Powerpoint Templates and Google slides for Use Protective Containers
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
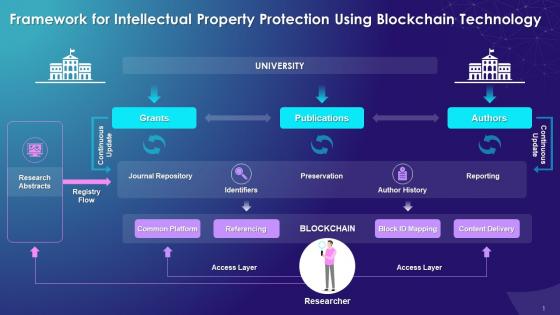 Framework For Intellectual Property Protection Using Blockchain Technology Training Ppt
Framework For Intellectual Property Protection Using Blockchain Technology Training PptPresenting Framework for Intellectual Property Protection Using Blockchain Technology. These slides are 100 percent made in PowerPoint and are compatible with all screen types and monitors. They also support Google Slides. Premium Customer Support is available. Suitable for use by managers, employees, and organizations. These slides are easily customizable. You can edit the color, text, icon, and font size to suit your requirements.
-
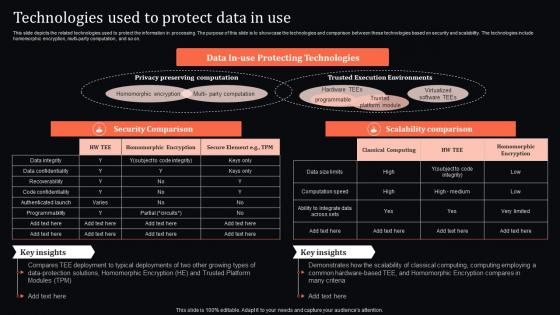 Technologies Used To Protect Data In Use Confidential Computing System Technology
Technologies Used To Protect Data In Use Confidential Computing System TechnologyThis slide depicts the related technologies used to protect the information in processing. The purpose of this slide is to showcase the technologies and comparison between these technologies based on security and scalability. The technologies include homomorphic encryption, multi-party computation, and so on. Deliver an outstanding presentation on the topic using this Technologies Used To Protect Data In Use Confidential Computing System Technology. Dispense information and present a thorough explanation of Technologies, Security Comparison, Scalability Comparison using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
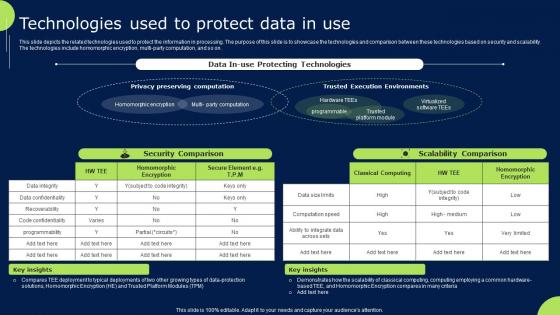
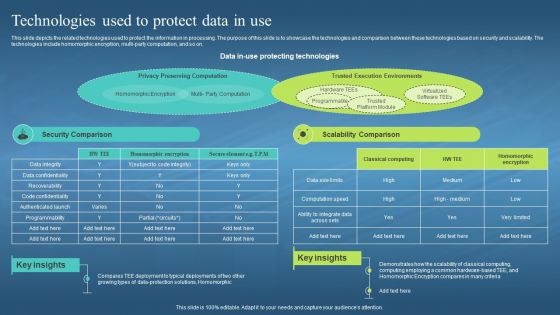 Confidential Computing Hardware Technologies Used To Protect Data In Use
Confidential Computing Hardware Technologies Used To Protect Data In UseThis slide depicts the related technologies used to protect the information in processing. The purpose of this slide is to showcase the technologies and comparison between these technologies based on security and scalability. The technologies include homomorphic encryption, multi-party computation, and so on. Present the topic in a bit more detail with this Confidential Computing Hardware Technologies Used To Protect Data In Use. Use it as a tool for discussion and navigation on Protect The Information In Processing, Security And Scalability, Homomorphic Encryption, Multi Party Computation. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
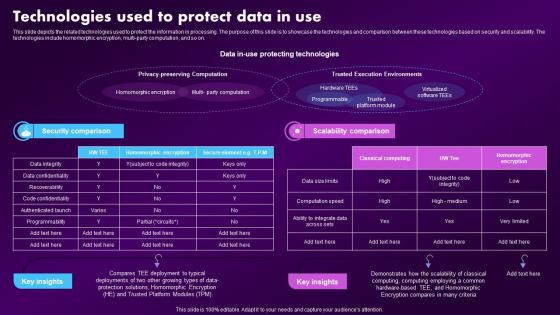 Confidential Computing Market Technologies Used To Protect Data In Use
