Powerpoint Templates and Google slides for Security Vs Compliance
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
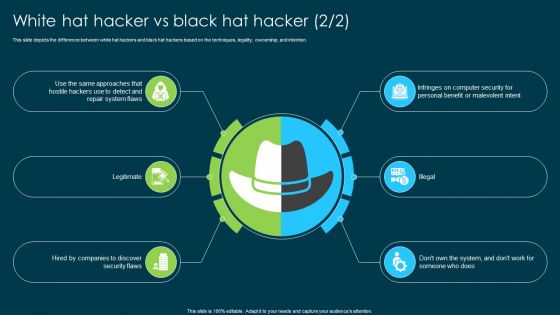 Ethical Hacking And Network Security White Hat Hacker Vs Black Hat Hacker
Ethical Hacking And Network Security White Hat Hacker Vs Black Hat HackerThis slide represents a comparison between white hat hackers and black hat hackers based on the factors such as legality, ownership, and motive. Deliver an outstanding presentation on the topic using this Ethical Hacking And Network Security White Hat Hacker Vs Black Hat Hacker. Dispense information and present a thorough explanation of Hacker Vs Black Hat Hacker, Legality, Ownership, Tactics And Methodologies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Compensation vs social security wages ppt powerpoint presentation infographic template example topics cpb
Compensation vs social security wages ppt powerpoint presentation infographic template example topics cpbPresenting our Compensation Vs Social Security Wages Ppt Powerpoint Presentation Infographic Template Example Topics Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Compensation Vs Social Security Wages This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Financial secured vs unsecured loan ppt powerpoint presentation layouts slides cpb
Financial secured vs unsecured loan ppt powerpoint presentation layouts slides cpbPresenting our Financial Secured Vs Unsecured Loan Ppt Powerpoint Presentation Layouts Slides Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Financial Secured VS Unsecured Loan This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Social security vs supplemental security income ppt powerpoint presentation show slides cpb
Social security vs supplemental security income ppt powerpoint presentation show slides cpbPresenting Social Security Vs Supplemental Security Income Ppt Powerpoint Presentation Show Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Social Security Vs Supplemental Security Income. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
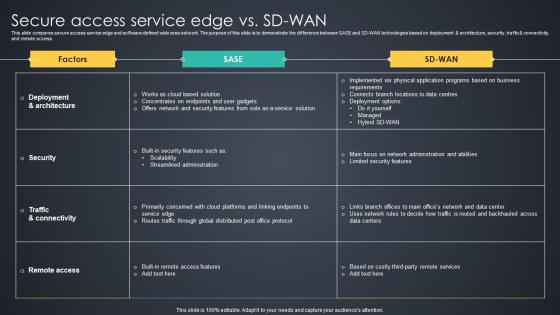 Secure Access Service Edge Vs SD WAN Managed Wan Services
Secure Access Service Edge Vs SD WAN Managed Wan ServicesThis slide compares secure access service edge and software defined wide area network. The purpose of this slide is to demonstrate the difference between SASE and SD WAN technologies based on deployment and architecture, security, traffic and connectivity, and remote access.Present the topic in a bit more detail with this Secure Access Service Edge Vs SD WAN Managed Wan Services. Use it as a tool for discussion and navigation on Streamlined Administration, Limited Security Features, Business Requirements. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
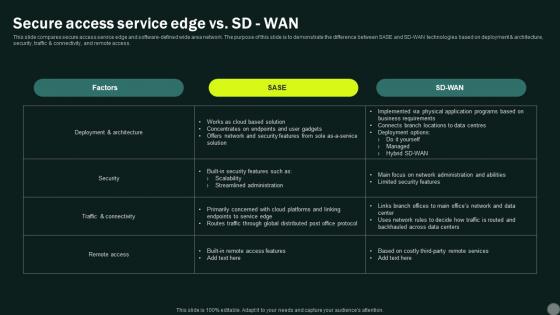 Intelligent Wan Secure Access Service Edge Vs Sd Wan
Intelligent Wan Secure Access Service Edge Vs Sd WanThis slide compares secure access service edge and software-defined wide area network. The purpose of this slide is to demonstrate the difference between SASE and SD-WAN technologies based on deployment and architecture, security, traffic and connectivity, and remote access. Present the topic in a bit more detail with this Intelligent Wan Secure Access Service Edge Vs Sd Wan. Use it as a tool for discussion and navigation on Secure, Service, Demonstrate. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
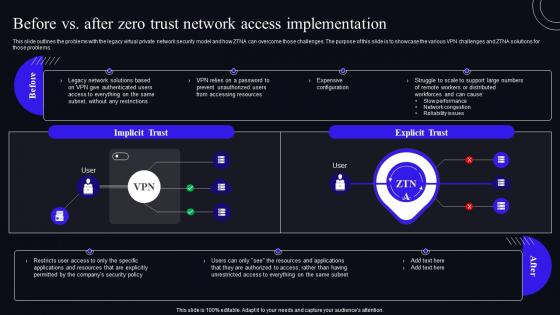 Before Vs After Zero Trust Network Access Implementation Zero Trust Security Model
Before Vs After Zero Trust Network Access Implementation Zero Trust Security ModelThis slide outlines the problems with the legacy virtual private network security model and how ZTNA can overcome those challenges. The purpose of this slide is to showcase the various VPN challenges and ZTNA solutions for those problems. Deliver an outstanding presentation on the topic using this Before Vs After Zero Trust Network Access Implementation Zero Trust Security Model. Dispense information and present a thorough explanation of Implementation, Distributed, Resources using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Endpoint Initiated Vs Service Initiated Zero Trust Security Model
Endpoint Initiated Vs Service Initiated Zero Trust Security ModelThis Slide Represents The Comparison Between The Two Primary Approaches To Implementing Zero-Trust Network Access For Organizations. The Purpose Of This Slide Is To Showcase The Endpoint-Initiated And Service-Initiated Approach Of Zero-Trust Network Access. Present The Topic In A Bit More Detail With This Endpoint Initiated Vs Service Initiated Zero Trust Security Model. Use It As A Tool For Discussion And Navigation On Enterprise, Environment, Connection. This Template Is Free To Edit As Deemed Fit For Your Organization. Therefore Download It Now.
