Powerpoint Templates and Google slides for Security And Networking
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Privacy And Data Security As A Major Challenge To Metaverse Training Ppt
Privacy And Data Security As A Major Challenge To Metaverse Training PptPresenting Privacy and Data Security as a Major Challenge to Metaverse. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. All slides are customizable. You can add or delete the content as per your need. Download this professionally designed business presentation, add your content, and present it with confidence.
-
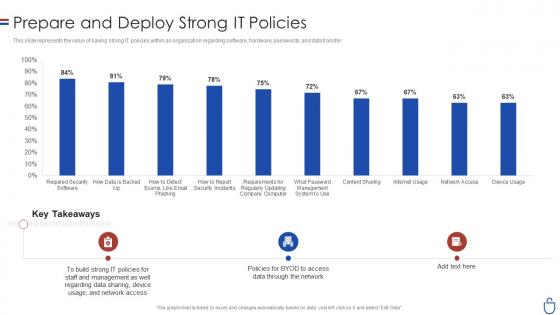 Data security it prepare and deploy strong it policies ppt slides deck
Data security it prepare and deploy strong it policies ppt slides deckThis slide represents the value of having strong IT policies within an organization regarding software, hardware, passwords, and data transfer. Present the topic in a bit more detail with this Data Security IT Prepare And Deploy Strong IT Policies Ppt Slides Deck. Use it as a tool for discussion and navigation on Build Strong, IT Policies, Required Security Software, Content Sharing, Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
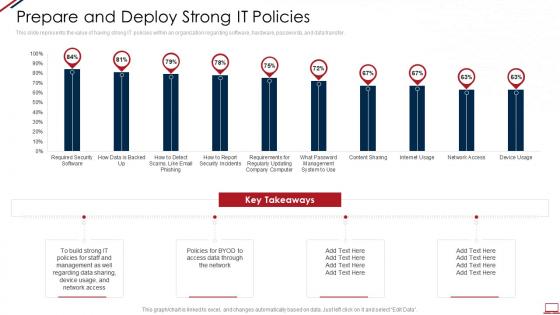 Computer system security prepare and deploy strong it policies
Computer system security prepare and deploy strong it policiesThis slide represents the value of having strong IT policies within an organization regarding software, hardware, passwords, and data transfer. Present the topic in a bit more detail with this Computer System Security Prepare And Deploy Strong It Policies. Use it as a tool for discussion and navigation on Prepare And Deploy Strong IT Policies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Computer system security update and installation of antivirus software
Computer system security update and installation of antivirus softwareThis slide depicts the benefits of using antivirus software in the organization, different antivirus software available in the market, and their usage by a graph. Present the topic in a bit more detail with this Computer System Security Update And Installation Of Antivirus Software. Use it as a tool for discussion and navigation on Update And Installation Of Antivirus Software. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
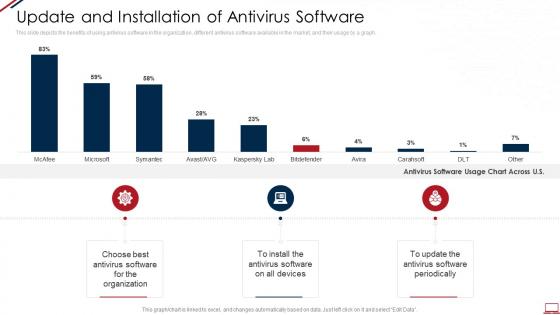
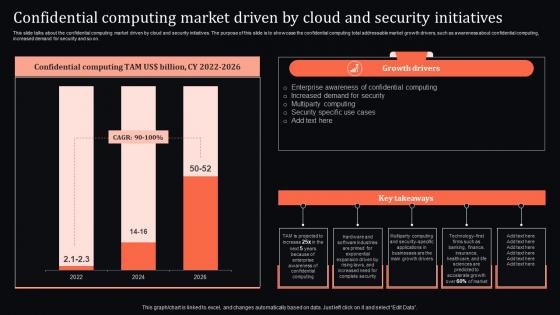 Confidential Driven By Cloud And Security Initiatives Confidential Computing System Technology
Confidential Driven By Cloud And Security Initiatives Confidential Computing System TechnologyThis slide talks about the confidential computing market driven by cloud and security initiatives. The purpose of this slide is to showcase the confidential computing total addressable market growth drivers, such as awareness about confidential computing, increased demand for security and so on. Deliver an outstanding presentation on the topic using this Confidential Driven By Cloud And Security Initiatives Confidential Computing System Technology. Dispense information and present a thorough explanation of Confidential, Enterprise, Awareness using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
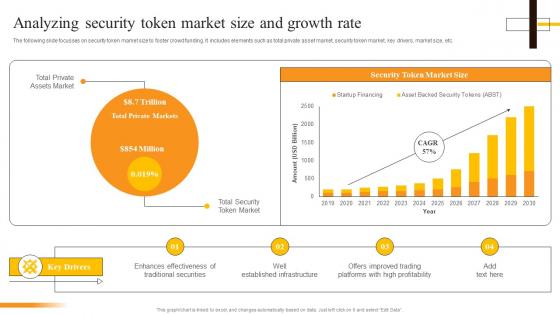 Analyzing Security Token Market Size And Growth Rate Security Token Offerings BCT SS
Analyzing Security Token Market Size And Growth Rate Security Token Offerings BCT SSThe following slide focusses on security token market size to foster crowd funding. It includes elements such as total private asset market, security token market, key drivers, market size, etc. Deliver an outstanding presentation on the topic using this Analyzing Security Token Market Size And Growth Rate Security Token Offerings BCT SS. Dispense information and present a thorough explanation of Security Token Market, Assets Market, Traditional Securities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
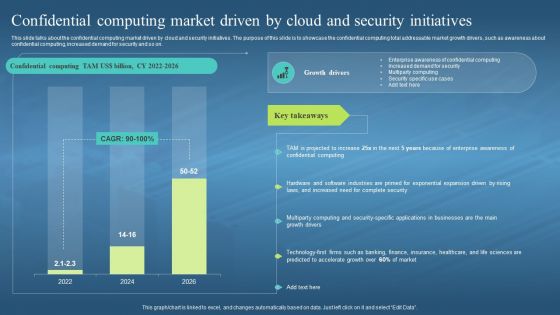 Confidential Computing Market Driven By Cloud And Security Confidential Computing Hardware