Confidential Computing Market Technologies Used To Protect Data In UseThis slide depicts the related technologies used to protect the information in processing. The purpose of this slide is to showcase the technologies and comparison between these technologies based on security and scalability. The technologies include homomorphic encryption, multi-party computation, and so on. Present the topic in a bit more detail with this Confidential Computing Market Technologies Used To Protect Data In Use. Use it as a tool for discussion and navigation on Technologies, Demonstrates, Deployment. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
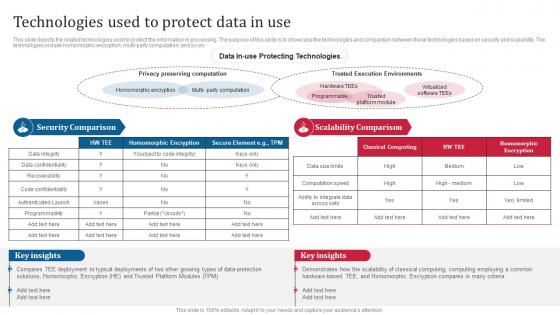 Confidential Computing Consortium Technologies Used To Protect Data In Use
Confidential Computing Consortium Technologies Used To Protect Data In UseThis slide depicts the related technologies used to protect the information in processing. The purpose of this slide is to showcase the technologies and comparison between these technologies based on security and scalability. The technologies include homomorphic encryption, multi-party computation, and so on. Deliver an outstanding presentation on the topic using this Confidential Computing Consortium Technologies Used To Protect Data In Use. Dispense information and present a thorough explanation of Protecting Technologies, Security And Scalability, Technologies Homomorphic Encryption, Multi Party Computation using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
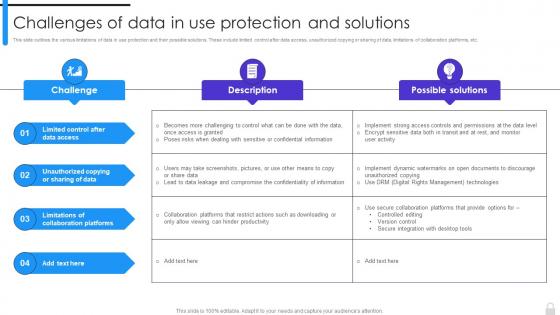 Encryption Implementation Strategies Challenges Of Data In Use Protection And Solutions
Encryption Implementation Strategies Challenges Of Data In Use Protection And SolutionsThis slide outlines the various limitations of data in use protection and their possible solutions. These include limited control after data access, unauthorized copying or sharing of data, limitations of collaboration platforms, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Challenges Of Data In Use Protection And Solutions. Use it as a tool for discussion and navigation on Limitations Of Collaboration Platforms, Unauthorized Copying Or Sharing Of Data, Limited Control After Data Access. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
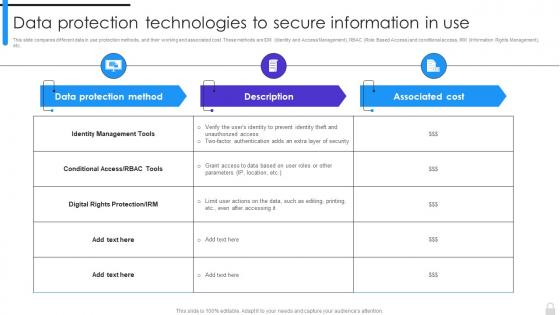 Encryption Implementation Strategies Data Protection Technologies To Secure Information In Use
Encryption Implementation Strategies Data Protection Technologies To Secure Information In UseThis slide compares different data in use protection methods, and their working and associated cost. These methods are IDM Identity and Access Management, RBAC Role Based Access and conditional access, IRM Information Rights Management, etc. Present the topic in a bit more detail with this Encryption Implementation Strategies Data Protection Technologies To Secure Information In Use. Use it as a tool for discussion and navigation on Identity Management Tools, Digital Rights Protection, Data Protection Technologies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
