Powerpoint Templates and Google slides for Security Identity Manager Knowledge
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Implementing Identity And Access Management For Operational Security OPSEC Training Ppt
Implementing Identity And Access Management For Operational Security OPSEC Training PptPresenting Implementing Identity and Access Management for Operational Security OPSEC. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
 Identity And Access Management Function As Security Tool IAM Process For Effective Access
Identity And Access Management Function As Security Tool IAM Process For Effective AccessThis slide showcases function of Identity and Access Management as a security tool. The purpose of this slide is to explain the function of IAM as an essential security tool these include context awareness, identity and access governance, and so on. Present the topic in a bit more detail with this Identity And Access Management Function As Security Tool IAM Process For Effective Access. Use it as a tool for discussion and navigation on Context Awareness, Identity And Access Governance, Management Function. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
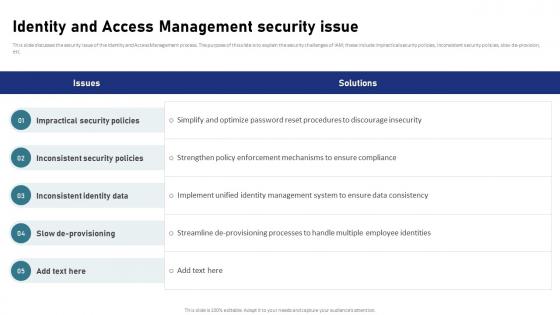 Identity And Access Management Security Issue IAM Process For Effective Access
Identity And Access Management Security Issue IAM Process For Effective AccessThis slide discusses the security issue of the Identity and Access Management process. The purpose of this slide is to explain the security challenges of IAM these include impractical security policies, inconsistent security policies, slow de-provision, etc. Deliver an outstanding presentation on the topic using this Identity And Access Management Security Issue IAM Process For Effective Access. Dispense information and present a thorough explanation of Impractical Security Policies, Inconsistent Security Policies, Inconsistent Identity Data using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
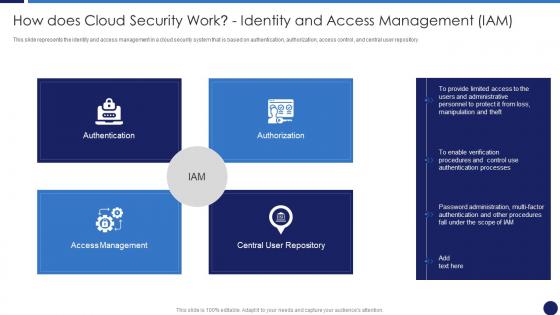 How Does Cloud Security Work Identity And Access Management Cloud Data Protection
How Does Cloud Security Work Identity And Access Management Cloud Data ProtectionThis slide represents the identity and access management in a cloud security system that is based on authentication, authorization, access control, and central user repository. Introducing How Does Cloud Security Work Identity And Access Management Cloud Data Protection to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispense information on Access Management, Authentication, Authorization, Central User Repository, using this template. Grab it now to reap its full benefits.
