Powerpoint Templates and Google slides for Threats By Owners
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Cyber Threats In Blockchain Top Ten Cryptocurrency Thefts Incidents By Amount BCT SS V
Cyber Threats In Blockchain Top Ten Cryptocurrency Thefts Incidents By Amount BCT SS VThe following slide represents the number of cryptocurrencies theft incidents by total amount to prevent attackers from unauthorized access. It includes elements such as Ronin, poly network, wormhole, BITMART, Venus, cream finance, along with key insights, etc. Present the topic in a bit more detail with this Cyber Threats In Blockchain Top Ten Cryptocurrency Thefts Incidents By Amount BCT SS V Use it as a tool for discussion and navigation on Top Cryptocurrency Threat, Loss Amount This template is free to edit as deemed fit for your organization. Therefore download it now.
-
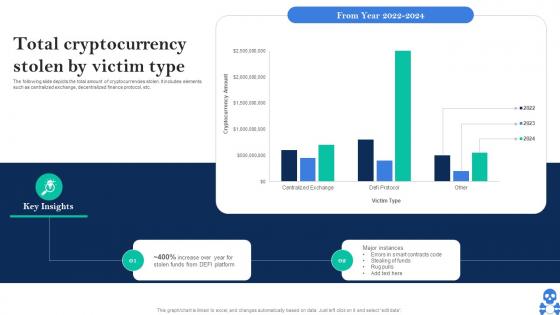 Cyber Threats In Blockchain Total Cryptocurrency Stolen By Victim Type BCT SS V
Cyber Threats In Blockchain Total Cryptocurrency Stolen By Victim Type BCT SS VThe following slide depicts the total amount of cryptocurrencies stolen. It includes elements such as centralized exchange, decentralized finance protocol, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Total Cryptocurrency Stolen By Victim Type BCT SS V Dispense information and present a thorough explanation of Major Instances, Contracts Code using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
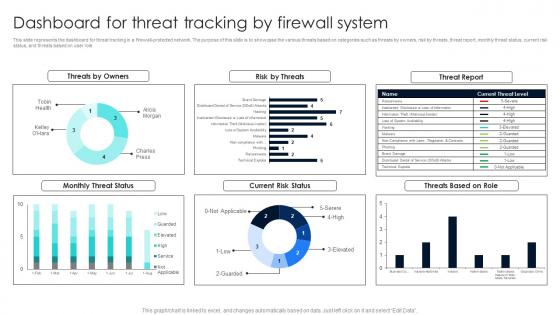 Firewall Network Security Dashboard For Threat Tracking By Firewall System
Firewall Network Security Dashboard For Threat Tracking By Firewall SystemThis slide represents the dashboard for threat tracking in a firewall-protected network. The purpose of this slide is to showcase the various threats based on categories such as threats by owners, risk by threats, threat report, monthly threat status, current risk status, and threats based on user role. Present the topic in a bit more detail with this Firewall Network Security Dashboard For Threat Tracking By Firewall System Use it as a tool for discussion and navigation on Threats By Owners, Current Risk Status, Threats Based On Role This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Ultimate Guide For Blockchain Threats Imposed By Sybil Attack On Blockchain Network BCT SS
Ultimate Guide For Blockchain Threats Imposed By Sybil Attack On Blockchain Network BCT SSThe following slide represents the number of cryptocurrencies theft incidents by total amount to prevent attackers from unauthorized access. It includes elements such as ronin, poly network, wormhole, bitmart, venus, cream finance, along with key insights, etc. Deliver an outstanding presentation on the topic using this Ultimate Guide For Blockchain Threats Imposed By Sybil Attack On Blockchain Network BCT SS Dispense information and present a thorough explanation of Breach Of Privacy, Block Users From Network using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
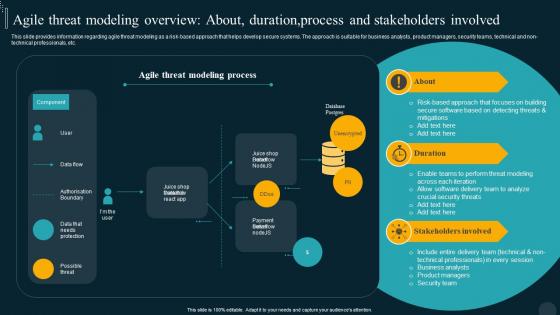 Agile Threat Modeling Overview Utilizing Technology Responsible By Product Developer Playbook
Agile Threat Modeling Overview Utilizing Technology Responsible By Product Developer PlaybookThis slide provides information regarding agile threat modeling as a risk-based approach that helps develop secure systems. The approach is suitable for business analysts, product managers, security teams, technical and non-technical professionals, etc. Present the topic in a bit more detail with this Agile Threat Modeling Overview Utilizing Technology Responsible By Product Developer Playbook. Use it as a tool for discussion and navigation on Stakeholders, Overview, Approach. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
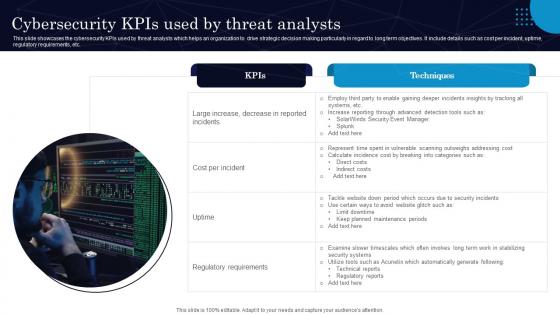 Cybersecurity Kpis Used By Threat Analysts
Cybersecurity Kpis Used By Threat AnalystsThis slide showcases the cybersecurity KPIs used by threat analysts which helps an organization to drive strategic decision making particularly in regard to long term objectives. It include details such as cost per incident, uptime, regulatory requirements, etc. Presenting our set of slides with Cybersecurity Kpis Used By Threat Analysts. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cost Per Incident, Regulatory Requirements.
