Powerpoint Templates and Google slides for Security Key To Unlock The Safe
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
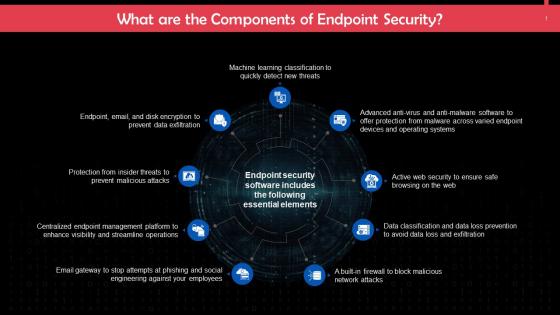 Key Components Of Endpoint Security Training Ppt
Key Components Of Endpoint Security Training PptPresenting Key Components of Endpoint Security. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizable alter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
 Key Board Attached Hanged Security Musician Piano
Key Board Attached Hanged Security Musician PianoEngage buyer personas and boost brand awareness by pitching yourself using this prefabricated set. This Key Board Attached Hanged Security Musician Piano is a great tool to connect with your audience as it contains high-quality content and graphics. This helps in conveying your thoughts in a well-structured manner. It also helps you attain a competitive advantage because of its unique design and aesthetics. In addition to this, you can use this PPT design to portray information and educate your audience on various topics. With twelve slides, this is a great design to use for your upcoming presentations. Not only is it cost-effective but also easily pliable depending on your needs and requirements. As such color, font, or any other design component can be altered. It is also available for immediate download in different formats such as PNG, JPG, etc. So, without any further ado, download it now.
-
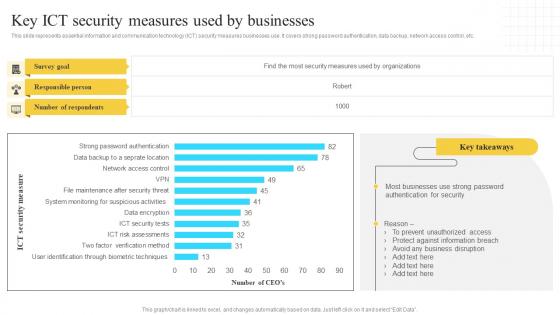
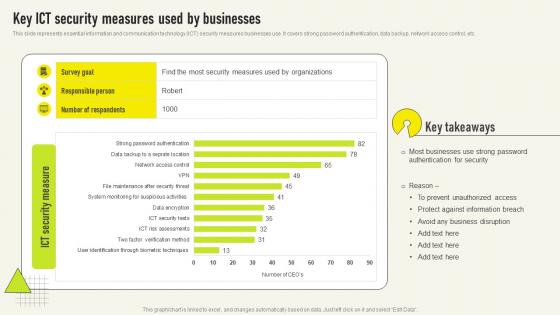 Key Ict Security Measures Used By Comprehensive Guide For Deployment Strategy SS V
Key Ict Security Measures Used By Comprehensive Guide For Deployment Strategy SS VThis slide represents essential information and communication technology ICT security measures businesses use It covers strong password authentication, data backup, network access control, etc Presenting our well structured Key Ict Security Measures Used By Comprehensive Guide For Deployment Strategy SS V The topics discussed in this slide are Authentication Security, Most Businesses, Protect Against This is an instantly available PowerPoint presentation that can be edited conveniently Download it right away and captivate your audience
-
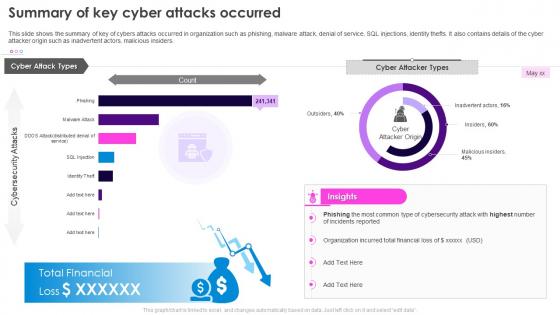 Security Plan To Prevent Cyber Summary Of Key Cyber Attacks Occurred
Security Plan To Prevent Cyber Summary Of Key Cyber Attacks OccurredThis slide shows the summary of key of cybers attacks occurred in organization such as phishing, malware attack, denial of service, SQL injections, identity thefts. It also contains details of the cyber attacker origin such as inadvertent actors, malicious insiders. Present the topic in a bit more detail with this Security Plan To Prevent Cyber Summary Of Key Cyber Attacks Occurred. Use it as a tool for discussion and navigation on Cybers Attacks, Phishing, Malware Attack, Denial Of Service, SQL Injections, Malicious Insiders. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
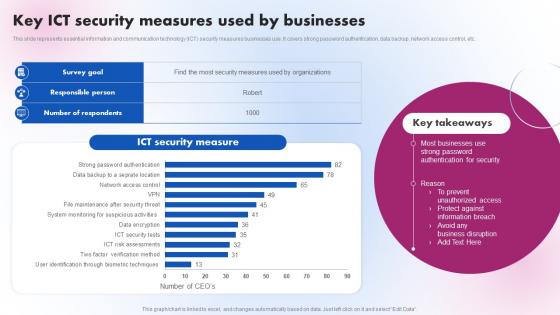 Key ICT Security Measures Used By Businesses Delivering ICT Services For Enhanced Business Strategy SS V
Key ICT Security Measures Used By Businesses Delivering ICT Services For Enhanced Business Strategy SS VThis slide represents essential information and communication technology ICT security measures businesses use. It covers strong password authentication, data backup, network access control, etc. Present the topic in a bit more detail with this Key ICT Security Measures Used By Businesses Delivering ICT Services For Enhanced Business Strategy SS V. Use it as a tool for discussion and navigation on Security Measure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
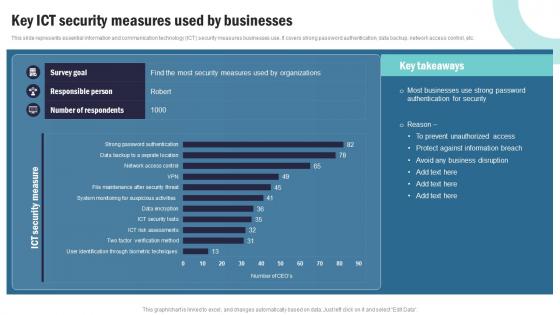 Strategic Plan To Implement Key Ict Security Measures Used By Businesses Strategy SS V
Strategic Plan To Implement Key Ict Security Measures Used By Businesses Strategy SS VThis slide represents essential information and communication technology ICT security measures businesses use. It covers strong password authentication, data backup, network access control, etc. Present the topic in a bit more detail with this Strategic Plan To Implement Key Ict Security Measures Used By Businesses Strategy SS V Use it as a tool for discussion and navigation on Data Sets And Compliance, IT Service Planning This template is free to edit as deemed fit for your organization. Therefore download it now.
