps you present information on five stages. You can also present information on Compromised Accounts, Malware Injections, Financial Penalties, Financial Access using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
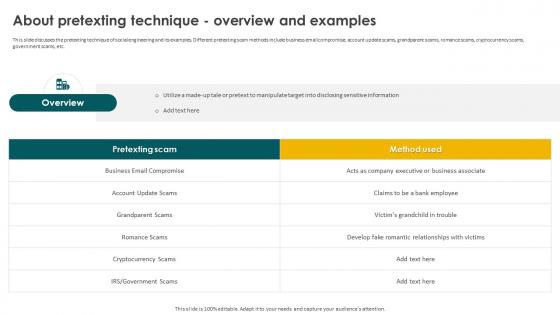 Social Engineering Methods And Mitigation About Pretexting Technique Overview And Examples
Social Engineering Methods And Mitigation About Pretexting Technique Overview And ExamplesThis slide discusses the pretexting technique of social engineering and its examples. Different pretexting scam methods include business email compromise, account update scams, grandparent scams, romance scams, cryptocurrency scams, government scams, etc. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation About Pretexting Technique Overview And Examples. Use it as a tool for discussion and navigation on Business Email Compromise, Grandparent Scams, Cryptocurrency Scams, Pretexting Technique. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Social Engineering Methods And Mitigation About Smishing Attacks Overview And Types
Social Engineering Methods And Mitigation About Smishing Attacks Overview And TypesThis slide talks about the smishing cyber attacks conducted by sending text messages to the targets. The purpose of this slide is to illustrate how fraudulent texts are sent to the users which contains malicious links and other mis-leading information. Introducing Social Engineering Methods And Mitigation About Smishing Attacks Overview And Types to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Smishing Scams, Financial Services Smishing, Gift Smishing, Customer Support Smishing, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Methods And Mitigation About Tailgating Attacks Overview And Techniques
Social Engineering Methods And Mitigation About Tailgating Attacks Overview And TechniquesThis slide demonstrates the procedure of tailgating attack with the help of an illustrative example. The purpose of this slide is to provide the overview of tailgating social engineering attack and the techniques used to implement it in organizations. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation About Tailgating Attacks Overview And Techniques. Dispense information and present a thorough explanation of Procedure Of Tailgating Attack, Tailgating Social Engineering Attack, Subcontractors Identity using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Social Engineering Methods And Mitigation About Vishing Attacks Overview And Identification
Social Engineering Methods And Mitigation About Vishing Attacks Overview And IdentificationThis slide talks about the vishing cyber attacks. The purpose of this slide is to explain the vishing technique used by phishers to scam victims. This slide also outlines the signs of vishing attack such as call from unknown number, act as an authority, etc. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation About Vishing Attacks Overview And Identification. Use it as a tool for discussion and navigation on Vishing Cyber Attacks, Vishing Technique, Phishers To Scam Victims, Internal Revenue Service. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
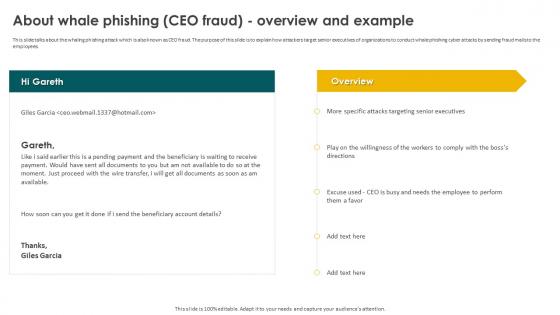 Social Engineering Methods And Mitigation About Whale Phishing CEO Fraud Overview And Example
Social Engineering Methods And Mitigation About Whale Phishing CEO Fraud Overview And ExampleThis slide talks about the whaling phishing attack which is also known as CEO fraud. The purpose of this slide is to explain how attackers target senior executives of organizations to conduct whale phishing cyber attacks by sending fraud mails to the employees. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation About Whale Phishing CEO Fraud Overview And Example. Dispense information and present a thorough explanation of Whaling Phishing Attack, Attackers Target Senior Executives, Phishing Cyber Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
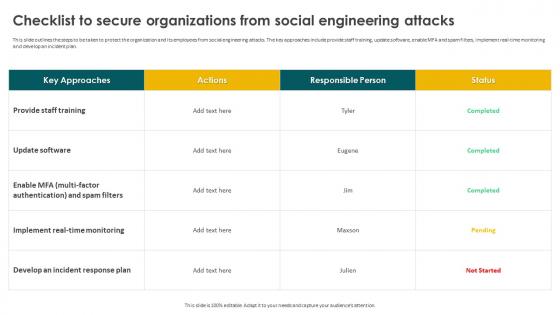 Social Engineering Methods And Mitigation Checklist To Secure Organizations From Social Engineering
Social Engineering Methods And Mitigation Checklist To Secure Organizations From Social EngineeringThis slide outlines the steps to be taken to protect the organization and its employees from social engineering attacks. The key approaches include provide staff training, update software, enable MFA and spam filters, implement real-time monitoring and develop an incident plan. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation Checklist To Secure Organizations From Social Engineering. Dispense information and present a thorough explanation of Social Engineering Attacks, Real Time Monitoring, Develop An Incident Plan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Social Engineering Methods And Mitigation Classification Of Different Social Engineering Attacks