Confidential Computing Market Driven By Cloud And Security Confidential Computing HardwareThis slide talks about the confidential computing market driven by cloud and security initiatives. The purpose of this slide is to showcase the confidential computing total addressable market growth drivers, such as awareness about confidential computing, increased demand for security and so on. Deliver an outstanding presentation on the topic using this Confidential Computing Market Driven By Cloud And Security Confidential Computing Hardware. Dispense information and present a thorough explanation of Confidential Computing, Market Driven By Cloud, Security Initiatives, Awareness About Confidential Computing, Demand For Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
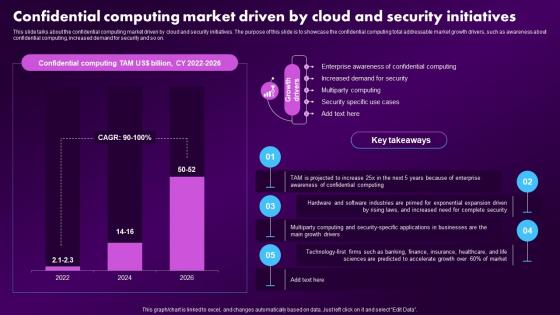 F1604 Confidential Computing Market Driven By Cloud And Security Confidential Computing Market
F1604 Confidential Computing Market Driven By Cloud And Security Confidential Computing MarketThis slide talks about the confidential computing market driven by cloud and security initiatives. The purpose of this slide is to showcase the confidential computing total addressable market growth drivers, such as awareness about confidential computing, increased demand for security and so on. Present the topic in a bit more detail with this F1604 Confidential Computing Market Driven By Cloud And Security Confidential Computing Market. Use it as a tool for discussion and navigation on Enterprise, Awareness, Confidential. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
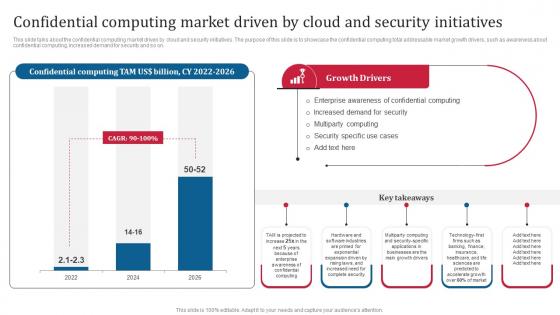 Confidential Computing Consortium Confidential Computing Market Driven By Cloud And Security
Confidential Computing Consortium Confidential Computing Market Driven By Cloud And SecurityThis slide talks about the confidential computing market driven by cloud and security initiatives. The purpose of this slide is to showcase the confidential computing total addressable market growth drivers, such as awareness about confidential computing, increased demand for security and so on. Present the topic in a bit more detail with this Confidential Computing Consortium Confidential Computing Market Driven By Cloud And Security. Use it as a tool for discussion and navigation on Confidential Computing, Market Driven By Cloud, Security Initiatives, Security Specific Use Cases. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
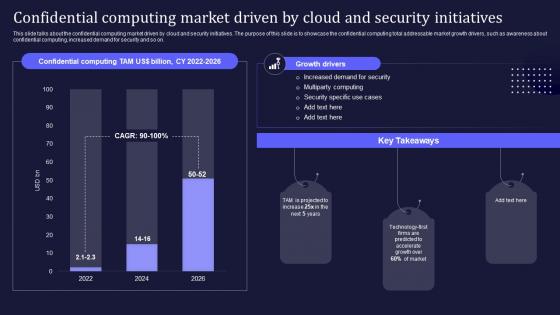 Confidential Computing V2 Market Driven By Cloud And Security Initiatives
Confidential Computing V2 Market Driven By Cloud And Security InitiativesThis slide talks about the confidential computing market driven by cloud and security initiatives. The purpose of this slide is to showcase the confidential computing total addressable market growth drivers, such as awareness about confidential computing, increased demand for security and so on. Deliver an outstanding presentation on the topic using this Confidential Computing V2 Market Driven By Cloud And Security Initiatives. Dispense information and present a thorough explanation of Confidential Computing Market, Cloud And Security Initiatives, Total Addressable Market using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
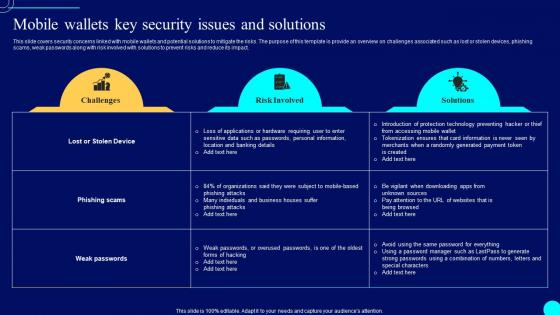 Mobile Wallets Key Security Comprehensive Guide To Blockchain Wallets And Applications BCT SS
Mobile Wallets Key Security Comprehensive Guide To Blockchain Wallets And Applications BCT SSThis slide covers security concerns linked with mobile wallets and potential solutions to mitigate the risks. The purpose of this template is provide an overview on challenges associated such as lost or stolen devices, phishing scams, weak passwords along with risk involved with solutions to prevent risks and reduce its impact. Deliver an outstanding presentation on the topic using this Mobile Wallets Key Security Comprehensive Guide To Blockchain Wallets And Applications BCT SS. Dispense information and present a thorough explanation of Solutions, Risk Involved, Security Issues using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
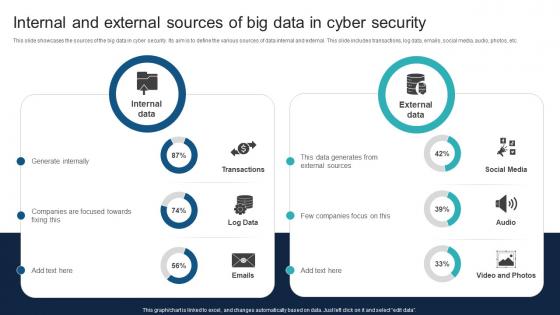 Internal And External Sources Of Big Data In Cyber Security
Internal And External Sources Of Big Data In Cyber SecurityThis slide showcases the sources of the big data in cyber security. Its aim is to define the various sources of data internal and external. This slide includes transactions, log data, emails, social media, audio, photos, etc. Introducing our Internal And External Sources Of Big Data In Cyber Security set of slides. The topics discussed in these slides are Generate, Focused, Companies. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
