Powerpoint Templates and Google slides for Terror
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
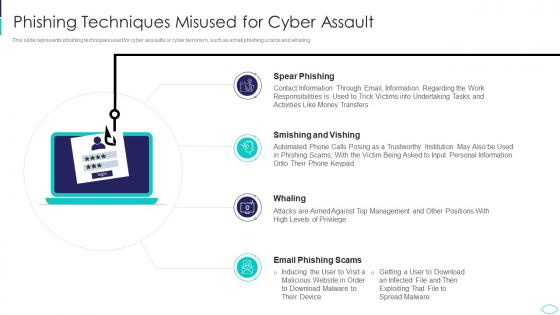 Phishing Techniques Misused For Cyber Assault Cyber Terrorism Attacks
Phishing Techniques Misused For Cyber Assault Cyber Terrorism AttacksThis slide represents phishing techniques used for cyber assaults or cyber terrorism, such as email phishing scams and whaling. Introducing Phishing Techniques Misused For Cyber Assault Cyber Terrorism Attacks to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Phishing Techniques Misused For Cyber Assault, using this template. Grab it now to reap its full benefits.
-
 Reputational Loss Faced By The Company Cyber Terrorism Attacks
Reputational Loss Faced By The Company Cyber Terrorism AttacksThis slide demonstrates the reputational loss of the company due to cyber terrorism, which leads to the customers leaving and a decline in sales. Increase audience engagement and knowledge by dispensing information using Reputational Loss Faced By The Company Cyber Terrorism Attacks. This template helps you present information on five stages. You can also present information on Margin Reduces, Cyber Assaults, Influence, Suppliers, Stakeholders using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Roadmap To Implement Cyber Security Cyber Terrorism Attacks
Roadmap To Implement Cyber Security Cyber Terrorism AttacksThis slide depicts the roadmap to implement strategies to mitigate cyber terrorism such as training employees about cyber terrorism, creating personal accounts. Introducing Roadmap To Implement Cyber Security Cyber Terrorism Attacks to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Personal Accounts, Awareness Training, Software Updated, using this template. Grab it now to reap its full benefits.
-
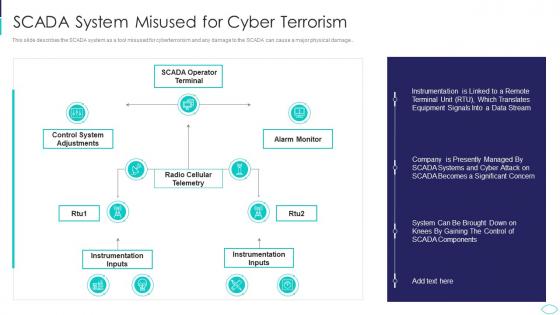 SCADA System Misused For Cyber Terrorism Cyber Terrorism Attacks
SCADA System Misused For Cyber Terrorism Cyber Terrorism AttacksThis slide describes the SCADA system as a tool misused for cyberterrorism and any damage to the SCADA can cause a major physical damage.. Present the topic in a bit more detail with this SCADA System Misused For Cyber Terrorism Cyber Terrorism Attacks. Use it as a tool for discussion and navigation on Scada System Misused For Cyber Terrorism. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
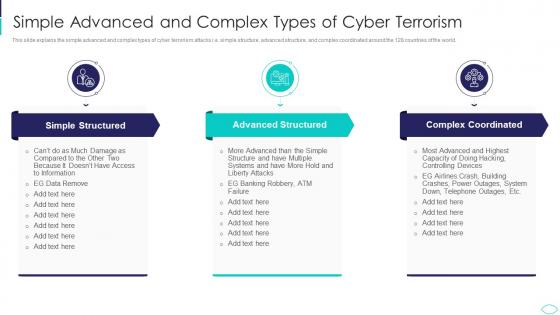 Simple Advanced And Complex Types Cyber Terrorism Attacks
Simple Advanced And Complex Types Cyber Terrorism AttacksThis slide explains the simple advanced and complex types of cyber terrorism attacks i.e. simple structure, advanced structure, and complex coordinated around the 128 countries of the world. Increase audience engagement and knowledge by dispensing information using Simple Advanced And Complex Types Cyber Terrorism Attacks. This template helps you present information on three stages. You can also present information on Simple Structured, Advanced Structured, Complex Coordinated using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
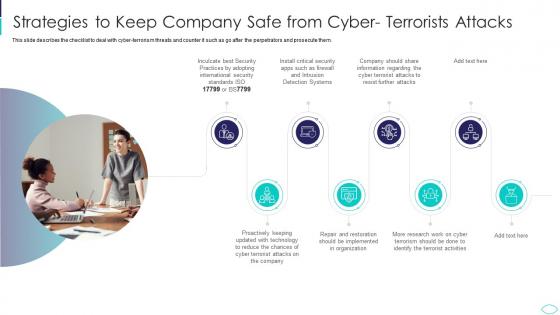 Strategies To Keep Company Safe From Cyber Terrorism Attacks
Strategies To Keep Company Safe From Cyber Terrorism AttacksThis slide describes the checklist to deal with cyber terrorism threats and counter it such as go after the perpetrators and prosecute them. Introducing Strategies To Keep Company Safe From Cyber Terrorism Attacks to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Technology, Reduce, Implemented, Restoration, Organization, using this template. Grab it now to reap its full benefits.
