Powerpoint Templates and Google slides for User Risk
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Conducting Blockchain Cybersecurity Training For Users Hands On Blockchain Security Risk BCT SS V
Conducting Blockchain Cybersecurity Training For Users Hands On Blockchain Security Risk BCT SS VThe following slide showcases blockchain cybersecurity training plan to reduce insider threats. It includes elements such as introduction ,blockchain security risks, smart contracts development, network security, data encryption, incidence response management, etc. Deliver an outstanding presentation on the topic using this Conducting Blockchain Cybersecurity Training For Users Hands On Blockchain Security Risk BCT SS V. Dispense information and present a thorough explanation of Trainer Name, Mode, Proposed Date using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
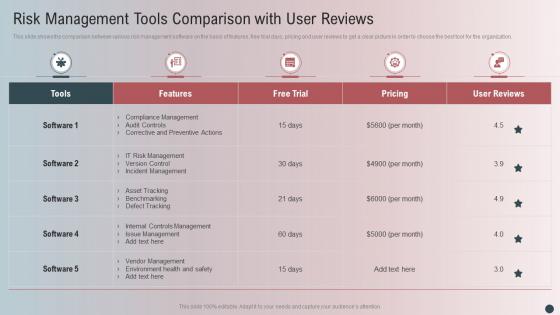 Risk Management Tools Comparison With User Reviews
Risk Management Tools Comparison With User ReviewsThis slide shows the comparison between various risk management software on the basis of features, free trial days, pricing and user reviews to get a clear picture in order to choose the best tool for the organization. Introducing our Risk Management Tools Comparison With User Reviews set of slides. The topics discussed in these slides are Risk Management Tools, Comparison, User Reviews. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 User Wallet Attack Risk Colored Icon In Powerpoint Pptx Png And Editable Eps Format
User Wallet Attack Risk Colored Icon In Powerpoint Pptx Png And Editable Eps FormatGive your next presentation a sophisticated, yet modern look with this 100 percent editable User wallet attack risk colored icon in powerpoint pptx png and editable eps format. Choose from a variety of customizable formats such as PPTx, png, eps. You can use these icons for your presentations, banners, templates, One-pagers that suit your business needs.
-
 User Wallet Attack Risk Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
User Wallet Attack Risk Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatMake your presentation profoundly eye-catching leveraging our easily customizable User wallet attack risk monotone icon in powerpoint pptx png and editable eps format. It is designed to draw the attention of your audience. Available in all editable formats, including PPTx, png, and eps, you can tweak it to deliver your message with ease.
-
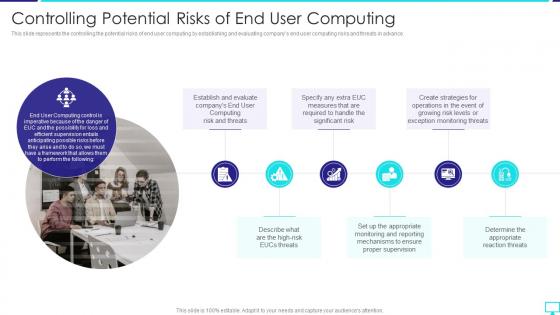 Controlling Potential Risks Of End User Computing Desktop Virtualization
Controlling Potential Risks Of End User Computing Desktop VirtualizationThis slide represents the controlling the potential risks of end user computing by establishing and evaluating companys end user computing risks and threats in advance.Increase audience engagement and knowledge by dispensing information using Controlling Potential Risks Of End User Computing Desktop Virtualization. This template helps you present information on six stages. You can also present information on Establish And Evaluate, Required To Handle, Exception Monitoring using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
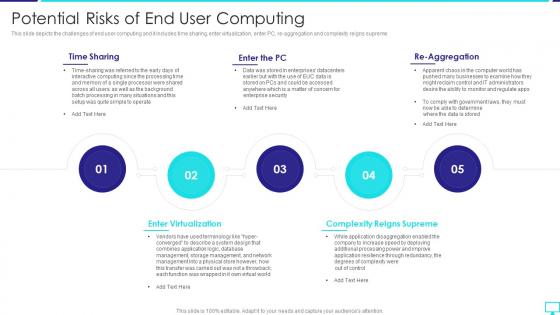 Potential Risks Of End User Computing Desktop Virtualization
Potential Risks Of End User Computing Desktop VirtualizationThis slide depicts the challenges of end user computing and it includes time sharing, enter virtualization, enter PC, re aggregation and complexity reigns supreme.Introducing Potential Risks Of End User Computing Desktop Virtualization to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Time Sharing, Enter Virtualization, Complexity Reigns, using this template. Grab it now to reap its full benefits.