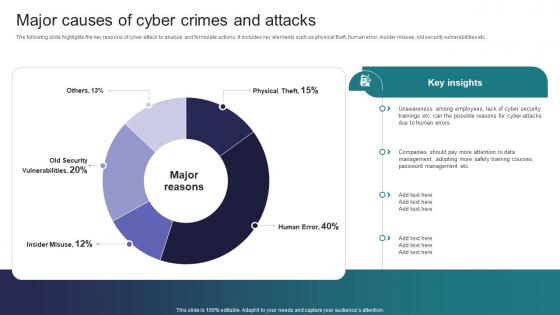 Major Causes Of Cyber Crimes And Attacks Implementing Strategies To Mitigate Cyber Security Threats
Major Causes Of Cyber Crimes And Attacks Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide highlights the key reasons of cyber attack to analyze and formulate actions. It includes key elements such as physical theft, human error, insider misuse, old security vulnerabilities etc. Deliver an outstanding presentation on the topic using this Major Causes Of Cyber Crimes And Attacks Implementing Strategies To Mitigate Cyber Security Threats Dispense information and present a thorough explanation of Employees, Management, Training Courses using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Impact Of Credit And Debit Payment On Business Enhancing Transaction Security With E Payment
Impact Of Credit And Debit Payment On Business Enhancing Transaction Security With E PaymentMentioned slide demonstrates impact of multiple card payment adoption on business growth. It includes key metrics such as business sales, customer satisfaction, convenience and expense tracking accuracy. Present the topic in a bit more detail with this Impact Of Credit And Debit Payment On Business Enhancing Transaction Security With E Payment Use it as a tool for discussion and navigation on Business Sales, Payment, Business This template is free to edit as deemed fit for your organization. Therefore download it now.
-
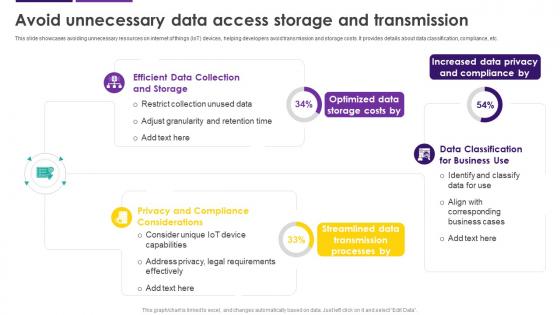 Avoid Unnecessary Data Access Storage And Transmission Internet Of Things IoT Security Cybersecurity SS
Avoid Unnecessary Data Access Storage And Transmission Internet Of Things IoT Security Cybersecurity SSThis slide showcases avoiding unnecessary resources on internet of things IoT devices, helping developers avoid transmission and storage costs. It provides details about data classification, compliance, etc. Deliver an outstanding presentation on the topic using this Avoid Unnecessary Data Access Storage And Transmission Internet Of Things IoT Security Cybersecurity SS. Dispense information and present a thorough explanation of Privacy And Compliance Considerations, Data Privacy And Compliance, Data Access Storage using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
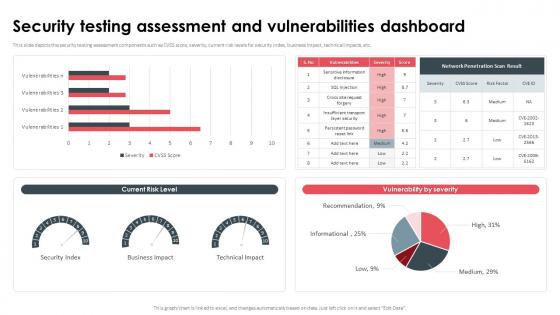 Security Testing Assessment And Vulnerabilities Dashboard
Security Testing Assessment And Vulnerabilities DashboardThis slide depicts the security testing assessment components such as CVSS score, severity, current risk levels for security index, business impact, technical impacts, etc. Present the topic in a bit more detail with this Security Testing Assessment And Vulnerabilities Dashboard. Use it as a tool for discussion and navigation on Security Testing Assessment, Vulnerabilities Dashboard, Business Impact, Technical Impacts. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
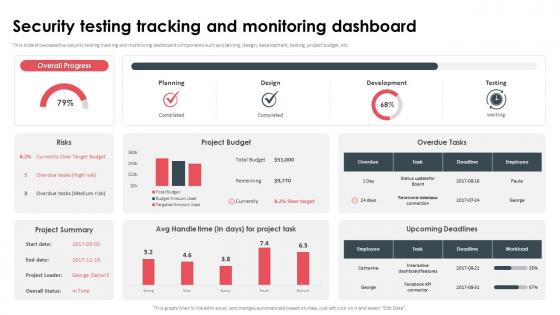 Security Testing Tracking And Monitoring Dashboard
Security Testing Tracking And Monitoring DashboardThis slide showcases the security testing tracking and monitoring dashboard components such as planning, design, development, testing, project budget, etc. Deliver an outstanding presentation on the topic using this Security Testing Implementation Training Program. Dispense information and present a thorough explanation of Security Testing Tracking, Monitoring Dashboard, Development, Testing, Project Budget using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
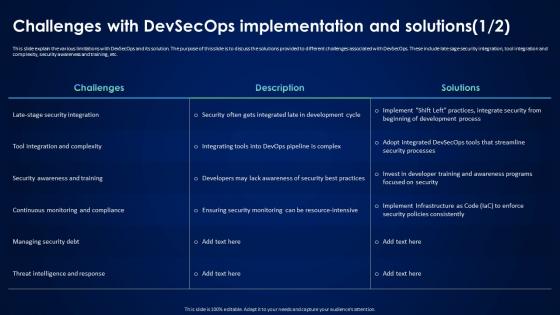 Devsecops Best Practices For Secure Challenges With Devsecops Implementation And Solutions
Devsecops Best Practices For Secure Challenges With Devsecops Implementation And SolutionsThis slide explain the various limitations with DevSecOps and its solution. The purpose of this slide is to discuss the solutions provided to different challenges associated with DevSecOps. These include late sage security integration, tool integration and complexity, security awareness and training, etc. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure Challenges With Devsecops Implementation And Solutions. Dispense information and present a thorough explanation of Security Awareness And Training, Continuous Monitoring And Compliance, Managing Security Debt using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