-
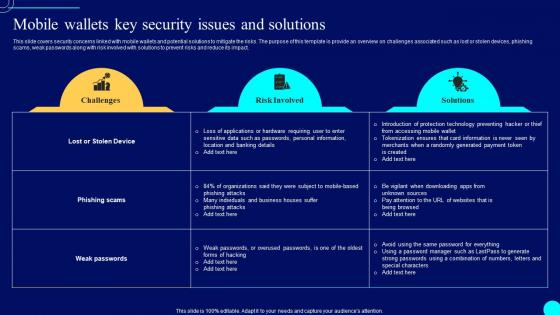 Mobile Wallets Key Security Comprehensive Guide To Blockchain Wallets And Applications BCT SS
Mobile Wallets Key Security Comprehensive Guide To Blockchain Wallets And Applications BCT SSThis slide covers security concerns linked with mobile wallets and potential solutions to mitigate the risks. The purpose of this template is provide an overview on challenges associated such as lost or stolen devices, phishing scams, weak passwords along with risk involved with solutions to prevent risks and reduce its impact. Deliver an outstanding presentation on the topic using this Mobile Wallets Key Security Comprehensive Guide To Blockchain Wallets And Applications BCT SS. Dispense information and present a thorough explanation of Solutions, Risk Involved, Security Issues using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Implementation Of Information Key Ict Security Measures Used By Businesses Strategy SS V
Implementation Of Information Key Ict Security Measures Used By Businesses Strategy SS VThis slide represents essential information and communication technology ICT security measures businesses use. It covers strong password authentication, data backup, network access control, etc. Deliver an outstanding presentation on the topic using this Implementation Of Information Key Ict Security Measures Used By Businesses Strategy SS V. Dispense information and present a thorough explanation of Survey Goal, Responsible Person using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
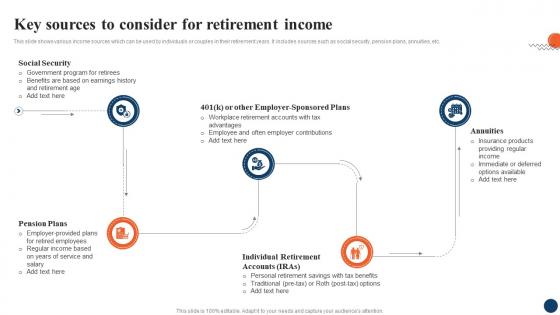 Key Sources To Consider Strategic Retirement Planning To Build Secure Future Fin SS
Key Sources To Consider Strategic Retirement Planning To Build Secure Future Fin SSThis slide shows various income sources which can be used by individuals or couples in their retirement years. It includes sources such as social security, pension plans, annuities, etc. Introducing Key Sources To Consider Strategic Retirement Planning To Build Secure Future Fin SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Social Security, Pension Plans, Annuities, using this template. Grab it now to reap its full benefits.
-
 Devsecops Best Practices For Secure Key Elements Of Successful Devsecops Implementation
Devsecops Best Practices For Secure Key Elements Of Successful Devsecops ImplementationThe slide discusses the critical elements for the successful implementation of DevSecOps. The purpose of this slide is to explain the various features that are integrated automated testing into a pipeline, automated deployment, infrastructure as code, etc. Introducing Devsecops Best Practices For Secure Key Elements Of Successful Devsecops Implementation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Infrastructure As Code, Integrate Security Testing Into Workflows, Automated Deployment, Devsecops Implementation, using this template. Grab it now to reap its full benefits.
-
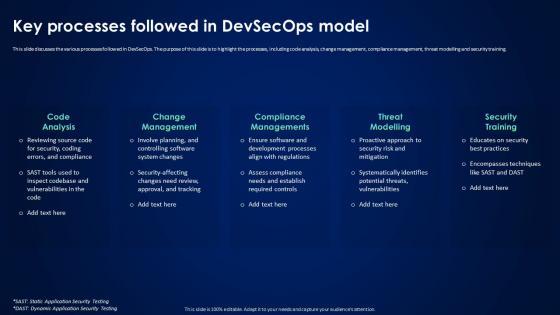 Devsecops Best Practices For Secure Key Processes Followed In Devsecops Model
Devsecops Best Practices For Secure Key Processes Followed In Devsecops ModelThis slide discusses the various processes followed in DevSecOps. The purpose of this slide is to highlight the processes, including code analysis, change management, compliance management, threat modelling and security training. Increase audience engagement and knowledge by dispensing information using Devsecops Best Practices For Secure Key Processes Followed In Devsecops Model. This template helps you present information on five stages. You can also present information on Code Analysis, Change Management, Compliance Managements, Threat Modelling using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
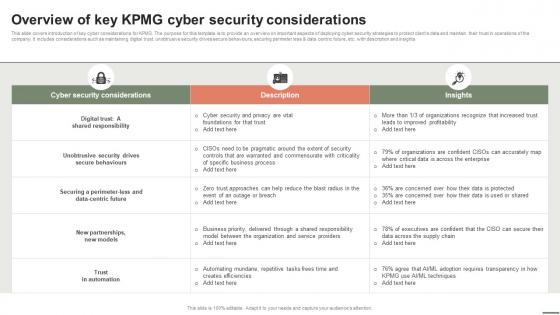 Extensive Business Strategy Overview Of Key KPMG Cyber Security Considerations Strategy SS V
Extensive Business Strategy Overview Of Key KPMG Cyber Security Considerations Strategy SS VThis slide covers introduction of key cyber considerations for KPMG. The purpose for this template is to provide an overview on important aspects of deploying cyber security strategies to protect clients data and maintain their trust in operations of the company. It includes considerations such as maintaining digital trust, unobtrusive security drives secure behaviours, securing perimeter less and data centric future, etc. with description and insights Present the topic in a bit more detail with this Extensive Business Strategy Overview Of Key KPMG Cyber Security Considerations Strategy SS V. Use it as a tool for discussion and navigation on Cyber Security Considerations, Description, Insights. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
