Consensus Mechanism in Blockchain Training Module on Blockchain Technology and its Applications Training Ppt
This PPT training deck covers the technical concepts of consensus mechanisms used in blockchain technology. It contains details of blockchain mining types and major objectives of the consensus mechanism, which are to achieve unified agreement, prevent double-spending, align economic incentives, be fair and equitable, and be fault-tolerant. Further, in-depth, it covers the working, benefits, and limitations of different types of consensus mechanisms proof of work, proof of stake, delegated proof of stake, proof of capacity, proof of authority, and proof of activity used in blockchain. It also contains key takeaways, discussion, and multiple-choice questions related to the topic to make the training session interactive. The PPT module also includes additional slides on about us, vision, mission, goal, 30-60-90 days plan, timeline, roadmap, training completion certificate, energizer activities, detailed client proposal, and training assessment form.
This PPT training deck covers the technical concepts of consensus mechanisms used in blockchain technology. It contains det..
- Google Slides is a new FREE Presentation software from Google.
- All our content is 100% compatible with Google Slides.
- Just download our designs, and upload them to Google Slides and they will work automatically.
- Amaze your audience with SlideTeam and Google Slides.
-
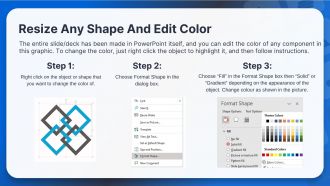
Want Changes to This PPT Slide? Check out our Presentation Design Services
- WideScreen Aspect ratio is becoming a very popular format. When you download this product, the downloaded ZIP will contain this product in both standard and widescreen format.
-

- Some older products that we have may only be in standard format, but they can easily be converted to widescreen.
- To do this, please open the SlideTeam product in Powerpoint, and go to
- Design ( On the top bar) -> Page Setup -> and select "On-screen Show (16:9)” in the drop down for "Slides Sized for".
- The slide or theme will change to widescreen, and all graphics will adjust automatically. You can similarly convert our content to any other desired screen aspect ratio.