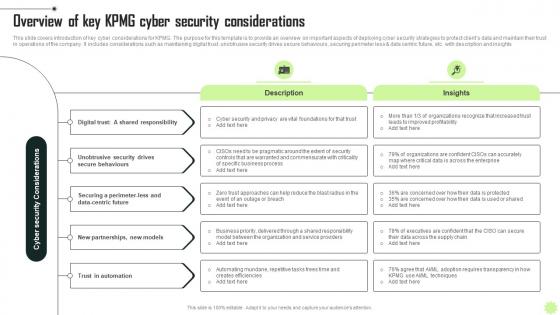 Overview Of Key KPMG Cyber Security KPMG Operational And Marketing Strategy SS V
Overview Of Key KPMG Cyber Security KPMG Operational And Marketing Strategy SS VThis slide covers introduction of key cyber considerations for KPMG. The purpose for this template is to provide an overview on important aspects of deploying cyber security strategies to protect clients data and maintain their trust in operations of the company. It includes considerations such as maintaining digital trust, unobtrusive security drives secure behaviours, securing perimeter less and data centric future, etc. with description and insights Increase audience engagement and knowledge by dispensing information using Overview Of Key KPMG Cyber Security KPMG Operational And Marketing Strategy SS V. This template helps you present information on five stages. You can also present information on Digital, Security, Automation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
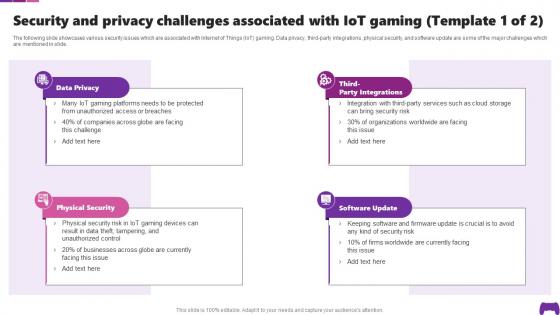 Security And Privacy Challenges Associated With IoT Transforming Future Of Gaming IoT SS
Security And Privacy Challenges Associated With IoT Transforming Future Of Gaming IoT SSThe following slide showcases various security issues which are associated with Internet of Things IoT gaming. Data privacy, third-party integrations, physical security, and software update are some of the major challenges which are mentioned in slide. Introducing Security And Privacy Challenges Associated With IoT Transforming Future Of Gaming IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Data Privacy, Physical Security, Software Update, using this template. Grab it now to reap its full benefits.
-
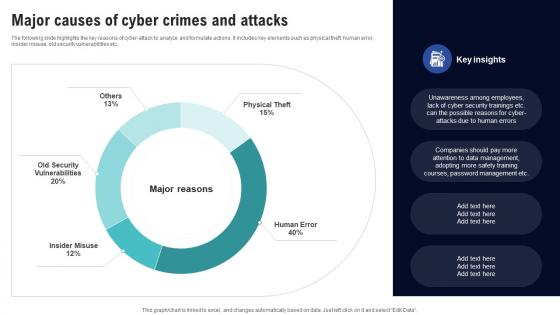 Major Causes Of Cyber Crimes And Attacks Creating Cyber Security Awareness
Major Causes Of Cyber Crimes And Attacks Creating Cyber Security AwarenessThe following slide highlights the key reasons of cyber-attack to analyze and formulate actions. It includes key elements such as physical theft, human error, insider misuse, old security vulnerabilities etc. Present the topic in a bit more detail with this Major Causes Of Cyber Crimes And Attacks Creating Cyber Security Awareness Use it as a tool for discussion and navigation on Mean Time To Detect, Mean Time To Resolve This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Ethical Hacking And Network Security Dashboard For Ethical Hacking
Ethical Hacking And Network Security Dashboard For Ethical HackingThis slide depicts the dashboard for ethical hacking by covering the details of top priorities issues, exposure time, problems discovered, and critical threat level. Present the topic in a bit more detail with this Ethical Hacking And Network Security Dashboard For Ethical Hacking. Use it as a tool for discussion and navigation on Dashboard For Ethical Hacking, Top Priorities Issues, Exposure Time, Problems Discovered, Critical Threat Level. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Ethical Hacking And Network Security Growth Of Ethical Hacking Profession
Ethical Hacking And Network Security Growth Of Ethical Hacking ProfessionThis slide represents the growth of the ethical hacking profession, including annual salary, hiring companies, and designation such as information security officer, computer forensics engineer, ethical hacker, and network security engineer. Deliver an outstanding presentation on the topic using this Ethical Hacking And Network Security Growth Of Ethical Hacking Profession. Dispense information and present a thorough explanation of Growth Of Ethical Hacking Profession, Computer Forensics Engineer, Ethical Hacker, Network Security Engineer using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
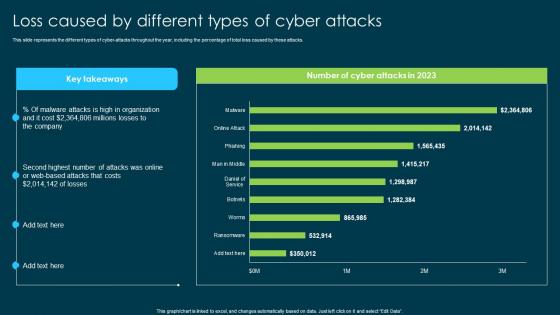 Ethical Hacking And Network Security Loss Caused By Different Types Of Cyber Attacks
Ethical Hacking And Network Security Loss Caused By Different Types Of Cyber AttacksThis slide represents the different types of cyber-attacks throughout the year, including the percentage of total loss caused by these attacks. Present the topic in a bit more detail with this Ethical Hacking And Network Security Loss Caused By Different Types Of Cyber Attacks. Use it as a tool for discussion and navigation on Cyber Attacks Throughout, Online Or Web Based Attacks, Malware Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
