Powerpoint Templates and Google slides for Stage Attack
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
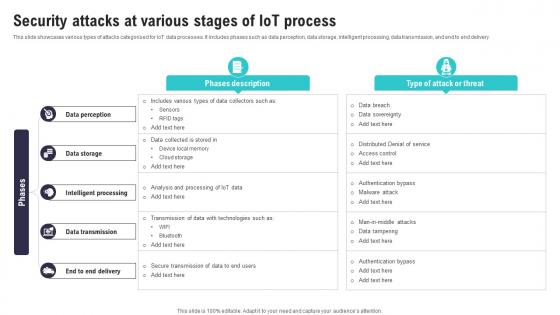 Security Attacks At Various Stages Of IoT Process IoT Security And Privacy Safeguarding IoT SS
Security Attacks At Various Stages Of IoT Process IoT Security And Privacy Safeguarding IoT SSThis slide showcases various types of attacks categorised for IoT data processes. It includes phases such as data perception, data storage, intelligent processing, data transmission, and end to end delivery. Present the topic in a bit more detail with this Security Attacks At Various Stages Of IoT Process IoT Security And Privacy Safeguarding IoT SS. Use it as a tool for discussion and navigation on Intelligent Processing, Data Transmission, Transmission Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
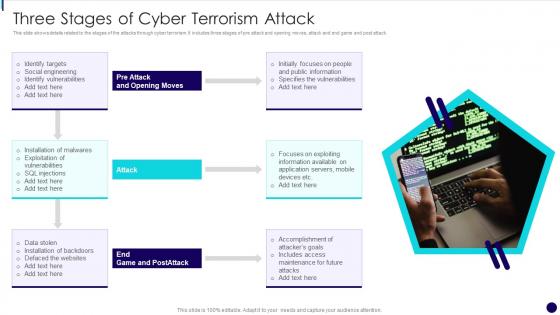 Three Stages Of Cyber Terrorism Attack
Three Stages Of Cyber Terrorism AttackThis slide shows details related to the stages of the attacks through cyber terrorism. It includes three stages of pre attack and opening moves, attack and end game and post attack. Presenting our set of slides with name Three Stages Of Cyber Terrorism Attack. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Social Engineering, Identify Vulnerabilities, Exploitation Of Vulnerabilities, Data Stolen.
-
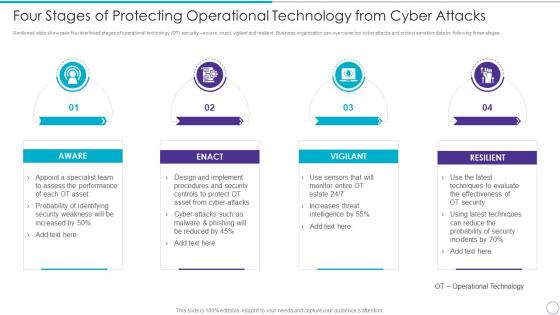 Four Stages Of Protecting Operational Technology From Cyber Attacks
Four Stages Of Protecting Operational Technology From Cyber AttacksMentioned slide showcase four interlinked stages of operational technology OT security aware, enact, vigilant and resilient. Business organization can overcome top cyber attacks and protect sensitive data by following these stages. Increase audience engagement and knowledge by dispensing information using four Stages Of Protecting Operational Technology From Cyber Attacks. This template helps you present information on four stages. You can also present information on Aware, Enact, Vigilant, Resilient using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Stages Of Botnet Malware Cybercriminal Attacks
Stages Of Botnet Malware Cybercriminal AttacksThis slide illustrates how to create a bot and orchestrating a botnet attack. It includes stages such as expose, infect and grow, activate, etc. Introducing our premium set of slides with Stages Of Botnet Malware Cybercriminal Attacks. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Expose, Infect And Grow, Activate. So download instantly and tailor it with your information.
-
 Order Stages Attacker Methodology In Powerpoint And Google Slides Cpb
Order Stages Attacker Methodology In Powerpoint And Google Slides CpbPresenting Order Stages Attacker Methodology In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase six stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Order Stages Attacker Methodology. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
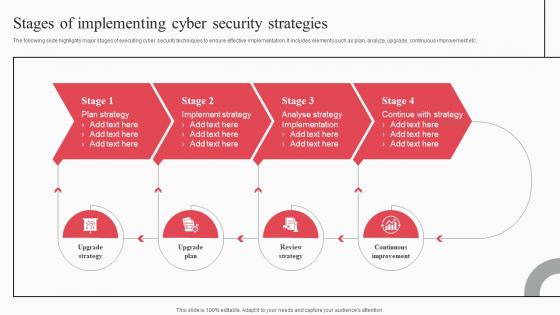 Stages Of Implementing Cyber Security Strategies Cyber Attack Risks Mitigation
Stages Of Implementing Cyber Security Strategies Cyber Attack Risks MitigationThe following slide highlights major stages of executing cyber security techniques to ensure effective implementation. It includes elements such as plan, analyze, upgrade, continuous improvement etc. Increase audience engagement and knowledge by dispensing information using Stages Of Implementing Cyber Security Strategies Cyber Attack Risks Mitigation. This template helps you present information on four stages. You can also present information on Plan Strategy, Implement Strategy, Analyse Strategy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Various Stages Of Web Malware Attack
Various Stages Of Web Malware AttackThis templates shows the different phases of a web malware attack. The purpose of this slide to give brief pictures regarding approximately how much sites are hacked and recovered . The phase starts withs entry point and ends with execution.Presenting our well structured Various Stages Of Web Malware Attack. The topics discussed in this slide are Flex Techniques, Personal Information, Credential Banking. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.