-
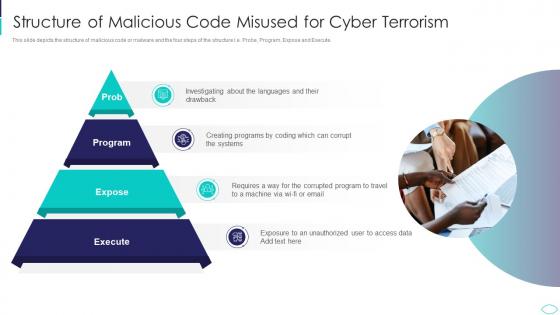 Structure Of Malicious Code Misused Cyber Terrorism Attacks
Structure Of Malicious Code Misused Cyber Terrorism AttacksThis slide depicts the structure of malicious code or malware and the four steps of the structure i.e. Probe, Program, Expose and Execute.Increase audience engagement and knowledge by dispensing information using Structure Of Malicious Code Misused Cyber Terrorism Attacks. This template helps you present information on four stages. You can also present information on Structure Of Malicious Code Misused For Cyber Terrorism using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Table Of Contents For Cyber Terrorism Attacks Mitigate
Table Of Contents For Cyber Terrorism Attacks MitigateIntroducing Table Of Contents For Cyber Terrorism Attacks Mitigate to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Assessment Matrix, Security Budget, Security Measures, using this template. Grab it now to reap its full benefits.
-
 Techniques To Protect SCADA Systems From Cyber Terrorism Attacks
Techniques To Protect SCADA Systems From Cyber Terrorism AttacksThis slide depicts the techniques to protect SCADA from cyber attacks which include security training of employees, strict firewalls. Increase audience engagement and knowledge by dispensing information using Techniques To Protect SCADA Systems From Cyber Terrorism Attacks. This template helps you present information on six stages. You can also present information on Security Training, Access Controls, Strict Firewalls, Security Procedures using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Three Major Forms Of Cyber Terrorism Attacks Ppt Slides Designs Download
Three Major Forms Of Cyber Terrorism Attacks Ppt Slides Designs DownloadThis slide describes the three major forms of cyber terrorism attacks such as privacy violation, networks damage, and disruptions, and distribution denial of service attack. Introducing Three Major Forms Of Cyber Terrorism Attacks Ppt Slides Designs Download to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Privacy Violation, Damage Disruptions, Distributed Denial, using this template. Grab it now to reap its full benefits.
-
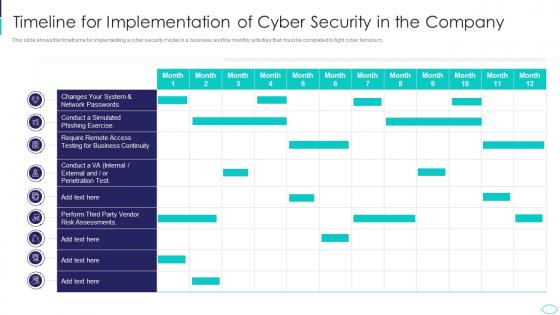 Timeline For Implementation Cyber Terrorism Attacks
Timeline For Implementation Cyber Terrorism AttacksThis slide shows the timeframe for implementing a cyber security model in a business and the monthly activities that must be completed to fight cyber terrorism. Deliver an outstanding presentation on the topic using this Timeline For Implementation Cyber Terrorism Attacks. Dispense information and present a thorough explanation of Timeline For Implementation Of Cyber Security In The Company using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
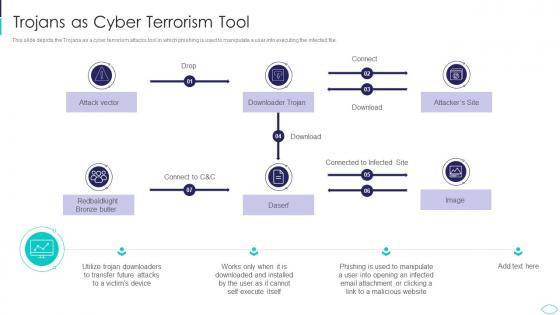 Trojans As Cyber Terrorism Tool Cyber Terrorism Attacks
Trojans As Cyber Terrorism Tool Cyber Terrorism AttacksThis slide depicts the Trojans as a cyber terrorism attacks tool in which phishing is used to manipulate a user into executing the infected file. Present the topic in a bit more detail with this Trojans As Cyber Terrorism Tool Cyber Terrorism Attacks. Use it as a tool for discussion and navigation on Trojans As Cyber Terrorism Tool. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
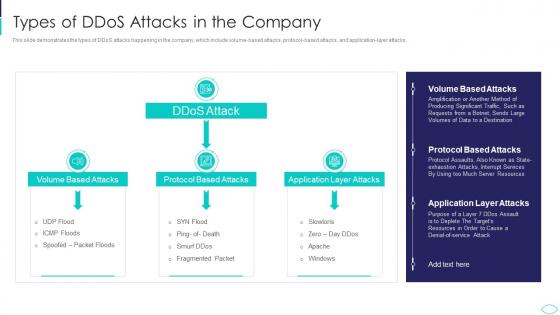 Types Of Ddos Attacks In The Company Cyber Terrorism Attacks
Types Of Ddos Attacks In The Company Cyber Terrorism AttacksThis slide demonstrates the types of DDoS attacks happening in the company, which include volume based attacks, protocol based attacks, and application layer attacks. Deliver an outstanding presentation on the topic using this Types Of Ddos Attacks In The Company Cyber Terrorism Attacks. Dispense information and present a thorough explanation of Application Layer Attacks, Protocol Based Attacks, Volume Based Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
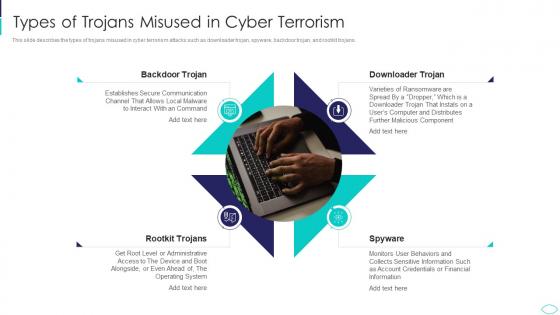 Types Of Trojans Misused In Cyber Terrorism Cyber Terrorism Attacks