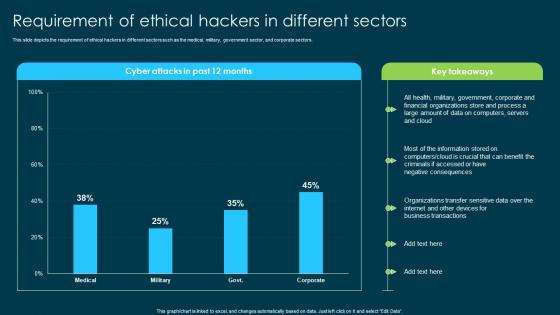 Ethical Hacking And Network Security Requirement Of Ethical Hackers In Different Sectors
Ethical Hacking And Network Security Requirement Of Ethical Hackers In Different SectorsThis slide depicts the requirement of ethical hackers in different sectors such as the medical, military, government sector, and corporate sectors. Present the topic in a bit more detail with this Ethical Hacking And Network Security Requirement Of Ethical Hackers In Different Sectors. Use it as a tool for discussion and navigation on Requirement Of Ethical Hackers, Military, Government Sector, Corporate Sectors. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
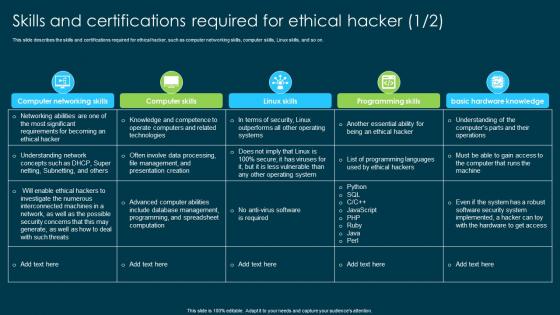 Ethical Hacking And Network Security Skills And Certifications Required For Ethical Hacker
Ethical Hacking And Network Security Skills And Certifications Required For Ethical HackerThis slide describes the skills and certifications required for ethical hacker, such as computer networking skills, computer skills, Linux skills, and so on. Deliver an outstanding presentation on the topic using this Ethical Hacking And Network Security Skills And Certifications Required For Ethical Hacker. Dispense information and present a thorough explanation of Skills And Certifications, Ethical Hacker, Computer Networking Skills, Computer Skills, Linux Skills using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
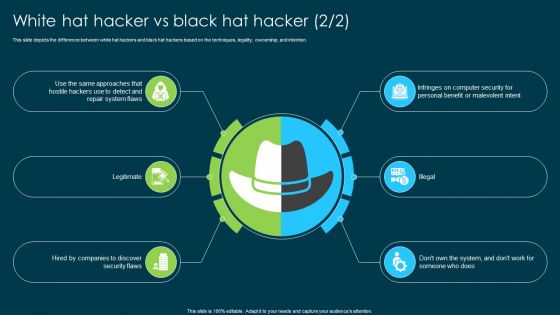 Ethical Hacking And Network Security White Hat Hacker Vs Black Hat Hacker
Ethical Hacking And Network Security White Hat Hacker Vs Black Hat HackerThis slide represents a comparison between white hat hackers and black hat hackers based on the factors such as legality, ownership, and motive. Deliver an outstanding presentation on the topic using this Ethical Hacking And Network Security White Hat Hacker Vs Black Hat Hacker. Dispense information and present a thorough explanation of Hacker Vs Black Hat Hacker, Legality, Ownership, Tactics And Methodologies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Table Of Contents For Ethical Hacking And Network Security Ppt Ideas Background Images
Table Of Contents For Ethical Hacking And Network Security Ppt Ideas Background ImagesIntroducing Table Of Contents For Ethical Hacking And Network Security Ppt Ideas Background Images to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Problems Ethical Hackers Can Solve, Ethical Hacking Training Program, Hacking And Ethical Hacking, Benefits And Limitations Of Ethical Hacking, using this template. Grab it now to reap its full benefits.
-
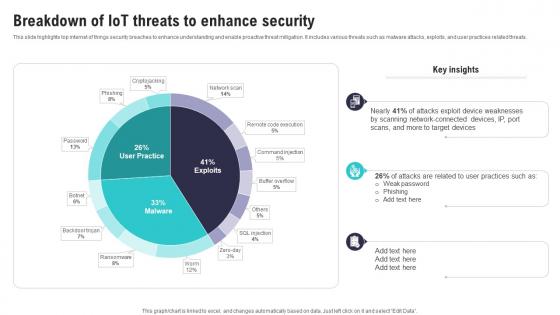 Breakdown Of IoT Threats To Enhance Security IoT Security And Privacy Safeguarding IoT SS
Breakdown Of IoT Threats To Enhance Security IoT Security And Privacy Safeguarding IoT SSThis slide highlights top internet of things security breaches to enhance understanding and enable proactive threat mitigation. It includes various threats such as malware attacks, exploits, and user practices related threats. Present the topic in a bit more detail with this Breakdown Of IoT Threats To Enhance Security IoT Security And Privacy Safeguarding IoT SS. Use it as a tool for discussion and navigation on Scanning Network Connected, Attacks Exploit, Device Weaknesses. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
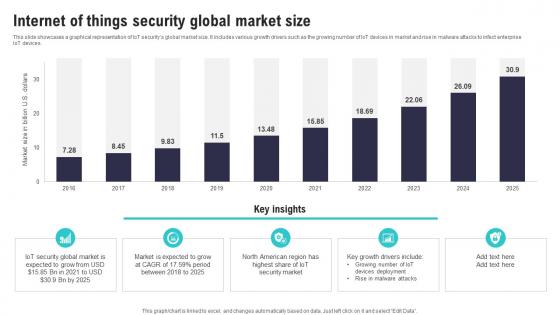 Internet Of Things Security Global Market Size IoT Security And Privacy Safeguarding IoT SS
Internet Of Things Security Global Market Size IoT Security And Privacy Safeguarding IoT SSThis slide showcases a graphical representation of IoT securitys global market size. It includes various growth drivers such as the growing number of IoT devices in market and rise in malware attacks to infect enterprise IoT devices.Deliver an outstanding presentation on the topic using this Internet Of Things Security Global Market Size IoT Security And Privacy Safeguarding IoT SS. Dispense information and present a thorough explanation of Security Global Market, American Region, Rise Malware Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
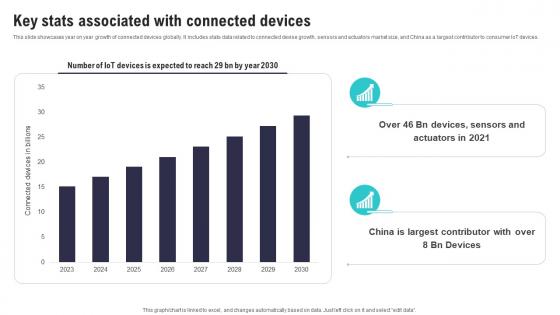 Key Stats Associated With Connected Devices IoT Security And Privacy Safeguarding IoT SS
