Cloud security it powerpoint presentation slides
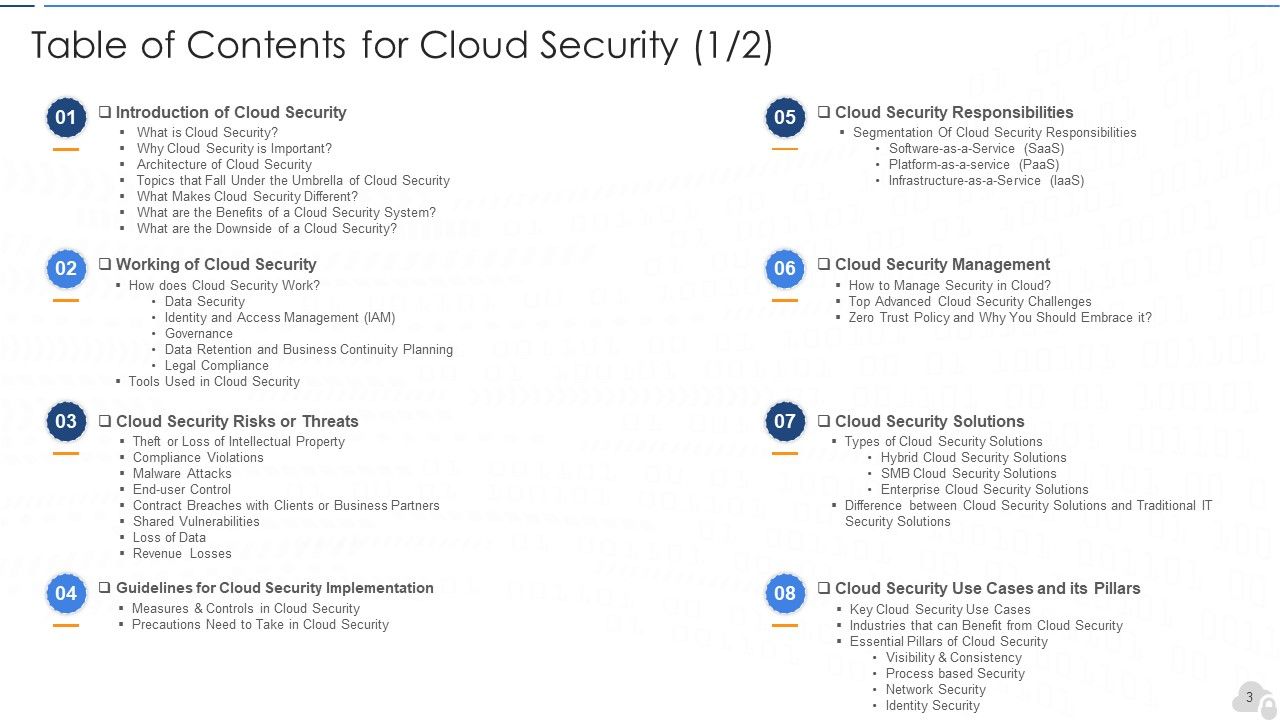
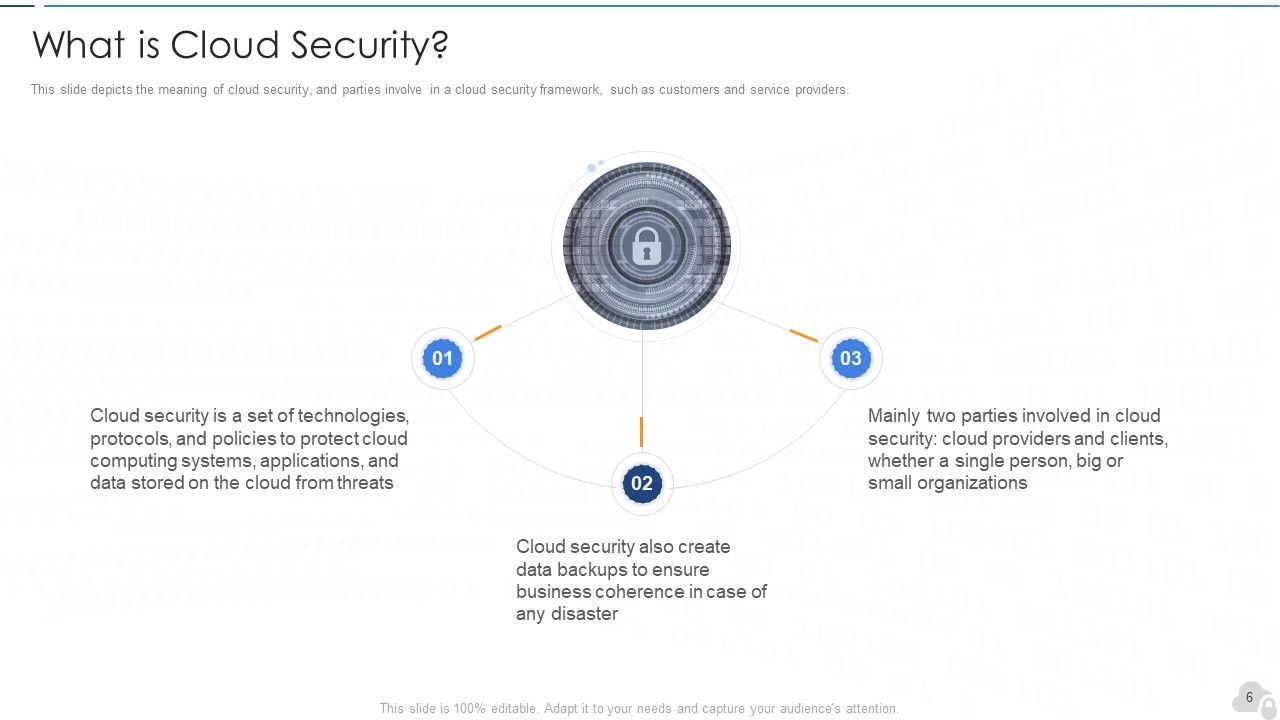
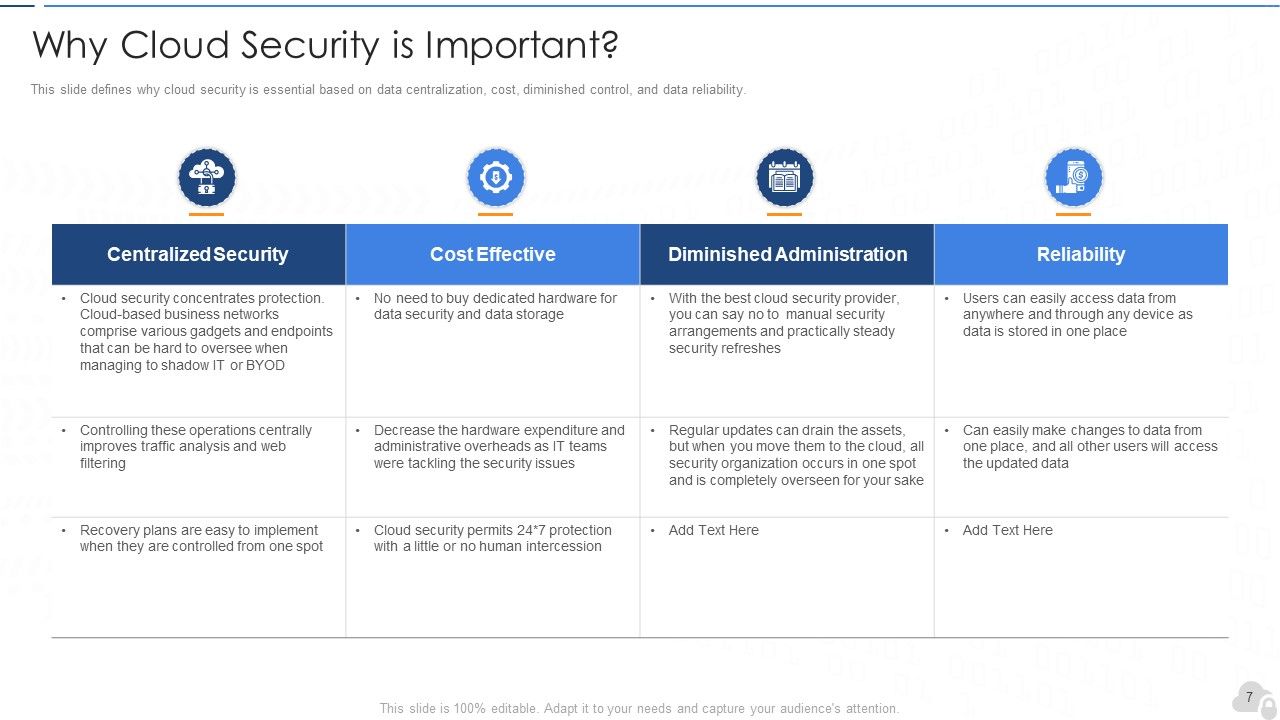
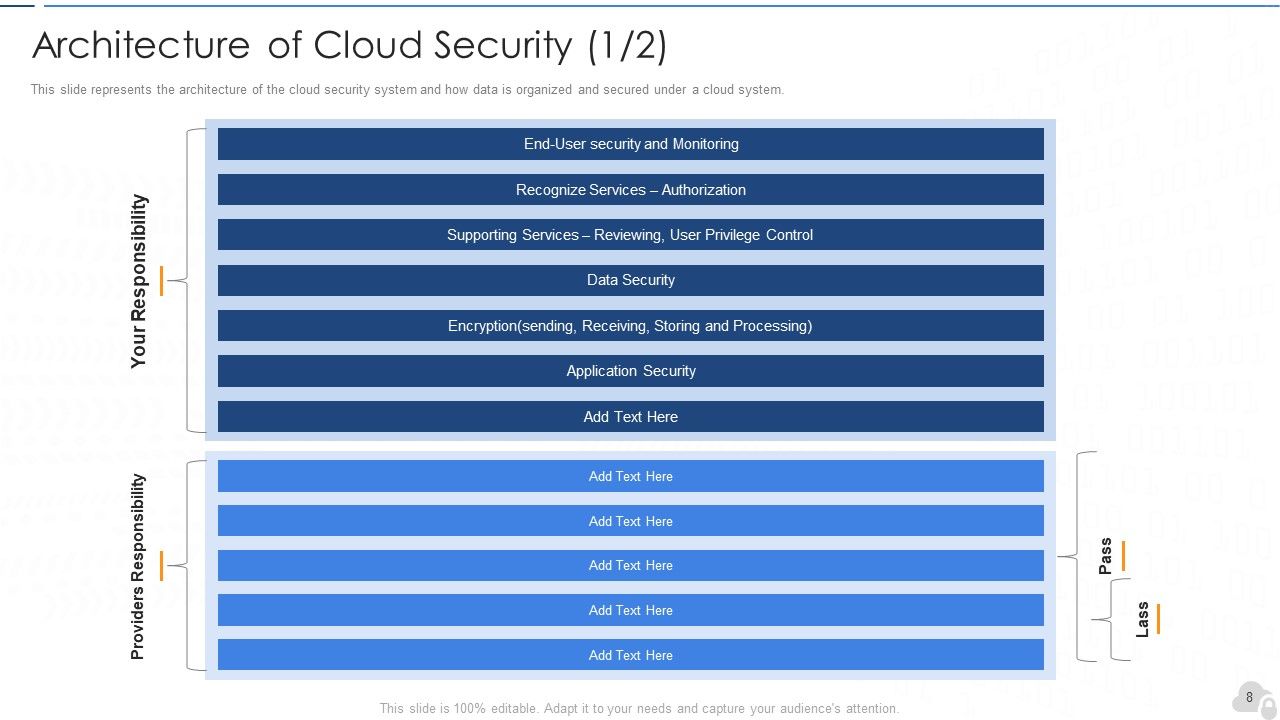
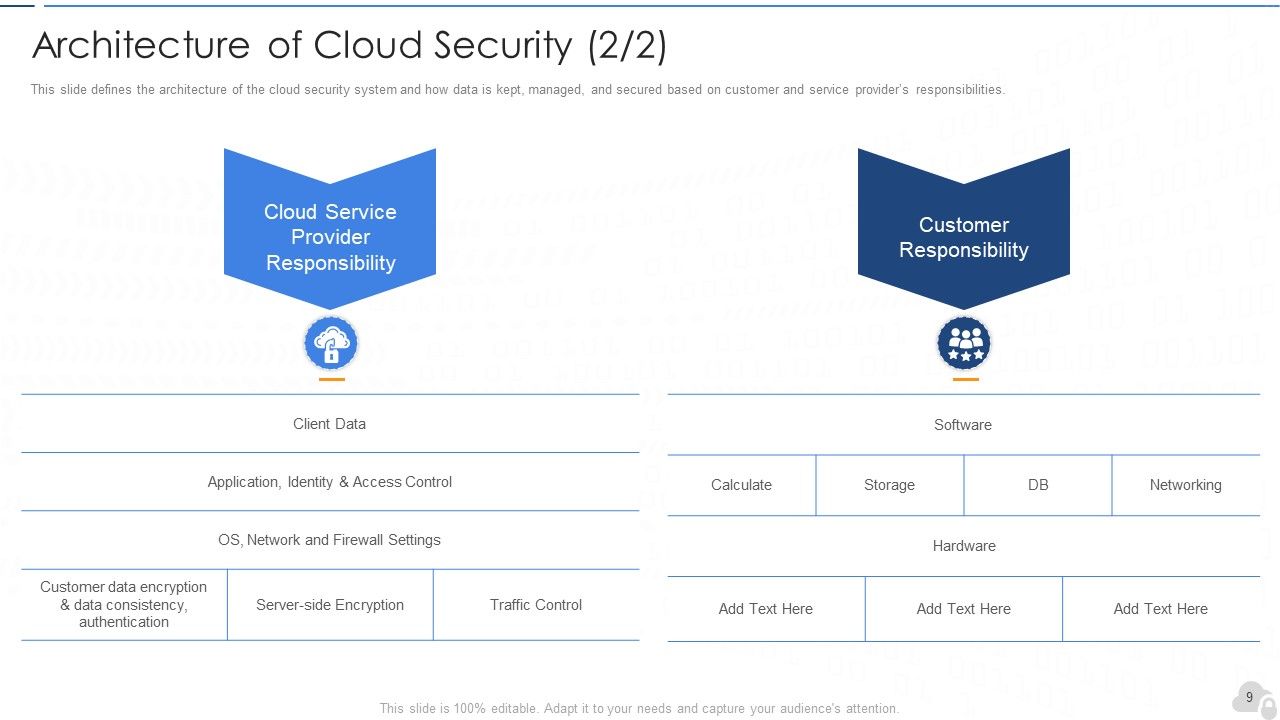
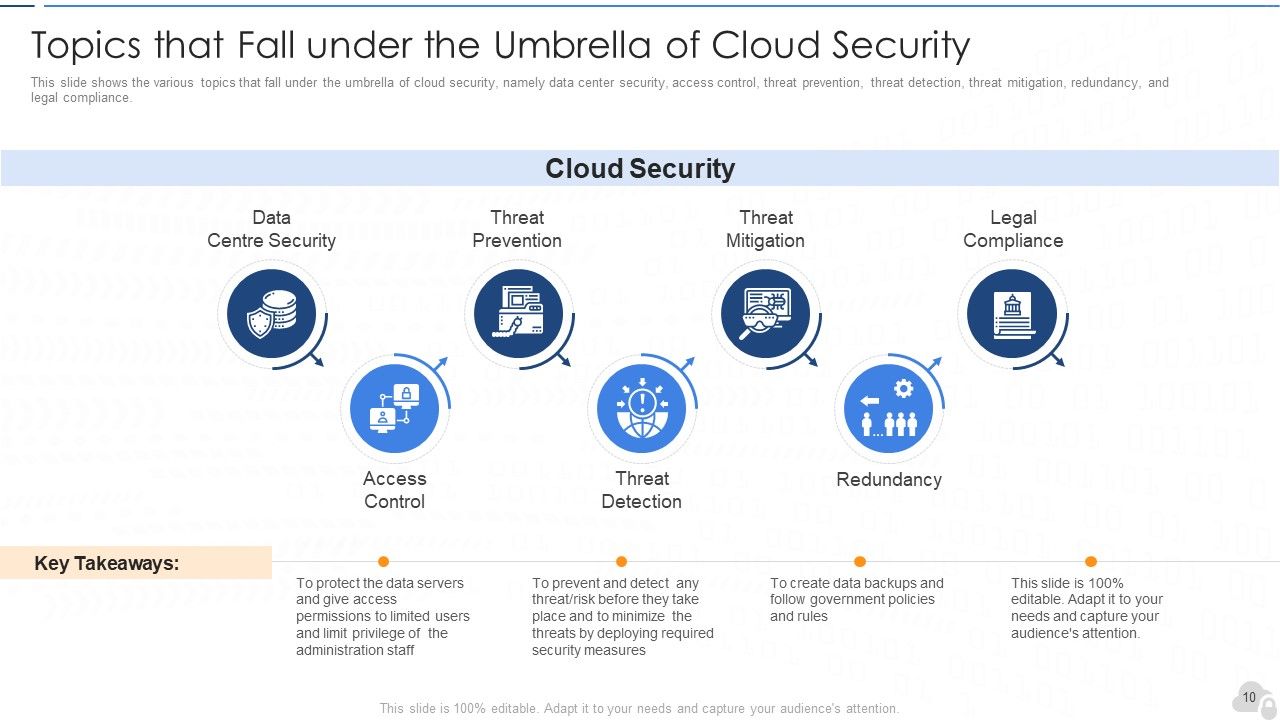
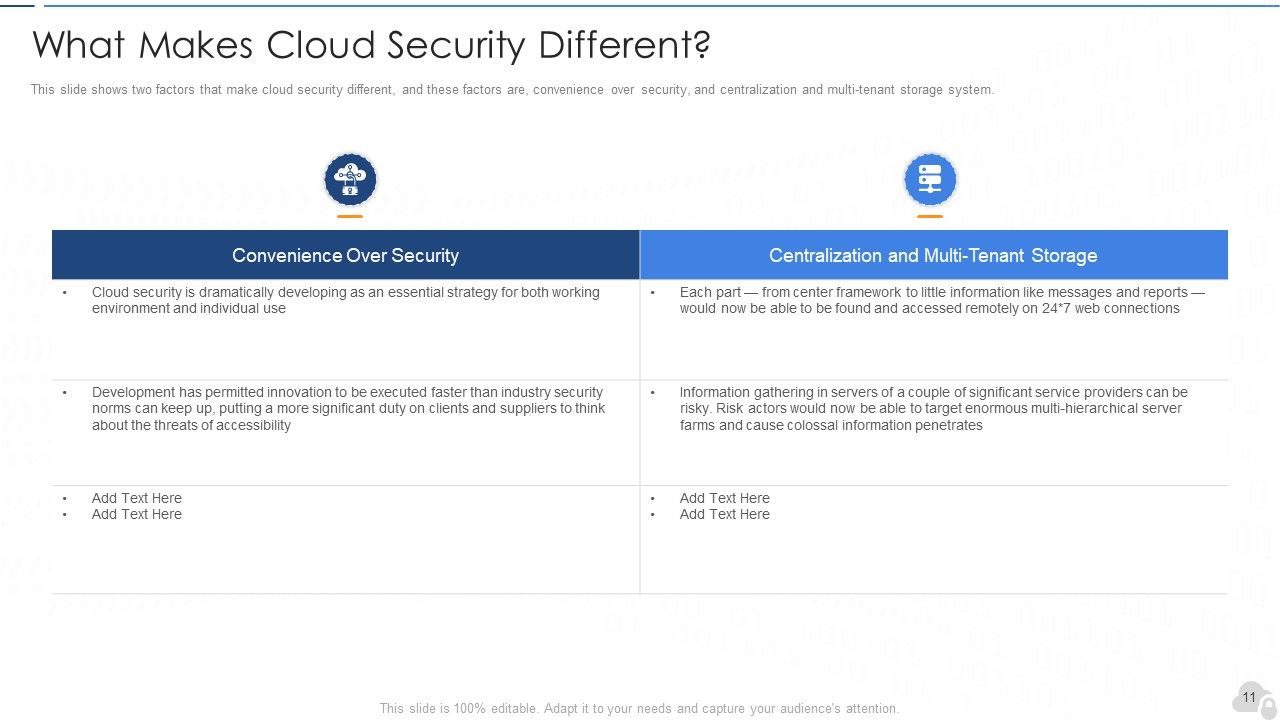
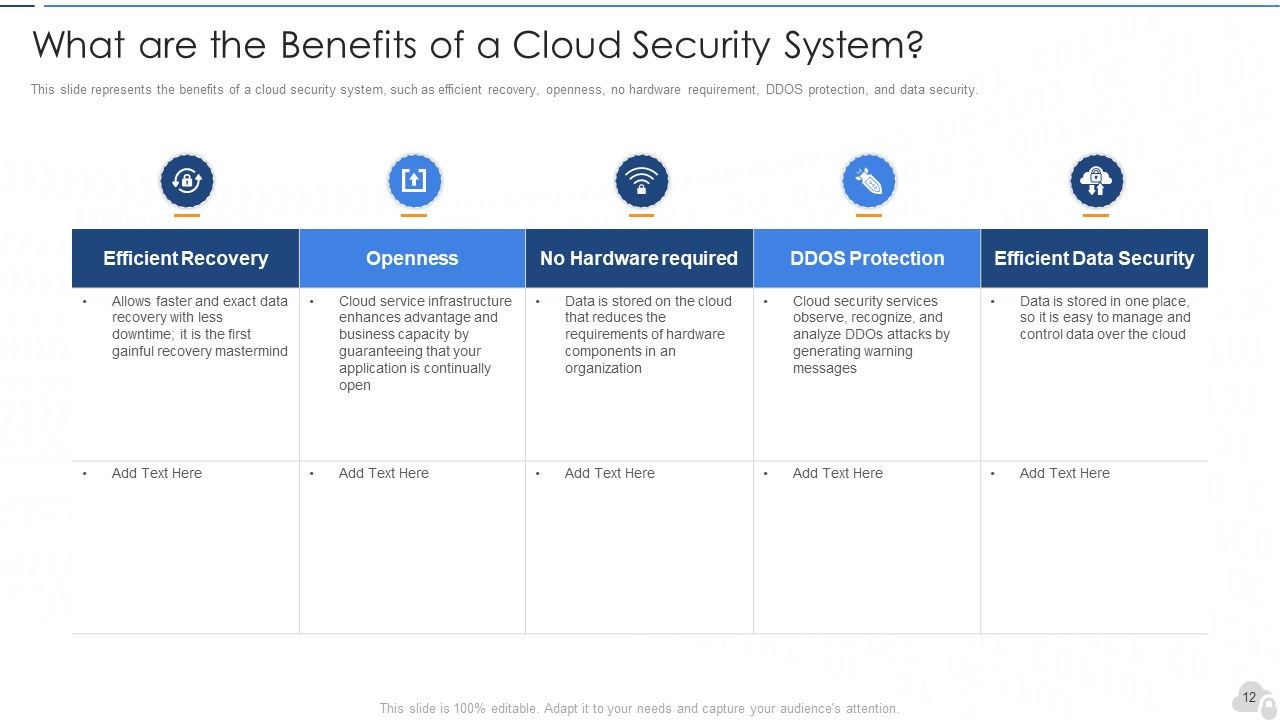
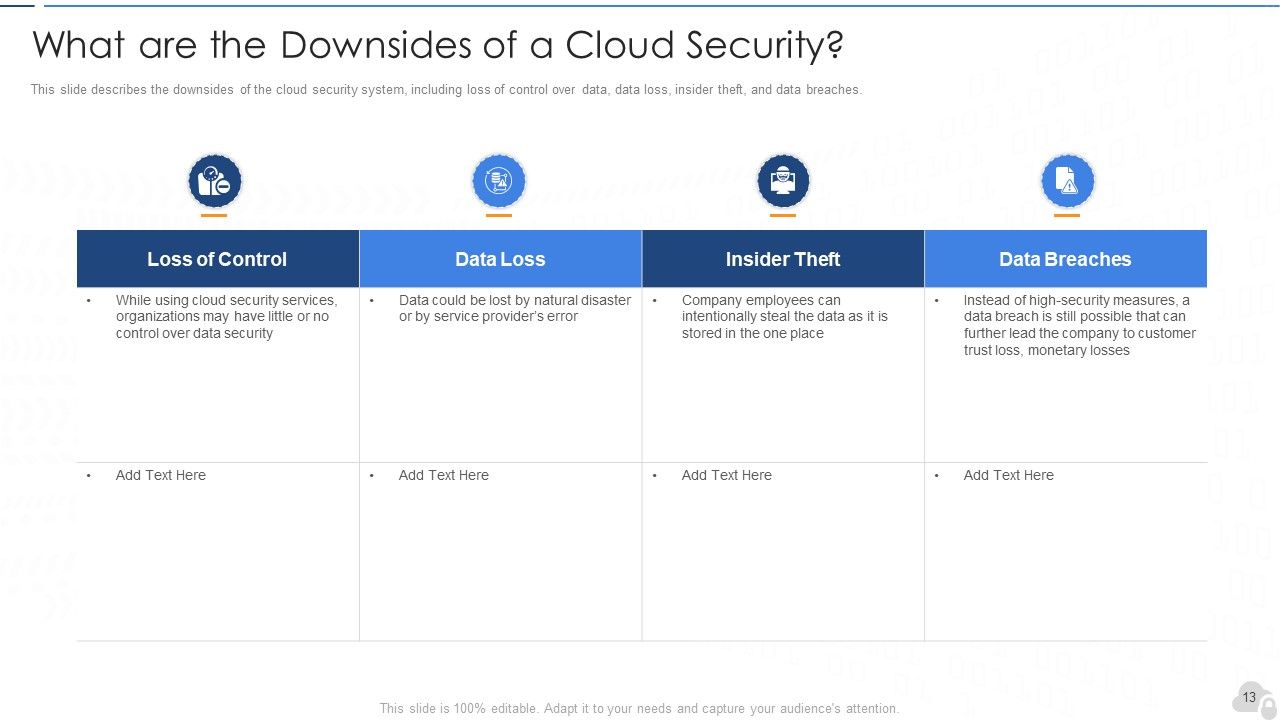
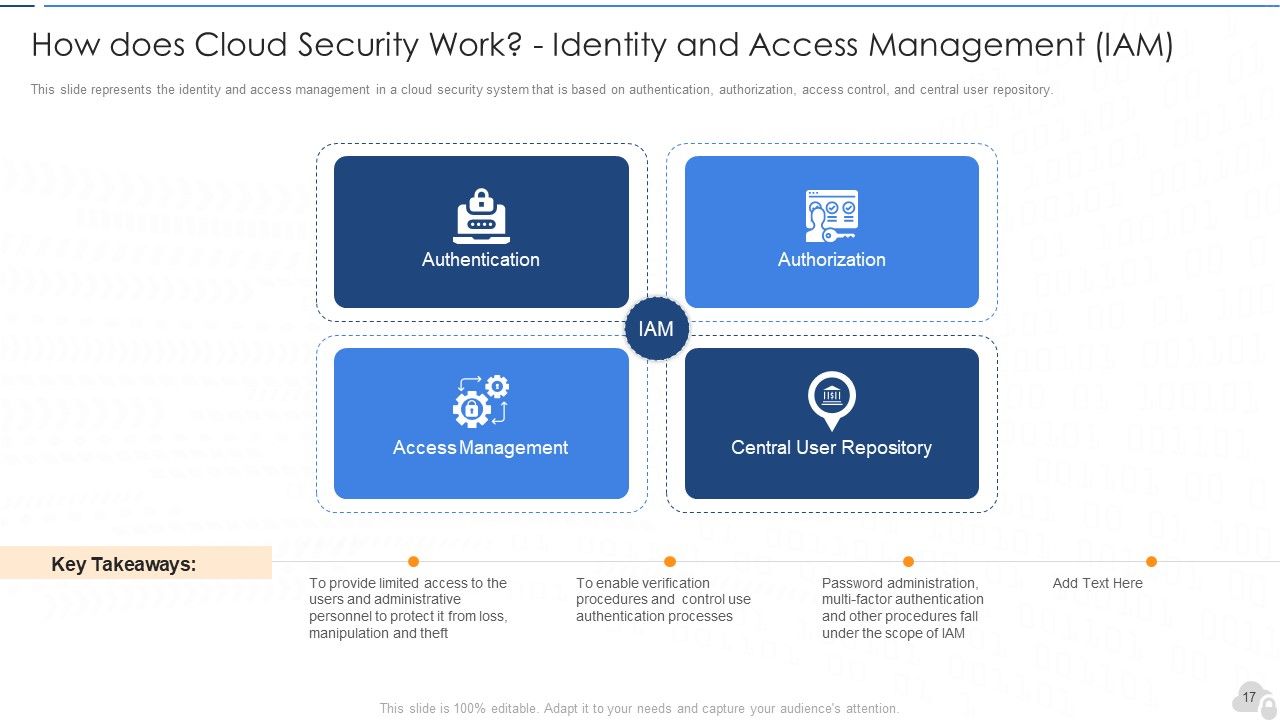
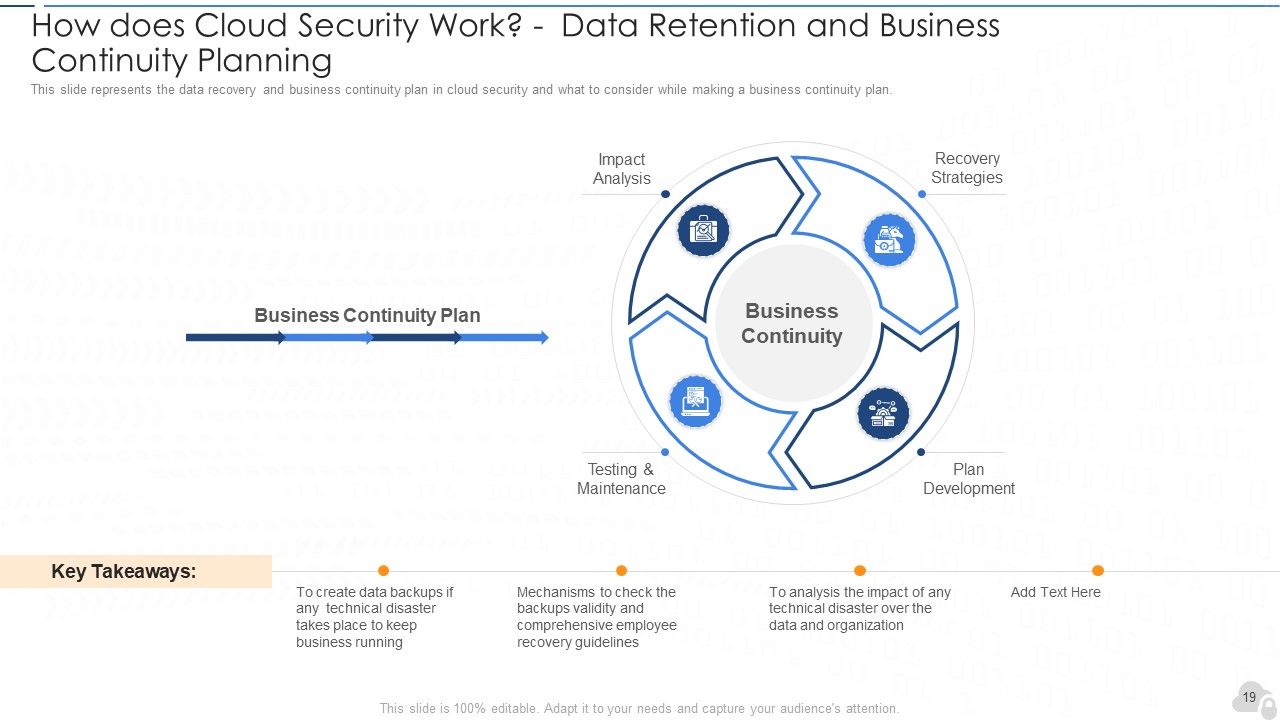
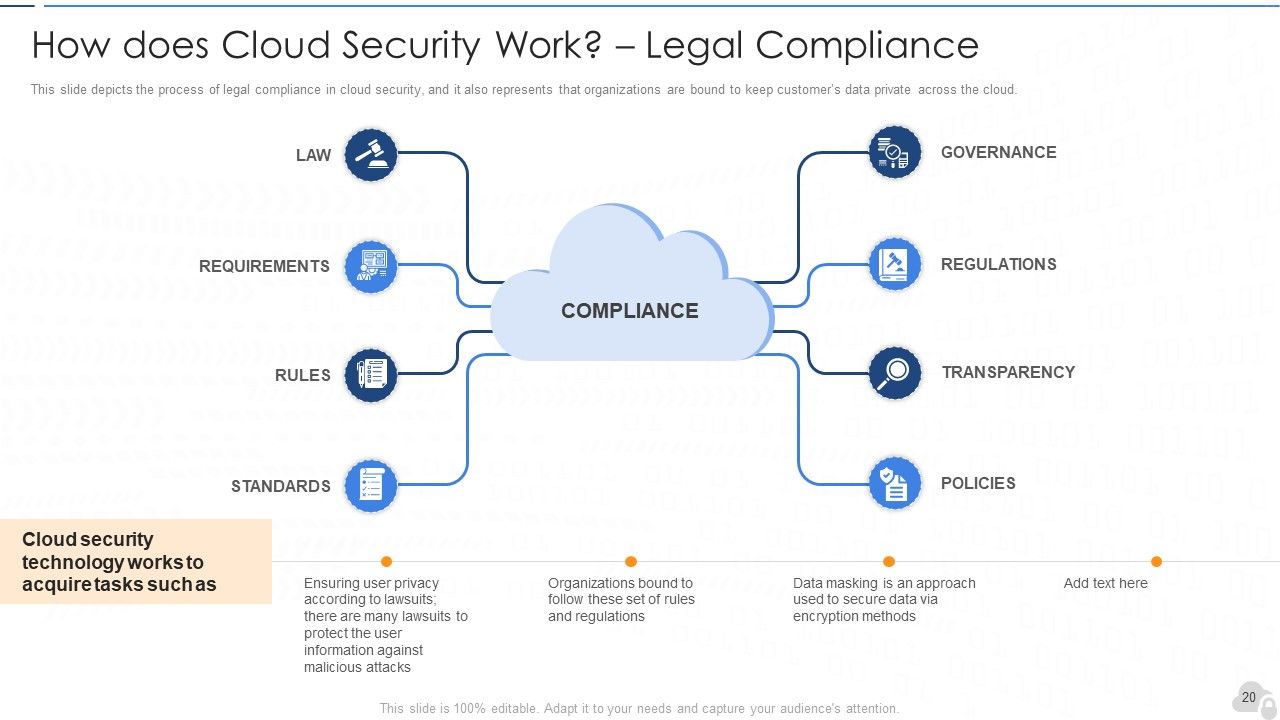
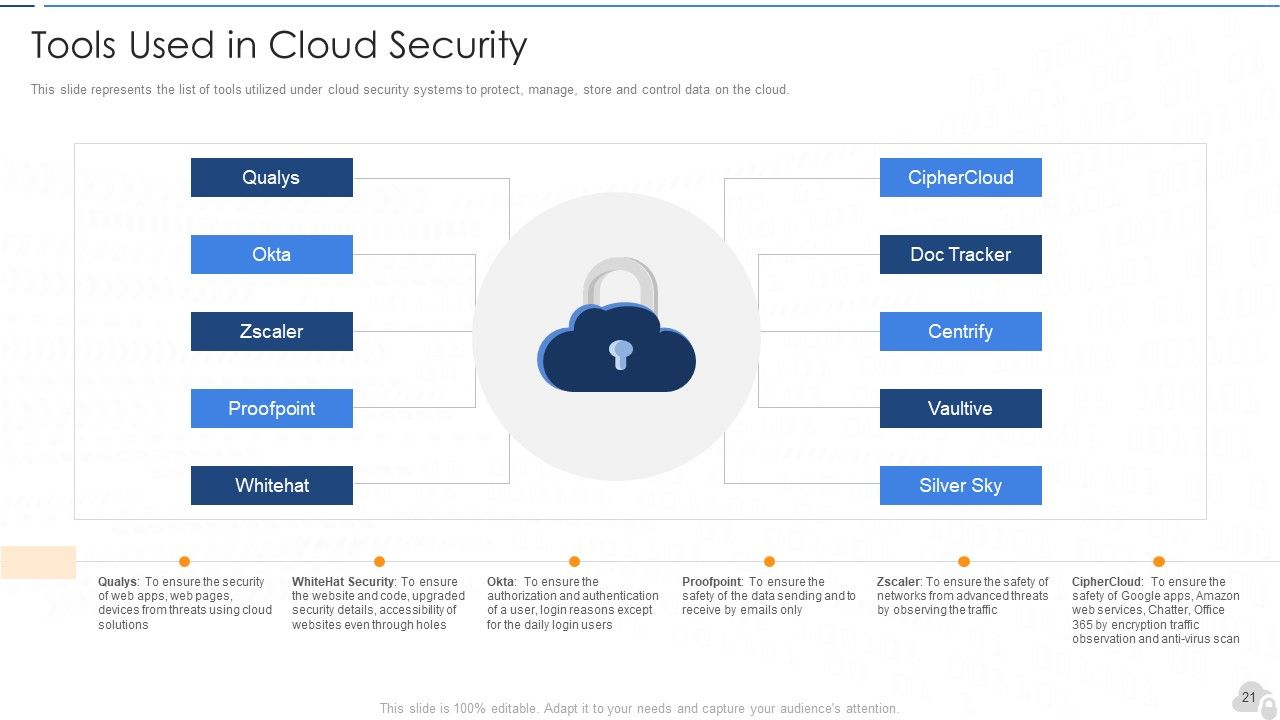
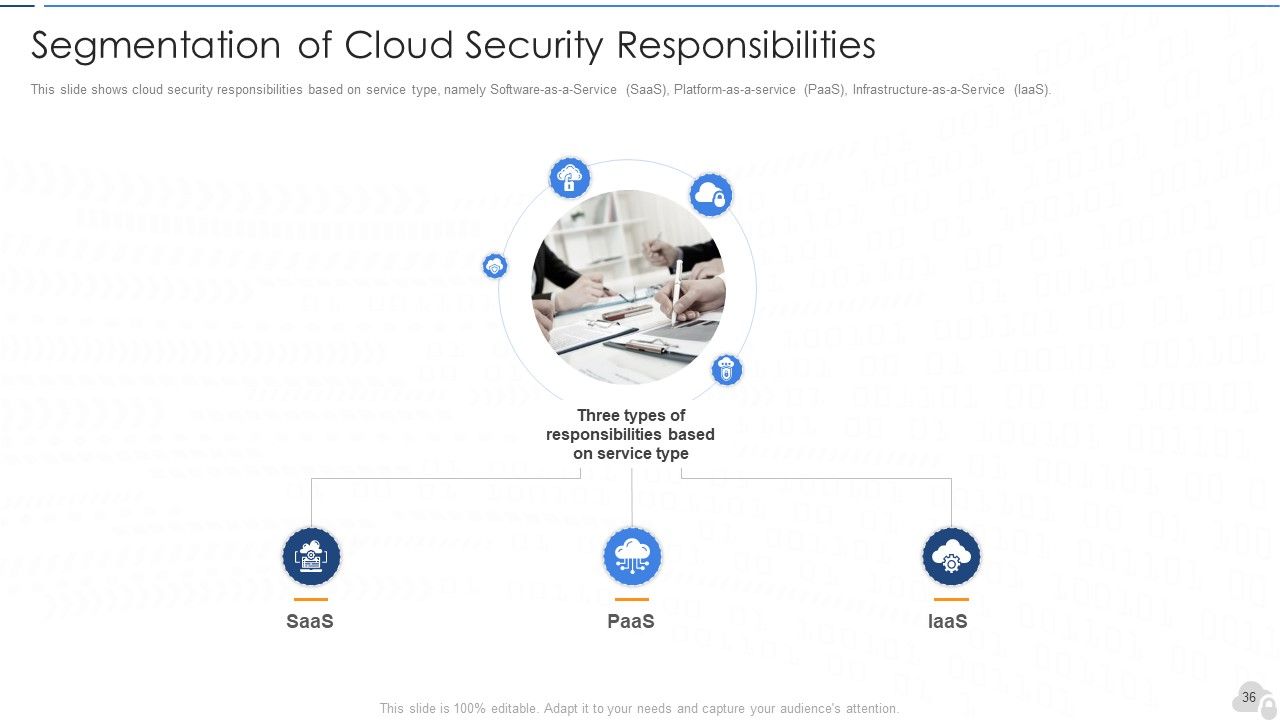
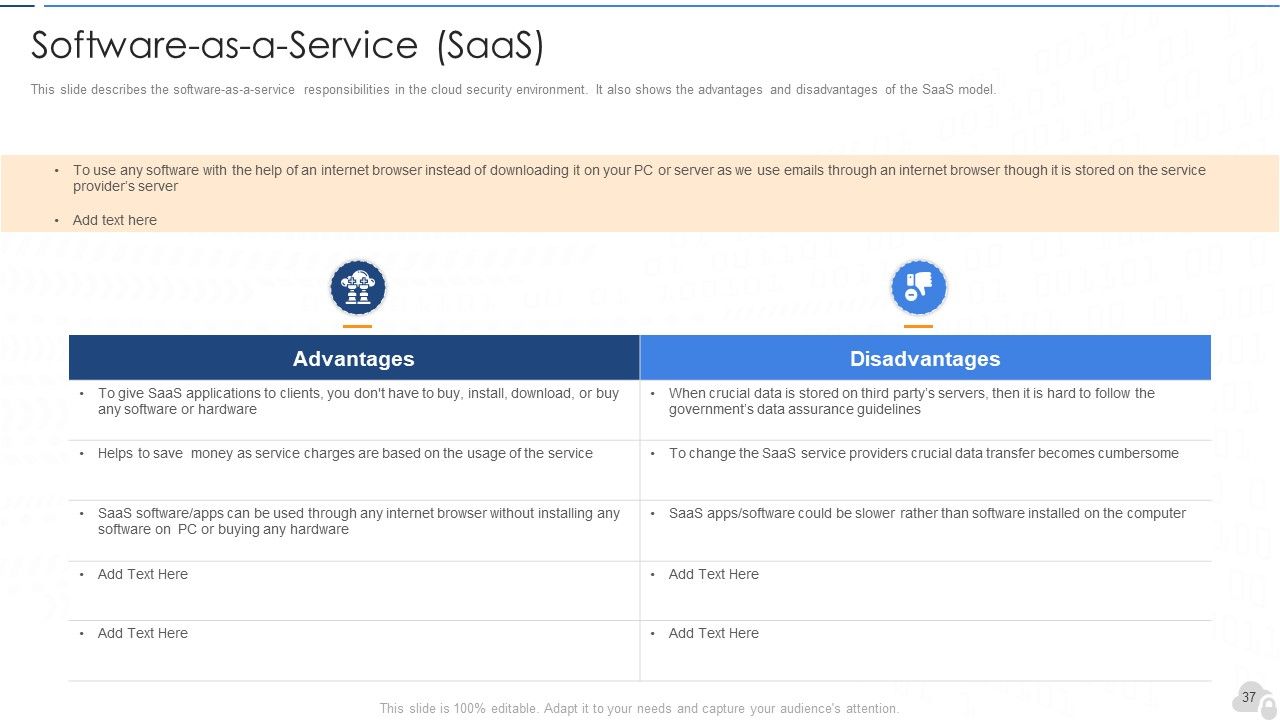
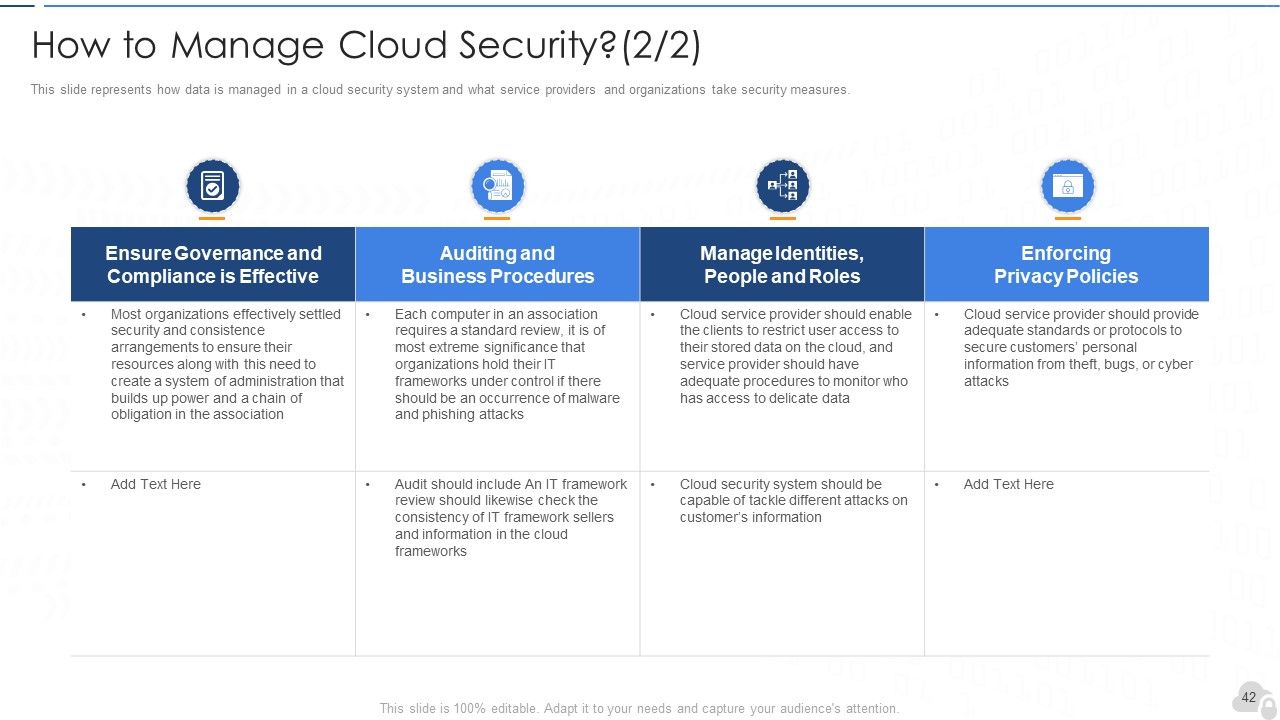
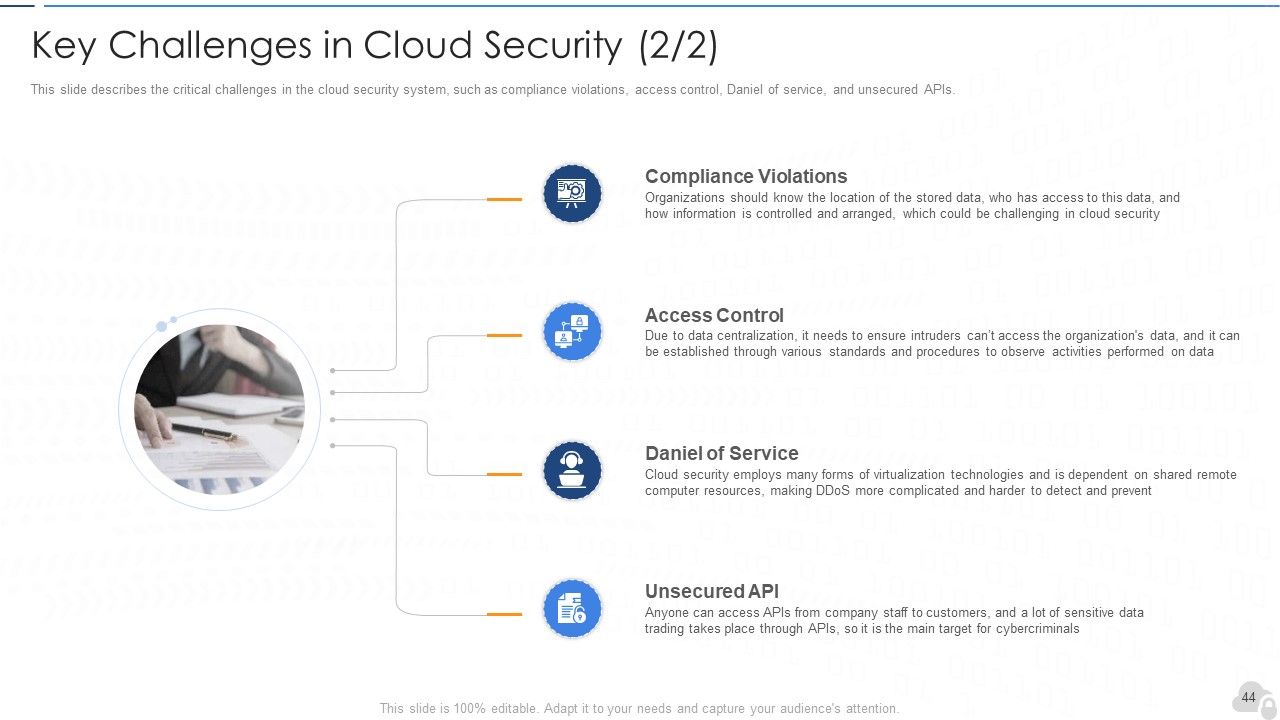