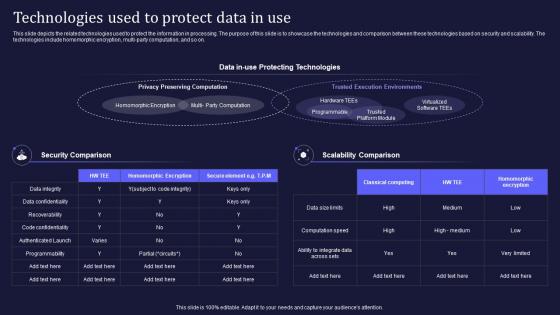 Confidential Computing V2 Technologies Used To Protect Data In Use
Confidential Computing V2 Technologies Used To Protect Data In UseThis slide depicts the related technologies used to protect the information in processing. The purpose of this slide is to showcase the technologies and comparison between these technologies based on security and scalability. The technologies include homomorphic encryption, multi-party computation, and so on. Present the topic in a bit more detail with this Confidential Computing V2 Technologies Used To Protect Data In Use. Use it as a tool for discussion and navigation on Homomorphic Encryption, Trusted Execution Environments, Privacy Preserving Computation, Protecting Technologies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
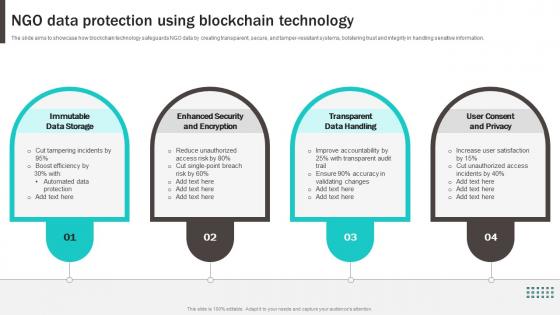 NGO Data Protection Using Blockchain Technology
NGO Data Protection Using Blockchain TechnologyThe slide aims to showcase how blockchain technology safeguards NGO data by creating transparent, secure, and tamper-resistant systems, bolstering trust and integrity in handling sensitive information. Presenting our set of slides with NGO Data Protection Using Blockchain Technology. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Immutable Data Storage, Enhanced Security And Encryption, Transparent Data Handling, User Consent And Privacy.
-
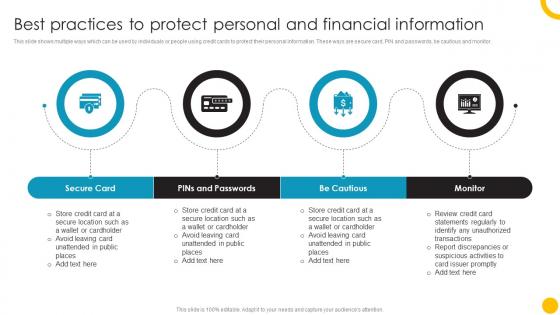 Best Practices To Protect Personal Guide To Use And Manage Credit Cards Effectively Fin SS
Best Practices To Protect Personal Guide To Use And Manage Credit Cards Effectively Fin SSThis slide shows multiple ways which can be used by individuals or people using credit cards to protect their personal information. These ways are secure card, PIN and passwords, be cautious and monitor. Introducing Best Practices To Protect Personal Guide To Use And Manage Credit Cards Effectively Fin SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Secure Card, Passwords, Monitor, using this template. Grab it now to reap its full benefits.
-
 Use Cases Of Blockchain Privacy Protection In Comprehensive Approach To Privacy BCT SS
Use Cases Of Blockchain Privacy Protection In Comprehensive Approach To Privacy BCT SSThis slide covers various sectors where blockchain is helping to increase privacy such as financial transactions, healthcare records, legal services, shipping and logistics,etc. Introducing Use Cases Of Blockchain Privacy Protection In Comprehensive Approach To Privacy BCT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Financial Transactions, Healthcare Records, Legal Services, Shipping And Logistics, using this template. Grab it now to reap its full benefits.
