Powerpoint Templates and Google slides for Technology System
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
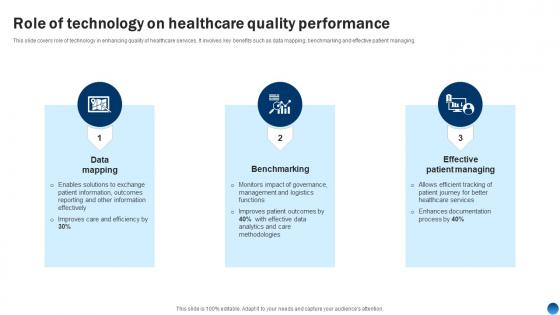 Role Of Technology On Healthcare Quality Performance Health Information Management System
Role Of Technology On Healthcare Quality Performance Health Information Management SystemThis slide covers role of technology in enhancing quality of healthcare services. It involves key benefits such as data mapping, benchmarking and effective patient managing. Introducing Role Of Technology On Healthcare Quality Performance Health Information Management System to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Data Mapping, Benchmarking, Effective Patient Managing, using this template. Grab it now to reap its full benefits.
-
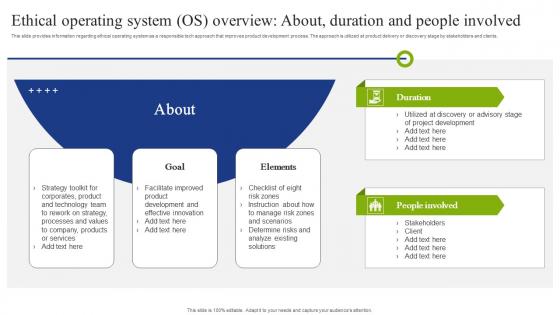 F1571 Ethical Operating System Os Overview People Playbook To Mitigate Negative Of Technology
F1571 Ethical Operating System Os Overview People Playbook To Mitigate Negative Of TechnologyThis slide provides information regarding ethical operating system as a responsible tech approach that improves product development process. The approach is utilized at product delivery or discovery stage by stakeholders and clients. Deliver an outstanding presentation on the topic using this F1571 Ethical Operating System Os Overview People Playbook To Mitigate Negative Of Technology. Dispense information and present a thorough explanation of Technology, Processes, Products using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
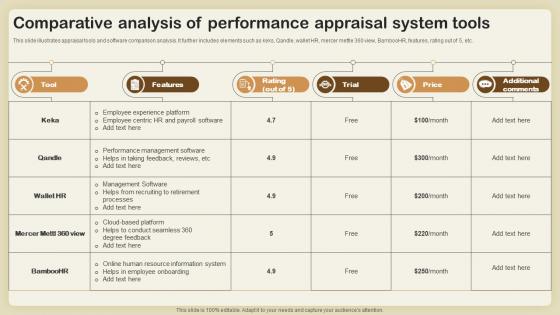 Comparative Analysis Of Performance Appraisal System Tools
Comparative Analysis Of Performance Appraisal System ToolsThis slide illustrates appraisal tools and software comparison analysis. It further includes elements such as keks, Qandle, wallet HR, mercer mettle 360 view, BambooHR, features, rating out of 5, etc. Presenting our well structured Comparative Analysis Of Performance Appraisal System Tools. The topics discussed in this slide are Features, Rating, Price. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
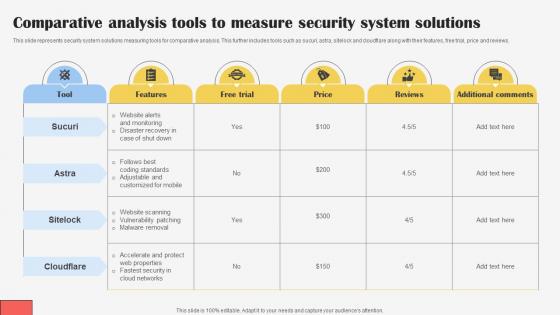 Comparative Analysis Tools To Measure Security System Solutions
Comparative Analysis Tools To Measure Security System SolutionsThis slide represents security system solutions measuring tools for comparative analysis. This further includes tools such as sucuri, astra, sitelock and cloudflare along with their features, free trial, price and reviews. Introducing our Comparative Analysis Tools To Measure Security System Solutions set of slides. The topics discussed in these slides are Features, Additional Comments, Comparative Analysis. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
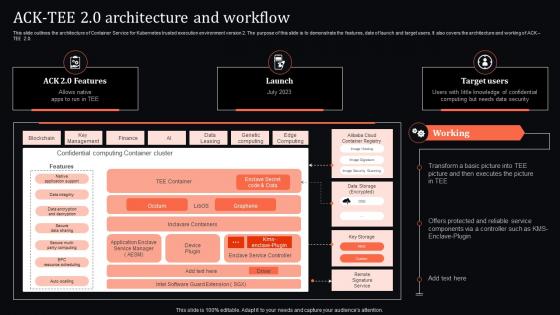 Ack Tee 2 0 Architecture And Workflow Confidential Computing System Technology
Ack Tee 2 0 Architecture And Workflow Confidential Computing System TechnologyThis slide outlines the architecture of Container Service for Kubernetes trusted execution environment version 2. The purpose of this slide is to demonstrate the features, date of launch and target users. It also covers the architecture and working of ACK TEE 2.0. Present the topic in a bit more detail with this Ack Tee 2 0 Architecture And Workflow Confidential Computing System Technology. Use it as a tool for discussion and navigation on Architecture, Workflow, Confidential. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
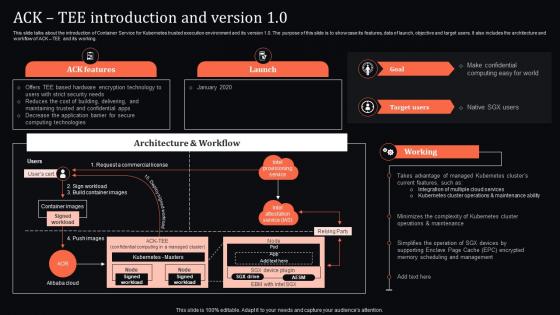 Ack Tee Introduction And Version 1 0 Confidential Computing System Technology
Ack Tee Introduction And Version 1 0 Confidential Computing System TechnologyThis slide talks about the introduction of Container Service for Kubernetes trusted execution environment and its version 1.0. The purpose of this slide is to showcase its features, data of launch, objective and target users. It also includes the architecture and workflow of ACK TEE and its working. Deliver an outstanding presentation on the topic using this Ack Tee Introduction And Version 1 0 Confidential Computing System Technology. Dispense information and present a thorough explanation of Introduction, Maintenance, Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Agenda For Confidential Computing System Technology
Agenda For Confidential Computing System TechnologyIntroducing Agenda For Confidential Computing System Technology to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Technology, Applications, Environment, using this template. Grab it now to reap its full benefits.
