Powerpoint Templates and Google slides for Technology Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
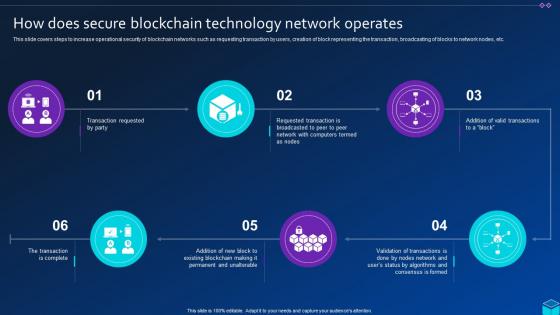 How Does Secure Blockchain Technology Comprehensive Approach To Privacy BCT SS
How Does Secure Blockchain Technology Comprehensive Approach To Privacy BCT SSThis slide covers steps to increase operational security of blockchain networks such as requesting transaction by users, creation of block representing the transaction, broadcasting of blocks to network nodes, etc. Introducing How Does Secure Blockchain Technology Comprehensive Approach To Privacy BCT SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Secure Blockchain Technology, Network Operates, using this template. Grab it now to reap its full benefits.
-
 Technological Trends Used For Enhancing Information Security Management
Technological Trends Used For Enhancing Information Security ManagementThis slide represents various technologies that help organizations enhance information security management and reduce data loss incidents. It includes strategies such as user behavior analytics, cloud access security brokers, etc. Presenting our well structured Technological Trends Used For Enhancing Information Security Management. The topics discussed in this slide are Security Testing Devops, User Behavior Analytics, Cloud Access Security Brokers. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
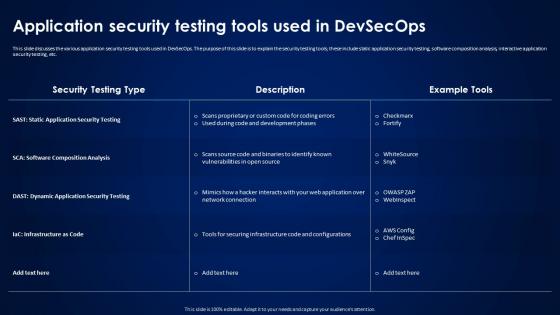 Devsecops Best Practices For Secure Application Security Testing Tools Used In Devsecops
Devsecops Best Practices For Secure Application Security Testing Tools Used In DevsecopsThis slide discusses the various application security testing tools used in DevSecOps. The purpose of this slide is to explain the security testing tools, these include static application security testing, software composition analysis, interactive application security testing, etc. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure Application Security Testing Tools Used In Devsecops. Dispense information and present a thorough explanation of Application Security Testing, Dynamic Application Security Testing, Infrastructure As Code using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
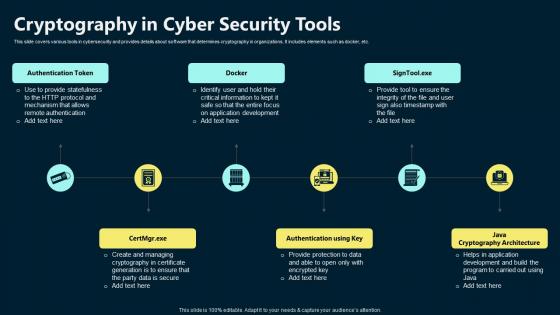 Cryptography In Cyber Security Tools
Cryptography In Cyber Security ToolsThis slide covers various tools in cybersecurity and provides details about software that determines cryptography in organizations. It includes elements such as docker Introducing our premium set of slides with Cryptography In Cyber Security Tools. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Authentication Token, Authentication Using Key, Java Cryptography Architecture. So download instantly and tailor it with your information.
-
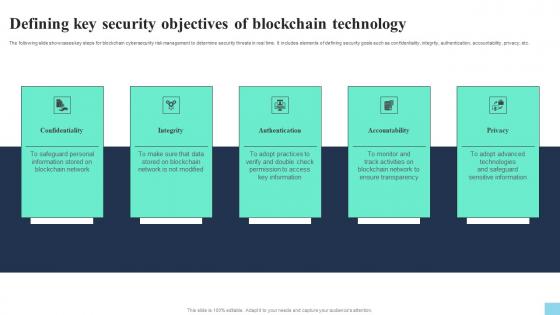 Defining Key Security Objectives Of Blockchain Technology Hands On Blockchain Security Risk BCT SS V
Defining Key Security Objectives Of Blockchain Technology Hands On Blockchain Security Risk BCT SS VThe following slide showcases key steps for blockchain cybersecurity risk management to determine security threats in real time. It includes elements of defining security goals such as confidentiality, integrity, authentication, accountability, privacy, etc. Increase audience engagement and knowledge by dispensing information using Defining Key Security Objectives Of Blockchain Technology Hands On Blockchain Security Risk BCT SS V. This template helps you present information on five stages. You can also present information on Confidentiality, Integrity, Authentication using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
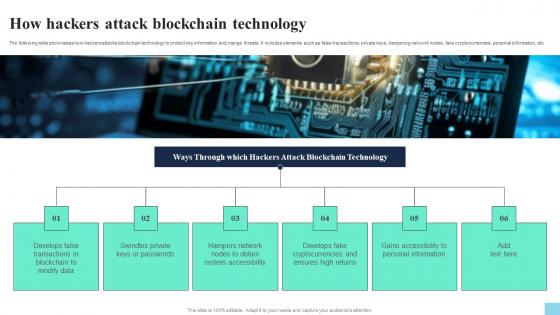 How Hackers Attack Blockchain Technology Hands On Blockchain Security Risk BCT SS V
How Hackers Attack Blockchain Technology Hands On Blockchain Security Risk BCT SS VThe following slide showcases how hackers attacks blockchain technology to protect key information and mange threats. It includes elements such as false transactions, private keys, hampering network nodes, fake cryptocurrencies, personal information, etc. Introducing How Hackers Attack Blockchain Technology Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Modify Data, Swindles Private, System Accessibility, using this template. Grab it now to reap its full benefits.
-
 Importance Of Cybersecurity In Blockchain Technology Hands On Blockchain Security Risk BCT SS V
Importance Of Cybersecurity In Blockchain Technology Hands On Blockchain Security Risk BCT SS VThe following slide highlights how blockchain cybersecurity is important to boost security and prevent cyberattacks. It includes elements such as decentralized architecture, immutable records, public key cryptography, smart contracts, etc. Introducing Importance Of Cybersecurity In Blockchain Technology Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Decentralized Architecture, Public Key Cryptography, Smart Contracts, using this template. Grab it now to reap its full benefits.