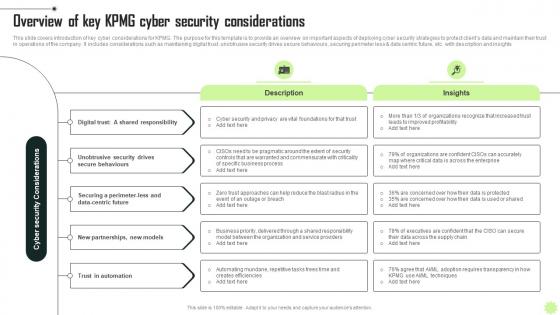 Overview Of Key KPMG Cyber Security KPMG Operational And Marketing Strategy SS V
Overview Of Key KPMG Cyber Security KPMG Operational And Marketing Strategy SS VThis slide covers introduction of key cyber considerations for KPMG. The purpose for this template is to provide an overview on important aspects of deploying cyber security strategies to protect clients data and maintain their trust in operations of the company. It includes considerations such as maintaining digital trust, unobtrusive security drives secure behaviours, securing perimeter less and data centric future, etc. with description and insights Increase audience engagement and knowledge by dispensing information using Overview Of Key KPMG Cyber Security KPMG Operational And Marketing Strategy SS V. This template helps you present information on five stages. You can also present information on Digital, Security, Automation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Analyzing Key Security Breaches Faced By Retail Comprehensive Retail Transformation DT SS
Analyzing Key Security Breaches Faced By Retail Comprehensive Retail Transformation DT SSThis slide analyses the key vvulnerabilities that lead to cybersecurity breaches at retailers. It includes integration of new technologies, weak segregation of duties, outdated infrastructure, outdated anti malware systems leveraging AI, etc. Deliver an outstanding presentation on the topic using this Analyzing Key Security Breaches Faced By Retail Comprehensive Retail Transformation DT SS. Dispense information and present a thorough explanation of Outdated Infrastructure, Anti Malware Systems, New Technologies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
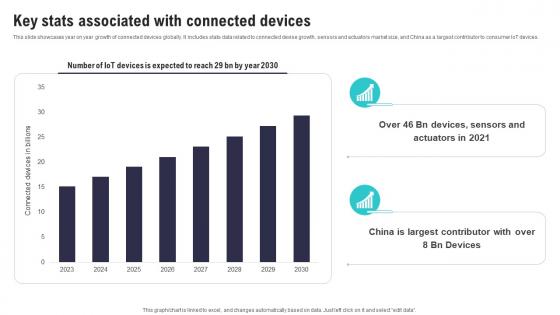 Key Stats Associated With Connected Devices IoT Security And Privacy Safeguarding IoT SS
Key Stats Associated With Connected Devices IoT Security And Privacy Safeguarding IoT SSThis slide showcases year on year growth of connected devices globally. It includes stats data related to connected devise growth, sensors and actuators market size, and China as a largest contributor to consumer IoT devices. Present the topic in a bit more detail with this Key Stats Associated With Connected Devices IoT Security And Privacy Safeguarding IoT SS. Use it as a tool for discussion and navigation on Largest Contributor, Associated Connected, Devices Expected. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
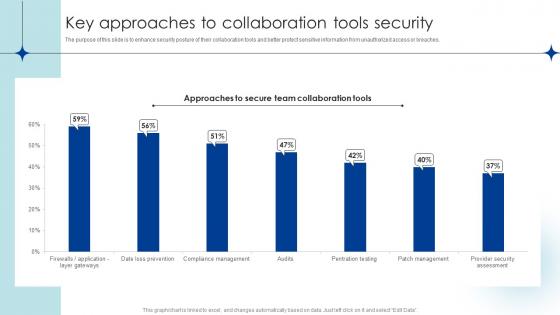 Key Approaches To Collaboration Tools Security
Key Approaches To Collaboration Tools SecurityThe purpose of this slide is to enhance security posture of their collaboration tools and better protect sensitive information from unauthorized access or breaches. Introducing our Key Approaches To Collaboration Tools Security set of slides. The topics discussed in these slides are Key Approaches, Collaboration, Tools Security. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Enhanced Hotel Facility Security With Effective Key Management Training Ppt
Enhanced Hotel Facility Security With Effective Key Management Training PptPresenting Enhanced Hotel Facility Security with Effective Key Management. This PPT presentation is meticulously researched and each slide consists of relevant content. Designed by SlideTeams PowerPoint experts, this PPT is fully customizablealter the colors, text, icons, and font size to meet your requirements. Compatible with Google Slides and backed by excellent customer support. Download to present with poise and assurance.
-
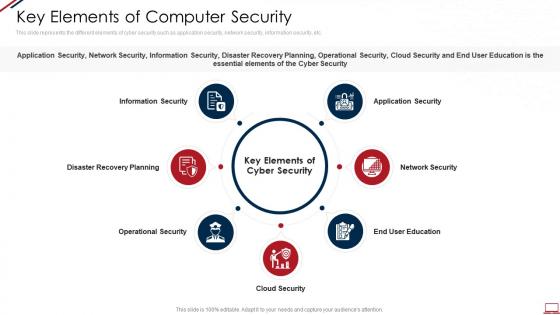 Computer system security key elements of computer security
Computer system security key elements of computer securityThis slide represents the different elements of cyber security such as application security, network security, information security, etc. Introducing Computer System Security Key Elements Of Computer Security to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Information Security, Disaster Recovery Planning, Operational Security, Cloud Security, Network Security, using this template. Grab it now to reap its full benefits.
-
 Data security it key elements of data security ppt slides background
Data security it key elements of data security ppt slides backgroundThis slide represents the different elements of data security such as application security, network security, information security, etc. Introducing Data Security IT Key Elements Of Data Security Ppt Slides Background to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Application Security, Network Security, End User Education, Cloud Security, Operational Security, Disaster Recovery Planning, Information Security, using this template. Grab it now to reap its full benefits.