-
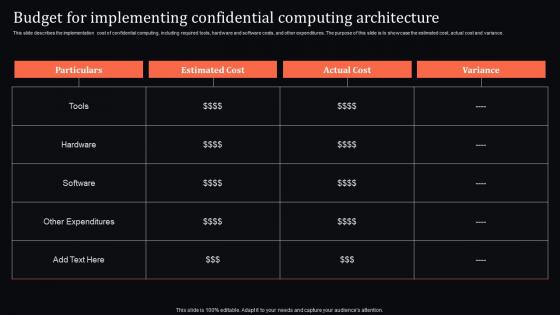 Budget For Implementing Architecture Confidential Computing System Technology
Budget For Implementing Architecture Confidential Computing System TechnologyThis slide describes the implementation cost of confidential computing, including required tools, hardware and software costs, and other expenditures. The purpose of this slide is to showcase the estimated cost, actual cost and variance. Deliver an outstanding presentation on the topic using this Budget For Implementing Architecture Confidential Computing System Technology. Dispense information and present a thorough explanation of Implementing, Confidential, Architecture using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
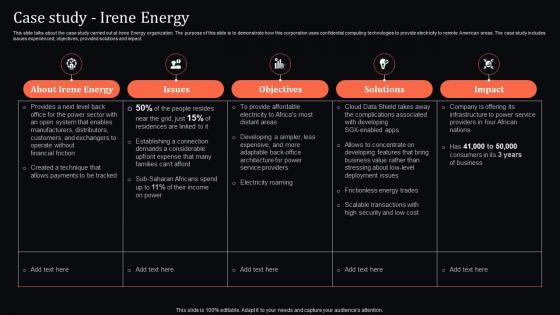 Case Study Irene Energy Confidential Computing System Technology
Case Study Irene Energy Confidential Computing System TechnologyThis slide talks about the case study carried out at Irene Energy organization. The purpose of this slide is to demonstrate how this corporation uses confidential computing technologies to provide electricity to remote American areas. The case study includes issues experienced, objectives, provided solutions and impact. Present the topic in a bit more detail with this Case Study Irene Energy Confidential Computing System Technology. Use it as a tool for discussion and navigation on Manufacturers, Distributors, Solutions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
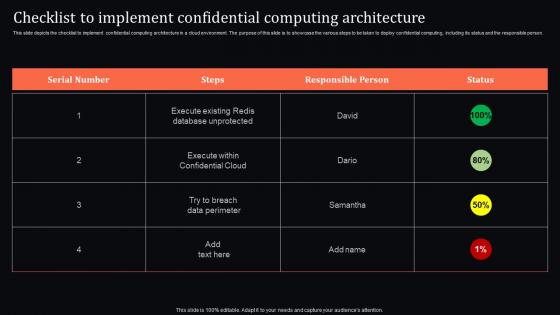 Checklist To Implement Architecture Confidential Computing System Technology
Checklist To Implement Architecture Confidential Computing System TechnologyThis slide depicts the checklist to implement confidential computing architecture in a cloud environment. The purpose of this slide is to showcase the various steps to be taken to deploy confidential computing, including its status and the responsible person. Deliver an outstanding presentation on the topic using this Checklist To Implement Architecture Confidential Computing System Technology. Dispense information and present a thorough explanation of Confidential, Computing, Architecture using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
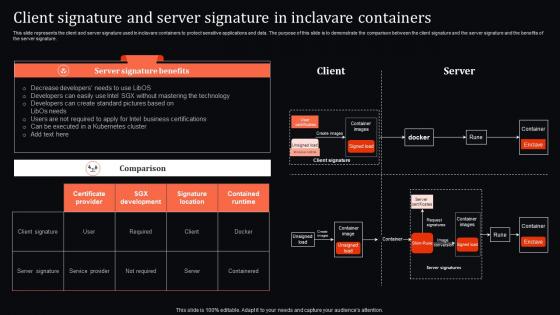 Client Signature And Server Signature In Inclavare Confidential Computing System Technology
Client Signature And Server Signature In Inclavare Confidential Computing System TechnologyThis slide represents the client and server signature used in inclavare containers to protect sensitive applications and data. The purpose of this slide is to demonstrate the comparison between the client signature and the server signature and the benefits of the server signature. Present the topic in a bit more detail with this Client Signature And Server Signature In Inclavare Confidential Computing System Technology. Use it as a tool for discussion and navigation on Technology, Business, Certifications. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
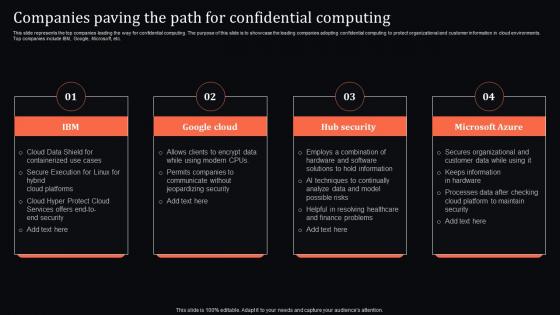 Companies Paving The Path For Confidential Computing System Technology
Companies Paving The Path For Confidential Computing System TechnologyThis slide represents the top companies leading the way for confidential computing. The purpose of this slide is to showcase the leading companies adopting confidential computing to protect organizational and customer information in cloud environments. Top companies include IBM, Google, Microsoft, etc. Introducing Companies Paving The Path For Confidential Computing System Technology to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Containerized, Services, Execution, using this template. Grab it now to reap its full benefits.
-
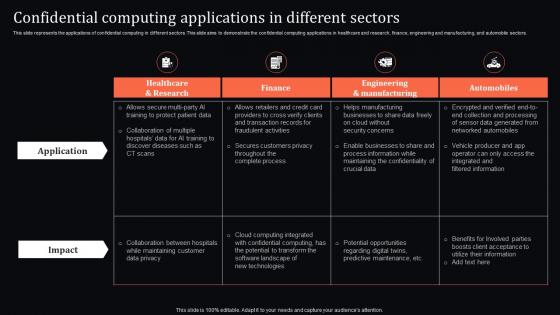 Confidential Applications In Different Sectors Confidential Computing System Technology
Confidential Applications In Different Sectors Confidential Computing System TechnologyThis slide represents the applications of confidential computing in different sectors. This slide aims to demonstrate the confidential computing applications in healthcare and research, finance, engineering and manufacturing, and automobile sectors. Deliver an outstanding presentation on the topic using this Confidential Applications In Different Sectors Confidential Computing System Technology. Dispense information and present a thorough explanation of Businesses, Information, Confidentiality using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
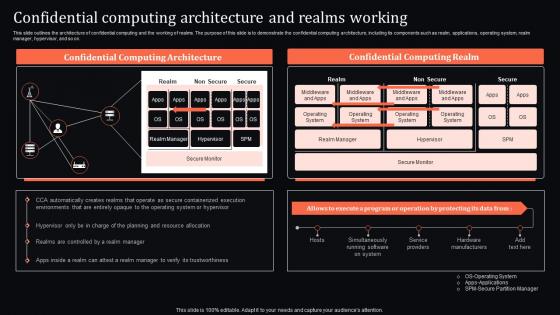 Confidential Architecture And Realms Working Confidential Computing System Technology
Confidential Architecture And Realms Working Confidential Computing System TechnologyThis slide outlines the architecture of confidential computing and the working of realms. The purpose of this slide is to demonstrate the confidential computing architecture, including its components such as realm, applications, operating system, realm manager, hypervisor, and so on. Present the topic in a bit more detail with this Confidential Architecture And Realms Working Confidential Computing System Technology. Use it as a tool for discussion and navigation on Confidential, Computing, Architecture. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
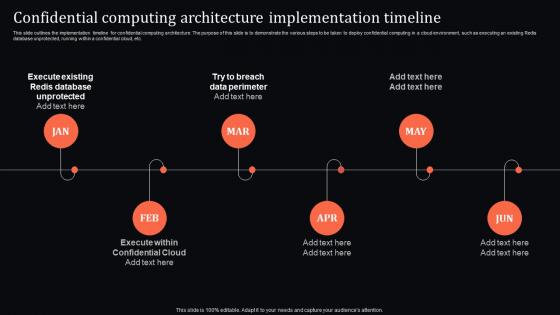 Confidential Computing Architecture Implementation Confidential Computing System Technology
Confidential Computing Architecture Implementation Confidential Computing System TechnologyThis slide outlines the implementation timeline for confidential computing architecture. The purpose of this slide is to demonstrate the various steps to be taken to deploy confidential computing in a cloud environment, such as executing an existing Redis database unprotected, running within a confidential cloud, etc. Introducing Confidential Computing Architecture Implementation Confidential Computing System Technology to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Architecture, Implementation, Timeline, using this template. Grab it now to reap its full benefits.