Types Of Trojans Misused In Cyber Terrorism Cyber Terrorism AttacksThis slide describes the types of trojans misused in cyber terrorism attacks such as downloader trojan, spyware, backdoor trojan, and rootkit trojans. Increase audience engagement and knowledge by dispensing information using Types Of Trojans Misused In Cyber Terrorism Cyber Terrorism Attacks. This template helps you present information on four stages. You can also present information on Types Of Trojans Misused In Cyber Terrorism using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
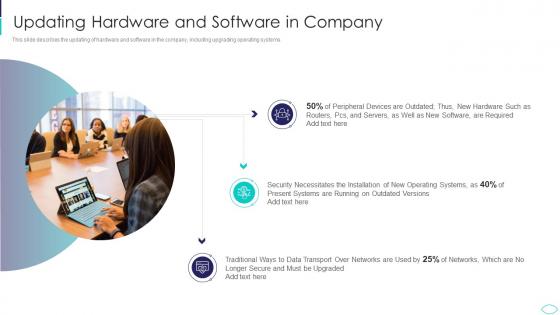 Updating Hardware And Software In Company Cyber Terrorism Attacks
Updating Hardware And Software In Company Cyber Terrorism AttacksThis slide describes the updating of hardware and software in the company, including upgrading operating systems. Introducing Updating Hardware And Software In Company Cyber Terrorism Attacks to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Required, Necessitates, Installation, Transport, using this template. Grab it now to reap its full benefits.
-
 What Is Cyber Terrorism Ppt Slides Infographic Template
What Is Cyber Terrorism Ppt Slides Infographic TemplateThis slide describes cyber terrorism and how it is used to access sensitive information and political or psychological aimed attacks. Increase audience engagement and knowledge by dispensing information using What Is Cyber Terrorism Ppt Slides Infographic Template. This template helps you present information on four stages. You can also present information on Confidential, Information, Violating, Networks, Ideological using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Average Financial Loss Of Companies Per Cyber Terrorism Incident
Average Financial Loss Of Companies Per Cyber Terrorism IncidentThis slide represents the financial losses faced by the companies per cyber terrorism incident. It shows the average financial loss faced by small, medium and large companies per cyber terrorism incident. Presenting our set of slides with name Average Financial Loss Of Companies Per Cyber Terrorism Incident. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Financial Loss, Cyber Terrorism, Revenue.
-
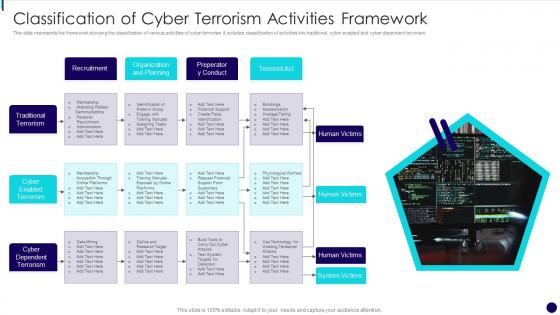 Classification Of Cyber Terrorism Activities Framework
Classification Of Cyber Terrorism Activities FrameworkThis slide represents the framework showing the classification of various activities of cyber terrorism. It includes classification of activities into traditional, cyber enabled and cyber dependent terrorism. Introducing our premium set of slides with name Classification Of Cyber Terrorism Activities Framework. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Recruitment, Organization And Planning, Traditional Terrorism, Cyber Dependent Terrorism. So download instantly and tailor it with your information.
-
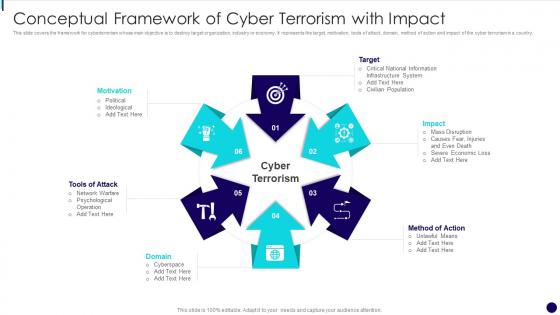 Conceptual Framework Of Cyber Terrorism With Impact
Conceptual Framework Of Cyber Terrorism With ImpactThis slide covers the framework for cyberterrorism whose main objective is to destroy target organization, industry or economy. It represents the target, motivation, tools of attack, domain, method of action and impact of the cyber terrorism in a country. Presenting our set of slides with name Conceptual Framework Of Cyber Terrorism With Impact. This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Motivation, Ideological, Network Warfare, Psychological Operation.
-
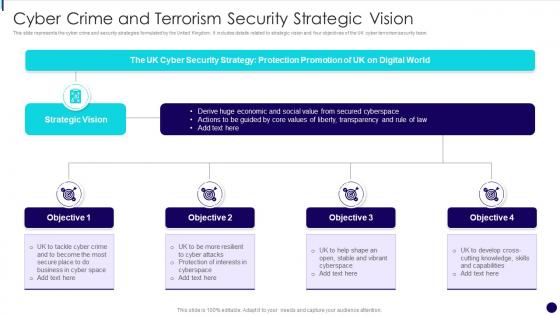 Cyber Crime And Terrorism Security Strategic Vision
Cyber Crime And Terrorism Security Strategic VisionThis slide represents the cyber crime and security strategies formulated by the United Kingdom. It includes details related to strategic vision and four objectives of the UK cyber terrorism security team. Introducing our premium set of slides with name Cyber Crime And Terrorism Security Strategic Vision. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Strategic Vision, Protection Promotion, Protection Of Interests In Cyberspace. So download instantly and tailor it with your information.