-
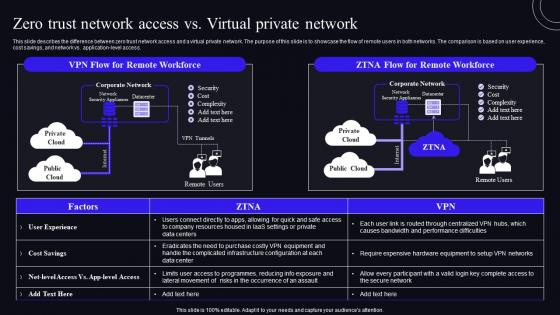 F1593 Zero Trust Network Access Vs Virtual Private Network Zero Trust Security Model
F1593 Zero Trust Network Access Vs Virtual Private Network Zero Trust Security ModelThis slide describes the difference between zero trust network access and a virtual private network. The purpose of this slide is to showcase the flow of remote users in both networks. The comparison is based on user experience, cost savings, and network vs. application-level access. Deliver an outstanding presentation on the topic using this F1593 Zero Trust Network Access Vs Virtual Private Network Zero Trust Security Model. Dispense information and present a thorough explanation of Infrastructure, Configuration, Equipment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
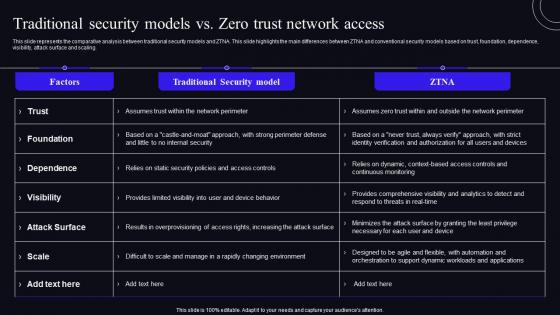 Traditional Security Models Vs Zero Trust Network Access Zero Trust Security Model
Traditional Security Models Vs Zero Trust Network Access Zero Trust Security ModelThis slide represents the comparative analysis between traditional security models and ZTNA. This slide highlights the main differences between ZTNA and conventional security models based on trust, foundation, dependence, visibility, attack surface and scaling. Present the topic in a bit more detail with this Traditional Security Models Vs Zero Trust Network Access Zero Trust Security Model. Use it as a tool for discussion and navigation on Dependence, Foundation, Attack Surface. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
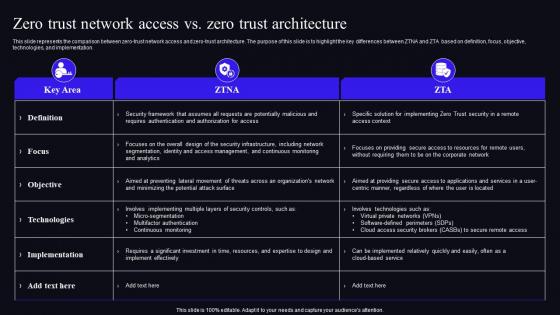 Zero Trust Network Access Vs Zero Trust Architecture Zero Trust Security Model
Zero Trust Network Access Vs Zero Trust Architecture Zero Trust Security ModelThis slide represents the comparison between zero-trust network access and zero-trust architecture. The purpose of this slide is to highlight the key differences between ZTNA and ZTA based on definition, focus, objective, technologies, and implementation. Deliver an outstanding presentation on the topic using this Zero Trust Network Access Vs Zero Trust Architecture Zero Trust Security Model. Dispense information and present a thorough explanation of Architecture, Implementation, Technologies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
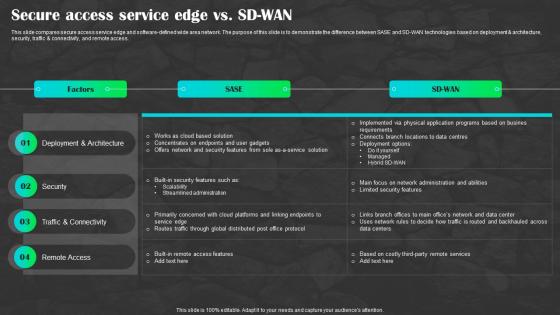 Sd Wan As A Service Secure Access Service Edge Vs Sd Wan Ppt Background
Sd Wan As A Service Secure Access Service Edge Vs Sd Wan Ppt BackgroundThis slide compares secure access service edge and software-defined wide area network. The purpose of this slide is to demonstrate the difference between SASE and SD-WAN technologies based on deployment And architecture, security, traffic And connectivity, and remote access. Present the topic in a bit more detail with this Sd Wan As A Service Secure Access Service Edge Vs Sd Wan Ppt Background. Use it as a tool for discussion and navigation on Deployment And Architecture, Security, Remote Access. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
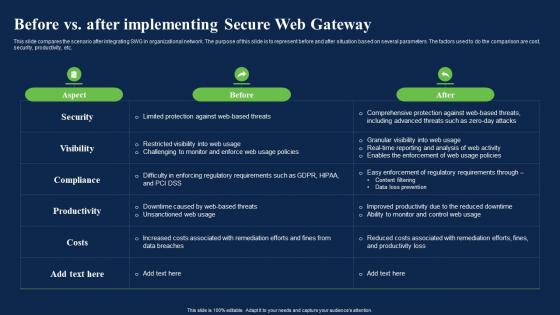 Before Vs After Implementing Secure Web Gateway Network Security Using Secure Web Gateway
Before Vs After Implementing Secure Web Gateway Network Security Using Secure Web GatewayThis slide compares the scenario after integrating SWG in organizational network. The purpose of this slide is to represent before and after situation based on several parameters. The factors used to do the comparison are cost, security, productivity, etc. Present the topic in a bit more detail with this Before Vs After Implementing Secure Web Gateway Network Security Using Secure Web Gateway. Use it as a tool for discussion and navigation on Productivity, Enforcement, Requirements. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
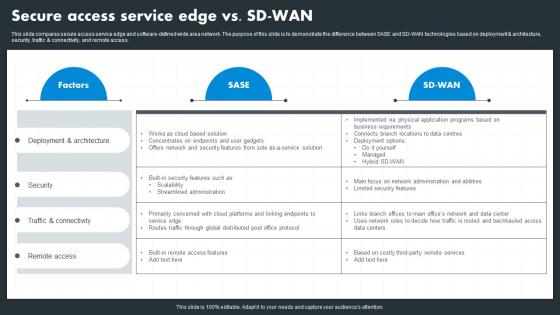 Hybrid Wan Secure Access Service Edge Vs Sd Wan
Hybrid Wan Secure Access Service Edge Vs Sd WanThis slide compares secure access service edge and software defined wide area network. The purpose of this slide is to demonstrate the difference between SASE and SD WAN technologies based on deployment and architecture, security, traffic and connectivity, and remote access. Present the topic in a bit more detail with this Hybrid Wan Secure Access Service Edge Vs Sd Wan. Use it as a tool for discussion and navigation on Security, Remote Access. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