-
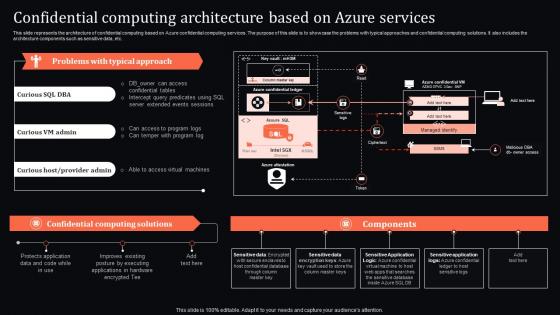 Confidential Computing Based On Azure Services Confidential Computing System Technology
Confidential Computing Based On Azure Services Confidential Computing System TechnologyThis slide represents the architecture of confidential computing based on Azure confidential computing services. The purpose of this slide is to showcase the problems with typical approaches and confidential computing solutions. It also includes the architecture components such as sensitive data, etc. Present the topic in a bit more detail with this Confidential Computing Based On Azure Services Confidential Computing System Technology. Use it as a tool for discussion and navigation on Architecture, Services, Solutions. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Confidential Computing System Technology For Table Of Contents
Confidential Computing System Technology For Table Of ContentsIntroducing Confidential Computing System Technology For Table Of Contents to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Technology, Approaches, Architecture, using this template. Grab it now to reap its full benefits.
-
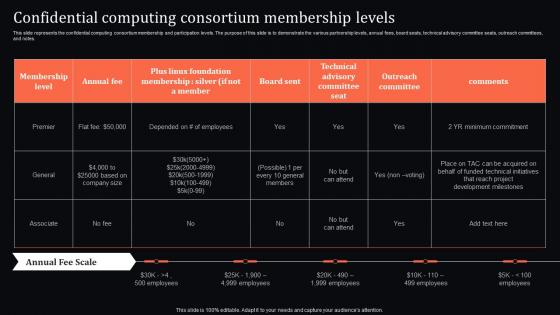 Confidential Consortium Membership Levels Confidential Computing System Technology
Confidential Consortium Membership Levels Confidential Computing System TechnologyThis slide represents the confidential computing consortium membership and participation levels. The purpose of this slide is to demonstrate the various partnership levels, annual fees, board seats, technical advisory committee seats, outreach committees, and notes. Deliver an outstanding presentation on the topic using this Confidential Consortium Membership Levels Confidential Computing System Technology. Dispense information and present a thorough explanation of Confidential, Computing, Consortium using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
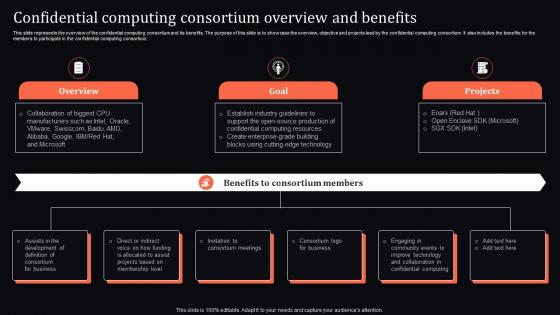 Confidential Consortium Overview And Benefits Confidential Computing System Technology
Confidential Consortium Overview And Benefits Confidential Computing System TechnologyThis slide represents the overview of the confidential computing consortium and its benefits. The purpose of this slide is to showcase the overview, objective and projects lead by the confidential computing consortium. It also includes the benefits for the members to participate in the confidential computing consortium. Present the topic in a bit more detail with this Confidential Consortium Overview And Benefits Confidential Computing System Technology. Use it as a tool for discussion and navigation on Confidential, Consortium, Overview. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
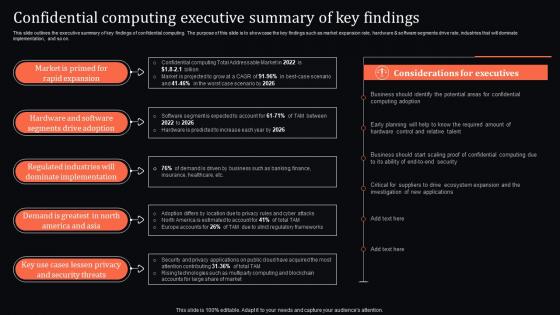 Confidential Executive Summary Of Key Findings Confidential Computing System Technology
Confidential Executive Summary Of Key Findings Confidential Computing System TechnologyThis slide outlines the executive summary of key findings of confidential computing. The purpose of this slide is to showcase the key findings such as market expansion rate, hardware and software segments drive rate, industries that will dominate implementation, and so on. Present the topic in a bit more detail with this Confidential Executive Summary Of Key Findings Confidential Computing System Technology. Use it as a tool for discussion and navigation on Implementation, Considerations, Executives. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
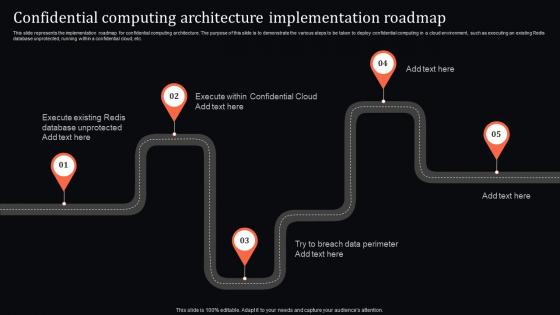 Confidential Implementation Roadmap Confidential Computing System Technology
Confidential Implementation Roadmap Confidential Computing System TechnologyThis slide represents the implementation roadmap for confidential computing architecture. The purpose of this slide is to demonstrate the various steps to be taken to deploy confidential computing in a cloud environment, such as executing an existing Redis database unprotected, running within a confidential cloud, etc. Increase audience engagement and knowledge by dispensing information using Confidential Implementation Roadmap Confidential Computing System Technology. This template helps you present information on five stages. You can also present information on Architecture, Implementation, Roadmap using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
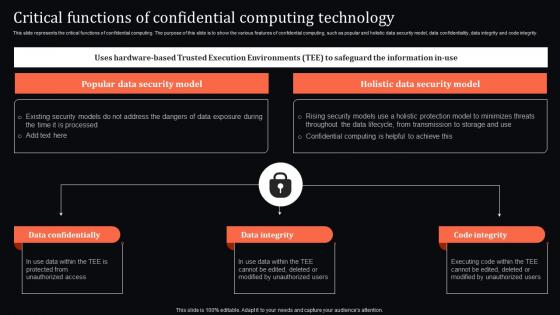 Critical Functions Of Confidential Computing Technology Confidential Computing System Technology
Critical Functions Of Confidential Computing Technology Confidential Computing System TechnologyThis slide represents the critical functions of confidential computing. The purpose of this slide is to show the various features of confidential computing, such as popular and holistic data security model, data confidentiality, data integrity and code integrity. Present the topic in a bit more detail with this Critical Functions Of Confidential Computing Technology Confidential Computing System Technology. Use it as a tool for discussion and navigation on Data Confidentially, Data Integrity, Code Integrity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
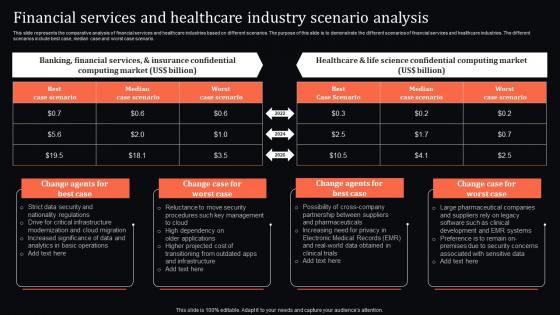 Financial And Healthcare Industry Scenario Analysis Confidential Computing System Technology