-
 Cyber Crime And Terrorism Strategies Icon
Cyber Crime And Terrorism Strategies IconPresenting our set of slides with name Cyber Crime And Terrorism Strategies Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Crime And Terrorism Strategies Icon.
-
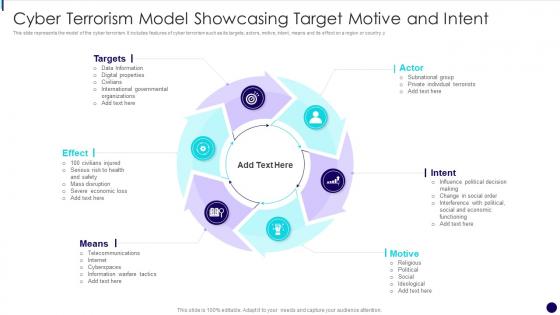 Cyber Terrorism Model Showcasing Target Motive And Intent
Cyber Terrorism Model Showcasing Target Motive And IntentThis slide represents the model of the cyber terrorism. It includes features of cyber terrorism such as its targets, actors, motive, intent, means and its effect on a region or country. Introducing our premium set of slides with name Cyber Terrorism Model Showcasing Target Motive And Intent. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Targets, Intent, Motive, Data Information, Digital Properties. So download instantly and tailor it with your information.
-
 Cyber Terrorism Prevention Tools Comparative Analysis
Cyber Terrorism Prevention Tools Comparative AnalysisThis slide represents the comparison between various cyber terrorism prevention tools on the basis of their top features, bottom line and the free trials provided. It includes features such as multiple server support, breach severity insights, anti-exploit module etc. Introducing our Cyber Terrorism Prevention Tools Comparative Analysis set of slides. The topics discussed in these slides are Analysis Of Event Logs, Detection Of SQL Injection Attacks, Highly Automated, Comprehensive. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
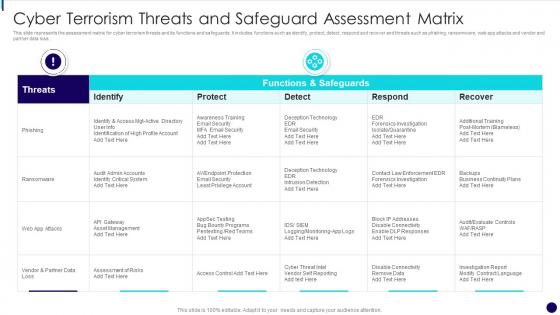 Cyber Terrorism Threats And Safeguard Assessment Matrix
Cyber Terrorism Threats And Safeguard Assessment MatrixThis slide represents the assessment matrix for cyber terrorism threats and its functions and safeguards. It includes functions such as identify, protect, detect, respond and recover and threats such as phishing, ransomware, web app attacks and vendor and partner data loss. Presenting our well structured Cyber Terrorism Threats And Safeguard Assessment Matrix. The topics discussed in this slide are Phishing, Ransomware, Deception Technology. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
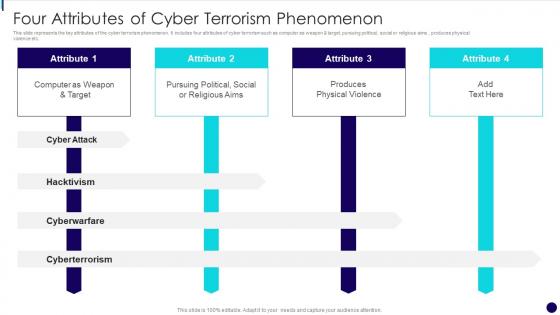 Four Attributes Of Cyber Terrorism Phenomenon
Four Attributes Of Cyber Terrorism PhenomenonThis slide represents the key attributes of the cyber terrorism phenomenon. It includes four attributes of cyber terrorism such as computer as weapon and target, pursuing political, social or religious aims , produces physical violence etc. Introducing our Four Attributes Of Cyber Terrorism Phenomenon set of slides. The topics discussed in these slides are Cyber Attack, Cyberwarfare, Cyberterrorism. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Global Cyber Terrorism Attacks Icon
Global Cyber Terrorism Attacks IconPresenting our set of slides with name Global Cyber Terrorism Attacks Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Global Cyber Terrorism Attacks Icon.
-
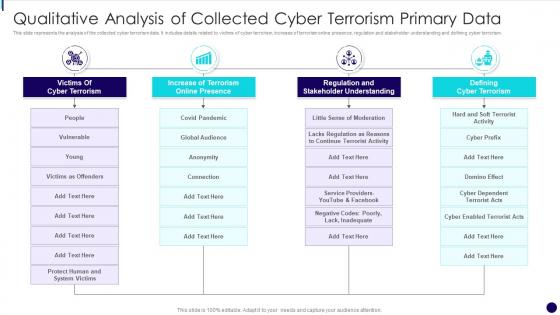 Qualitative Analysis Of Collected Cyber Terrorism Primary Data
Qualitative Analysis Of Collected Cyber Terrorism Primary DataThis slide represents the analysis of the collected cyber terrorism data. It includes details related to victims of cyber terrorism, increase of terrorism online presence, regulation and stakeholder understanding and defining cyber terrorism. Introducing our premium set of slides with name Qualitative Analysis Of Collected Cyber Terrorism Primary Data. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Regulation And Stakeholder Understanding, Defining Cyber Terrorism, Terrorism Online Presence. So download instantly and tailor it with your information.
