Powerpoint Templates and Google slides for Various Cyber Security
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Raising Cyber Security Awareness In Organizations Using Various Tools And Tactics PPT Template Bundles DK MD
Raising Cyber Security Awareness In Organizations Using Various Tools And Tactics PPT Template Bundles DK MDDeliver a credible and compelling presentation by deploying this Raising Cyber Security Awareness In Organizations Using Various Tools And Tactics PPT Template Bundles DK MD. Intensify your message with the right graphics, images, icons, etc. presented in this complete deck. This PPT template is a great starting point to convey your messages and build a good collaboration. The fifteen slides added to this PowerPoint slideshow helps you present a thorough explanation of the topic. You can use it to study and present various kinds of information in the form of stats, figures, data charts, and many more. This Raising Cyber Security Awareness In Organizations Using Various Tools And Tactics PPT Template Bundles DK MD PPT slideshow is available for use in standard and widescreen aspects ratios. So, you can use it as per your convenience. Apart from this, it can be downloaded in PNG, JPG, and PDF formats, all completely editable and modifiable. The most profound feature of this PPT design is that it is fully compatible with Google Slides making it suitable for every industry and business domain.
-
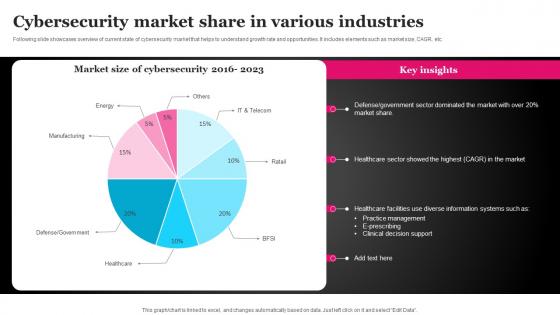 Cybersecurity Market Share In Various Industries FIO SS
Cybersecurity Market Share In Various Industries FIO SSFollowing slide showcases overview of current state of cybersecurity market that helps to understand growth rate and opportunities. It includes elements such as market size, CAGR, etc.Introducing our Cybersecurity Market Share In Various Industries FIO SS set of slides. The topics discussed in these slides are Practice Management, E Prescribing, Clinical Decision Support. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
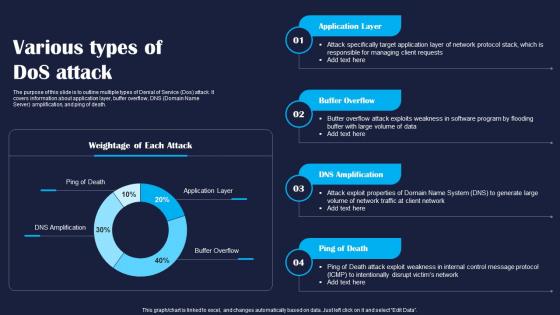 Various Types Of Dos Attack Improving IoT Device Cybersecurity IoT SS
Various Types Of Dos Attack Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to outline multiple types of Denial of Service Dos attack. It covers information about application layer, buffer overflow, DNS Domain Name Server amplification, and ping of death. Deliver an outstanding presentation on the topic using this Various Types Of Dos Attack Improving IoT Device Cybersecurity IoT SS. Dispense information and present a thorough explanation of Application, Layer, Death using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
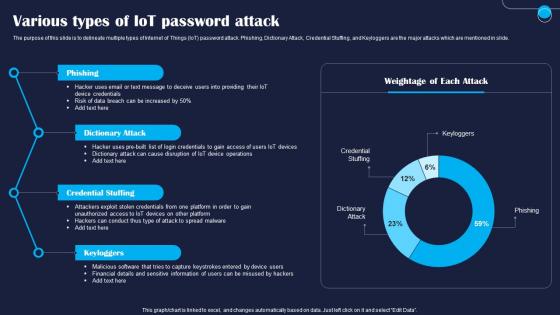 Various Types Of IoT Password Attack Improving IoT Device Cybersecurity IoT SS
Various Types Of IoT Password Attack Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to delineate multiple types of Internet of Things IoT password attack. Phishing, Dictionary Attack, Credential Stuffing, and Keyloggers are the major attacks which are mentioned in slide. Present the topic in a bit more detail with this Various Types Of IoT Password Attack Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Phishing, Dictionary, Credential. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Threats In Blockchain Various Types Of Crypto Phishing Attacks BCT SS V
Cyber Threats In Blockchain Various Types Of Crypto Phishing Attacks BCT SS VThe following slide illustrates various types of phishing attacks to analyze how cryptocurrency funds are stolen from blockchain network. It includes elements such as spear, whaling, clone, spoof emails, accessibility to personal details, replacing original link with fake one, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Various Types Of Crypto Phishing Attacks BCT SS V This template helps you present information on Three stages. You can also present information on Spear Phishing, Whaling Phishing, Clone Phishing using this PPT design. This layout is completely editable so personaize it now
-
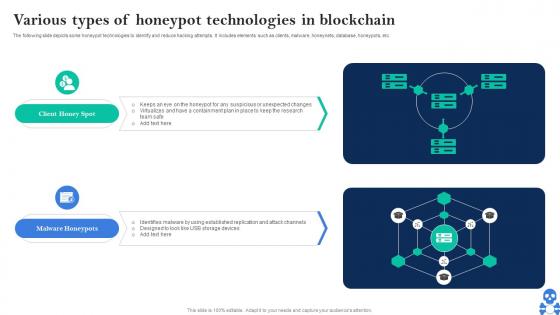 Cyber Threats In Blockchain Various Types Of Honeypot Technologies In Blockchain BCT SS V
Cyber Threats In Blockchain Various Types Of Honeypot Technologies In Blockchain BCT SS VThe following slide depicts some honeypot technologies to identify and reduce hacking attempts. It includes elements such as clients, malware, honeynets, database, honeypots, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threats In Blockchain Various Types Of Honeypot Technologies In Blockchain BCT SS V This template helps you present information on Two stages. You can also present information on Client Honey Spot, Malware Honeypots using this PPT design. This layout is completely editable so personaize it now
-
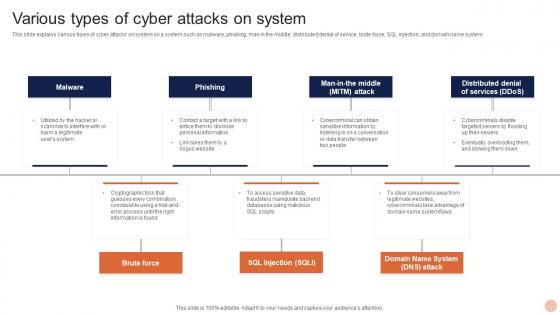 Advanced Technologies Various Types Of Cyber Attacks On System
Advanced Technologies Various Types Of Cyber Attacks On SystemThis slide explains Various types of cyber attacks on system on a system such as malware, phishing, man in the middle, distributed denial of service, brute force, SQL injection, and domain name system. Introducing Advanced Technologies Various Types Of Cyber Attacks On System to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Malware, Phishing, Brute Force, using this template. Grab it now to reap its full benefits.
