Powerpoint Templates and Google slides for Secured Identities
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Implementing Identity And Access Management For Operational Security OPSEC Training Ppt
Implementing Identity And Access Management For Operational Security OPSEC Training PptPresenting Implementing Identity and Access Management for Operational Security OPSEC. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Substantially Identical Securities In Powerpoint And Google Slides Cpb
Substantially Identical Securities In Powerpoint And Google Slides CpbPresenting our Substantially Identical Securities In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Substantially Identical Securities. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Effective GCP Identity And Security Services
Effective GCP Identity And Security ServicesThis slide exhibits the google cloud platform GCP security services which ensure and maintain the security of the infrastructure. It includes security tools such as cloud resource manager, cloud IAM, cloud security scanner, and stack driver logging. Introducing our premium set of slides with Effective GCP Identity And Security Services. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Manager, Security, Scanner. So download instantly and tailor it with your information.
-
 GCP Identity And Security Services Icon
GCP Identity And Security Services IconIntroducing our GCP Identity And Security Services Icon set of slides. The topics discussed in these slides are Security, Services, Identity. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Security Identity Card Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Security Identity Card Colored Icon In Powerpoint Pptx Png And Editable Eps FormatA coloured powerpoint icon depicting an Identity Card. Perfect for presentations, documents, and websites. Can be used to represent identity, security, and access. Easy to customize and resize. Ideal for business, education, and personal use.
-
 Security Identity Card Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Security Identity Card Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon on Identity Card is a visual representation of a card, perfect for use in presentations related to identity, security, or access control. It is a simple, yet effective design that can easily be customized to fit your presentations theme.
-
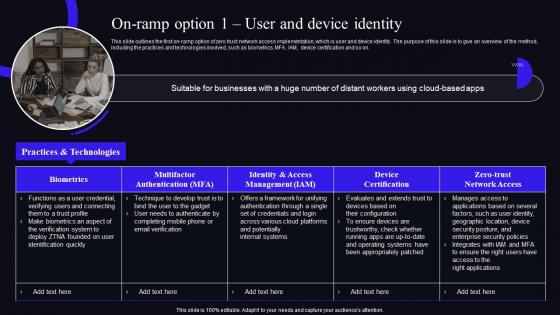 On Ramp Option 1 User And Device Identity Zero Trust Security Model
On Ramp Option 1 User And Device Identity Zero Trust Security ModelThis slide outlines the first on-ramp option of zero trust network access implementation, which is user and device identity. The purpose of this slide is to give an overview of the method, including the practices and technologies involved, such as biometrics, MFA, IAM, device certification and so on. Present the topic in a bit more detail with this On Ramp Option 1 User And Device Identity Zero Trust Security Model. Use it as a tool for discussion and navigation on Device Certification, Management, Multifactor Authentication. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
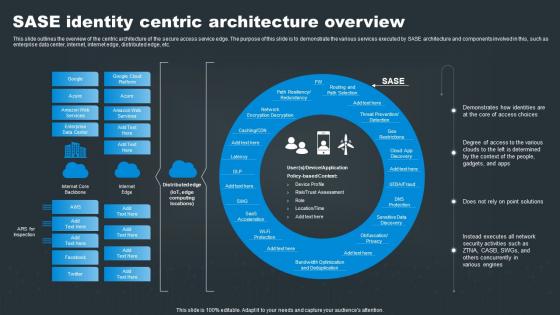 SASE Network Security SASE Identity Centric Architecture Overview
SASE Network Security SASE Identity Centric Architecture OverviewThis slide outlines the overview of the centric architecture of the secure access service edge. The purpose of this slide is to demonstrate the various services executed by SASE architecture and components involved in this, such as enterprise data center, internet, internet edge, distributed edge, etc. Present the topic in a bit more detail with this SASE Network Security SASE Identity Centric Architecture Overview. Use it as a tool for discussion and navigation on Identities, Solutions, Activities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