-
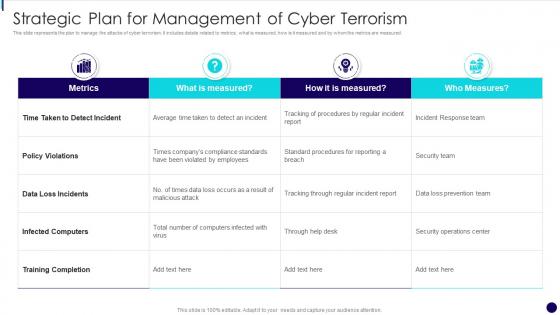 Strategic Plan For Management Of Cyber Terrorism
Strategic Plan For Management Of Cyber TerrorismThis slide represents the plan to manage the attacks of cyber terrorism. It includes details related to metrics, what is measured, how is it measured and by whom the metrics are measured. Introducing our Strategic Plan For Management Of Cyber Terrorism set of slides. The topics discussed in these slides are Policy Violations, Training Completion, Strategic Plan. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Survey Insights On Cyber Terrorism Attacks Icons
Survey Insights On Cyber Terrorism Attacks IconsIntroducing our premium set of slides with name Survey Insights On Cyber Terrorism Attacks Icons. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Survey Insights On Cyber Terrorism Attacks Icons. So download instantly and tailor it with your information.
-
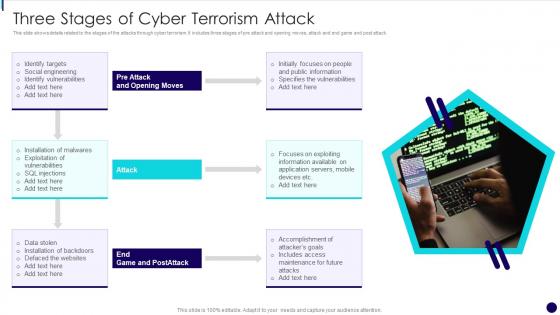 Three Stages Of Cyber Terrorism Attack
Three Stages Of Cyber Terrorism AttackThis slide shows details related to the stages of the attacks through cyber terrorism. It includes three stages of pre attack and opening moves, attack and end game and post attack. Presenting our set of slides with name Three Stages Of Cyber Terrorism Attack. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Social Engineering, Identify Vulnerabilities, Exploitation Of Vulnerabilities, Data Stolen.
-
 Various Cyber Terrorism Threats With Risk Priority
Various Cyber Terrorism Threats With Risk PriorityThis slide represents the five major threats caused by cyber terrorism along with their risk priorities. It includes threats such as malware, phishing, spear fishing, SQL injection and advanced persistent threats. Presenting our well structured Various Cyber Terrorism Threats With Risk Priority. The topics discussed in this slide are Phishing, Malicious Software, Threat. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cyberterrorism it agenda for cyber terrorism ppt slides diagrams
Cyberterrorism it agenda for cyber terrorism ppt slides diagramsIntroducing Cyberterrorism IT Agenda For Cyber Terrorism Ppt Slides Diagrams to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Cyber Terrorism, Current Situation, Globe And Tools, using this template. Grab it now to reap its full benefits.
-
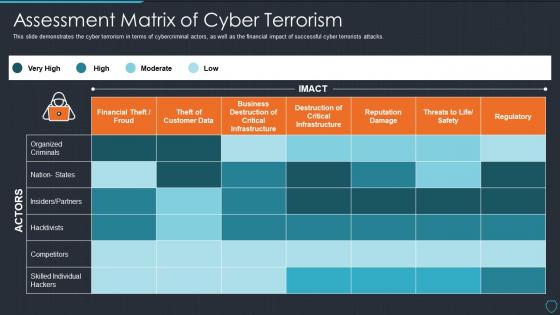 Cyberterrorism it assessment matrix of cyber terrorism ppt slides picture
Cyberterrorism it assessment matrix of cyber terrorism ppt slides pictureThis slide demonstrate cyber terrorism in terms of cybercriminal actors, as well as the financial impact of successful cyber terrorists attacks. Present the topic in a bit more detail with this Cyberterrorism IT Assessment Matrix Of Cyber Terrorism Ppt Slides Picture. Use it as a tool for discussion and navigation on Organized Criminals, Financial Theft Froud, Business Destruction. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyberterrorism it checklist to deal with cyber terrorism threats ppt slides templates
Cyberterrorism it checklist to deal with cyber terrorism threats ppt slides templatesThis slide represents the checklist to deal with cyber terrorism threats which involve 24 7 monitoring, employee training, keeping software updated. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Checklist To Deal With Cyber Terrorism Threats Ppt Slides Templates. This template helps you present information on one stages. You can also present information on Incident Response Plan, Limited Access Privileges, Evaluating Risk Third Party Vendor, Cyber Security Assessment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
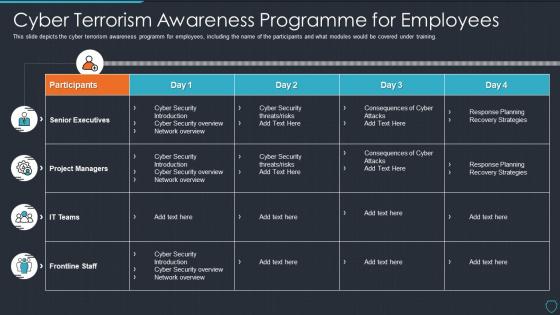 Cyberterrorism it cyber terrorism awareness programme for employees
Cyberterrorism it cyber terrorism awareness programme for employeesThis slide depicts the cyber terrorism awareness programm for employees, including the name of the participants and what modules would be covered under training. Present the topic in a bit more detail with this Cyberterrorism IT Cyber Terrorism Awareness Programme For Employees. Use it as a tool for discussion and navigation on Frontline Staff, IT Teams, Project Managers, Senior Executives. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyberterrorism it cyber terrorism issues faced by the company ppt slides styles
Cyberterrorism it cyber terrorism issues faced by the company ppt slides stylesThis slide represents the cyber terrorism issues faced by the company, such as increased costs, reputational damage, loss in revenue. Introducing Cyberterrorism IT Cyber Terrorism Issues Faced By The Company Ppt Slides Styles to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Increased Costs, Reputational Damage, Lost Revenue, Intellectual Property Theft, using this template. Grab it now to reap its full benefits.