-
 Mitigate Credential Risk Protection Icon Using Multi Factor Authentication
Mitigate Credential Risk Protection Icon Using Multi Factor AuthenticationIntroducing our premium set of slides with Mitigate Credential Risk Protection Icon Using Multi Factor Authentication. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Protection, Authentication, Credential. So download instantly and tailor it with your information.
-
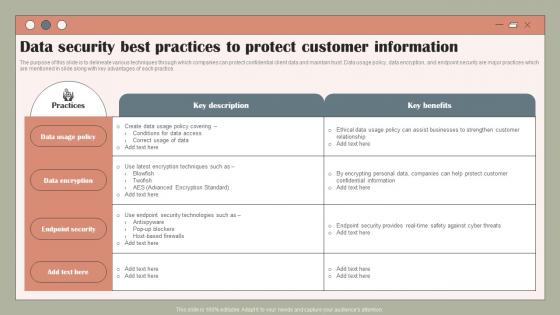 Data Security Best Practices To Protect Using Customer Data To Improve MKT SS V
Data Security Best Practices To Protect Using Customer Data To Improve MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Deliver an outstanding presentation on the topic using this Data Security Best Practices To Protect Using Customer Data To Improve MKT SS V. Dispense information and present a thorough explanation of Policy, Data, Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
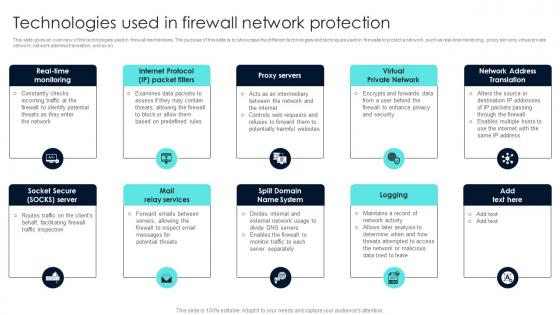 Firewall Network Security Technologies Used In Firewall Network Protection
Firewall Network Security Technologies Used In Firewall Network ProtectionThis slide gives an overview of the technologies used in firewall mechanisms. The purpose of this slide is to showcase the different technologies and techniques used in firewalls to protect a network, such as real-time monitoring, proxy servers, virtual private network, network address translation, and so on. Introducing Firewall Network Security Technologies Used In Firewall Network Protection to increase your presentation threshold. Encompassed with Eight stages, this template is a great option to educate and entice your audience. Dispence information on Packet Filters, Proxy Servers, Virtual Private Network using this template. Grab it now to reap its full benefits.
-
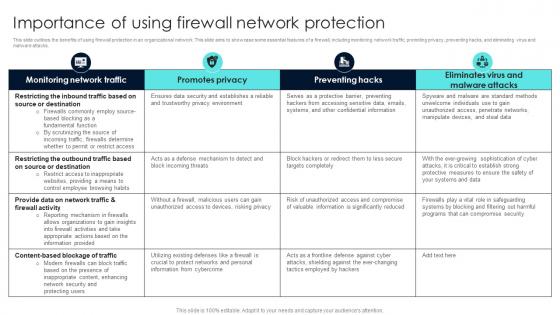 Firewall Network Security Importance Of Using Firewall Network Protection
Firewall Network Security Importance Of Using Firewall Network ProtectionThis slide outlines the benefits of using firewall protection in an organizational network. This slide aims to showcase some essential features of a firewall, including monitoring network traffic, promoting privacy, preventing hacks, and eliminating virus and malware attacks. Deliver an outstanding presentation on the topic using this Firewall Network Security Importance Of Using Firewall Network Protection Dispense information and present a thorough explanation of Enhance Security, IP Addresses, Malicious Content using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