-
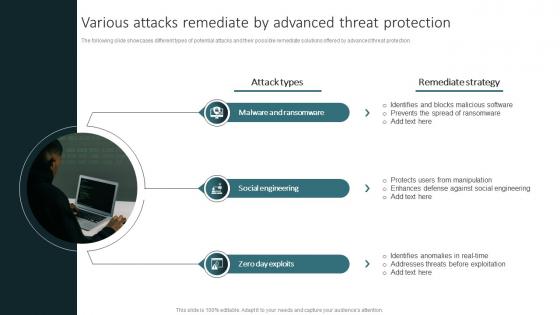 Various Attacks Remediate By Advanced Threat Protection
Various Attacks Remediate By Advanced Threat ProtectionThe following slide showcases different types of potential attacks and their possible remediate solutions offered by advanced threat protection. Introducing our premium set of slides with Various Attacks Remediate By Advanced Threat Protection. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Ransomware, Engineering, Exploits. So download instantly and tailor it with your information.
-
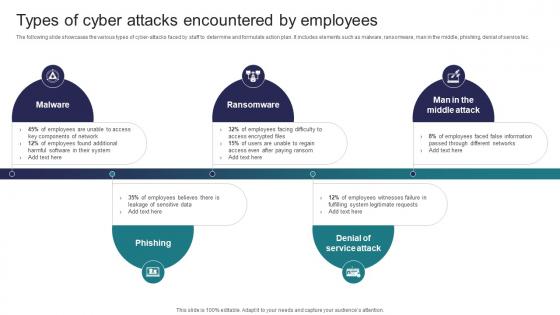 Types Of Cyber Attacks Encountered By Employees Implementing Strategies To Mitigate Cyber Security Threats
Types Of Cyber Attacks Encountered By Employees Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide showcases the various types of cyber attacks faced by staff to determine and formulate action plan. It includes elements such as malware, ransomware, man in the middle, phishing, denial of service tec. Introducing Types Of Cyber Attacks Encountered By Employees Implementing Strategies To Mitigate Cyber Security Threats to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Malware, Ransomware, Phishing using this template. Grab it now to reap its full benefits.