Key Stats Associated With Connected Devices IoT Security And Privacy Safeguarding IoT SSThis slide showcases year on year growth of connected devices globally. It includes stats data related to connected devise growth, sensors and actuators market size, and China as a largest contributor to consumer IoT devices. Present the topic in a bit more detail with this Key Stats Associated With Connected Devices IoT Security And Privacy Safeguarding IoT SS. Use it as a tool for discussion and navigation on Largest Contributor, Associated Connected, Devices Expected. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Table Of Contents IoT Security And Privacy Safeguarding The Digital Ecosystem IoT SS
Table Of Contents IoT Security And Privacy Safeguarding The Digital Ecosystem IoT SSIncrease audience engagement and knowledge by dispensing information using Table Of Contents IoT Security And Privacy Safeguarding The Digital Ecosystem IoT SS. This template helps you present information on five stages. You can also present information on Introduction Iot Security, Need Iot, Security Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
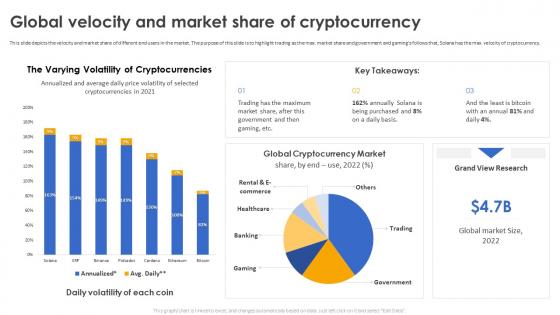 Secure Your Digital Assets Global Velocity And Market Share Of Cryptocurrency
Secure Your Digital Assets Global Velocity And Market Share Of CryptocurrencyThis slide depicts the velocity and market share of different end users in the market. The purpose of this slide is to highlight trading as the max. market share and government and gamings follows that, Solana has the max. velocity of cryptocurrency. Deliver an outstanding presentation on the topic using this Secure Your Digital Assets Global Velocity And Market Share Of Cryptocurrency. Dispense information and present a thorough explanation of Velocity And Market Share, Government And Gaming Follows, Solana Has The Max, Velocity Of Cryptocurrency using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
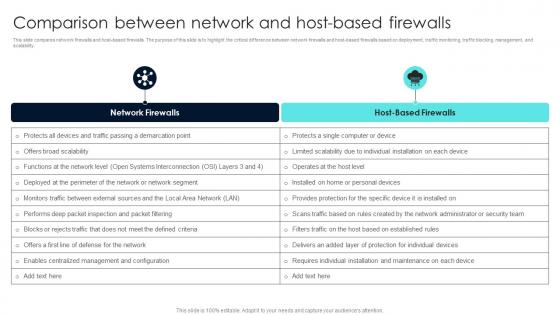 Firewall Network Security Comparison Between Network And Host Based Firewalls
Firewall Network Security Comparison Between Network And Host Based FirewallsThis slide compares network firewalls and host-based firewalls. The purpose of this slide is to highlight the critical difference between network firewalls and host-based firewalls based on deployment, traffic monitoring, traffic blocking, management, and scalability. Deliver an outstanding presentation on the topic using this Firewall Network Security Comparison Between Network And Host Based Firewalls Dispense information and present a thorough explanation of Network Firewalls, Host-Based Firewalls using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
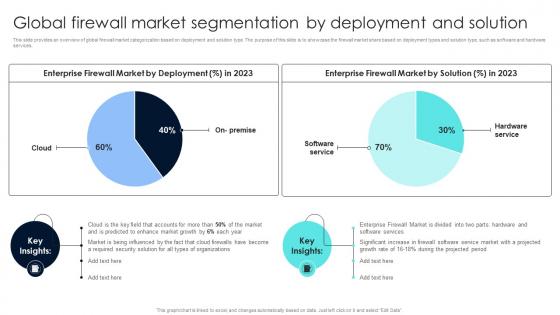 Firewall Network Security Global Firewall Market Segmentation By Deployment And Solution
Firewall Network Security Global Firewall Market Segmentation By Deployment And SolutionThis slide provides an overview of global firewall market categorization based on deployment and solution type. The purpose of this slide is to showcase the firewall market share based on deployment types and solution type, such as software and hardware services. Deliver an outstanding presentation on the topic using this Firewall Network Security Global Firewall Market Segmentation By Deployment And Solution Dispense information and present a thorough explanation of Oragnisation Size Segment Overview, Regional Analysis using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
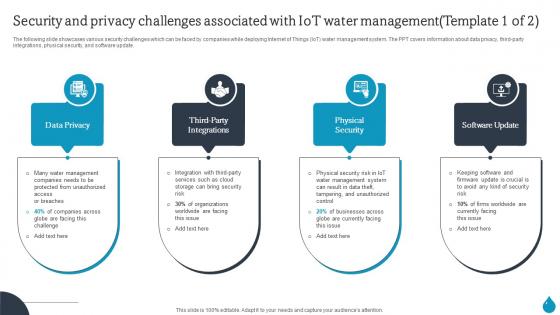 Smart Water Management Security And Privacy Challenges Associated With Iot Water Management IoT SS
Smart Water Management Security And Privacy Challenges Associated With Iot Water Management IoT SSThe following slide showcases various security challenges which can be faced by companies while deploying Internet of Things IoT water management system. The PPT covers information about data privacy, third-party integrations, physical security, and software update. Introducing Smart Water Management Security And Privacy Challenges Associated With Iot Water Management IoT SS to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Smart Water Management Key Benefits Of Using Iot In Water Management IoT SS using this template. Grab it now to reap its full benefits.