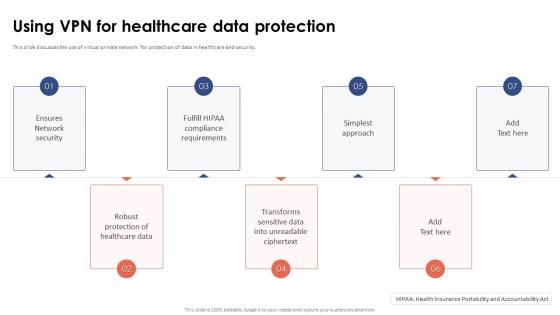 Virtual Private Network VPN Using VPN For Healthcare Data Protection
Virtual Private Network VPN Using VPN For Healthcare Data ProtectionThis slide discusses the use of virtual private network for protection of data in healthcare and security. Increase audience engagement and knowledge by dispensing information using Virtual Private Network VPN Using VPN For Healthcare Data Protection. This template helps you present information on seven stages. You can also present information on Transforms Sensitive Data, Unreadable Ciphertext, Robust Protection, Healthcare Data using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
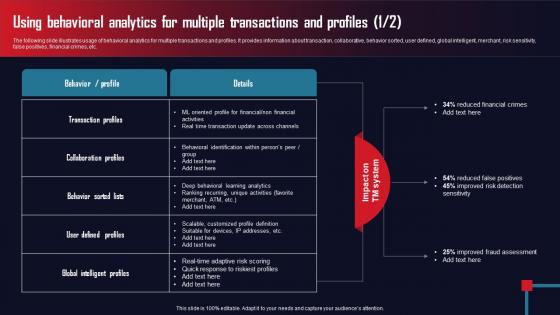 Using Behavioral Analytics For Multiple AML Transaction Assessment Tool For Protecting
Using Behavioral Analytics For Multiple AML Transaction Assessment Tool For ProtectingThe following slide illustrates usage of behavioral analytics for multiple transactions and profiles. It provides information about transaction, collaborative, behavior sorted, user defined, global intelligent, merchant, risk sensitivity, false positives, financial crimes, etc.Present the topic in a bit more detail with this Using Behavioral Analytics For Multiple AML Transaction Assessment Tool For Protecting. Use it as a tool for discussion and navigation on Collaboration Profiles, Reduced Financial, Global Intelligent Profiles. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
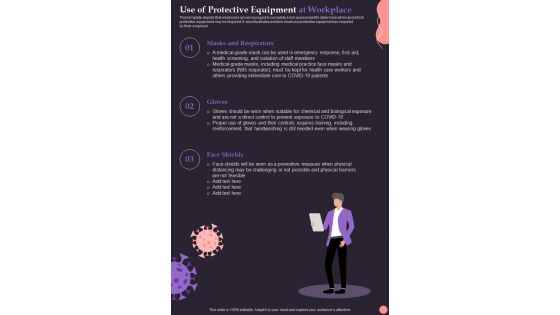
 Use Of Protective Equipment At Workplace Post Pandemic Business Playbook
Use Of Protective Equipment At Workplace Post Pandemic Business PlaybookThis template depicts that employers are encouraged to complete a risk assessment to determine when and which protective equipment may be required. It also illustrates workers must use protective equipment as required by their employer. Introducing Use Of Protective Equipment At Workplace Post Pandemic Business Playbook to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Masks And Respirators, Gloves, Face Shields, using this template. Grab it now to reap its full benefits.
