Powerpoint Templates and Google slides for Vulnerability to attacks
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Signs That Your Business May Be Vulnerable To Cyber Threats Training Ppt
Signs That Your Business May Be Vulnerable To Cyber Threats Training PptPresenting Signs that your Business may be Vulnerable to Cyber Threats. This PPT presentation is thoroughly researched and each slide consists of appropriate content. Designed by PowerPoint specialists, this PPT is fully customizable alter the colors, text, icons, and font size to meet your needs. Compatible with Google Slides and backed by superior customer support. Download today to deliver your presentation confidently.
-
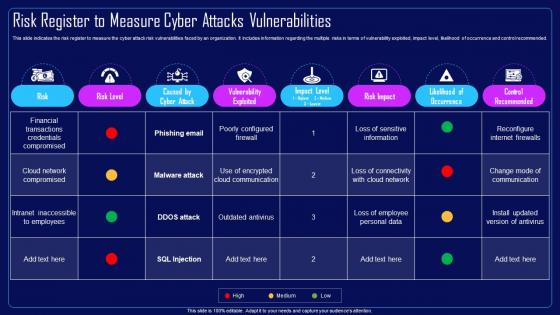 Action Plan To Combat Cyber Crimes Risk Register To Measure Cyber Attacks Vulnerabilities
Action Plan To Combat Cyber Crimes Risk Register To Measure Cyber Attacks VulnerabilitiesThis slide indicates the risk register to measure the cyber attack risk vulnerabilities faced by an organization. It includes information regarding the multiple risks in terms of vulnerability exploited, impact level, likelihood of occurrence and control recommended. Present the topic in a bit more detail with this Action Plan To Combat Cyber Crimes Risk Register To Measure Cyber Attacks Vulnerabilities. Use it as a tool for discussion and navigation on Cloud Network Compromised, Financial Transactions, Credentials Compromised. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
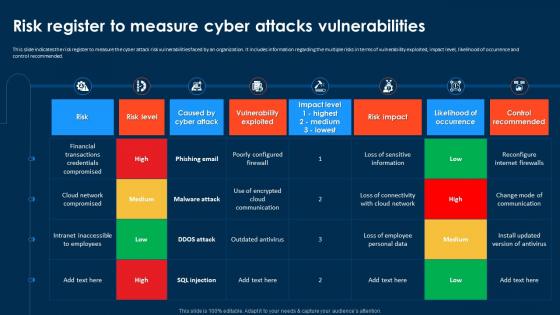 Compressive Planning Guide Risk Register To Measure Cyber Attacks Vulnerabilities
Compressive Planning Guide Risk Register To Measure Cyber Attacks VulnerabilitiesThis slide indicates the risk register to measure the cyber attack risk vulnerabilities faced by an organization. It includes information regarding the multiple risks in terms of vulnerability exploited, impact level, likelihood of occurrence and control recommended. Present the topic in a bit more detail with this Compressive Planning Guide Risk Register To Measure Cyber Attacks Vulnerabilities. Use it as a tool for discussion and navigation on Cyber Attack Risk Vulnerabilities, Vulnerability Exploited, Occurrence And Control Recommended. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
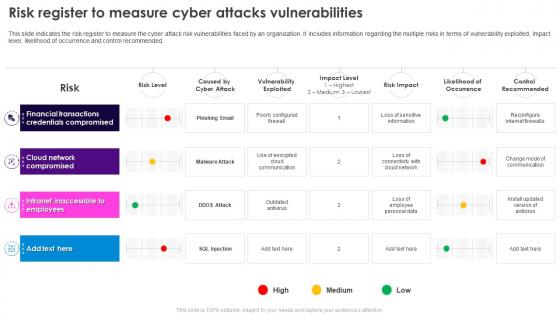 Security Plan To Prevent Cyber Risk Register To Measure Cyber Attacks Vulnerabilities
Security Plan To Prevent Cyber Risk Register To Measure Cyber Attacks VulnerabilitiesThis slide indicates the risk register to measure the cyber attack risk vulnerabilities faced by an organization. It includes information regarding the multiple risks in terms of vulnerability exploited, impact level, likelihood of occurrence and control recommended. Present the topic in a bit more detail with this Security Plan To Prevent Cyber Risk Register To Measure Cyber Attacks Vulnerabilities. Use it as a tool for discussion and navigation on Financial Transactions, Credentials Compromised, Cloud Network, Compromised. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
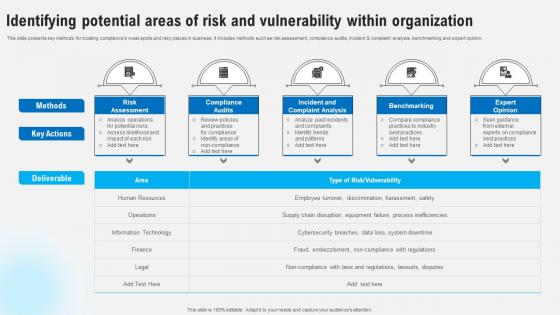 Identifying Potential Areas Of Risk And Vulnerability Within Strategies To Comply Strategy SS V
Identifying Potential Areas Of Risk And Vulnerability Within Strategies To Comply Strategy SS VThis slide presents key methods for locating compliances weak spots and risky places in business. It includes methods such as risk assessment, compliance audits, incident and complaint analysis, benchmarking and expert opinion. Introducing Identifying Potential Areas Of Risk And Vulnerability Within Strategies To Comply Strategy SS V to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Risk Assessment, Compliance Audits, Incident And Complaint Analysis, using this template. Grab it now to reap its full benefits.
-
 Classify Assets Vulnerable To Cyber Attack Implementing Strategies To Mitigate Cyber Security Threats
Classify Assets Vulnerable To Cyber Attack Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide depicts some major assets that are more prone to cyber attack. It mainly includes elements such as sales record, sales lead record, company internal database, customer and product information etc. Present the topic in a bit more detail with this Classify Assets Vulnerable To Cyber Attack Implementing Strategies To Mitigate Cyber Security Threats Use it as a tool for discussion and navigation on Sales Record, Customer Database, Product Database This template is free to edit as deemed fit for your organization. Therefore download it now.