-
 Cyberterrorism it cyber terrorist attacks experienced by company in previous financial year
Cyberterrorism it cyber terrorist attacks experienced by company in previous financial yearThis slide describes the number of cyber-terrorist attacks experienced by the company in the previous financial year 2020. Present the topic in a bit more detail with this Cyberterrorism IT Cyber Terrorist Attacks Experienced By Company In Previous Financial Year. Use it as a tool for discussion and navigation on Cyber Crime, Lowest Cyber Crimes. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyberterrorism it employee awareness training budget against cyber terrorism fy2020
Cyberterrorism it employee awareness training budget against cyber terrorism fy2020This slide demonstrates the employee awareness training budget against cyber-terrorism by a graph that includes the training date, and the degree of capacity. Present the topic in a bit more detail with this Cyberterrorism IT Employee Awareness Training Budget Against Cyber Terrorism FY2020. Use it as a tool for discussion and navigation on Provider, Training Date, Duration, Budget, Capability Level. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
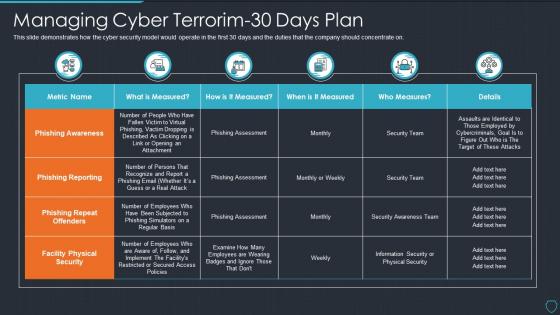 Cyberterrorism it managing cyber terrorim 30 days plan
Cyberterrorism it managing cyber terrorim 30 days planThis slide demonstrates how the cyber security model would operate in the first 30 days and the duties that the company should concentrate on. Present the topic in a bit more detail with this Cyberterrorism IT Managing Cyber Terrorim 30 Days Plan. Use it as a tool for discussion and navigation on Phishing Awareness, Phishing Reporting, Phishing Repeat Offende, Facility Physical Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
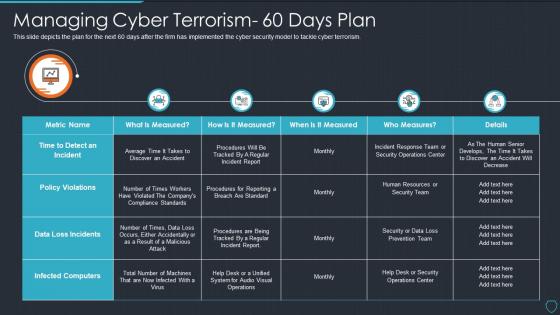 Cyberterrorism it managing cyber terrorism 60 days plan
Cyberterrorism it managing cyber terrorism 60 days planThis slide depicts the plan for the next 60 days after the firm has implemented the cyber security model to tackle cyber terrorism. Deliver an outstanding presentation on the topic using this Cyberterrorism IT Managing Cyber Terrorism 60 Days Plan. Dispense information and present a thorough explanation of Data Loss Incidents, Infected Computers, Policy Violations, Measures using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
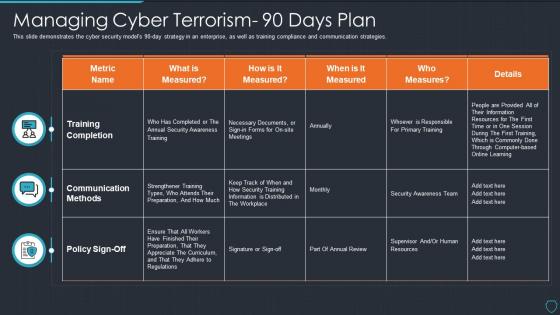 Cyberterrorism it managing cyber terrorism 90 days plan
Cyberterrorism it managing cyber terrorism 90 days planThis slide demonstrates the cyber security models 90 day strategy in an enterprise, as well as training compliance and communication strategies. Present the topic in a bit more detail with this Cyberterrorism IT Managing Cyber Terrorism 90 Days Plan. Use it as a tool for discussion and navigation on Training Completion, Communication Methods, Measured. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyberterrorism it peroration of cyber terrorism ppt slides layout
Cyberterrorism it peroration of cyber terrorism ppt slides layoutThis slide explains the conclusion or peroration of cyber terrorism and how it is different from information warfare as it targets civilians rather than operations. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Peroration Of Cyber Terrorism Ppt Slides Layout. This template helps you present information on six stages. You can also present information on Cyber Terrorism, Information Warfare, Except IT Targets, Cyber Terrorism using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyberterrorism it phishing cyber terrorism tool ppt slides graphics
Cyberterrorism it phishing cyber terrorism tool ppt slides graphicsThis slide describes phishing in which an attacker tricks a victim to open an email, provide card credentials or any sensitive information. Introducing Cyberterrorism IT Phishing Cyber Terrorism Tool Ppt Slides Graphics to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Obtain Sensitive Information, Credit Card Details, Business, Consumer Confidence, using this template. Grab it now to reap its full benefits.