Social Engineering Methods And Mitigation Classification Of Different Social Engineering AttacksThis slide represents the different types of social engineering attacks based on technology and human interaction. These include impersonation, tailgating, baiting, pretexting, scareware, quid pro quo, reverse social engineering, phishing, email phishing, spear phishing, whaling, etc. Increase audience engagement and knowledge by dispensing information using Social Engineering Methods And Mitigation Classification Of Different Social Engineering Attacks. This template helps you present information on two stages. You can also present information on Human Based Attacks, Social Engineering Attacks, Technology Based Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
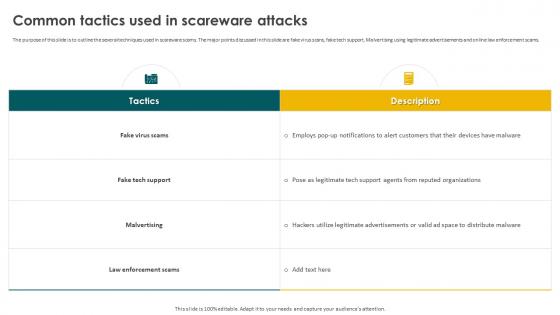 Social Engineering Methods And Mitigation Common Tactics Used In Scareware Attacks
Social Engineering Methods And Mitigation Common Tactics Used In Scareware AttacksThe purpose of this slide is to outline the several techniques used in scareware scams. The major points discussed in this slide are fake virus scans, fake tech support, Malvertising using legitimate advertisements and online law enforcement scams. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation Common Tactics Used In Scareware Attacks. Use it as a tool for discussion and navigation on Fake Virus Scams, Malvertising, Law Enforcement Scams, Fake Tech Support. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
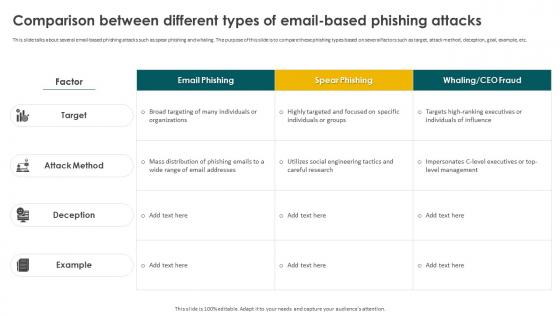 Social Engineering Methods And Mitigation Comparison Between Different Types Of Email Based Phishing
Social Engineering Methods And Mitigation Comparison Between Different Types Of Email Based PhishingThis slide talks about several email-based phishing attacks such as spear phishing and whaling. The purpose of this slide is to compare these phishing types based on several factors such as target, attack method, deception, goal, example, etc. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation Comparison Between Different Types Of Email Based Phishing. Dispense information and present a thorough explanation of Email Based Phishing Attacks, Goal, Target, Spear Phishing And Whaling using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Social Engineering Methods And Mitigation Defensive Strategies Against Tailgating Attacks
Social Engineering Methods And Mitigation Defensive Strategies Against Tailgating AttacksThis slide highlights the best practices to avoid tailgating social engineering attacks. These include beware of surroundings, implement biometric scanners, issue smart badges or cards with RFID technology, install AI-based video surveillance, etc. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation Defensive Strategies Against Tailgating Attacks. Use it as a tool for discussion and navigation on Implement Biometric Scanners, Be Aware Of Surroundings, Unique Physical Features. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
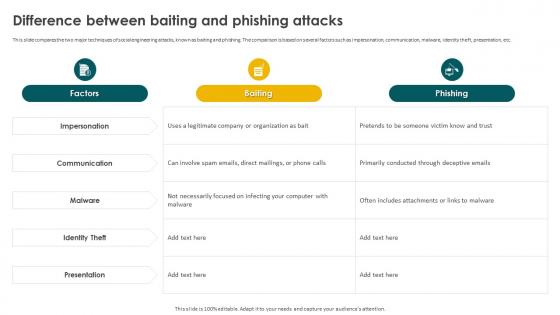 Social Engineering Methods And Mitigation Difference Between Baiting And Phishing Attacks
Social Engineering Methods And Mitigation Difference Between Baiting And Phishing AttacksThis slide compares the two major techniques of social engineering attacks, known as baiting and phishing. The comparison is based on several factors such as impersonation, communication, malware, identity theft, presentation, etc. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation Difference Between Baiting And Phishing Attacks. Dispense information and present a thorough explanation of Impersonation, Communication, Identity Theft, Presentation, Malware using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
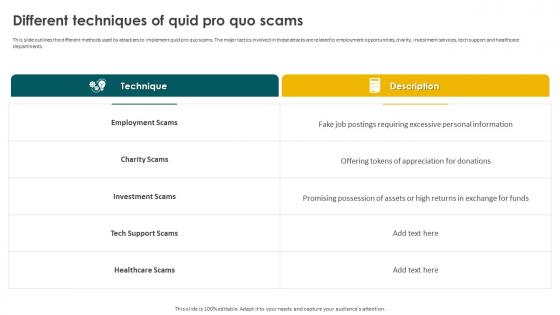 Social Engineering Methods And Mitigation Different Techniques Of Quid Pro Quo Scams
Social Engineering Methods And Mitigation Different Techniques Of Quid Pro Quo ScamsThis slide outlines the different methods used by attackers to implement quid pro quo scams. The major tactics involved in these attacks are related to employment opportunities, charity, investment services, tech support and healthcare departments. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation Different Techniques Of Quid Pro Quo Scams. Use it as a tool for discussion and navigation on Employment Scams, Charity Scams, Investment Scams, Tech Support Scams, Healthcare Scams. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Social Engineering Methods And Mitigation Different Types Of Vishing Cyber Attacks
Social Engineering Methods And Mitigation Different Types Of Vishing Cyber AttacksThis slide talks about the various types of vishing cyber attacks. The purpose of this slide is to briefly explain different techniques of vishing scams used by the attackers to scam users. These are caller ID spoofing, dumpster diving, wardialing, etc. Introducing Social Engineering Methods And Mitigation Different Types Of Vishing Cyber Attacks to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Vishing Cyber Attacks, Dumpster Diving, Wardialing, Techniques Of Vishing Scams, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Methods And Mitigation Execution Of Man In The Middle Cyber Attacks
