Powerpoint Templates and Google slides for Security Access Protection System For Cyber Threat
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Training Program For Cloud Access Security Broker Ppt Layouts Picture
Training Program For Cloud Access Security Broker Ppt Layouts PictureThis slide describes the training program for employees to implement cloud access security broke in an organization. The purpose of this slide is to highlight the training schedule for CASB deployment and the main components include agenda, system requirements, mode and cost of the training. Introducing Training Program For Cloud Access Security Broker Ppt Layouts Picture. to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Agenda, System Requirements, Mode, using this template. Grab it now to reap its full benefits.
-
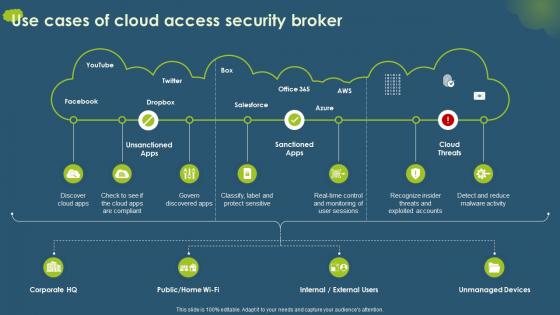 Use Cases Of Cloud Access Security Broker Ppt Ideas Influencers
Use Cases Of Cloud Access Security Broker Ppt Ideas InfluencersPresent the topic in a bit more detail with this Use Cases Of Cloud Access Security Broker Ppt Ideas Influencers. Use it as a tool for discussion and navigation on Unsanctioned Apps, Sanctioned Apps, Cloud Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
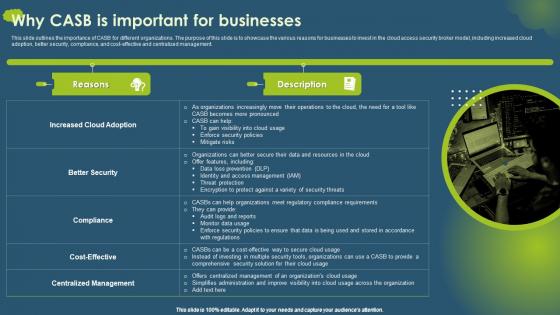 Why CASB Is Important For Businesses Cloud Access Security Broker CASB
Why CASB Is Important For Businesses Cloud Access Security Broker CASBThis slide outlines the importance of CASB for different organizations. The purpose of this slide is to showcase the various reasons for businesses to invest in the cloud access security broker model, including increased cloud adoption, better security, compliance, and cost effective and centralized management. Increase audience engagement and knowledge by dispensing information using Why CASB Is Important For Businesses Cloud Access Security Broker CASB. This template helps you present information on one stages. You can also present information on Reasons, Description, Increased Cloud Adoption using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 ZTNA Comparison Between ZTNA And Secure Access Service Edge
ZTNA Comparison Between ZTNA And Secure Access Service EdgeThis slide compares the two security models, such as zero trust network architecture and secure access service edge. The purpose of this slide is to highlight the difference between ZTNA and SASE based on definition, key features, deployment, use cases, benefits and challenges. Present the topic in a bit more detail with this ZTNA Comparison Between ZTNA And Secure Access Service Edge. Use it as a tool for discussion and navigation on Deployment, Benefits, Applications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 ZTNA Features Of Zero Trust Network Access Security Model
ZTNA Features Of Zero Trust Network Access Security ModelThis slide represents the main features of ZTNA. The purpose of this slide is to showcase the various features of zero trust network access, including safeguarding private apps, connecting security controls to apps more closely, restriction of access, recognizing internal app use, and so on. Deliver an outstanding presentation on the topic using this ZTNA Features Of Zero Trust Network Access Security Model. Dispense information and present a thorough explanation of Security Controls, Location, Network Visibility using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 ZTNA Traditional Security Models Vs Zero Trust Network Access
ZTNA Traditional Security Models Vs Zero Trust Network AccessThis slide represents the comparative analysis between traditional security models and ZTNA. This slide highlights the main differences between ZTNA and conventional security models based on trust, foundation, dependence, visibility, attack surface and scaling. Deliver an outstanding presentation on the topic using this ZTNA Traditional Security Models Vs Zero Trust Network Access. Dispense information and present a thorough explanation of Traditional Security Model, Static Security, Changing Environment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Access Control Security Risks Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Access Control Security Risks Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis PowerPoint icon depicts a shield with a red warning sign, representing the security risks associated with digital data. It is a great visual aid for presentations on cyber security, risk management, and data protection.