-
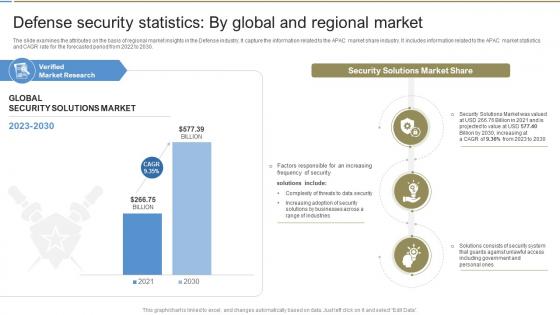 Defense Security Statistics By Global And Global Defense Industry Report IR SS
Defense Security Statistics By Global And Global Defense Industry Report IR SSThe slide examines the attributes on the basis of regional market insights in the Defense industry. It capture the information related to the APAC market share industry. It includes information related to the APAC market statistics and CAGR rate for the forecasted period from 2022 to 2030. Present the topic in a bit more detail with this Defense Security Statistics By Global And Global Defense Industry Report IR SS. Use it as a tool for discussion and navigation on Market Research, Security Solutions, Solutions Market. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
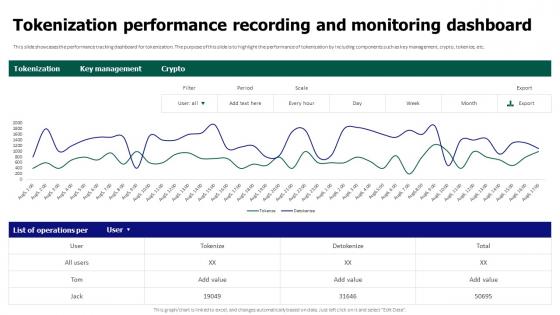 Tokenization For Improved Data Security Tokenization Performance Recording And Monitoring Dashboard
Tokenization For Improved Data Security Tokenization Performance Recording And Monitoring DashboardThis slide showcases the performance tracking dashboard for tokenization. The purpose of this slide is to highlight the performance of tokenization by including components such as key management, crypto, tokenize, etc. Present the topic in a bit more detail with this Tokenization For Improved Data Security Tokenization Performance Recording And Monitoring Dashboard. Use it as a tool for discussion and navigation on Tokenization Performance Recording, Monitoring Dashboard, Tracking Dashboard, Key Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Data security it update and installation of antivirus software
Data security it update and installation of antivirus softwareThis slide depicts the benefits of using antivirus software in the organization, different antivirus software available in the market, and their usage by a graph. Deliver an outstanding presentation on the topic using this Data Security IT Update And Installation Of Antivirus Software. Dispense information and present a thorough explanation of Organization, Antivirus Software using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Data security it what is data security and how does it work
Data security it what is data security and how does it workThis slide defines the meaning of data security and how it helps to prevent data through different methods and techniques. Introducing Data Security IT What Is Data Security And How Does IT Work to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Collective Methods, Protect Data, Computer Systems, Networks, Servers And Mobile Devices, using this template. Grab it now to reap its full benefits.
-
 Data security it minimize administrative and staff privileges
Data security it minimize administrative and staff privilegesThis slide shows the importance of minimizing the administrative and staff privilege by showing its benefits for the company. Introducing Data Security IT Minimize Administrative And Staff Privileges to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Employees, Cyber Attack, using this template. Grab it now to reap its full benefits.
-
 Computer system security dispose data and equipment properly
Computer system security dispose data and equipment properlyThis slide depicts the importance of disposal of the data and equipment that is not in use anymore and restricts the employees who already left the organization. Deliver an outstanding presentation on the topic using this Computer System Security Dispose Data And Equipment Properly. Dispense information and present a thorough explanation of Dispose Data And Equipment Properly using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Computer system security hardware and software update in company
Computer system security hardware and software update in companyThis slide depicts the hardware or software update measure under the cyber security model. It also tells the current status of the devices that need to update in the organization. Introducing Computer System Security Hardware And Software Update In Company to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Technology, Security, Servers, using this template. Grab it now to reap its full benefits.
-
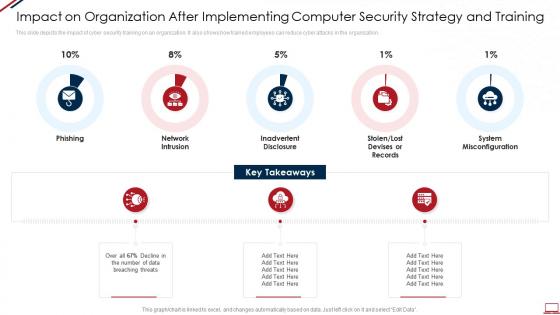 Computer system security impact on organization after implementing computer security strategy and training
Computer system security impact on organization after implementing computer security strategy and trainingThis slide depicts the impact of cyber security training on an organization. It also shows how trained employees can reduce cyber attacks in the organization. Increase audience engagement and knowledge by dispensing information using Computer System Security Impact On Organization After Implementing Computer Security Strategy And Training. This template helps you present information on five stages. You can also present information on Phishing, Network Intrusion, Inadvertent Disclosure, Stolen Or Lost Devises Or Records, System Misconfiguration using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Computer system security minimize administrative and staff privileges
Computer system security minimize administrative and staff privilegesThis slide shows the importance of minimizing the administrative and staff privilege by showing its benefits for the company. Introducing Computer System Security Minimize Administrative And Staff Privileges to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Minimize Administrative And Staff Privileges, using this template. Grab it now to reap its full benefits.
-
 Computer system security what is computer security and how does it work
Computer system security what is computer security and how does it workThis slide defines the meaning of cyber security and how it helps to prevent data through different methods and techniques. Introducing Computer System Security What Is Computer Security And How Does It Work to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Techniques, Collective, Networks, Computer Systems, using this template. Grab it now to reap its full benefits.
-
 Data security it dispose data and equipment properly
Data security it dispose data and equipment properlyThis slide depicts the importance of disposal of the data and equipment that is not in use anymore and restricts the employees who already left the organization. Increase audience engagement and knowledge by dispensing information using Data Security IT Dispose Data And Equipment Properly. This template helps you present information on three stages. You can also present information on Employees, Organization, Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Data security it hardware and software update in company
Data security it hardware and software update in companyThis slide depicts the hardware or software update measure under the cyber security model. It also tells the current status of the devices that need to update in the organization. Introducing Data Security IT Hardware And Software Update In Company to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Peripheral Devices, Technology, Computers And Servers, using this template. Grab it now to reap its full benefits.