-
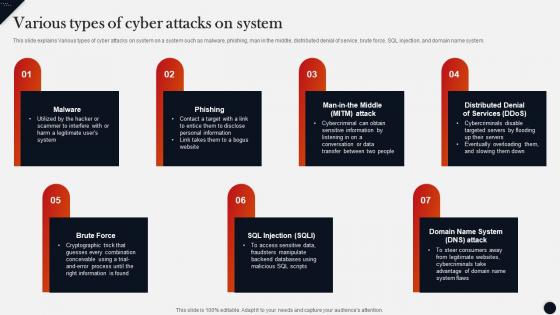 Various Types Of Cyber Attacks On System Modern Technologies
Various Types Of Cyber Attacks On System Modern TechnologiesThis slide explains Various types of cyber attacks on system on a system such as malware,phishing,man in the middle,distributed denial of service,brute force,SQL injection,and domain name system. Introducing Various Types Of Cyber Attacks On System Modern Technologies to increase your presentation threshold. Encompassed with seven stages,this template is a great option to educate and entice your audience. Dispence information on Information Found,Conceivable Using,Cryptographic Trick,using this template. Grab it now to reap its full benefits.
-
 Various Sources Of Cyber Security Incidents Improving Cyber Security Risks Management
Various Sources Of Cyber Security Incidents Improving Cyber Security Risks ManagementThe following slide depicts some multiple drivers of cyber security incidents to generate awareness about cyber crimes. It includes elements such as corporate spies, malicious insiders, criminal groups, hackers, hacktivists, terrorist groups etc. Increase audience engagement and knowledge by dispensing information using Various Sources Of Cyber Security Incidents Improving Cyber Security Risks Management. This template helps you present information on seven stages. You can also present information on Criminal Groups, Terrorist Groups, Malicious Insiders, Corporate Spies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
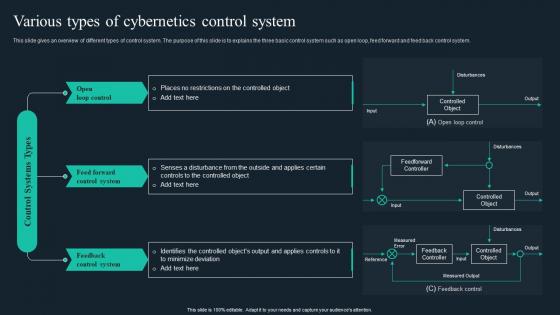 Cybernetic Implants Various Types Of Cybernetics Control System
Cybernetic Implants Various Types Of Cybernetics Control SystemThis slide gives an overview of different types of control system. The purpose of this slide is to explains the three basic control system such as open loop, feed forward and feed back control system. Introducing Cybernetic Implants Various Types Of Cybernetics Control System to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Control, System, Feedback, using this template. Grab it now to reap its full benefits.
-
 Various Cyber Security Incidents Detected By Technology Deployment Plan To Improve Organizations
Various Cyber Security Incidents Detected By Technology Deployment Plan To Improve OrganizationsThis slide represents the detection of certain attacks which affected the systems and networks of the organization by the IT department of the organization. It includes detection of cyber security incidents such as insider threat, phishing attack, malware attack etc. Introducing Various Cyber Security Incidents Detected By Technology Deployment Plan To Improve Organizations to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Phishing, Malware, Application, using this template. Grab it now to reap its full benefits.
-
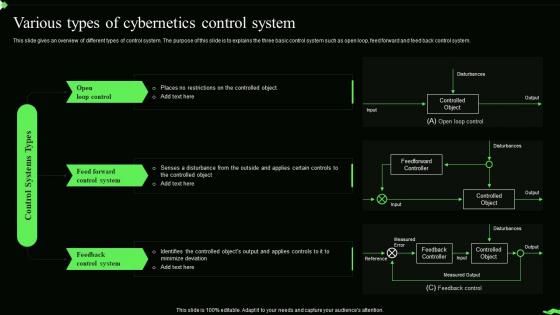 Information Theory Various Types Of Cybernetics Control System
Information Theory Various Types Of Cybernetics Control SystemThis slide gives an overview of different types of control system. The purpose of this slide is to explains the three basic control system such as open loop, feed forward and feed back control system. Introducing Information Theory Various Types Of Cybernetics Control System to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Feed Forward Control System, Feedback Control System, Cybernetics Control System, using this template. Grab it now to reap its full benefits.
-
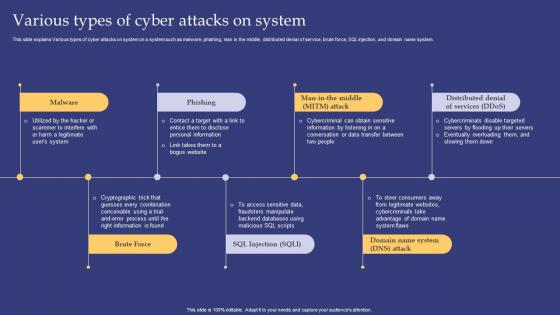 Emerging Technologies Various Types Of Cyber Attacks On System
Emerging Technologies Various Types Of Cyber Attacks On SystemThis slide explains Various types of cyber attacks on system on a system such as malware, phishing, man in the middle, distributed denial of service, brute force, SQL injection, and domain name system. Increase audience engagement and knowledge by dispensing information using Emerging Technologies Various Types Of Cyber Attacks On System. This template helps you present information on seven stages. You can also present information on Malware, Phishing using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
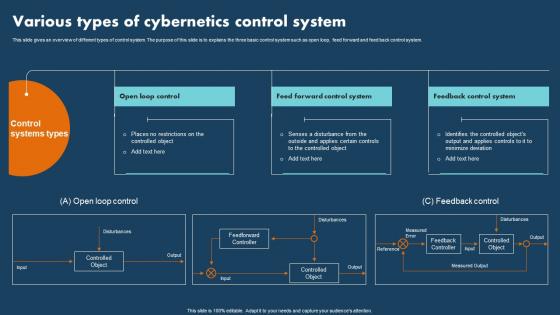 Operations Research Various Types Of Cybernetics Control System
Operations Research Various Types Of Cybernetics Control SystemThis slide gives an overview of different types of control system. The purpose of this slide is to explains the three basic control system such as open loop, feed forward and feed back control system. Introducing Operations Research Various Types Of Cybernetics Control System to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Controlled, Disturbance, Identifies, using this template. Grab it now to reap its full benefits.