-
 Access Control Security Risks Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Access Control Security Risks Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon on Security Risks is a great visual aid for presentations on cyber security and data protection. It features a silhouette of a person in a protective stance, illustrating the need to be aware of potential risks.
-
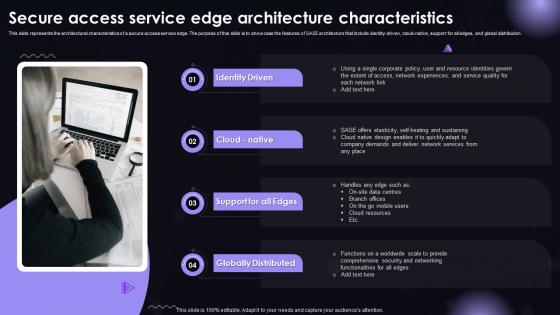 SASE IT Secure Access Service Edge Architecture Characteristics Ppt Powerpoint Background
SASE IT Secure Access Service Edge Architecture Characteristics Ppt Powerpoint BackgroundThis slide represents the architectural characteristics of a secure access service edge. The purpose of this slide is to showcase the features of SASE architecture that include identity-driven, cloud-native, support for all edges, and global distribution. Introducing SASE IT Secure Access Service Edge Architecture Characteristics Ppt Powerpoint Background to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Identity Driven, Cloud Native, Support For All Edges, Globally Distributed, using this template. Grab it now to reap its full benefits.
-
 SASE IT Secure Access Service Edge Implementation Steps Ppt Powerpoint Guidelines
SASE IT Secure Access Service Edge Implementation Steps Ppt Powerpoint GuidelinesThis slide outlines the steps to implement a secure service edge in a business. The purpose of this slide is to demonstrate the various guidelines to consider while implementing the SASE model in an organization. The main steps include defining SASE goals and requirements, selecting the SD-WAN backbone, incorporating zero-trust solutions, etc. Increase audience engagement and knowledge by dispensing information using SASE IT Secure Access Service Edge Implementation Steps Ppt Powerpoint Guidelines. This template helps you present information on five stages. You can also present information on SASE Goals And Requirements, Select SD-WAN Backbone, Incorporate Zero Trust Solutions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 SASE IT Secure Access Service Edge Importance Ppt Powerpoint Guidelines
SASE IT Secure Access Service Edge Importance Ppt Powerpoint GuidelinesThis slide represents the importance of secure access service edge. This slides purpose is to demonstrate why businesses need the SASE model. The main reasons include scaling with business needs, encouraging work from anywhere environment, standing up for cyber threats, and offering a base for IoT adoption. Introducing SASE IT Secure Access Service Edge Importance Ppt Powerpoint Guidelines to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Scales With Business, Encourage Work-From-Anywhere, Cyberthreat Evolution, using this template. Grab it now to reap its full benefits.