-
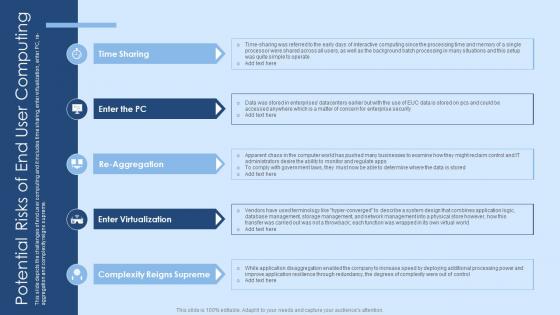 Potential Risks Of End User Computing Virtual Desktop Infrastructure Ppt Professional Graphics Tutorials
Potential Risks Of End User Computing Virtual Desktop Infrastructure Ppt Professional Graphics TutorialsThis slide depicts the challenges of end user computing and it includes time sharing, enter virtualization, enter PC, re-aggregation and complexity reigns supreme Increase audience engagement and knowledge by dispensing information using Potential Risks Of End User Computing Virtual Desktop Infrastructure Ppt Professional Graphics Tutorials. This template helps you present information on five stages. You can also present information on Potential Risks, Enter Virtualization, Complexity Reigns Supreme using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
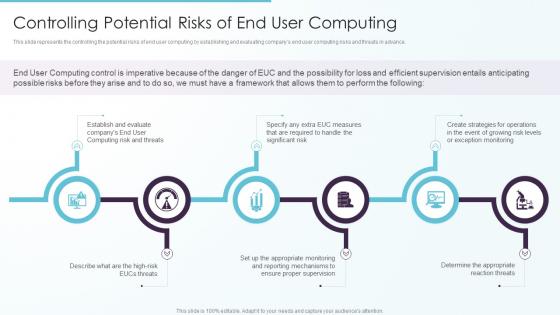 Controlling Potential Risks Of End User Computing Ppt Outline Gallery
Controlling Potential Risks Of End User Computing Ppt Outline GalleryThis slide represents the controlling the potential risks of end user computing by establishing and evaluating companys end user computing risks and threats in advance. Introducing Controlling Potential Risks Of End User Computing Ppt Outline Gallery to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Computing Risk, Required, Significant Risk, using this template. Grab it now to reap its full benefits.
-
 Potential Risks Of End User Computing Ppt Infographics Format Ideas
Potential Risks Of End User Computing Ppt Infographics Format IdeasThis slide depicts the challenges of end user computing and it includes time sharing, enter virtualization, enter PC, re aggregation and complexity reigns supreme. Increase audience engagement and knowledge by dispensing information using Potential Risks Of End User Computing Ppt Infographics Format Ideas. This template helps you present information on five stages. You can also present information on Enter Virtualization, Complexity Reigns Supreme, Time Sharing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
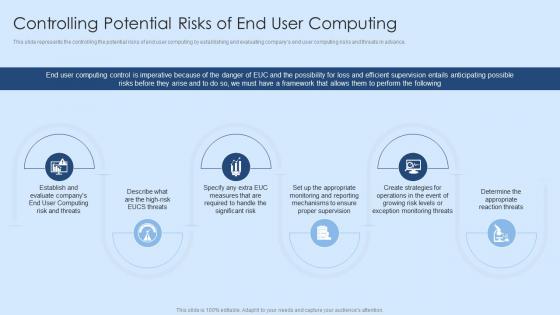 Controlling Potential Risks Of End User Computing Virtual Desktop Infrastructure Ppt Professional
Controlling Potential Risks Of End User Computing Virtual Desktop Infrastructure Ppt ProfessionalThis slide represents the controlling the potential risks of end user computing by establishing and evaluating companys end user computing risks and threats in advance. Increase audience engagement and knowledge by dispensing information using Controlling Potential Risks Of End User Computing Virtual Desktop Infrastructure Ppt Professional. This template helps you present information on five stages. You can also present information on Controlling, Potential, Establishing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
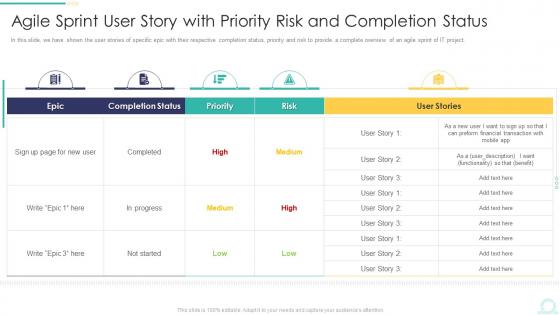 Agile Sprint User Story With Priority Risk And Completion Status Ppt Graphics Example
Agile Sprint User Story With Priority Risk And Completion Status Ppt Graphics ExampleIn this slide, we have shown the user stories of specific epic with their respective completion status, priority and risk to provide a complete overview of an agile sprint of IT project. Present the topic in a bit more detail with this Agile Sprint User Story With Priority Risk And Completion Status Ppt Graphics Example. Use it as a tool for discussion and navigation on Agile Sprint User Story With Priority Risk And Completion Status. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