-
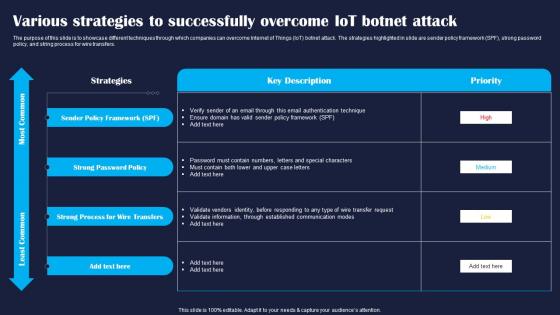 Various Strategies To Successfully Improving IoT Device Cybersecurity IoT SS
Various Strategies To Successfully Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase different techniques through which companies can overcome Internet of Things IoT botnet attack. The strategies highlighted in slide are sender policy framework SPF, strong password policy, and string process for wire transfers. Present the topic in a bit more detail with this Various Strategies To Successfully Improving IoT Device Cybersecurity IoT SS. Use it as a tool for discussion and navigation on Policy, Strong, Process. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
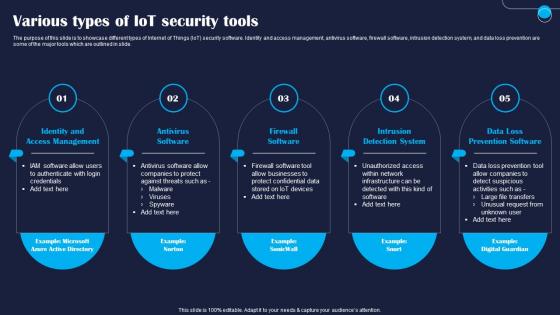 Various Types Of IoT Security Tools Improving IoT Device Cybersecurity IoT SS
Various Types Of IoT Security Tools Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to showcase different types of Internet of Things IoT security software. Identity and access management, antivirus software, firewall software, intrusion detection system, and data loss prevention are some of the major tools which are outlined in slide. Introducing Various Types Of IoT Security Tools Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Management, Software, System, using this template. Grab it now to reap its full benefits.
-
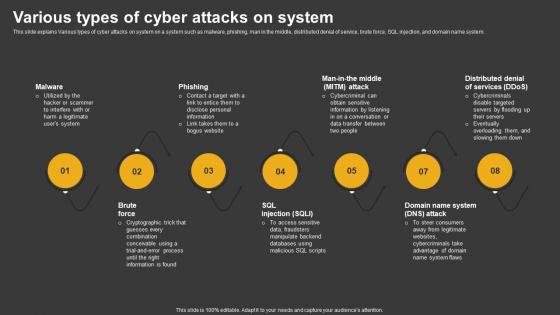 Trending Technologies Various Types Of Cyber Attacks On System
Trending Technologies Various Types Of Cyber Attacks On SystemThis slide explains Various types of cyber attacks on system on a system such as malware, phishing, man in the middle, distributed denial of service, brute force, SQL injection, and domain name system. Increase audience engagement and knowledge by dispensing information using Trending Technologies Various Types Of Cyber Attacks On System. This template helps you present information on eight stages. You can also present information on Malware, Phishing, Brute Force using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
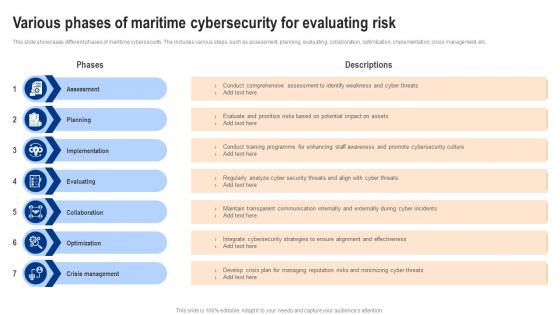 Various Phases Of Maritime Cybersecurity For Evaluating Risk
Various Phases Of Maritime Cybersecurity For Evaluating RiskThis slide showcases different phases of maritime cybersecurity. The includes various steps such as assessment, planning, evaluating, collaboration, optimization, implementation, crisis management, etc. Introducing our premium set of slides with Various Phases Of Maritime Cybersecurity For Evaluating Risk. Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Conduct Comprehensive, Conduct Training Programme, Analyze Cyber Security. So download instantly and tailor it with your information.
-
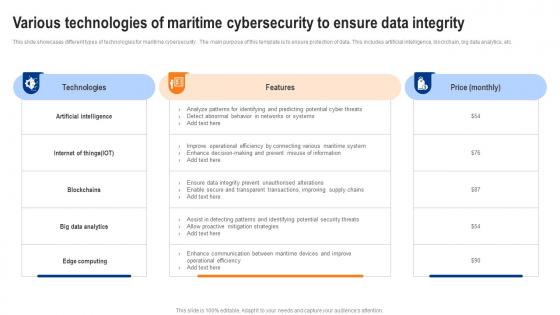 Various Technologies Of Maritime Cybersecurity To Ensure Data Integrity
Various Technologies Of Maritime Cybersecurity To Ensure Data IntegrityThis slide showcases different types of technologies for maritime cybersecurity . The main purpose of this template is to ensure protection of data. This includes artificial intelligence, blockchain, big data analytics, etc. Introducing our Various Technologies Of Maritime Cybersecurity To Ensure Data Integrity set of slides. The topics discussed in these slides are Artificial Intelligence, Internet Of Things, Big Data Analytics. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Various Types Of Cyber Security Audit
Various Types Of Cyber Security AuditThis slide covers various kinds of audit and provides details about categories to optimize performance in organization. It includes elements such as new audit, repeat audit , etc. Presenting our set of slides with Various Types Of Cyber Security Audit. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on New Audit, Repeat Audit, Incident Audit .
-
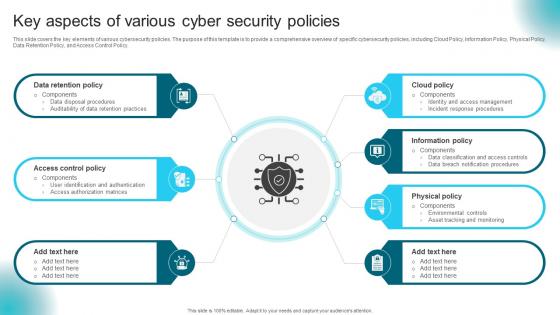 Key Aspects Of Various Cyber Security Policies
Key Aspects Of Various Cyber Security PoliciesThis slide covers the key elements of various cybersecurity policies. The purpose of this template is to provide a comprehensive overview of specific cybersecurity policies, including Cloud Policy, Information Policy, Physical Policy, Data Retention Policy, and Access Control Policy. Presenting our set of slides with Key Aspects Of Various Cyber Security Policies This exhibits information on Seven stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Data Retention Policy, Cloud Policy, Information Policy
-
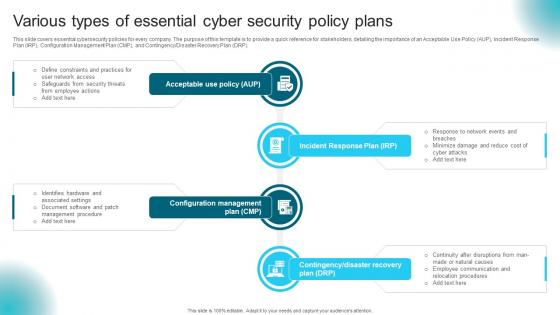 Various Types Of Essential Cyber Security Policy Plans
Various Types Of Essential Cyber Security Policy PlansThis slide covers essential cybersecurity policies for every company. The purpose of this template is to provide a quick reference for stakeholders, detailing the importance of an Acceptable Use Policy AUP, Incident Response Plan IRP, Configuration Management Plan CMP, and ContingencyDisaster Recovery Plan DRP. Introducing our premium set of slides with Various Types Of Essential Cyber Security Policy Plans Ellicudate the Six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Incident Response Plan, Configuration Management, Acceptable Use Policy. So download instantly and tailor it with your information.