-
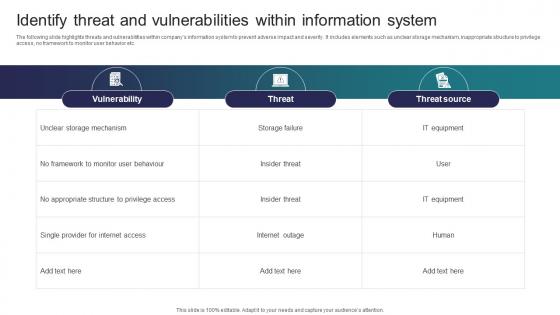 Identify Threat And Vulnerabilities Within Information System Implementing Strategies To Mitigate Cyber Security
Identify Threat And Vulnerabilities Within Information System Implementing Strategies To Mitigate Cyber SecurityThe following slide highlights threats and vulnerabilities within companys information system to prevent adverse impact and severity. It includes elements such as unclear storage mechanism, inappropriate structure to privilege access, no framework to monitor user behavior etc. Deliver an outstanding presentation on the topic using this Identify Threat And Vulnerabilities Within Information System Implementing Strategies To Mitigate Cyber Security Dispense information and present a thorough explanation of Vulnerability, Threat, Threat Source using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 List Of Devices Vulnerable To Hacking Risks
List Of Devices Vulnerable To Hacking RisksThis slide covers devices that are most vulnerable to hacking. The purpose of this slide is to help businesses in limiting chances of device hacking by providing understanding of factors causing vulnerabilities. It covers four major devices such as smart devices, webcams, email and routers.Introducing our premium set of slides with List Of Devices Vulnerable To Hacking Risks Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Inconsistent Software, Attachments Through, Access Computer. So download instantly and tailor it with your information.
-
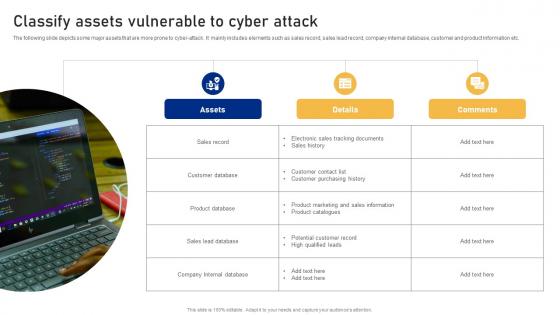 Classify Assets Vulnerable To Cyber Attack Cyber Risk Assessment
Classify Assets Vulnerable To Cyber Attack Cyber Risk AssessmentThe following slide depicts some major assets that are more prone to cyber-attack. It mainly includes elements such as sales record, sales lead record, company internal database, customer and product information etc. Introducing Classify Assets Vulnerable To Cyber Attack Cyber Risk Assessment to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Customer Database, Product Database, Sales Lead Database using this template. Grab it now to reap its full benefits.
-
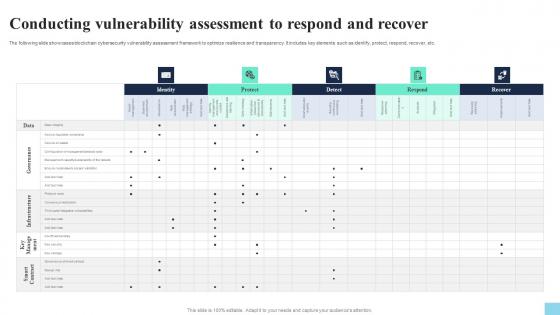 Conducting Vulnerability Assessment To Respond And Recover Hands On Blockchain Security Risk BCT SS V
Conducting Vulnerability Assessment To Respond And Recover Hands On Blockchain Security Risk BCT SS VThe following slide showcases blockchain cybersecurity vulnerability assessment framework to optimize resilience and transparency. It includes key elements such as identify, protect, respond, recover, etc. Present the topic in a bit more detail with this Conducting Vulnerability Assessment To Respond And Recover Hands On Blockchain Security Risk BCT SS V. Use it as a tool for discussion and navigation on Identity, Protect, Detect, Respond. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Classify Assets Vulnerable To Cyber Attack Creating Cyber Security Awareness
Classify Assets Vulnerable To Cyber Attack Creating Cyber Security AwarenessThe following slide depicts some major assets that are more prone to cyber-attack. It mainly includes elements such as sales record, sales lead record, company internal database, customer and product information etc. Introducing Classify Assets Vulnerable To Cyber Attack Creating Cyber Security Awareness to increase your presentation threshold. Encompassed with One stages, this template is a great option to educate and entice your audience. Dispence information on Sales Record, Customer Database, Product Database using this template. Grab it now to reap its full benefits.
-
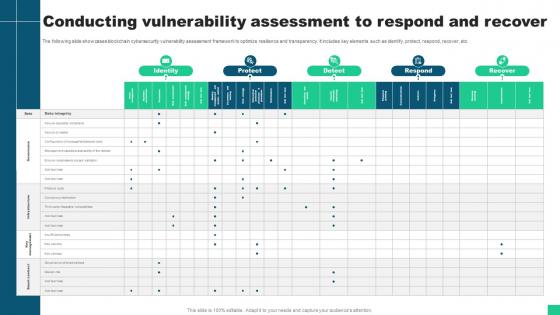 Conducting Vulnerability Assessment To Respond And Recover Guide For Blockchain BCT SS V
Conducting Vulnerability Assessment To Respond And Recover Guide For Blockchain BCT SS VThe following slide showcases blockchain cybersecurity vulnerability assessment framework to optimize resilience and transparency. It includes key elements such as identify, protect, respond, recover, etc. Present the topic in a bit more detail with this Conducting Vulnerability Assessment To Respond And Recover Guide For Blockchain BCT SS V Use it as a tool for discussion and navigation on Identity, Protect, Respond, Recover This template is free to edit as deemed fit for your organization. Therefore download it now.
-
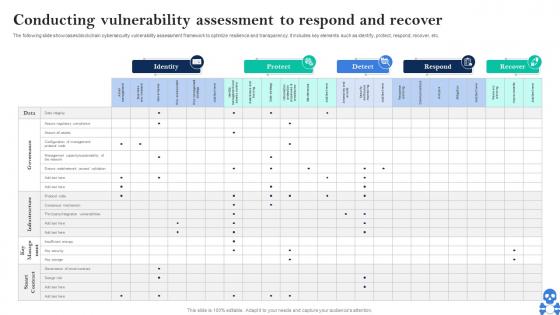 Cyber Threats In Blockchain Conducting Vulnerability Assessment To Respond And Recover BCT SS V
Cyber Threats In Blockchain Conducting Vulnerability Assessment To Respond And Recover BCT SS VThe following slide showcases blockchain cybersecurity vulnerability assessment framework to optimize resilience and transparency. It includes key elements such as identify, protect, respond, recover, etc. Present the topic in a bit more detail with this Cyber Threats In Blockchain Conducting Vulnerability Assessment To Respond And Recover BCT SS V Use it as a tool for discussion and navigation on Identity, Protect, Detect This template is free to edit as deemed fit for your organization. Therefore download it now.