-
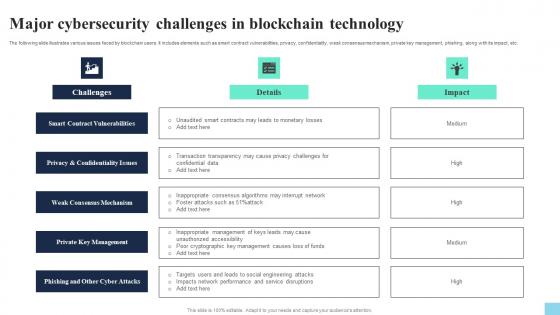 Major Cybersecurity Challenges In Blockchain Technology Hands On Blockchain Security Risk BCT SS V
Major Cybersecurity Challenges In Blockchain Technology Hands On Blockchain Security Risk BCT SS VThe following slide illustrates various issues faced by blockchain users. It includes elements such as smart contract vulnerabilities, privacy, confidentiality, weak consensus mechanism, private key management, phishing, along with its impact, etc. Introducing Major Cybersecurity Challenges In Blockchain Technology Hands On Blockchain Security Risk BCT SS V to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Smart Contract Vulnerabilities, Weak Consensus Mechanism, Private Key Management, using this template. Grab it now to reap its full benefits.
-
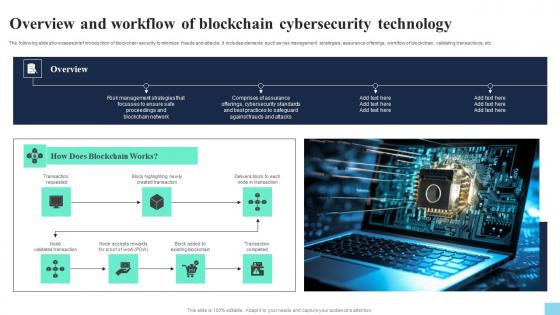 Overview And Workflow Of Blockchain Cybersecurity Technology Hands On Blockchain Security Risk BCT SS V
Overview And Workflow Of Blockchain Cybersecurity Technology Hands On Blockchain Security Risk BCT SS VThe following slide showcases brief introduction of blockchain security to minimize frauds and attacks. It includes elements such as risk management strategies, assurance offerings, workflow of blockchain, validating transactions, etc. Increase audience engagement and knowledge by dispensing information using Overview And Workflow Of Blockchain Cybersecurity Technology Hands On Blockchain Security Risk BCT SS V. This template helps you present information on seven stages. You can also present information on Transaction Requested, Created Transaction, Existing Blockchain using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
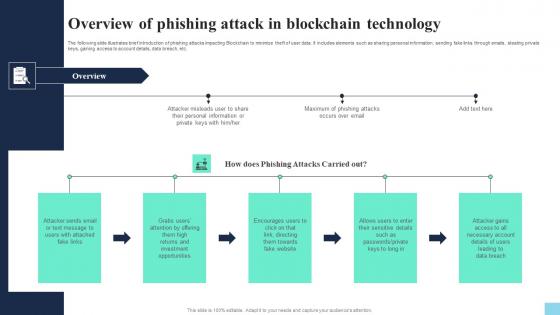 Overview Of Phishing Attack In Blockchain Technology Hands On Blockchain Security Risk BCT SS V
Overview Of Phishing Attack In Blockchain Technology Hands On Blockchain Security Risk BCT SS VThe following slide illustrates brief introduction of phishing attacks impacting Blockchain to minimize theft of user data. It includes elements such as sharing personal information, sending fake links through emails, stealing private keys, gaining access to account details, data breach, etc. Increase audience engagement and knowledge by dispensing information using Overview Of Phishing Attack In Blockchain Technology Hands On Blockchain Security Risk BCT SS V. This template helps you present information on five stages. You can also present information on Fake Links, Investment Opportunities, Towards Fake Website using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Current Trending Technologies Cyber Security Technology Market Overview
Current Trending Technologies Cyber Security Technology Market OverviewThis slide explains Cyber security technology market overview with top players in the year 2021. It also predicts market growth and compound annual growth rate from year 2021 till 2028. Deliver an outstanding presentation on the topic using this Current Trending Technologies Cyber Security Technology Market Overview. Dispense information and present a thorough explanation of Cyber Security Technology, Market Growth, Compound Annual Growth Rate, Business Continuity using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Current Trending Technologies Need For Cyber Security Technology
Current Trending Technologies Need For Cyber Security TechnologyThis slide gives an overview of cyber security technology. It also gives an idea about which industries are most venerable for a cyber attack and why cyber security is needed. Increase audience engagement and knowledge by dispensing information using Current Trending Technologies Need For Cyber Security Technology. This template helps you present information on three stages. You can also present information on Cyber Security Technology, Prevention Of Cybercrime, Protection Of Sensitive Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Current Trending Technologies Objectives Of Cyber Security Technology
Current Trending Technologies Objectives Of Cyber Security TechnologyThis slide explains the objectives of cyber security technology such as confidentiality, integrity and availability. It also talks about the three goals and how they collectively ensures the data protection. Introducing Current Trending Technologies Objectives Of Cyber Security Technology to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Confidentiality, Cyber Security Technology, Data Protection, Integrity And Availability, using this template. Grab it now to reap its full benefits.