-
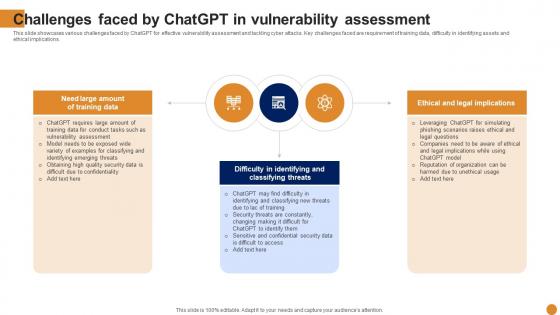 Challenges Faced By Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Challenges Faced By Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various challenges faced by ChatGPT for effective vulnerability assessment and tackling cyber attacks. Key challenges faced are requirement of training data, difficulty in identifying assets and ethical implications. Increase audience engagement and knowledge by dispensing information using Challenges Faced By Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. This template helps you present information on three stages. You can also present information on Vulnerability, Assessment, Implications using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Types Of Cyber Attacks Faced By Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V
Types Of Cyber Attacks Faced By Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS VThis slide showcases various types of cyber attacks that significantly damage the organization resources and reputation. Different types of attacks faced are Malware, Phishing, Man in middle attack, SQL injection etc. Increase audience engagement and knowledge by dispensing information using Types Of Cyber Attacks Faced By Chatgpt For Threat Intelligence And Vulnerability Assessment AI SS V. This template helps you present information on five stages. You can also present information on Phishing, SQL Injection, Organization using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
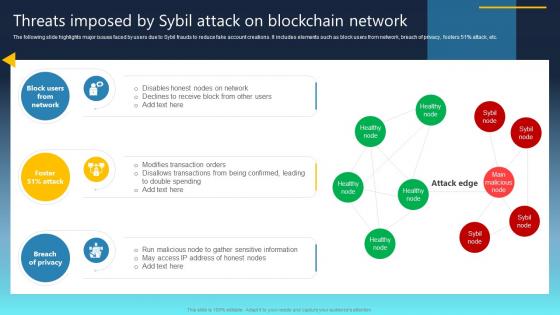
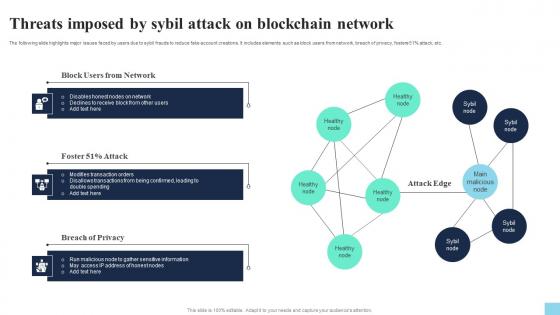 Threats Imposed By Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS V
Threats Imposed By Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS VThe following slide highlights major issues faced by users due to sybil frauds to reduce fake account creations. It includes elements such as block users from network, breach of privacy, fosters 51percentage attack, etc. Increase audience engagement and knowledge by dispensing information using Threats Imposed By Sybil Attack On Blockchain Network Hands On Blockchain Security Risk BCT SS V. This template helps you present information on three stages. You can also present information on Block Users From Network, Attack, Breach Of Privacy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
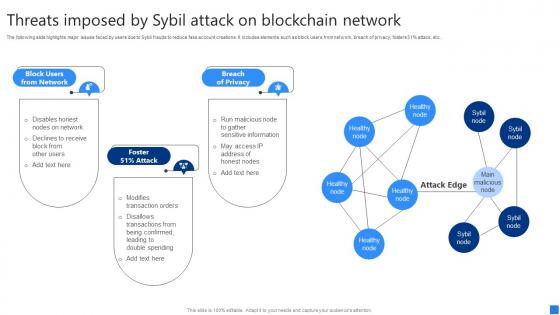 Threats Imposed By Sybil Attack Securing Blockchain Transactions A Beginners Guide BCT SS V
Threats Imposed By Sybil Attack Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide highlights major issues faced by users due to Sybil frauds to reduce fake account creations. It includes elements such as block users from network, breach of privacy, fosters 51percent attack, etc. Introducing Threats Imposed By Sybil Attack Securing Blockchain Transactions A Beginners Guide BCT SS V to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Block Users Network, Foster Attack, Breach Privacy, using this template. Grab it now to reap its full benefits.
-
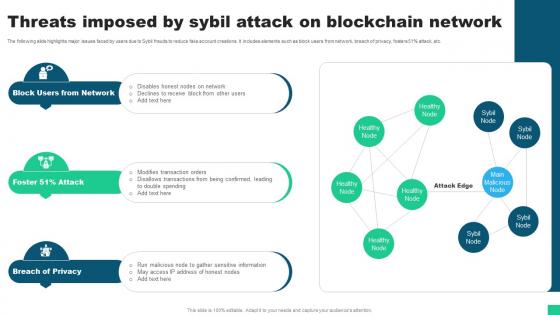 Threats Imposed By Sybil Attack On Blockchain Network Guide For Blockchain BCT SS V
Threats Imposed By Sybil Attack On Blockchain Network Guide For Blockchain BCT SS VThe following slide highlights major issues faced by users due to Sybil frauds to reduce fake account creations. It includes elements such as block users from network, breach of privacy, fosters 51 percent attack, etc. Increase audience engagement and knowledge by dispensing information using Threats Imposed By Sybil Attack On Blockchain Network Guide For Blockchain BCT SS V This template helps you present information on three stages. You can also present information on Block Users From Network, Breach Of Privacy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