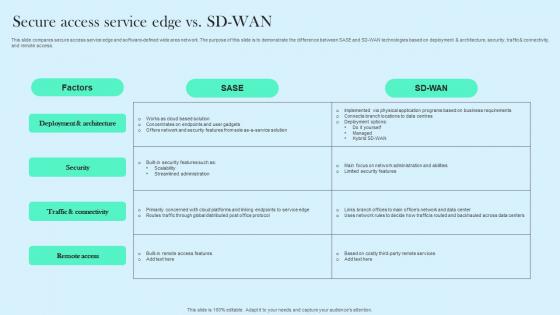 Secure Access Service Edge Vs SD WAN Cloud WAN Ppt Guidelines
Secure Access Service Edge Vs SD WAN Cloud WAN Ppt GuidelinesThis slide compares secure access service edge and software defined wide area network. The purpose of this slide is to demonstrate the difference between SASE and SD WAN technologies based on deployment and architecture, security, traffic and connectivity, and remote access. Deliver an outstanding presentation on the topic using this Secure Access Service Edge Vs SD WAN Cloud WAN Ppt Guidelines. Dispense information and present a thorough explanation of Architecture, Deployment, Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
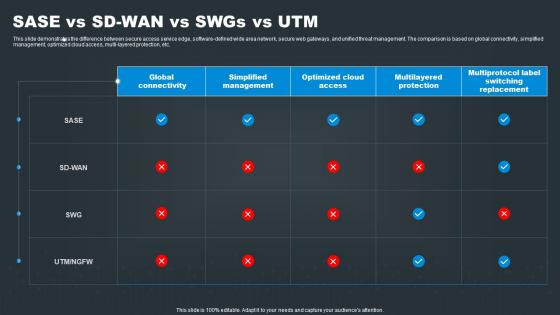 SASE Network Security SASE Vs SD WAN Vs Swgs Vs UTM
SASE Network Security SASE Vs SD WAN Vs Swgs Vs UTMThis slide demonstrates the difference between secure access service edge, software defined wide area network, secure web gateways, and unified threat management. The comparison is based on global connectivity, simplified management, optimized cloud access, multi layered protection, etc. Deliver an outstanding presentation on the topic using this SASE Network Security SASE Vs SD WAN Vs Swgs Vs UTM. Dispense information and present a thorough explanation of Protection, Management, Global using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
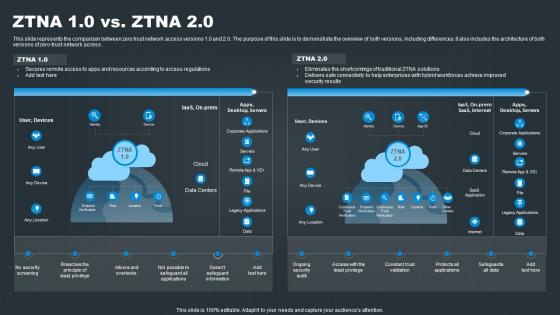 SASE Network Security ZTNA 1 0 Vs ZTNA 2 0 Ppt Slides
SASE Network Security ZTNA 1 0 Vs ZTNA 2 0 Ppt SlidesThis slide represents the comparison between zero trust network access versions 1.0 and 2.0. The purpose of this slide is to demonstrate the overview of both versions, including differences. It also includes the architecture of both versions of zero trust network access. Present the topic in a bit more detail with this SASE Network Security ZTNA 1 0 Vs ZTNA 2 0 Ppt Slides. Use it as a tool for discussion and navigation on Security, Privilege, Validation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
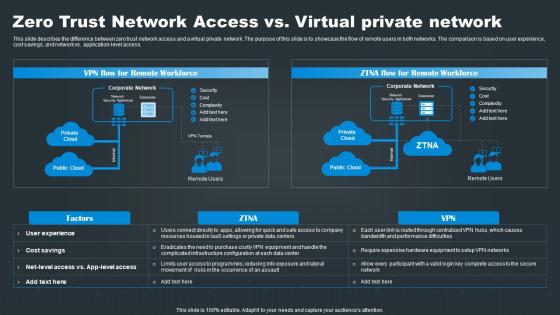 Zero Trust Network Access Vs Virtual Private Network SASE Network Security
Zero Trust Network Access Vs Virtual Private Network SASE Network SecurityThis slide describes the difference between zero trust network access and a virtual private network. The purpose of this slide is to showcase the flow of remote users in both networks. The comparison is based on user experience, cost savings, and network vs. application level access. Present the topic in a bit more detail with this Zero Trust Network Access Vs Virtual Private Network SASE Network Security. Use it as a tool for discussion and navigation on Security, Private, Network. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
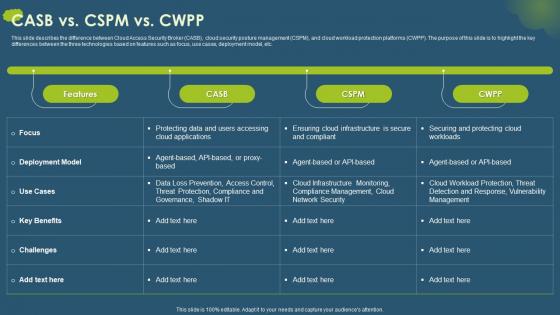 CASB Vs CSPM Vs CWPP Cloud Access Security Broker CASB V2 Ppt Ideas Samples
CASB Vs CSPM Vs CWPP Cloud Access Security Broker CASB V2 Ppt Ideas SamplesThis slide describes the difference between Cloud Access Security Broker CASB, cloud security posture management CSPM, and cloud workload protection platforms CWPP. The purpose of this slide is to highlight the key differences between the three technologies based on features such as focus, use cases, deployment model, etc. Present the topic in a bit more detail with this CASB Vs CSPM Vs CWPP Cloud Access Security Broker CASB V2 Ppt Ideas Samples. Use it as a tool for discussion and navigation on Cloud Workload Protection, Threat Detection And Response, Vulnerability Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
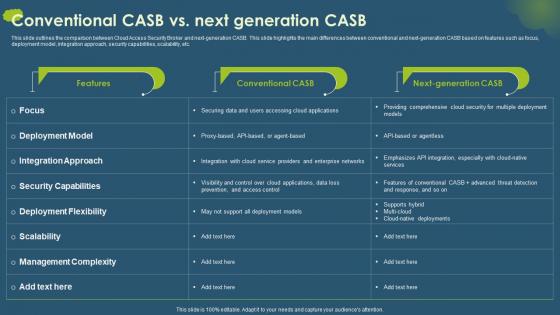 Cloud Access Security Broker CASB V2 Conventional CASB Vs Next Generation CASB
Cloud Access Security Broker CASB V2 Conventional CASB Vs Next Generation CASBThis slide outlines the comparison between Cloud Access Security Broker and next-generation CASB. This slide highlights the main differences between conventional and next-generation CASB based on features such as focus, deployment model, integration approach, security capabilities, scalability, etc. Present the topic in a bit more detail with this Cloud Access Security Broker CASB V2 Conventional CASB Vs Next Generation CASB. Use it as a tool for discussion and navigation on Integration Approach, Security Capabilities, Deployment Flexibility, Management Complexity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