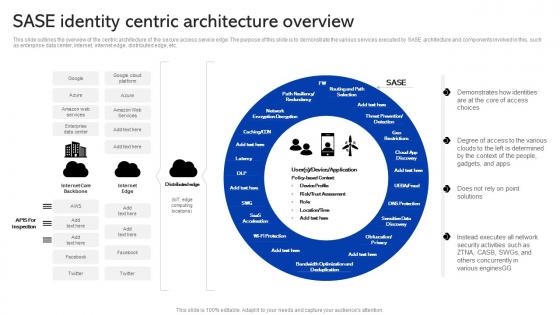 Sase Security Sase Identity Centric Architecture Overview
Sase Security Sase Identity Centric Architecture OverviewThis slide outlines the overview of the centric architecture of the secure access service edge. The purpose of this slide is to demonstrate the various services executed by SASE architecture and components involved in this, such as enterprise data center, internet, internet edge, distributed edge, etc. Deliver an outstanding presentation on the topic using this Sase Security Sase Identity Centric Architecture Overview. Dispense information and present a thorough explanation of Architecture, Overview, Concurrently using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
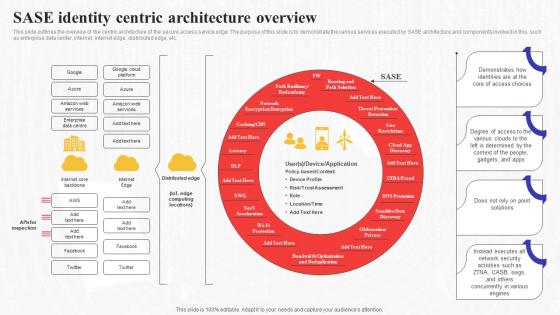 Sase Identity Centric Architecture Overview Secure Access Service Edge Sase
Sase Identity Centric Architecture Overview Secure Access Service Edge SaseThis slide outlines the overview of the centric architecture of the secure access service edge. The purpose of this slide is to demonstrate the various services executed by SASE architecture and components involved in this, such as enterprise data center, internet, internet edge, distributed edge, etc. Present the topic in a bit more detail with this Sase Identity Centric Architecture Overview Secure Access Service Edge Sase. Use it as a tool for discussion and navigation on Architecture, Overview, Demonstrates. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
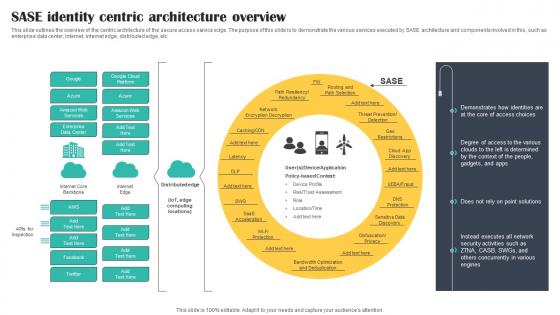 SASE Identity Centric Architecture Overview Cloud Security Model
SASE Identity Centric Architecture Overview Cloud Security ModelThis slide outlines the overview of the centric architecture of the secure access service edge. The purpose of this slide is to demonstrate the various services executed by SASE architecture and components involved in this, such as enterprise data center, internet, internet edge, distributed edge, etc. Deliver an outstanding presentation on the topic using this SASE Identity Centric Architecture Overview Cloud Security Model. Dispense information and present a thorough explanation of Identity, Architecture, Overview using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 IoT Device Identity Platform Implementation Internet Of Things IoT Security Cybersecurity SS
IoT Device Identity Platform Implementation Internet Of Things IoT Security Cybersecurity SSThis slide showcases internet of things IoT device identity platform deployment, referable for businesses in developing mitigation process. It provides details about APIs, architecture, device client, etc. Deliver an outstanding presentation on the topic using this IoT Device Identity Platform Implementation Internet Of Things IoT Security Cybersecurity SS. Dispense information and present a thorough explanation of IoT Device, Platform Deployment, Developing Mitigation Process using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
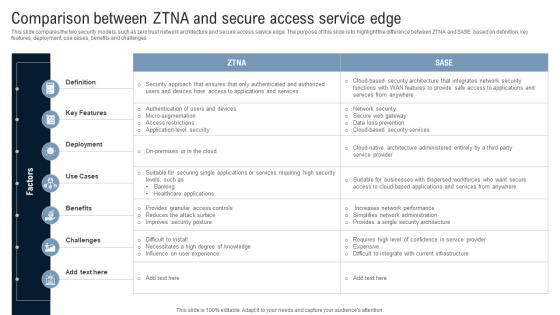 Comparison Between ZTNA And Secure Access Service Edge Identity Defined Networking
Comparison Between ZTNA And Secure Access Service Edge Identity Defined NetworkingThis slide compares the two security models, such as zero trust network architecture and secure access service edge. The purpose of this slide is to highlight the difference between ZTNA and SASE based on definition, key features, deployment, use cases, benefits and challenges. Present the topic in a bit more detail with this Comparison Between ZTNA And Secure Access Service Edge Identity Defined Networking Use it as a tool for discussion and navigation on Key Features, Deployment, Benefits, Challenges This template is free to edit as deemed fit for your organization. Therefore download it now.