-
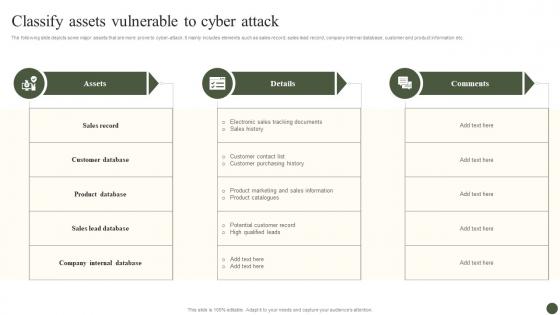 Classify Assets Vulnerable To Cyber Attack Implementing Cyber Risk Management Process
Classify Assets Vulnerable To Cyber Attack Implementing Cyber Risk Management ProcessThe following slide depicts some major assets that are more prone to cyber-attack. It mainly includes elements such as sales record, sales lead record, company internal database, customer and product information etc. Present the topic in a bit more detail with this Classify Assets Vulnerable To Cyber Attack Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Assets, Details, Comments. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Solutions To Overcome Challenges In Effective Vulnerability Management For SAP Systems
Solutions To Overcome Challenges In Effective Vulnerability Management For SAP SystemsThis slide depicts the resolutions to challenges in effective vulnerability management for SAP systems. The purpose of this template is to help the business ensure it can overcome these challenges through the use of given solutions. It includes challenges such as lack of resources and budgets, lack of visibility, etc. Introducing our Solutions To Overcome Challenges In Effective Vulnerability Management For SAP Systems set of slides. The topics discussed in these slides are Lack Of Resources And Budgets, Lack Of Visibility, Determining Start Point. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
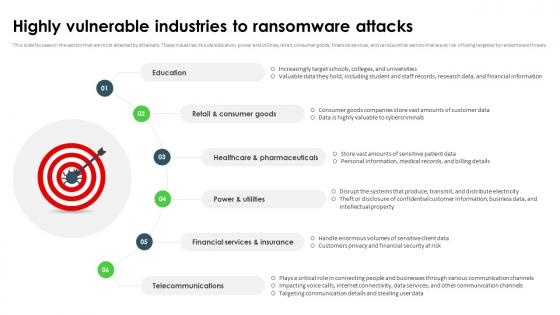 Ransomware In Digital Age Highly Vulnerable Industries To Ransomware Attacks
Ransomware In Digital Age Highly Vulnerable Industries To Ransomware AttacksThis slide focuses on the sectors that are most attacked by attackers. These industries include education, power and utilities, retail, consumer goods, financial services, and various other sectors that are at risk of being targeted by ransomware threats. Increase audience engagement and knowledge by dispensing information using Ransomware In Digital Age Highly Vulnerable Industries To Ransomware Attacks. This template helps you present information on six stages. You can also present information on Retail And Consumer Goods, Healthcare And Pharmaceuticals, Financial Services And Insurance, Telecommunications using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
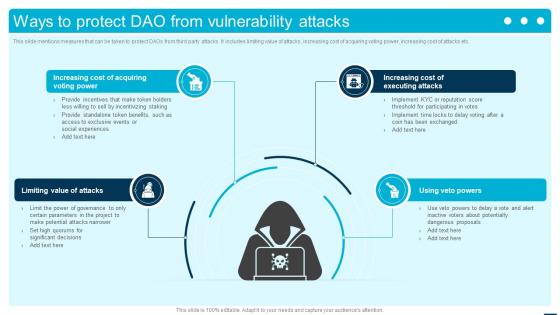 Ways To Protect DAO From Vulnerability Attacks Introduction To Decentralized Autonomous BCT SS
Ways To Protect DAO From Vulnerability Attacks Introduction To Decentralized Autonomous BCT SSThis slide mentions measures that can be taken to protect DAOs from third party attacks. It includes limiting value of attacks, increasing cost of acquiring voting power, increasing cost of attacks etc. Introducing Ways To Protect DAO From Vulnerability Attacks Introduction To Decentralized Autonomous BCT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Limiting Value Of Attacks, Increasing Cost Of Acquiring Voting Power, Increasing Cost Of Executing Attacks, using this template. Grab it now to reap its full benefits.
-
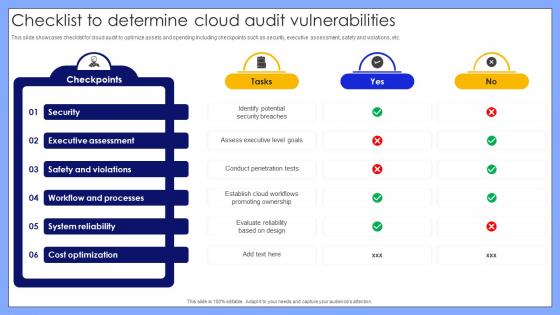 Checklist To Determine Cloud Audit Vulnerabilities
Checklist To Determine Cloud Audit VulnerabilitiesThis slide showcases checklist for cloud audit to optimize assets and spending including checkpoints such as security, executive assessment, safety and violations, etc. Presenting our well structured Checklist To Determine Cloud Audit Vulnerabilities. The topics discussed in this slide are Security, Executive Assessment, Safety And Violations, Workflow And Processes. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Vulnerability Administration At Workplace Statistics Associated To Workplace Threats
Vulnerability Administration At Workplace Statistics Associated To Workplace ThreatsThis slide provides details regarding statistics associated to workplace threats that firms face in terms of data records theft, workplace violence, financial phishing, etc. Present the topic in a bit more detail with this Vulnerability Administration At Workplace Statistics Associated To Workplace Threats. Use it as a tool for discussion and navigation on Cyber Attacks Costs, Organizations, Organizations Have. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
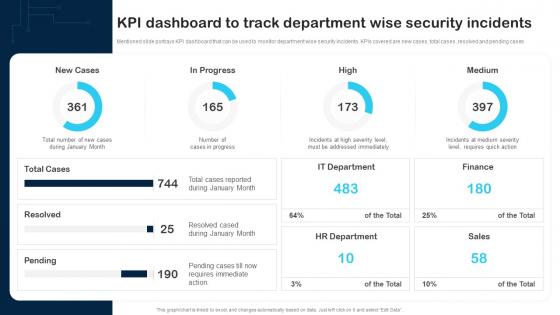 KPI Dashboard To Track Department Wise Security Incidents Cybersecurity Incident And Vulnerability
KPI Dashboard To Track Department Wise Security Incidents Cybersecurity Incident And VulnerabilityMentioned slide portrays KPI dashboard that can be used to monitor department wise security incidents. KPIs covered are new cases, total cases, resolved and pending cases. Present the topic in a bit more detail with this KPI Dashboard To Track Department Wise Security Incidents Cybersecurity Incident And Vulnerability. Use it as a tool for discussion and navigation on New Cases, In Progress, IT Department. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
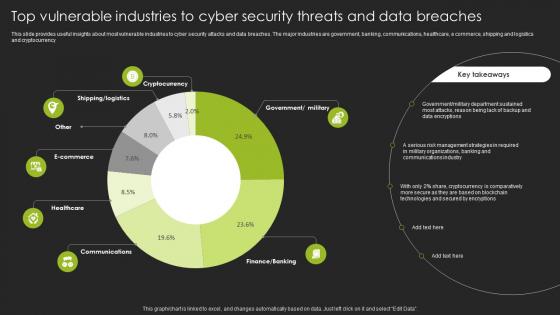 Top Vulnerable Industries To Cyber Security Threats And Data Breaches
Top Vulnerable Industries To Cyber Security Threats And Data BreachesThis slide provides useful insights about most vulnerable industries to cyber security attacks and data breaches. The major industries are government, banking, communications, healthcare, e commerce, shipping and logistics and cryptocurrency Introducing our Top Vulnerable Industries To Cyber Security Threats And Data Breaches set of slides. The topics discussed in these slides are Government, Department. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
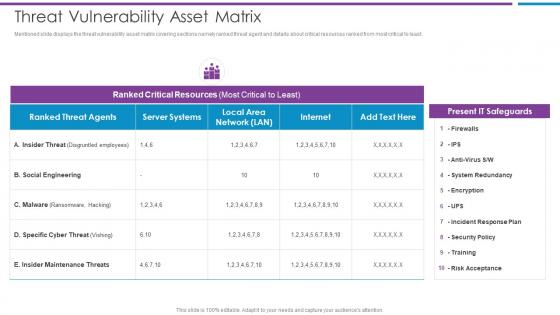 Threat Vulnerability Asset Matrix Risk Based Methodology To Cyber
Threat Vulnerability Asset Matrix Risk Based Methodology To CyberMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least.Present the topic in a bit more detail with this Threat Vulnerability Asset Matrix Risk Based Methodology To Cyber Use it as a tool for discussion and navigation on Social Engineering, Ranked Critical Resources, Present IT Safeguards This template is free to edit as deemed fit for your organization. Therefore download it now.