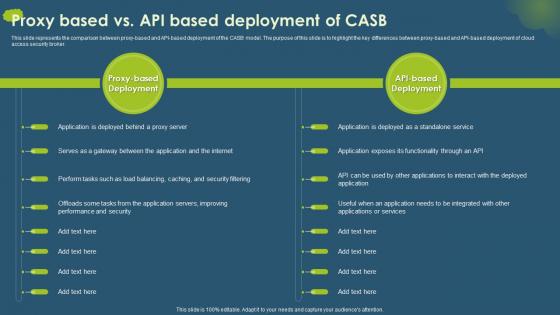 Cloud Access Security Broker CASB V2 Proxy Based Vs API Based Deployment Of CASB
Cloud Access Security Broker CASB V2 Proxy Based Vs API Based Deployment Of CASBThis slide represents the comparison between proxy-based and API-based deployment of the CASB model. The purpose of this slide is to highlight the key differences between proxy-based and API-based deployment of cloud access security broker. Present the topic in a bit more detail with this Cloud Access Security Broker CASB V2 Proxy Based Vs API Based Deployment Of CASB. Use it as a tool for discussion and navigation on Performance And Security, Proxy Based Deployment, Standalone Service. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
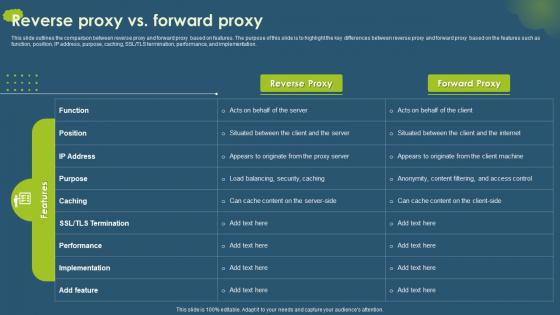 Cloud Access Security Broker CASB V2 Reverse Proxy Vs Forward Proxy
Cloud Access Security Broker CASB V2 Reverse Proxy Vs Forward ProxyThis slide outlines the comparison between reverse proxy and forward proxy based on features. The purpose of this slide is to highlight the key differences between reverse proxy and forward proxy based on the features such as function, position, IP address, purpose, caching, SSL or TLS termination, performance, and implementation. Deliver an outstanding presentation on the topic using this Cloud Access Security Broker CASB V2 Reverse Proxy Vs Forward Proxy. Dispense information and present a thorough explanation of Reverse Proxy, Forward Proxy, Performance And Implementation, Load Balancing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
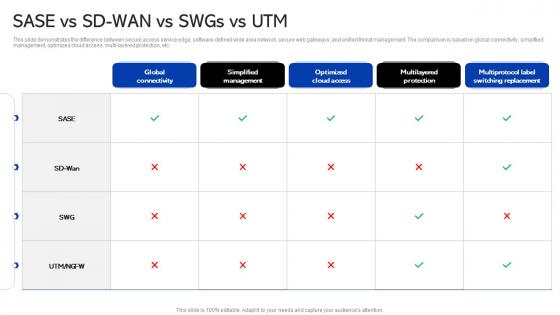 Sase Security Sase Vs Sd Wan Vs Swgs Vs Utm
Sase Security Sase Vs Sd Wan Vs Swgs Vs UtmThis slide demonstrates the difference between secure access service edge, software-defined wide area network, secure web gateways, and unified threat management. The comparison is based on global connectivity, simplified management, optimized cloud access, multi-layered protection, etc. Present the topic in a bit more detail with this Sase Security Sase Vs Sd Wan Vs Swgs Vs Utm. Use it as a tool for discussion and navigation on Optimized Cloud Access, Simplified Management, Global Connectivity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Sase Security Zero Network Access Vs Virtual Private Network Ppt Show Design Templates
Sase Security Zero Network Access Vs Virtual Private Network Ppt Show Design TemplatesThis slide describes the difference between zero trust network access and a virtual private network. The purpose of this slide is to showcase the flow of remote users in both networks. The comparison is based on user experience, cost savings, and network vs. application-level access. Present the topic in a bit more detail with this Sase Security Zero Network Access Vs Virtual Private Network Ppt Show Design Templates. Use it as a tool for discussion and navigation on Equipment, Infrastructure, Configuration . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
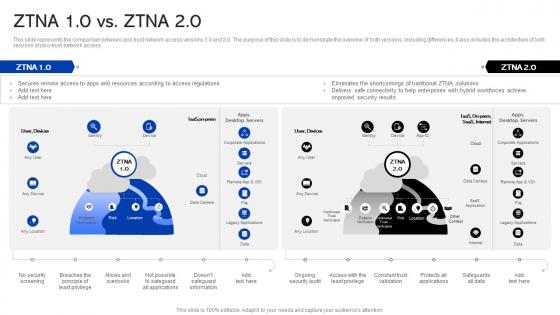 Sase Security Ztna 10 Vs Ztna 20 Ppt Show Slide Download
Sase Security Ztna 10 Vs Ztna 20 Ppt Show Slide DownloadThis slide represents the comparison between zero trust network access versions 1.0 and 2.0. The purpose of this slide is to demonstrate the overview of both versions, including differences. It also includes the architecture of both versions of zero-trust network access. Present the topic in a bit more detail with this Sase Security Ztna 10 Vs Ztna 20 Ppt Show Slide Download. Use it as a tool for discussion and navigation on Connectivity, Resources, Regulations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
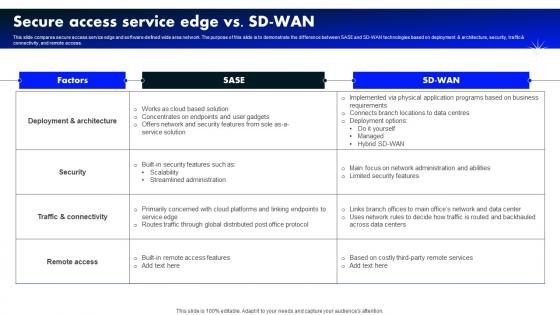 Secure Access Service Edge Vs Sd Wan Software Defined Wide Area Network