-
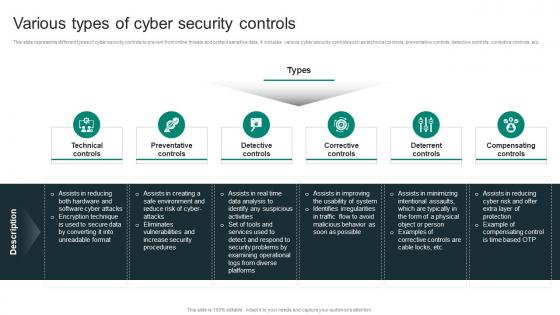 Various Types Of Cyber Security Controls
Various Types Of Cyber Security ControlsThis slide represents different types of cyber security controls to prevent from online threats and protect sensitive data. It includes various cyber security controls such as technical controls, preventative controls, detective controls, corrective controls, etc. Presenting our set of slides with Various Types Of Cyber Security Controls This exhibits information on six stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Technical Controls, Preventative Controls, Detective Controls
-
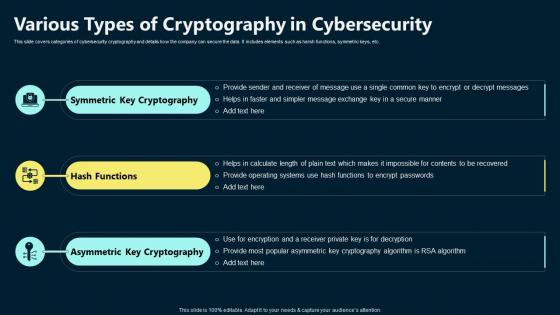 Various Types Of Cryptography In Cybersecurity
Various Types Of Cryptography In CybersecurityThis slide covers categories of cybersecurity cryptography and details how the company can secure the data. It includes elements such as harsh functions, symmetric keys, etc. Introducing our premium set of slides with Various Types Of Cryptography In Cybersecurity. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Symmetric Key Cryptography, Hash Functions, Asymmetric Key Cryptography. So download instantly and tailor it with your information.
-
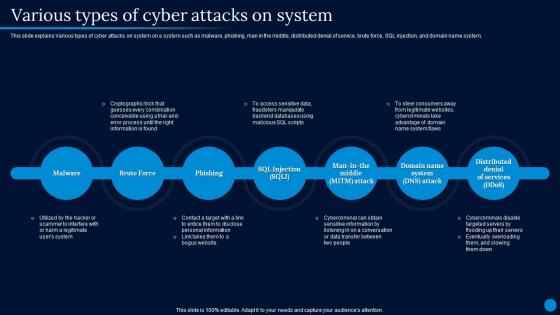 Current Trending Technologies Various Types Of Cyber Attacks On System
Current Trending Technologies Various Types Of Cyber Attacks On SystemThis slide explains Various types of cyber attacks on system on a system such as malware, phishing, man in the middle, distributed denial of service, brute force, SQL injection, and domain name system. Introducing Current Trending Technologies Various Types Of Cyber Attacks On System to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Cyber Attacks On System, Distributed Denial Of Service, Cryptographic Trick, Cybercriminals Disable Targeted Servers, using this template. Grab it now to reap its full benefits.
-
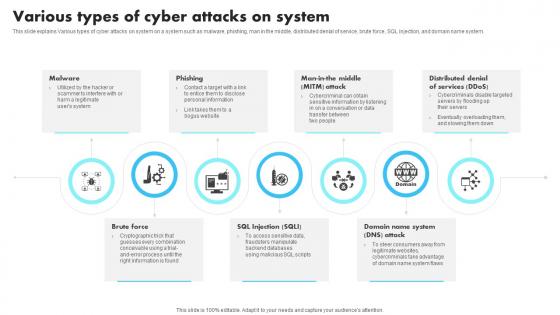 New Technologies Various Types Of Cyber Attacks On System
New Technologies Various Types Of Cyber Attacks On SystemThis slide explains Various types of cyber attacks on system on a system such as malware, phishing, man in the middle, distributed denial of service, brute force, SQL injection, and domain name system. Introducing New Technologies Various Types Of Cyber Attacks On System to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Malware, Phishing, Distributed, using this template. Grab it now to reap its full benefits.
-
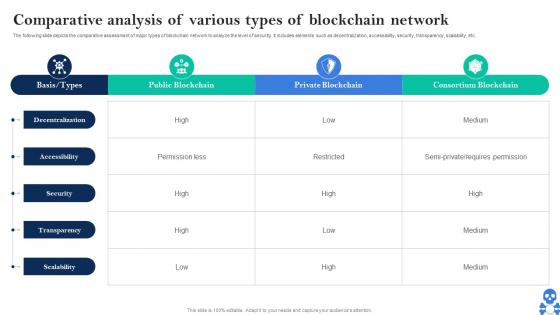 Cyber Threats In Blockchain Comparative Analysis Of Various Types Of Blockchain Network BCT SS V
Cyber Threats In Blockchain Comparative Analysis Of Various Types Of Blockchain Network BCT SS VThe following slide depicts the comparative assessment of major types of blockchain network to analyze the level of security. It includes elements such as decentralization, accessibility, security, transparency, scalability, etc. Present the topic in a bit more detail with this Cyber Threats In Blockchain Comparative Analysis Of Various Types Of Blockchain Network BCT SS V Use it as a tool for discussion and navigation on Public Blockchain, Private Blockchain, Consortium Blockchain This template is free to edit as deemed fit for your organization. Therefore download it now.
-
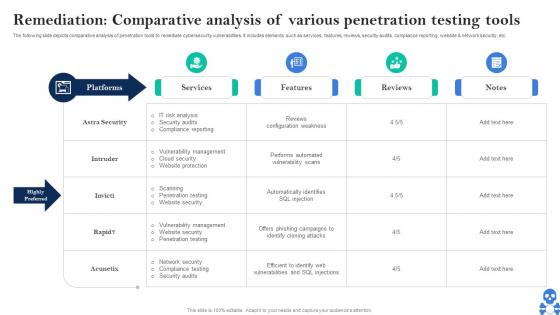 Cyber Threats In Blockchain Remediation Comparative Analysis Of Various Penetration Testing Tools BCT SS V
Cyber Threats In Blockchain Remediation Comparative Analysis Of Various Penetration Testing Tools BCT SS VThe following slide depicts comparative analysis of penetration tools to remediate cybersecurity vulnerabilities. It includes elements such as services, features, reviews, security audits, compliance reporting, website and network security, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Remediation Comparative Analysis Of Various Penetration Testing Tools BCT SS V Dispense information and present a thorough explanation of Services, Features, Reviews using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
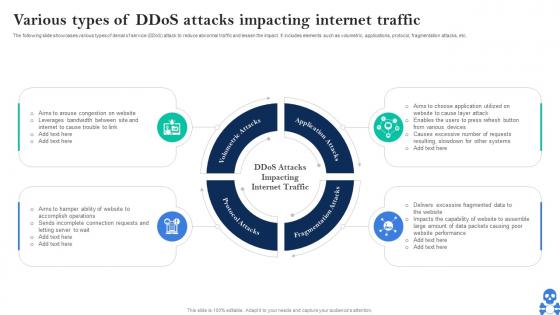 Cyber Threats In Blockchain Various Types Of Ddos Attacks Impacting Internet Traffic BCT SS V
Cyber Threats In Blockchain Various Types Of Ddos Attacks Impacting Internet Traffic BCT SS VThe following slide showcases various types of denial of service DDoS attack to reduce abnormal traffic and lessen the impact. It includes elements such as volumetric, applications, protocol, fragmentation attacks, etc. Introducing Cyber Threats In Blockchain Various Types Of Ddos Attacks Impacting Internet Traffic BCT SS V to increase your presentation threshold. Encompassed with Five stages, this template is a great option to educate and entice your audience. Dispence information on Volumetric Attacks, Application Attacks, Fragmentation Attacks using this template. Grab it now to reap its full benefits.