-
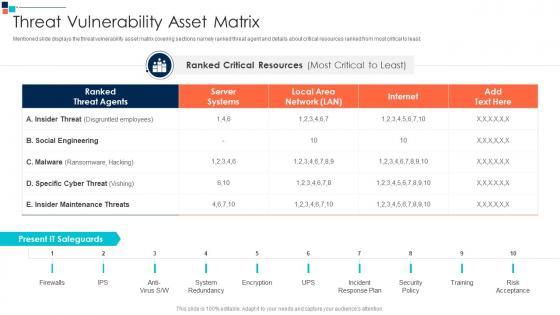 Threat Vulnerability Asset Matrix Introducing A Risk Based Approach To Cyber Security
Threat Vulnerability Asset Matrix Introducing A Risk Based Approach To Cyber SecurityMentioned slide displays the threat vulnerability asset matrix covering sections namely ranked threat agent and details about critical resources ranked from most critical to least.Present the topic in a bit more detail with this Threat Vulnerability Asset Matrix Introducing A Risk Based Approach To Cyber Security Use it as a tool for discussion and navigation on System Redundancy, Incident Response Plan, Security Policy This template is free to edit as deemed fit for your organization. Therefore download it now.
-
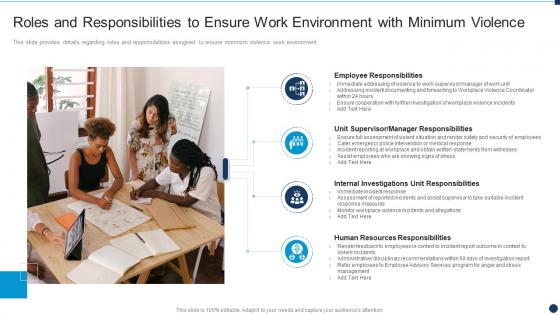 Roles And Responsibilities To Ensure Work Environment Vulnerability Administration Workplace
Roles And Responsibilities To Ensure Work Environment Vulnerability Administration WorkplaceThis slide provides details regarding roles and responsibilities assigned to ensure minimum violence work environment Introducing Roles And Responsibilities To Ensure Work Environment Vulnerability Administration Workplace to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Employee Responsibilities, Manager Responsibilities, Resources Responsibilities, using this template. Grab it now to reap its full benefits.
-
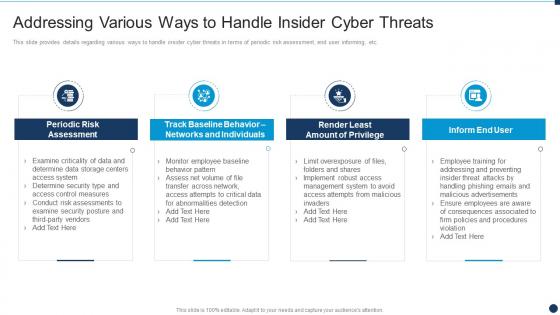 Various Ways To Handle Insider Cyber Threats Vulnerability Administration At Workplace
Various Ways To Handle Insider Cyber Threats Vulnerability Administration At WorkplaceThis slide provides details regarding various ways to handle insider cyber threats in terms of periodic risk assessment, end user informing, etc. Present the topic in a bit more detail with this Various Ways To Handle Insider Cyber Threats Vulnerability Administration At Workplace. Use it as a tool for discussion and navigation on Assessment, Individuals, Management This template is free to edit as deemed fit for your organization. Therefore download it now.