-
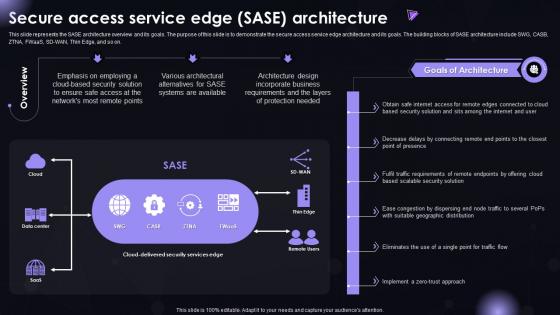 SASE IT Secure Access Service Edge SASE Architecture Ppt Powerpoint Information
SASE IT Secure Access Service Edge SASE Architecture Ppt Powerpoint InformationThis slide represents the SASE architecture overview and its goals. The purpose of this slide is to demonstrate the secure access service edge architecture and its goals. The building blocks of SASE architecture include SWG, CASB, ZTNA, FWaaS, SD-WAN, Thin Edge, and so on. Deliver an outstanding presentation on the topic using this SASE IT Secure Access Service Edge SASE Architecture Ppt Powerpoint Information. Dispense information and present a thorough explanation of Goals Of Architecture, Incorporate Business, Cloud-Based Security Solution using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 SASE IT Secure Access Service Edge Training Program Ppt Powerpoint Rules
SASE IT Secure Access Service Edge Training Program Ppt Powerpoint RulesThis slide represents the training program for the secure access service edge model. The purpose of this slide is to demonstrate the teams eligible for training, the modules to be covered during the training, the schedule and venue of the training. Present the topic in a bit more detail with this SASE IT Secure Access Service Edge Training Program Ppt Powerpoint Rules. Use it as a tool for discussion and navigation on Secure Access Service, Edge Training Program. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
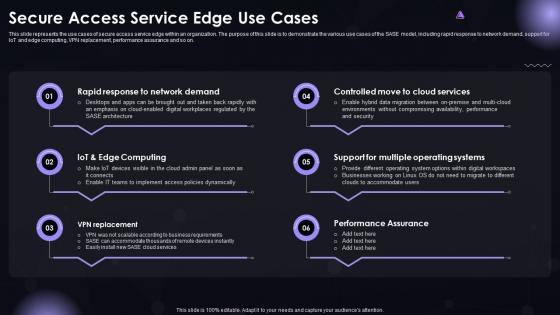 SASE IT Secure Access Service Edge Use Cases Ppt Powerpoint Summary
SASE IT Secure Access Service Edge Use Cases Ppt Powerpoint SummaryThis slide represents the use cases of secure access service edge within an organization. The purpose of this slide is to demonstrate the various use cases of the SASE model, including rapid response to network demand, support for IoT and edge computing, VPN replacement, performance assurance and so on. Increase audience engagement and knowledge by dispensing information using SASE IT Secure Access Service Edge Use Cases Ppt Powerpoint Summary. This template helps you present information on six stages. You can also present information on VPN Replacement, Performance Assurance, Support For Multiple Operating Systems, Controlled Move To Cloud Services using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
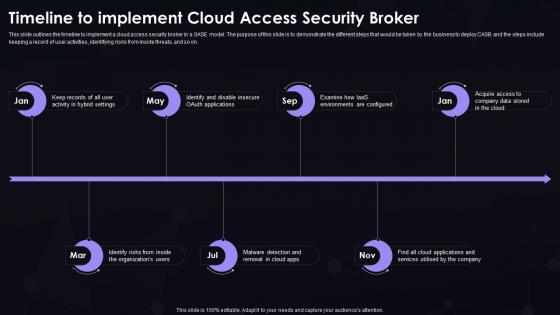 SASE IT Timeline To Implement Cloud Access Security Broker Ppt Powerpoint Portrait
SASE IT Timeline To Implement Cloud Access Security Broker Ppt Powerpoint PortraitThis slide outlines the timeline to implement a cloud access security broker in a SASE model. The purpose of this slide is to demonstrate the different steps that would be taken by the business to deploy CASB and the steps include keeping a record of user activities, identifying risks from inside threats, and so on. Increase audience engagement and knowledge by dispensing information using SASE IT Timeline To Implement Cloud Access Security Broker Ppt Powerpoint Portrait. This template helps you present information on seven stages. You can also present information on Hybrid Settings, Organizations Users, Cloud Apps using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 SASE IT Timeline To Implement Secure Access Service Edge Ppt Powerpoint Brochure
SASE IT Timeline To Implement Secure Access Service Edge Ppt Powerpoint BrochureThis slide outlines the timeline to implement secure access service edge in an organization. The purpose of this slide is to demonstrate all the steps to be taken in the SASE implementation process, covering defining SASE objectives and needs, examining the environment and discovering gaps, etc. Introducing SASE IT Timeline To Implement Secure Access Service Edge Ppt Powerpoint Brochure to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on SASE Objectives And Needs, SASE Providers And Solutions,Transition, Troubleshooting, And Assistance, using this template. Grab it now to reap its full benefits.