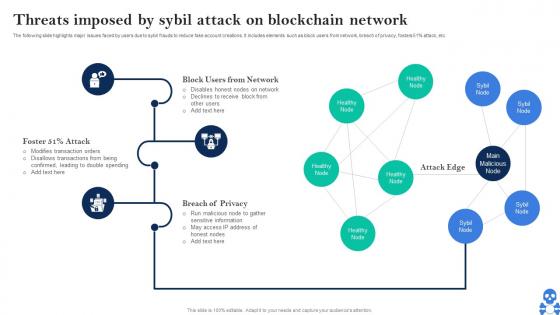 Cyber Threats In Blockchain Threats Imposed By Sybil Attack On Blockchain Network BCT SS V
Cyber Threats In Blockchain Threats Imposed By Sybil Attack On Blockchain Network BCT SS VThe following slide highlights major issues faced by users due to sybil frauds to reduce fake account creations. It includes elements such as block users from network, breach of privacy, fosters 51percent attack, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Threats Imposed By Sybil Attack On Blockchain Network BCT SS V Dispense information and present a thorough explanation of Block Users From Network, Breach Of Privacy, Attack Edge using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
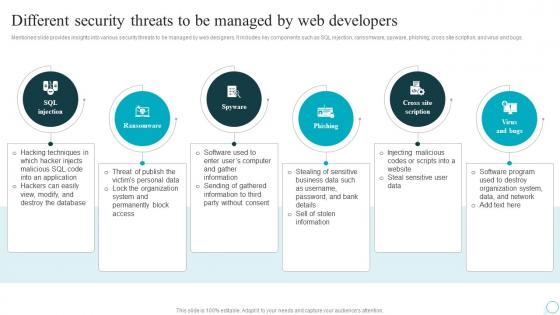 Different Security Threats To Be Managed By Web Strategic Guide For Web Design Company
Different Security Threats To Be Managed By Web Strategic Guide For Web Design CompanyMentioned slide provides insights into various security threats to be managed by web designers. It includes key components such as SQL injection, ransomware, spyware, phishing, cross site scription, and virus and bugs. Increase audience engagement and knowledge by dispensing information using Different Security Threats To Be Managed By Web Strategic Guide For Web Design Company. This template helps you present information on six stages. You can also present information on Injection, Scription, Developers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
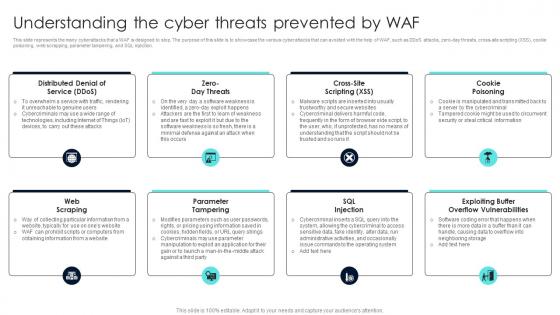 Firewall Network Security Understanding The Cyber Threats Prevented By Waf
Firewall Network Security Understanding The Cyber Threats Prevented By WafThis slide represents the many cyberattacks that a WAF is designed to stop. The purpose of this slide is to showcase the various cyber attacks that can avoided with the help of WAF, such as DDoS attacks, zero-day threats, cross-site scripting XSS, cookie poisoning, web scrapping, parameter tampering, and SQL injection. Introducing Firewall Network Security Understanding The Cyber Threats Prevented By Waf to increase your presentation threshold. Encompassed with Eight stages, this template is a great option to educate and entice your audience. Dispence information on Cookie Poisoning, Sql Injection, Parameter Tampering using this template. Grab it now to reap its full benefits.
-
 Vulnerability Administration At Workplace Current Potential Implications Faced By Firm As Threats
Vulnerability Administration At Workplace Current Potential Implications Faced By Firm As ThreatsThis slide provides information regarding the potential implications or concerns existing in firm in terms of increase in issues related to employees such as lack of expertise, ineffectiveness in handling issues, reported financial losses due to financial threats and data breaches with records exposed. Deliver an outstanding presentation on the topic using this Vulnerability Administration At Workplace Current Potential Implications Faced By Firm As Threats. Dispense information and present a thorough explanation of Potential, Implications, Ineffectiveness using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
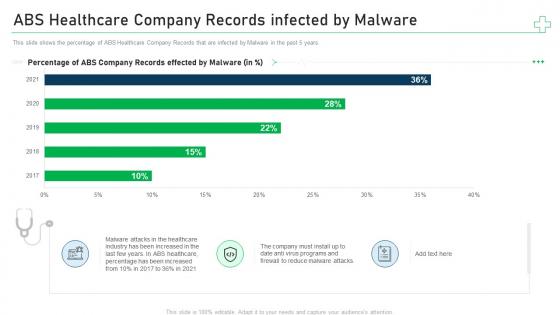 Abs healthcare company records infected by minimize cybersecurity threats in healthcare company
Abs healthcare company records infected by minimize cybersecurity threats in healthcare companyThis slide shows the percentage of ABS Healthcare Company Records that are infected by Malware in the past 5 years. Deliver an outstanding presentation on the topic using this ABS Healthcare Company Records Infected By Minimize Cybersecurity Threats In Healthcare Company. Dispense information and present a thorough explanation of Abs Healthcare Company Records Infected By Malware using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