-
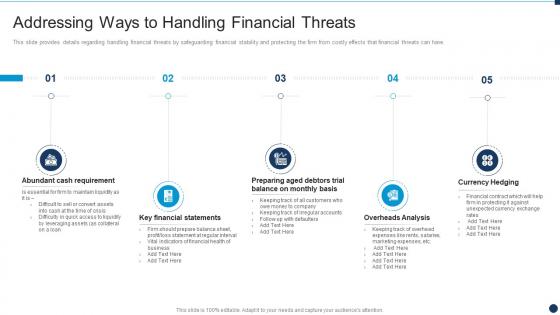 Vulnerability Administration At Workplace Addressing Ways To Handling Financial Threats
Vulnerability Administration At Workplace Addressing Ways To Handling Financial ThreatsThis slide provides details regarding handling financial threats by safeguarding financial stability and protecting the firm from costly effects that financial threats can have. Increase audience engagement and knowledge by dispensing information using Vulnerability Administration At Workplace Addressing Ways To Handling Financial Threats. This template helps you present information on five stages. You can also present information on Requirement, Financial, Statements using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
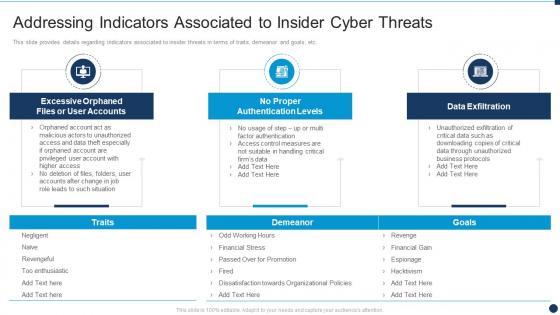 Vulnerability Administration At Workplace Indicators Associated To Insider Cyber Threats
Vulnerability Administration At Workplace Indicators Associated To Insider Cyber ThreatsThis slide provides details regarding indicators associated to insider threats in terms of traits, demeanor and goals, etc. Present the topic in a bit more detail with this Vulnerability Administration At Workplace Indicators Associated To Insider Cyber Threats. Use it as a tool for discussion and navigation on Associated, Authentication, Data Exfiltration . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Vulnerability Administration At Workplace Key Activities Checklist Associated To Insider Threat Program
Vulnerability Administration At Workplace Key Activities Checklist Associated To Insider Threat ProgramThis slide provides details regarding checklist associated to insider threat program in terms of plan and collect, review and analyze and strategic framework development. Deliver an outstanding presentation on the topic using this Vulnerability Administration At Workplace Key Activities Checklist Associated To Insider Threat Program. Dispense information and present a thorough explanation of Processes, Effectiveness, Review And Analyze using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
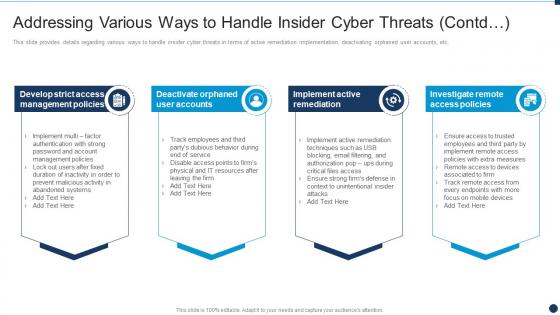 Vulnerability Administration At Workplace Various Ways To Handle Insider Cyber Threats Contd
Vulnerability Administration At Workplace Various Ways To Handle Insider Cyber Threats ContdThis slide provides details regarding various ways to handle insider cyber threats in terms of active remediation implementation, deactivating orphaned user accounts, etc. Increase audience engagement and knowledge by dispensing information using Vulnerability Administration At Workplace Various Ways To Handle Insider Cyber Threats Contd. This template helps you present information on four stages. You can also present information on Management Policies, Remediation, Investigate Remote using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
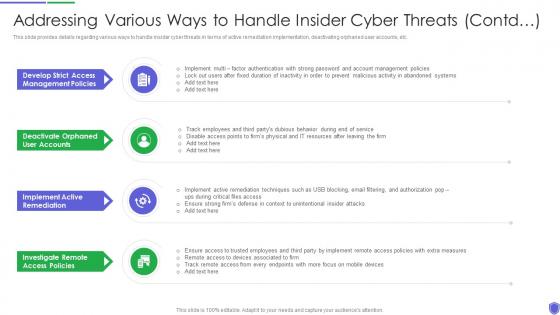 Addressing various ways to managing critical threat vulnerabilities and security threats
Addressing various ways to managing critical threat vulnerabilities and security threatsThis slide provides details regarding various ways to handle insider cyber threats in terms of active remediation implementation, deactivating orphaned user accounts, etc. Increase audience engagement and knowledge by dispensing information using Addressing Various Ways To Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on four stages. You can also present information on Management Policies, User Accounts, Active Remediation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
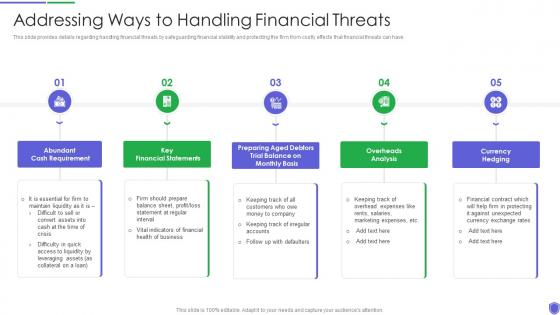 Addressing ways to handling managing critical threat vulnerabilities and security threats
Addressing ways to handling managing critical threat vulnerabilities and security threatsThis slide provides details regarding handling financial threats by safeguarding financial stability and protecting the firm from costly effects that financial threats can have. Introducing Addressing Ways To Handling Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Cash Requirement, Financial Statements, Overheads Analysis, Currency Hedging, using this template. Grab it now to reap its full benefits.
-
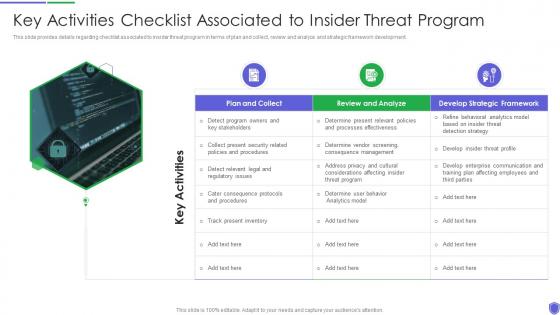 Key activities checklist associated to managing critical threat vulnerabilities and security threats
Key activities checklist associated to managing critical threat vulnerabilities and security threatsThis slide provides details regarding checklist associated to insider threat program in terms of plan and collect, review and analyze and strategic framework development. Introducing Key Activities Checklist Associated To Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Plan And Collect, Review And Analyze, Develop Strategic Framework, using this template. Grab it now to reap its full benefits.
-
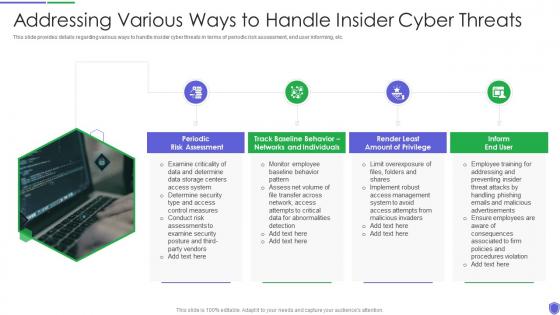 Managing critical threat vulnerabilities and security threats addressing various ways to handle
Managing critical threat vulnerabilities and security threats addressing various ways to handleThis slide provides details regarding various ways to handle insider cyber threats in terms of periodic risk assessment, end user informing, etc. Increase audience engagement and knowledge by dispensing information using Managing Critical Threat Vulnerabilities And Security Threats Addressing Various Ways To Handle. This template helps you present information on four stages. You can also present information on Risk Assessment, End User, Networks And Individuals using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
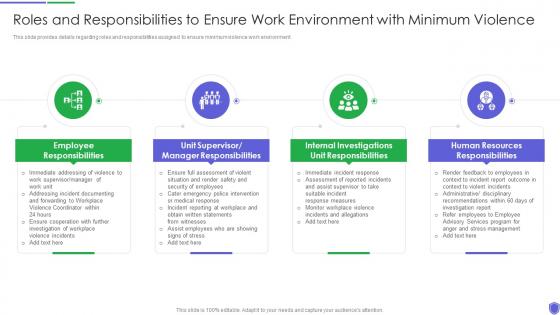 Roles and responsibilities to managing critical threat vulnerabilities and security threats
Roles and responsibilities to managing critical threat vulnerabilities and security threatsThis slide provides details regarding roles and responsibilities assigned to ensure minimum violence work environment. Introducing Roles And Responsibilities To Managing Critical Threat Vulnerabilities And Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Employee Responsibilities, Manager Responsibilities, Unit Responsibilities, Human Resources Responsibilities, using this template. Grab it now to reap its full benefits.