-
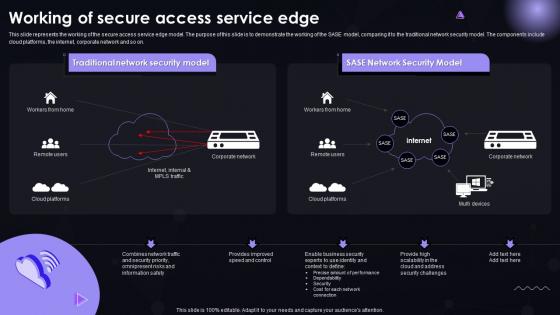 SASE IT Working Of Secure Access Service Edge Ppt Powerpoint Graphics
SASE IT Working Of Secure Access Service Edge Ppt Powerpoint GraphicsThis slide represents the working of the secure access service edge model. The purpose of this slide is to demonstrate the working of the SASE model, comparing it to the traditional network security model. The components include cloud platforms, the internet, corporate network and so on. Deliver an outstanding presentation on the topic using this SASE IT Working Of Secure Access Service Edge Ppt Powerpoint Graphics. Dispense information and present a thorough explanation of Traditional Network Security Model, SASE Network Security Model using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Access Control Policy Icon
Cyber Security Access Control Policy IconPresenting our set of slides with Cyber Security Access Control Policy Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Security, Access Control Policy Icon.
-
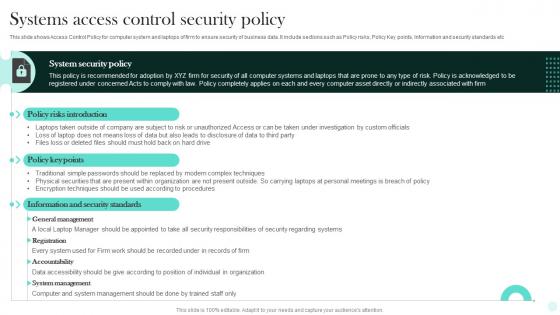 Systems Access Control Security Policy
Systems Access Control Security PolicyThis slide shows Access Control Policy for computer system and laptops of firm to ensure security of business data. It include sections such as Policy risks, Policy Key points, Information and security standards etc. Introducing our Systems Access Control Security Policy set of slides. The topics discussed in these slides are Systems, Security, Policy. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Unauthorized Computer Access Icon Causing Cyber Security Threat
Unauthorized Computer Access Icon Causing Cyber Security ThreatPresenting our set of slides with Unauthorized Computer Access Icon Causing Cyber Security Threat. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Unauthorized, Computer Access.
-
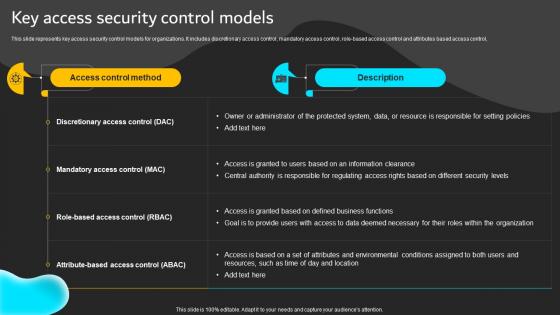 Key Access Security Control Models Implementation Of ICT Strategic Plan Strategy SS
Key Access Security Control Models Implementation Of ICT Strategic Plan Strategy SSThis slide represents key access security control models for organizations. It includes discretionary access control, mandatory access control, role based access control and attributes based access control.Deliver an outstanding presentation on the topic using this Key Access Security Control Models Implementation Of ICT Strategic Plan Strategy SS. Dispense information and present a thorough explanation of Discretionary Access, Mandatory Access, Access Granted using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
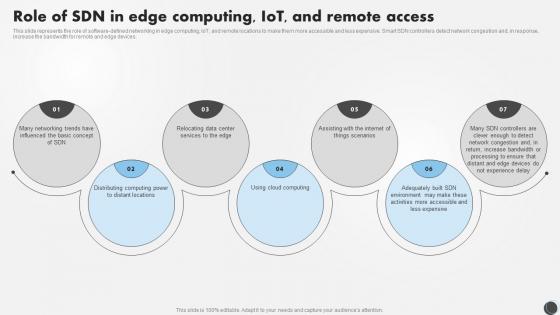 SDN Security IT Role Of SDN In Edge Computing IOT And Remote Access
SDN Security IT Role Of SDN In Edge Computing IOT And Remote AccessThis slide represents the role of software defined networking in edge computing, IoT, and remote locations to make them more accessible and less expensive. Smart SDN controllers detect network congestion and, in response, increase the bandwidth for remote and edge devices. Introducing SDN Security IT Role Of SDN In Edge Computing IOT And Remote Access to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Role, Computing, Remote, using this template. Grab it now to reap its full benefits.