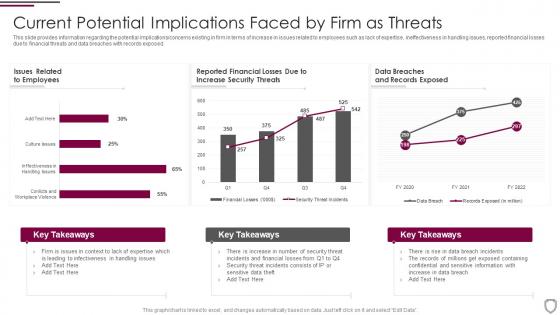 Current potential implications faced by firm as threats corporate security management
Current potential implications faced by firm as threats corporate security managementThis slide provides information regarding the potential implications concerns existing in firm in terms of increase in issues related to employees such as lack of expertise, ineffectiveness in handling issues, reported financial losses due to financial threats and data breaches with records exposed. Present the topic in a bit more detail with this Current Potential Implications Faced By Firm As Threats Corporate Security Management. Use it as a tool for discussion and navigation on Employees, Increase Security Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
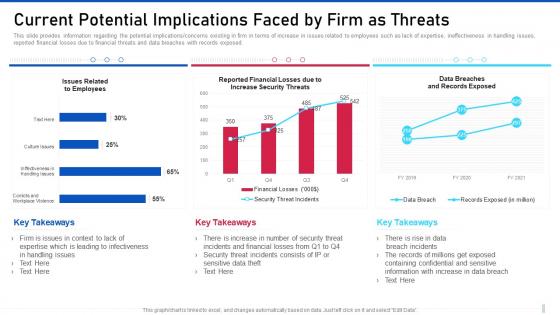 Threat management for organization critical current potential implications faced by firm as threats
Threat management for organization critical current potential implications faced by firm as threatsThis slide provides information regarding the potential implications or concerns existing in firm in terms of increase in issues related to employees such as lack of expertise, ineffectiveness in handling issues, reported financial losses due to financial threats and data breaches with records exposed. Deliver an outstanding presentation on the topic using this Threat Management For Organization Critical Current Potential Implications Faced By Firm As Threats. Dispense information and present a thorough explanation of Current Potential Implications Faced By Firm As Threats using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
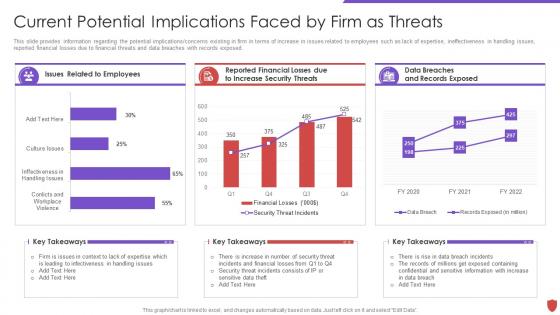 Cyber security risk management current potential implications faced by firm threats
Cyber security risk management current potential implications faced by firm threatsThis slide provides information regarding the potential implications or concerns existing in firm in terms of increase in issues related to employees such as lack of expertise, ineffectiveness in handling issues, reported financial losses due to financial threats and data breaches with records exposed. Present the topic in a bit more detail with this Cyber Security Risk Management Current Potential Implications Faced By Firm Threats. Use it as a tool for discussion and navigation on Issues Related, Employees, Data Breaches, Records Exposed, Reported Financial. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
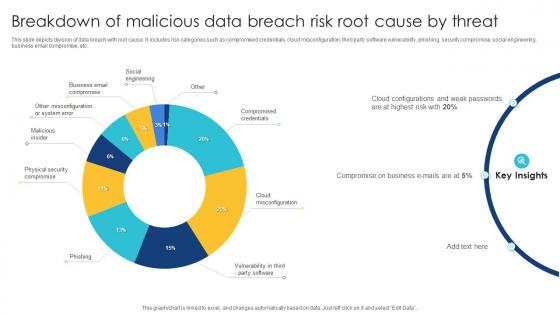 Breakdown Of Malicious Data Breach Risk Root Cause By Threat
Breakdown Of Malicious Data Breach Risk Root Cause By ThreatThis slide depicts division of data breach with root cause. It includes risk categories such as compromised credentials, cloud misconfiguration, third party software vulnerability, phishing, security compromise, social engineering, business email compromise, etc. Introducing our Breakdown Of Malicious Data Breach Risk Root Cause By Threat set of slides. The topics discussed in these slides are Social Engineering, Business Email Compromise, Malicious Insider. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Current Potential Implications Faced By Firm As Threats Managing IT Threats At Workplace Overview