Financial And Healthcare Industry Scenario Analysis Confidential Computing System TechnologyThis slide represents the comparative analysis of financial services and healthcare industries based on different scenarios. The purpose of this slide is to demonstrate the different scenarios of financial services and healthcare industries. The different scenarios include best case, median case and worst case scenario. Deliver an outstanding presentation on the topic using this Financial And Healthcare Industry Scenario Analysis Confidential Computing System Technology. Dispense information and present a thorough explanation of Financial, Services, Analysis using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
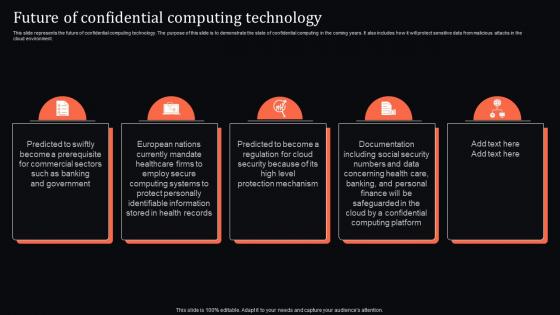 Future Of Confidential Computing Technology Confidential Computing System Technology
Future Of Confidential Computing Technology Confidential Computing System TechnologyThis slide represents the future of confidential computing technology. The purpose of this slide is to demonstrate the state of confidential computing in the coming years. It also includes how it will protect sensitive data from malicious attacks in the cloud environment. Introducing Future Of Confidential Computing Technology Confidential Computing System Technology to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Confidential, Computing, Technology, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Confidential Computing System Technology
Icons Slide For Confidential Computing System TechnologyPresent the topic in a bit more detail with this Icons Slide For Confidential Computing System Technology. Use it as a tool for discussion and navigation on Icons. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
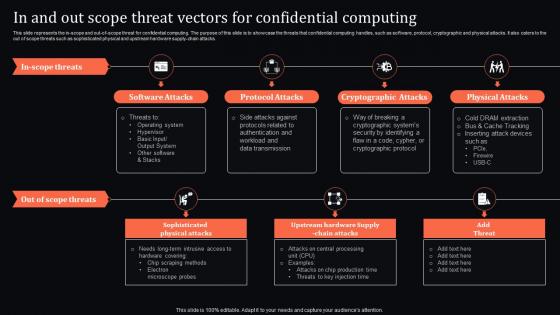 In And Threat Vectors For Confidential Computing Confidential Computing System Technology
In And Threat Vectors For Confidential Computing Confidential Computing System TechnologyThis slide represents the in-scope and out-of-scope threat for confidential computing. The purpose of this slide is to showcase the threats that confidential computing handles, such as software, protocol, cryptographic and physical attacks. It also caters to the out of scope threats such as sophisticated physical and upstream hardware supply-chain attacks. Increase audience engagement and knowledge by dispensing information using In And Threat Vectors For Confidential Computing Confidential Computing System Technology. This template helps you present information on seven stages. You can also present information on Software Attacks, Protocol Attacks, Cryptographic Attacks using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
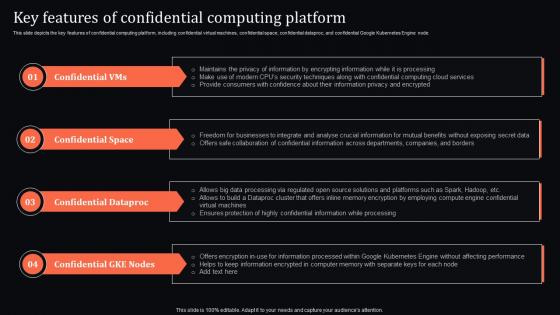 Key Features Of Confidential Computing Platform Confidential Computing System Technology
Key Features Of Confidential Computing Platform Confidential Computing System TechnologyThis slide depicts the key features of confidential computing platform, including confidential virtual machines, confidential space, confidential dataproc, and confidential Google Kubernetes Engine node. Introducing Key Features Of Confidential Computing Platform Confidential Computing System Technology to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Confidential Space, Confidential Dataproc, Confidential Gke Nodes, using this template. Grab it now to reap its full benefits.
-
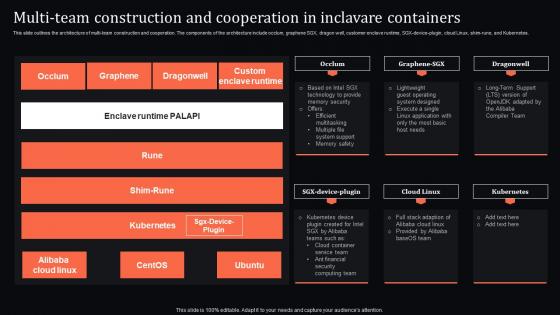 Multi Team And Cooperation In Inclavare Containers Confidential Computing System Technology
Multi Team And Cooperation In Inclavare Containers Confidential Computing System TechnologyThis slide outlines the architecture of multi-team construction and cooperation. The components of the architecture include occlum, graphene SGX, dragon well, customer enclave runtime, SGX-device-plugin, cloud Linux, shim-rune, and Kubernetes. Deliver an outstanding presentation on the topic using this Multi Team And Cooperation In Inclavare Containers Confidential Computing System Technology. Dispense information and present a thorough explanation of Construction, Cooperation, Containers using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
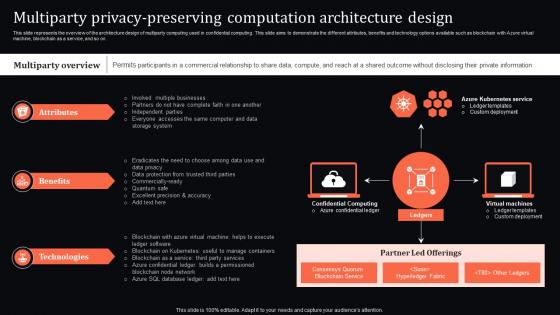 Multiparty Privacy Computation Architecture Design Confidential Computing System Technology
Multiparty Privacy Computation Architecture Design Confidential Computing System TechnologyThis slide represents the overview of the architecture design of multiparty computing used in confidential computing. This slide aims to demonstrate the different attributes, benefits and technology options available such as blockchain with Azure virtual machine, blockchain as a service, and so on. Present the topic in a bit more detail with this Multiparty Privacy Computation Architecture Design Confidential Computing System Technology. Use it as a tool for discussion and navigation on Computation, Architecture, Technologies . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
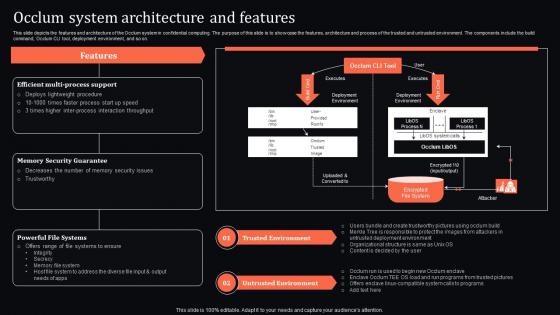 Occlum System Architecture And Features Confidential Computing System Technology
Occlum System Architecture And Features Confidential Computing System TechnologyThis slide depicts the features and architecture of the Occlum system in confidential computing. The purpose of this slide is to showcase the features, architecture and process of the trusted and untrusted environment. The components include the build command, Occlum CLI tool, deployment environment, and so on. Present the topic in a bit more detail with this Occlum System Architecture And Features Confidential Computing System Technology. Use it as a tool for discussion and navigation on Trusted Environment, Untrusted Environment, Memory Security Guarantee. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