Secure Access Service Edge Vs Sd Wan Software Defined Wide Area NetworkThis slide compares secure access service edge and software-defined wide area network. The purpose of this slide is to demonstrate the difference between SASE and SD-WAN technologies based on deployment and architecture, security, traffic and connectivity, and remote access. Present the topic in a bit more detail with this Secure Access Service Edge Vs Sd Wan Software Defined Wide Area Network. Use it as a tool for discussion and navigation on Business, Requirements, Locations . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
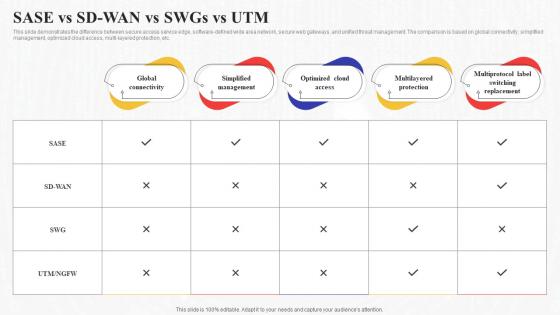 Sase Vs Sd Wan Vs Swgs Vs Utm Secure Access Service Edge Sase
Sase Vs Sd Wan Vs Swgs Vs Utm Secure Access Service Edge SaseThis slide demonstrates the difference between secure access service edge, software-defined wide area network, secure web gateways, and unified threat management. The comparison is based on global connectivity, simplified management, optimized cloud access, multi-layered protection, etc. Deliver an outstanding presentation on the topic using this Sase Vs Sd Wan Vs Swgs Vs Utm Secure Access Service Edge Sase. Dispense information and present a thorough explanation of Simplified Management, Global Connectivity, Multilayered Protection using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
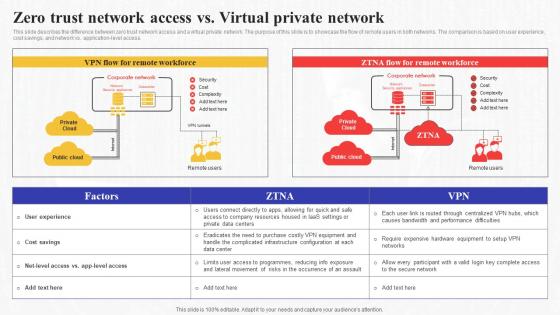 Zero Trust Access Vs Virtual Private Network Secure Access Service Edge Sase
Zero Trust Access Vs Virtual Private Network Secure Access Service Edge SaseThis slide describes the difference between zero trust network access and a virtual private network. The purpose of this slide is to showcase the flow of remote users in both networks. The comparison is based on user experience, cost savings, and network vs. application-level access. Present the topic in a bit more detail with this Zero Trust Access Vs Virtual Private Network Secure Access Service Edge Sase. Use it as a tool for discussion and navigation on Infrastructure, Configuration, Equipment . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
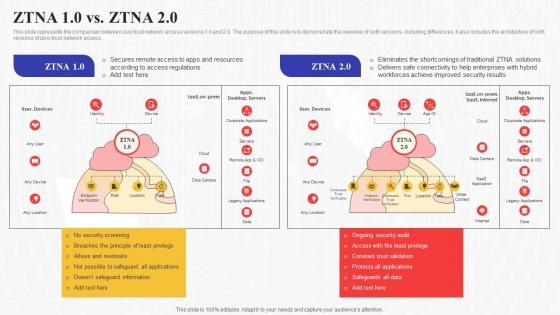 Ztna 10 Vs Ztna 20 Secure Access Service Edge Sase
Ztna 10 Vs Ztna 20 Secure Access Service Edge SaseThis slide represents the comparison between zero trust network access versions 1.0 and 2.0. The purpose of this slide is to demonstrate the overview of both versions, including differences. It also includes the architecture of both versions of zero-trust network access. Present the topic in a bit more detail with this Ztna 10 Vs Ztna 20 Secure Access Service Edge Sase. Use it as a tool for discussion and navigation on Enterprises, Resources, Applications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
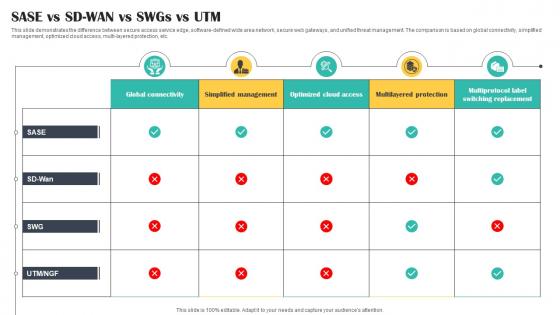 SASE Vs SD WAN Vs SWGs Vs UTM Cloud Security Model
SASE Vs SD WAN Vs SWGs Vs UTM Cloud Security ModelThis slide demonstrates the difference between secure access service edge, software defined wide area network, secure web gateways, and unified threat management. The comparison is based on global connectivity, simplified management, optimized cloud access, multi layered protection, etc. Present the topic in a bit more detail with this SASE Vs SD WAN Vs SWGs Vs UTM Cloud Security Model. Use it as a tool for discussion and navigation on Management, Protection, Service. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
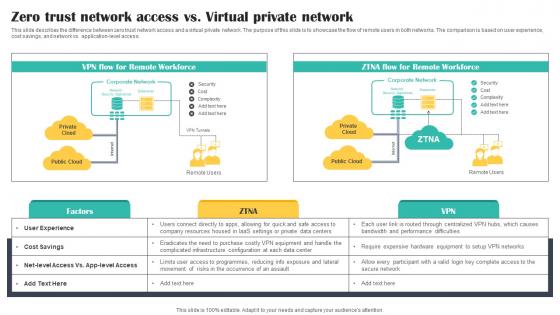 Zero Trust Network Access Vs Virtual Private Network Cloud Security Model
Zero Trust Network Access Vs Virtual Private Network Cloud Security ModelThis slide describes the difference between zero trust network access and a virtual private network. The purpose of this slide is to showcase the flow of remote users in both networks. The comparison is based on user experience, cost savings, and network vs. application level access. Present the topic in a bit more detail with this Zero Trust Network Access Vs Virtual Private Network Cloud Security Model. Use it as a tool for discussion and navigation on Workforce, Network, Private. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
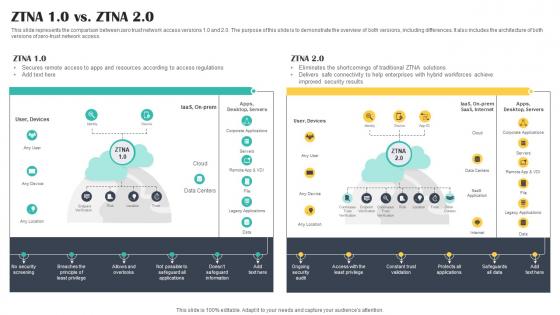 ZTNA 1 0 Vs ZTNA 2 0 Cloud Security Model Ppt Pictures
ZTNA 1 0 Vs ZTNA 2 0 Cloud Security Model Ppt PicturesThis slide represents the comparison between zero trust network access versions 1.0 and 2.0. The purpose of this slide is to demonstrate the overview of both versions, including differences. It also includes the architecture of both versions of zero trust network access. Present the topic in a bit more detail with this ZTNA 1 0 Vs ZTNA 2 0 Cloud Security Model Ppt Pictures. Use it as a tool for discussion and navigation on Remote, Secures, Regulations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
