Powerpoint Templates and Google slides for Secures Existing Data
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Mortgage Backed Securities Still Exist Powerpoint Presentation And Google Slides ICP
Mortgage Backed Securities Still Exist Powerpoint Presentation And Google Slides ICPReimagine your presentation with our adaptable Icon PowerPoint template, accessible in editable PPTx and customizable PNG formats. This deck is fully editable, allowing you to tailor it precisely to your message. Moreover, you have exclusive image rights, empowering you to use them as desired, all within the user-friendly framework of PowerPoint.
-
 Types Security Risk Assessments Exists In Powerpoint And Google Slides Cpb
Types Security Risk Assessments Exists In Powerpoint And Google Slides CpbPresenting our Types Security Risk Assessments Exists In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Types Security Risk Assessments Exists. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
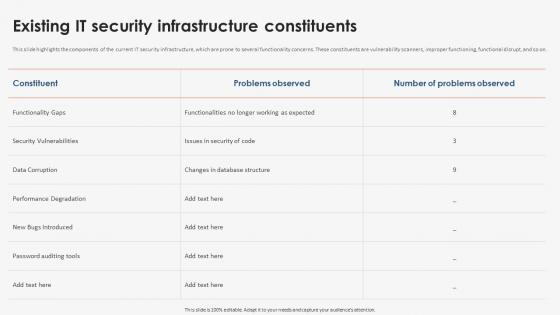 Existing IT Security Strategic Implementation Of Regression Testing
Existing IT Security Strategic Implementation Of Regression TestingThis slide highlights the components of the current IT security infrastructure, which are prone to several functionality concerns. These constituents are vulnerability scanners, improper functioning, functional disrupt, and so on. Deliver an outstanding presentation on the topic using this Existing IT Security Strategic Implementation Of Regression Testing. Dispense information and present a thorough explanation of Existing IT Security, Infrastructure Constituents using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
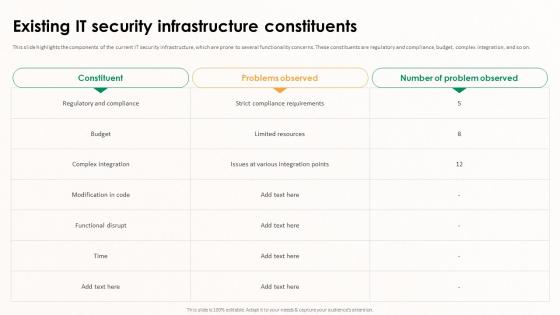 Implementing Effective Software Testing Existing IT Security Infrastructure Constituents
Implementing Effective Software Testing Existing IT Security Infrastructure ConstituentsThis slide highlights the components of the current IT security infrastructure, which are prone to several functionality concerns. These constituents are regulatory and compliance, budget, complex integration, and so on. Present the topic in a bit more detail with this Implementing Effective Software Testing Existing IT Security Infrastructure Constituents. Use it as a tool for discussion and navigation on Complex Integration, Strict Compliance Requirements, Functional Disrupt, IT Security Infrastructure Constituents. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Application Security Implementation Plan Existing IT Security Infrastructure Threats
Application Security Implementation Plan Existing IT Security Infrastructure ThreatsThis slide highlights the components of the current IT security infrastructure, which are prone to several functionality concerns. Deliver an outstanding presentation on the topic using this Application Security Implementation Plan Existing IT Security Infrastructure Threats. Dispense information and present a thorough explanation of Broken Authentication, Cross Site Scripting, Denial Of Service, Infrastructure Threats using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
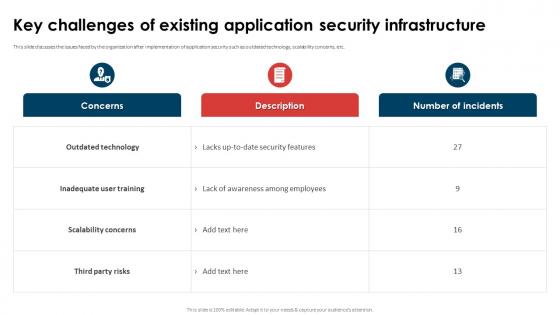 Application Security Implementation Plan Key Challenges Of Existing Application Security Infrastructure
Application Security Implementation Plan Key Challenges Of Existing Application Security InfrastructureThis slide discusses the issues faced by the organization after implementation of application security such as outdated technology, scalability concerns, etc. Deliver an outstanding presentation on the topic using this Application Security Implementation Plan Key Challenges Of Existing Application Security Infrastructure. Dispense information and present a thorough explanation of Inadequate User Training, Scalability Concerns, Outdated Technology using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Implementing Effective Tokenization Existing IT Security Infrastructure Threats