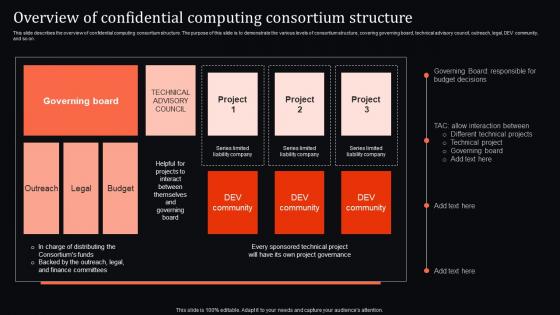 Overview Of Computing Consortium Structure Confidential Computing System Technology
Overview Of Computing Consortium Structure Confidential Computing System TechnologyThis slide describes the overview of confidential computing consortium structure. The purpose of this slide is to demonstrate the various levels of consortium structure, covering governing board, technical advisory council, outreach, legal, DEV community, and so on. Present the topic in a bit more detail with this Overview Of Computing Consortium Structure Confidential Computing System Technology. Use it as a tool for discussion and navigation on Computing, Consortium, Structure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
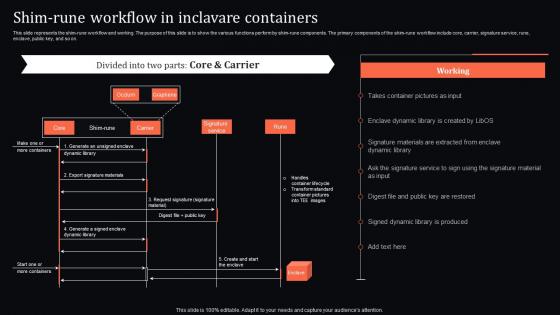 Shim Rune Workflow In Inclavare Containers Confidential Computing System Technology
Shim Rune Workflow In Inclavare Containers Confidential Computing System TechnologyThis slide represents the shim-rune workflow and working. The purpose of this slide is to show the various functions perform by shim-rune components. The primary components of the shim-rune workflow include core, carrier, signature service, rune, enclave, public key, and so on. Present the topic in a bit more detail with this Shim Rune Workflow In Inclavare Containers Confidential Computing System Technology. Use it as a tool for discussion and navigation on Component, Workflow, Inclavare Containers. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
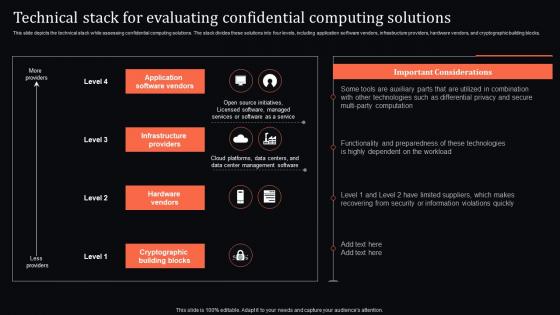 Technical Stack For Confidential Computing Solutions Confidential Computing System Technology
Technical Stack For Confidential Computing Solutions Confidential Computing System TechnologyThis slide depicts the technical stack while assessing confidential computing solutions. The stack divides these solutions into four levels, including application software vendors, infrastructure providers, hardware vendors, and cryptographic building blocks. Present the topic in a bit more detail with this Technical Stack For Confidential Computing Solutions Confidential Computing System Technology. Use it as a tool for discussion and navigation on Application Software Vendors, Infrastructure Providers, Hardware Vendors. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
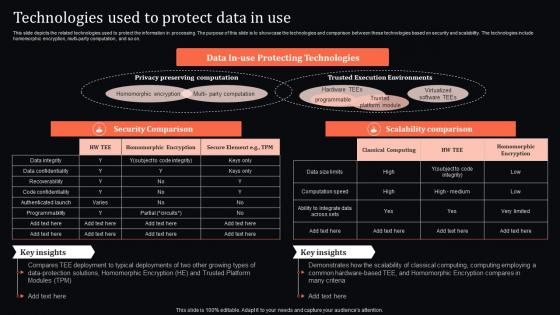 Technologies Used To Protect Data In Use Confidential Computing System Technology
Technologies Used To Protect Data In Use Confidential Computing System TechnologyThis slide depicts the related technologies used to protect the information in processing. The purpose of this slide is to showcase the technologies and comparison between these technologies based on security and scalability. The technologies include homomorphic encryption, multi-party computation, and so on. Deliver an outstanding presentation on the topic using this Technologies Used To Protect Data In Use Confidential Computing System Technology. Dispense information and present a thorough explanation of Technologies, Security Comparison, Scalability Comparison using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
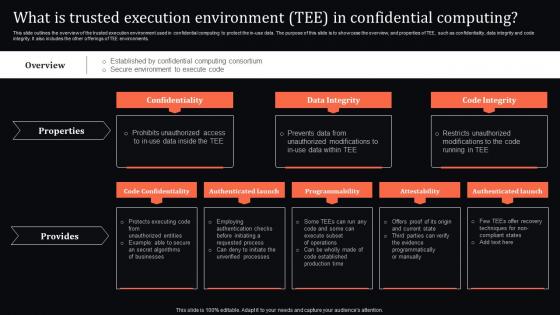 What Is Environment Tee In Confidential Computing Confidential Computing System Technology
What Is Environment Tee In Confidential Computing Confidential Computing System TechnologyThis slide outlines the overview of the trusted execution environment used in confidential computing to protect the in-use data. The purpose of this slide is to showcase the overview, and properties of TEE, such as confidentiality, data integrity and code integrity. It also includes the other offerings of TEE environments. Present the topic in a bit more detail with this What Is Environment Tee In Confidential Computing Confidential Computing System Technology. Use it as a tool for discussion and navigation on Confidentiality, Data Integrity, Code Integrity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
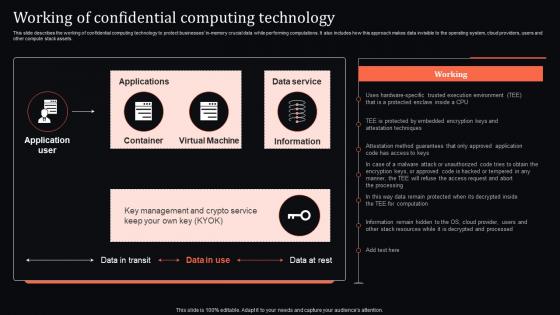 Working Of Confidential Computing Technology Confidential Computing System Technology
Working Of Confidential Computing Technology Confidential Computing System TechnologyThis slide describes the working of confidential computing technology to protect businesses in-memory crucial data while performing computations. It also includes how this approach makes data invisible to the operating system, cloud providers, users and other compute stack assets. Present the topic in a bit more detail with this Working Of Confidential Computing Technology Confidential Computing System Technology. Use it as a tool for discussion and navigation on Confidential, Computing, Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
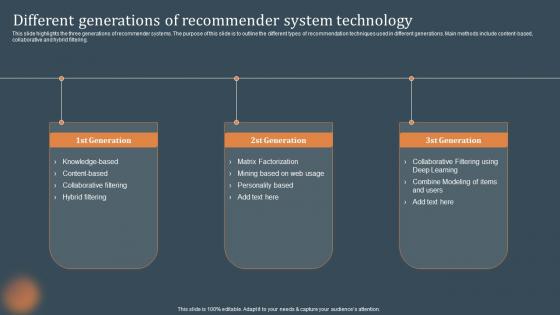 Different Generations Of Recommender System Technology Recommendations Based On Machine Learning
Different Generations Of Recommender System Technology Recommendations Based On Machine LearningThis slide highlights the three generations of recommender systems. The purpose of this slide is to outline the different types of recommendation techniques used in different generations. Main methods include content-based, collaborative and hybrid filtering. Increase audience engagement and knowledge by dispensing information using Different Generations Of Recommender System Technology Recommendations Based On Machine Learning. This template helps you present information on three stages. You can also present information on Generation, Factorization, Knowledge using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