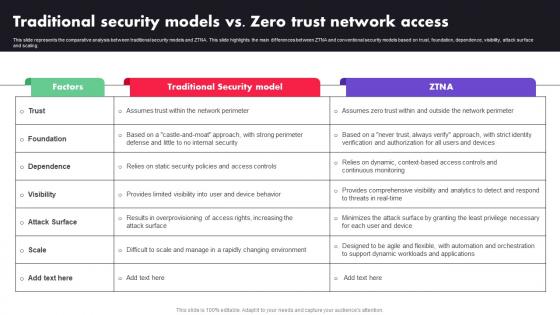 M72 Traditional Security Models Vs Zero Trust Network Access Zero Trust Architecture ZTA
M72 Traditional Security Models Vs Zero Trust Network Access Zero Trust Architecture ZTAThis slide represents the comparative analysis between traditional security models and ZTNA. This slide highlights the main differences between ZTNA and conventional security models based on trust, foundation, dependence, visibility, attack surface and scaling. Deliver an outstanding presentation on the topic using this M72 Traditional Security Models Vs Zero Trust Network Access Zero Trust Architecture ZTA. Dispense information and present a thorough explanation of Factors, Traditional Security Model, ZTNA using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
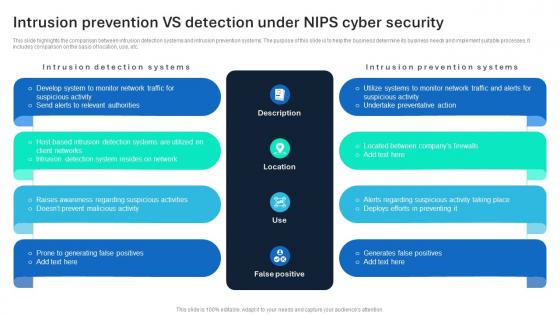 Intrusion Prevention VS Detection Under NIPS Cyber Security
Intrusion Prevention VS Detection Under NIPS Cyber SecurityThis slide highlights the comparison between intrusion detection systems and intrusion prevention systems. The purpose of this slide is to help the business determine its business needs and implement suitable processes. It includes comparison on the basis of location, use, etc. Presenting our well structured Intrusion Prevention VS Detection Under NIPS Cyber Security The topics discussed in this slide are Description, Location, False Positive This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
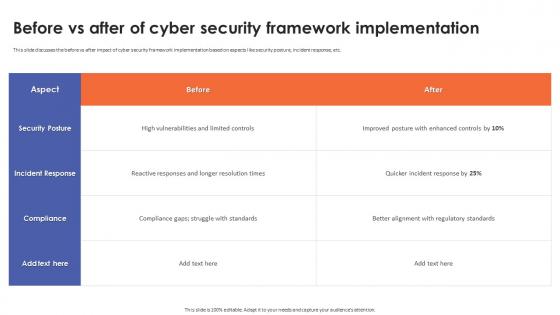 Before Vs After Of Cyber Security Framework Implementation
Before Vs After Of Cyber Security Framework ImplementationThis slide discusses the before vs after impact of cyber security framework implementation based on aspects like security posture, incident response, etc. Present the topic in a bit more detail with this Before Vs After Of Cyber Security Framework Implementation. Use it as a tool for discussion and navigation on Incident Response, Cyber Security, Framework Implementation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
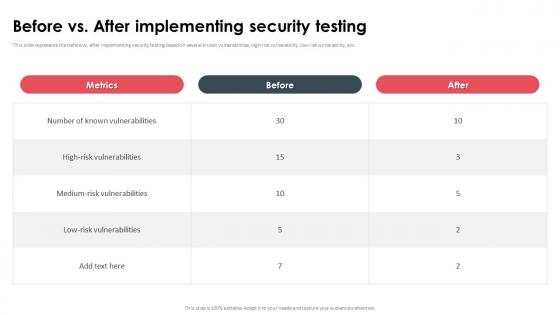 Before Vs After Implementing Security Testing
Before Vs After Implementing Security TestingThis slide represents the before vs. after implementing security testing based on several known vulnerabilities, high-risk vulnerability, low-risk vulnerability, etc. Deliver an outstanding presentation on the topic using this Before Vs After Implementing Security Testing. Dispense information and present a thorough explanation of High Risk Vulnerabilities, Medium Risk Vulnerabilities, Low Risk Vulnerabilities using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
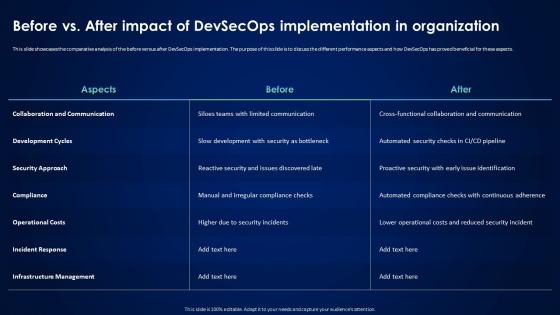 Devsecops Best Practices For Secure Before Vs After Impact Of Devsecops Implementation
Devsecops Best Practices For Secure Before Vs After Impact Of Devsecops ImplementationThis slide showcases the comparative analysis of the before versus after DevSecOps implementation. The purpose of this slide is to discuss the different performance aspects and how DevSecOps has proved beneficial for these aspects. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure Before Vs After Impact Of Devsecops Implementation. Dispense information and present a thorough explanation of Collaboration And Communication, Development Cycles, Operational Costs, Infrastructure Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
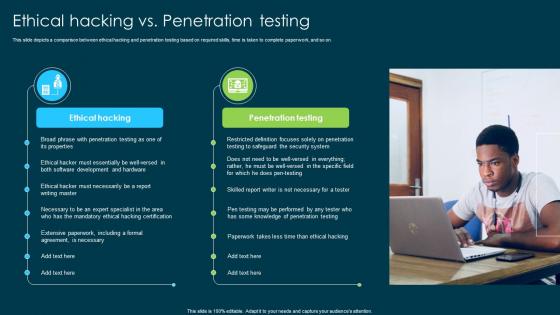 Ethical Hacking And Network Security Ethical Hacking Vs Penetration Testing
Ethical Hacking And Network Security Ethical Hacking Vs Penetration TestingThis slide depicts a comparison between ethical hacking and penetration testing based on required skills, time is taken to complete paperwork, and so on. Introducing Ethical Hacking And Network Security Ethical Hacking Vs Penetration Testing to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Ethical Hacking, Penetration Testing, Extensive Paperwork, Mandatory Ethical Hacking Certification, using this template. Grab it now to reap its full benefits.