-
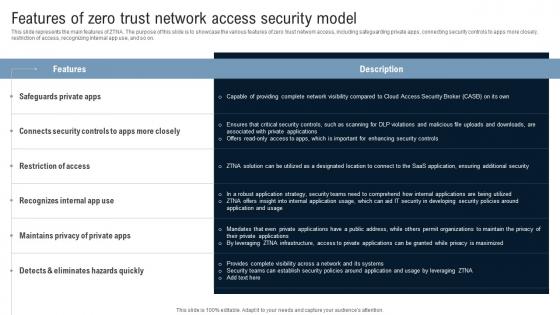 Features Of Zero Trust Network Access Security Model Identity Defined Networking
Features Of Zero Trust Network Access Security Model Identity Defined NetworkingThis slide represents the main features of ZTNA. The purpose of this slide is to showcase the various features of zero trust network access, including safeguarding private apps, connecting security controls to apps more closely, restriction of access, recognizing internal app use, and so on. Deliver an outstanding presentation on the topic using this Features Of Zero Trust Network Access Security Model Identity Defined Networking Dispense information and present a thorough explanation of Safeguards Private, Restriction Of Access, Hazards Quickly using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Role Of ZTNA To Improve Business Operations And Security Identity Defined Networking
Role Of ZTNA To Improve Business Operations And Security Identity Defined NetworkingThis slide talks about the ways in which ZTNA improves the business operations and security. The purpose of this slide is to showcase the various domains that zero trust network access improves, including increased user experience, remote workforce protection, improve data protection, and network visibility. Present the topic in a bit more detail with this Role Of ZTNA To Improve Business Operations And Security Identity Defined Networking. Use it as a tool for discussion and navigation on Traditional Method, Workforce Protection, Data Protection. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
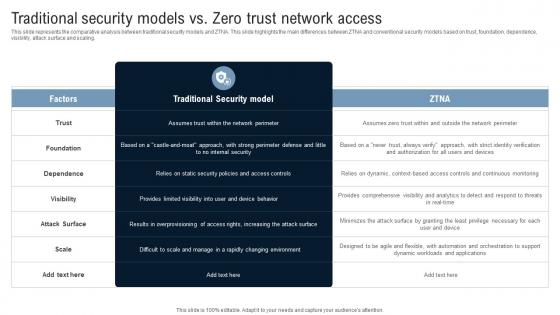 Traditional Security Models Vs Zero Trust Network Access Identity Defined Networking
Traditional Security Models Vs Zero Trust Network Access Identity Defined NetworkingThis slide represents the comparative analysis between traditional security models and ZTNA. This slide highlights the main differences between ZTNA and conventional security models based on trust, foundation, dependence, visibility, attack surface and scaling. Deliver an outstanding presentation on the topic using this Traditional Security Models Vs Zero Trust Network Access Identity Defined Networking Dispense information and present a thorough explanation of Traditional Security Model, Foundation, Dependence, Visibility using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Identity And Access Management Function As Security Tool IAM Process For Effective Access
Identity And Access Management Function As Security Tool IAM Process For Effective AccessThis slide showcases function of Identity and Access Management as a security tool. The purpose of this slide is to explain the function of IAM as an essential security tool these include context awareness, identity and access governance, and so on. Present the topic in a bit more detail with this Identity And Access Management Function As Security Tool IAM Process For Effective Access. Use it as a tool for discussion and navigation on Context Awareness, Identity And Access Governance, Management Function. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
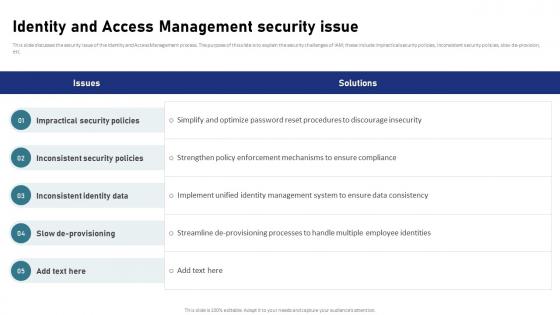 Identity And Access Management Security Issue IAM Process For Effective Access