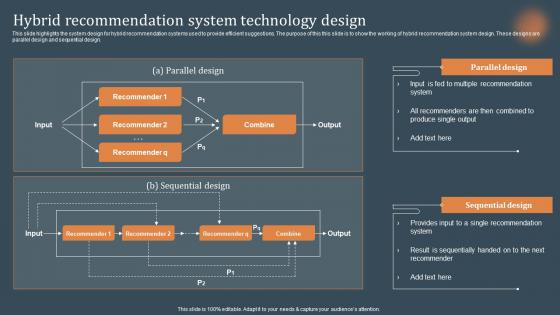 Hybrid Recommendation System Technology Design Recommendations Based On Machine Learning
Hybrid Recommendation System Technology Design Recommendations Based On Machine LearningThis slide highlights the system design for hybrid recommendation systems used to provide efficient suggestions. The purpose of this this slide is to show the working of hybrid recommendation system design. These designs are parallel design and sequential design. Deliver an outstanding presentation on the topic using this Hybrid Recommendation System Technology Design Recommendations Based On Machine Learning. Dispense information and present a thorough explanation of Recommendation, Technology, Sequentially using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
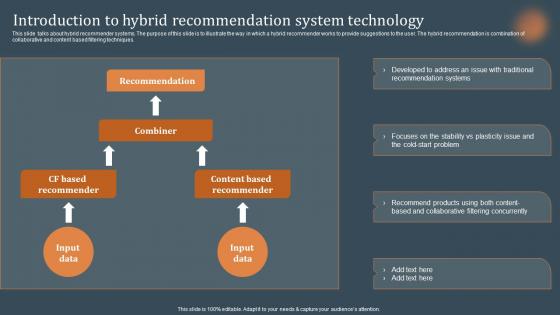 Introduction To Hybrid Recommendation System Technology Recommendations Based On Machine Learning
Introduction To Hybrid Recommendation System Technology Recommendations Based On Machine LearningThis slide talks about hybrid recommender systems. The purpose of this slide is to illustrate the way in which a hybrid recommender works to provide suggestions to the user. The hybrid recommendation is combination of collaborative and content based filtering techniques. Present the topic in a bit more detail with this Introduction To Hybrid Recommendation System Technology Recommendations Based On Machine Learning. Use it as a tool for discussion and navigation on Technology, Recommendation, Concurrently. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
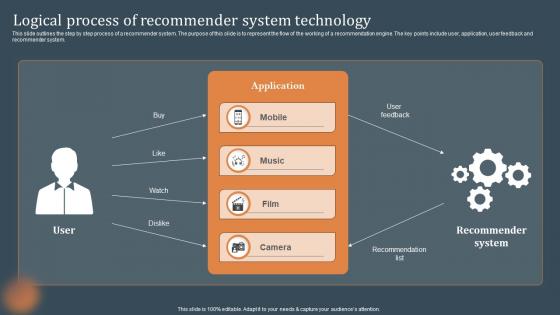 Logical Process Of Recommender System Technology Recommendations Based On Machine Learning
Logical Process Of Recommender System Technology Recommendations Based On Machine LearningThis slide outlines the step by step process of a recommender system. The purpose of this slide is to represent the flow of the working of a recommendation engine. The key points include user, application, user feedback and recommender system. Present the topic in a bit more detail with this Logical Process Of Recommender System Technology Recommendations Based On Machine Learning. Use it as a tool for discussion and navigation on Technology, Application, Recommender. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
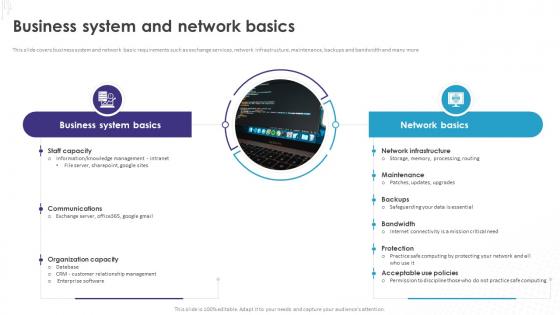 Implementation Of Technology Action Business System And Network Basics
Implementation Of Technology Action Business System And Network BasicsThis slide covers business system and network basic requirements such as exchange services, network infrastructure, maintenance, backups and bandwidth and many more. Increase audience engagement and knowledge by dispensing information using Implementation Of Technology Action Business System And Network Basics. This template helps you present information on two stages. You can also present information on Business System, Network Basic Requirements, Exchange Services, Network Infrastructure, Maintenance, Backups And Bandwidth using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Comparative Analysis Of Market Research Tools Marketing Intelligence System MKT SS V
Comparative Analysis Of Market Research Tools Marketing Intelligence System MKT SS VThis slide covers comparative study of market research tools. It involves key features such as customized surveys, statistical tools, cloud based accessibility and location filters. Present the topic in a bit more detail with this Comparative Analysis Of Market Research Tools Marketing Intelligence System MKT SS V. Use it as a tool for discussion and navigation on Customized Surveys, Statistical Tools, Cloud Based Accessibility. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Latest Technology Trends To Transform Market Research Marketing Intelligence System MKT SS V
Latest Technology Trends To Transform Market Research Marketing Intelligence System MKT SS VThis slide covers latest technology trends to enhance market research process. It involves artificial intelligence, real time feedback, microdata and social targeting. Introducing Latest Technology Trends To Transform Market Research Marketing Intelligence System MKT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Artificial Intelligence, Microdata, Social Targeting, Real Time Feedback, using this template. Grab it now to reap its full benefits.
-
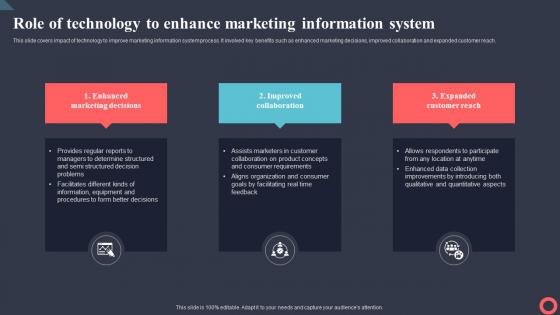 Role Of Technology To Enhance Marketing Information Marketing Intelligence System MKT SS V
Role Of Technology To Enhance Marketing Information Marketing Intelligence System MKT SS VThis slide covers impact of technology to improve marketing information system process. It involved key benefits such as enhanced marketing decisions, improved collaboration and expanded customer reach. Introducing Role Of Technology To Enhance Marketing Information Marketing Intelligence System MKT SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Enhanced Marketing Decisions, Improved Collaboration, Expanded Customer Reach, using this template. Grab it now to reap its full benefits.