Current Potential Implications Faced By Firm As Threats Managing IT Threats At Workplace OverviewThis slide provides information regarding the potential implications concerns existing in firm in terms of increase in issues related to employees such as lack of expertise, ineffectiveness in handling issues, reported financial losses due to financial threats and data breaches with records exposed. Deliver an outstanding presentation on the topic using this Current Potential Implications Faced By Firm As Threats Managing IT Threats At Workplace Overview. Dispense information and present a thorough explanation of Employees, Financial, Records using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
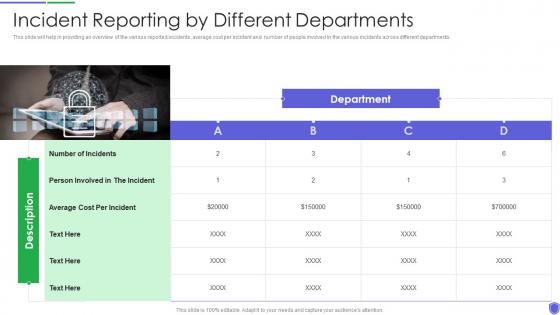 Incident reporting by different managing critical threat vulnerabilities and security threats
Incident reporting by different managing critical threat vulnerabilities and security threatsThis slide will help in providing an overview of the various reported incidents, average cost per incident and number of people involved in the various incidents across different departments. Increase audience engagement and knowledge by dispensing information using Incident Reporting By Different Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on one stages. You can also present information on Incident Reporting By Different Departments using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
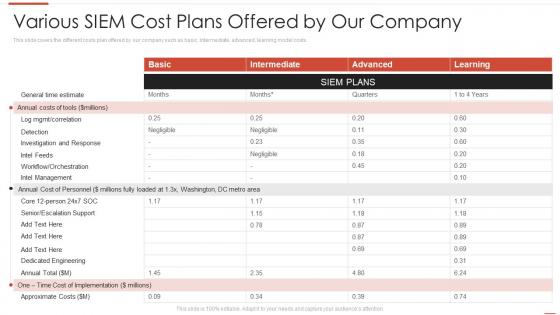 Automating threat identification various siem cost plans offered by our company
Automating threat identification various siem cost plans offered by our companyThis slide covers the different costs plan offered by our company such as basic, intermediate, advanced, learning model costs. Present the topic in a bit more detail with this Automating Threat Identification Various Siem Cost Plans Offered By Our Company. Use it as a tool for discussion and navigation on Various SIEM Cost Plans Offered By Our Company. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
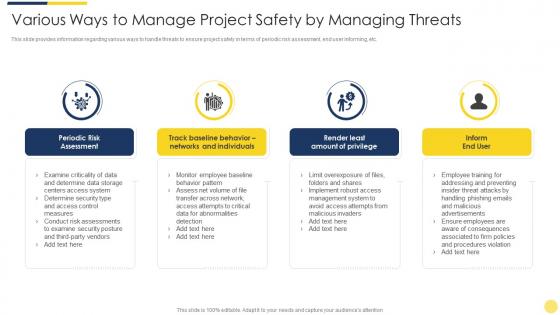 Various ways to manage project safety by managing threats key initiatives for project safety it
Various ways to manage project safety by managing threats key initiatives for project safety itThis slide provides information regarding various ways to handle threats to ensure project safety in terms of periodic risk assessment, end user informing, etc. Introducing Various Ways To Manage Project Safety By Managing Threats Key Initiatives For Project Safety It to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Determine, Security, Measures, Management, Advertisements, using this template. Grab it now to reap its full benefits.
-
 Various ways to manage project safety by managing threats project safety management it
Various ways to manage project safety by managing threats project safety management itThis slide provides information regarding various ways to handle threats to ensure project safety in terms of periodic risk assessment, end user informing, etc. Introducing Various Ways To Manage Project Safety By Managing Threats Project Safety Management It to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Advertisements, Emails, Network, Risk, Management, using this template. Grab it now to reap its full benefits.
-
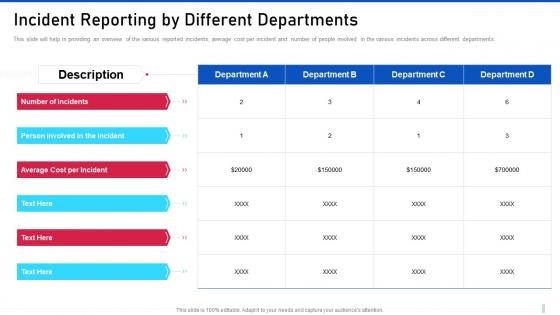 Threat management for organization critical incident reporting by different departments
Threat management for organization critical incident reporting by different departmentsThis slide will help in providing an overview of the various reported incidents, average cost per incident and number of people involved in the various incidents across different departments. Introducing Threat Management For Organization Critical Incident Reporting By Different Departments to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Average Cost Per Incident, Person Involved In The Incident, Description, using this template. Grab it now to reap its full benefits.