-
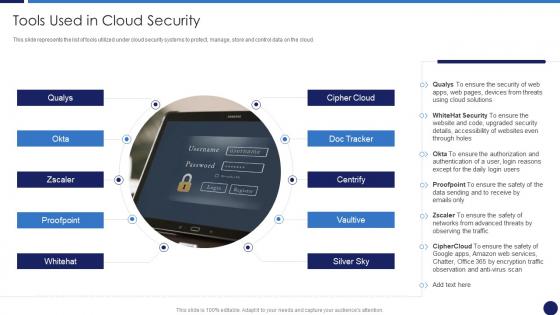 Cloud Data Protection Tools Used In Cloud Security
Cloud Data Protection Tools Used In Cloud SecurityThis slide represents the list of tools utilized under cloud security systems to protect, manage, store and control data on the cloud. Increase audience engagement and knowledge by dispensing information using Cloud Data Protection Tools Used In Cloud Security. This template helps you present information on one stage. You can also present information on Cloud Solutions, Security, Networks using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
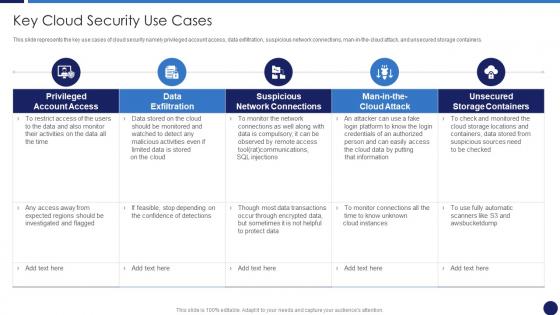 Key Cloud Security Use Cases Cloud Data Protection
Key Cloud Security Use Cases Cloud Data ProtectionThis slide represents the key use cases of cloud security namely privileged account access, data exfiltration, suspicious network connections, man-in-the-cloud attack, and unsecured storage containers. Present the topic in a bit more detail with this Key Cloud Security Use Cases Cloud Data Protection. Use it as a tool for discussion and navigation on Suspicious Network Connections, Data Exfiltration, Unsecured Storage Containers. This template is free to edit as deemed fit for your organization. Therefore download it now
-
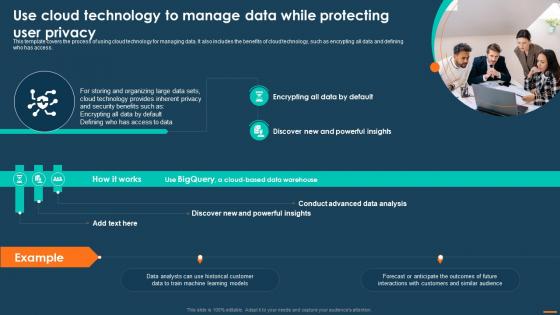 Digital Marketing Playbook For Driving Use Cloud Technology To Manage Data While Protecting
Digital Marketing Playbook For Driving Use Cloud Technology To Manage Data While ProtectingThis template covers the process of using cloud technology for managing data. It also includes the benefits of cloud technology, such as encrypting all data and defining who has access. Increase audience engagement and knowledge by dispensing information using Digital Marketing Playbook For Driving Use Cloud Technology To Manage Data While Protecting. This template helps you present information on one stages. You can also present information on Cloud Technology, Protecting User Privacy, Data Warehouse using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Post COVID Business Recovery Playbook Use Of Protective Equipment At Workplace
Post COVID Business Recovery Playbook Use Of Protective Equipment At WorkplaceThis template depicts that employers are encouraged to complete a risk assessment to determine when and which protective equipment may be required. It also illustrates workers must use protective equipment as required by their employer. Introducing Post COVID Business Recovery Playbook Use Of Protective Equipment At Workplace to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Masks And Respirators, Gloves, Face Shields, using this template. Grab it now to reap its full benefits.
-
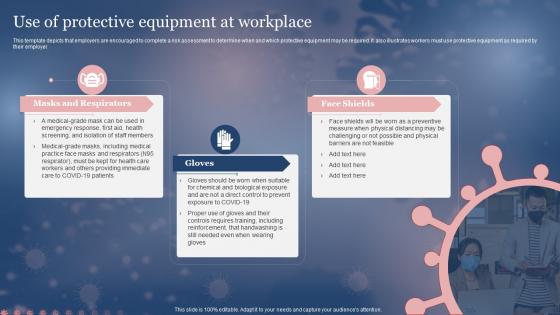 Use Of Protective Equipment At Workplace Framework For Post Pandemic Business Planning
Use Of Protective Equipment At Workplace Framework For Post Pandemic Business PlanningThis template depicts that employers are encouraged to complete a risk assessment to determine when and which protective equipment may be required. It also illustrates workers must use protective equipment as required by their employer. Increase audience engagement and knowledge by dispensing information using Use Of Protective Equipment At Workplace Framework For Post Pandemic Business Planning. This template helps you present information on three stages. You can also present information on Protective, Equipment, Workplace using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Use Of Protective Equipment At Workplace Pandemic Business Strategy Playbook
Use Of Protective Equipment At Workplace Pandemic Business Strategy PlaybookThis template depicts that employers are encouraged to complete a risk assessment to determine when and which protective equipment may be required. It also illustrates workers must use protective equipment as required by their employer. Introducing Use Of Protective Equipment At Workplace Pandemic Business Strategy Playbook to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Masks And Respirators, Gloves, Face Shields, using this template. Grab it now to reap its full benefits.