-
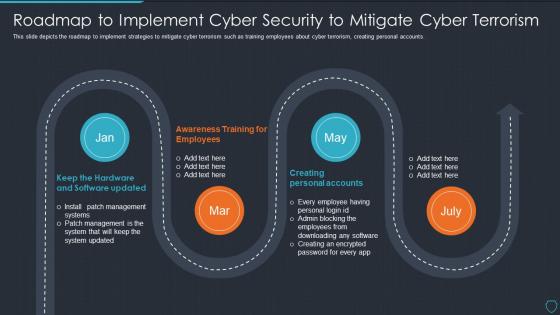 Cyberterrorism it roadmap to implement cyber security to mitigate cyber terrorism
Cyberterrorism it roadmap to implement cyber security to mitigate cyber terrorismThis slide depicts the roadmap to implement strategies to mitigate cyber terrorism such as training employees about cyber terrorism, creating personal accounts. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Roadmap To Implement Cyber Security To Mitigate Cyber Terrorism. This template helps you present information on four stages. You can also present information on Creating Personal Accounts, Awareness Training Employees, Keep Hardware And Software Updated using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
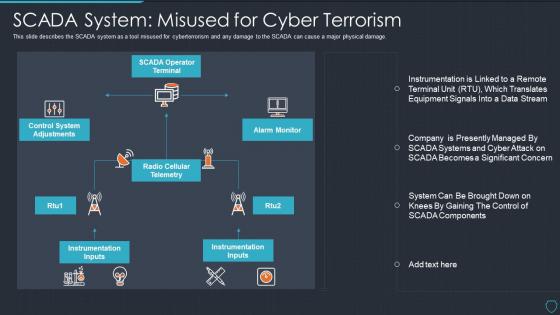 Cyberterrorism it scada system misused for cyber terrorism
Cyberterrorism it scada system misused for cyber terrorismThis slide describes the SCADA system as a tool misused for cyberterrorism and any damage to the SCADA can cause a major physical damage. Introducing Cyberterrorism IT SCADA System Misused For Cyber Terrorism to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on SCADA Operator Terminal, Alarm Monitor, Radio Cellular Telemetry, Control System Adjustments, Instrumentation Inputs, using this template. Grab it now to reap its full benefits.
-
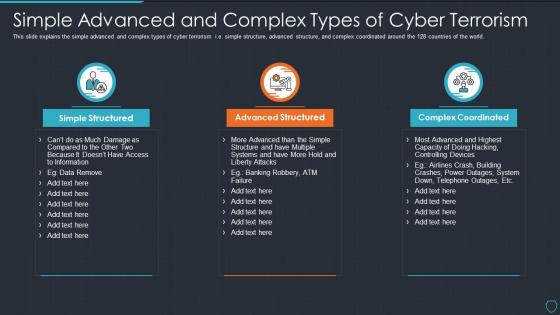 Cyberterrorism it simple advanced and complex types of cyber terrorism
Cyberterrorism it simple advanced and complex types of cyber terrorismThis slide explains the simple advanced and complex types of cyber terrorism i.e. simple structure, advanced structure, and complex coordinated around the 128 countries of the world. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Simple Advanced And Complex Types Of Cyber Terrorism. This template helps you present information on three stages. You can also present information on Simple Structured, Advanced Structured, Complex Coordinated using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
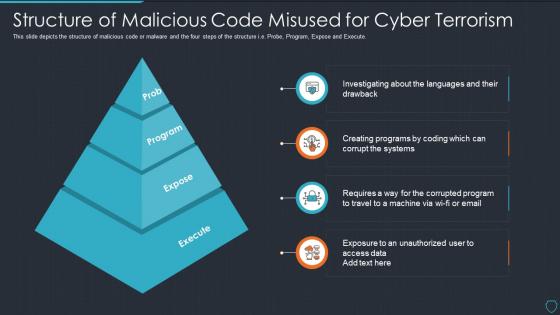 Cyberterrorism it structure of malicious code misused for cyber terrorism
Cyberterrorism it structure of malicious code misused for cyber terrorismThis slide depicts the structure of malicious code or malware and the four steps of the structure i.e. Probe, Program, Expose and Execute. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Structure Of Malicious Code Misused For Cyber Terrorism. This template helps you present information on four stages. You can also present information on Prob, Program, Expose, Execute using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyberterrorism it table of contents for cyber terrorism ppt slides sample
Cyberterrorism it table of contents for cyber terrorism ppt slides samplePresent the topic in a bit more detail with this Cyberterrorism IT Table Of Contents For Cyber Terrorism Ppt Slides Sample. Use it as a tool for discussion and navigation on Assessment Matrix, Cyber Terrorism, Timeline, Dashboard, Threat Tracking. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
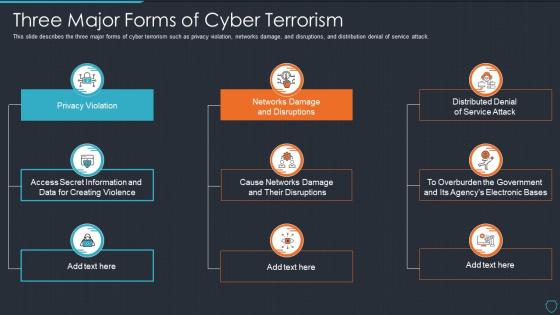 Cyberterrorism it three major forms of cyber terrorism ppt slides tips
Cyberterrorism it three major forms of cyber terrorism ppt slides tipsThis slide describes the three major forms of cyber terrorism such as privacy violation, networks damage, and disruptions, and distribution denial of service attack. Introducing Cyberterrorism IT Three Major Forms Of Cyber Terrorism Ppt Slides Tips to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Privacy Violation, Networks Damage And Disruptions, Distributed Denial Service Attack, Cause Networks Damage And Their Disruptions, using this template. Grab it now to reap its full benefits.