Identity And Access Management Security Issue IAM Process For Effective AccessThis slide discusses the security issue of the Identity and Access Management process. The purpose of this slide is to explain the security challenges of IAM these include impractical security policies, inconsistent security policies, slow de-provision, etc. Deliver an outstanding presentation on the topic using this Identity And Access Management Security Issue IAM Process For Effective Access. Dispense information and present a thorough explanation of Impractical Security Policies, Inconsistent Security Policies, Inconsistent Identity Data using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security and identity powerpoint slides themes
Security and identity powerpoint slides themesPresenting security and identity powerpoint slides themes. This is a security and identity powerpoint slides themes. This is a four stage process. The stages in this process are database platform, data warehouse platform, security and identity, development.
-
 Google Cloud Services Identity And Security Ppt Powerpoint Presentation Professional Template
Google Cloud Services Identity And Security Ppt Powerpoint Presentation Professional TemplateThis slide describes the identity and security service of google cloud, and it includes cloud resource manager, cloud IAM, cloud security scanner, and cloud platform security. Increase audience engagement and knowledge by dispensing information using Google Cloud Services Identity And Security Ppt Powerpoint Presentation Professional Template. This template helps you present information on four stages. You can also present information on Cloud Resource Manager, Cloud Security Scanner, Cloud Platform Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
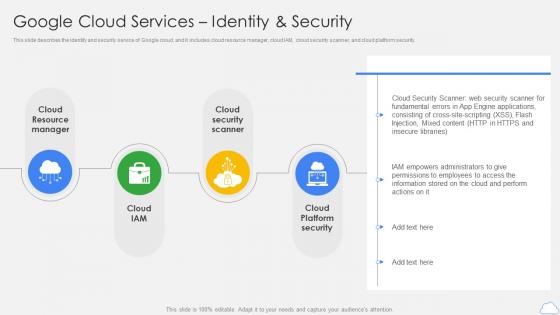 Google Cloud Services Identity And Security Google Cloud Platform Ppt Diagrams
Google Cloud Services Identity And Security Google Cloud Platform Ppt DiagramsThis slide describes the identity and security service of Google cloud, and it includes cloud resource manager, cloud IAM, cloud security scanner, and cloud platform security. Increase audience engagement and knowledge by dispensing information using Google Cloud Services Identity And Security Google Cloud Platform Ppt Diagrams. This template helps you present information on four stages. You can also present information on Cloud Resource Manager, Cloud Security Scanner, Cloud Platform Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
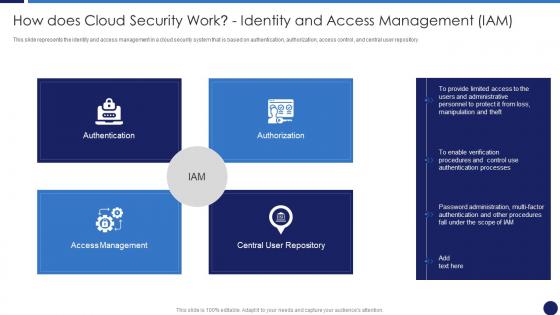 How Does Cloud Security Work Identity And Access Management Cloud Data Protection
How Does Cloud Security Work Identity And Access Management Cloud Data ProtectionThis slide represents the identity and access management in a cloud security system that is based on authentication, authorization, access control, and central user repository. Introducing How Does Cloud Security Work Identity And Access Management Cloud Data Protection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Access Management, Authentication, Authorization, Central User Repository, using this template. Grab it now to reap its full benefits.