-
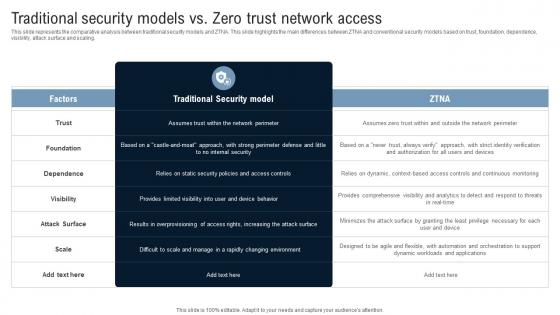 Traditional Security Models Vs Zero Trust Network Access Identity Defined Networking
Traditional Security Models Vs Zero Trust Network Access Identity Defined NetworkingThis slide represents the comparative analysis between traditional security models and ZTNA. This slide highlights the main differences between ZTNA and conventional security models based on trust, foundation, dependence, visibility, attack surface and scaling. Deliver an outstanding presentation on the topic using this Traditional Security Models Vs Zero Trust Network Access Identity Defined Networking Dispense information and present a thorough explanation of Traditional Security Model, Foundation, Dependence, Visibility using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Secure Your Digital Assets Before Vs After Crypto Wallets Integration
Secure Your Digital Assets Before Vs After Crypto Wallets IntegrationThis slide represents the before versus after crypto wallets integration for business operations. The purpose of this slide is to showcase how integration of crypto wallets has removed the third party vendors from digital transactions. Increase audience engagement and knowledge by dispensing information using Secure Your Digital Assets Before Vs After Crypto Wallets Integration. This template helps you present information on five stages. You can also present information on Crypto Wallets Integration, Digital Transactions, Bitcoin Network using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
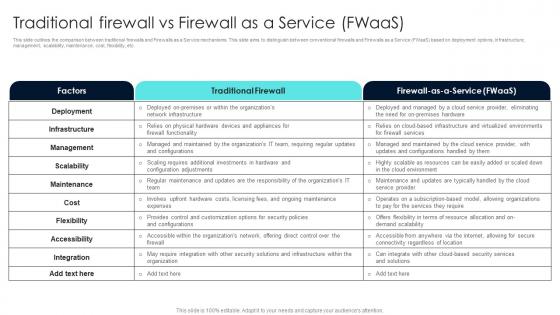 Firewall Network Security Traditional Firewall Vs Firewall As A Service FWaas
Firewall Network Security Traditional Firewall Vs Firewall As A Service FWaasThis slide outlines the comparison between traditional firewalls and Firewalls as a Service mechanisms. This slide aims to distinguish between conventional firewalls and Firewalls as a Service FWaaS based on deployment options, infrastructure, management, scalability, maintenance, cost, flexibility, etc. Present the topic in a bit more detail with this Firewall Network Security Traditional Firewall Vs Firewall As A Service FWaas Use it as a tool for discussion and navigation on Traditional Firewall, Factors, Maintenance This template is free to edit as deemed fit for your organization. Therefore download it now.
-
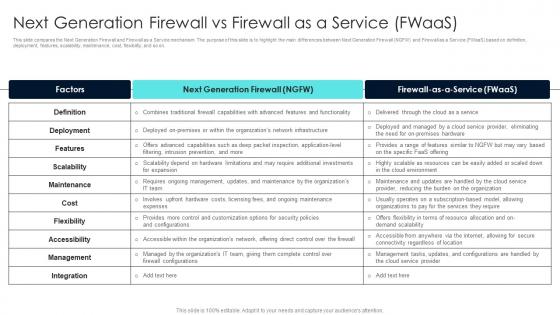 Firewall Network Security Next Generation Firewall Vs Firewall As A Service FWaas
Firewall Network Security Next Generation Firewall Vs Firewall As A Service FWaasThis slide compares the Next Generation Firewall and Firewall as a Service mechanism. The purpose of this slide is to highlight the main differences between Next Generation Firewall NGFW and Firewall as a Service FWaas based on definition, deployment, features, scalability, maintenance, cost, flexibility, and so on. Deliver an outstanding presentation on the topic using this Firewall Network Security Next Generation Firewall Vs Firewall As A Service FWaas Dispense information and present a thorough explanation of Make Decisions, Protocol Usage, Passing Through, Implementing These Policies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
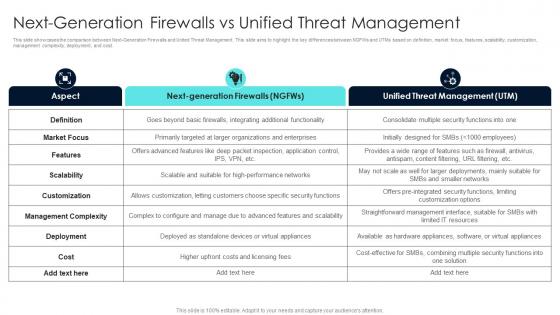 Firewall Network Security Next Generation Firewalls Vs Unified Threat Management
Firewall Network Security Next Generation Firewalls Vs Unified Threat ManagementThis slide showcases the comparison between Next-Generation Firewalls and United Threat Management. This slide aims to highlight the key differences between NGFWs and UTMs based on definition, market focus, features, scalability, customization, management complexity, deployment, and cost. Present the topic in a bit more detail with this Firewall Network Security Next Generation Firewalls Vs Unified Threat Management Use it as a tool for discussion and navigation on Firewall, Features, Providers This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Tokenization For Improved Data Security Before Vs After Implementing Tokenization In Data Security
Tokenization For Improved Data Security Before Vs After Implementing Tokenization In Data SecurityThis slide showcases the comparative analysis of the before versus after tokenization. The purpose of this slide is to showcase the different performance metrics and how tokenization has improved these metrics. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Before Vs After Implementing Tokenization In Data Security. Dispense information and present a thorough explanation of Compliance With Regulations, Reduced Insider Threats, Exposure Of Sensitive Data using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
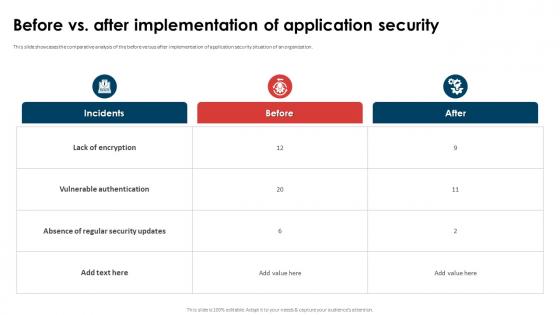 Application Security Implementation Plan Before Vs After Implementation Of Application Security
Application Security Implementation Plan Before Vs After Implementation Of Application SecurityThis slide showcases the comparative analysis of the before versus after implementation of application security situation of an organization. Deliver an outstanding presentation on the topic using this Application Security Implementation Plan Before Vs After Implementation Of Application Security. Dispense information and present a thorough explanation of Lack Of Encryption, Vulnerable Authentication, Absence Of Regular Security Updates using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
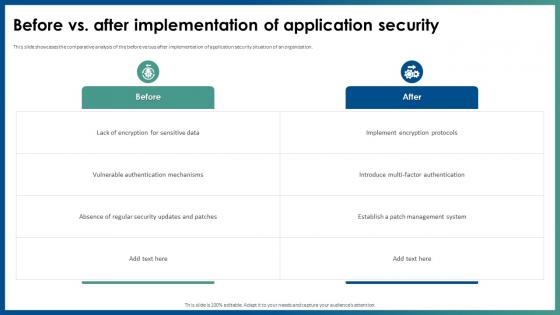 Before Vs After Implementation Of Application Security
Before Vs After Implementation Of Application SecurityThis slide discusses the overview of authorization in application security for authorized access of resource. Introducing Before Vs After Implementation Of Application Security to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Implement Encryption Protocols, Patch Management System, Vulnerable Authentication Mechanisms, using this template. Grab it now to reap its full benefits.