-
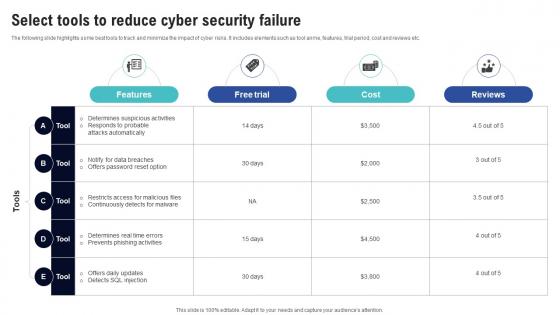 Select Tools To Reduce Cyber Security Failure Creating Cyber Security Awareness
Select Tools To Reduce Cyber Security Failure Creating Cyber Security AwarenessThe following slide highlights some best tools to track and minimize the impact of cyber risks. It includes elements such as tool anme, features, trial period, cost and reviews etc. Deliver an outstanding presentation on the topic using this Select Tools To Reduce Cyber Security Failure Creating Cyber Security Awareness Dispense information and present a thorough explanation of Duration, Mode, Start Date, End Date using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Drone Technology Icon For Security Surveillance
Drone Technology Icon For Security SurveillancePresenting our well structured Drone Technology Icon For Security Surveillance. The topics discussed in this slide are Drone Technology Icon, Security Surveillance. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
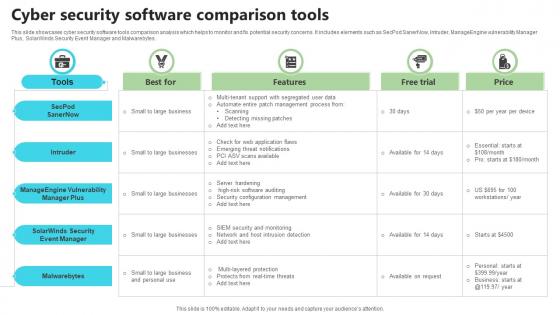 Cyber Security Software Comparison Tools
Cyber Security Software Comparison ToolsThis slide showcases cyber security software tools comparison analysis which helps to monitor and fix potential security concerns. It includes elements such as SecPod SanerNow, Intruder, ManageEngine vulnerability Manager Plus, SolarWinds Security Event Manager and Malwarebytes. Presenting our well structured Cyber Security Software Comparison Tools. The topics discussed in this slide are Best For Features, Free Trial. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
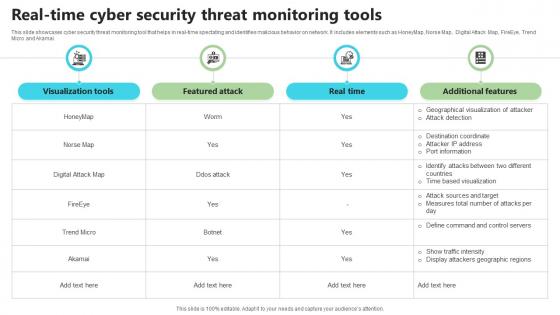 Real Time Cyber Security Threat Monitoring Tools
Real Time Cyber Security Threat Monitoring ToolsThis slide showcases cyber security threat monitoring tool that helps in real-time spectating and identifies malicious behavior on network. It includes elements such as HoneyMap, Norse Map, Digital Attack Map, FireEye, Trend Micro and Akamai. Presenting our well structured Real Time Cyber Security Threat Monitoring Tools. The topics discussed in this slide are Visualization Tools, Real Time, Additional Features. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Banking Solutions For Improving Customer Mobile Banking Application Security Testing Tools Fin SS V
Banking Solutions For Improving Customer Mobile Banking Application Security Testing Tools Fin SS VThis slide shows various tools which can be used to evaluate or analyze the security level of mobile banking apps. It includes features and ratings of applications. It also contains various tools such as ImmuniWeb MobileSuite, CodifiedSecurity, QARK, etc. Present the topic in a bit more detail with this Banking Solutions For Improving Customer Mobile Banking Application Security Testing Tools Fin SS V. Use it as a tool for discussion and navigation on Mobile Banking Application, Security Testing Tools, Mobile Banking Apps, Real Time Bot Protection. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
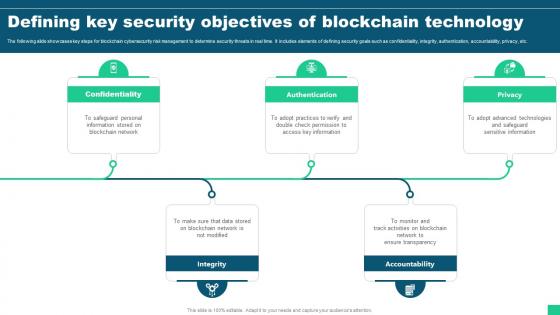 Defining Key Security Objectives Of Blockchain Technology Guide For Blockchain BCT SS V
Defining Key Security Objectives Of Blockchain Technology Guide For Blockchain BCT SS VThe following slide showcases key steps for blockchain cybersecurity risk management to determine security threats in real time. It includes elements of defining security goals such as confidentiality, integrity, authentication, accountability, privacy, etc. Introducing Defining Key Security Objectives Of Blockchain Technology Guide For Blockchain BCT SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Confidentiality, Authentication, Integrity, Accountability using this template. Grab it now to reap its full benefits.
-
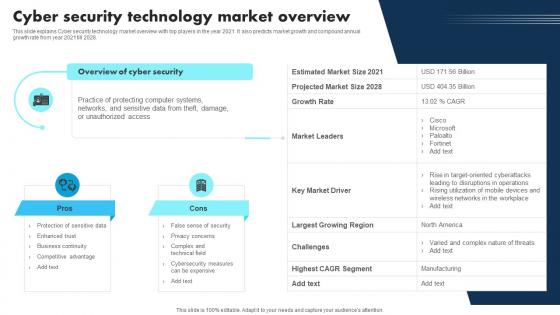 New Technologies Cyber Security Technology Market Overview
New Technologies Cyber Security Technology Market OverviewThis slide explains Cyber security technology market overview with top players in the year 2021. It also predicts market growth and compound annual growth rate from year 2021 till 2028. Present the topic in a bit more detail with this New Technologies Cyber Security Technology Market Overview. Use it as a tool for discussion and navigation on Technology, Overview, Cyber Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 New Technologies Need For Cyber Security Technology
New Technologies Need For Cyber Security TechnologyThis slide gives an overview of cyber security technology. It also gives an idea about which industries are most venerable for a cyber attack and why cyber security is needed. Deliver an outstanding presentation on the topic using this New Technologies Need For Cyber Security Technology. Dispense information and present a thorough explanation of Technology, Information, Protecting using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
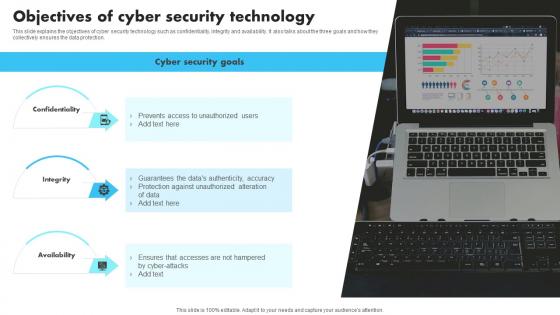 New Technologies Objectives Of Cyber Security Technology
New Technologies Objectives Of Cyber Security TechnologyThis slide explains the objectives of cyber security technology such as confidentiality, integrity and availability. It also talks about the three goals and how they collectively ensures the data protection. Introducing New Technologies Objectives Of Cyber Security Technology to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Confidentiality, Technology, Availability, using this template. Grab it now to reap its full benefits.
-
 Security Implications For Face Recognition Technology
Security Implications For Face Recognition TechnologyThe slide aims to explain the advanced architecture of a face recognition system, optimizing accuracy and performance for robust facial identification. Presenting our set of slides with Security Implications For Face Recognition Technology. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Authentication Security, Spoofing Protection, Encryption.