-
 Pillars Of Cloud Security Identity Security Cloud Data Protection
Pillars Of Cloud Security Identity Security Cloud Data ProtectionThis slide depicts the identity security pillar of cloud security. It also shows how it could be beneficial to protect data from loss. Increase audience engagement and knowledge by dispensing information using Pillars Of Cloud Security Identity Security Cloud Data Protection. This template helps you present information on four stages. You can also present information on Pillars Of Cloud Security Identity Security using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
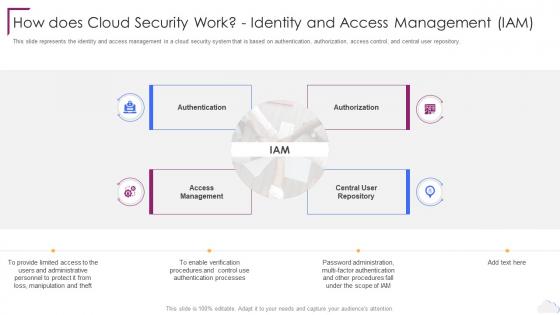 Cloud Computing Security How Does Cloud Security Work Identity And Access Management
Cloud Computing Security How Does Cloud Security Work Identity And Access ManagementThis slide represents the identity and access management in a cloud security system that is based on authentication, authorization, access control, and central user repository. Introducing Cloud Computing Security How Does Cloud Security Work Identity And Access Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Authentication, Authorization, Access Management, Central User Repository, using this template. Grab it now to reap its full benefits.
-
 Pillars Of Cloud Security Identity Security Cloud Computing Security
Pillars Of Cloud Security Identity Security Cloud Computing SecurityThis slide depicts the identity security pillar of cloud security. It also shows how it could be beneficial to protect data from loss. Increase audience engagement and knowledge by dispensing information using Pillars Of Cloud Security Identity Security Cloud Computing Security. This template helps you present information on four stages. You can also present information on Cloud Security, Identity Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
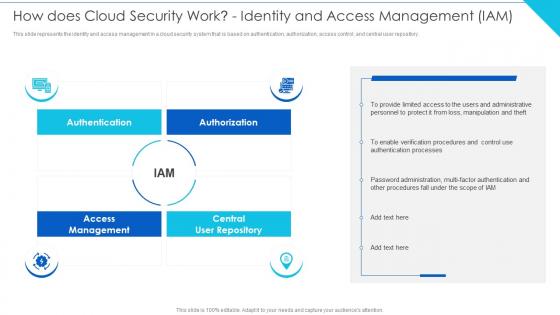 How Does Cloud Security Work Identity And IAM Cloud Information Security
How Does Cloud Security Work Identity And IAM Cloud Information SecurityThis slide represents the identity and access management in a cloud security system that is based on authentication, authorization, access control, and central user repository.Present the topic in a bit more detail with this How Does Cloud Security Work Identity And IAM Cloud Information Security Use it as a tool for discussion and navigation on Requirements, Transparency, Governance This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Pillars Of Cloud Security Identity Security Cloud Information Security
Pillars Of Cloud Security Identity Security Cloud Information SecurityThis slide depicts the identity security pillar of cloud security. It also shows how it could be beneficial to protect data from loss.Increase audience engagement and knowledge by dispensing information using Pillars Of Cloud Security Identity Security Cloud Information Security This template helps you present information on four stages. You can also present information on Controlled Operations, Vulnerability Management, Persistently Identify using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Google Cloud Services Identity And Security Services On Google Cloud Platform
Google Cloud Services Identity And Security Services On Google Cloud PlatformThis slide depicts the security services on the Google Cloud Platform. The purpose of this slide is to show the various security services available on the Google cloud platform. The main components include a cloud resource manager, cloud identity and access management, cloud security scanner, and cloud platform security. Introducing Google Cloud Services Identity And Security Services On Google Cloud Platform to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Cloud Resource Manager, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Policy Access Authorization Modification And Identity Access Management
Cyber Security Policy Access Authorization Modification And Identity Access ManagementThis slide represents the access authorization, modification, and identity access management based on polp, including the departments involved in creating this policy, such as HR and IT. Increase audience engagement and knowledge by dispensing information using Cyber Security Policy Access Authorization Modification And Identity Access Management. This template helps you present information on seven stages. You can also present information on Management, Authorization, Modification using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Bank Security Breached Icon Of Identity Fraud