Social Engineering Methods And Mitigation Execution Of Man In The Middle Cyber AttacksThis slide illustrates the process of executing man-in-the-middle cyber attacks. The purpose of this slide is to outline the two stages of execution of MITM scams. These stages are interception and decryption. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation Execution Of Man In The Middle Cyber Attacks. Dispense information and present a thorough explanation of Cyber Attacks, Intercepting User Traffic, Malicious Wi Fi Hotspots using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Social Engineering Methods And Mitigation Guidelines To Stay Safe From Phishing Scams
Social Engineering Methods And Mitigation Guidelines To Stay Safe From Phishing ScamsThis slide outlines the various preventive measures to stay safe from phishing attacks. These include know how to spot phishing scams, avoid clicking that link, install free anti-phishing extensions, change passwords regularly, install firewalls, never miss updates, etc. Increase audience engagement and knowledge by dispensing information using Social Engineering Methods And Mitigation Guidelines To Stay Safe From Phishing Scams. This template helps you present information on seven stages. You can also present information on Install Firewalls, Change Passwords Regularly, Avoid Clicking That Link, Stay Safe From Phishing Scams using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Social Engineering Methods And Mitigation How To Protect Users From Vishing Attacks
Social Engineering Methods And Mitigation How To Protect Users From Vishing AttacksThis slide talks about the ways to protect users from vishing attacks. These include avoid calls from robots, never respond to audio-automated calls, verify the identity of the caller, never share personal information over the call, use multi-factor authentication, etc. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation Guidelines To Stay Safe From Phishing Scams. Use it as a tool for discussion and navigation on Facto Authentication, Government Organizations, Identity Of The Caller, Avoid Calls From Robots. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
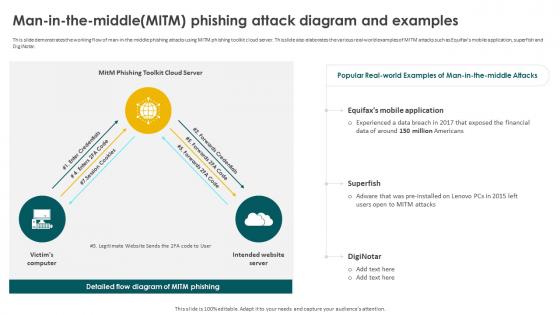 Social Engineering Methods And Mitigation Man In The Middlemitm Phishing Attack Diagram
Social Engineering Methods And Mitigation Man In The Middlemitm Phishing Attack DiagramThis slide demonstrates the working flow of man-in-the-middle phishing attacks using MITM phishing toolkit cloud server. This slide also elaborates the various real-world examples of MITM attacks such as Equifaxs mobile application, superfish and DigiNotar. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation Man In The Middlemitm Phishing Attack Diagram. Dispense information and present a thorough explanation of Equifaxs Mobile Application, Superfish, Phishing Attack Diagram, Financial Data using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
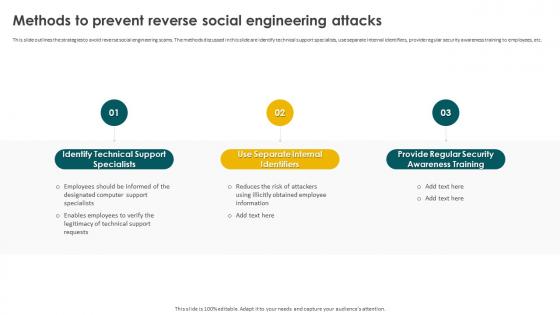 Social Engineering Methods And Mitigation Methods To Prevent Reverse Social Engineering Attacks
Social Engineering Methods And Mitigation Methods To Prevent Reverse Social Engineering AttacksThis slide outlines the strategies to avoid reverse social engineering scams. The methods discussed in this slide are identify technical support specialists, use separate internal identifiers, provide regular security awareness training to employees, etc. Increase audience engagement and knowledge by dispensing information using Social Engineering Methods And Mitigation Methods To Prevent Reverse Social Engineering Attacks. This template helps you present information on three stages. You can also present information on Identify Technical Support Specialists, Use Separate Internal Identifiers, Provide Regular Security Awareness Training using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
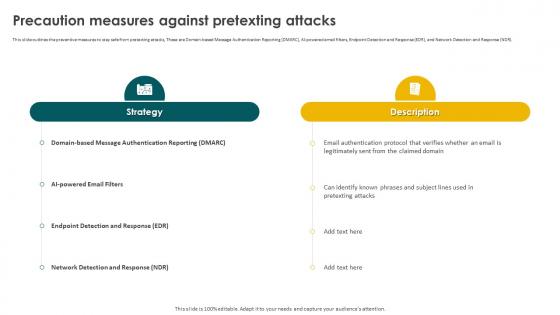 Social Engineering Methods And Mitigation Precaution Measures Against Pretexting Attacks
Social Engineering Methods And Mitigation Precaution Measures Against Pretexting AttacksThis slide outlines the preventive measures to stay safe from pretexting attacks, These are Domain-based Message Authentication Reporting DMARC, AI-powered email filters, Endpoint Detection and Response EDR, and Network Detection and Response NDR. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation Precaution Measures Against Pretexting Attacks. Use it as a tool for discussion and navigation on Endpoint Detection And Response, Network Detection And Response, Pretexting Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
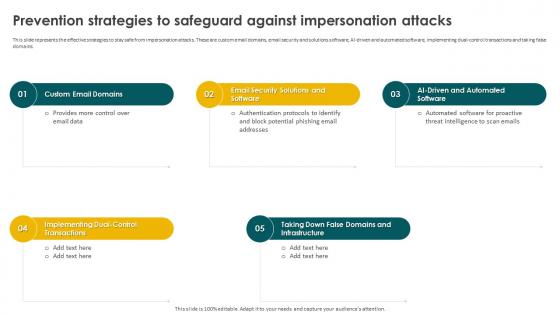 Social Engineering Methods And Mitigation Prevention Strategies To Safeguard Against Impersonation
Social Engineering Methods And Mitigation Prevention Strategies To Safeguard Against ImpersonationThis slide represents the effective strategies to stay safe from impersonation attacks. These are custom email domains, email security and solutions software, AI-driven and automated software, implementing dual-control transactions and taking false domains. Introducing Social Engineering Methods And Mitigation Prevention Strategies To Safeguard Against Impersonation to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Custom Email Domains, Taking Down False Domains, Dual Control Transactions, using this template. Grab it now to reap its full benefits.