-
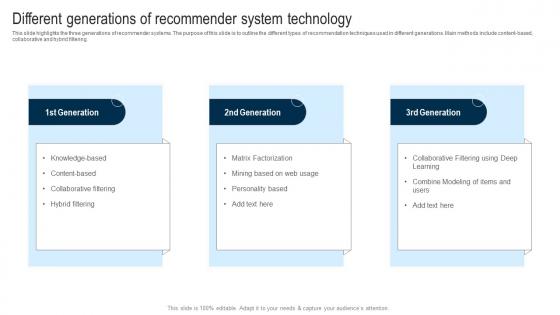 Applications Of Filtering Techniques Different Generations Of Recommender System Technology
Applications Of Filtering Techniques Different Generations Of Recommender System TechnologyThis slide highlights the three generations of recommender systems. The purpose of this slide is to outline the different types of recommendation techniques used in different generations. Main methods include content-based, collaborative and hybrid filtering. Increase audience engagement and knowledge by dispensing information using Applications Of Filtering Techniques Different Generations Of Recommender System Technology. This template helps you present information on three stages. You can also present information on Collaborative Filtering, Hybrid Filtering, Matrix Factorization, Personality Based using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
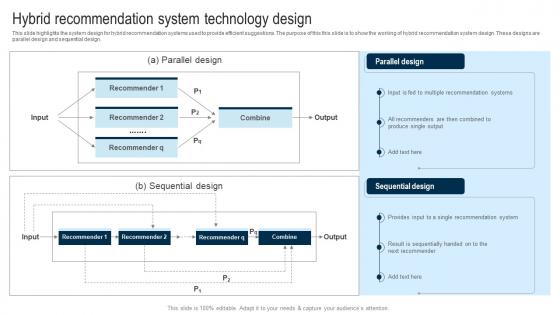 Applications Of Filtering Techniques Hybrid Recommendation System Technology Design
Applications Of Filtering Techniques Hybrid Recommendation System Technology DesignThis slide highlights the system design for hybrid recommendation systems used to provide efficient suggestions. The purpose of this this slide is to show the working of hybrid recommendation system design. These designs are parallel design and sequential design. Present the topic in a bit more detail with this Applications Of Filtering Techniques Hybrid Recommendation System Technology Design. Use it as a tool for discussion and navigation on Multiple Recommendation Systems, Single Recommendation System, Hybrid Recommendation System. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
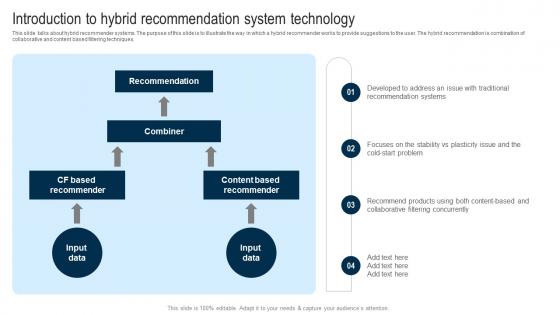 Applications Of Filtering Techniques Introduction To Hybrid Recommendation System Technology
Applications Of Filtering Techniques Introduction To Hybrid Recommendation System TechnologyThis slide talks about hybrid recommender systems. The purpose of this slide is to illustrate the way in which a hybrid recommender works to provide suggestions to the user. The hybrid recommendation is combination of collaborative and content based filtering techniques. Present the topic in a bit more detail with this Applications Of Filtering Techniques Introduction To Hybrid Recommendation System Technology. Use it as a tool for discussion and navigation on Collaborative Filtering Concurrently, Traditional Recommendation Systems, Hybrid Recommendation System Technology. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Applications Of Filtering Techniques Logical Process Of Recommender System Technology
Applications Of Filtering Techniques Logical Process Of Recommender System TechnologyThis slide outlines the step by step process of a recommender system. The purpose of this slide is to represent the flow of the working of a recommendation engine. The key points include user, application, user feedback and recommender system. Increase audience engagement and knowledge by dispensing information using Applications Of Filtering Techniques Logical Process Of Recommender System Technology. This template helps you present information on four stages. You can also present information on Recommender System, Logical Process, Recommender System Technology, Recommendation Engine using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Embedded Systems Tools In Powerpoint And Google Slides Cpb
Embedded Systems Tools In Powerpoint And Google Slides CpbPresenting Embedded Systems Tools In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Embedded Systems Tools. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
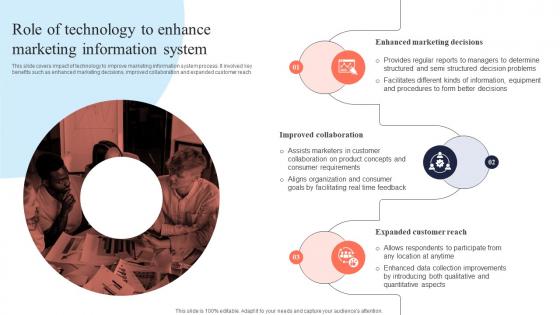 Role Of Technology To Information System Mis Integration To Enhance Marketing Services MKT SS V
Role Of Technology To Information System Mis Integration To Enhance Marketing Services MKT SS VThis slide covers impact of technology to improve marketing information system process. It involved key benefits such as enhanced marketing decisions, improved collaboration and expanded customer reach. Introducing Role Of Technology To Information System Mis Integration To Enhance Marketing Services MKT SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Enhanced Marketing Decisions, Improved Collaboration, Expanded Customer Reach , using this template. Grab it now to reap its full benefits.
-
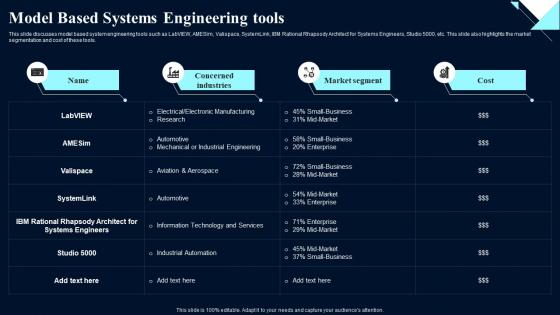 Model Engineering Tools System Design Optimization Systems Engineering MBSE
Model Engineering Tools System Design Optimization Systems Engineering MBSEThis slide discusses model based system engineering tools such as LabVIEW, AMESim, Valispace, SystemLink, IBM Rational Rhapsody Architect for Systems Engineers, Studio 5000, etc. This slide also highlights the market segmentation and cost of these tools. Deliver an outstanding presentation on the topic using this Model Engineering Tools System Design Optimization Systems Engineering MBSE. Dispense information and present a thorough explanation of Engineering, Segmentation, Architect using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
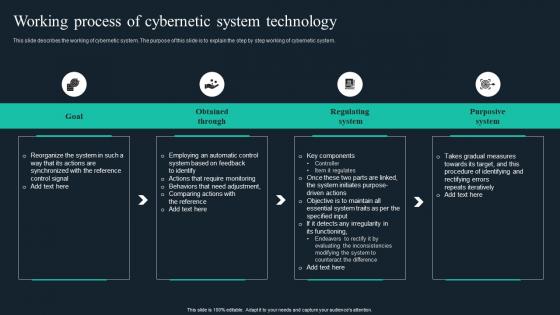 Cybernetic Implants Working Process Of Cybernetic System Technology
Cybernetic Implants Working Process Of Cybernetic System TechnologyThis slide describes the working of cybernetic system. The purpose of this slide is to explain the step by step working of cybernetic system. Increase audience engagement and knowledge by dispensing information using Cybernetic Implants Working Process Of Cybernetic System Technology. This template helps you present information on four stages. You can also present information on Goal, Obtained, Regulating using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
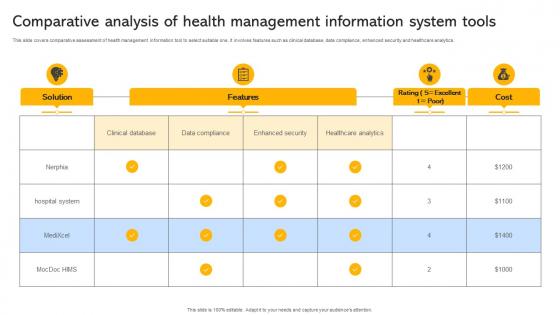 Transforming Medical Services With His Comparative Analysis Of Health Management Information System Tools
Transforming Medical Services With His Comparative Analysis Of Health Management Information System ToolsThis slide covers comparative assessment of health management information tool to select suitable one. It involves features such as clinical database, data compliance, enhanced security and healthcare analytics. Present the topic in a bit more detail with this Transforming Medical Services With His Comparative Analysis Of Health Management Information System Tools. Use it as a tool for discussion and navigation on Solution, Features, Cost. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
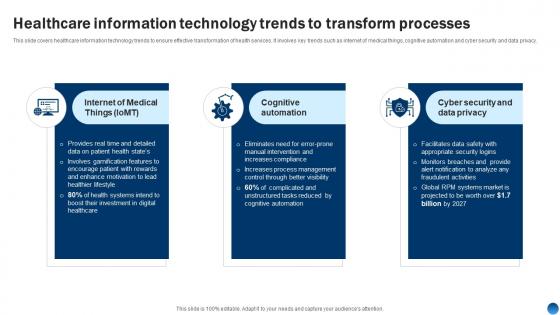 Health Information Management System Healthcare Information Technology Trends To Transform Processes
Health Information Management System Healthcare Information Technology Trends To Transform ProcessesThis slide covers healthcare information technology trends to ensure effective transformation of health services. It involves key trends such as internet of medical things, cognitive automation and cyber security and data privacy. Introducing Health Information Management System Healthcare Information Technology Trends To Transform Processes to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Information,Technology,Processes, using this template. Grab it now to reap its full benefits.