-
 Use Of Protective Equipment At Workplace Pandemic Business Playbook
Use Of Protective Equipment At Workplace Pandemic Business PlaybookThis template depicts that employers are encouraged to complete a risk assessment to determine when and which protective equipment may be required. It also illustrates workers must use protective equipment as required by their employer Present the topic in a bit more detail with this Use Of Protective Equipment At Workplace Pandemic Business Playbook. Use it as a tool for discussion and navigation on Protective, Equipment, Workplace. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Use Of Protective Equipment At Workplace New Normal Adaption Playbook
Use Of Protective Equipment At Workplace New Normal Adaption PlaybookThis template depicts that employers are encouraged to complete a risk assessment to determine when and which protective equipment may be required. It also illustrates workers must use protective equipment as required by their employer. Introducing Use Of Protective Equipment At Workplace New Normal Adaption Playbook to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Masks And Respirators, Gloves, Face Shields, using this template. Grab it now to reap its full benefits.
-
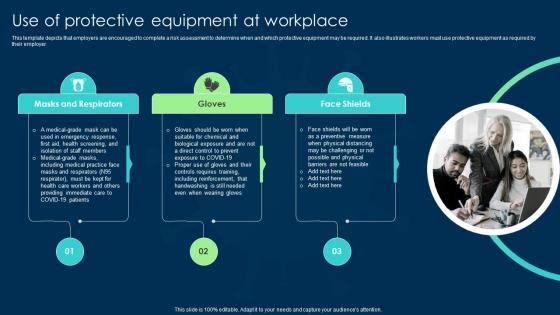 Use Of Protective Equipment At Workplace Business Transformation Guidelines
Use Of Protective Equipment At Workplace Business Transformation GuidelinesIntroducing Use Of Protective Equipment At Workplace Business Transformation Guidelines to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Including Reinforcement, Controls Requires, Handwashing Still, using this template. Grab it now to reap its full benefits.
-
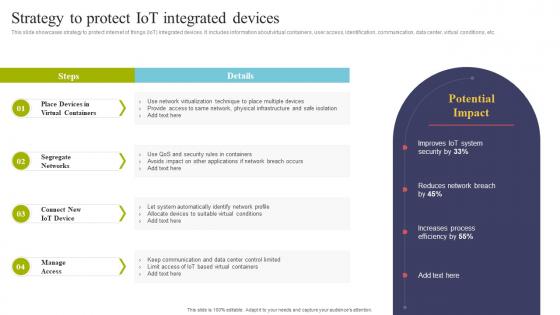 Strategy To Protect IOT Integrated Devices Using IOT Technologies For Better Logistics
Strategy To Protect IOT Integrated Devices Using IOT Technologies For Better LogisticsThis slide showcases strategy to protect internet of things IoT integrated devices. It includes information about virtual containers, user access, identification, communication, data center, virtual conditions, etc. Deliver an outstanding presentation on the topic using this Strategy To Protect IOT Integrated Devices Using IOT Technologies For Better Logistics. Dispense information and present a thorough explanation of Virtualization Technique, System Automatically, Keep Communication using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
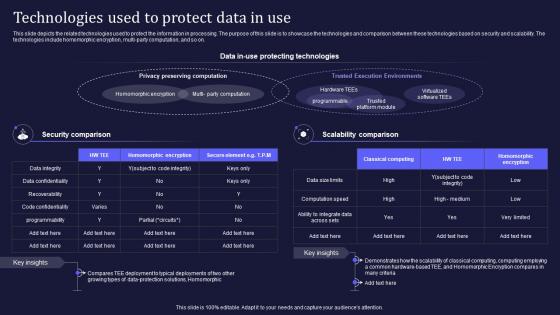 Confidential Computing It Technologies Used To Protect Data In Use Ppt Slides Styles
Confidential Computing It Technologies Used To Protect Data In Use Ppt Slides StylesThis slide depicts the related technologies used to protect the information in processing. The purpose of this slide is to showcase the technologies and comparison between these technologies based on security and scalability. The technologies include homomorphic encryption, multi party computation, and so on. Introducing Confidential Computing It Technologies Used To Protect Data In Use Ppt Slides Styles to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Privacy Preserving Computation, Security Comparison, Scalability Comparison, using this template. Grab it now to reap its full benefits.