Compatible With Google Slides

Get This In WideScreen
You must be logged in to download this presentation.
PowerPoint presentation slides
Presenting Training Session on Consensus Mechanism in Blockchain. This deck contains 104 uniquely designed slides. Our PowerPoint experts have included all the necessary templates, designs, icons, graphs and other essential material. This deck is well crafted by extensive research. Slides consists of amazing visuals and appropriate content. These PPT slides can be instantly downloaded with just a click. Compatible with all screen types and monitors. Supports Google Slides. Premium Customer Support available. Suitable for use by managers, employees and organizations. These slides are easily customizable. You can edit the color, text, icon and font size to suit your requirement.
People who downloaded this PowerPoint presentation also viewed the following :
Content of this Powerpoint Presentation
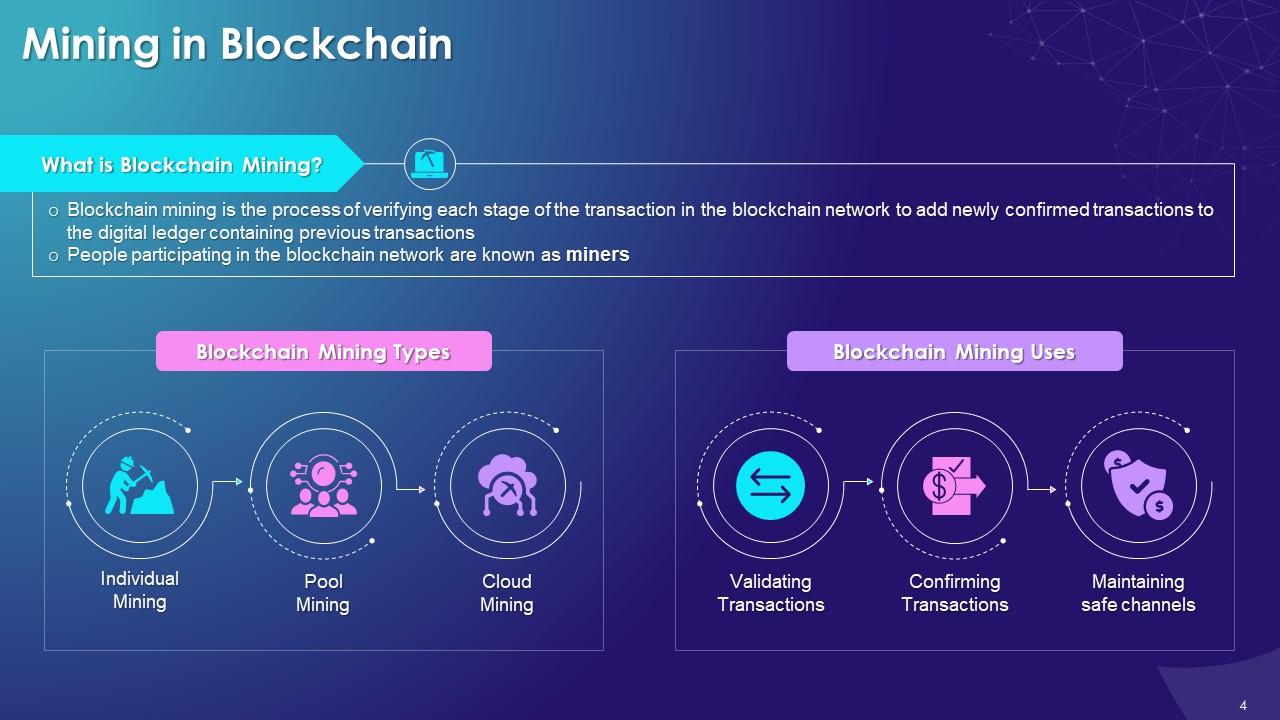
Slide 4
The purpose of this slide is to highlight the concept of blockchain mining. It also includes details on blockchain mining types such as individual mining, pool mining, and cloud mining. The uses of blockchain mining are also enlisted, which are validating transactions, confirming transactions, and channel safety.
Instructor’s Notes:
Blockchain Mining Types:
The multiple types of blockchain mining are as follows:
- Individual Mining: When an individual does blockchain mining
- Pool Mining: A group of miners collaborate to authorize a transaction
- Cloud Mining: When blockchain mining is done using cloud technology
Blockchain Mining Uses:
The multiple uses of blockchain mining are as follows:
- Validating Transactions: To validate the multiple blocks added to the blockchain network
- Confirming Transactions: To determine the transactions' genuineness in the blockchain
- Channels Safety: To ensure the safety of blockchain by tracking any malicious activity on the network
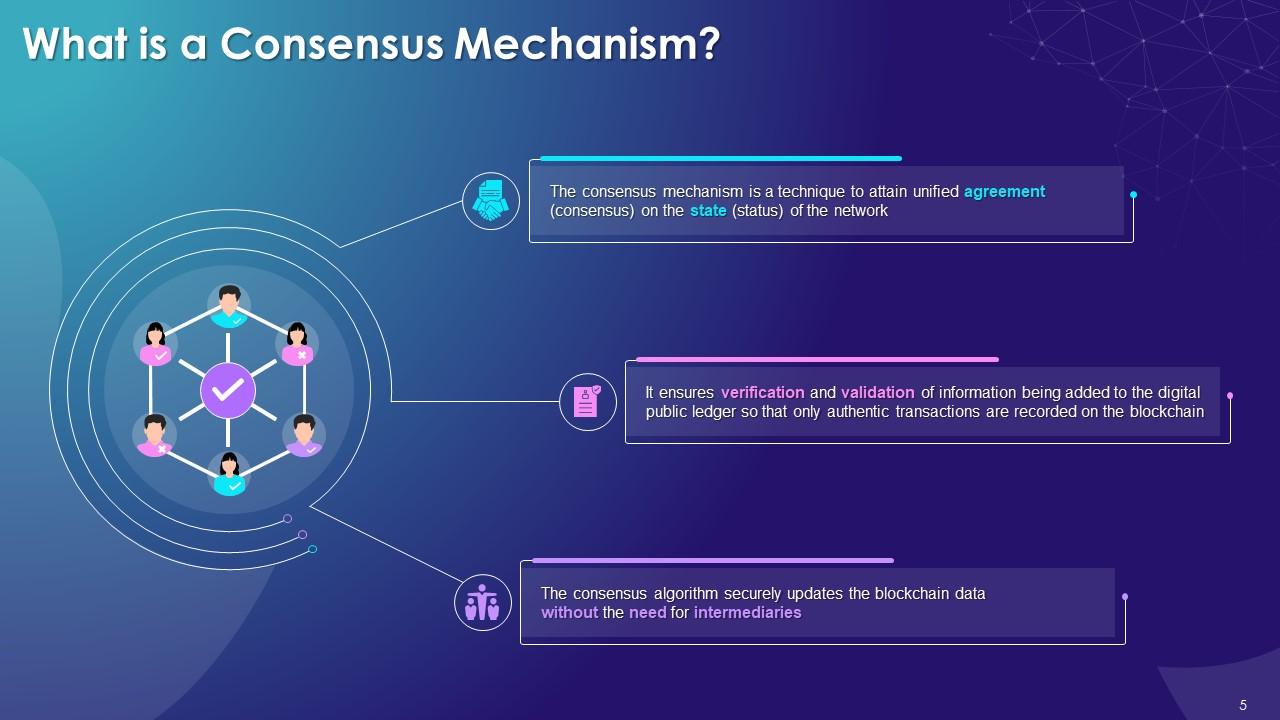
Slide 5
The purpose of this slide is to provide information regarding the consensus algorithm, and its usage in the blockchain to verify the data being added in the digital ledger.