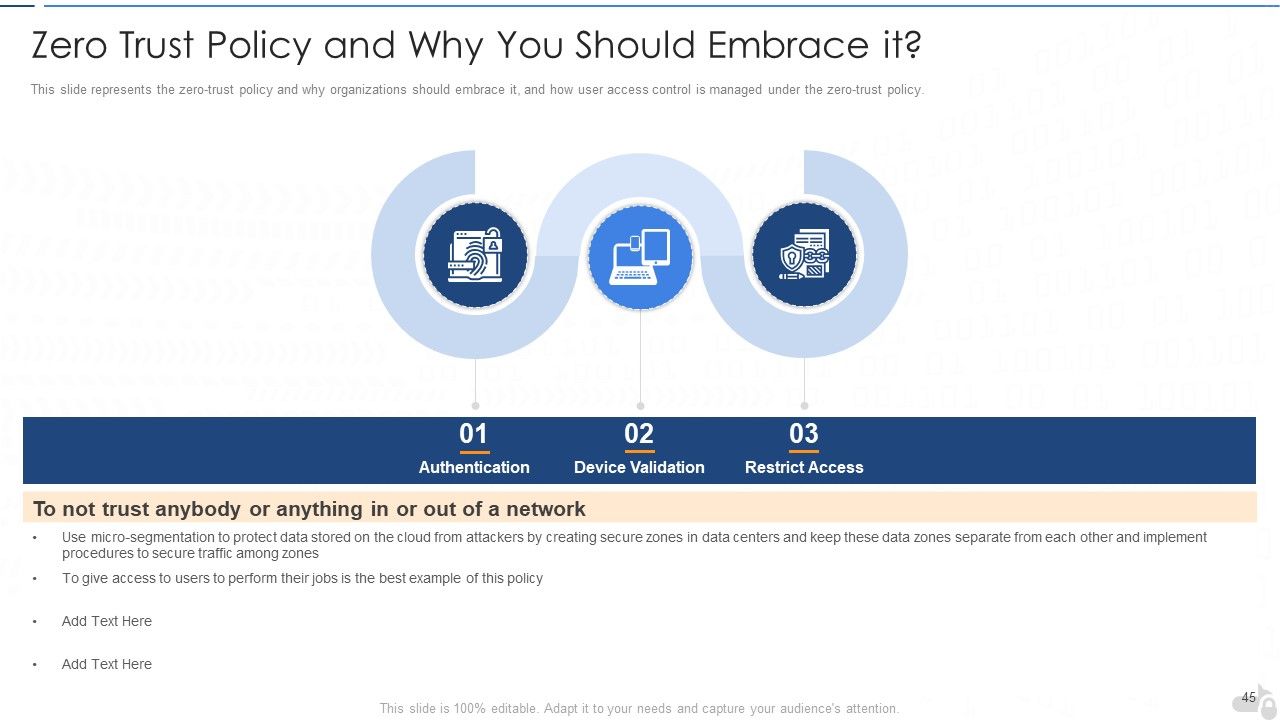
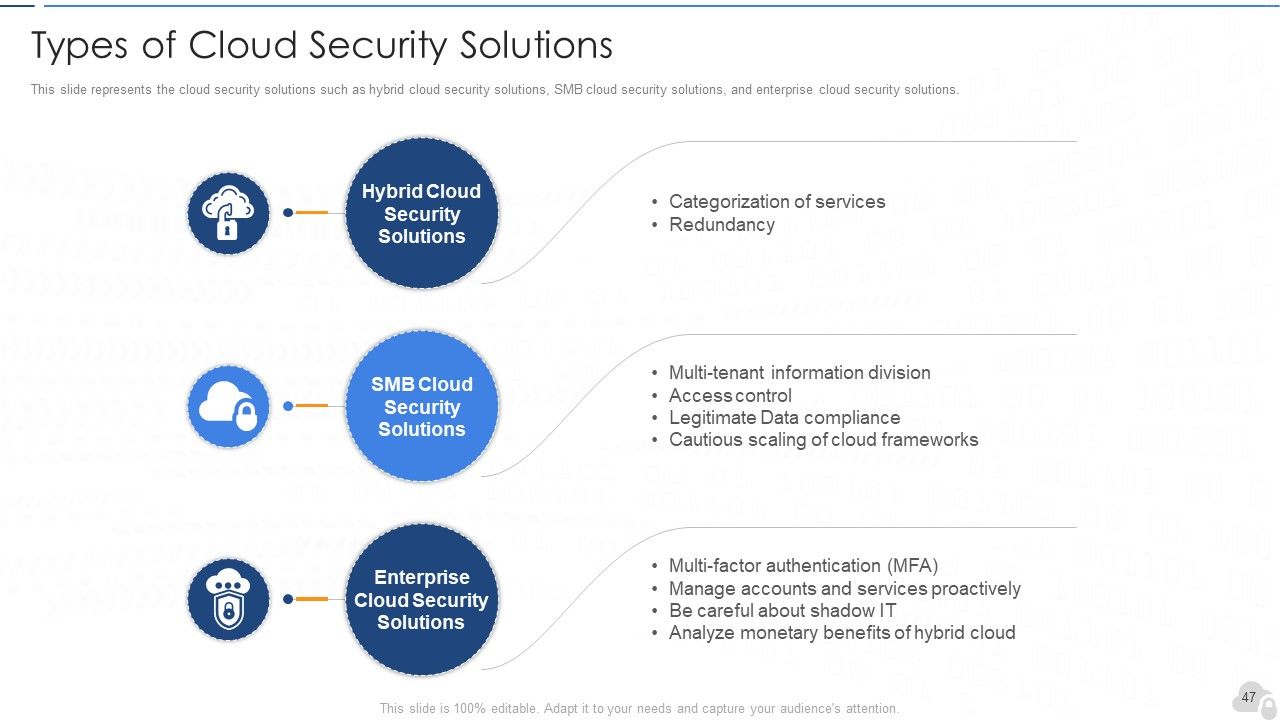
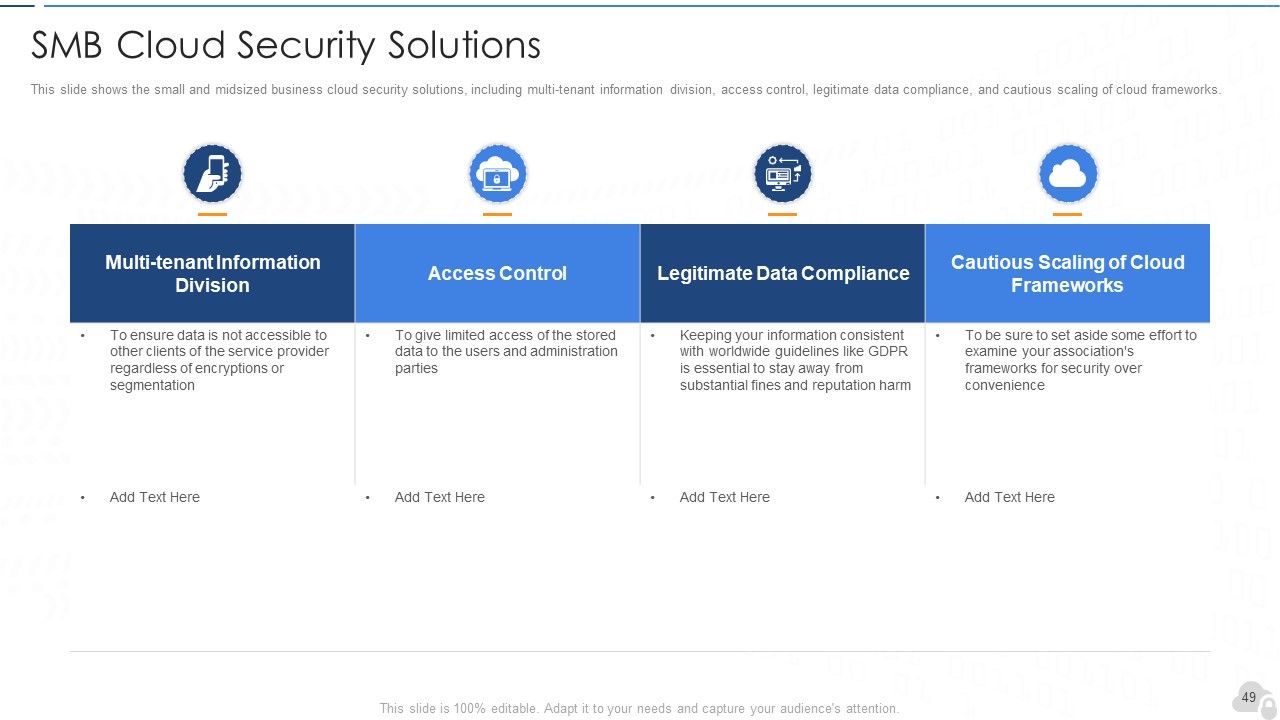
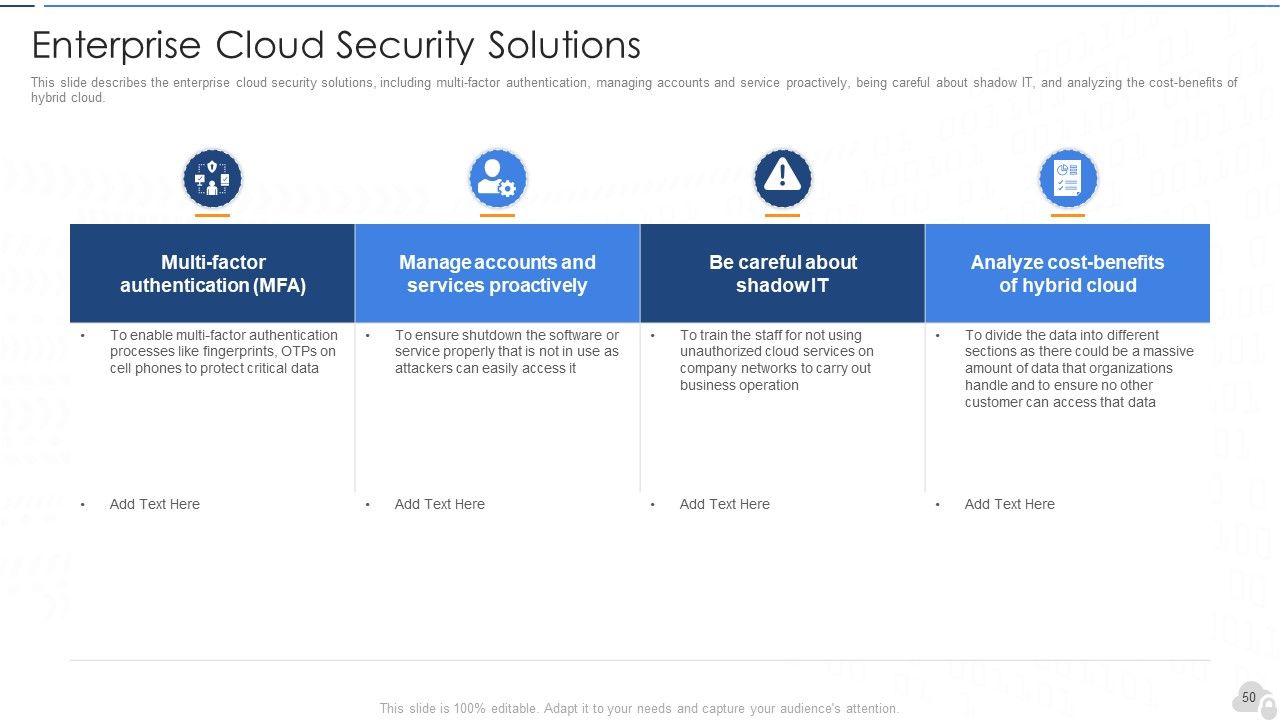
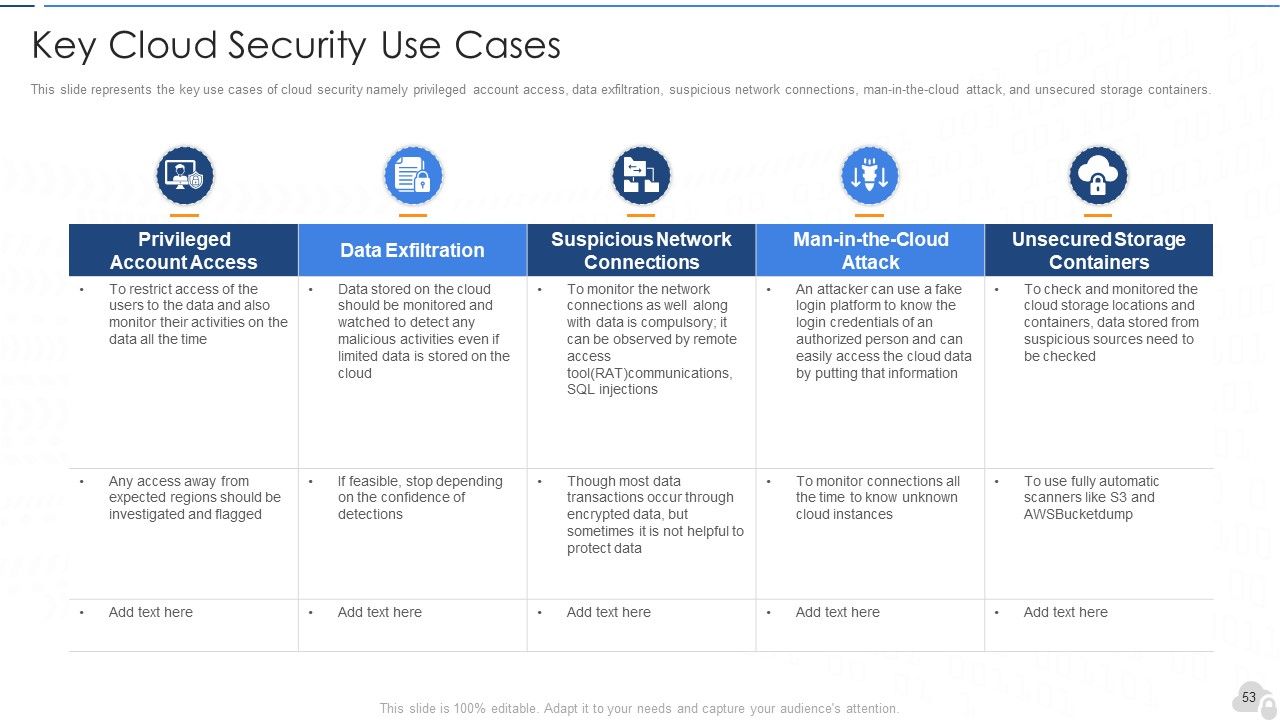
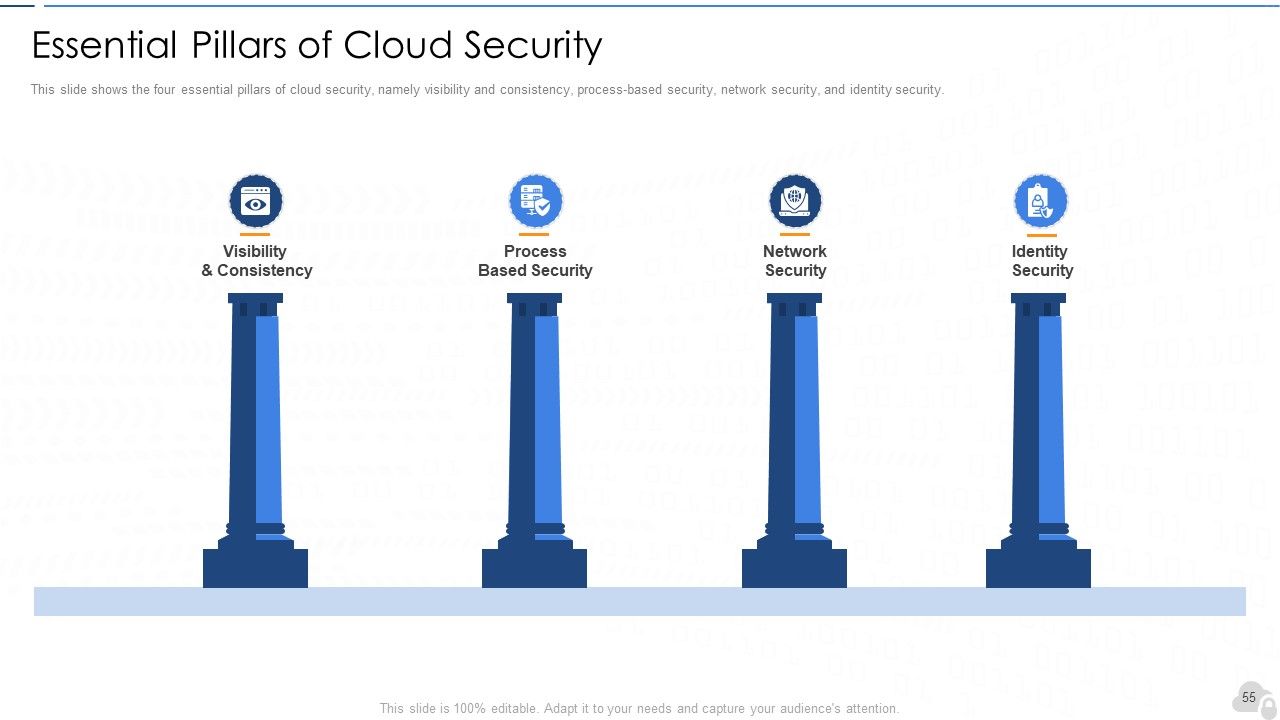
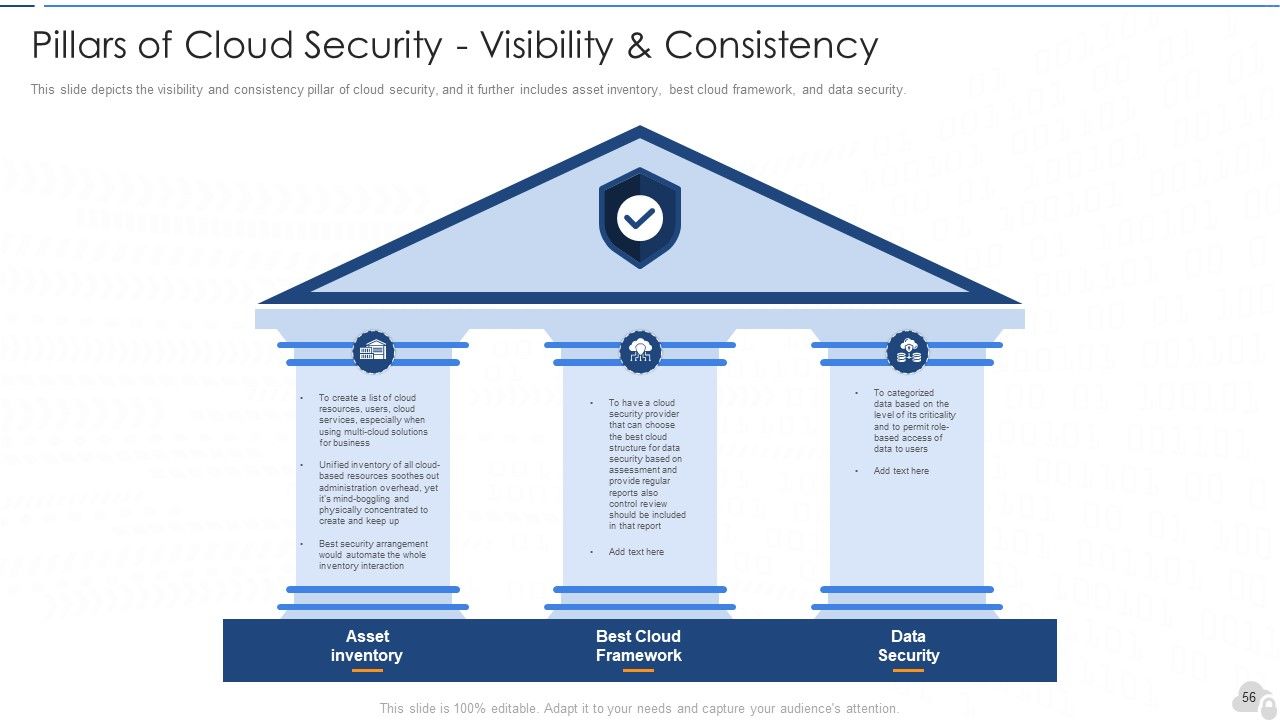
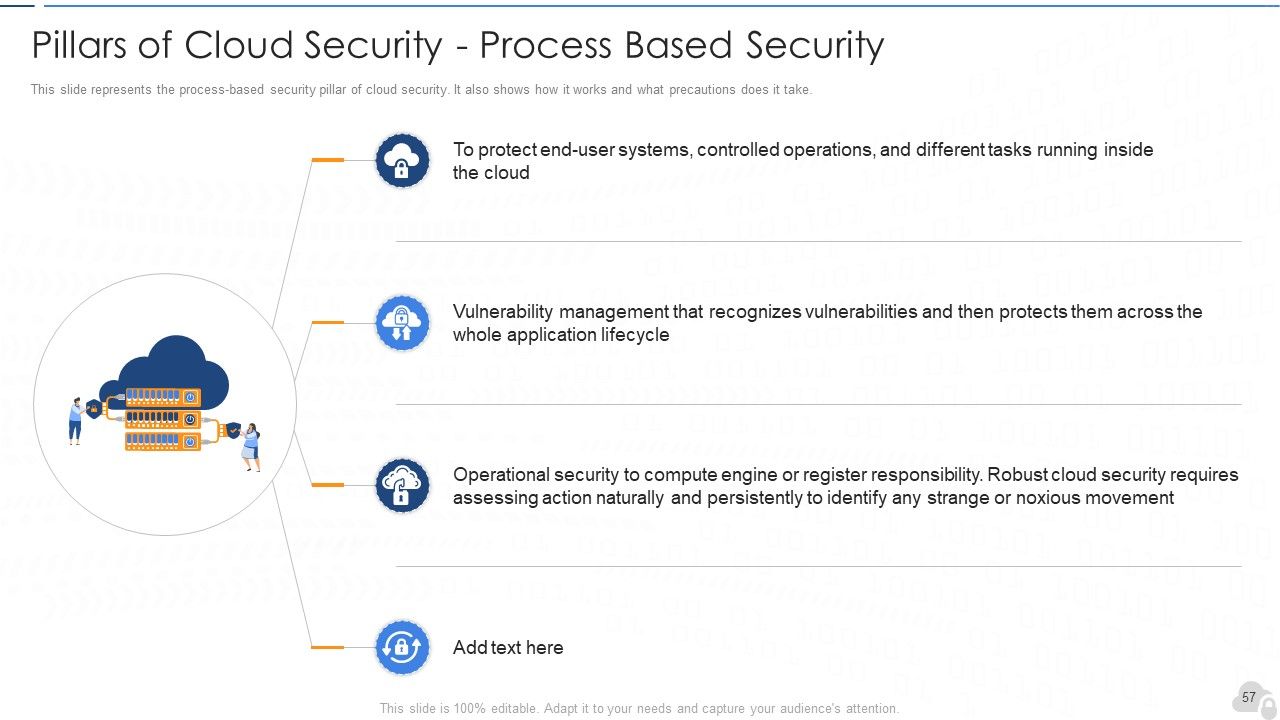
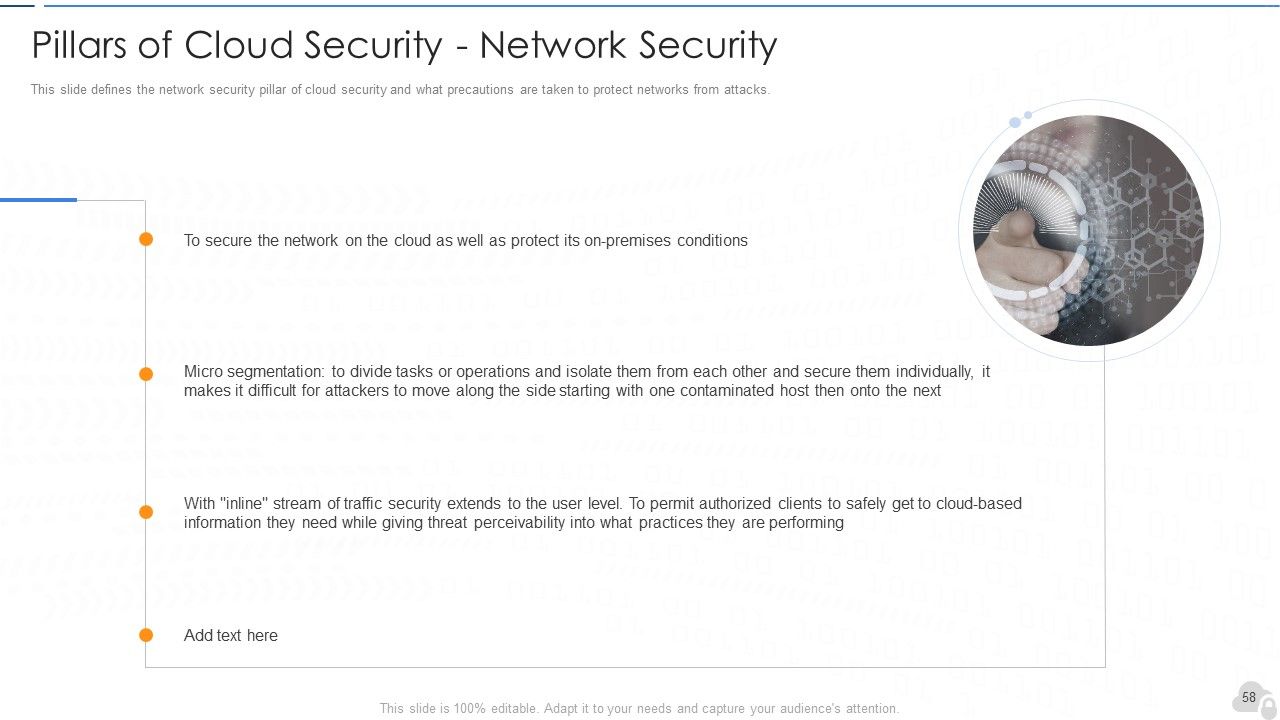
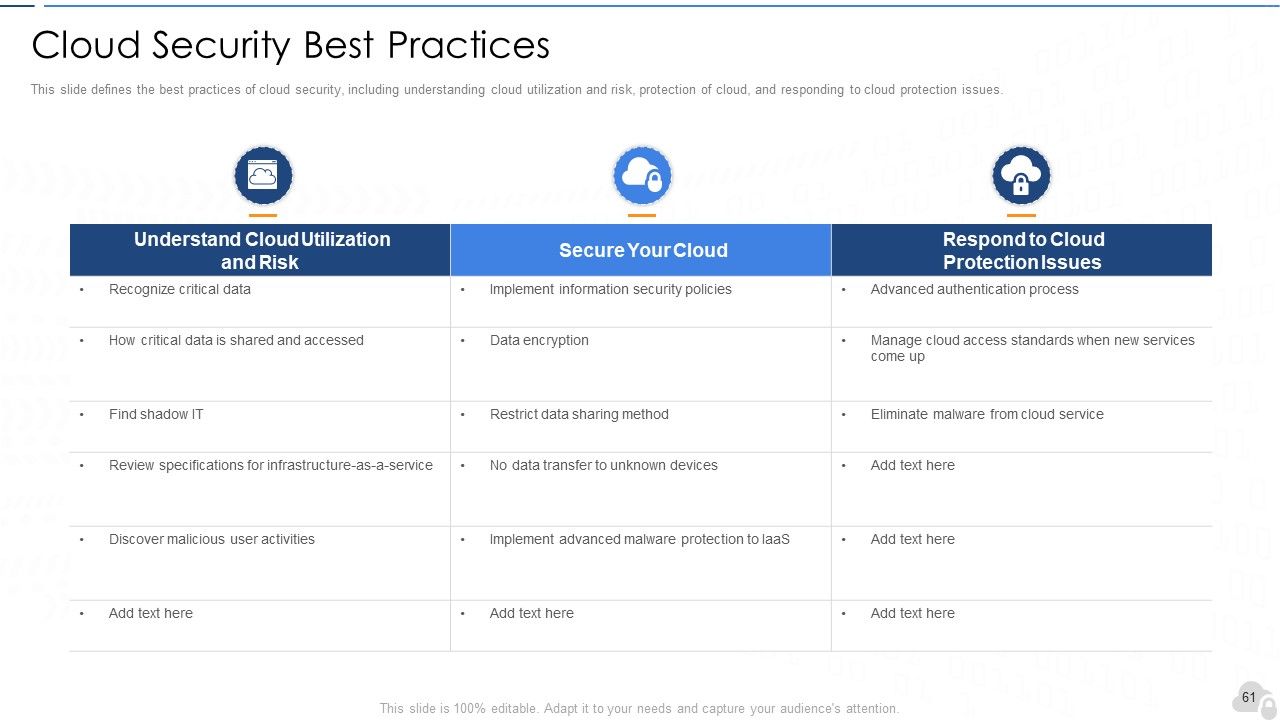
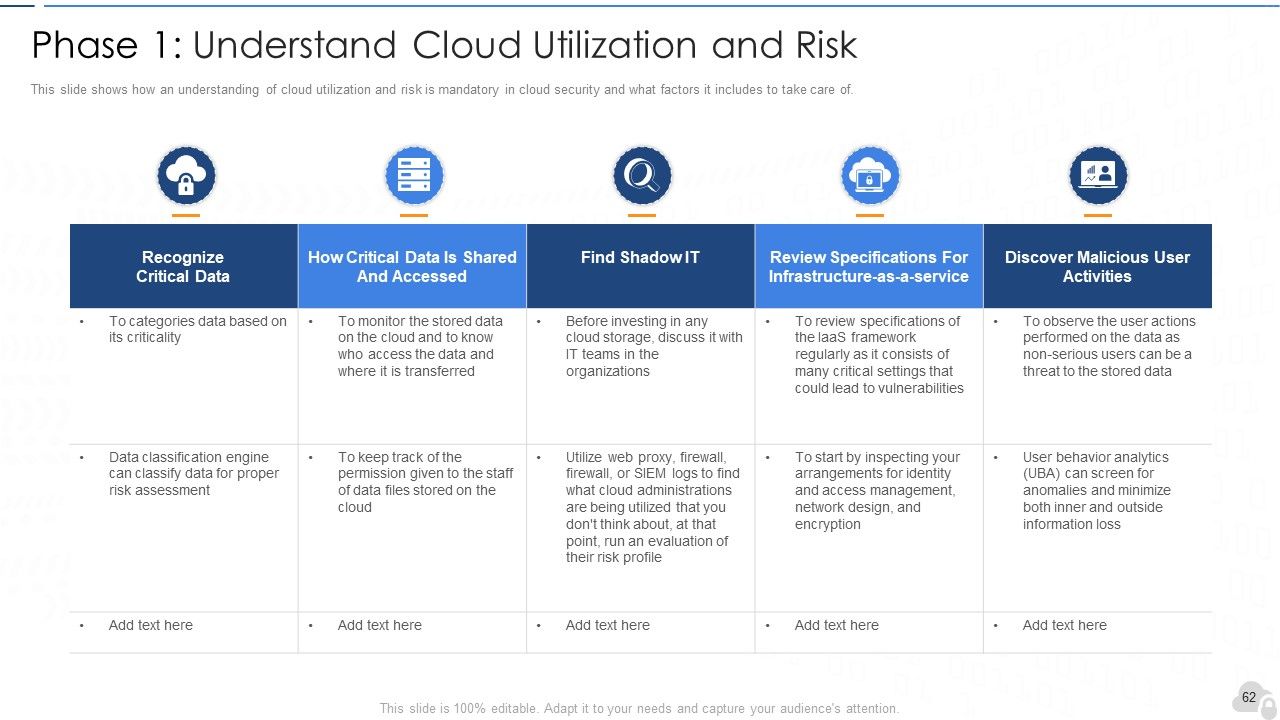
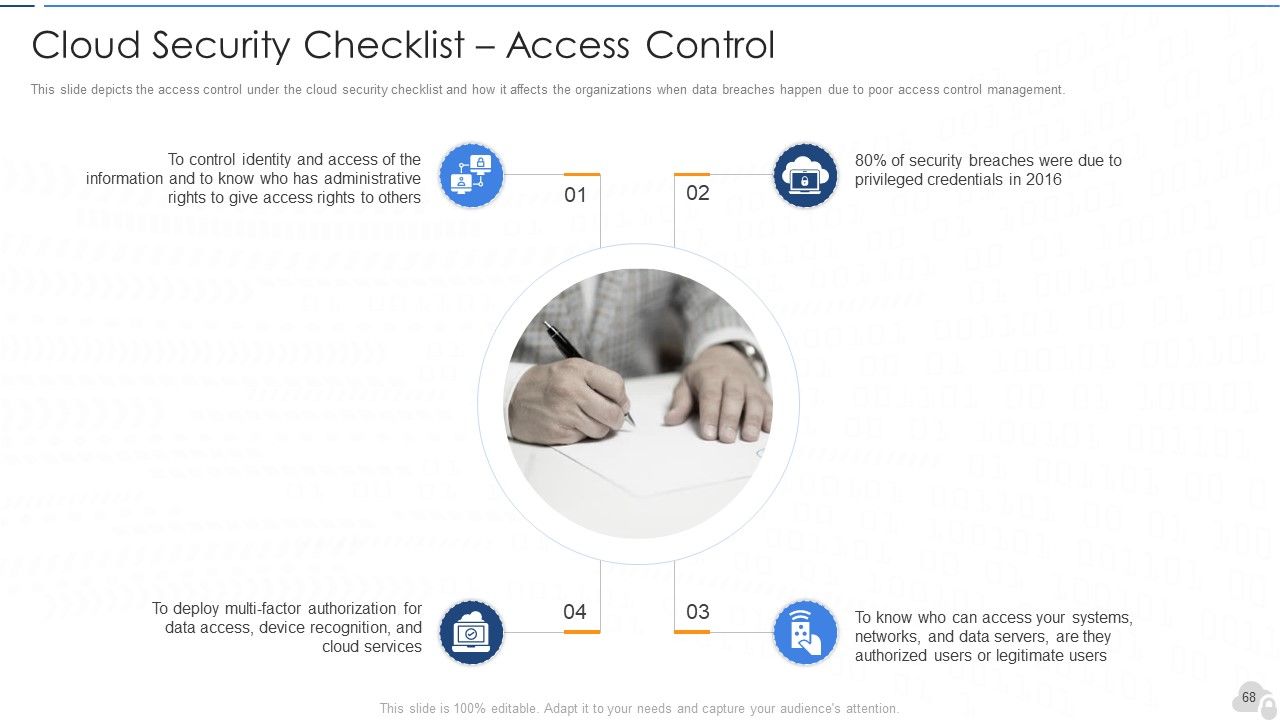
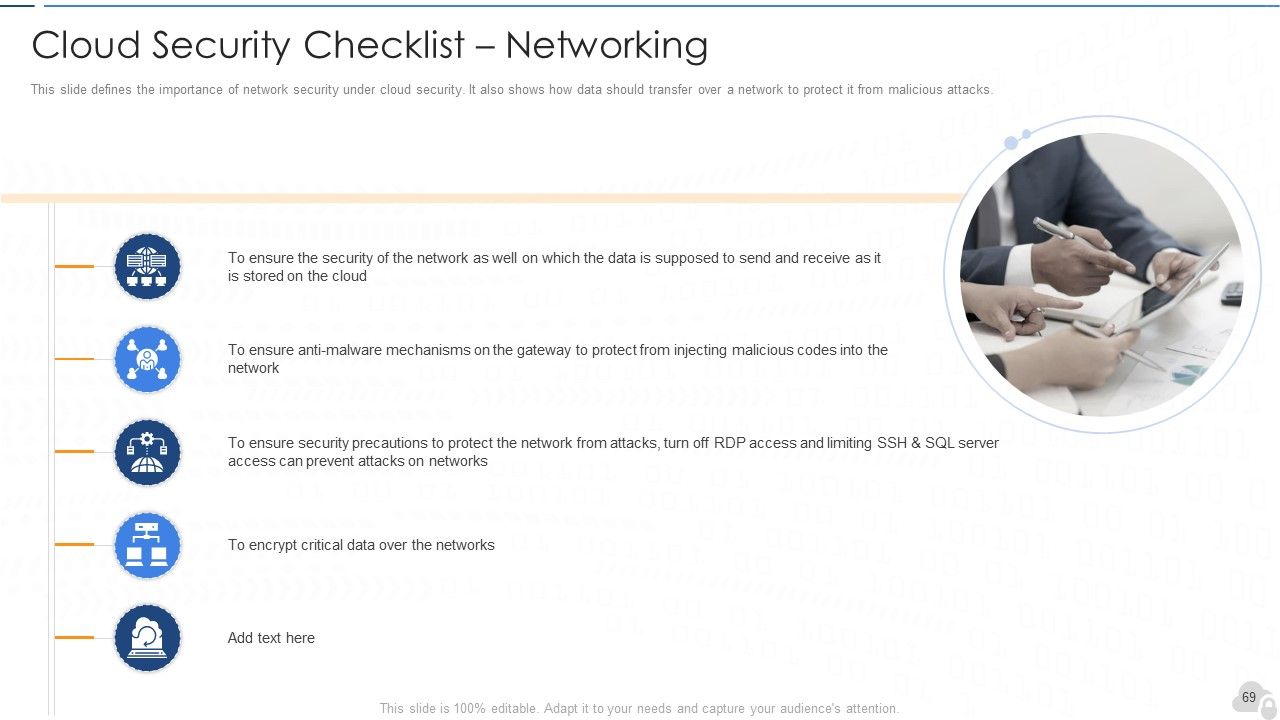
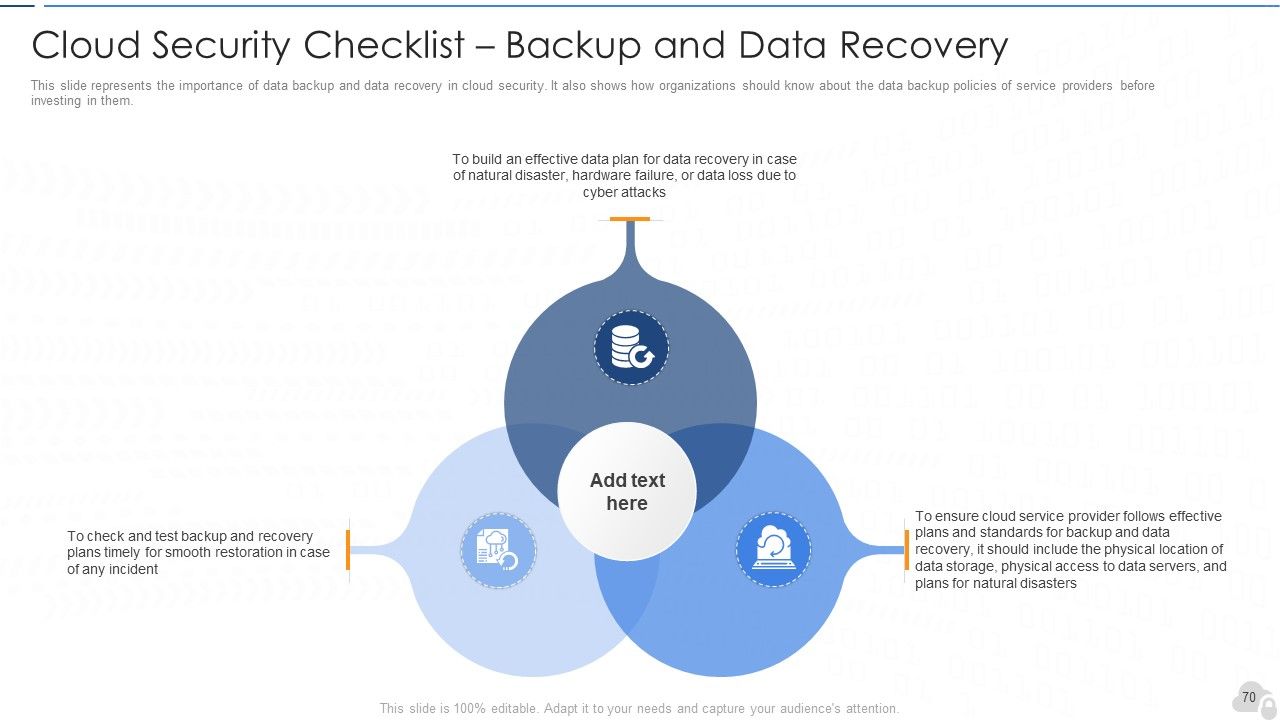
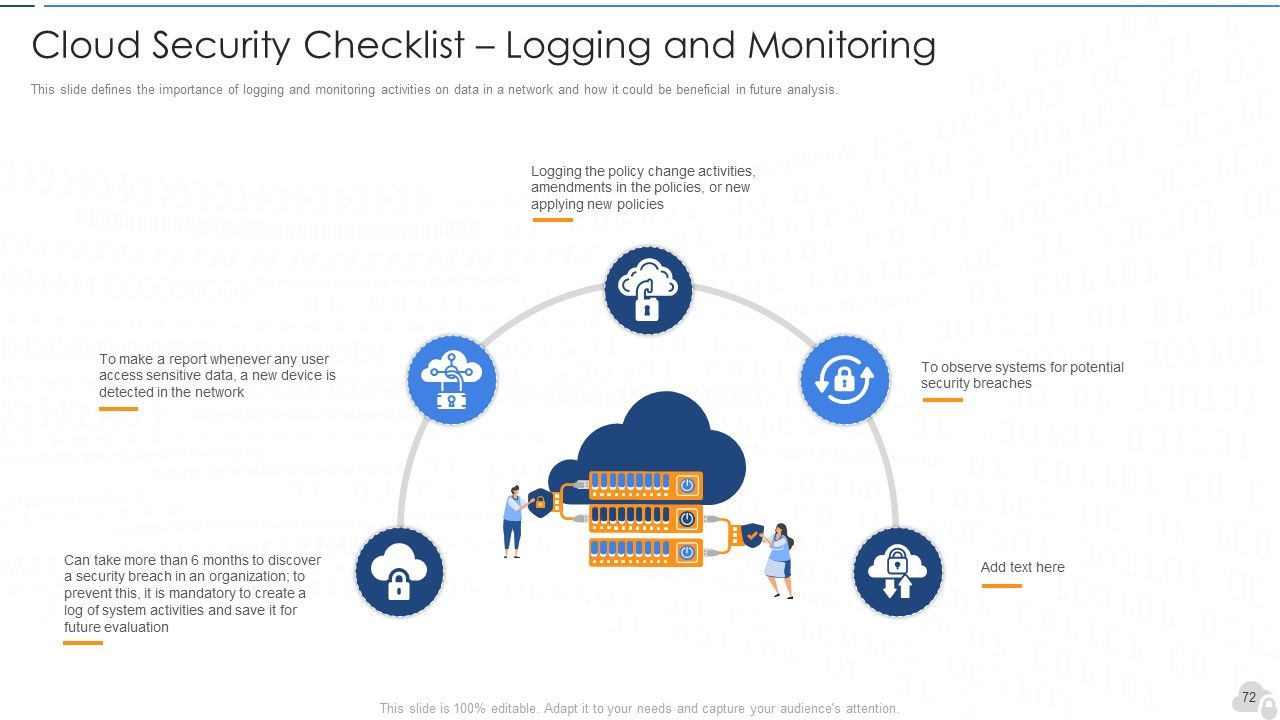
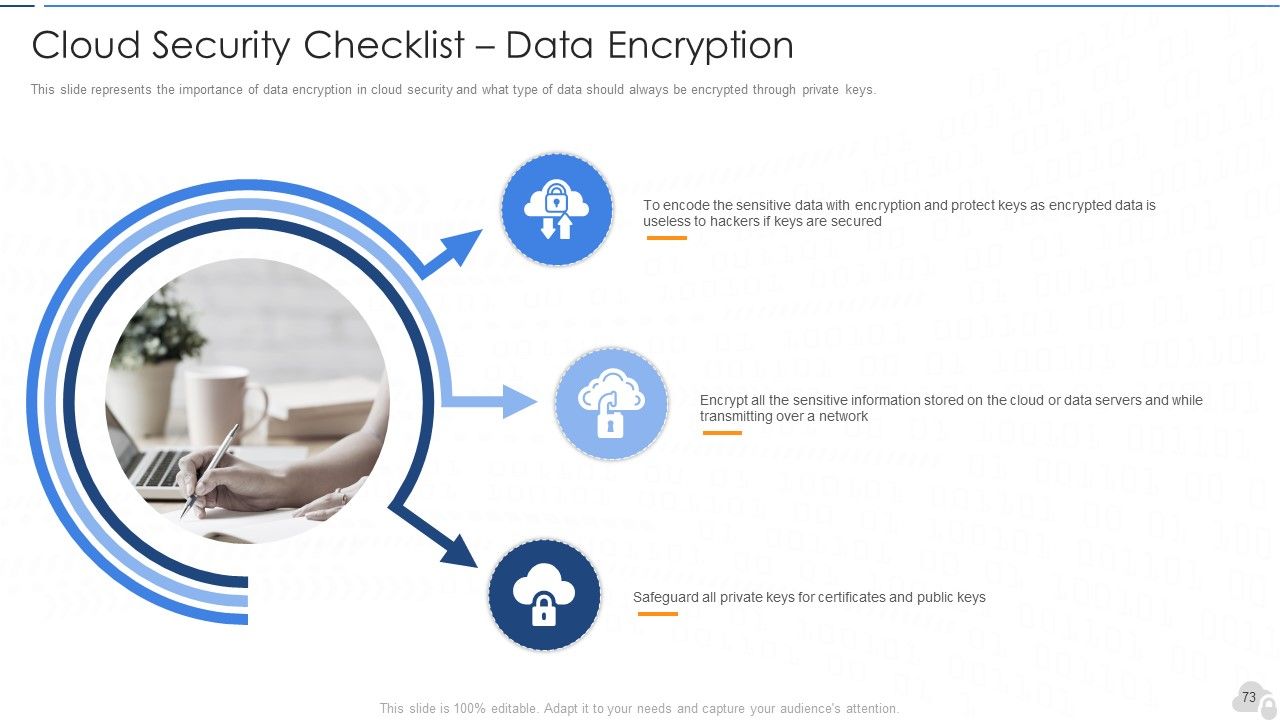
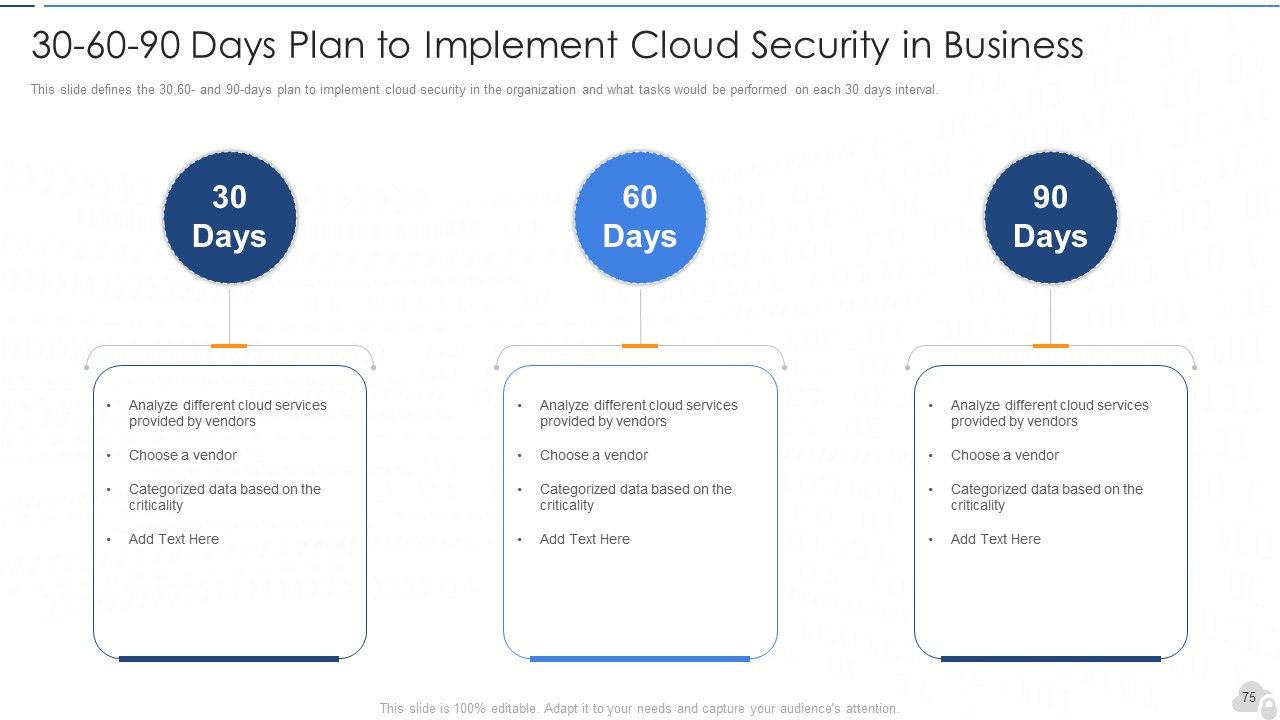
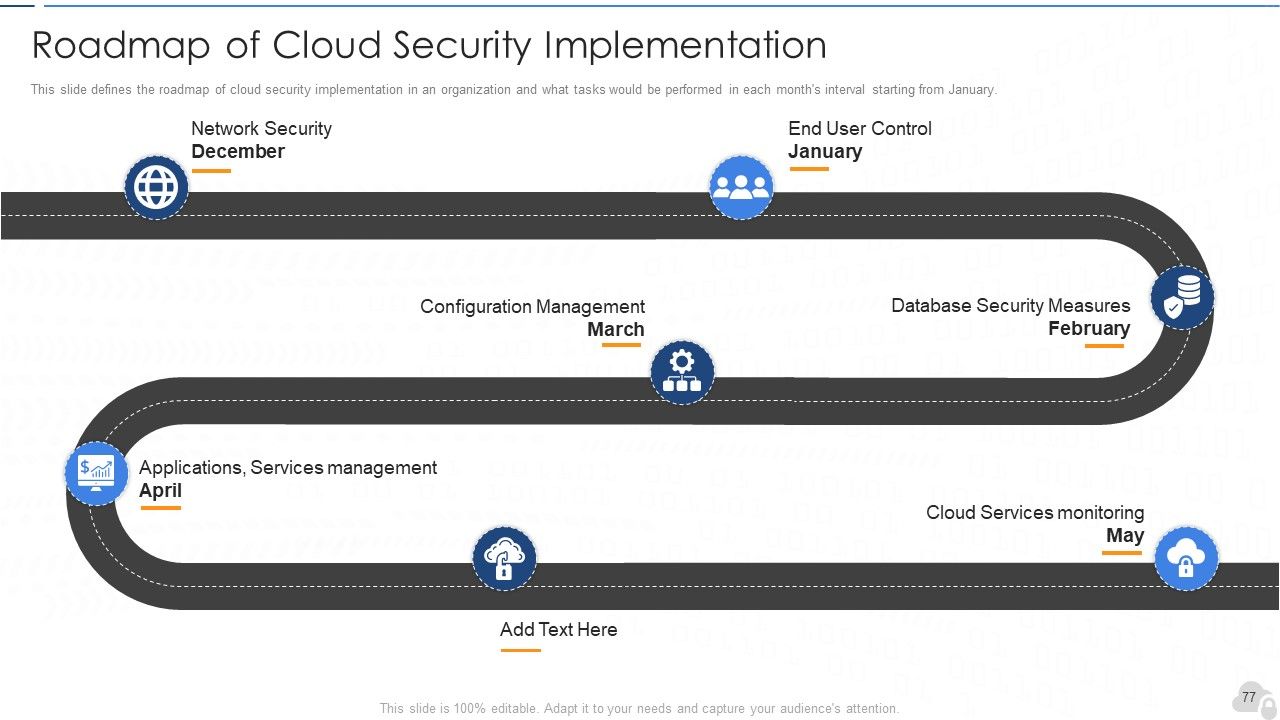
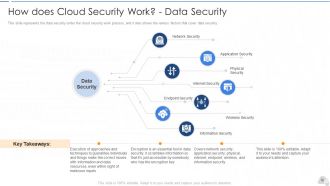