-
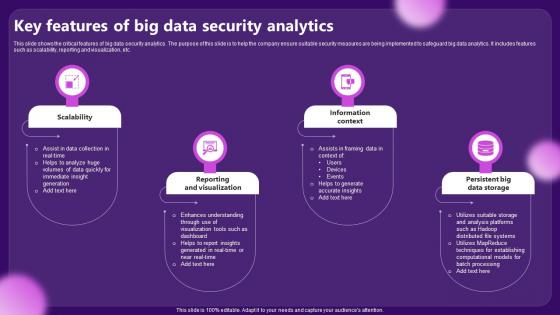 Key Features Of Big Data Security Analytics
Key Features Of Big Data Security AnalyticsThis slide shows the critical features of big data security analytics. The purpose of this slide is to help the company ensure suitable security measures are being implemented to safeguard big data analytics. It includes features such as scalability, reporting and visualization, etc. Presenting our set of slides with Key Features Of Big Data Security Analytics. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Scalability, Information Context.
-
 Key Components Of A Security Management Plan
Key Components Of A Security Management PlanThis slide showcases the critical components of a business security plan. This slide aims to help the business management develop an effective security plan in case of emergencies or uncertainties to avoid financial losses. It includes elements such as risk assessments, security policy development, training and awareness of employees, etc.Presenting our set of slides with Key Components Of A Security Management Plan. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Develop Suitable, Strategies Procedures, Customized Business.
-
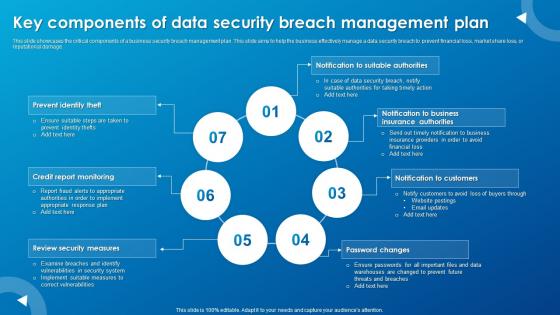 Key Components Of Data Security Breach Management Plan
Key Components Of Data Security Breach Management PlanThis slide showcases the critical components of a business security breach management plan. This slide aims to help the business effectively manage a data security breach to prevent financial loss, market share loss, or reputational damage.Introducing our premium set of slides with Key Components Of Data Security Breach Management Plan. Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Prevent Identity, Credit Report Monitoring, Review Security Measures. So download instantly and tailor it with your information.
-
 Security Keyholder Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Security Keyholder Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis coloured powerpoint icon is perfect for presentations and documents. It is a high-resolution vector image of a keyholder, and comes in a variety of colours to choose from. It is easy to use and is perfect for adding a professional touch to any project.
-
 Security Keyholder Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Security Keyholder Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon on Keyholder is a perfect addition to any presentation. It is a professional-looking icon that is easy to customize and use. It is a great way to add a unique touch to any presentation and is sure to make an impression.
-
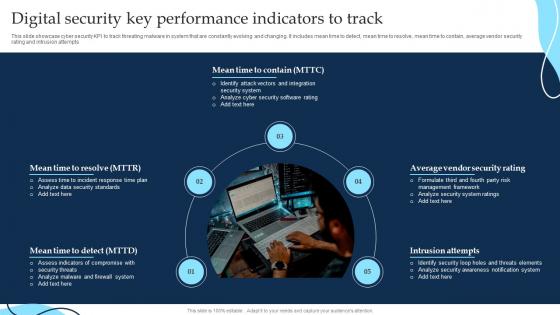 Digital Security Key Performance Indicators To Track
Digital Security Key Performance Indicators To TrackThis slide showcase cyber security KPI to track threating malware in system that are constantly evolving and changing. It includes mean time to detect, mean time to resolve, mean time to contain, average vendor security rating and intrusion attempts Presenting our set of slides with Digital Security Key Performance Indicators To Track. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Performance, Security, Digital.
-
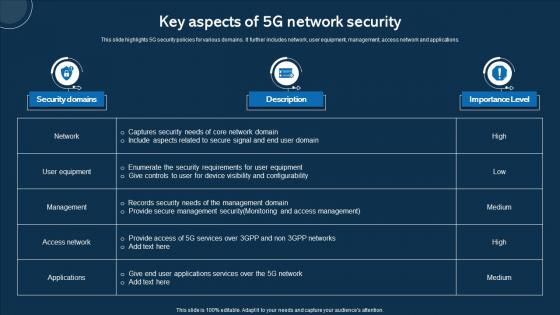 Key Aspects Of 5G Network Security
Key Aspects Of 5G Network SecurityThis slide highlights 5G security policies for various domains. It further includes network, user equipment, management, access network and applications. Introducing our Key Aspects Of 5G Network Security set of slides. The topics discussed in these slides are User Equipment, Management. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Key Uses And Applications Of Cryptographic Security Cloud Cryptography
Key Uses And Applications Of Cryptographic Security Cloud CryptographyThis slide outlines the various uses of cryptography. The purpose of this slide is to elaborate the key applications of cryptography. These are computer security, digital currencies, web surfing security, electronic signatures, authentication, cryptocurrencies, etc. Increase audience engagement and knowledge by dispensing information using Key Uses And Applications Of Cryptographic Security Cloud Cryptography. This template helps you present information on nine stages. You can also present information on Computer Security, Digital Currencies, Web Surfing Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
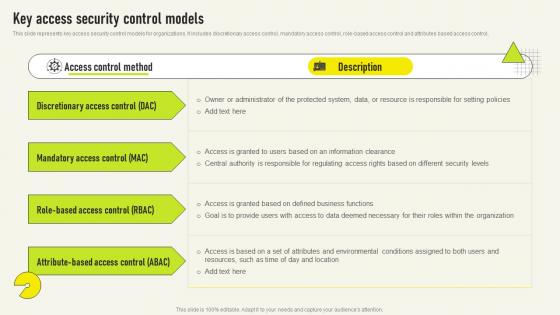 Key Access Security Control Models Comprehensive Guide For Deployment Strategy SS V
Key Access Security Control Models Comprehensive Guide For Deployment Strategy SS VThis slide represents key access security control models for organizations It includes discretionary access control, mandatory access control, role based access control and attributes based access control,Present the topic in a bit more detail with this Key Access Security Control Models Comprehensive Guide For Deployment Strategy SS V Use it as a tool for discussion and navigation on Mandatory Access, Discretionary Access, Administrator Protected This template is free to edit as deemed fit for your organization Therefore download it now
-
 Key Strategies To Secure Business Data
Key Strategies To Secure Business DataThis slide showcase strategies that can be used for securing cyberattacks and target organizational data security and access. It includes updating devices, secure iot technology, track cloud storage, train employees and secure network access. Introducing our premium set of slides with Key Strategies To Secure Business Data. Ellicudate the Five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Updated Devices, Track Cloud Storage, Train Employees. So download instantly and tailor it with your information.