-
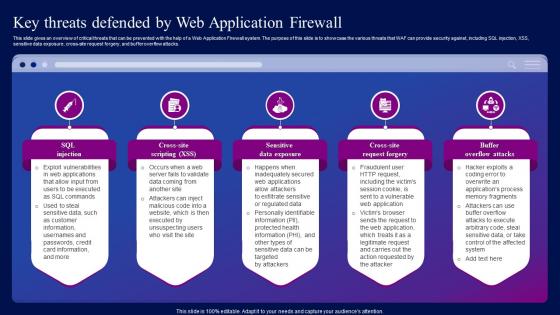 Key Threats Defended By Web Application Firewall Ppt Introduction
Key Threats Defended By Web Application Firewall Ppt IntroductionThis slide gives an overview of critical threats that can be prevented with the help of a Web Application Firewall system. The purpose of this slide is to showcase the various threats that WAF can provide security against, including SQL injection, XSS, sensitive data exposure, cross-site request forgery, and buffer overflow attacks. Introducing Key Threats Defended By Web Application Firewall Ppt Introduction to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Defended, Threats, Application, using this template. Grab it now to reap its full benefits.
-
 Cyber Security Threats Faced By Business Organizations
Cyber Security Threats Faced By Business OrganizationsThis slide covers various types of cyber security threats as faced by many organizations in their day to day working. The major cyber security risks are malware, phishing, denial of service attack, advanced persistent threats and ransomware Presenting our well structured Cyber Security Threats Faced By Business Organizations. The topics discussed in this slide are Malware, Phishing, Denial Of Service Attack. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Techniques Used By Cyber Security Threat Actors
Techniques Used By Cyber Security Threat ActorsFollowing template depicts various techniques as deployed by cyber security risk hijackers to steal or leak information that might be critical for organizations success. The major techniques are bots, code injection, password cracking and person in the middle Presenting our set of slides with Techniques Used By Cyber Security Threat Actors. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Bots, Code Injection, Password Cracking.
-
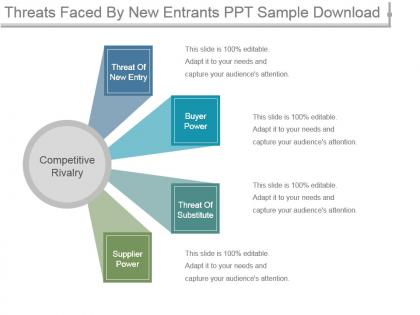 Threats faced by new entrants ppt sample download
Threats faced by new entrants ppt sample downloadPresenting threats faced by new entrants ppt sample download. This is a threats faced by new entrants ppt sample download. This is a four stage process. The stages in this process are threat of new entry, buyer power, threat of substitute, supplier power, competitive rivalry.
-
 Cyber threat analysis by computer forensics
Cyber threat analysis by computer forensicsPresenting our set of slides with name Cyber Threat Analysis By Computer Forensics. This exhibits information on one stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Cyber Threat, Analysis, Computer Forensics.
-
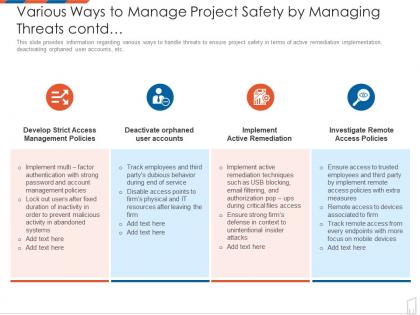 Various ways to manage project safety by managing threats contd management to improve project safety it
Various ways to manage project safety by managing threats contd management to improve project safety itThis slide provides information regarding various ways to handle threats to ensure project safety in terms of active remediation implementation, deactivating orphaned user accounts, etc. Increase audience engagement and knowledge by dispensing information using Various Ways To Manage Project Safety By Managing Threats Contd Management To Improve Project Safety IT. This template helps you present information on four stages. You can also present information on Develop Strict Access Management Policies, Deactivate Orphaned User Accounts, Implement Active Remediation, Investigate Remote Access Policies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
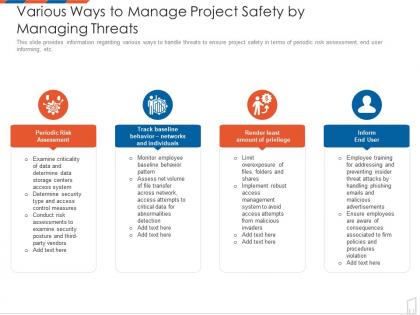 Various ways to manage project safety by managing threats management to improve project safety it
Various ways to manage project safety by managing threats management to improve project safety itThis slide provides information regarding various ways to handle threats to ensure project safety in terms of periodic risk assessment, end user informing, etc. Introducing Various Ways To Manage Project Safety By Managing Threats Management To Improve Project Safety IT to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Periodic Risk Assessment, Track Baseline Behavior Networks And Individuals, Render Least Amount Of Privilege, Inform End User, using this template. Grab it now to reap its full benefits.