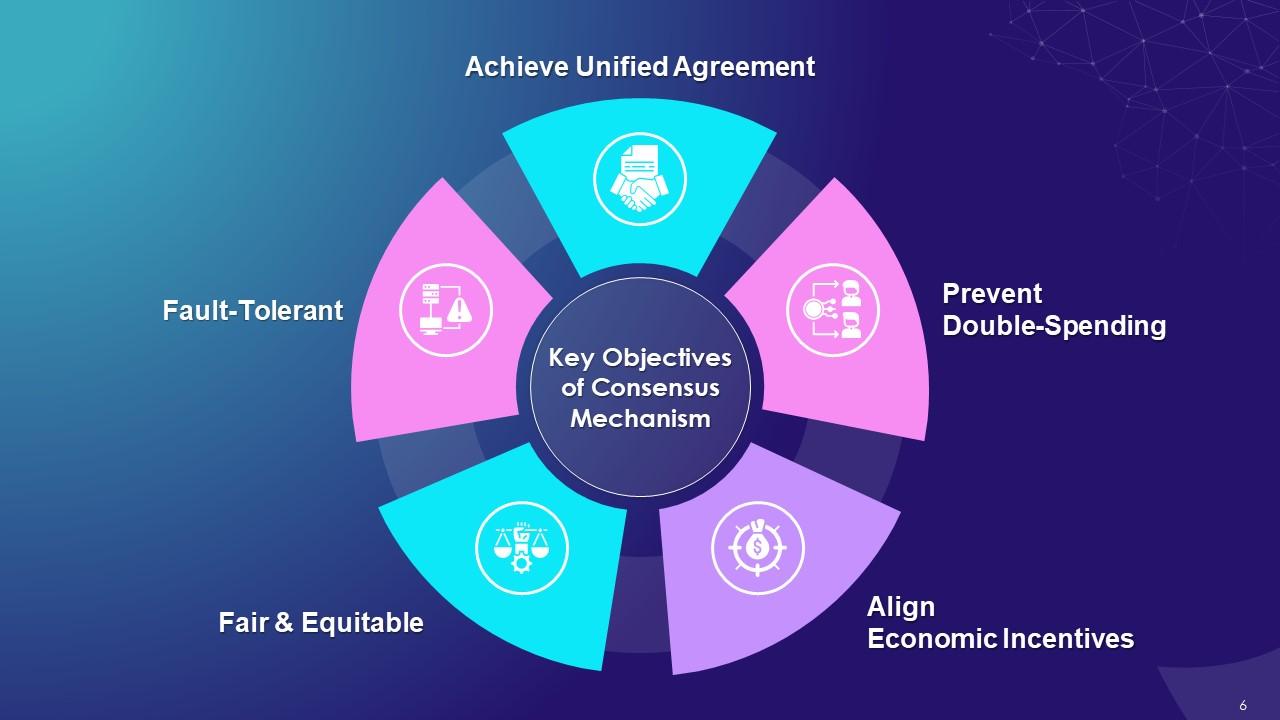
Slide 6
This slide indicates the primary objectives of the blockchain consensus algorithms in blockchain, such as achieving unified agreement, preventing double-spending, aligning economic incentives, being fair & equitable, and being fault-tolerant.