-
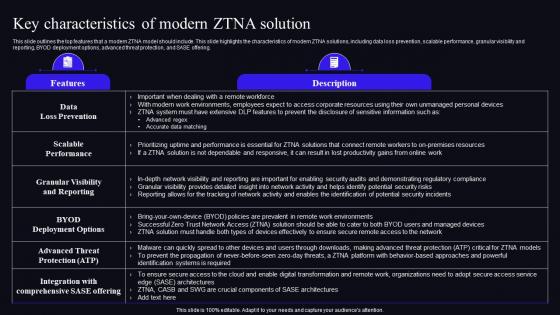 Key Characteristics Of Modern ZTNA Solution Zero Trust Security Model
Key Characteristics Of Modern ZTNA Solution Zero Trust Security ModelThis slide outlines the top features that a modern ZTNA model should include. This slide highlights the characteristics of modern ZTNA solutions, including data loss prevention, scalable performance, granular visibility and reporting, BYOD deployment options, advanced threat protection, and SASE offering. Deliver an outstanding presentation on the topic using this Key Characteristics Of Modern ZTNA Solution Zero Trust Security Model. Dispense information and present a thorough explanation of Deployment, Solution, Characteristics using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
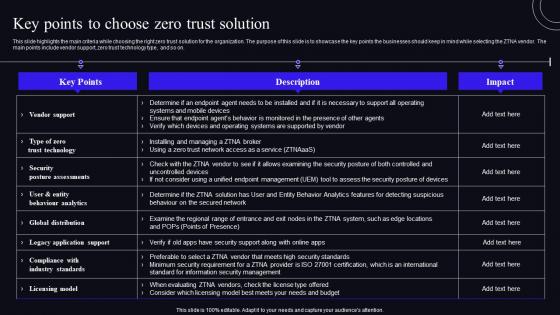 Key Points To Choose Zero Trust Solution Zero Trust Security Model
Key Points To Choose Zero Trust Solution Zero Trust Security ModelThis slide highlights the main criteria while choosing the right zero trust solution for the organization. The purpose of this slide is to showcase the key points the businesses should keep in mind while selecting the ZTNA vendor. The main points include vendor support, zero trust technology type, and so on. Present the topic in a bit more detail with this Key Points To Choose Zero Trust Solution Zero Trust Security Model. Use it as a tool for discussion and navigation on Solution, Businesses, Technology This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Key Opportunities Driving Growth Of Security Token Offerings Security Token Offerings BCT SS
Key Opportunities Driving Growth Of Security Token Offerings Security Token Offerings BCT SSThe following slide showcases various success factors driving growth of security token offerings STO adoption to insure success of. It includes elements such as ecosystem, credibility, regulation, investors literacy, etc. Increase audience engagement and knowledge by dispensing information using Key Opportunities Driving Growth Of Security Token Offerings Security Token Offerings BCT SS. This template helps you present information on four stages. You can also present information on Regulation, Credibility, Investor Literacy, Sto Ecosystem using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Key Services Offered By STO Marketing Agency Security Token Offerings BCT SS
Key Services Offered By STO Marketing Agency Security Token Offerings BCT SSThe following slide illustrates various services offered by security token offering STO marketing agency to. It includes elements such as legal offerings, website development, listing on exchange, marketing, technical support, etc. Present the topic in a bit more detail with this Key Services Offered By STO Marketing Agency Security Token Offerings BCT SS. Use it as a tool for discussion and navigation on Legal Services, Website Development, Marketing, Technical Support. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
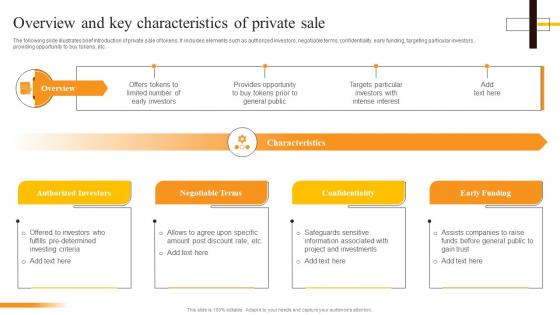 Overview And Key Characteristics Of Private Sale Security Token Offerings BCT SS
Overview And Key Characteristics Of Private Sale Security Token Offerings BCT SSThe following slide illustrates brief introduction of private sale of tokens. It includes elements such as authorized investors, negotiable terms, confidentiality, early funding, targeting particular investors, providing opportunity to buy tokens, etc. Introducing Overview And Key Characteristics Of Private Sale Security Token Offerings BCT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Authorized Investors, Negotiable Terms, Confidentiality, Early Funding, using this template. Grab it now to reap its full benefits.