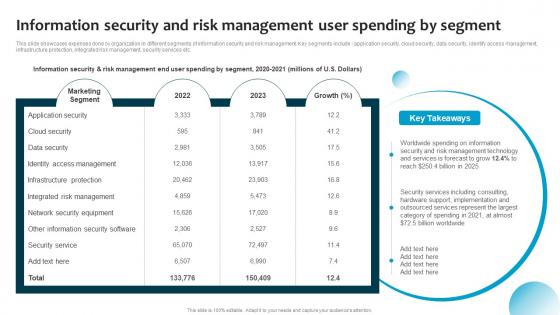 Information Security And Risk Management User Spending By Segment Information System Security And Risk
Information Security And Risk Management User Spending By Segment Information System Security And RiskThis slide showcases expenses done by organization in different segments of information security and risk management. Key segments include application security, cloud security, data security, identify access management, infrastructure protection, integrated risk management, security services etc. Present the topic in a bit more detail with this Information Security And Risk Management User Spending By Segment Information System Security And Risk. Use it as a tool for discussion and navigation on Marketing Segment, Network Security Equipment, Integrated Risk Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 F856 Information Security And Risk Management User Cybersecurity Risk Analysis And Management Plan
F856 Information Security And Risk Management User Cybersecurity Risk Analysis And Management PlanThis slide showcases expenses done by organization in different segments of information security and risk management. Key segments include - application security, cloud security, data security, identify access management, infrastructure protection, integrated risk management, security services etc Deliver an outstanding presentation on the topic using this F856 Information Security And Risk Management User Cybersecurity Risk Analysis And Management Plan. Dispense information and present a thorough explanation of Information, Management, Application using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
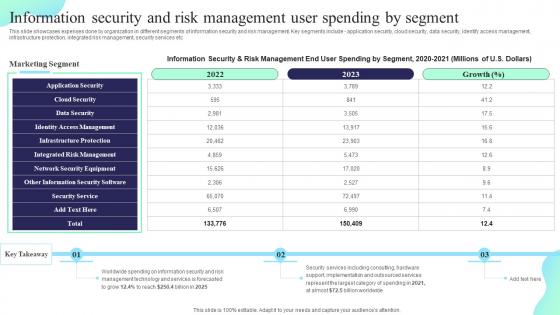 Information Security And Risk Management User Spending Formulating Cybersecurity Plan
Information Security And Risk Management User Spending Formulating Cybersecurity PlanThis slide showcases expenses done by organization in different segments of information security and risk management. Key segments include application security, cloud security, data security, identify access management, infrastructure protection, integrated risk management, security services etc. Deliver an outstanding presentation on the topic using this Information Security And Risk Management User Spending Formulating Cybersecurity Plan. Dispense information and present a thorough explanation of Application Security, Identity Access Management, Integrated Risk Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Controlling Potential Risks Of End User Computing EUC Ppt File Information
Controlling Potential Risks Of End User Computing EUC Ppt File InformationThis slide represents the controlling the potential risks of end user computing by establishing and evaluating companys end user computing risks and threats in advance. Introducing Controlling Potential Risks Of End User Computing EUC Ppt File Information to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispense information on Controlling Potential Risks, End User Computing, using this template. Grab it now to reap its full benefits.