Implementing Effective Tokenization Existing IT Security Infrastructure ThreatsThis slide highlights the components of the current IT security infrastructure, which are prone to several functionality concerns. Present the topic in a bit more detail with this Implementing Effective Tokenization Existing IT Security Infrastructure Threats. Use it as a tool for discussion and navigation on Compliance Challenges, Resource Intensiveness, Faced Security Vulnerabilities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Existing Challenges In Finance And Banking Industry Lack Of Security BCT SS
Existing Challenges In Finance And Banking Industry Lack Of Security BCT SSThe following slide focusses on various security and transparency challenges faced by banking and finance companies. It includes elements such as data breaches, cyber-attacks, privacy issues, delay in identification of threats, etc. Increase audience engagement and knowledge by dispensing information using Existing Challenges In Finance And Banking Industry Lack Of Security BCT SS. This template helps you present information on four stages. You can also present information on Data Breaches, Privacy Issues, Delay Detection Of Issues using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
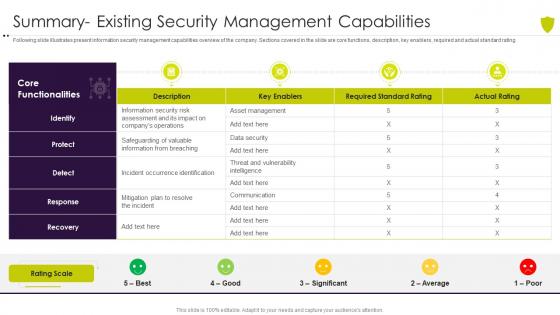 Summary existing security managing cyber risk in a digital age
Summary existing security managing cyber risk in a digital ageFollowing slide illustrates present information security management capabilities overview of the company. Sections covered in the slide are core functions, description, key enablers, required and actual standard rating. Present the topic in a bit more detail with this Summary Existing Security Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Summary Existing Security Management Capabilities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
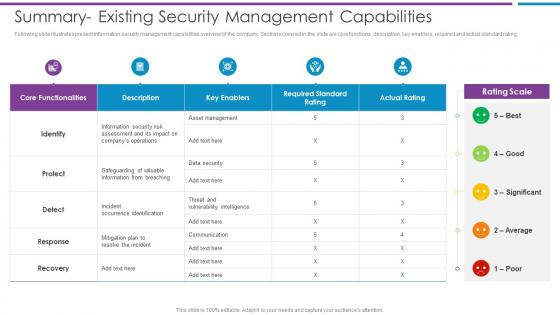 Summary Existing Security Management Capabilities Risk Based Methodology To Cyber
Summary Existing Security Management Capabilities Risk Based Methodology To CyberFollowing slide illustrates present information security management capabilities overview of the company. Sections covered in the slide are core functions, description, key enablers, required and actual standard rating.Deliver an outstanding presentation on the topic using this Summary Existing Security Management Capabilities Risk Based Methodology To Cyber Dispense information and present a thorough explanation of Information From Breaching, Occurrence Identification, Information Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
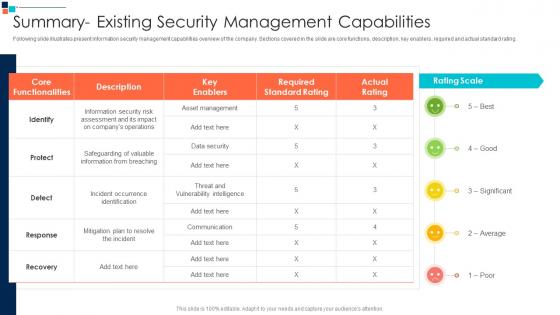 Summary Existing Security Management Capabilities Introducing A Risk Based
Summary Existing Security Management Capabilities Introducing A Risk BasedFollowing slide illustrates present information security management capabilities overview of the company. Sections covered in the slide are core functions, description, key enablers, required and actual standard rating.Deliver an outstanding presentation on the topic using this Summary Existing Security Management Capabilities Introducing A Risk Based Dispense information and present a thorough explanation of Incident Occurrence Identification, Safeguarding Of Valuable, Information From Breaching using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
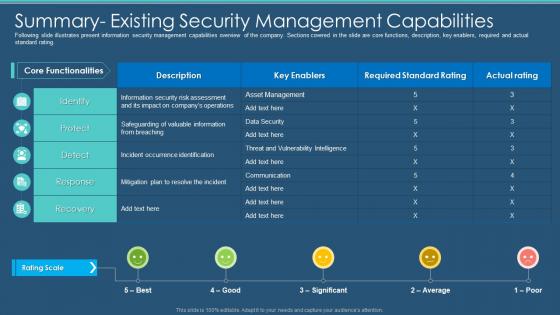 Information Program Cybersecurity Summary Existing Security Management Capabilities