-
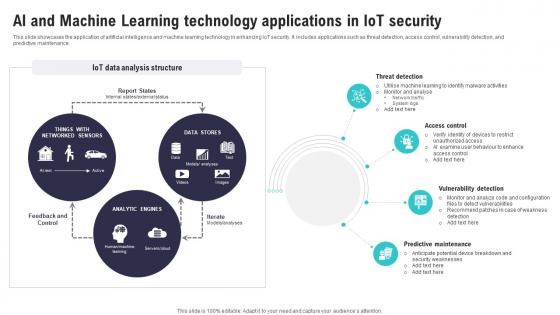 Ai And Machine Learning Technology IoT Security And Privacy Safeguarding IoT SS
Ai And Machine Learning Technology IoT Security And Privacy Safeguarding IoT SSThis slide showcases the application of artificial intelligence and machine learning technology in enhancing IoT security. It includes applications such as threat detection, access control, vulnerability detection, and predictive maintenance. Deliver an outstanding presentation on the topic using this Ai And Machine Learning Technology IoT Security And Privacy Safeguarding IoT SS. Dispense information and present a thorough explanation of Threat Detection, Access Control, Vulnerability Detection using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
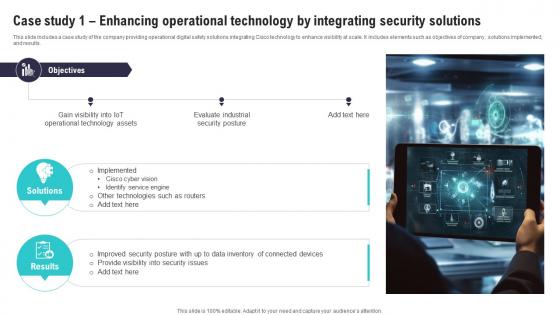 Case Study 1 Enhancing Operational Technology IoT Security And Privacy Safeguarding IoT SS
Case Study 1 Enhancing Operational Technology IoT Security And Privacy Safeguarding IoT SSThis slide includes a case study of the company providing operational digital safety solutions integrating Cisco technology to enhance visibility at scale. It includes elements such as objectives of company , solutions implemented, and results. Introducing Case Study 1 Enhancing Operational Technology IoT Security And Privacy Safeguarding IoT SS to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Operational Technology, Identify Service Engine, Security Posture, using this template. Grab it now to reap its full benefits.
-
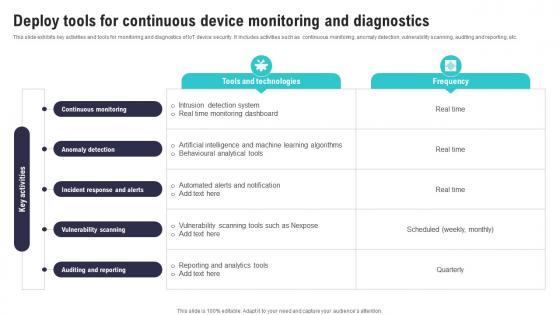 Deploy Tools For Continuous Device Monitoring IoT Security And Privacy Safeguarding IoT SS
Deploy Tools For Continuous Device Monitoring IoT Security And Privacy Safeguarding IoT SSThis slide exhibits key activities and tools for monitoring and diagnostics of IoT device security. It includes activities such as continuous monitoring, anomaly detection, vulnerability scanning, auditing and reporting, etc. Present the topic in a bit more detail with this Deploy Tools For Continuous Device Monitoring IoT Security And Privacy Safeguarding IoT SS. Use it as a tool for discussion and navigation on Vulnerability Scanning, Auditing Reporting, Anomaly Detection . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
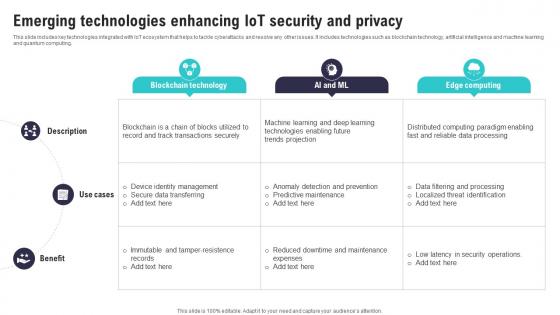 Emerging Technologies Enhancing IoT Security And IoT Security And Privacy Safeguarding IoT SS
Emerging Technologies Enhancing IoT Security And IoT Security And Privacy Safeguarding IoT SSThis slide includes key technologies integrated with IoT ecosystem that helps to tackle cyberattacks and resolve any other issues. It includes technologies such as blockchain technology, artificial intelligence and machine learning and quantum computing.Present the topic in a bit more detail with this Emerging Technologies Enhancing IoT Security And IoT Security And Privacy Safeguarding IoT SS. Use it as a tool for discussion and navigation on Transactions Securely, Identity Management, Predictive Maintenance. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
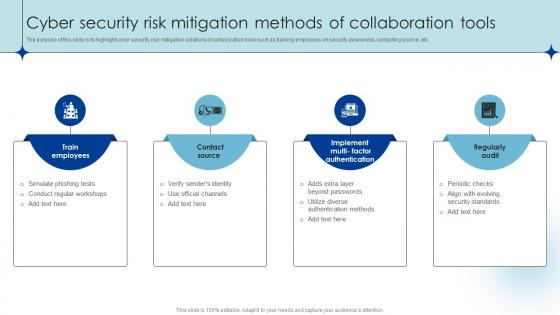 Cyber Security Risk Mitigation Methods Of Collaboration Tools
Cyber Security Risk Mitigation Methods Of Collaboration ToolsThe purpose of this slide is to highlight cyber security risk mitigation solutions of collaboration tools such as training employees on security awareness, contacting source, etc. Introducing our premium set of slides with Cyber Security Risk Mitigation Methods Of Collaboration Tools. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Simulate Phishing Tests, Verify Senders Identity, Use Official Channels . So download instantly and tailor it with your information.
-
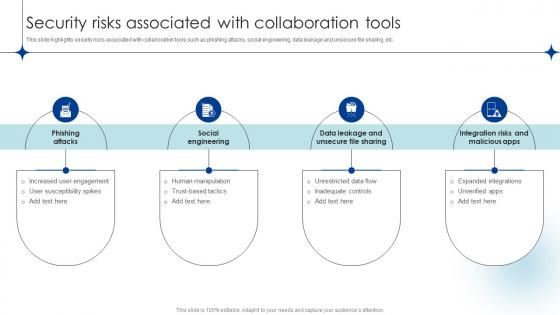 Security Risks Associated With Collaboration Tools
Security Risks Associated With Collaboration ToolsThis slide highlights security risks associated with collaboration tools such as phishing attacks, social engineering, data leakage and unsecure file sharing, etc. Presenting our set of slides with Security Risks Associated With Collaboration Tools. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Phishing Attacks, Social Engineering, Unrestricted Data Flow, Human Manipulation .
-
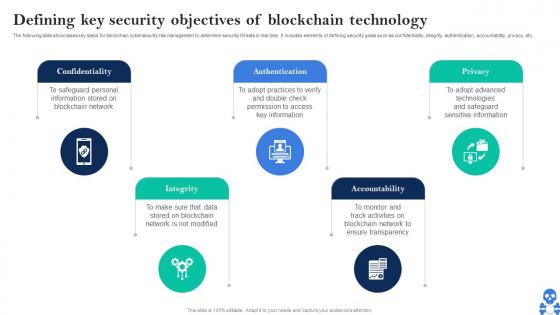 Cyber Threats In Blockchain Defining Key Security Objectives Of Blockchain Technology BCT SS V
Cyber Threats In Blockchain Defining Key Security Objectives Of Blockchain Technology BCT SS VThe following slide showcases key steps for blockchain cybersecurity risk management to determine security threats in real time. It includes elements of defining security goals such as confidentiality, integrity, authentication, accountability, privacy, etc. Introducing Cyber Threats In Blockchain Defining Key Security Objectives Of Blockchain Technology BCT SS V to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Confidentiality, Integrity, Authentication using this template. Grab it now to reap its full benefits.