Bank Security Breached Icon Of Identity FraudPresenting our well structured Bank Security Breached Icon Of Identity Fraud. The topics discussed in this slide are Bank Security, Breached Icon, Identity Fraud. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Set cross departmental standards manage identity management security
Set cross departmental standards manage identity management securityPresenting this set of slides with name - Set Cross Departmental Standards Manage Identity Management Security. This is an editable five stages graphic that deals with topics like Set Cross Departmental Standards, Manage Identity Management Security to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Secure network it infrastructure identity management common methodology
Secure network it infrastructure identity management common methodologyPresenting this set of slides with name - Secure Network It Infrastructure Identity Management Common Methodology. This is an editable two stages graphic that deals with topics like Secure Network It Infrastructure, Identity Management, Common Methodology to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Identity And Access Management Lifecycle In Cloud Security
Identity And Access Management Lifecycle In Cloud SecurityThis slide depicts access and identification management lifecycle in cloud computing systems. It provides information about user request, revoke access, approval, deletions, validations, etc. Presenting our set of slides with Identity And Access Management Lifecycle In Cloud Security. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identity And Access Management Lifecycle In Cloud Security.
-
 Identity info security powerpoint templates and powerpoint backgrounds 0211
Identity info security powerpoint templates and powerpoint backgrounds 0211Microsoft PowerPoint Template and Background with scaned hand for internet identity and security
-
 Digital identity security ppt powerpoint presentation outline example cpb
Digital identity security ppt powerpoint presentation outline example cpbPresenting this set of slides with name Digital Identity Security Ppt Powerpoint Presentation Outline Example Cpb. This is an editable Powerpoint one stages graphic that deals with topics like Digital Identity Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Security identity manager knowledge ppt powerpoint presentation background cpb
Security identity manager knowledge ppt powerpoint presentation background cpbPresenting this set of slides with name Security Identity Manager Knowledge Ppt Powerpoint Presentation Background Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Security Identity Manager Knowledge to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Identity based security access management ppt powerpoint presentation portfolio format cpb
Identity based security access management ppt powerpoint presentation portfolio format cpbPresenting this set of slides with name Identity Based Security Access Management Ppt Powerpoint Presentation Portfolio Format Cpb. This is an editable Powerpoint one stages graphic that deals with topics like Identity Based Security Access Management to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Information security identity access management ppt powerpoint presentation ideas guidelines cpb
Information security identity access management ppt powerpoint presentation ideas guidelines cpbPresenting this set of slides with name Information Security Identity Access Management Ppt Powerpoint Presentation Ideas Guidelines Cpb. This is an editable Powerpoint eight stages graphic that deals with topics like Information Security Identity Access Management to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Powerpoint template and background with identity information security
Powerpoint template and background with identity information securityBolster your presentation designs and make them impactful with our Powerpoint Template And Background With Identity Information Security. This cutting edge PPT will help you meet your audience expectations due to its interactive design. Useful content has been added to help you convey your ideas vision and principle aspects more proficiently. Throw light on what is important and take your presentation game a notch higher with this multipurpose design that comes with an assortment of features. No matter what is the purpose of your presentation conveying business ideas proposals analysis reports or any other you will find this creative design template perfect for all the scenarios. Also input any information and keep your audience hooked with this content ready template that is fully editable and customizable. Besides this you can represent large sets of complex data and information with this template design that can be adopted by any industry agency individual or group to deliver awe inspiring presentations.