Information Program Cybersecurity Summary Existing Security Management CapabilitiesFollowing slide illustrates present information security management capabilities overview of the company. Sections covered in the slide are core functions, description, key enablers, required and actual standard rating. Present the topic in a bit more detail with this Information Program Cybersecurity Summary Existing Security Management Capabilities. Use it as a tool for discussion and navigation on Management, Capabilities, Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
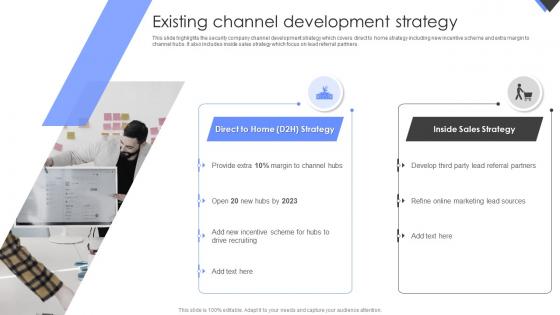 Existing Channel Development Strategy Wireless Home Security Systems Company Profile
Existing Channel Development Strategy Wireless Home Security Systems Company ProfileThis slide highlights the security company channel development strategy which covers direct to home strategy including new incentive scheme and extra margin to channel hubs. It also includes inside sales strategy which focus on lead referral partners. Introducing Existing Channel Development Strategy Wireless Home Security Systems Company Profile to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispense information on Direct To Home Strategy, Inside Sales Strategy, using this template. Grab it now to reap its full benefits.
-
 Existing Channel Development Strategy Home Security Systems Company Profile
Existing Channel Development Strategy Home Security Systems Company ProfileThis slide highlights the security company channel development strategy which covers direct to home strategy including new incentive scheme and extra margin to channel hubs. It also includes inside sales strategy which focus on lead referral partners. Present the topic in a bit more detail with this Existing Channel Development Strategy Home Security Systems Company Profile . Use it as a tool for discussion and navigation on Development, Strategy, Sources. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Existing Channel Development Strategy Smart Security Systems Company Profile Ppt Show Graphics Pictures
Existing Channel Development Strategy Smart Security Systems Company Profile Ppt Show Graphics PicturesThis slide highlights the security company channel development strategy which covers direct to home strategy including new incentive scheme and extra margin to channel hubs. It also includes inside sales strategy which focus on lead referral partners. Present the topic in a bit more detail with this Existing Channel Development Strategy Smart Security Systems Company Profile Ppt Show Graphics Pictures. Use it as a tool for discussion and navigation on Development, Strategy, Sources. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Existing Channel Development Strategy Security Alarm And Monitoring Systems Company Profile
Existing Channel Development Strategy Security Alarm And Monitoring Systems Company ProfileThis slide highlights the security company channel development strategy which covers direct to home strategy including new incentive scheme and extra margin to channel hubs. It also includes inside sales strategy which focus on lead referral partners. Present the topic in a bit more detail with this Existing Channel Development Strategy Security Alarm And Monitoring Systems Company Profile. Use it as a tool for discussion and navigation on Development, Strategy, Marketing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
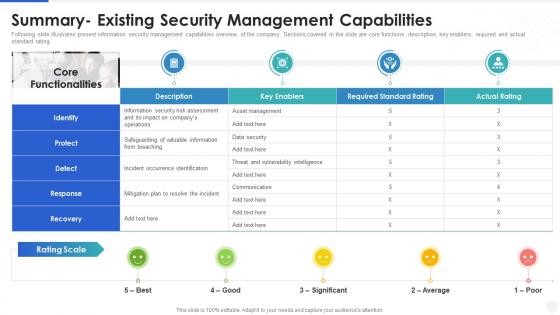 Cybersecurity and digital business risk management summary- existing security management