-
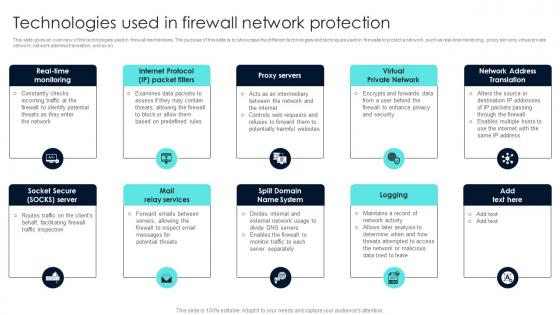 Firewall Network Security Technologies Used In Firewall Network Protection
Firewall Network Security Technologies Used In Firewall Network ProtectionThis slide gives an overview of the technologies used in firewall mechanisms. The purpose of this slide is to showcase the different technologies and techniques used in firewalls to protect a network, such as real-time monitoring, proxy servers, virtual private network, network address translation, and so on. Introducing Firewall Network Security Technologies Used In Firewall Network Protection to increase your presentation threshold. Encompassed with Eight stages, this template is a great option to educate and entice your audience. Dispence information on Packet Filters, Proxy Servers, Virtual Private Network using this template. Grab it now to reap its full benefits.
-
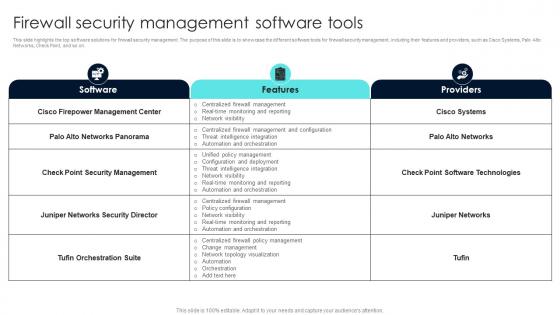 Firewall Network Security Firewall Security Management Software Tools
Firewall Network Security Firewall Security Management Software ToolsThis slide highlights the top software solutions for firewall security management. The purpose of this slide is to showcase the different software tools for firewall security management, including their features and providers, such as Cisco Systems, Palo Alto Networks, Check Point, and so on. Deliver an outstanding presentation on the topic using this Firewall Network Security Firewall Security Management Software Tools Dispense information and present a thorough explanation of General Features, Host-Level Features using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Select Tools To Reduce Cyber Security Failure Implementing Cyber Risk Management Process
Select Tools To Reduce Cyber Security Failure Implementing Cyber Risk Management ProcessThe following slide highlights some best tools to track and minimize the impact of cyber risks. It includes elements such as tool anme, features, trial period, cost and reviews etc. Deliver an outstanding presentation on the topic using this Select Tools To Reduce Cyber Security Failure Implementing Cyber Risk Management Process. Dispense information and present a thorough explanation of Features, Free Trial, Cost using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
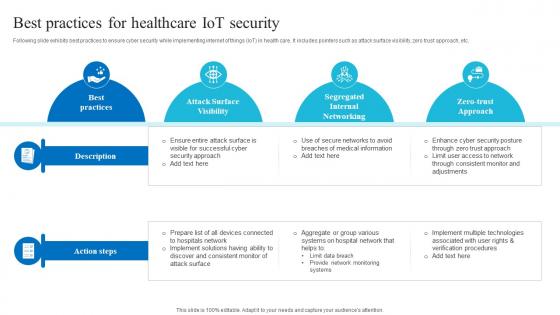 Best For Healthcare Iot Security Role Of Iot And Technology In Healthcare Industry IoT SS V
Best For Healthcare Iot Security Role Of Iot And Technology In Healthcare Industry IoT SS VFollowing slide exhibits best practices to ensure cyber security while implementing internet of things IoT in health care. It includes pointers such as attack surface visibility, zero trust approach, etc. Deliver an outstanding presentation on the topic using this Best For Healthcare Iot Security Role Of Iot And Technology In Healthcare Industry IoT SS V. Dispense information and present a thorough explanation of Attack Surface Visibility, Segregated Internal Networking, Zero Trust Approach using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
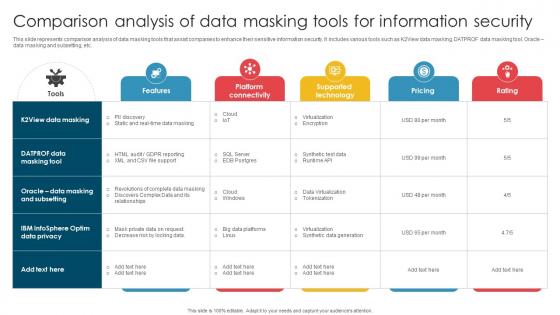 Comparison Analysis Of Data Masking Tools For Information Security
Comparison Analysis Of Data Masking Tools For Information SecurityThis slide represents comparison analysis of data masking tools that assist companies to enhance their sensitive information security. It includes various tools such as K2View data masking, DATPROF data masking tool, Oracle data masking and subsetting, etc. Presenting our well structured Comparison Analysis Of Data Masking Tools For Information Security. The topics discussed in this slide are Virtualization, Synthetic Data Generation, Tokenization. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
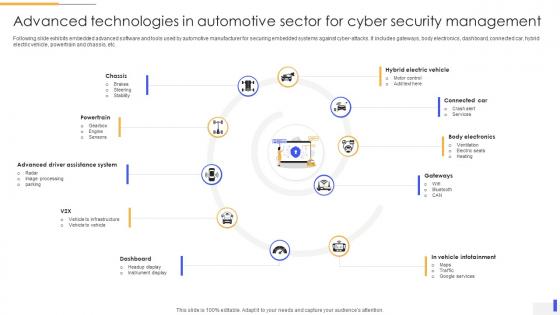 Advanced Technologies In Automotive Sector For Cyber Security Management
Advanced Technologies In Automotive Sector For Cyber Security ManagementFollowing slide exhibits embedded advanced software and tools used by automotive manufacturer for securing embedded systems against cyber-attacks. It includes gateways, body electronics, dashboard, connected car, hybrid electric vehicle, powertrain and chassis, etc. Presenting our set of slides with Advanced Technologies In Automotive Sector For Cyber Security Management. This exhibits information on ten stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Advanced Driver Assistance System, Hybrid Electric Vehicle, Connected Car.