-
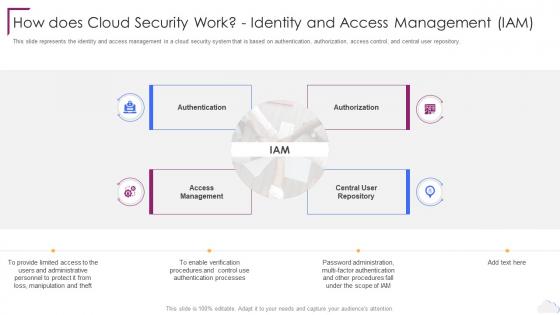 Cloud Computing Security How Does Cloud Security Work Identity And Access Management
Cloud Computing Security How Does Cloud Security Work Identity And Access ManagementThis slide represents the identity and access management in a cloud security system that is based on authentication, authorization, access control, and central user repository. Introducing Cloud Computing Security How Does Cloud Security Work Identity And Access Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Authentication, Authorization, Access Management, Central User Repository, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Policy Access Authorization Modification And Identity Access Management
Cyber Security Policy Access Authorization Modification And Identity Access ManagementThis slide represents the access authorization, modification, and identity access management based on polp, including the departments involved in creating this policy, such as HR and IT. Increase audience engagement and knowledge by dispensing information using Cyber Security Policy Access Authorization Modification And Identity Access Management. This template helps you present information on seven stages. You can also present information on Management, Authorization, Modification using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Set cross departmental standards manage identity management security
Set cross departmental standards manage identity management securityPresenting this set of slides with name - Set Cross Departmental Standards Manage Identity Management Security. This is an editable five stages graphic that deals with topics like Set Cross Departmental Standards, Manage Identity Management Security to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Secure network it infrastructure identity management common methodology
Secure network it infrastructure identity management common methodologyPresenting this set of slides with name - Secure Network It Infrastructure Identity Management Common Methodology. This is an editable two stages graphic that deals with topics like Secure Network It Infrastructure, Identity Management, Common Methodology to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Identity And Access Management Lifecycle In Cloud Security
Identity And Access Management Lifecycle In Cloud SecurityThis slide depicts access and identification management lifecycle in cloud computing systems. It provides information about user request, revoke access, approval, deletions, validations, etc. Presenting our set of slides with Identity And Access Management Lifecycle In Cloud Security. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Identity And Access Management Lifecycle In Cloud Security.
-
 Security identity manager knowledge ppt powerpoint presentation background cpb
Security identity manager knowledge ppt powerpoint presentation background cpbPresenting this set of slides with name Security Identity Manager Knowledge Ppt Powerpoint Presentation Background Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Security Identity Manager Knowledge to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Identity based security access management ppt powerpoint presentation portfolio format cpb
Identity based security access management ppt powerpoint presentation portfolio format cpbPresenting this set of slides with name Identity Based Security Access Management Ppt Powerpoint Presentation Portfolio Format Cpb. This is an editable Powerpoint one stages graphic that deals with topics like Identity Based Security Access Management to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Information security identity access management ppt powerpoint presentation ideas guidelines cpb
Information security identity access management ppt powerpoint presentation ideas guidelines cpbPresenting this set of slides with name Information Security Identity Access Management Ppt Powerpoint Presentation Ideas Guidelines Cpb. This is an editable Powerpoint eight stages graphic that deals with topics like Information Security Identity Access Management to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Secure identity access management system ppt powerpoint gallery cpb
Secure identity access management system ppt powerpoint gallery cpbPresenting this set of slides with name Secure Identity Access Management System Ppt Powerpoint Gallery Cpb. This is an editable Powerpoint three stages graphic that deals with topics like Secure Identity Access Management System to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
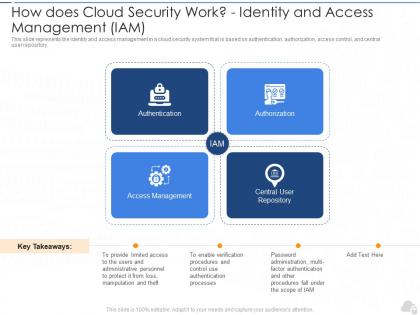 How does cloud security work identity and access management i am cloud security it
How does cloud security work identity and access management i am cloud security itThis slide represents the identity and access management in a cloud security system that is based on authentication, authorization, access control, and central user repository.Introducing How Does Cloud Security Work Identity And Access Management I am Cloud Security IT to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Authentication, Access Management, Central User Repository, using this template. Grab it now to reap its full benefits.
-
 Identity And Access Management Security Trends
Identity And Access Management Security TrendsThis slide showcases emerging trends in IAM shaping future of security such as cloud IAM, entitlement management and decentralized identity. Presenting our set of slides with name Identity And Access Management Security Trends. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Decentralized Identity, Entitlement Management, Management Security Trends.
-
 Identity Management In Cloud Security Icon
Identity Management In Cloud Security IconIntroducing our premium set of slides with name Identity Management In Cloud Security Icon. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Identity Management, Cloud Security Icon. So download instantly and tailor it with your information.