-
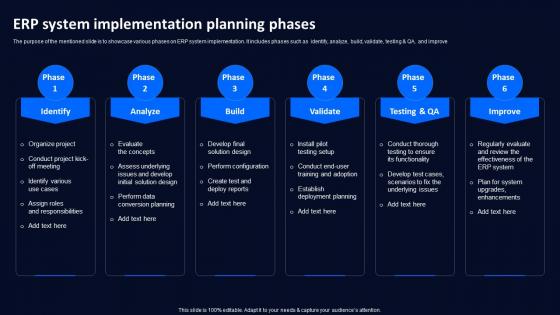 ERP System Implementation Planning Phases Technology Deployment Plan To Improve Organizations
ERP System Implementation Planning Phases Technology Deployment Plan To Improve OrganizationsThe purpose of the mentioned slide is to showcase various phases on ERP system implementation. It includes phases such as identify, analyze, build, validate, testing and QA, and improve Increase audience engagement and knowledge by dispensing information using ERP System Implementation Planning Phases Technology Deployment Plan To Improve Organizations. This template helps you present information on six stages. You can also present information on Identify, Analyze, Improve using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Smart Grid Technology Impact Of Smart Grid System Implementation
Smart Grid Technology Impact Of Smart Grid System ImplementationThis slide depicts the implementation impact of smart grid technology, including electricity load reduction, elimination of demand fraction, and distribution of power generation by customers or end users. Introducing Smart Grid Technology Impact Of Smart Grid System Implementation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Implementation, Distribution, Power Generation, using this template. Grab it now to reap its full benefits.
-
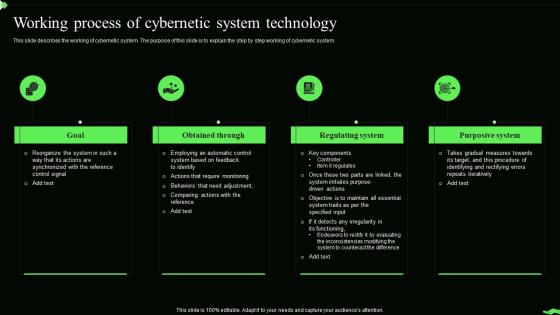 Information Theory Working Process Of Cybernetic System Technology
Information Theory Working Process Of Cybernetic System TechnologyThis slide describes the working of cybernetic system. The purpose of this slide is to explain the step by step working of cybernetic system. Increase audience engagement and knowledge by dispensing information using Information Theory Working Process Of Cybernetic System Technology. This template helps you present information on four stages. You can also present information on Obtained Through, Regulating System, Purposive System, Cybernetic System Technology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
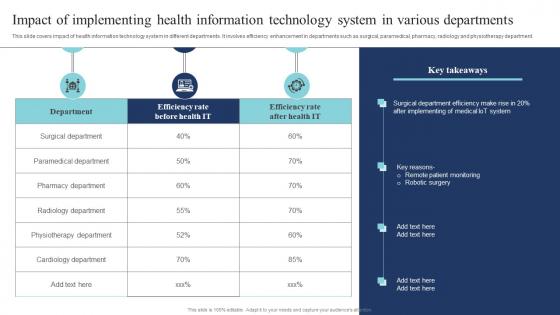 Impact Of Implementing Health Information Technology System Guide Of Digital Transformation DT SS
Impact Of Implementing Health Information Technology System Guide Of Digital Transformation DT SSThis slide covers impact of health information technology system in different departments. It involves efficiency enhancement in departments such as surgical, paramedical, pharmacy, radiology and physiotherapy department. Present the topic in a bit more detail with this Impact Of Implementing Health Information Technology System Guide Of Digital Transformation DT SS Use it as a tool for discussion and navigation on Surgical Department, Paramedical Department, Radiology Department This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Smart Healthcare System Framework With Key Technologies Guide Of Digital Transformation DT SS
Smart Healthcare System Framework With Key Technologies Guide Of Digital Transformation DT SSThis slide covers smart healthcare system framework with emerging technologies and advancements. It involves virtual assistants, smart furniture, motion sensors and IoT trackers. Present the topic in a bit more detail with this Smart Healthcare System Framework With Key Technologies Guide Of Digital Transformation DT SS Use it as a tool for discussion and navigation on Connected Appliances, Medical Asset Trackers, Motion Sensors This template is free to edit as deemed fit for your organization. Therefore download it now.
-
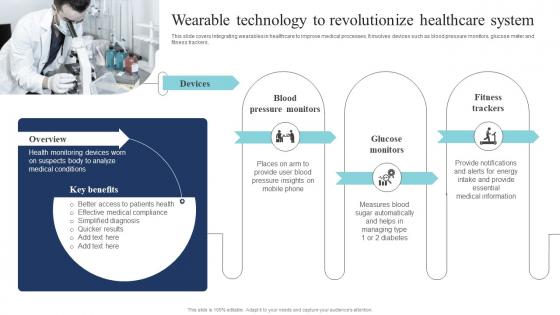 Wearable Technology To Revolutionize Healthcare System Guide Of Digital Transformation DT SS
Wearable Technology To Revolutionize Healthcare System Guide Of Digital Transformation DT SSThis slide covers integrating wearables in healthcare to improve medical processes. It involves devices such as blood pressure monitors, glucose meter and fitness trackers. Introducing Wearable Technology To Revolutionize Healthcare System Guide Of Digital Transformation DT SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Blood Pressure Monitors, Glucose Monitors, Fitness Trackers using this template. Grab it now to reap its full benefits.