-
 Access Control Security Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Access Control Security Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon depicts a shield with a checkmark, symbolizing that your account is safe and secure. It is perfect for presentations on security, privacy, and protection of data. The icon is bright and colourful, adding a modern touch to your slides.
-
 Access Control Security Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Access Control Security Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis monotone powerpoint icon is perfect for illustrating a secure and protected account. It features a padlock icon with a checkmark, indicating that the account is safe and secure. Use this icon to show that your account is safe and secure.
-
 Secure Cloud Access Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Secure Cloud Access Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured PowerPoint icon is perfect for presentations on cloud access. It features a cloud with an arrow pointing up, symbolizing the concept of accessing information from the cloud. It is bright and eye-catching, making it an ideal addition to any presentation.
-
 Secure Cloud Access Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Secure Cloud Access Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis monotone powerpoint icon is perfect for presentations about cloud access. It features a cloud with an arrow pointing up, symbolizing the ability to access the cloud. It is simple and modern, making it ideal for any presentation.
-
 Cloud Security Access Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Cloud Security Access Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured PowerPoint icon is perfect for presentations on cloud access. It features a cloud with an arrow pointing up, symbolizing the concept of accessing information from the cloud. It is bright and eye-catching, making it an ideal addition to any presentation.
-
 Cloud Security Access Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Cloud Security Access Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis monotone powerpoint icon is perfect for presentations about cloud access. It features a cloud with an arrow pointing up, symbolizing the ability to access the cloud. It is simple and modern, making it ideal for any presentation.
-
 Secure Cloud Access Data Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Secure Cloud Access Data Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis powerpoint icon is a colourful representation of secure cloud data, perfect for any presentation. It displays a cloud with a secure padlock, signifying the safety and security of the data stored within.
-
 Secure Cloud Access Data Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Secure Cloud Access Data Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone Powerpoint Icon is a perfect illustration for your presentation on secure cloud data. It is a simple yet powerful design that conveys the message of data security and trustworthiness. It is a great visual aid for any presentation on cloud security.
-
 WIFI Security Access Control Colored Icon In Powerpoint Pptx Png And Editable Eps Format
WIFI Security Access Control Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon is a visual representation of WIFI security. It features a shield with a lock to represent the protection of your WIFI network. It is a great visual aid for presentations on WIFI security and can be used to highlight the importance of keeping your network secure.
-
 WIFI Security Access Control Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
WIFI Security Access Control Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone powerpoint icon is perfect for illustrating the concept of WIFI Security. It features a simple, modern design that is sure to make your presentation stand out. It is perfect for any project related to WIFI Security, from educational materials to corporate presentations.
-
 Data Security Encryption Access Control Illustration
Data Security Encryption Access Control IllustrationThis coloured PowerPoint Illustration depicts a data security concept, with a padlock and a key to represent secure data protection. It is ideal for presentations on data protection, cyber security, and other related topics.
-
 Security Access Control Measures Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Security Access Control Measures Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon depicts a shield with a lock, representing security measures. Its perfect for presentations on data protection, cyber security, and other related topics. The icon is bright and vibrant, making it stand out and draw attention to your message.