-
 Technologies Used To Protect Data In Use Confidential Cloud Computing
Technologies Used To Protect Data In Use Confidential Cloud ComputingThis slide depicts the related technologies used to protect the information in processing. The purpose of this slide is to showcase the technologies and comparison between these technologies based on security and scalability. The technologies include homomorphic encryption, multi-party computation, and so on. Deliver an outstanding presentation on the topic using this Technologies Used To Protect Data In Use Confidential Cloud Computing. Dispense information and present a thorough explanation of Technologies, Homomorphic, Information using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Federal bank regulation in us consumer protection powerpoint presentation portfolio
Federal bank regulation in us consumer protection powerpoint presentation portfolioPresenting this set of slides with name Federal Bank Regulation In Us Consumer Protection Powerpoint Presentation Portfolio. This is a six stage process. The stages in this process are Consumer Protection,Debt Collection,Lending Limits,Business,Management. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 0814 wrench screwdriver hammer with handsaw and protection hat for site use image graphics for powerpoint
0814 wrench screwdriver hammer with handsaw and protection hat for site use image graphics for powerpointWe are proud to present our 0814 wrench screwdriver hammer with handsaw and protection hat for site use image graphics for powerpoint. Create dynamic presentations with this professional image displaying hammer, wrench and screwdriver. This image may be used to explain importance of tools for industrial project. Add this image in your presentations to visually support your content and express your thoughts.
-
 Protect us dollar security powerpoint templates and powerpoint backgrounds 0711
Protect us dollar security powerpoint templates and powerpoint backgrounds 0711Microsoft PowerPoint Template and Background with protect your investment united states of america dollars growth
-
 Computer security using shield safe protection
Computer security using shield safe protectionPresenting this set of slides with name Computer Security Using Shield Safe Protection. This is a four stage process. The stages in this process are Computer Security Using Shield Safe Protection. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Why us for organization cyber protection services ppt powerpoint presentation gridlines
Why us for organization cyber protection services ppt powerpoint presentation gridlinesPresenting this set of slides with name Why Us For Organization Cyber Protection Services Ppt Powerpoint Presentation Gridlines. This is a two stage process. The stages in this process are Innovative, Cyber Security, Services, Development, Extensive. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Tourists using protective leg covers in flooded area
Tourists using protective leg covers in flooded areaPresenting this set of slides with name Tourists Using Protective Leg Covers In Flooded Area. The topics discussed in these slide is Tourists Using Protective Leg Covers In Flooded Area. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Person using mobile device having security protection
Person using mobile device having security protectionIntroducing our premium set of slides with Person Using Mobile Device Having Security Protection. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Person Using Mobile Device Having Security Protection. So download instantly and tailor it with your information.
-
 Employee protecting data by using firewall network security device
Employee protecting data by using firewall network security devicePresenting our set of slides with Employee Protecting Data By Using Firewall Network Security Device. This exhibits information on one stage of the process. This is an easy-to-edit and innovatively designed PowerPoint template. So download immediately and highlight information on Employee Protecting Data By Using Firewall Network Security Device.
-
 Personal protective equipment used by workers at construction site
Personal protective equipment used by workers at construction siteIntroducing our Personal Protective Equipment Used By Workers At Construction Site set of slides. The topics discussed in these slides are Personal Protective Equipment Used By Workers At Construction Site. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Post Pandemic Use Of Protective Equipment At Workplace One Pager Sample Example Document
Post Pandemic Use Of Protective Equipment At Workplace One Pager Sample Example DocumentThis is a One Pager designed in Powerpoint titled Post Pandemic Use Of Protective Equipment At Workplace One Pager Sample Example Document. It is crafted using high-quality visuals that can be readjusted in PowerPoint and Google Slides. This template comes in an editable format and is available in A4 size format for immediate download.