-
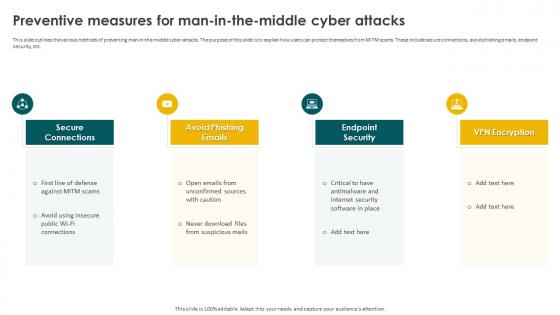 Social Engineering Methods And Mitigation Preventive Measures For Man In The Middle Cyber Attacks
Social Engineering Methods And Mitigation Preventive Measures For Man In The Middle Cyber AttacksThis slide outlines the various methods of preventing man-in-the-middle cyber attacks. The purpose of this slide is to explain how users can protect themselves from MITM scams. These include secure connections, avoid phishing emails, endpoint security, etc. Increase audience engagement and knowledge by dispensing information using Social Engineering Methods And Mitigation Preventive Measures For Man In The Middle Cyber Attacks. This template helps you present information on four stages. You can also present information on Secure Connections, Avoid Phishing Emails, Endpoint Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
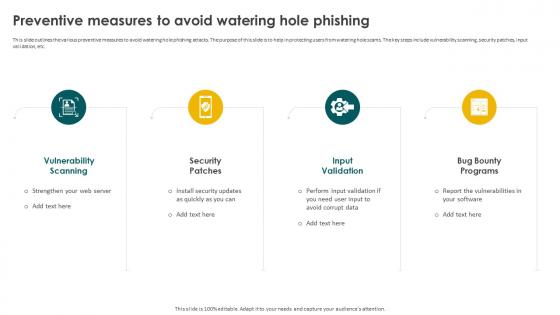 Social Engineering Methods And Mitigation Preventive Measures To Avoid Watering Hole Phishing
Social Engineering Methods And Mitigation Preventive Measures To Avoid Watering Hole PhishingThis slide outlines the various preventive measures to avoid watering hole phishing attacks. The purpose of this slide is to help in protecting users from watering hole scams. The key steps include vulnerability scanning, security patches, input validation, etc. Introducing Social Engineering Methods And Mitigation Preventive Measures To Avoid Watering Hole Phishing to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Vulnerability Scanning, Security Patches, Input Vulnerability, Bug Bounty Programs, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Methods And Mitigation Preventive Strategies For Baiting Cyber Attacks
Social Engineering Methods And Mitigation Preventive Strategies For Baiting Cyber AttacksThis slide outlines the methods to prevent baiting attacks. These are employee training, dont follow links blindly, use anti-virus and anti-malware software, avoid use of external devices without scanning and hold organized simulated attacks. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation Preventive Strategies For Baiting Cyber Attacks. Dispense information and present a thorough explanation of Vulnerability Scanning, Security Patches, Input Vulnerability, Bug Bounty Programs using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
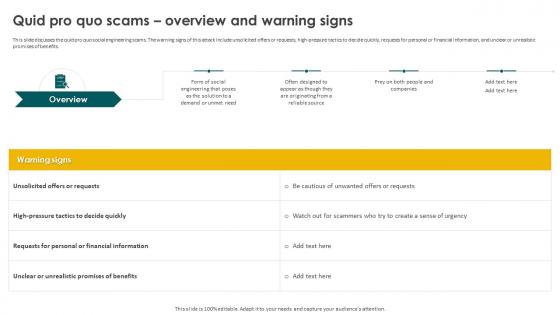 Social Engineering Methods And Mitigation Quid Pro Quo Scams Overview And Warning Signs
Social Engineering Methods And Mitigation Quid Pro Quo Scams Overview And Warning SignsThis slide discusses the quid pro quo social engineering scams. The warning signs of this attack include unsolicited offers or requests, high-pressure tactics to decide quickly, requests for personal or financial information, and unclear or unrealistic promises of benefits. Increase audience engagement and knowledge by dispensing information using Social Engineering Methods And Mitigation Quid Pro Quo Scams Overview And Warning Signs. This template helps you present information on four stages. You can also present information on Quid Pro Quo Scams, Unrealistic Promises Of Benefits, Financial Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
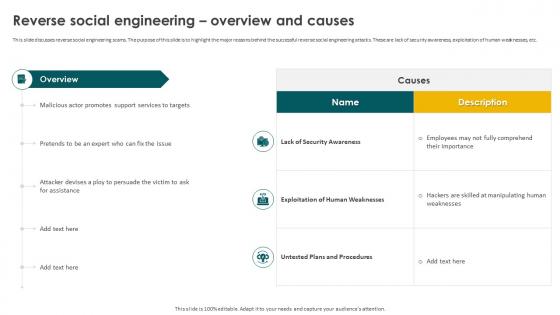 Social Engineering Methods And Mitigation Reverse Social Engineering Overview And Causes
Social Engineering Methods And Mitigation Reverse Social Engineering Overview And CausesThis slide discusses reverse social engineering scams. The purpose of this slide is to highlight the major reasons behind the successful reverse social engineering attacks. These are lack of security awareness, exploitation of human weaknesses, etc. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation Reverse Social Engineering Overview And Causes. Use it as a tool for discussion and navigation on Lack Of Security Awareness, Exploitation Of Human Weaknesses, Untested Plans And Procedures. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
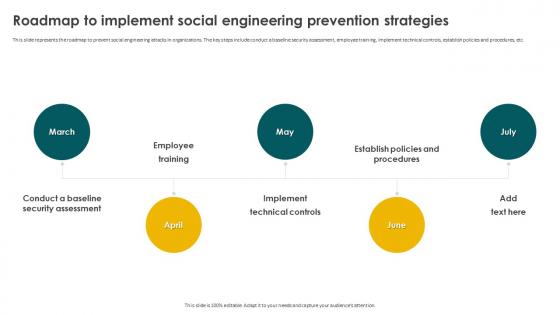 Social Engineering Methods And Mitigation Roadmap To Implement Social Engineering Prevention Strategies
Social Engineering Methods And Mitigation Roadmap To Implement Social Engineering Prevention StrategiesThis slide represents the roadmap to prevent social engineering attacks in organizations. The key steps include conduct a baseline security assessment, employee training, implement technical controls, establish policies and procedures, etc. Introducing Social Engineering Methods And Mitigation Roadmap To Implement Social Engineering Prevention Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Employee Training, Implement Technical Controls, Social Engineering Prevention Strategies, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Methods And Mitigation Scareware Technique Overview And Warning Signs
Social Engineering Methods And Mitigation Scareware Technique Overview And Warning SignsThis slide represents the scareware technique used by scammers to attempt social engineering attacks. The purpose of this slide is to demonstrate the various warning signs of scareware attack. Increase audience engagement and knowledge by dispensing information using Social Engineering Methods And Mitigation Scareware Technique Overview And Warning Signs. This template helps you present information on five stages. You can also present information on Scareware Technique, Scareware Attack, Social Engineering Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