-
 Statistics associated to workplace managing critical threat vulnerabilities and security threats
Statistics associated to workplace managing critical threat vulnerabilities and security threatsThis slide provides details regarding statistics associated to workplace threats that firms face in terms of data records theft, workplace violence, financial phishing, etc. Increase audience engagement and knowledge by dispensing information using Statistics Associated To Workplace Managing Critical Threat Vulnerabilities And Security Threats. This template helps you present information on five stages. You can also present information on Cyber Attacks Cost, Organizations Face, Data Records using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
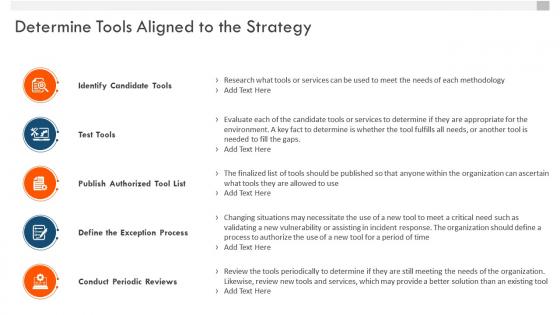 Vulnerability management whitepaper determine tools aligned to the strategy
Vulnerability management whitepaper determine tools aligned to the strategyIntroducing Vulnerability Management Whitepaper Determine Tools Aligned To The Strategy to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Identify Candidate Tools, Test Tools, Publish Authorized Tool List, Define The Exception Process, Conduct Periodic Reviews, using this template. Grab it now to reap its full benefits.
-
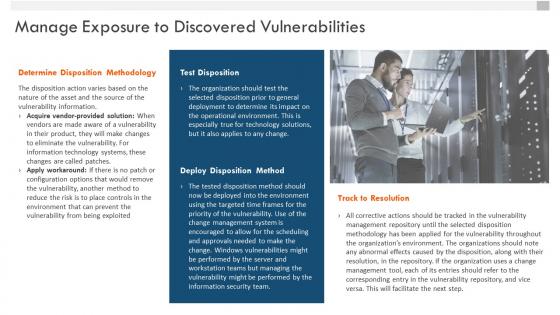 Vulnerability management whitepaper manage exposure to discovered vulnerabilities
Vulnerability management whitepaper manage exposure to discovered vulnerabilitiesIncrease audience engagement and knowledge by dispensing information using Vulnerability Management Whitepaper Manage Exposure To Discovered Vulnerabilities. This template helps you present information on one stages. You can also present information on Determine Disposition Methodology, Track To Resolution, Technology using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
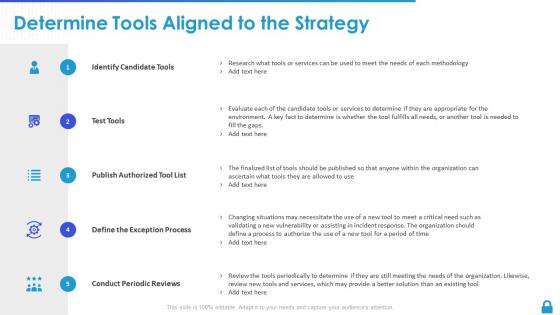 Enterprise vulnerability management determine tools aligned to the strategy
Enterprise vulnerability management determine tools aligned to the strategyIncrease audience engagement and knowledge by dispensing information using Enterprise Vulnerability Management Determine Tools Aligned To The Strategy. This template helps you present information on five stages. You can also present information on Publish Authorized, Exception Process, Conduct Periodic Reviews using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Enterprise vulnerability management manage exposure to discovered vulnerabilities
Enterprise vulnerability management manage exposure to discovered vulnerabilitiesIncrease audience engagement and knowledge by dispensing information using Enterprise Vulnerability Management Manage Exposure To Discovered Vulnerabilities This template helps you present information on four stages. You can also present information on Test Disposition, Deploy Disposition Method, Track To Resolution using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
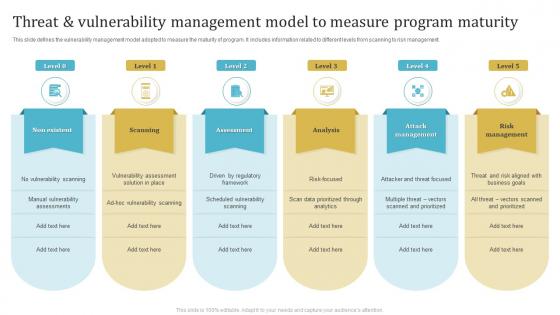 Threat And Vulnerability Management Model To Measure Program Maturity
Threat And Vulnerability Management Model To Measure Program MaturityThis slide defines the vulnerability management model adopted to measure the maturity of program. It includes information related to different levels from scanning to risk management. Introducing our premium set of slides with Threat And Vulnerability Management Model To Measure Program Maturity. Ellicudate the six stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Non Existent, Scanning, Assessment. So download instantly and tailor it with your information.
-
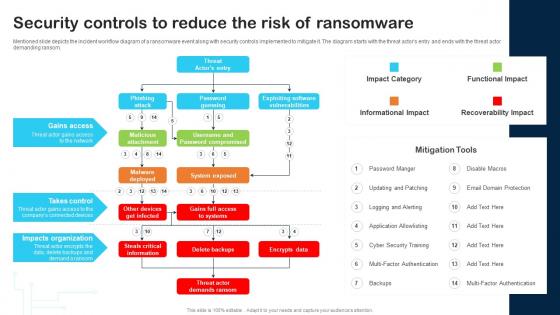 Security Controls To Reduce The Risk Of Ransomware Cybersecurity Incident And Vulnerability
Security Controls To Reduce The Risk Of Ransomware Cybersecurity Incident And VulnerabilityMentioned slide depicts the incident workflow diagram of a ransomware event along with security controls implemented to mitigate it. The diagram starts with the threat actors entry and ends with the threat actor demanding ransom. Deliver an outstanding presentation on the topic using this Security Controls To Reduce The Risk Of Ransomware Cybersecurity Incident And Vulnerability. Dispense information and present a thorough explanation of Gains Access, Takes Control, Impacts Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Food Fraud Mitigation Plan Development To Remove Vulnerability
Food Fraud Mitigation Plan Development To Remove VulnerabilityThis slide provide information about procedure to formulate food fraud mitigation plan to remove vulnerability. It includes elements such as pre-screening, vulnerability assessment, impact assessment, overall risk assessment etc. Presenting our set of slides with Food Fraud Mitigation Plan Development To Remove Vulnerability. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Pre Screening, Vulnerability Assessment, Impact Assessment, Overall Risk Assessment.