-
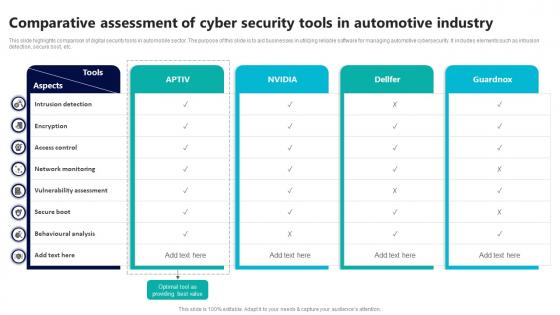 Comparative Assessment Of Cyber Security Tools In Automotive Industry
Comparative Assessment Of Cyber Security Tools In Automotive IndustryThis slide highlights comparison of digital security tools in automobile sector. The purpose of this slide is to aid businesses in utilizing reliable software for managing automotive cybersecurity. It includes elements such as intrusion detection, secure boot, etc. Introducing our Comparative Assessment Of Cyber Security Tools In Automotive Industry set of slides. The topics discussed in these slides are Intrusion Detection, Access Control, Network Monitoring This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Icon For Role Of 5g Technology In Automotive Cyber Security
Icon For Role Of 5g Technology In Automotive Cyber SecurityIntroducing our premium set of slides with Icon For Role Of 5g Technology In Automotive Cyber Security Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Icon For Role, 5G Technology In Automotive, Cyber Security So download instantly and tailor it with your information.
-
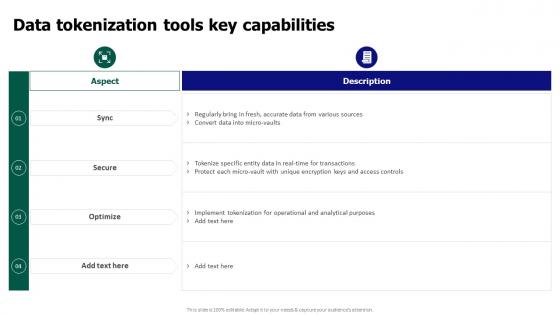 Tokenization For Improved Data Security Data Tokenization Tools Key Capabilities
Tokenization For Improved Data Security Data Tokenization Tools Key CapabilitiesPresent the topic in a bit more detail with this Tokenization For Improved Data Security Data Tokenization Tools Key Capabilities. Use it as a tool for discussion and navigation on Data Tokenization Tools, Key Capabilities, Operational And Analytical Purposes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
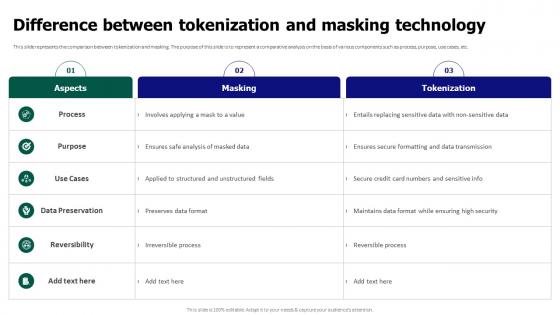 Tokenization For Improved Data Security Difference Between Tokenization And Masking Technology
Tokenization For Improved Data Security Difference Between Tokenization And Masking TechnologyThis slide represents the comparison between tokenization and masking. The purpose of this slide is to represent a comparative analysis on the basis of various components such as process, purpose, use cases, etc. Deliver an outstanding presentation on the topic using this Tokenization For Improved Data Security Difference Between Tokenization And Masking Technology. Dispense information and present a thorough explanation of Data Preservation, Masking Technology, Maintains Data Format using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
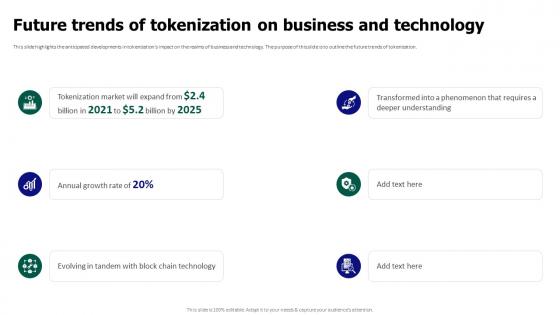 Tokenization For Improved Data Security Future Trends Of Tokenization On Business And Technology
Tokenization For Improved Data Security Future Trends Of Tokenization On Business And TechnologyThis slide highlights the anticipated developments in tokenizations impact on the realms of business and technology. The purpose of this slide is to outline the future trends of tokenization. Introducing Tokenization For Improved Data Security Future Trends Of Tokenization On Business And Technology to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Anticipated Developments, Business And Technology, Future Trends Of Tokenization, using this template. Grab it now to reap its full benefits.
-
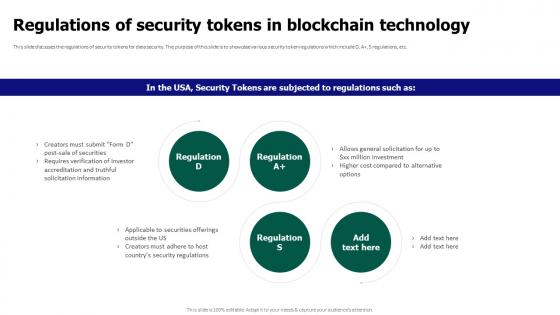 Tokenization For Improved Data Security Regulations Of Security Tokens In Blockchain Technology
Tokenization For Improved Data Security Regulations Of Security Tokens In Blockchain TechnologyThis slide discusses the regulations of security tokens for data security. The purpose of this slide is to showcase various security token regulations which include D, A plus, S regulations, etc. Introducing Tokenization For Improved Data Security Regulations Of Security Tokens In Blockchain Technology to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Regulations Of Security Tokens, Blockchain Technology, Data Security, using this template. Grab it now to reap its full benefits.