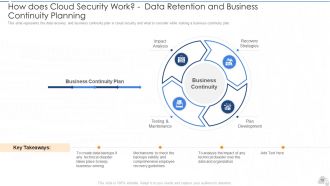
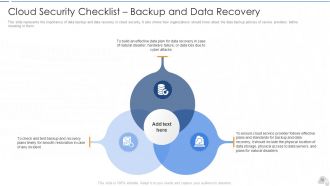
Introducing this cloud security PowerPoint presentation to provide a comprehensive overview of Cloud security. Cloud Security, also known as cloud computing security, comprises various approaches, controls, strategies, and technologies that work together to safeguard cloud-based frameworks, information, and infrastructure. These security measures are designed to protect cloud information, support administrative consistency, secure clients' privacy, and set validation rules for individual clients and devices. This PPT deck will familiarize readers with cloud security, its architecture, benefits, and working details. It also talks about the four essential pills of cloud security, best practices to optimize it, and the difference between cloud security and traditional security. Furthermore, this cloud security PPT throws light on the tools that are used in it. Also, it highlights the security measures taken in cloud security and details on risks or threats that can impact the security of a cloud. Also, this PPT covers the segmentation of cloud security responsibilities and topics that fall under the umbrella of cloud security, namely data center security, access control, threat prevention, threat detection, threat mitigation, redundancy, and legal compliance. In addition to that, the cloud information security deck illustrates the downside of cloud security, associated critical