-
 Potential Risks Of End User Computing EUC Ppt Powerpoint Presentation File Styles
Potential Risks Of End User Computing EUC Ppt Powerpoint Presentation File StylesThis slide depicts the challenges of end user computing and it includes time sharing, enter virtualization, enter PC, re aggregation and complexity reigns supreme. Increase audience engagement and knowledge by dispensing information using Potential Risks Of End User Computing EUC Ppt Powerpoint Presentation File Styles. This template helps you present information on five stages. You can also present information on Time Sharing, Enter Virtualization, Enter The PC, Re Aggregation using this PPT design. This layout is completely editable so personalize it now to meet your audiences expectations
-
 Information Security And Risk Management User Information Security Risk Management
Information Security And Risk Management User Information Security Risk ManagementThis slide showcases expenses done by organization in different segments of information security and risk management. Key segments include - application security, cloud security, data security, identify access management, infrastructure protection, integrated risk management, security services etc. Introducing Information Security And Risk Management User Information Security Risk Management to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispense information on Marketing Segment, Identity Access Management, Information Security, using this template. Grab it now to reap its full benefits.
-
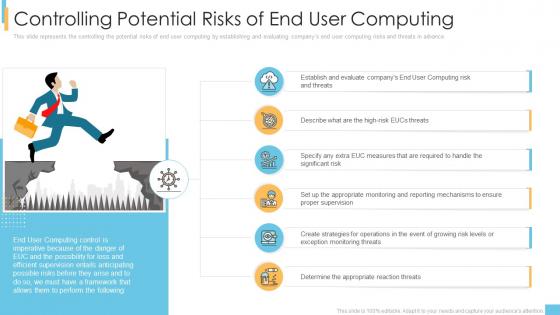 End user computing it controlling potential risks of end user computing ppt deck
End user computing it controlling potential risks of end user computing ppt deckThis slide represents the controlling the potential risks of end user computing by establishing and evaluating companys end user computing risks and threats in advance. Introducing End User Computing IT Controlling Potential Risks Of End User Computing Ppt Deck to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Evaluate, Measures, Monitoring, Exception, using this template. Grab it now to reap its full benefits.
-
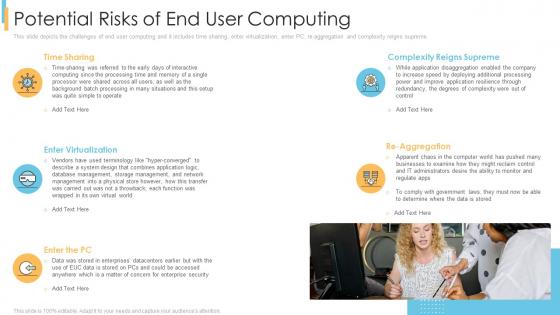 End user computing it potential risks of end user computing ppt powerpoint example
End user computing it potential risks of end user computing ppt powerpoint exampleThis slide depicts the challenges of end user computing and it includes time sharing, enter virtualization, enter PC, re aggregation and complexity reigns supreme. Introducing End User Computing IT Potential Risks Of End User Computing Ppt Powerpoint Example to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Time Sharing, Enter Virtualization, Enter The Pc, Complexity Reigns Supreme, Re Aggregation, using this template. Grab it now to reap its full benefits.
-
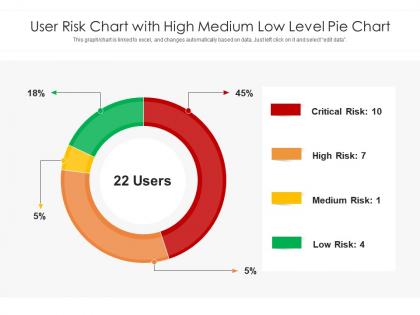 User risk chart with high medium low level pie chart
User risk chart with high medium low level pie chartIntroducing our User Risk Chart With High Medium Low Level Pie Chart set of slides. The topics discussed in these slides are User Risk Chart With High Medium Low Level Pie Chart. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
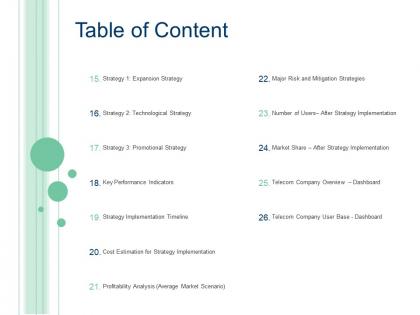 Table of content risk case competition declining user base telecom company ppt show
Table of content risk case competition declining user base telecom company ppt showDeliver an outstanding presentation on the topic using this Table Of Content Risk Case Competition Declining User Base Telecom Company Ppt Show. Dispense information and present a thorough explanation of Technological Strategy, Promotional Strategy, Key Performance Indicators, Strategy Implementation Timeline using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.