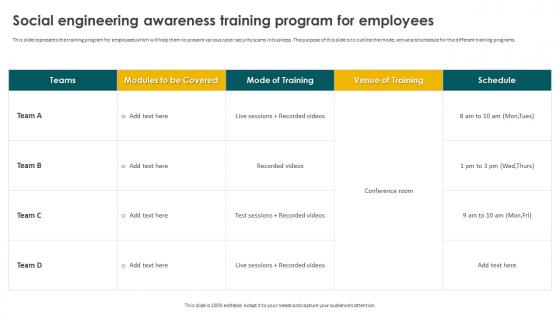 Social Engineering Methods And Mitigation Social Engineering Awareness Training Program For Employees
Social Engineering Methods And Mitigation Social Engineering Awareness Training Program For EmployeesThis slide represents the training program for employees which will help them to prevent various cyber security scams in business. The purpose of this slide is to outline the mode, venue and schedule for the different training programs. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation Social Engineering Awareness Training Program For Employees. Use it as a tool for discussion and navigation on Social Engineering, Awareness Training, Program For Employees. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Social Engineering Methods And Mitigation Social Engineering Technique Dumpster Diving
Social Engineering Methods And Mitigation Social Engineering Technique Dumpster DivingThis slide discusses dumpster diving technique used to carry out social engineering attacks. The various types of information collected include passwords, access codes, organizational charts, calendars, credit card receipts, expense reports, phone numbers, etc. Introducing Social Engineering Methods And Mitigation Social Engineering Technique Dumpster Diving to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Organizational Charts, Network Or Application Diagrams, Dumpster Diving, Social Engineering Technique, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Methods And Mitigation Steps To Identify Whaling Phishing Attacks
Social Engineering Methods And Mitigation Steps To Identify Whaling Phishing AttacksThis slide talks about the various methods of identifying whale phishing cyber attacks. The purpose of this slide is to help users identify CEO phishing scams. These include flag emails received from external domains, cross-verify sensitive requests, etc. Increase audience engagement and knowledge by dispensing information using Social Engineering Methods And Mitigation Steps To Identify Whaling Phishing Attacks. This template helps you present information on six stages. You can also present information on Phishing Cyber Attacks, Phishing Scams, External Domains, Cross Verify Sensitive Requests using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
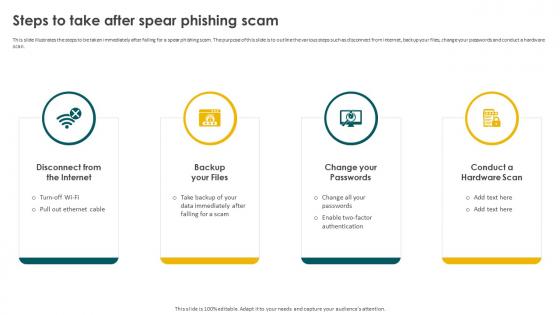 Social Engineering Methods And Mitigation Steps To Take After Spear Phishing Scam
Social Engineering Methods And Mitigation Steps To Take After Spear Phishing ScamThis slide illustrates the steps to be taken immediately after falling for a spear phishing scam. The purpose of this slide is to outline the various steps such as disconnect from internet, backup your files, change your passwords and conduct a hardware scan. Introducing Social Engineering Methods And Mitigation Steps To Take After Spear Phishing Scam to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Disconnect From The Internet, Change Your Passwords, Conduct A Hardware Scan, Backup Your Files, using this template. Grab it now to reap its full benefits.
-
 Social Engineering Methods And Mitigation Strategies Techniques Table Of Contents
Social Engineering Methods And Mitigation Strategies Techniques Table Of ContentsIncrease audience engagement and knowledge by dispensing information using Social Engineering Methods And Mitigation Strategies Techniques Table Of Contents. This template helps you present information on one stages. You can also present information on Overview And Warning Signs, Common Tactics Used, Working Process, Tools And Best Practices using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
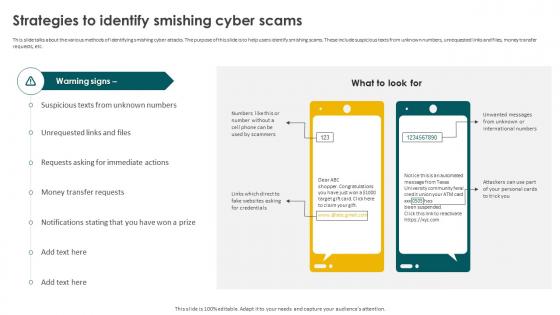 Social Engineering Methods And Mitigation Strategies To Identify Smishing Cyber Scams
Social Engineering Methods And Mitigation Strategies To Identify Smishing Cyber ScamsThis slide talks about the various methods of identifying smishing cyber attacks. The purpose of this slide is to help users identify smishing scams. These include suspicious texts from unknown numbers, unrequested links and files, money transfer requests, etc. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation Strategies To Identify Smishing Cyber Scams. Dispense information and present a thorough explanation of Smishing Cyber Scams, Money Transfer Requests, Unrequested Links And Files using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
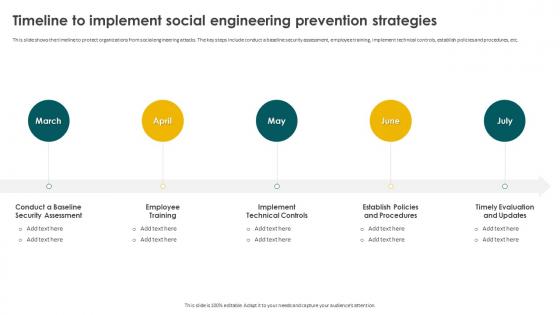 Social Engineering Methods And Mitigation Timeline To Implement Social Engineering Prevention Strategies
Social Engineering Methods And Mitigation Timeline To Implement Social Engineering Prevention StrategiesThis slide shows the timeline to protect organizations from social engineering attacks. The key steps include conduct a baseline security assessment, employee training, implement technical controls, establish policies and procedures, etc. Introducing Social Engineering Methods And Mitigation Timeline To Implement Social Engineering Prevention Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Employee Training, Implement Technical Controls, Establish Policies And Procedures, Timely Evaluation And Updates, using this template. Grab it now to reap its full benefits.