-
 Various Types Of Csirt Cyber Security
Various Types Of Csirt Cyber SecurityThis slide highlights different types of CSIRT cyber security. The main purpose of this template is showcasing various approaches of dealing with cyber security. This includes internal CSIRT, National CSIRT, Vendor CSIRT, etc. Presenting our set of slides with Various Types Of Csirt Cyber Security. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Maintaining Data, Cyber Threat, Cyber Security.
-
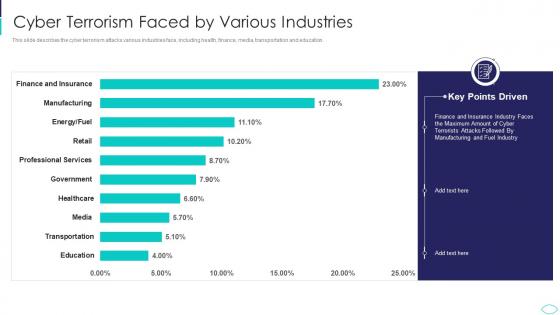 Cyber Terrorism Faced By Various Industries Cyber Terrorism Attacks
Cyber Terrorism Faced By Various Industries Cyber Terrorism AttacksThis slide describes the cyber terrorism attacks various industries face, including health, finance, media, transportation and education. Deliver an outstanding presentation on the topic using this Cyber Terrorism Faced By Various Industries Cyber Terrorism Attacks. Dispense information and present a thorough explanation of Cyber Terrorism Faced By Various Industries using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyberterrorism it cyber terrorism faced by various industries ppt slides model
Cyberterrorism it cyber terrorism faced by various industries ppt slides modelThis slide describes the cyber terrorism various industries face, including health, finance, media, transportation and education. Present the topic in a bit more detail with this Cyberterrorism IT Cyber Terrorism Faced By Various Industries Ppt Slides Model. Use it as a tool for discussion and navigation on Education, Transportation, Media, Healthcare, Government. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
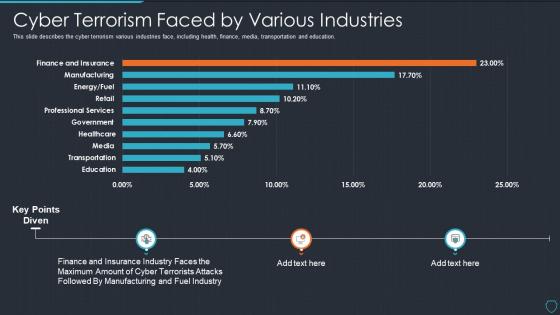
 Top Cyber Risks Faced By The Real Estate Company Managing Various Risks
Top Cyber Risks Faced By The Real Estate Company Managing Various RisksThe following slide exhibits four cyber risks which are faced by the real estate organization. It provides key information about the ransomware, phishing, web based attack and email fraud attack. Present the topic in a bit more detail with this Top Cyber Risks Faced By The Real Estate Company Managing Various Risks. Use it as a tool for discussion and navigation on Phishing, Business Email Compromise, Ransomware. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
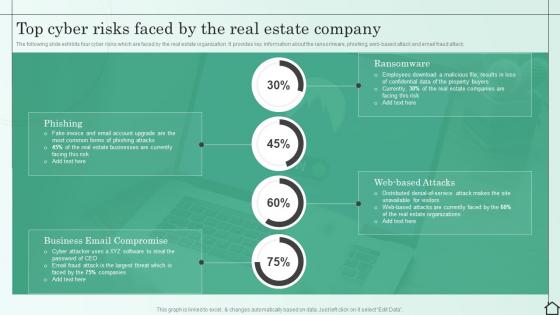
 Cyber Bullying Cases Occurred In Various Areas
Cyber Bullying Cases Occurred In Various AreasPresenting our well structured Cyber Bullying Cases Occurred In Various Areas. The topics discussed in this slide are Respondents, Social, Media. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
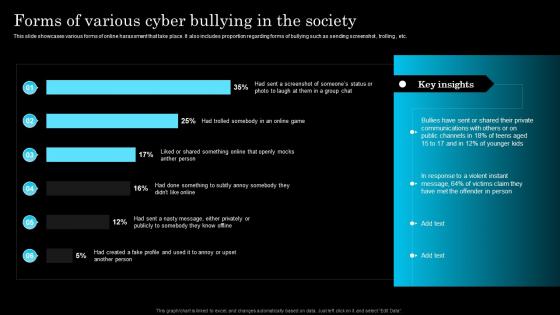 Forms Of Various Cyber Bullying In The Society
Forms Of Various Cyber Bullying In The SocietyThis slide showcases various forms of online harassment that take place. It also includes proportion regarding forms of bullying such as sending screenshot, trolling , etc. Introducing our Forms Of Various Cyber Bullying In The Society set of slides. The topics discussed in these slides are Bullies, Communications, Response. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
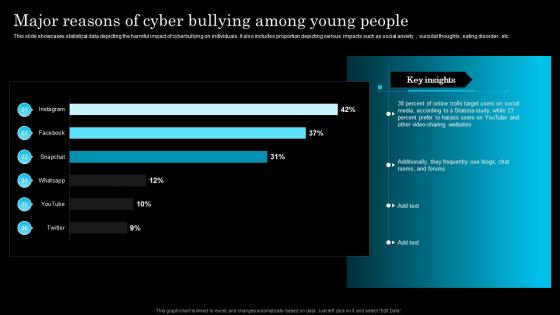 Cyber bullying cases on various social media platforms
Cyber bullying cases on various social media platformsThis slide showcases statistical data depicting the reasons for cyberbullying among young generation. It also includes percentage of reasons such as internet and hobbies, household income, academic performances, etc. Presenting our well structured Cyber bullying cases on various social media platforms. The topics discussed in this slide are Cyberbullies, Commit, Disgrace. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
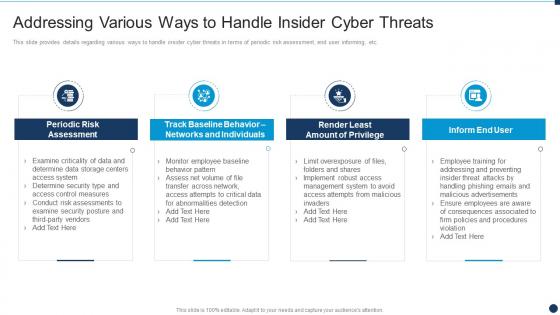
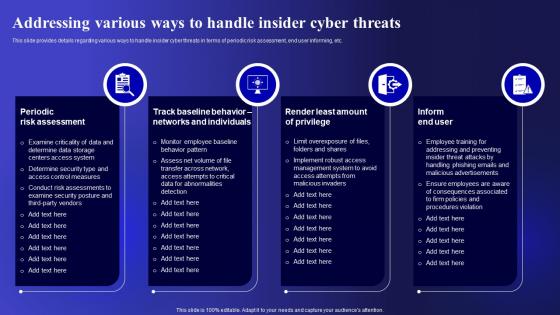 Addressing Various Ways To Handle Cyber Threats Management To Enable Digital Assets Security
Addressing Various Ways To Handle Cyber Threats Management To Enable Digital Assets SecurityThis slide provides details regarding various ways to handle insider cyber threats in terms of periodic risk assessment, end user informing, etc. Present the topic in a bit more detail with this Addressing Various Ways To Handle Cyber Threats Management To Enable Digital Assets Security. Use it as a tool for discussion and navigation on Periodic Risk Assessment, Individuals, Implement. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Various Ways To Handle Insider Cyber Threats Vulnerability Administration At Workplace