Instructor’s Notes:
The key objectives of consensus mechanism are as follows:
- Achieve Unified Agreement: Consensus mechanism helps achieve a unified agreement on which data is true and accurate. In the blockchain, users are not dependent on a single central authority to approve the transactions. Instead, protocol rules embedded in the network ensure that the public digital ledger is updated with the consensus of the masses
- Prevent Double-Spending: Consensus mechanism helps avoid a long-standing problem of double-spending in digital currencies. The consensus mechanism ensures that miners spend a lot of computational resources to complete transactions making it exponentially harder to double-spend or alter transactions
- Align Economic Incentives: Consensus mechanism rewards miners with financial incentives (such as bitcoins) for good behavior, such as managing the trust and integrity of the blockchain network. Also, any malicious acts such as network hacking or double-spending are avoided and kept under control as massive amount of computing and financial resources are required to conduct the same
- Fair & Equitable: Consensus mechanism avoids any form of discrimination by ensuring that each blockchain participant has the same footing by providing them equal participation and data inspection & verification access on the system
- Fault-Tolerant: The rules of consensus mechanism ensure that blockchains operate reliably and consistently even when faced with cyber attack threats or system failures
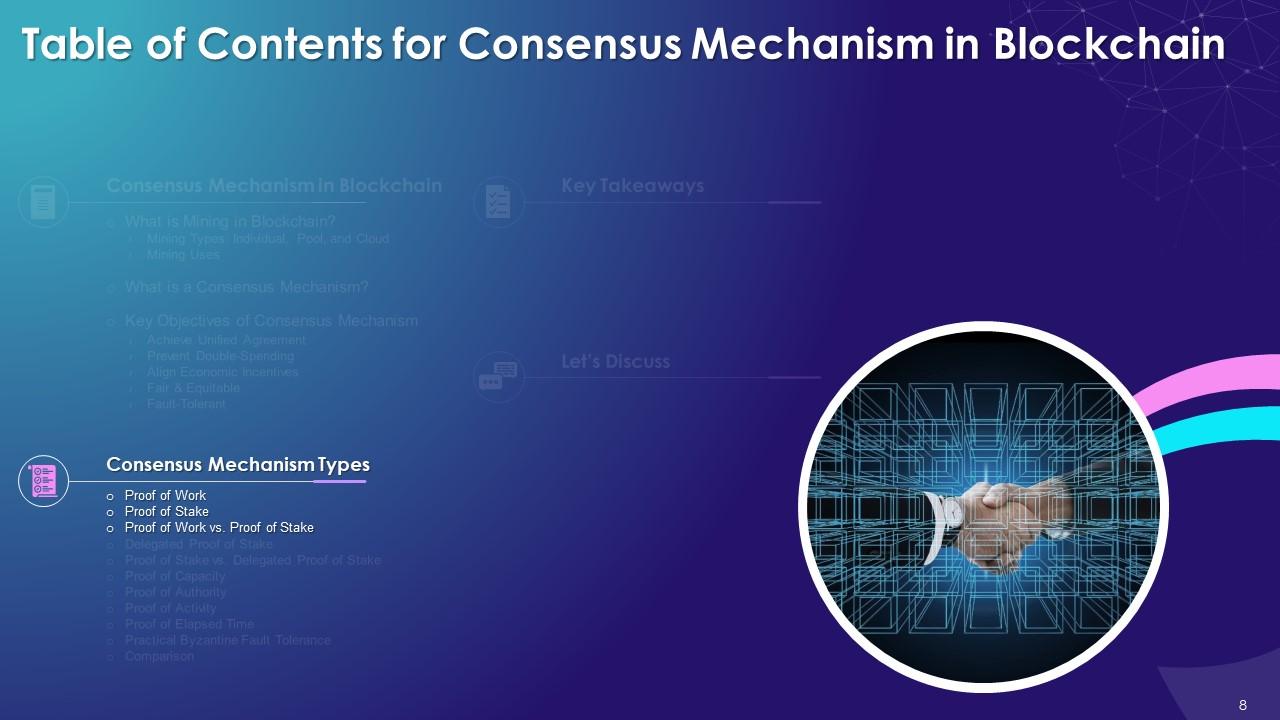
Slide 7
This slide indicates multiple types of consensus mechanism algorithms in blockchain that are Proof of Work, Proof of Stake, Delegated Proof of Stake, Proof of Capacity, Proof of Authority, Proof of Activity, Proof of Elapsed Time and Byzantine Fault Tolerance.