-
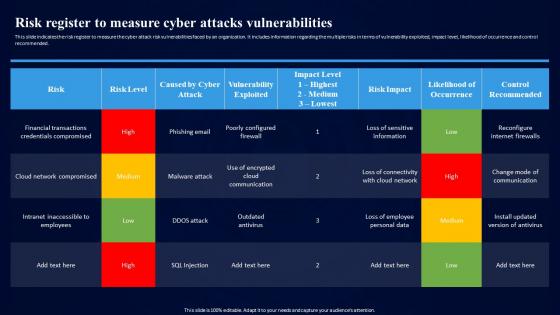 Cybersecurity Risk Assessment Program Risk Register To Measure Cyber Attacks Vulnerabilities
Cybersecurity Risk Assessment Program Risk Register To Measure Cyber Attacks VulnerabilitiesThis slide indicates the risk register to measure the cyber attack risk vulnerabilities faced by an organization. It includes information regarding the multiple risks in terms of vulnerability exploited, impact level, likelihood of occurrence and control recommended. Present the topic in a bit more detail with this Cybersecurity Risk Assessment Program Risk Register To Measure Cyber Attacks Vulnerabilities. Use it as a tool for discussion and navigation on Cyber Attacks, Vulnerabilities, Cloud Network Compromised, Outdated Antivirus. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
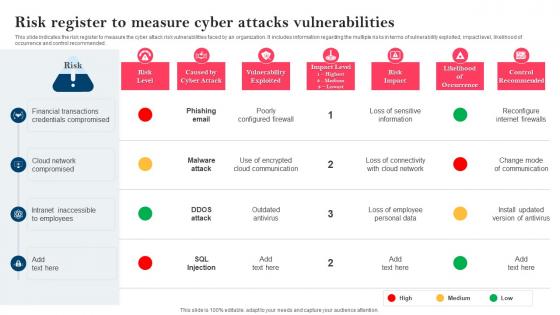 Strategy To Minimize Cyber Attacks Risk Register To Measure Cyber Attacks Vulnerabilities
Strategy To Minimize Cyber Attacks Risk Register To Measure Cyber Attacks VulnerabilitiesThis slide indicates the risk register to measure the cyber attack risk vulnerabilities faced by an organization. It includes information regarding the multiple risks in terms of vulnerability exploited, impact level, likelihood of occurrence and control recommended. Deliver an outstanding presentation on the topic using this Strategy To Minimize Cyber Attacks Risk Register To Measure Cyber Attacks Vulnerabilities. Dispense information and present a thorough explanation of Financial Transactions, Credentials Compromised, Cloud Network Compromised using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
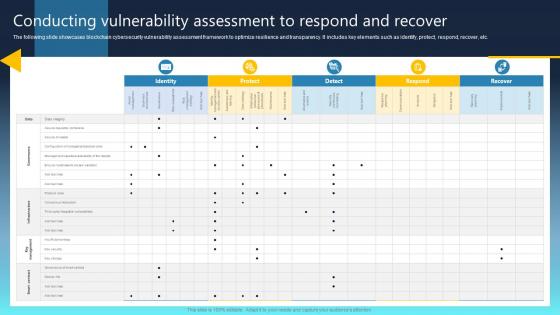 Ultimate Guide For Blockchain Conducting Vulnerability Assessment To Respond And Recover BCT SS
Ultimate Guide For Blockchain Conducting Vulnerability Assessment To Respond And Recover BCT SSPresent the topic in a bit more detail with this Ultimate Guide For Blockchain Conducting Vulnerability Assessment To Respond And Recover BCT SS Use it as a tool for discussion and navigation on Protect, Detect, Detect This template is free to edit as deemed fit for your organization. Therefore download it now.
-
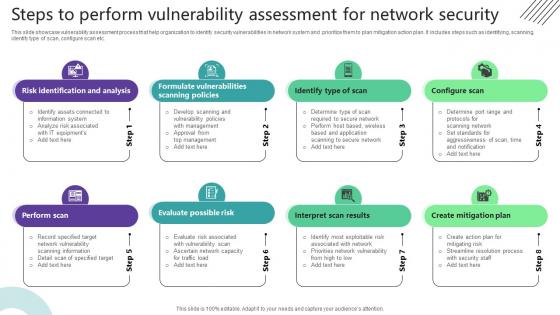 Steps To Perform Vulnerability Assessment For Network Security
Steps To Perform Vulnerability Assessment For Network SecurityThis slide showcase vulnerability assessment process that help organization to identify security vulnerabilities in network system and prioritize them to plan mitigation action plan. It includes steps such as identifying, scanning, identify type of scan, configure scan etc. Introducing our premium set of slides with Steps To Perform Vulnerability Assessment For Network Security. Ellicudate the Four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Risk Identification And Analysis, Identify Type Of Scan, Configure Scan. So download instantly and tailor it with your information.