-
 Enhanced security event management analysing various threats faced by firm ppt graphics
Enhanced security event management analysing various threats faced by firm ppt graphicsThis slide portrays information regarding the various threats that are faced by firm at present times with their cause of threat, risks associated to threats, occurrence of threats, and monetary loss to firm. Present the topic in a bit more detail with this Enhanced Security Event Management Analysing Various Threats Faced By Firm Ppt Graphics. Use it as a tool for discussion and navigation on Threats, Negligent, Occurrence, Compromised, Malicious. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
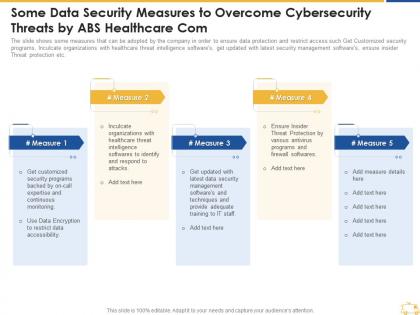 Some data security measures to overcome cybersecurity threats by abs healthcare com
Some data security measures to overcome cybersecurity threats by abs healthcare comThe slide shows some measures that can be adopted by the company in order to ensure data protection and restrict access such Get Customized security programs, Inculcate organizations with healthcare threat intelligence softwares, get updated with latest security management softwares, ensure insider Threat protection etc. Increase audience engagement and knowledge by dispensing information using Some Data Security Measures To Overcome Cybersecurity Threats By Abs Healthcare Com. This template helps you present information on four stages. You can also present information on Data, Softwares, Organizations, Management, Techniques using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
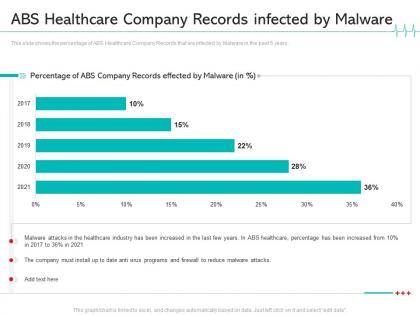 Abs healthcare company records infected by malware reduce cloud threats healthcare company
Abs healthcare company records infected by malware reduce cloud threats healthcare companyThis slide shows the percentage of ABS Healthcare Company Records that are infected by Malware in the past 5 years. Present the topic in a bit more detail with this Abs Healthcare Company Records Infected By Malware Reduce Cloud Threats Healthcare Company. Use it as a tool for discussion and navigation on Reduce, Industry. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 It security operations analysing various threats faced by firm ppt powerpoint pictures example
It security operations analysing various threats faced by firm ppt powerpoint pictures exampleThis slide portrays information regarding the various threats that are faced by firm at present times with their cause of threat, risks associated to threats, occurrence of threats, and monetary loss to firm. Present the topic in a bit more detail with this IT Security Operations Analysing Various Threats Faced By Firm Ppt Powerpoint Pictures Example. Use it as a tool for discussion and navigation on Threats, Negligent, Occurrence, Compromised, Malicious. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Analysing various threats faced by firm security operations integration ppt clipart
Analysing various threats faced by firm security operations integration ppt clipartPresent the topic in a bit more detail with this Analysing Various Threats Faced By Firm Security Operations Integration Ppt Clipart. Use it as a tool for discussion and navigation on Operations Disruption, Carelessness Or Ignorance, Intellectual Property. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Enterprise security operations analysing various threats faced by firm ppt powerpoint clipart
Enterprise security operations analysing various threats faced by firm ppt powerpoint clipartThis slide portrays information regarding the various threats that are faced by firm at present times with their cause of threat, risks associated to threats, occurrence of threats, and monetary loss to firm. Present the topic in a bit more detail with this Enterprise Security Operations Analysing Various Threats Faced By Firm Ppt Powerpoint Clipart. Use it as a tool for discussion and navigation on Threats, Negligent, Occurrence, Compromised, Malicious. This template is free to edit as deemed fit for your organization. Therefore download it now.