Instructor’s Notes:
The multiple types of consensus mechanism algorithms in blockchain are as follows:
- Proof of Work (PoW): Miners compete against each other to solve a complicated mathematical puzzle to create a new block in order to complete transactions on the blockchain network
- Proof of Stake (PoS): The Proof of Stake is a consensus mechanism in which validator are selected in a deterministic manner to create blocks based on their stake or equity ownership in the blockchain
- Delegated Proof of Stake (DPoS): In the DPoS consensus mechanism, blockchain users vote and select delegates/witnesses to validate transactions in the blockchain
- Proof of Capacity (PoC): In the Proof of capacity (PoC) consensus mechanism, the mining equipment uses their available hard drive device space to decide the mining rights
- Proof of Elapsed Time (PoET): In PoET, the user who generates a new block is decided randomly and fairly using the waiting time
- Proof of Authority (PoA): Proof of Authority is a reputation-based consensus mechanism in which the right to generate new blocks are awarded to nodes that have proven their authority to do so
- Proof of Activity: In the blockchain, Proof of Activity is a hybrid consensus mechanism that combines features of both Proof of Work (PoW) and Proof of Stake (PoS) consensus algorithms
- Proof of Elapsed Time (PoET): In PoET, each node has to wait for a randomly generated specific time period, and the node which completes this wait time first wins the rights to create the new block
- Byzantine Fault Tolerance (BFT): BFT helps create a new block in blockchain by reaching the consensus even if some nodes in the network fail to respond or respond with incorrect information. There are many variations of BFT that are deployed based on use cases
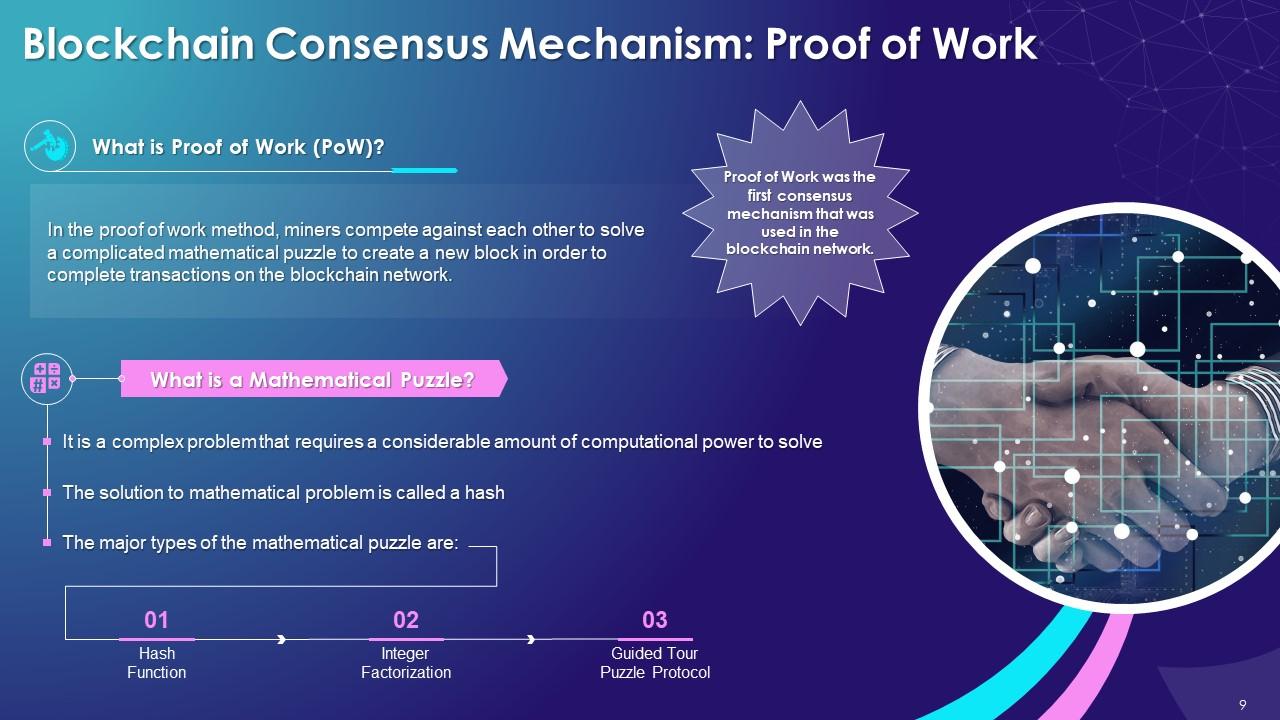
Slide 9
This slide provides information regarding the overview of PoW algorithm used in blockchain technology. It also includes details of mathematical puzzle used in mechanism such as hash function, integer factorization and guided tour puzzle protocol.