-
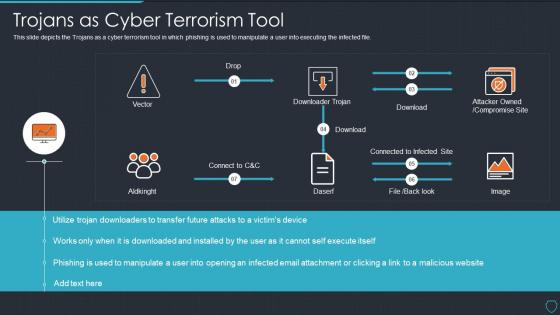 Cyberterrorism it trojans as cyber terrorism tool ppt slides aids
Cyberterrorism it trojans as cyber terrorism tool ppt slides aidsThis slide depicts the Trojans as a cyber terrorism tool in which phishing is used to manipulate a user into executing the infected file. Deliver an outstanding presentation on the topic using this Cyberterrorism IT Trojans As Cyber Terrorism Tool Ppt Slides Aids. Dispense information and present a thorough explanation of Attacker Owned, Compromise Site, Downloader Trojan using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
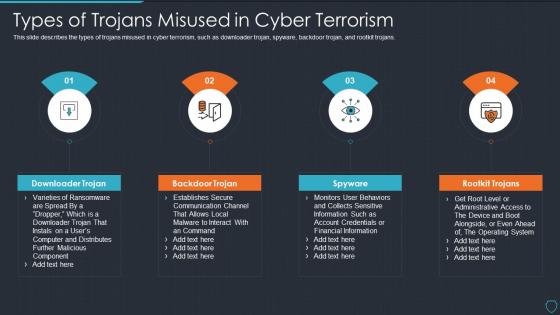 Cyberterrorism it types of trojans misused in cyber terrorism ppt slides tips
Cyberterrorism it types of trojans misused in cyber terrorism ppt slides tipsThis slide describes the types of trojans misused in cyber terrorism, such as downloader trojan, spyware, backdoor trojan, and rootkit trojans. Introducing Cyberterrorism IT Types Of Trojans Misused In Cyber Terrorism Ppt Slides Tips to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Downloader Trojan, Backdoor Trojan, Spyware, Rootkit Trojans, using this template. Grab it now to reap its full benefits.
-
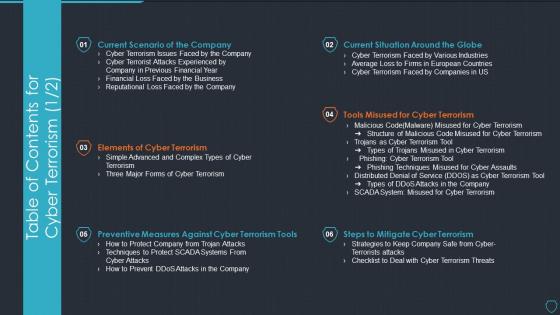 Table of contents for cyber terrorism cyberterrorism it ppt slides tools
Table of contents for cyber terrorism cyberterrorism it ppt slides toolsPresent the topic in a bit more detail with this Table Of Contents For Cyber Terrorism Cyberterrorism IT Ppt Slides Tools. Use it as a tool for discussion and navigation on Current Scenario Company, Elements Cyber Terrorism, Preventive Measures, Against Cyber Terrorism Tools, Steps To Mitigate Cyber Terrorism, Tools Misused Cyber Terrorism, Current Situation Around Globe. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Terrorist Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Terrorist Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Terrorist colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Terrorist Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Terrorist Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Terrorist monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Armed Terrorist Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Armed Terrorist Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Armed terrorist colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Armed Terrorist Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Armed Terrorist Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Armed terrorist monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
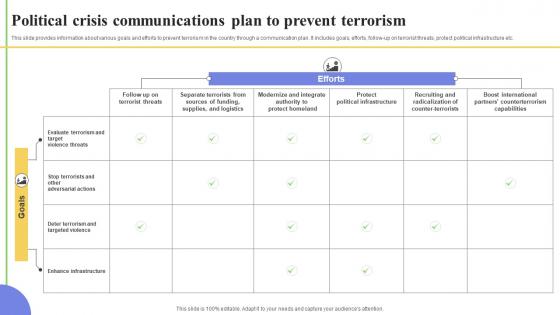 Political Crisis Communications Plan To Prevent Terrorism
Political Crisis Communications Plan To Prevent TerrorismThis slide provides information about various goals and efforts to prevent terrorism in the country through a communication plan. It includes goals, efforts, follow up on terrorist threats, protect political infrastructure etc. Presenting our well structured Political Crisis Communications Plan To Prevent Terrorism. The topics discussed in this slide are Communications, Terrorism, Political. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Haunted House Fright Terror Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Haunted House Fright Terror Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable Haunted house fright terror colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 Haunted House Fright Terror Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Haunted House Fright Terror Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable Haunted house fright terror monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
 Country Wise Security Strategies For Virtual Terrorism
Country Wise Security Strategies For Virtual TerrorismThis slide shows various strategies adopted by different countries to eliminate threat of cyber attacks. It include various risk area covered such as Hostile cyber attacks, International Cyber Attacks etc.Presenting our set of slides with Country Wise Security Strategies For Virtual Terrorism. This exhibits information on one stage of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Consumer Commission, Trusted Identities, Cyber Damage.