-
 Security Access Control Measures Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Security Access Control Measures Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis monotone powerpoint icon is the perfect visual representation of security measures, providing a simple and effective way to communicate the importance of safety and security to any audience. It is an essential tool for any presentation on security topics.
-
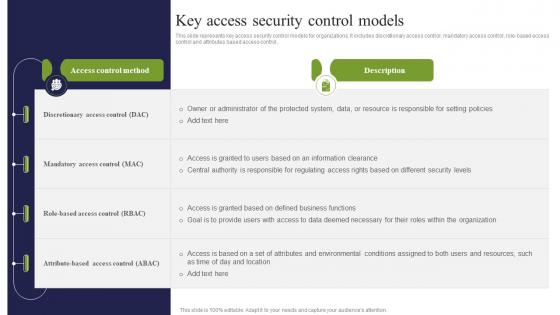 Key Access Security Control Models ICT Strategic Framework Strategy SS V
Key Access Security Control Models ICT Strategic Framework Strategy SS VThis slide represents key access security control models for organizations. It includes discretionary access control, mandatory access control, role based access control and attributes based access control, Present the topic in a bit more detail with this Key Access Security Control Models ICT Strategic Framework Strategy SS V. Use it as a tool for discussion and navigation on Discretionary Access, Mandatory Access, Role Based Access. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Mobile Access Control Security Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Mobile Access Control Security Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon will provide a visually engaging representation of Mobile Security. It is a great addition to any presentation and can be used to demonstrate the importance of mobile security and the various measures that can be taken to protect mobile devices.
-
 Mobile Access Control Security Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Mobile Access Control Security Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone Powerpoint Icon on Mobile Security is perfect for presentations on the importance of mobile security. It is a simple yet effective way to illustrate the need for secure mobile practices.
-
 Improved Access Control Security Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Improved Access Control Security Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured PowerPoint icon represents improved security. It features a padlock icon in a vibrant blue and green colour scheme, symbolising a secure and reliable system. Perfect for presentations on data protection and cyber security.
-
 Improved Access Control Security Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Improved Access Control Security Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon on Improved Security is perfect for presentations on data security. It features a shield with a lock, representing strong protection of sensitive information. Use this icon to illustrate the importance of secure data storage and transmission.
-
 Well Established Corporations Access Securities Markets In Powerpoint And Google Slides Cpb
Well Established Corporations Access Securities Markets In Powerpoint And Google Slides CpbPresenting our Well Established Corporations Access Securities Markets In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Well Established Corporations Access Securities Markets This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Three secured locks for secured internet access ppt slides
Three secured locks for secured internet access ppt slidesPresenting three secured locks for secured internet access ppt slides. This is a three secured locks for secured internet access ppt slides. This is a three stage process. The stages in this process are security.
-
 Access real time reporting secure company assets onboard manage
Access real time reporting secure company assets onboard managePresenting this set of slides with name - Access Real Time Reporting Secure Company Assets Onboard Manage. This is an editable four stages graphic that deals with topics like Access Real Time Reporting, Secure Company Assets, Onboard Manage to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Select full wipe security enforcement access control certificate management
Select full wipe security enforcement access control certificate managementPresenting this set of slides with name - Select Full Wipe Security Enforcement Access Control Certificate Management. This is an editable five stages graphic that deals with topics like Select Full Wipe, Security Enforcement, Access Control, Certificate Management to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Access rights key with five security access
Access rights key with five security accessPresenting this set of slides with name - Access Rights Key With Five Security Access. This is a one stage process. The stages in this process are Access Rights, Permission, Logins.
-
 Product type amount infosphere federation server security access
Product type amount infosphere federation server security accessPresenting this set of slides with name - Product Type Amount Infosphere Federation Server Security Access. This is an editable four stages graphic that deals with topics like Product Type Amount, Infosphere Federation Server, Security Access to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Security problems integrity problems difficulty accessing data concurrent access
Security problems integrity problems difficulty accessing data concurrent accessPresenting this set of slides with name - Security Problems Integrity Problems Difficulty Accessing Data Concurrent Access. This is an editable three stages graphic that deals with topics like Security Problems, Integrity Problems, Difficulty Accessing Data, Concurrent Access to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Risk factors showing innovation cyber security price capital access and productivity
Risk factors showing innovation cyber security price capital access and productivityPresenting this set of slides with name - Risk Factors Showing Innovation Cyber Security Price Capital Access And Productivity. This is a five stage process. The stages in this process are Risk Factors, Risk Management, Risk Variable.