Instructor’s Notes:
- Miners: In the blockchain network, users send each other digital tokens, and a decentralized ledger maintains the record of all the user transactions into blocks. The nodes that confirm the transactions and arrange blocks are known as miners
- The major types of the mathematical puzzle are:
- Hash Function: Based on the known output, find the input
- Integer Factorization: Present a number as a multiplication of two other numbers
- Guided Tour Puzzle Protocol: In case of suspected Denial of Service (DoS) attack by a server, computing hash function via a particular order of nodes
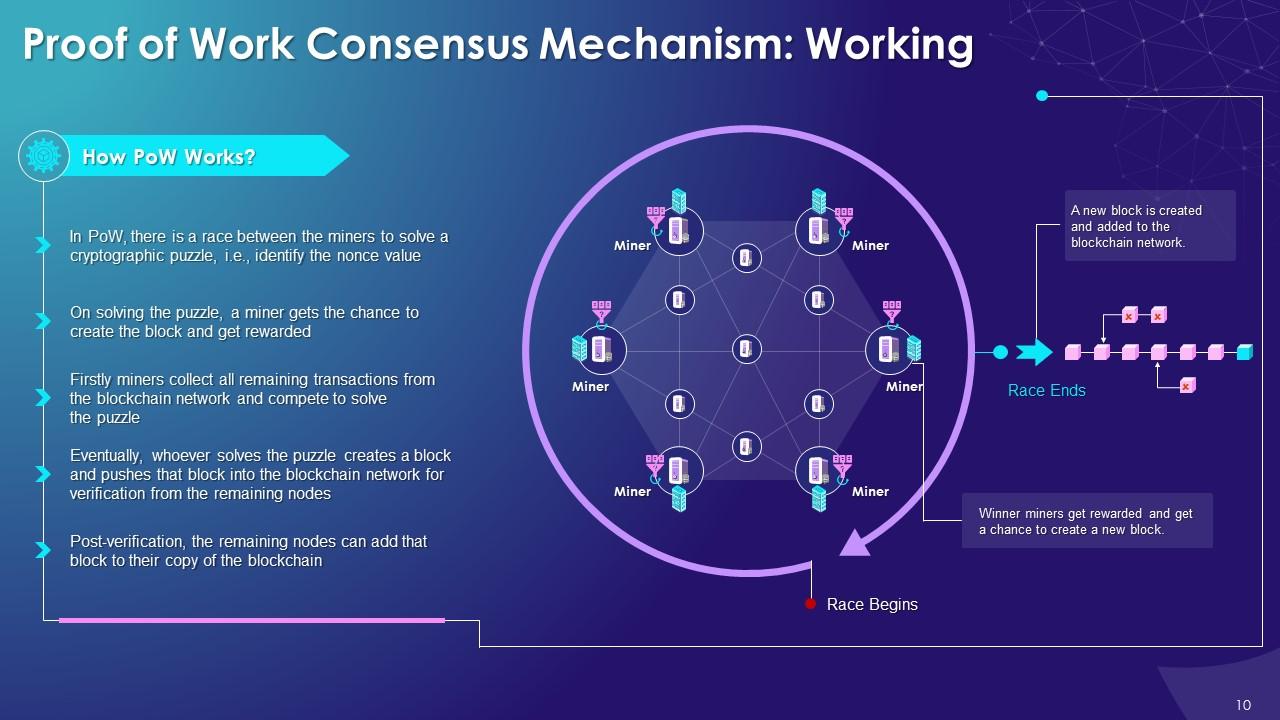
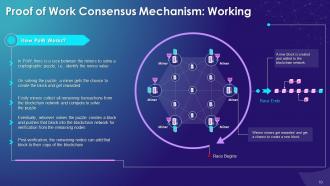
Slide 10
This slide provides information about the working of PoW consensus in the blockchain showcasing how miners get rewarded for successfully identifying nonce value and winning a chance to create a new block.