Various Ways To Handle Insider Cyber Threats Vulnerability Administration At WorkplaceThis slide provides details regarding various ways to handle insider cyber threats in terms of periodic risk assessment, end user informing, etc. Present the topic in a bit more detail with this Various Ways To Handle Insider Cyber Threats Vulnerability Administration At Workplace. Use it as a tool for discussion and navigation on Assessment, Individuals, Management This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vulnerability Administration At Workplace Cyber Threats In Various Industries
Vulnerability Administration At Workplace Cyber Threats In Various IndustriesThis slide provides details regarding insider threats identified in various industries such as healthcare, manufacturing, government, energy, etc. Present the topic in a bit more detail with this Vulnerability Administration At Workplace Cyber Threats In Various Industries. Use it as a tool for discussion and navigation on Healthcare, Manufacturing, Government. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
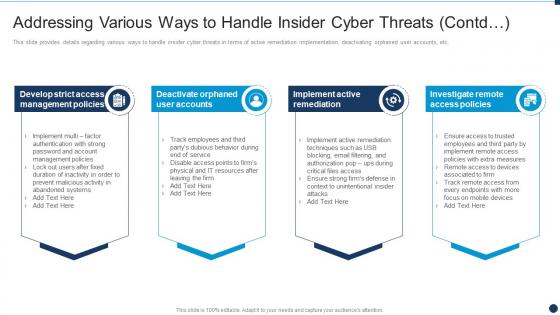 Vulnerability Administration At Workplace Various Ways To Handle Insider Cyber Threats Contd
Vulnerability Administration At Workplace Various Ways To Handle Insider Cyber Threats ContdThis slide provides details regarding various ways to handle insider cyber threats in terms of active remediation implementation, deactivating orphaned user accounts, etc. Increase audience engagement and knowledge by dispensing information using Vulnerability Administration At Workplace Various Ways To Handle Insider Cyber Threats Contd. This template helps you present information on four stages. You can also present information on Management Policies, Remediation, Investigate Remote using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Various Cyber Terrorism Threats With Risk Priority
Various Cyber Terrorism Threats With Risk PriorityThis slide represents the five major threats caused by cyber terrorism along with their risk priorities. It includes threats such as malware, phishing, spear fishing, SQL injection and advanced persistent threats. Presenting our well structured Various Cyber Terrorism Threats With Risk Priority. The topics discussed in this slide are Phishing, Malicious Software, Threat. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
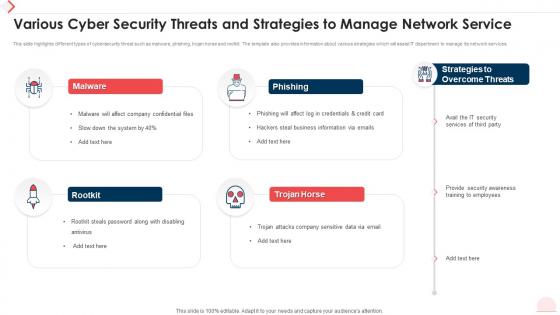 Various Cyber Security Threats And Strategies To Manage Network Service
Various Cyber Security Threats And Strategies To Manage Network ServiceThis slide highlights different types of cybersecurity threat such as malware, phishing, trojan horse and rootkit. The template also provides information about various strategies which will assist IT department to manage its network services. Introducing our premium set of slides with Various Cyber Security Threats And Strategies To Manage Network Service. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Strategies Overcome Threats, IT Security Services, Provide Security Awareness. So download instantly and tailor it with your information.
-
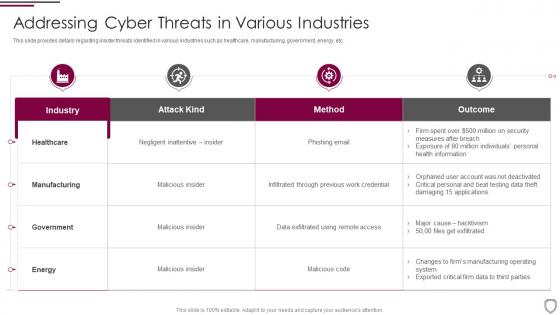 Addressing cyber threats in various industries corporate security management
Addressing cyber threats in various industries corporate security managementThis slide provides details regarding insider threats identified in various industries such as healthcare, manufacturing, government, energy, etc. Deliver an outstanding presentation on the topic using this Addressing Cyber Threats In Various Industries Corporate Security Management. Dispense information and present a thorough explanation of Healthcare, Manufacturing, Government, Industry using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
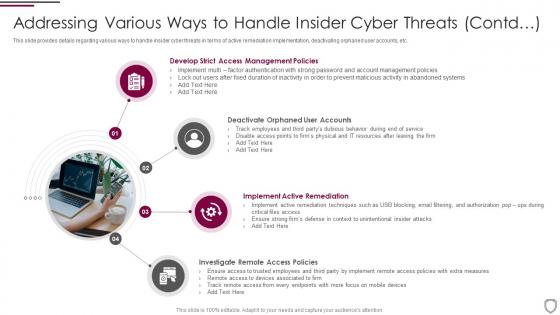 Addressing various ways to handle insider cyber threats corporate security management
Addressing various ways to handle insider cyber threats corporate security managementThis slide provides details regarding various ways to handle insider cyber threats in terms of active remediation implementation, deactivating orphaned user accounts, etc. Introducing Addressing Various Ways To Handle Insider Cyber Threats Corporate Security Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Management Policies, Implement Active Remediation, Investigate Remote Access Policies, Deactivate Orphaned User Accounts, using this template. Grab it now to reap its full benefits.
-
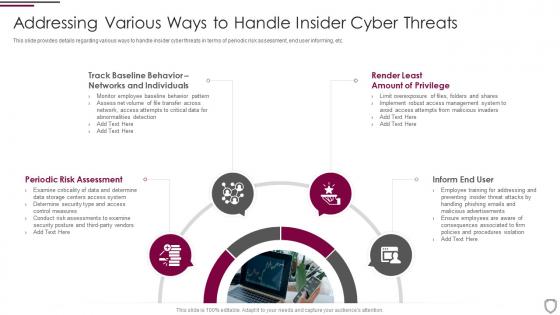 Corporate security management addressing various ways to handle insider cyber threats
Corporate security management addressing various ways to handle insider cyber threatsThis slide provides details regarding various ways to handle insider cyber threats in terms of periodic risk assessment, end user informing, etc. Introducing Corporate Security Management Addressing Various Ways To Handle Insider Cyber Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Periodic Risk Assessment, Inform End User, Render Least, Networks And Individuals, using this template. Grab it now to reap its full benefits.