-
 Server storage security applications enterprise portals data access
Server storage security applications enterprise portals data accessPresenting this set of slides with name - Server Storage Security Applications Enterprise Portals Data Access. This is an editable six stages graphic that deals with topics like Server Storage, Security Applications, Enterprise Portals, Data Access to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Ensure security and access controls establish a common vocabulary
Ensure security and access controls establish a common vocabularyPresenting this set of slides with name - Ensure Security And Access Controls Establish A Common Vocabulary. This is a two stage process. The stages in this process are Icons, Strategy, Business, Management, Marketing.
-
 Content management system with user friendly accessibility optimization and security
Content management system with user friendly accessibility optimization and securityPresenting this set of slides with name - Content Management System With User Friendly Accessibility Optimization And Security. This is a five stage process. The stages in this process are Content Management System, Cms.
-
 Identity And Access Management Lifecycle In Cloud Security
Identity And Access Management Lifecycle In Cloud SecurityThis slide depicts access and identification management lifecycle in cloud computing systems. It provides information about user request, revoke access, approval, deletions, validations, etc. Presenting our set of slides with Identity And Access Management Lifecycle In Cloud Security. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identity And Access Management Lifecycle In Cloud Security.
-
 Access to information security supplies tools ppt icons graphics
Access to information security supplies tools ppt icons graphicsPresenting access to information security supplies tools ppt icons graphics. This Power Point icon template diagram has been crafted with graphic of four technology icons. This icon template diagram contains the concept of access to information and security system service techniques. Use this icon template diagram for technology and data related presentations.
-
 Secure internet access security powerpoint templates ppt themes and graphics 0113
Secure internet access security powerpoint templates ppt themes and graphics 0113We are proud to present our secure internet access security powerpoint templates ppt themes and graphics 0113. Whatever the nuance you want to project. We have a security powerpoint templates that will get it across. Create a connection with your audience using our internet powerpoint templates. Transfer your depth of knowledge clearly across to them.
-
 Secure internet access computer powerpoint templates and powerpoint backgrounds 0811
Secure internet access computer powerpoint templates and powerpoint backgrounds 0811Microsoft PowerPoint Template and Background with transparent internet browser with a large chrome key protruding out from the window
-
 Security access management ppt powerpoint presentation inspiration background cpb
Security access management ppt powerpoint presentation inspiration background cpbPresenting this set of slides with name Security Access Management Ppt Powerpoint Presentation Inspiration Background Cpb. This is an editable Powerpoint one stages graphic that deals with topics like Security Access Management to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Icon for individual accessing secure portal
Icon for individual accessing secure portalPresenting this set of slides with name Icon For Individual Accessing Secure Portal. This is a four stage process. The stages in this process are Icon For Individual Accessing Secure Portal. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Access control security assessment ppt powerpoint presentation inspiration samples cpb
Access control security assessment ppt powerpoint presentation inspiration samples cpbPresenting this set of slides with name Access Control Security Assessment Ppt Powerpoint Presentation Inspiration Samples Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Access Control Security Assessment to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Privileged access security ppt powerpoint presentation professional samples cpb
Privileged access security ppt powerpoint presentation professional samples cpbPresenting this set of slides with name Privileged Access Security Ppt Powerpoint Presentation Professional Samples Cpb. This is an editable Powerpoint five stages graphic that deals with topics like Privileged Access Security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Identity based security access management ppt powerpoint presentation portfolio format cpb
Identity based security access management ppt powerpoint presentation portfolio format cpbPresenting this set of slides with name Identity Based Security Access Management Ppt Powerpoint Presentation Portfolio Format Cpb. This is an editable Powerpoint one stages graphic that deals with topics like Identity Based Security Access Management to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.