-
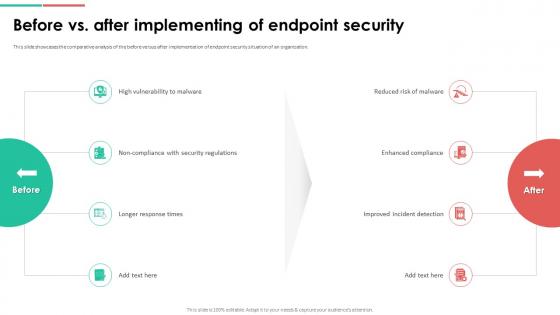 Endpoint Security Before Vs After Implementing Of Endpoint Security
Endpoint Security Before Vs After Implementing Of Endpoint SecurityThis slide showcases the comparative analysis of the before versus after implementation of endpoint security situation of an organization. Increase audience engagement and knowledge by dispensing information using Endpoint Security Before Vs After Implementing Of Endpoint Security. This template helps you present information on four stages. You can also present information on Enhanced Compliance, Improved Incident Detection, High Vulnerability To Malware using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
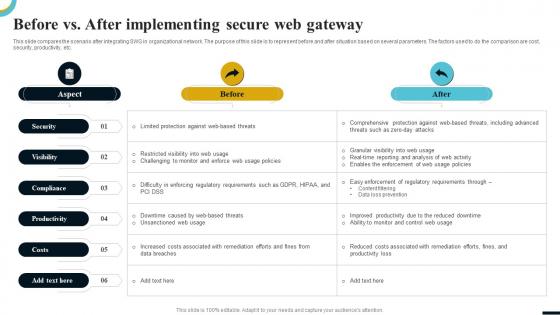 Internet Gateway Security IT Before Vs After Implementing Secure Web
Internet Gateway Security IT Before Vs After Implementing Secure WebThis slide compares the scenario after integrating SWG in organizational network. The purpose of this slide is to represent before and after situation based on several parameters. The factors used to do the comparison are cost, security, productivity, etc. Present the topic in a bit more detail with this Internet Gateway Security IT Before Vs After Implementing Secure Web. Use it as a tool for discussion and navigation on Security, Visibility, Compliance, Productivity, Costs. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Secured Line Credit Vs Unsecured Line Credit Ppt Professional Styles Cpb
Secured Line Credit Vs Unsecured Line Credit Ppt Professional Styles CpbPresenting our Secured Line Credit Vs Unsecured Line Credit Ppt Professional Styles Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Secured Line Credit Vs Unsecured Line Credit. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
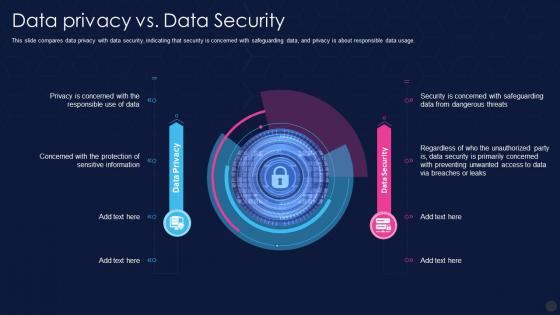 F41 Data Privacy It Data Privacy Vs Data Security
F41 Data Privacy It Data Privacy Vs Data SecurityThis slide compares data privacy with data security, indicating that security is concerned with safeguarding data, and privacy is about responsible data usage. Deliver an outstanding presentation on the topic using this F41 Data Privacy It Data Privacy Vs Data Security. Dispense information and present a thorough explanation of Information, Unauthorized, Dangerous using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Siem For Security Analysis Sim Vs Sem Vs Siem
Siem For Security Analysis Sim Vs Sem Vs SiemPresent the topic in a bit more detail with this Siem For Security Analysis Sim Vs Sem Vs Siem. Use it as a tool for discussion and navigation on Information, Management, Capabilities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Holding Deposit Vs Security Deposit Ppt Powerpoint Presentation Professional Graphics Design Cpb
Holding Deposit Vs Security Deposit Ppt Powerpoint Presentation Professional Graphics Design CpbPresenting our Holding Deposit Vs Security Deposit Ppt Powerpoint Presentation Professional Graphics Design Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Holding Deposit vs Security Deposit This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Secured Vs Unsecured Credit Cards Ppt Powerpoint Presentation Inspiration Cpb
Secured Vs Unsecured Credit Cards Ppt Powerpoint Presentation Inspiration CpbPresenting our Secured Vs Unsecured Credit Cards Ppt Powerpoint Presentation Inspiration Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Secured Vs Unsecured Credit Cards This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Network Security VS Cyber Security Ppt Powerpoint Presentation Slides Diagrams Cpb
Network Security VS Cyber Security Ppt Powerpoint Presentation Slides Diagrams CpbPresenting Network Security VS Cyber Security Ppt Powerpoint Presentation Slides Diagrams Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Network Security VS Cyber Security. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Debit Cart Vs Credit Card Security Ppt Powerpoint Presentation File Inspiration Cpb
Debit Cart Vs Credit Card Security Ppt Powerpoint Presentation File Inspiration CpbPresenting our Debit Cart Vs Credit Card Security Ppt Powerpoint Presentation File Inspiration Cpb PowerPoint template design. This PowerPoint slide showcases eight stages. It is useful to share insightful information on Debit Cart Vs Credit Card Security This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Debit Card VS Credit Card Security Ppt Powerpoint Presentation Outline Graphic Cpb
Debit Card VS Credit Card Security Ppt Powerpoint Presentation Outline Graphic CpbPresenting Debit Card VS Credit Card Security Ppt Powerpoint Presentation Outline Graphic Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Debit Card VS Credit Card Security. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Intranet Vs Internet Security Ppt Powerpoint Presentation File Gallery Cpb
Intranet Vs Internet Security Ppt Powerpoint Presentation File Gallery CpbPresenting Intranet Vs Internet Security Ppt Powerpoint Presentation File Gallery Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase nine stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Intranet Vs Internet Security. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Secured line credit vs unsecured ppt powerpoint presentation file outline cpb
Secured line credit vs unsecured ppt powerpoint presentation file outline cpbPresenting Secured Line Credit Vs Unsecured Ppt Powerpoint Presentation File Outline Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Secured Line Credit Vs Unsecured. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Real time analysis of security alerts sim vs sem vs siem
Real time analysis of security alerts sim vs sem vs siemDeliver an outstanding presentation on the topic using this Real Time Analysis Of Security Alerts Sim Vs Sem Vs Siem. Dispense information and present a thorough explanation of Security, Information, Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
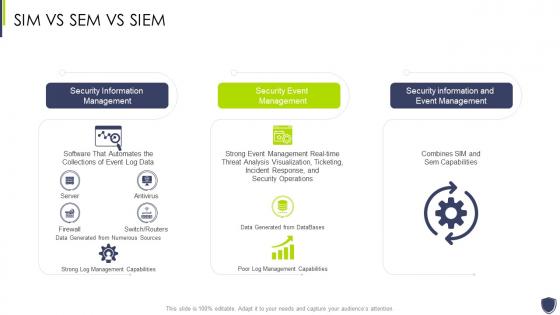 Improve it security with vulnerability management sim vs sem vs siem
Improve it security with vulnerability management sim vs sem vs siemDeliver an outstanding presentation on the topic using this Improve It Security With Vulnerability Management Sim Vs Sem Vs Siem. Dispense information and present a thorough explanation of Security, Information, Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.