-
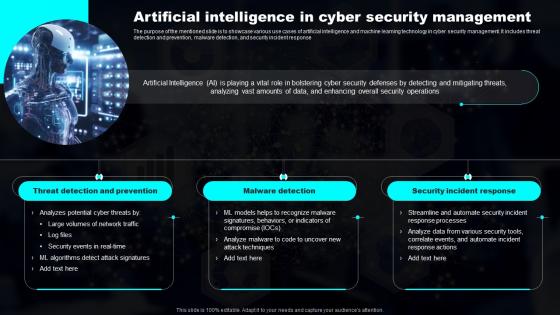 Artificial Intelligence In Cyber Security Transforming Industries With AI ML And NLP Strategy
Artificial Intelligence In Cyber Security Transforming Industries With AI ML And NLP StrategyThe purpose of the mentioned slide is to showcase various use cases of artificial intelligence and machine learning technology in cyber security management. It includes threat detection and prevention, malware detection, and security incident response Increase audience engagement and knowledge by dispensing information using Artificial Intelligence In Cyber Security Transforming Industries With AI ML And NLP Strategy. This template helps you present information on three stages. You can also present information on Prevention, Detection, Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
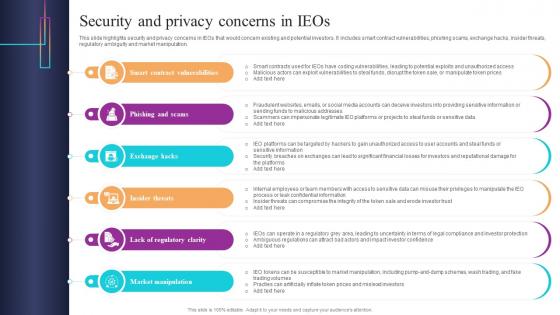 Security And Privacy Concerns In IEOs Introduction To Blockchain Based Initial BCT SS
Security And Privacy Concerns In IEOs Introduction To Blockchain Based Initial BCT SSThis slide highlights security and privacy concerns in IEOs that would concern existing and potential investors. It includes smart contract vulnerabilities, phishing scams, exchange hacks, insider threats, regulatory ambiguity and market manipulation. Introducing Security And Privacy Concerns In IEOs Introduction To Blockchain Based Initial BCT SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Scams, Exchange, Market, using this template. Grab it now to reap its full benefits.
-
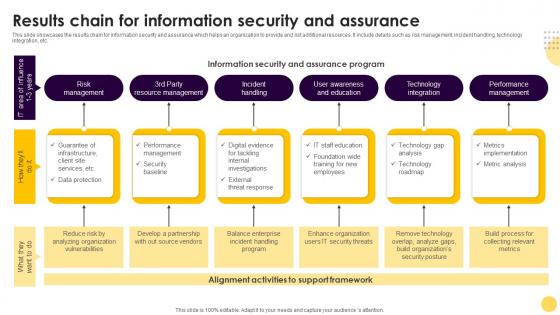 Results Chain For Information Security And Assurance
Results Chain For Information Security And AssuranceThis slide showcases the results chain for information security and assurance which helps an organization to provide and list additional resources. It include details such as risk management, incident handling, technology integration, etc. Introducing our premium set of slides with Results Chain For Information Security And Assurance. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Management, Resource, Education. So download instantly and tailor it with your information.
-
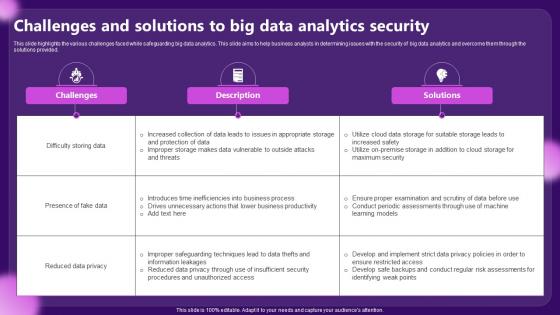 Challenges And Solutions To Big Data Analytics Security
Challenges And Solutions To Big Data Analytics SecurityThis slide highlights the various challenges faced while safeguarding big data analytics. This slide aims to help business analysts in determining issues with the security of big data analytics and overcome them through the solutions provided. Introducing our Challenges And Solutions To Big Data Analytics Security set of slides. The topics discussed in these slides are Difficulty Storing Data, Presence Of Fake Data. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Securities Bonds Types In Powerpoint And Google Slides Cpb
Securities Bonds Types In Powerpoint And Google Slides CpbPresenting Securities Bonds Types In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Securities Bonds Types. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Social Security Checks Calendar In Powerpoint And Google Slides Cpb
Social Security Checks Calendar In Powerpoint And Google Slides CpbPresenting our Social Security Checks Calendar In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases five stages. It is useful to share insightful information on Social Security Checks Calendar This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Web Security Threats Approaches In Powerpoint And Google Slides Cpb
Web Security Threats Approaches In Powerpoint And Google Slides CpbPresenting Web Security Threats Approaches In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Web Security Threats Approaches. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Funds Government Securities In Powerpoint And Google Slides Cpb
Funds Government Securities In Powerpoint And Google Slides CpbPresenting Funds Government Securities In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Funds Government Securities. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Party Vendor Management Security Best Practices In Powerpoint And Google Slides Cpb
Party Vendor Management Security Best Practices In Powerpoint And Google Slides CpbPresenting Party Vendor Management Security Best Practices In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase six stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Party Vendor Management Security Best Practices. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Mortgage Backed Securities Types In Powerpoint And Google Slides Cpb
Mortgage Backed Securities Types In Powerpoint And Google Slides CpbPresenting our Mortgage Backed Securities Types In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Mortgage Backed Securities Types This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Difference Secured Unsecured Bonds In Powerpoint And Google Slides Cpb
Difference Secured Unsecured Bonds In Powerpoint And Google Slides CpbPresenting Difference Secured Unsecured Bonds In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Difference Secured Unsecured Bonds. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Best Student Secured Credit Cards In Powerpoint And Google Slides Cpb
Best Student Secured Credit Cards In Powerpoint And Google Slides CpbPresenting Best Student Secured Credit Cards In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Best Student Secured Credit Cards. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.