-
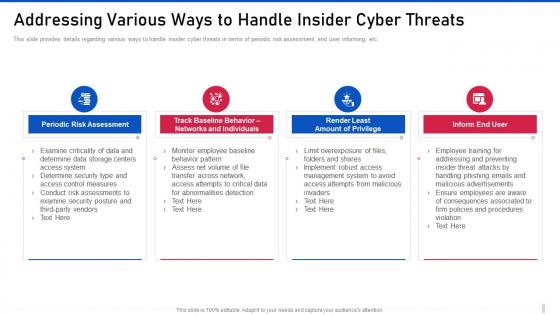 Addressing various ways to handle insider cyber threat management for organization critical
Addressing various ways to handle insider cyber threat management for organization criticalThis slide provides details regarding various ways to handle insider cyber threats in terms of periodic risk assessment, end user informing, etc. Introducing Addressing Various Ways To Handle Insider Cyber Threat Management For Organization Critical to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Periodic Risk Assessment, Networks And Individuals, Amount Of Privilege, using this template. Grab it now to reap its full benefits.
-
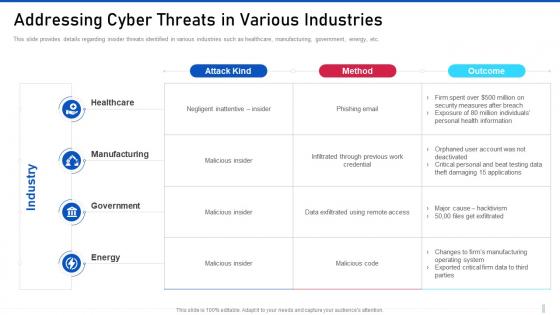 Threat management for organization critical addressing cyber threats in various industries
Threat management for organization critical addressing cyber threats in various industriesThis slide provides details regarding insider threats identified in various industries such as healthcare, manufacturing, government, energy, etc. Present the topic in a bit more detail with this Threat Management For Organization Critical Addressing Cyber Threats In Various Industries. Use it as a tool for discussion and navigation on Manufacturing, Government, Malicious Insider. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
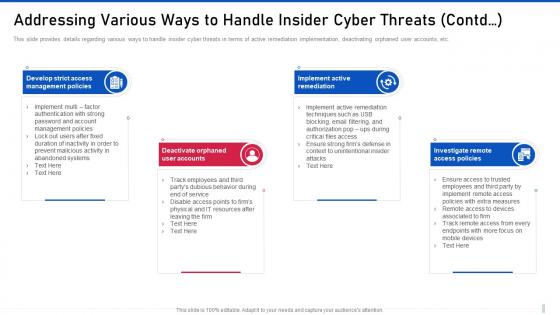 Threat management for organization critical addressing various ways to handle insider cyber threats contd
Threat management for organization critical addressing various ways to handle insider cyber threats contdThis slide provides details regarding various ways to handle insider cyber threats in terms of active remediation implementation, deactivating orphaned user accounts, etc. Introducing Threat Management For Organization Critical Addressing Various Ways To Handle Insider Cyber Threats Contd to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Management Policies, Deactivate Orphaned, Implement Active, using this template. Grab it now to reap its full benefits.
-
 Addressing cyber threats various industries cyber security risk management
Addressing cyber threats various industries cyber security risk managementThis slide provides details regarding insider threats identified in various industries such as healthcare, manufacturing, government, energy, etc. Introducing Addressing Cyber Threats Various Industries Cyber Security Risk Management to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Industry, Healthcare, Manufacturing, Government, Energy, using this template. Grab it now to reap its full benefits.
-
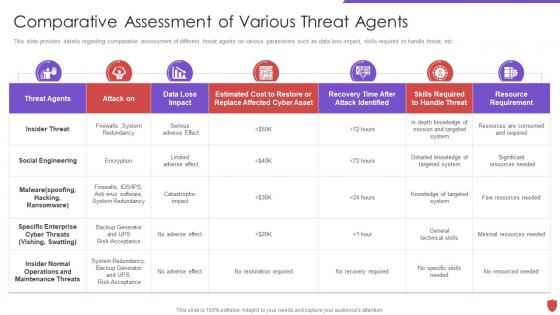 Cyber security risk management comparative assessment various threat agents
Cyber security risk management comparative assessment various threat agentsThis slide provides details regarding comparative assessment of different threat agents on various parameters such as data loss impact, skills required to handle threat, etc. Deliver an outstanding presentation on the topic using this Cyber Security Risk Management Comparative Assessment Various Threat Agents. Dispense information and present a thorough explanation of Insider Threat, Social Engineering, Threat Agents, Cyber Threats using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
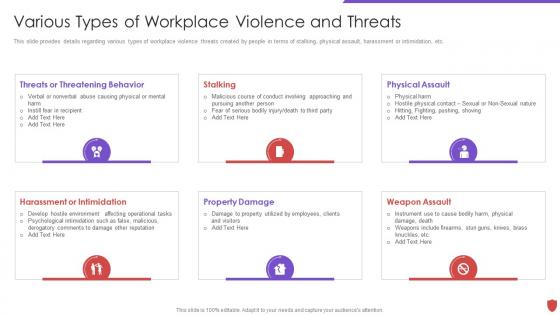 Cyber security risk management various types of workplace violence and threats
Cyber security risk management various types of workplace violence and threatsThis slide provides details regarding various types of workplace violence threats created by people in terms of stalking, physical assault, harassment or intimidation, etc. Introducing Cyber Security Risk Management Various Types Of Workplace Violence And Threats to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Threats Or Threatening Behavior, Physical Assault, Property Damage, using this template. Grab it now to reap its full benefits.
-
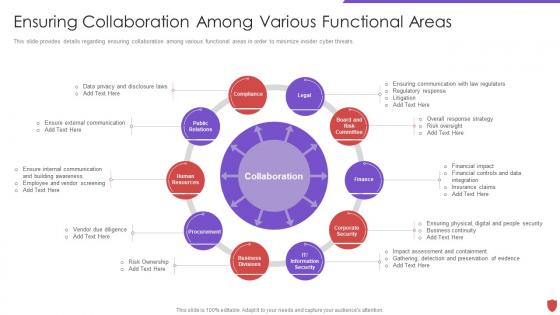 Ensuring collaboration among various functional areas cyber security risk management
Ensuring collaboration among various functional areas cyber security risk managementThis slide provides details regarding ensuring collaboration among various functional areas in order to minimize insider cyber threats. Introducing Ensuring Collaboration Among Various Functional Areas Cyber Security Risk Management to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Legal, Compliance, Public Relations, Human Resources, Procurement, Board And Risk Committee, using this template. Grab it now to reap its full benefits.