-
 Hacker securing identity using vpn software to commit cyber crime
Hacker securing identity using vpn software to commit cyber crimePresenting this set of slides with name Hacker Securing Identity Using VPN Software To Commit Cyber Crime. This is a four stage process. The stages in this process are Hacker Securing Identity Using VPN Software To Commit Cyber Crime. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Powerpoint template and background with scanned hand for internet identity and security
Powerpoint template and background with scanned hand for internet identity and securityTemplates act as productivity boosters as they help in getting more work done in a lesser time frame. They are also great design frameworks with everything pre designed. This Powerpoint Template And Background With Scanned Hand For Internet Identity And Security is one such layout that can help you meet your goals and expectations in no time. It will provide you with great design elements that are suitable for any scenario consulting marketing sales personal agenda or any other. Not only this but this template layout will help you navigate the most important ideas and streamline your way of presenting. With everything pre laden and fully equipped this design is an absolute steal. The high resolution graphics and images used will empower your message and catch the audiences attention in minutes thereby helping you deliver inspiring presentations. The biggest advantage of this template is that it can be manipulated as per your business understanding. So feel free to adjust it to your terms and conditions once you click on the download button.
-
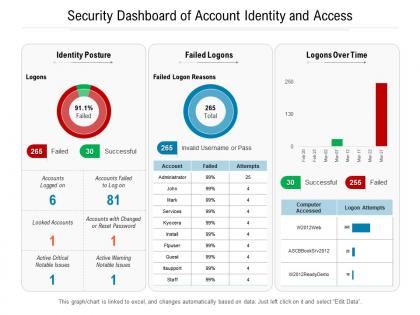 Security dashboard of account identity and access
Security dashboard of account identity and accessPresenting this set of slides with name Security Dashboard Of Account Identity And Access. The topics discussed in these slides are Security Dashboard Of Account Identity And Access. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Digital security with fingerprints across the internet our digital identity people template
Digital security with fingerprints across the internet our digital identity people templateBoost your presentation and its significance with this neatly presented Digital Security With Fingerprints Across The Internet Our Digital Identity People Template. This is a sharp professional presentation design that adheres to the standards of user friendliness and utility. It includes built in sections laden with content to help you portray important information with ease. Its versatility and flexibility is something that can help you take your presentation off the charts. Also an assortment of customizations that this layout responds to is noteworthy. Since it is a user friendly template it is suitable for any setting whether it is business academic or personal. With pre loaded graphics images content etc. it is very simple to use and include in your operations. Also presenting complex information and data in an easy to interpret format is one of the most notable features of this design that can be altered to fit your needs. Use it on multiple occasions as once downloaded this template can be saved for future portrayal.
-
 Secure identity access management system ppt powerpoint gallery cpb
Secure identity access management system ppt powerpoint gallery cpbPresenting this set of slides with name Secure Identity Access Management System Ppt Powerpoint Gallery Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Secure Identity Access Management System to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 An open door with hands holding guns surrounded by words like cyber crime stolen identity virus phishing security
An open door with hands holding guns surrounded by words like cyber crime stolen identity virus phishing securityTemplates act as productivity boosters as they help in getting more work done in a lesser time frame. They are also great design frameworks with everything pre designed. This An Open Door With Hands Holding Guns Surrounded By Words Like Cyber Crime Stolen Identity Virus Phishing Security is one such layout that can help you meet your goals and expectations in no time. It will provide you with great design elements that are suitable for any scenario consulting marketing sales personal agenda or any other. Not only this but this template layout will help you navigate the most important ideas and streamline your way of presenting. With everything pre laden and fully equipped this design is an absolute steal. The high resolution graphics and images used will empower your message and catch the audiences attention in minutes thereby helping you deliver inspiring presentations. The biggest advantage of this template is that it can be manipulated as per your business understanding. So feel free to adjust it to your terms and conditions once you click on the download button.