-
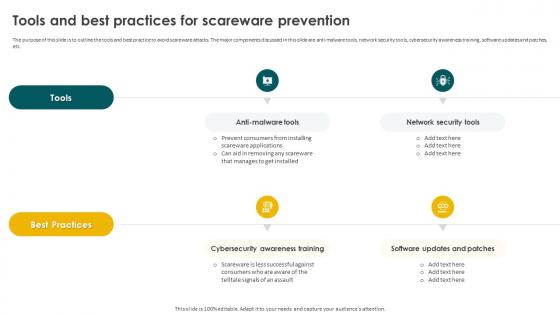 Social Engineering Methods And Mitigation Tools And Best Practices For Scareware Prevention
Social Engineering Methods And Mitigation Tools And Best Practices For Scareware PreventionThe purpose of this slide is to outline the tools and best practice to avoid scareware attacks. The major components discussed in this slide are anti-malware tools, network security tools, cybersecurity awareness training, software updates and patches, etc. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation Tools And Best Practices For Scareware Prevention. Use it as a tool for discussion and navigation on Anti Malware Tools, Network Security Tools, Software Updates And Patches, Cybersecurity Awareness Training. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Social Engineering Methods And Mitigation Understanding The Process Of E Mail Based Phishing Attacks
Social Engineering Methods And Mitigation Understanding The Process Of E Mail Based Phishing AttacksThis slide demonstrates the procedure of email-based phishing attacks. The purpose of this slide is to explain how fake websites are used by attackers to get the sensitive data of the users. The key components include database, fake website, etc. Deliver an outstanding presentation on the topic using this Social Engineering Methods And Mitigation Understanding The Process Of E Mail Based Phishing Attacks. Dispense information and present a thorough explanation of Phishing Attacks, Fake Website, Email Based Phishing Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Social Engineering Methods And Mitigation Understanding The Working Process Of Scareware Scam
Social Engineering Methods And Mitigation Understanding The Working Process Of Scareware ScamThis slide represents the various steps involved in fake antivirus scareware campaign process. The major components are victim, bank, fake anti-virus website, payment processor, affiliates, settlement systems, credit card company, etc. Present the topic in a bit more detail with this Social Engineering Methods And Mitigation Understanding The Working Process Of Scareware Scam. Use it as a tool for discussion and navigation on Understanding The Working Process, Scareware Scam, Payment Processor, Affiliates, Settlement Systems. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Social Engineering Methods And Mitigation Working Of Watering Hole Phishing Attack
Social Engineering Methods And Mitigation Working Of Watering Hole Phishing AttackThis slide represents the working process of watering hole phishing attacks. The purpose of this slide is to illustrate the flow diagram of watering hole phishing scams. The key points include research and identification, analysis, preparation and execution. Increase audience engagement and knowledge by dispensing information using Social Engineering Methods And Mitigation Working Of Watering Hole Phishing Attack. This template helps you present information on four stages. You can also present information on Research And Identification, Analysis, Preparation, Domain And Subdomain Vulnerabilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
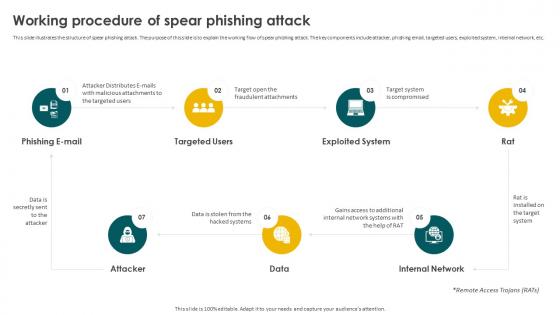 Social Engineering Methods And Mitigation Working Procedure Of Spear Phishing Attack
Social Engineering Methods And Mitigation Working Procedure Of Spear Phishing AttackThis slide illustrates the structure of spear phishing attack. The purpose of this slide is to explain the working flow of spear phishing attack. The key components include attacker, phishing email, targeted users, exploited system, internal network, etc. Introducing Social Engineering Methods And Mitigation Working Procedure Of Spear Phishing Attack to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Phishing Email, Targeted Users, Exploited System, Internal Network, using this template. Grab it now to reap its full benefits.
-
 Table Of Contents For Social Engineering Methods And Mitigation Strategies
Table Of Contents For Social Engineering Methods And Mitigation StrategiesIncrease audience engagement and knowledge by dispensing information using Table Of Contents For Social Engineering Methods And Mitigation Strategies. This template helps you present information on five stages. You can also present information on Social Engineering Attacks, Mitigation Strategies, Training And Budget, Tracking Dashboard using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Principle Variational Methods In Powerpoint And Google Slides Cpb
Principle Variational Methods In Powerpoint And Google Slides CpbPresenting our Principle Variational Methods In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases two stages. It is useful to share insightful information on Principle Variational Methods This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
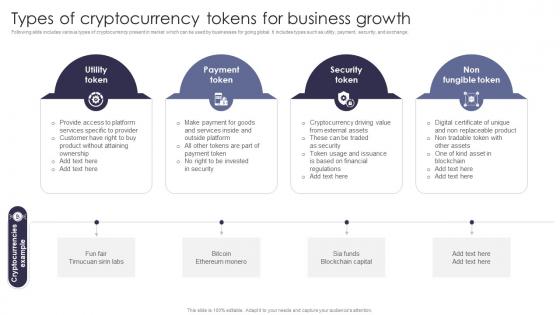 Types Of Cryptocurrency Comprehensive Guide Of Cashless Payment Methods
Types Of Cryptocurrency Comprehensive Guide Of Cashless Payment MethodsFollowing slide includes various types of cryptocurrency present in market which can be used by businesses for going global. It includes types such as utility, payment, security, and exchange. Increase audience engagement and knowledge by dispensing information using Types Of Cryptocurrency Comprehensive Guide Of Cashless Payment Methods. This template helps you present information on four stages. You can also present information on Utility Token, Payment Token, Security Token using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Qualitative Research Methods Icon For Product Promotion
Qualitative Research Methods Icon For Product PromotionPresenting our set of slides with Qualitative Research Methods Icon For Product Promotion. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Qualitative Research Methods, Product Promotion.