-
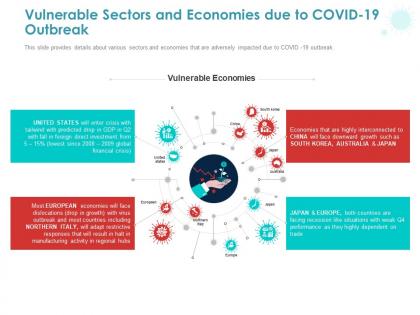 Vulnerable sectors and economies due to covid 19 outbreak ppt powerpoint presentation styles deck
Vulnerable sectors and economies due to covid 19 outbreak ppt powerpoint presentation styles deckThis slide provides details about various sectors and economies that are adversely impacted due to COVID -19 outbreak. Presenting this set of slides with name Vulnerable Sectors And Economies Due To COVID 19 Outbreak Ppt Powerpoint Presentation Styles Deck. The topics discussed in these slide is Vulnerable Economies. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Vulnerable sectors and economies due to covid 19 outbreak social ppt powerpoint presentation inspiration
Vulnerable sectors and economies due to covid 19 outbreak social ppt powerpoint presentation inspirationThis slide provides details about various sectors and economies that are adversely impacted due to COVID-19 outbreak. Presenting this set of slides with name Vulnerable Sectors And Economies Due To COVID 19 Outbreak Social Ppt Powerpoint Presentation Inspiration. This is a six stage process. The stages in this process are Travel And Tourism, Aviation, Entertainment, Restaurant And Hotel, Agriculture, Vulnerable Sectors. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Job vulnerability by income level due to disruption in employee productivity ppt demonstration
Job vulnerability by income level due to disruption in employee productivity ppt demonstrationThe following slide displays the vulnerability of job in automobile sector by income band and annual income. Presenting this set of slides with name Job Vulnerability By Income Level Due To Disruption In Employee Productivity Ppt Demonstration. The topics discussed in these slides are Job Vulnerability By Income Level Due To Disruption In Employee Productivity. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
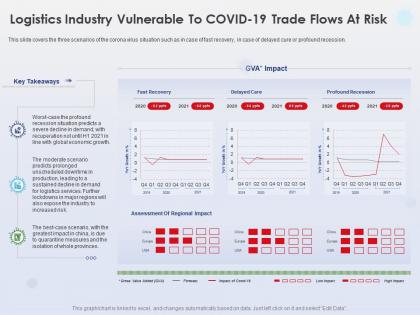 Logistics industry vulnerable to covid 19 trade profound recession ppt powerpoint pictures
Logistics industry vulnerable to covid 19 trade profound recession ppt powerpoint picturesThis slide covers the three scenarios of the corona virus situation such as in case of fast recovery, in case of delayed cure or profound recession. Presenting this set of slides with name Logistics Industry Vulnerable To Covid 19 Trade Profound Recession Ppt Powerpoint Pictures. The topics discussed in these slides are Logistics Industry, Vulnerable Covid 19, Trade Profound, Recession. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Scanning system for vulnerability to cyber attack
Scanning system for vulnerability to cyber attackPresenting this set of slides with name Scanning System For Vulnerability To Cyber Attack. This is a three stage process. The stages in this process are Scanning System For Vulnerability To Cyber Attack. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Vulnerability scanning of website to detect malware attack
Vulnerability scanning of website to detect malware attackPresenting this set of slides with name Vulnerability Scanning Of Website To Detect Malware Attack. The topics discussed in these slides is Vulnerability Scanning Of Website To Detect Malware Attack. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
 Vulnerability scanning to detect broken it network link
Vulnerability scanning to detect broken it network linkPresenting this set of slides with name Vulnerability Scanning To Detect Broken IT Network Link. The topics discussed in these slides is Vulnerability Scanning To Detect Broken IT Network Link. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
-
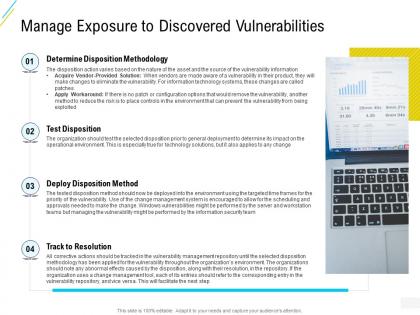 Organization risk probability management manage exposure to discovered vulnerabilities ppt template
Organization risk probability management manage exposure to discovered vulnerabilities ppt templateIncrease audience engagement and knowledge by dispensing information using Organization Risk Probability Management Manage Exposure To Discovered Vulnerabilities Ppt Template. This template helps you present information on four stages. You can also present information on Manage, Determine, Disposition, Resolution, Vulnerabilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Enhanced security event management secops dashboard to track vulnerabilities ppt powerpoint slide
Enhanced security event management secops dashboard to track vulnerabilities ppt powerpoint slideThis slide provides information regarding the SecOps dashboard which is used to track and monitor various vulnerabilities identified. Present the topic in a bit more detail with this Enhanced Security Event Management Secops Dashboard To Track Vulnerabilities Ppt Powerpoint Slide. Use it as a tool for discussion and navigation on Assets, Vulnerabilities, Severity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
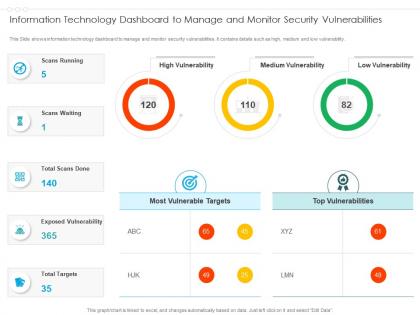 Information technology dashboard to manage and monitor security vulnerabilities
Information technology dashboard to manage and monitor security vulnerabilitiesPresenting our well structured Information Technology Dashboard To Manage And Monitor Security Vulnerabilities. The topics discussed in this slide are Information Technology Dashboard To Manage And Monitor Security Vulnerabilities. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
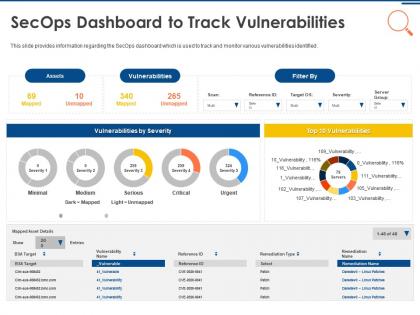 It security operations secops dashboard to track vulnerabilities ppt powerpoint gallery outfit
It security operations secops dashboard to track vulnerabilities ppt powerpoint gallery outfitThis slide provides information regarding the SecOps dashboard which is used to track and monitor various vulnerabilities identified. Present the topic in a bit more detail with this IT Security Operations Secops Dashboard To Track Vulnerabilities Ppt Powerpoint Gallery Outfit. Use it as a tool for discussion and navigation on Assets, Vulnerabilities, Severity. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
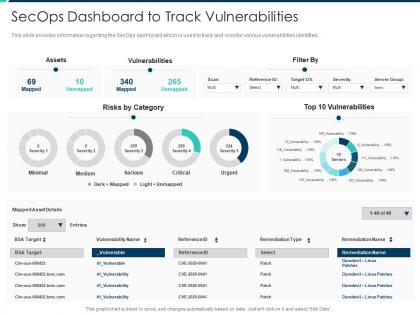 Secops dashboard to track vulnerabilities security operations integration ppt icons
Secops dashboard to track vulnerabilities security operations integration ppt iconsThis slide provides information regarding the SecOps dashboard which is used to track and monitor various vulnerabilities identified. Present the topic in a bit more detail with this Secops Dashboard To Track Vulnerabilities Security Operations Integration Ppt Icons. Use it as a tool for discussion and navigation on Secops Dashboard To Track Vulnerabilities. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
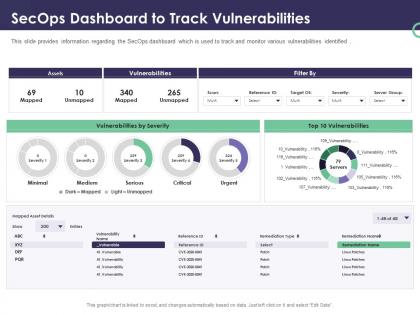 Enterprise security operations secops dashboard to track vulnerabilities ppt powerpoint templates
Enterprise security operations secops dashboard to track vulnerabilities ppt powerpoint templatesThis slide provides information regarding the SecOps dashboard which is used to track and monitor various vulnerabilities identified. Present the topic in a bit more detail with this Enterprise Security Operations Secops Dashboard To Track Vulnerabilities Ppt Powerpoint Templates. Use it as a tool for discussion and navigation on Assets, Vulnerabilities, Severity. This template is free to edit as deemed fit for your organization. Therefore download it now.