Instructor’s Notes:
Nonce: The full form of the nonce is "number only used once." It is an attribute in the block header structure so that when rehashed, it meets the difficulty level restrictions in the blockchain.
Slide 11
This slide highlights the major benefits of PoW consensus, such as defense from DoS attacks and preventing abuses and misuses. It also covers details of proof of work algorithm’s limitations of being hugely expensive and uselessness of computations. This slide also provides information regarding cryptocurrency coins that use PoW consensus, which is bitcoin.
Instructor’s Notes:
The major benefits offered by PoW are as follows:
- Defense against DoS Attacks: Proof of Work prevents a DoS (Denial of Service) attack on the blockchain network. The cost involved is just prohibitive and it also requires a lot of computational power to execute one
- Prevent Abuses and Misuses: In Proof of Work, it is crucial to have a large computational power to solve the puzzles and create new blocks. Thus, preventing the holders of huge amounts of money to become solely in charge of making decisions for the entire network
The PoW consensus has following limitations:
- Hugely Expensive: In PoW, mining involves high costs due to need of specialized skilled talent and complicated hardware and software to run complex algorithms
- Uselessness of Computations: In PoW, miners spend considerable resources to compute the calculations but these can't be applied to any other field
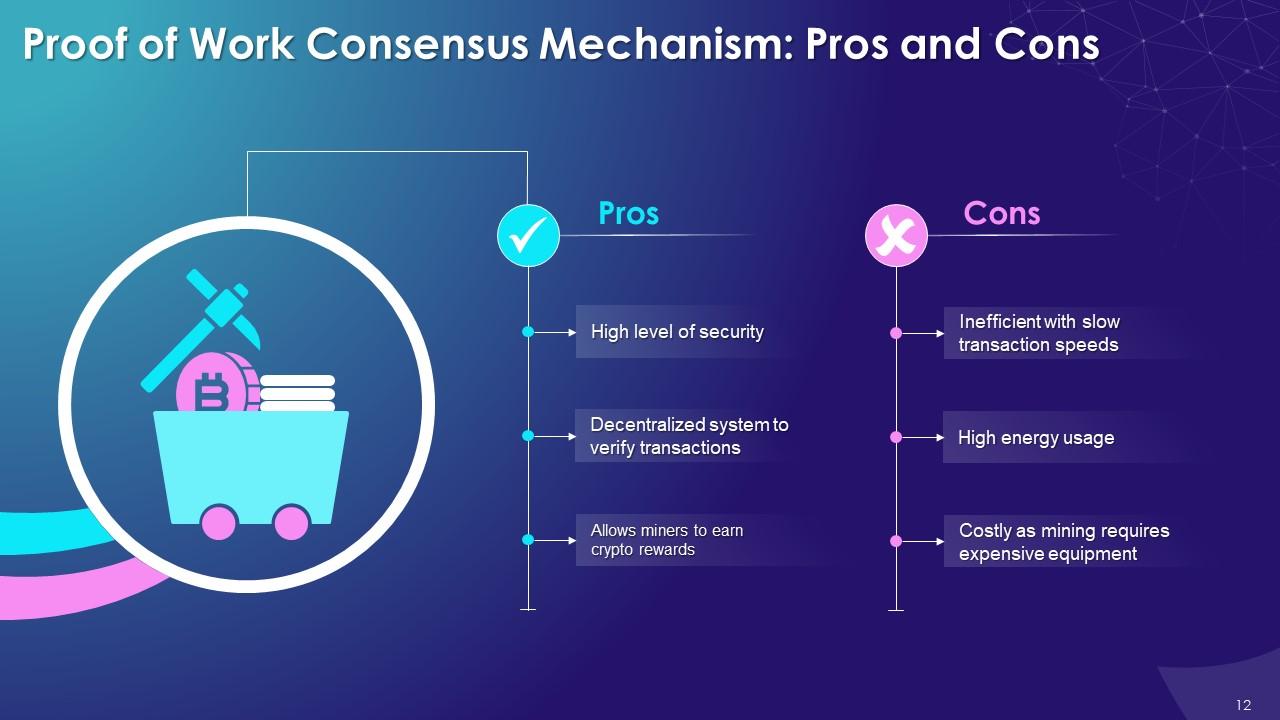
Slide 12
This slide tabulate the advantages and disadvantages of the PoW algorithm used in Blockchain. The major benefit of the PoW mechanism is the high level of security, and the primary limitation is high cost and energy usage.