-
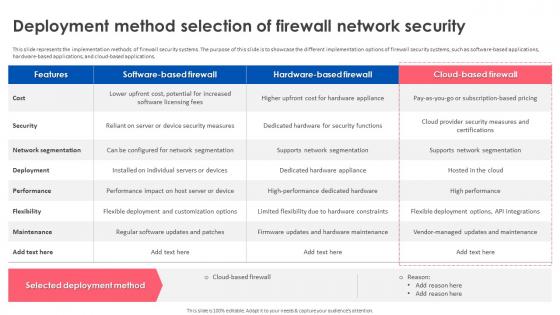 Firewall Implementation For Cyber Security Deployment Method Selection Of Firewall Network Security
Firewall Implementation For Cyber Security Deployment Method Selection Of Firewall Network SecurityThis slide represents the implementation methods of firewall security systems. The purpose of this slide is to showcase the different implementation options of firewall security systems, such as software-based applications, hardware-based applications, and cloud-based applications. Present the topic in a bit more detail with this Firewall Implementation For Cyber Security Deployment Method Selection Of Firewall Network Security. Use it as a tool for discussion and navigation on Network Segmentation, Supports Network Segmentation, Hardware For Security Functions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
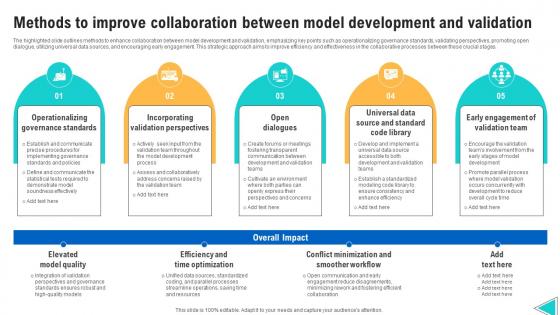 Methods To Improve Collaboration Between Model Development And Validation
Methods To Improve Collaboration Between Model Development And ValidationThe highlighted slide outlines methods to enhance collaboration between model development and validation, emphasizing key points such as operationalizing governance standards, validating perspectives, promoting open dialogue, utilizing universal data sources, and encouraging early engagement. This strategic approach aims to improve efficiency and effectiveness in the collaborative processes between these crucial stages. Introducing our premium set of slides with Methods To Improve Collaboration Between Model Development And Validation. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Operationalizing Governance Standards, Incorporating Validation Perspectives, Elevated Model Quality. So download instantly and tailor it with your information.
-
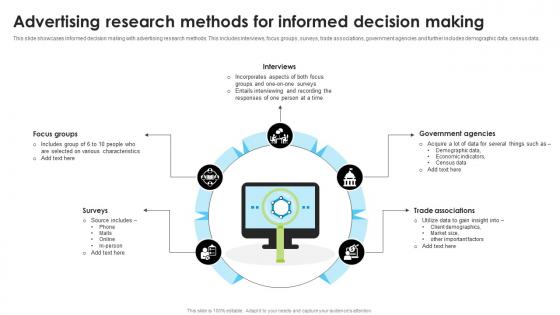 Advertising Research Methods For Informed Decision Making
Advertising Research Methods For Informed Decision MakingThis slide showcases informed decision making with advertising research methods. This includes interviews, focus groups, surveys, trade associations, government agencies and further includes demographic data, census data. Introducing our premium set of slides with name Advertising Research Methods For Informed Decision Making. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Government Agencies, Trade Associations, Focus Groups, Informed Decision Making. So download instantly and tailor it with your information.
-
 Identity Access Management User Verification Methods
Identity Access Management User Verification MethodsThe purpose of this slide is to highlight identity access management user authentication procedures including unique passwords, pre-shared key, biometrics, etc. Presenting our well structured Identity Access Management User Verification Methods. The topics discussed in this slide are Unique Passwords, Identity Access Management, User Verification Methods. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Identity Management Solutions To Reduce Dependency On Manual Methods
Identity Management Solutions To Reduce Dependency On Manual MethodsThe purpose of this slide is to showcase key solutions of identity management to minimize reliance on manual processes through identity flows, directory services etc. Presenting our set of slides with name Identity Management Solutions To Reduce Dependency On Manual Methods. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Lifecycle Management, Identity Flows, Directory Services.
-
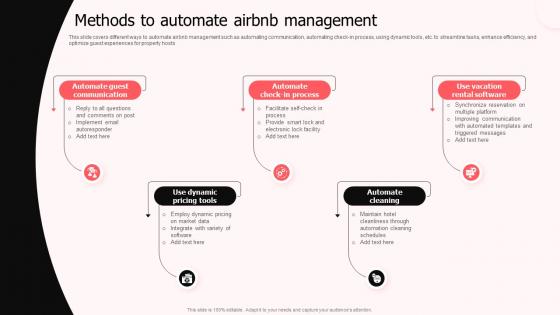 Methods To Automate Airbnb Management
Methods To Automate Airbnb ManagementThis slide covers different ways to automate airbnb management such as automating communication, automating check in process, using dynamic tools, etc. to streamline tasks, enhance efficiency, and optimize guest experiences for property hosts Introducing our premium set of slides with Methods To Automate Airbnb Management Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Automate Guest Communication, Use Dynamic Pricing Tools, Automate Cleaning So download instantly and tailor it with your information.
