Powerpoint Templates and Google slides for Verified Security Icon For Company Cloud Data
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Adopt Security Auditing Checklist To Verify Processes Hands On Blockchain Security Risk BCT SS V
Adopt Security Auditing Checklist To Verify Processes Hands On Blockchain Security Risk BCT SS VThe following slide depicts blockchain cybersecurity auditing checklist to minimize probability of frauds. It includes elements such as network, node, smart contract, security, consensus mechanism, data encryption, access management, etc. Present the topic in a bit more detail with this Adopt Security Auditing Checklist To Verify Processes Hands On Blockchain Security Risk BCT SS V. Use it as a tool for discussion and navigation on Parameters, Description, Comments. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Adopt Security Auditing Checklist To Verify Processes Guide For Blockchain BCT SS V
Adopt Security Auditing Checklist To Verify Processes Guide For Blockchain BCT SS VThe following slide depicts blockchain cybersecurity auditing checklist to minimize probability of frauds. It includes elements such as network, node, smart contract, security, consensus mechanism, data encryption, access management, etc. Present the topic in a bit more detail with this Adopt Security Auditing Checklist To Verify Processes Guide For Blockchain BCT SS V Use it as a tool for discussion and navigation on Network Security, Node Security, Consensus Mechanism This template is free to edit as deemed fit for your organization. Therefore download it now.
-
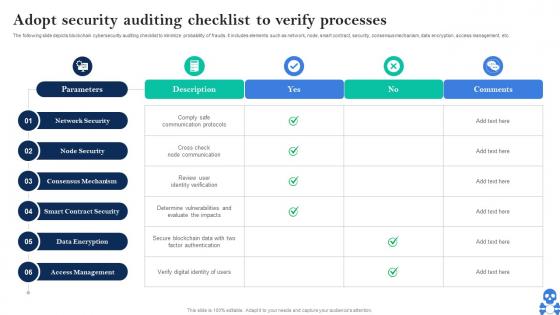 Cyber Threats In Blockchain Adopt Security Auditing Checklist To Verify Processes BCT SS V
Cyber Threats In Blockchain Adopt Security Auditing Checklist To Verify Processes BCT SS VThe following slide depicts blockchain cybersecurity auditing checklist to minimize probability of frauds. It includes elements such as network, node, smart contract, security, consensus mechanism, data encryption, access management, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Adopt Security Auditing Checklist To Verify Processes BCT SS V Dispense information and present a thorough explanation of Consensus Mechanism, Smart Contract Security, Data Encryption using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Security Audit Procedure Icon To Verify Company Data Protection
Security Audit Procedure Icon To Verify Company Data ProtectionPresenting our set of slides with Security Audit Procedure Icon To Verify Company Data Protection. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Security Audit Procedure, Verify Company, Data Protection.
-
 Ultimate Guide For Blockchain Adopt Security Auditing Checklist To Verify Processes BCT SS
Ultimate Guide For Blockchain Adopt Security Auditing Checklist To Verify Processes BCT SSThe following slide depicts blockchain cybersecurity auditing checklist to minimize probability of frauds. It includes elements such as network, node, smart contract, security, consensus mechanism, data encryption, access management, etc. Present the topic in a bit more detail with this Ultimate Guide For Blockchain Adopt Security Auditing Checklist To Verify Processes BCT SS Use it as a tool for discussion and navigation on Network Security, Node Security This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Verified encrypted data security layer with arrows
Verified encrypted data security layer with arrowsPresenting this set of slides with name - Verified Encrypted Data Security Layer With Arrows. This is a six stage process. The stages in this process are Security Layers, Safety Layers, Protection Layers.
-
 Verify credit card security directory service approval rejection
Verify credit card security directory service approval rejectionPresenting Verify Credit Card Security Directory Service Approval Rejection. Make modifications in the font color, font size, and font style of the slide as it is entirely customizable. Its compatibility with Google Slides makes it accessible at once. You can transform and save the slide in PDF and JPG formats as well. Get this high-quality slide to present it in front of thousands of people on a standard screen and widescreen.
-
 Verified security icon for company cloud data
Verified security icon for company cloud dataPresenting this set of slides with name Verified Security Icon For Company Cloud Data. This is a four stage process. The stages in this process are Verified Security Icon For Company Cloud Data. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.