-
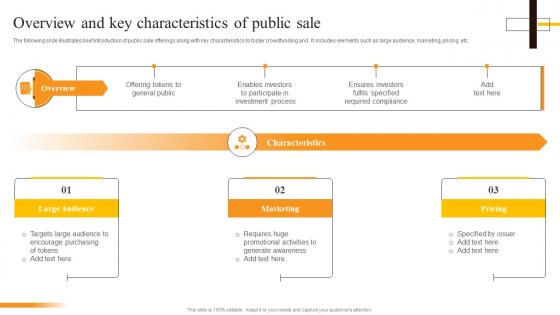 Overview And Key Characteristics Of Public Sale Security Token Offerings BCT SS
Overview And Key Characteristics Of Public Sale Security Token Offerings BCT SSThe following slide illustrates brief introduction of public sale offerings along with key characteristics to foster crowdfunding and . It includes elements such as large audience, marketing, pricing, etc. Increase audience engagement and knowledge by dispensing information using Overview And Key Characteristics Of Public Sale Security Token Offerings BCT SS. This template helps you present information on three stages. You can also present information on Large Audience, Marketing, Pricing, Characteristics using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Security Plan To Prevent Cyber Key Approaches To Minimize Cyber Attacks Risks
Security Plan To Prevent Cyber Key Approaches To Minimize Cyber Attacks RisksThis slide indicates the key approaches to minimize the risk associated with cyber attacks. The approaches discussed are update and upgrade outdated software, control accounts access, introduce signed software execution policies, regularly track network intrusions and use multifactor authentication. Increase audience engagement and knowledge by dispensing information using Security Plan To Prevent Cyber Key Approaches To Minimize Cyber Attacks Risks. This template helps you present information on five stages. You can also present information on Use Multifactor Authentication, Regularly Track Network Intrusions, Control Accounts Access using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
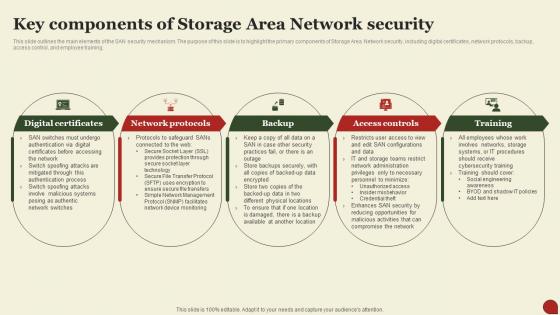 Storage Area Network San Key Components Of Storage Area Network Security
Storage Area Network San Key Components Of Storage Area Network SecurityThis Slide Outlines The Main Elements Of The SAN Security Mechanism. The Purpose Of This Slide Is To Highlight The Primary Components Of Storage Area Network Security, Including Digital Certificates, Network Protocols, Backup, Access Control, And Employee Training. Increase Audience Engagement And Knowledge By Dispensing Information Using Storage Area Network San Key Components Of Storage Area Network Security. This Template Helps You Present Information On Five Stages. You Can Also Present Information On Digital Certificates, Network Protocols, Access Controls Using This PPT Design. This Layout Is Completely Editable So Personaize It Now To Meet Your Audiences Expectations.
-
 Key Benefits Of Using Secure Web Gateway Network Security Using Secure Web Gateway
Key Benefits Of Using Secure Web Gateway Network Security Using Secure Web GatewayThis slide outlines the advantages of implementing Secure Web Gateway into organizations. The purpose of this slide to explain various benefits of SWG such as improved security, increased productivity, reduced risk of data loss, compliance, etc. Introducing Key Benefits Of Using Secure Web Gateway Network Security Using Secure Web Gateway to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Improved Security, Increased Productivity, Simplified Administration, using this template. Grab it now to reap its full benefits.
-
 Key Growth Drivers Of Next Generation Swg Market Network Security Using Secure Web Gateway
Key Growth Drivers Of Next Generation Swg Market Network Security Using Secure Web GatewayThis slide illustrates the different factors which contribute to the increasing need of Next Generation Secure Web Gateways for cloud security. The purpose of this slide is to outline the main growth catalysts of next generation SGV technology market. Increase audience engagement and knowledge by dispensing information using Key Growth Drivers Of Next Generation Swg Market Network Security Using Secure Web Gateway. This template helps you present information on three stages. You can also present information on Growth, Resources, Vulnerability using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Key Secure Web Gateway Solution Providers Network Security Using Secure Web Gateway
Key Secure Web Gateway Solution Providers Network Security Using Secure Web GatewayThis slide outlines the popular service providers of Secure Wen Gateway. The purpose of this slide is to demonstrate the services provided by various SWG solutions such as Cisco, Symantec, McAfee, Zscaler, Barracuda Networks, Fortinet, etc. Deliver an outstanding presentation on the topic using this Key Secure Web Gateway Solution Providers Network Security Using Secure Web Gateway. Dispense information and present a thorough explanation of Comprehensive, Application, Protection using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
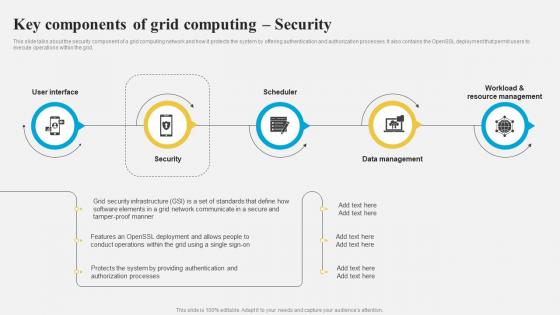 Grid Computing Architecture Key Components Of Grid Computing Security
Grid Computing Architecture Key Components Of Grid Computing SecurityThis slide talks about the security component of a grid computing network and how it protects the system by offering authentication and authorization processes. It also contains the OpenSSL deployment that permit users to execute operations within the grid. Introducing Grid Computing Architecture Key Components Of Grid Computing Security to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Security Component, Grid Computing Network, Protects The System, Authentication And Authorization Processes, using this template. Grab it now to reap its full benefits.
-
 Key Access Security Control Models Delivering ICT Services For Enhanced Business Strategy SS V
Key Access Security Control Models Delivering ICT Services For Enhanced Business Strategy SS VThis slide represents key access security control models for organizations. It includes discretionary access control, mandatory access control, role-based access control and attributes based access control, Deliver an outstanding presentation on the topic using this Key Access Security Control Models Delivering ICT Services For Enhanced Business Strategy SS V. Dispense information and present a thorough explanation of Access Control Method, Description using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
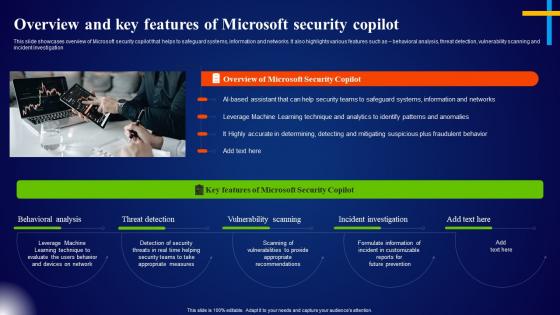 Overview And Key Features Of Microsoft Security Copilot Microsoft AI Solutions AI SS
Overview And Key Features Of Microsoft Security Copilot Microsoft AI Solutions AI SSThis slide showcases overview of Microsoft security copilot that helps to safeguard systems, information and networks. It also highlights various features such as behavioral analysis, threat detection, vulnerability scanning and incident investigation. Introducing Overview And Key Features Of Microsoft Security Copilot Microsoft AI Solutions AI SS to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Behavioral Analysis, Threat Detection, Vulnerability Scanning, using this template. Grab it now to reap its full benefits.