-
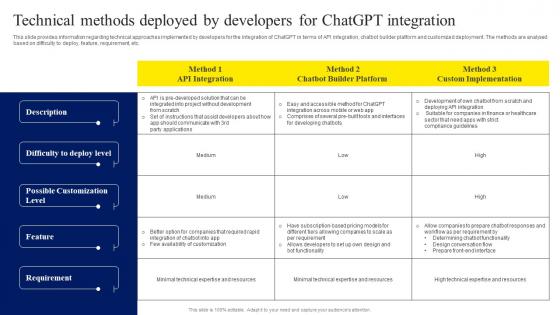 Technical Methods Deployed By Developers For ChatGPT OpenAI Conversation AI Chatbot ChatGPT CD V
Technical Methods Deployed By Developers For ChatGPT OpenAI Conversation AI Chatbot ChatGPT CD VThis slide provides information regarding technical approaches implemented by developers for the integration of ChatGPT in terms of API integration, chatbot builder platform and customized deployment. The methods are analysed based on difficulty to deploy, feature, requirement, etc. Deliver an outstanding presentation on the topic using this Technical Methods Deployed By Developers For ChatGPT OpenAI Conversation AI Chatbot ChatGPT CD V. Dispense information and present a thorough explanation of API Integration, Chatbot Builder Platform, Custom Implementation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
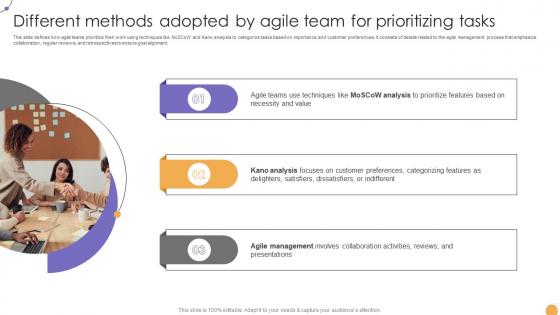 A155 Different Methods Adopted By Agile Responsive Change Management CM SS V
A155 Different Methods Adopted By Agile Responsive Change Management CM SS VThis slide defines how agile teams prioritize their work using techniques like MoSCoW and Kano analysis to categorize tasks based on importance and customer preferences. It consists of details related to the agile management process that emphasize collaboration, regular reviews, and retrospectives to ensure goal alignment. Introducing A155 Different Methods Adopted By Agile Responsive Change Management CM SS V to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Agile Teams Use Techniques, Kano Analysis, Agile Management, using this template. Grab it now to reap its full benefits.
-
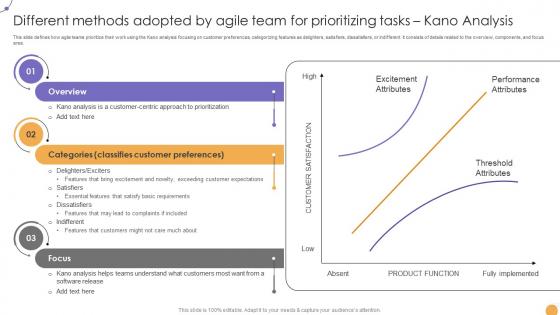 A156 Different Methods Adopted By Agile Team Responsive Change Management CM SS V
A156 Different Methods Adopted By Agile Team Responsive Change Management CM SS VThis slide defines how agile teams prioritize their work using the Kano analysis focusing on customer preferences, categorizing features as delighters, satisfiers, dissatisfiers, or indifferent. It consists of details related to the overview, components, and focus area. Increase audience engagement and knowledge by dispensing information using A156 Different Methods Adopted By Agile Team Responsive Change Management CM SS V. This template helps you present information on Three stages. You can also present information on Overview, Categories, Focus using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
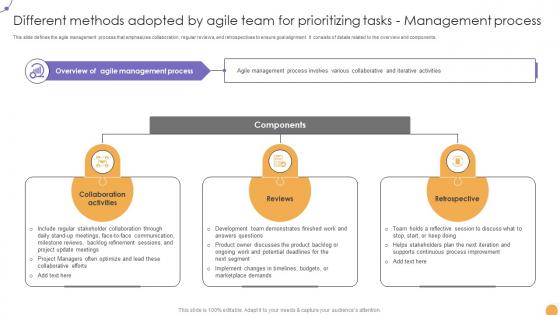 A157 Different Methods Adopted By Agile Team For Prioritizing Responsive Change Management CM SS V
A157 Different Methods Adopted By Agile Team For Prioritizing Responsive Change Management CM SS VThis slide defines the agile management process that emphasizes collaboration, regular reviews, and retrospectives to ensure goal alignment. It consists of details related to the overview and components. Introducing A157 Different Methods Adopted By Agile Team For Prioritizing Responsive Change Management CM SS V to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Collaboration Activities, Reviews, Retrospective, using this template. Grab it now to reap its full benefits.
-
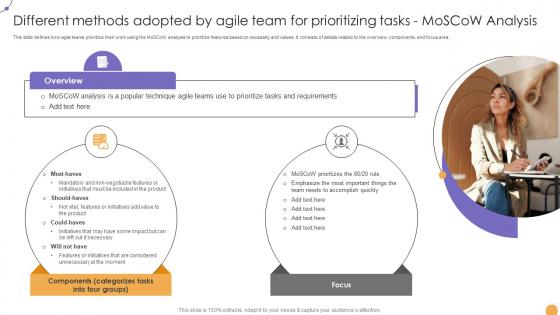 Responsive Change Management Different Methods Adopted By Agile Team CM SS V
Responsive Change Management Different Methods Adopted By Agile Team CM SS VThis slide defines how agile teams prioritize their work using the MoSCoW analysis to prioritize features based on necessity and values. It consists of details related to the overview, components, and focus area. Increase audience engagement and knowledge by dispensing information using Responsive Change Management Different Methods Adopted By Agile Team CM SS V. This template helps you present information on Two stages. You can also present information on Overview, Components, Focus using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.