-
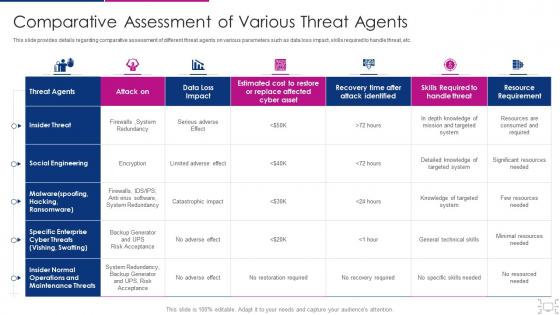 Cyber threat management workplace comparative assessment various threat
Cyber threat management workplace comparative assessment various threatThis slide provides details regarding comparative assessment of different threat agents on various parameters such as data loss impact, skills required to handle threat, etc. Present the topic in a bit more detail with this Cyber Threat Management Workplace Comparative Assessment Various Threat. Use it as a tool for discussion and navigation on Insider Threat, Social Engineering, Insider Normal Operations And Maintenance Threats. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
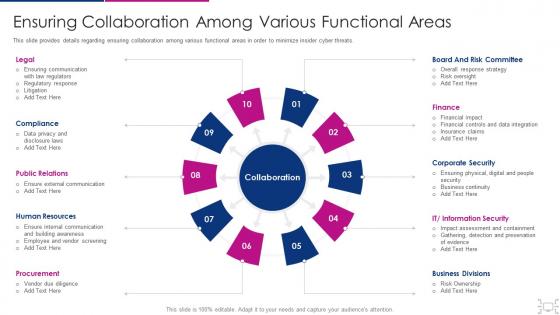 Cyber threat management workplace ensuring collaboration among various
Cyber threat management workplace ensuring collaboration among variousThis slide provides details regarding ensuring collaboration among various functional areas in order to minimize insider cyber threats. Increase audience engagement and knowledge by dispensing information using Cyber Threat Management Workplace Ensuring Collaboration Among Various. This template helps you present information on ten stages. You can also present information on Legal, Compliance, Public Relations, Human Resources, Procurement, Board And Risk Committee, Finance, Corporate Security, Business Divisions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber threat management workplace addressing cyber threats various industries
Cyber threat management workplace addressing cyber threats various industriesThis slide provides details regarding insider threats identified in various industries such as healthcare, manufacturing, government, energy, etc. Present the topic in a bit more detail with this Cyber Threat Management Workplace Addressing Cyber Threats Various Industries. Use it as a tool for discussion and navigation on Industry, Healthcare, Manufacturing, Government, Energy. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
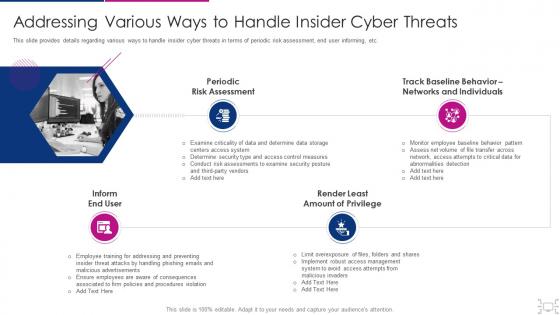 Cyber threat management workplace addressing various ways handle insider
Cyber threat management workplace addressing various ways handle insiderThis slide provides details regarding various ways to handle insider cyber threats in terms of periodic risk assessment, end user informing, etc. Increase audience engagement and knowledge by dispensing information using Cyber Threat Management Workplace Addressing Various Ways Handle Insider. This template helps you present information on four stages. You can also present information on Periodic Risk Assessment, Inform End User, Render Least Amount Privilege, Track Baseline Behavior, Networks And Individuals using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
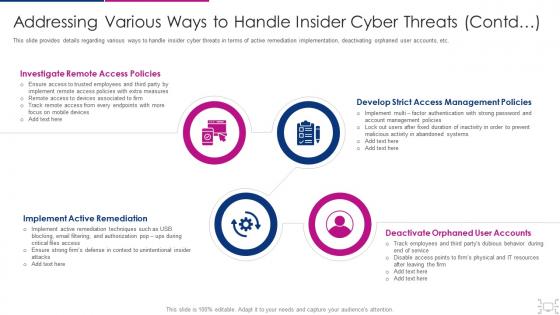 Cyber threat management workplace addressing various ways to handle insider
Cyber threat management workplace addressing various ways to handle insiderThis slide provides details regarding various ways to handle insider cyber threats in terms of active remediation implementation, deactivating orphaned user accounts, etc. Introducing Cyber Threat Management Workplace Addressing Various Ways To Handle Insider to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Investigate Remote Access Policies, Develop Strict Access Management Policies, Deactivate Orphaned User Accounts, Implement Active Remediation , using this template. Grab it now to reap its full benefits.
-
 Cyber threat management workplace various types of workplace violence
Cyber threat management workplace various types of workplace violenceThis slide provides details regarding various types of workplace violence threats created by people in terms of stalking, physical assault, harassment or intimidation, etc. Introducing Cyber Threat Management Workplace Various Types Of Workplace Violence to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Threats Or Threatening Behavior, Physical Assault, Property Damage, Stalking Harassment Or Intimidation, Weapon Assault, using this template. Grab it now to reap its full benefits.
-
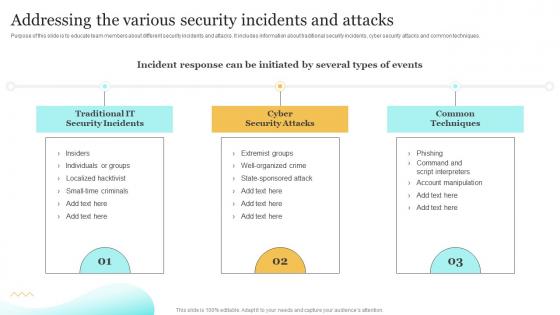 Addressing The Various Security Incidents Upgrading Cybersecurity With Incident Response Playbook
Addressing The Various Security Incidents Upgrading Cybersecurity With Incident Response PlaybookPurpose of this slide is to educate team members about different security incidents and attacks. It includes information about traditional security incidents, cyber security attacks and common techniques. Deliver an outstanding presentation on the topic using this Addressing The Various Security Incidents Upgrading Cybersecurity With Incident Response Playbook. Dispense information and present a thorough explanation of Individuals, Manipulation, Techniques using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
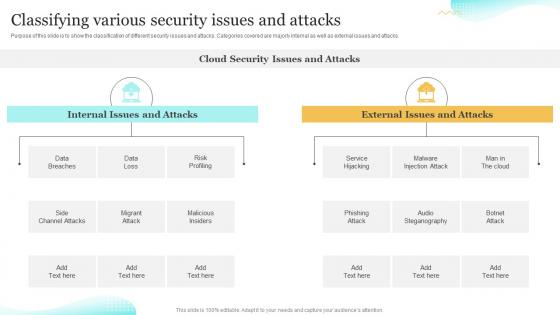 Classifying Various Security Issues And Attacks Upgrading Cybersecurity With Incident Response Playbook
Classifying Various Security Issues And Attacks Upgrading Cybersecurity With Incident Response PlaybookPurpose of this slide is to show the classification of different security issues and attacks. Categories covered are majorly internal as well as external issues and attacks. Deliver an outstanding presentation on the topic using this Classifying Various Security Issues And Attacks Upgrading Cybersecurity With Incident Response Playbook. Dispense information and present a thorough explanation of Classifying, Steganography, Classification using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.