-
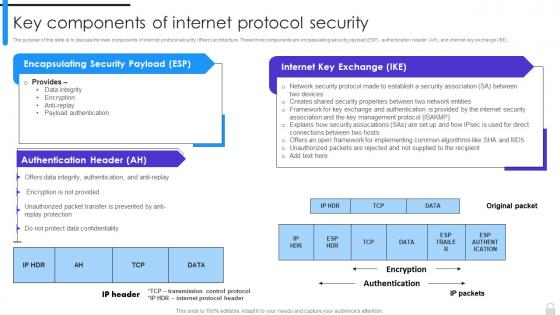 Encryption Implementation Strategies Key Components Of Internet Protocol Security
Encryption Implementation Strategies Key Components Of Internet Protocol SecurityThe purpose of this slide is to discuss the main components of internet protocol security IPsec architecture. These three components are encapsulating security payload ESP, authentication header AH, and internet key exchange IKE. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Key Components Of Internet Protocol Security. Dispense information and present a thorough explanation of Data Integrity, Encryption, Anti Replay, Payload Authentication using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Key Areas Cyber Security In Powerpoint And Google Slides Cpb
Key Areas Cyber Security In Powerpoint And Google Slides CpbPresenting Key Areas Cyber Security In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase five stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Key Areas Cyber Security. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 SASE Network Security Key Drivers For SASE Adoption Ppt Background
SASE Network Security Key Drivers For SASE Adoption Ppt BackgroundThis slide outlines the critical drivers for secure access service edge adoption. This slide aims to demonstrate the key drivers that boost SASE adoption among different organizations, including cloud adoption, increased flexibility and agility, cost effective network traffic management, etc. Introducing SASE Network Security Key Drivers For SASE Adoption Ppt Background to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Improve, Security, Manageability, using this template. Grab it now to reap its full benefits.
-
 Edge Computing Technology Key Edge AI Security Strategies AI SS
Edge Computing Technology Key Edge AI Security Strategies AI SSThis slide showcases 5 major edge AI security strategies so that developers can build and deploy their models in secured way. It provides details about secured perimeter, secured applications, early detection, automated patch, etc. Introducing Edge Computing Technology Key Edge AI Security Strategies AI SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Creating A Secure Perimeter, Securing Applications, Early Detection, Creating Automated Patch, using this template. Grab it now to reap its full benefits.
-
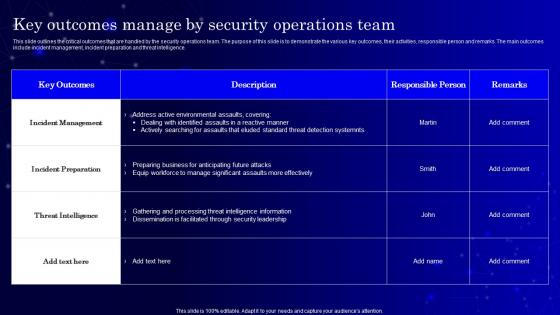 Secops V2 Key Outcomes Manage By Security Operations Team
Secops V2 Key Outcomes Manage By Security Operations TeamThis slide outlines the critical outcomes that are handled by the security operations team. The purpose of this slide is to demonstrate the various key outcomes, their activities, responsible person and remarks. The main outcomes include incident management, incident preparation and threat intelligence. Deliver an outstanding presentation on the topic using this Secops V2 Key Outcomes Manage By Security Operations Team. Dispense information and present a thorough explanation of Incident Management, Incident Preparation, Threat Intelligence, Security Leadership using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
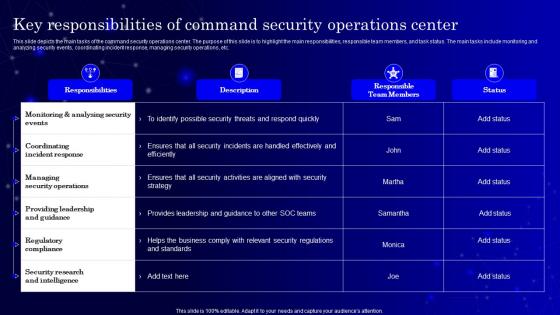 Secops V2 Key Responsibilities Of Command Security Operations Center
Secops V2 Key Responsibilities Of Command Security Operations CenterThis slide depicts the main tasks of the command security operations center. The purpose of this slide is to highlight the main responsibilities, responsible team members, and task status. The main tasks include monitoring and analyzing security events, coordinating incident response, managing security operations, etc. Present the topic in a bit more detail with this Secops V2 Key Responsibilities Of Command Security Operations Center. Use it as a tool for discussion and navigation on Monitoring And Analysing Security Events, Coordinating Incident Response, Regulatory Compliance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Lorawan Lorawan Technology Security Session Keys Ppt Show Inspiration
Lorawan Lorawan Technology Security Session Keys Ppt Show InspirationThis slide explains LoRaWAN security session keys which are used to ensure secure communication between LoRaWAN devices and network servers. Purpose of this slide is to define two types of session keys the application session key AppSKey and the network session key NwkSKey. Deliver an outstanding presentation on the topic using this Lorawan Lorawan Technology Security Session Keys Ppt Show Inspiration. Dispense information and present a thorough explanation of Overview, Technology, Transmission using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Lock Protect Guard Key Security Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Lock Protect Guard Key Security Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis colourful icon features a lock and key design, perfect for adding a touch of security to presentations. Ideal for business, security, or safety-related topics, it will provide a professional and eye-catching look to any project.
-
 Lock Protect Guard Key Security Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Lock Protect Guard Key Security Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is perfect for presentations on security, access control, and encryption. It features a simple, black-and-white design of a lock and key, making it an ideal visual aid for any discussion of protection and safety.
-
 Security Lock And Key Image Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Security Lock And Key Image Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis colourful icon features a lock and key design, perfect for adding a touch of security to presentations. Ideal for business, security, or safety-related topics, it will provide a professional and eye-catching look to any project.