challenges, types of cloud security solutions, and the key use-cases of cloud security. Moreover, the cloud data protection PPT covers the list of the industries that can benefit from cloud security. It also provides information on the zero-trust policy along with its benefit. At last, this cloud computing security presentation captures the 30-60-90 days plan to implement cloud security in the organization, a roadmap to measure the implementation process, and a dashboard to observe the performance after implementing cloud security in the business. Get your hands on this exclusive cloud security PowerPoint presentation.
Introducing this cloud security PowerPoint presentation to provide a comprehensive overview of Cloud security. Cloud Securi..
- Google Slides is a new FREE Presentation software from Google.
- All our content is 100% compatible with Google Slides.
- Just download our designs, and upload them to Google Slides and they will work automatically.
- Amaze your audience with SlideTeam and Google Slides.
-
Want Changes to This PPT Slide? Check out our Presentation Design Services
- WideScreen Aspect ratio is becoming a very popular format. When you download this product, the downloaded ZIP will contain this product in both standard and widescreen format.
-

- Some older products that we have may only be in standard format, but they can easily be converted to widescreen.
- To do this, please open the SlideTeam product in Powerpoint, and go to
- Design ( On the top bar) -> Page Setup -> and select "On-screen Show (16:9)” in the drop down for "Slides Sized for".
- The slide or theme will change to widescreen, and all graphics will adjust automatically. You can similarly convert our content to any other desired screen aspect ratio.
Compatible With Google Slides

Get This In WideScreen
You must be logged in to download this presentation.
PowerPoint presentation slides
Enthrall your audience with this Cloud Security IT Powerpoint Presentation Slides. Increase your presentation threshold by deploying this well crafted template. It acts as a great communication tool due to its well researched content. It also contains stylized icons, graphics, visuals etc, which make it an immediate attention grabber. Comprising eighty nine slides, this complete deck is all you need to get noticed. All the slides and their content can be altered to suit your unique business setting. Not only that, other components and graphics can also be modified to add personal touches to this prefabricated set.
People who downloaded this PowerPoint presentation also viewed the following :
Cloud security it powerpoint presentation slides with all 89 slides:
Use our Cloud Security IT Powerpoint Presentation Slides to effectively help you save your valuable time. They are readymade to fit into any presentation structure.
-
Designs have enough space to add content.
-
Informative presentations that are easily editable.
-
Great designs, Easily Editable.
-
Perfect template with attractive color combination.