Cybersecurity and digital business risk management summary- existing security managementFollowing slide illustrates present information security management capabilities overview of the company. Sections covered in the slide are core functions, description, key enablers, required and actual standard rating. Deliver an outstanding presentation on the topic using this Cybersecurity And Digital Business Risk Management Summary- Existing Security Management. Dispense information and present a thorough explanation of Management, Information, Communication using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Secure video sharing platform investor funding elevator competitive landscape major players existing
Secure video sharing platform investor funding elevator competitive landscape major players existingThis slide caters details competitive landscape of various competitors existing in online video platform industry by comparing them on various parameters or features. Present the topic in a bit more detail with this Secure Video Sharing Platform Investor Funding Elevator Competitive Landscape Major Players Existing. Use it as a tool for discussion and navigation on Competitive, Landscape, Platform. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
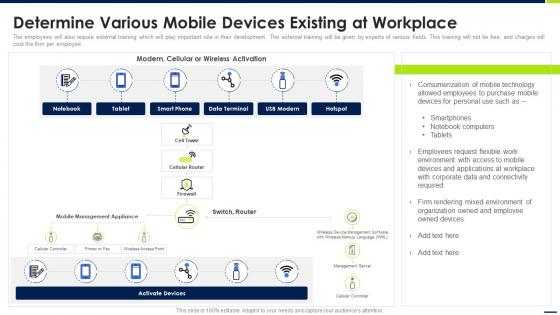 Android Device Security Management Determine Various Mobile Devices Existing At Workplace
Android Device Security Management Determine Various Mobile Devices Existing At WorkplaceThe employees will also require external training which will play important role in their development. The external training will be given by experts of various fields. This training will not be free, and charges will cost the firm per employee. Present the topic in a bit more detail with this Android Device Security Management Determine Various Mobile Devices Existing At Workplace. Use it as a tool for discussion and navigation on Activate Devices, Technology, Consumerization. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
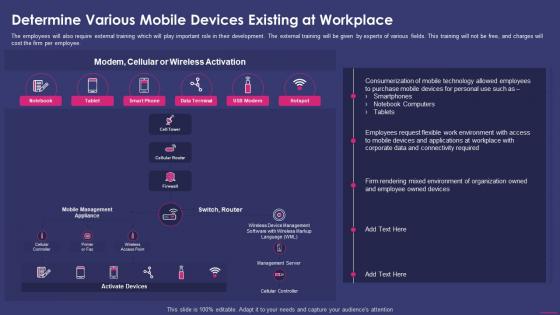 Determine Various Mobile Devices Existing At Workplace Enterprise Mobile Security For On Device
Determine Various Mobile Devices Existing At Workplace Enterprise Mobile Security For On DeviceThe employees will also require external training which will play important role in their development. The external training will be given by experts of various fields. This training will not be free, and charges will cost the firm per employee. Present the topic in a bit more detail with this Determine Various Mobile Devices Existing At Workplace Enterprise Mobile Security For On Device. Use it as a tool for discussion and navigation on Technology Allowed, Employees Request, Mixed Environment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Rivalry among existing firms threat substitute products software security touchpoints
Rivalry among existing firms threat substitute products software security touchpointsPresenting this set of slides with name - Rivalry Among Existing Firms Threat Substitute Products Software Security Touchpoints. This is an editable five stages graphic that deals with topics like Rivalry Among Existing Firms, Threat Substitute Products, Software Security Touchpoints to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 On premise e mail security existing system ppt powerpoint presentation design ideas
On premise e mail security existing system ppt powerpoint presentation design ideasThis slide displays the overview and key features of On Premise E Mail Security. Presenting this set of slides with name On Premise E Mail Security Existing System Ppt Powerpoint Presentation Design Ideas. This is a eight stage process. The stages in this process are On Premise, E Mail Security, Existing System. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.