-
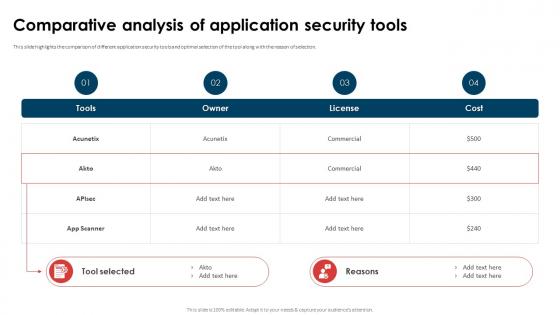 Application Security Implementation Plan Comparative Analysis Of Application Security Tools
Application Security Implementation Plan Comparative Analysis Of Application Security ToolsThis slide highlights the comparison of different application security tools and optimal selection of the tool along with the reason of selection. Deliver an outstanding presentation on the topic using this Application Security Implementation Plan Comparative Analysis Of Application Security Tools. Dispense information and present a thorough explanation of Comparative Analysis, Application Security Tools, Commercial, License using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
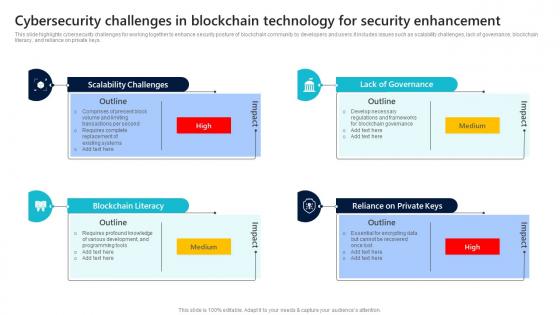 Cybersecurity Challenges In Blockchain Technology For Security Enhancement
Cybersecurity Challenges In Blockchain Technology For Security EnhancementThis slide highlights cybersecurity challenges for working together to enhance security posture of blockchain community by developers and users.It includes issues such as scalability challenges, lack of governance, blockchain literacy, and reliance on private keys. Presenting our set of slides with Cybersecurity Challenges In Blockchain Technology For Security Enhancement This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Scalability Challenges, Blockchain Literacy, Lack Of Governance
-
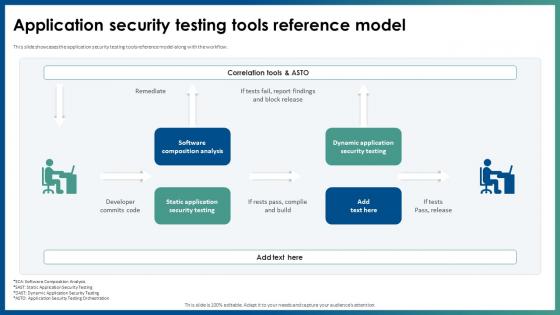 Application Security Testing Tools Reference Model Ppt File Infographics
Application Security Testing Tools Reference Model Ppt File InfographicsThis slide showcases the application security testing tools reference model along with the workflow. Deliver an outstanding presentation on the topic using this Application Security Testing Tools Reference Model Ppt File Infographics. Dispense information and present a thorough explanation of Software Composition Analysis, Static Application Security Testing, Dynamic Application Security Testing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
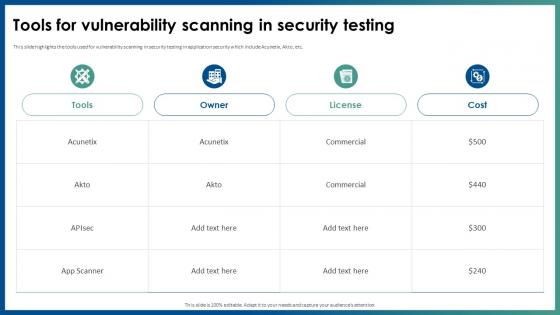 Application Security Tools For Vulnerability Scanning In Security Testing
Application Security Tools For Vulnerability Scanning In Security TestingThis slide highlights the tools used for vulnerability scanning in security testing in application security which include Acunetix, Akto, etc. Present the topic in a bit more detail with this Application Security Tools For Vulnerability Scanning In Security Testing. Use it as a tool for discussion and navigation on Tools For Vulnerability, Scanning In Security Testing, Application Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
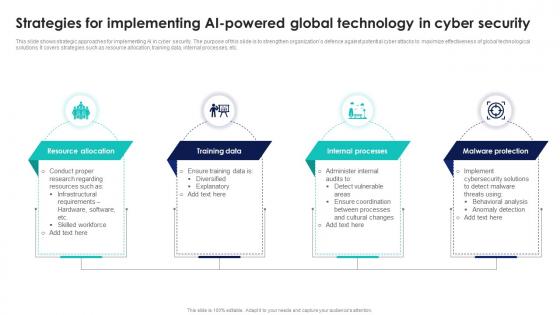 Strategies For Implementing AI Powered Global Technology In Cyber Security
Strategies For Implementing AI Powered Global Technology In Cyber SecurityThis slide shows strategic approaches for implementing AI in cyber security. The purpose of this slide is to strengthen organizations defence against potential cyber attacks to maximize effectiveness of global technological solutions. It covers strategies such as resource allocation, training data, internal processes, etc. Presenting our set of slides with Strategies For Implementing AI Powered Global Technology In Cyber Security. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Resource Allocation, Training Data, Internal Processes.
-
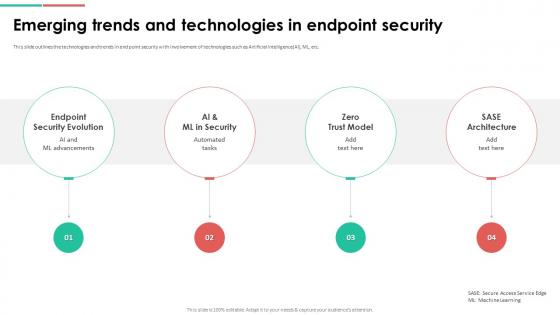 Endpoint Security Emerging Trends And Technologies In Endpoint Security
Endpoint Security Emerging Trends And Technologies In Endpoint SecurityThis slide outlines the technologies and trends in end point security with involvement of technologies such as Artificial Intelligence AI, ML, etc. Increase audience engagement and knowledge by dispensing information using Endpoint Security Emerging Trends And Technologies In Endpoint Security. This template helps you present information on four stages. You can also present information on Emerging Trends, Technologies In Endpoint Security, Artificial Intelligence using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Endpoint Security Top Endpoint Security Tools And Cost
Endpoint Security Top Endpoint Security Tools And CostThis slide highlights the tools used for endpoint security such as Sophos, Vipre, and CrowdStrike along with their cost and features. Deliver an outstanding presentation on the topic using this Endpoint Security Top Endpoint Security Tools And Cost. Dispense information and present a thorough explanation of Prevents Ransomware, Security Tools And Cost, Crowdstrike using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
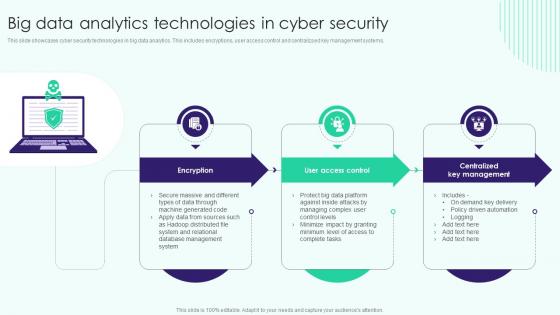 Big Data Analytics Technologies In Cyber Security
Big Data Analytics Technologies In Cyber SecurityThis slide showcases cyber security technologies in big data analytics. This includes encryptions, user access control and centralizsed key management systems. Presenting our set of slides with name Big Data Analytics Technologies In Cyber Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Big Data Analytics, Centralized Key Management, Technologies In Cyber Security.