-
 Security Lock And Key Image Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Security Lock And Key Image Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint Icon is perfect for presentations on security, access control, and encryption. It features a simple, black-and-white design of a lock and key, making it an ideal visual aid for any discussion of protection and safety.
-
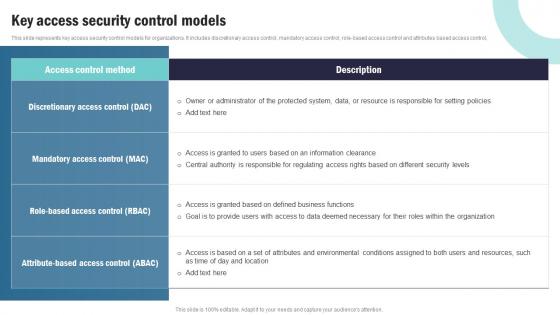 Strategic Plan To Implement Key Access Security Control Models Strategy SS V
Strategic Plan To Implement Key Access Security Control Models Strategy SS VThis slide represents key access security control models for organizations. It includes discretionary access control, mandatory access control, role-based access control and attributes based access control. Deliver an outstanding presentation on the topic using this Strategic Plan To Implement Key Access Security Control Models Strategy SS V Dispense information and present a thorough explanation of This slide represents key access security control models for organizations. It includes discretionary access control, mandatory access control, role-based access control and attributes based access control, using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
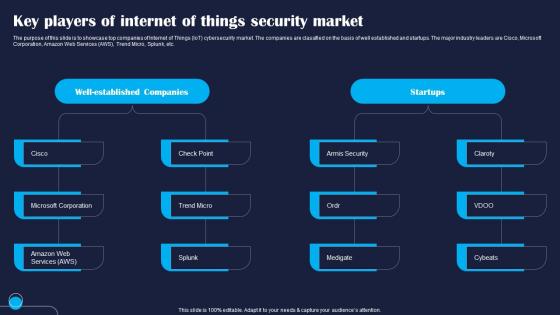 Key Players Of Internet Of Things Security Improving IoT Device Cybersecurity IoT SS
Key Players Of Internet Of Things Security Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase top companies of Internet of Things IoT cybersecurity market. The companies are classified on the basis of well established and startups. The major industry leaders are Cisco, Microsoft Corporation, Amazon Web Services AWS, Trend Micro, Splunk, etc. Deliver an outstanding presentation on the topic using this Key Players Of Internet Of Things Security Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Microsoft, Services, Companies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
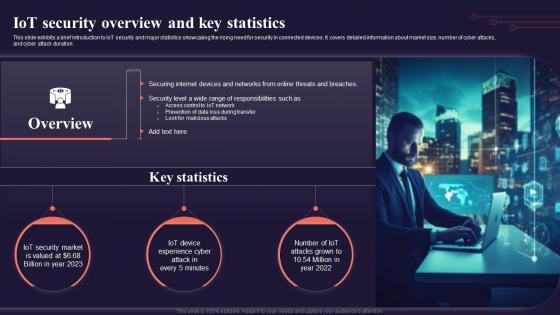 Iot Security Overview And Key Statistics Introduction To Internet Of Things IoT SS
Iot Security Overview And Key Statistics Introduction To Internet Of Things IoT SSThis slide exhibits a brief introduction to IoT security and major statistics showcasing the rising need for security in connected devices. It covers detailed information about market size, number of cyber attacks, and cyber attack duration. Increase audience engagement and knowledge by dispensing information using Iot Security Overview And Key Statistics Introduction To Internet Of Things IoT SS. This template helps you present information on three stages. You can also present information on Security Market, Experience Cyber using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
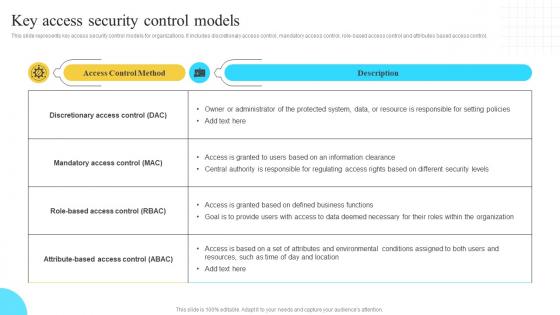 Implementation Of Information Key Access Security Control Models Strategy SS V
Implementation Of Information Key Access Security Control Models Strategy SS VThis slide represents key access security control models for organizations. It includes discretionary access control, mandatory access control, role based access control and attributes based access control, Present the topic in a bit more detail with this Implementation Of Information Key Access Security Control Models Strategy SS V. Use it as a tool for discussion and navigation on Discretionary Access, Mandatory Access. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
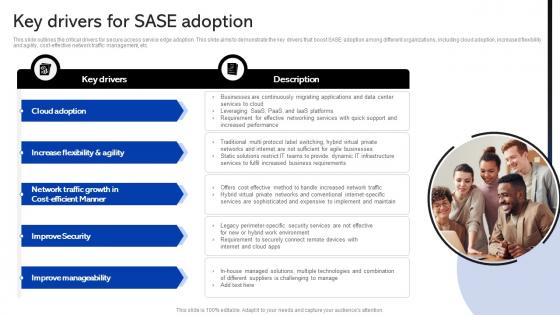 Sase Security Key Drivers For Sase Adoption
Sase Security Key Drivers For Sase AdoptionThis slide outlines the critical drivers for secure access service edge adoption. This slide aims to demonstrate the key drivers that boost SASE adoption among different organizations, including cloud adoption, increased flexibility and agility, cost-effective network traffic management, etc. Deliver an outstanding presentation on the topic using this Sase Security Key Drivers For Sase Adoption. Dispense information and present a thorough explanation of Improve Security, Improve Manageability, Increase Flexibility Agility using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Key Drivers For Sase Adoption Secure Access Service Edge Sase
Key Drivers For Sase Adoption Secure Access Service Edge SaseThis slide outlines the critical drivers for secure access service edge adoption. This slide aims to demonstrate the key drivers that boost SASE adoption among different organizations, including cloud adoption, increased flexibility and agility, cost-effective network traffic management, etc. Present the topic in a bit more detail with this Key Drivers For Sase Adoption Secure Access Service Edge Sase. Use it as a tool for discussion and navigation on Cloud Adoption, Improve Security, Improve Manageability. This template is free to edit as deemed fit for your organization. Therefore download it now.