-
 Hand punching through the image identity theft security powerpoint template
Hand punching through the image identity theft security powerpoint templateEnhance your PowerPoint presentation and make them impressive with our Hand Punching Through The Image Identity Theft Security Powerpoint Template. Using this attention-grabbing PPT, you can leave a significant impact on your audience and convince them. This handy template is entirely editable and portrays your ideas comprehensively. With this illustrative slide, emphasize the critical points and make your presentation praiseworthy. The color palette used in this PPT turns your dull presentation into a vibrant and attractive one. By utilizing our Hand Punching Through The Image Identity Theft Security Powerpoint Template, you can engagingly describe the topic. Present your ideas, data insights, interpretation, analysis, and other crucial business information by using our professionally designed PPT. Showcase your skills and expertise in the domain of your choice with our visually appealing template which can be employed by any organization. Simply tweak this editable PPT and wow your audience. Take your presentation to the next level using this versatile PowerPoint theme which is equipped with attractive design elements.
-
 Identity based security ppt powerpoint presentation ideas designs cpb
Identity based security ppt powerpoint presentation ideas designs cpbPresenting Identity Based Security Ppt Powerpoint Presentation Ideas Designs Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Identity Based Security. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Hacker trying to steal secured digital identity
Hacker trying to steal secured digital identityIntroducing our premium set of slides with Hacker Trying To Steal Secured Digital Identity. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Hacker Trying To Steal Secured Digital Identity. So download instantly and tailor it with your information.
-
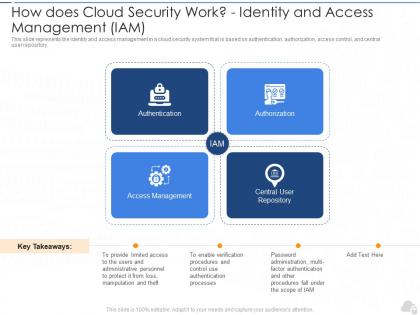 How does cloud security work identity and access management i am cloud security it
How does cloud security work identity and access management i am cloud security itThis slide represents the identity and access management in a cloud security system that is based on authentication, authorization, access control, and central user repository.Introducing How Does Cloud Security Work Identity And Access Management I am Cloud Security IT to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Authentication, Access Management, Central User Repository, using this template. Grab it now to reap its full benefits.
-
 Pillars of cloud security identity security cloud security it ppt formats
Pillars of cloud security identity security cloud security it ppt formatsThis slide depicts the identity security pillar of cloud security. It also shows how it could be beneficial to protect data from loss.Introducing Pillars Of Cloud Security Identity Security Cloud Security IT Ppt Formats to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Pillars Of Cloud Security Identity Security, using this template. Grab it now to reap its full benefits.
-
 Google cloud services identity and security google cloud it ppt topics
Google cloud services identity and security google cloud it ppt topicsThis slide describes the identity and security service of Google cloud, and it includes cloud resource manager, cloud IAM, cloud security scanner and cloud platform security. Increase audience engagement and knowledge by dispensing information using Google Cloud Services Identity And Security Google Cloud IT Ppt Topics. This template helps you present information on four stages. You can also present information on Cloud Platform Security, Cloud Resource Manager, Cloud Security Scanner using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations.
-
 Identity And Access Management Security Trends
Identity And Access Management Security TrendsThis slide showcases emerging trends in IAM shaping future of security such as cloud IAM, entitlement management and decentralized identity. Presenting our set of slides with name Identity And Access Management Security Trends. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Decentralized Identity, Entitlement Management, Management Security Trends.
-
 Identity Management In Cloud Security Icon
Identity Management In Cloud Security IconIntroducing our premium set of slides with name Identity Management In Cloud Security Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identity Management, Cloud Security Icon. So download instantly and tailor it with your information.