-
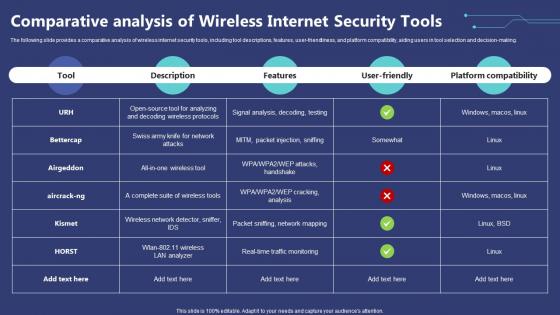 Comparative Analysis Of Wireless Internet Security Tools
Comparative Analysis Of Wireless Internet Security ToolsThe following slide provides a comparative analysis of wireless internet security tools, including tool descriptions, features, user-friendliness, and platform compatibility, aiding users in tool selection and decision-making. Introducing our Comparative Analysis Of Wireless Internet Security Tools set of slides. The topics discussed in these slides are Comparative, Analysis, Security Tools. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
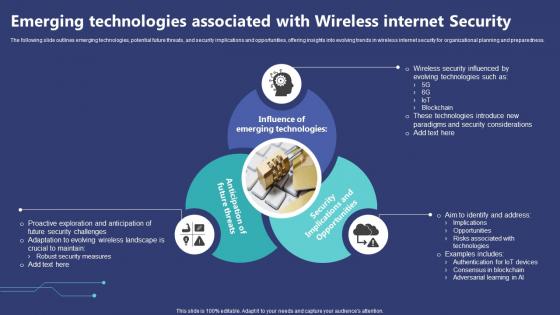 Emerging Technologies Associated With Wireless Internet Security
Emerging Technologies Associated With Wireless Internet SecurityThe following slide outlines emerging technologies, potential future threats, and security implications and opportunities, offering insights into evolving trends in wireless internet security for organizational planning and preparedness. Presenting our set of slides with Emerging Technologies Associated With Wireless Internet Security. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Technologies, Associated, Considerations.
-
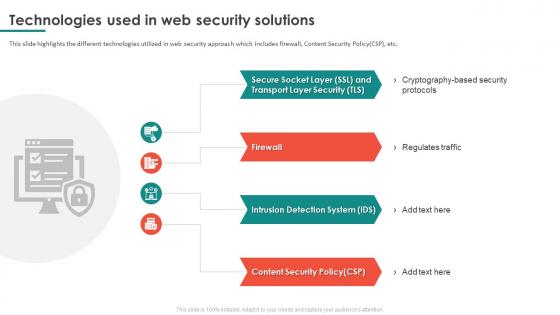 Technologies Used In Web Security Solutions
Technologies Used In Web Security SolutionsThis slide highlights the different technologies utilized in web security approach which includes firewall, Content Security Policy CSP, etc. Presenting our set of slides with name Technologies Used In Web Security Solutions. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Regulates Traffic, Intrusion Detection System, Content Security Policy.
-
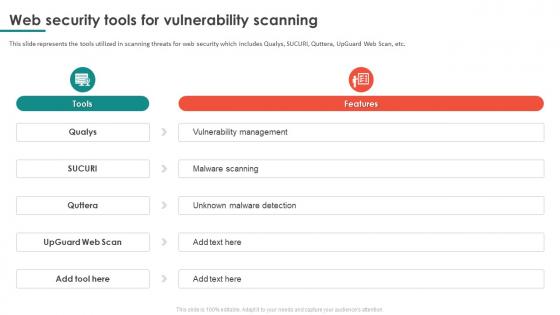 Web Security Tools For Vulnerability Scanning
Web Security Tools For Vulnerability ScanningThis slide represents the tools utilized in scanning threats for web security which includes Qualys, SUCURI, Quttera, UpGuard Web Scan, etc. Introducing our Web Security Tools For Vulnerability Scanning set of slides. The topics discussed in these slides are Vulnerability Scanning, Vulnerability Management, Unknown Malware Detection. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Comparative Analysis Of Server Security Tools
Comparative Analysis Of Server Security ToolsFollowing slide showcases server security comparative tools to choose best option, also including tools, file backup, unified dashboard, starting price, and multiple platform support. Introducing our Comparative Analysis Of Server Security Tools set of slides. The topics discussed in these slides are Avast Server Antivirus, Syxsense Cortex, Platform Support. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Data Protection Server Security Technology Icon
Data Protection Server Security Technology IconPresenting our set of slides with Data Protection Server Security Technology Icon. This exhibits information on threestages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Protection, Server Security Technology.
-
 Icon For Role Of 5g Technology In Retail Cyber Security
Icon For Role Of 5g Technology In Retail Cyber SecurityIntroducing our Icon For Role Of 5g Technology In Retail Cyber Security set of slides. The topics discussed in these slides are Icon For Role Of 5G Technology, Retail Cyber Security This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Complete Guide To Commercial Biometric Technology For Enhancing Online Security Fin SS V
Complete Guide To Commercial Biometric Technology For Enhancing Online Security Fin SS VThis slide shows information which can be used by organizations to get insights about use of biometric technology growth in commercial banking. It includes details about process and types of biometric data. Increase audience engagement and knowledge by dispensing information using Complete Guide To Commercial Biometric Technology For Enhancing Online Security Fin SS V. This template helps you present information on four stages. You can also present information on Voice Recognition, Facial Recognition, Iris Recognition, Enhancing Online Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
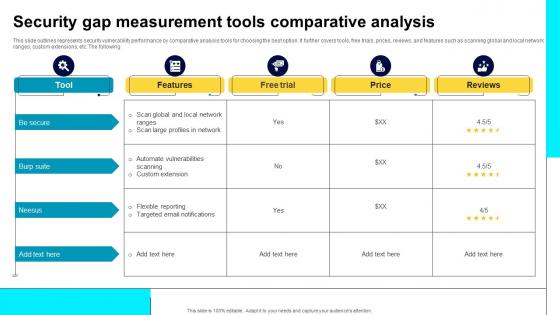 Security Gap Measurement Tools Comparative Analysis
Security Gap Measurement Tools Comparative AnalysisThis slide outlines represents security vulnerability performance by comparative analysis tools for choosing the best option. It further covers tools, free trials, prices, reviews, and features such as scanning global and local network ranges, custom extensions, etc. The following. Introducing our Security Gap Measurement Tools Comparative Analysis set of slides. The topics discussed in these slides are Scan Global, Local Network Ranges, Automate Vulnerabilities, Custom Extension. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Comparative Analysis Of Mobile Security Tools
Comparative Analysis Of Mobile Security ToolsThis slide showcases mobile security software applications comparison matrix and includes anti-theft protection, remote SMS control, call blocking, web protection, and wi-fi protection. Introducing our Comparative Analysis Of Mobile Security Tools set of slides. The topics discussed in these slides are Anti- Theft Protection, Remote Sms Control, Call Blocking, Web Protection. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.