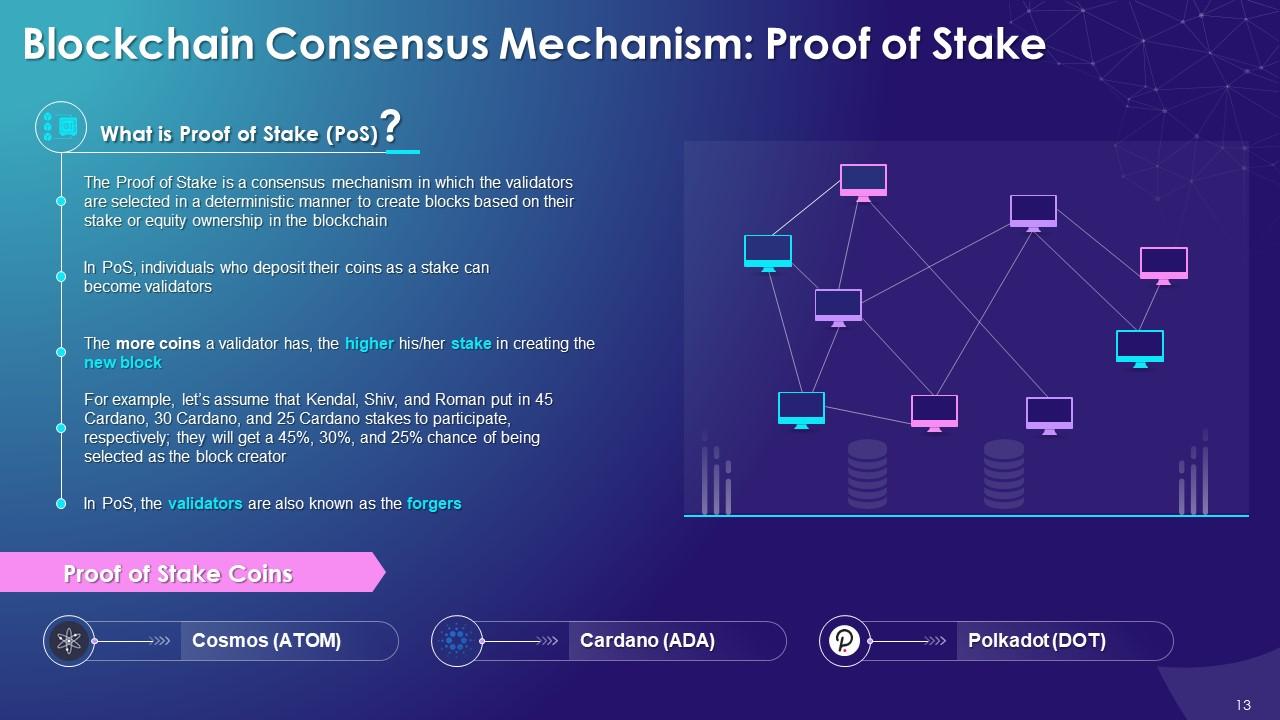
Slide 13
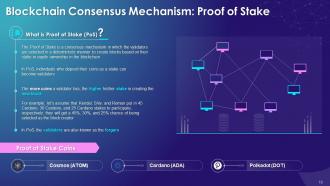
The purpose of this slide is to provide an overview of the PoS consensus mechanism used in the blockchain. It also includes information regarding the validators (forgers) and coins that use the proof of concept algorithm in the blockchain.
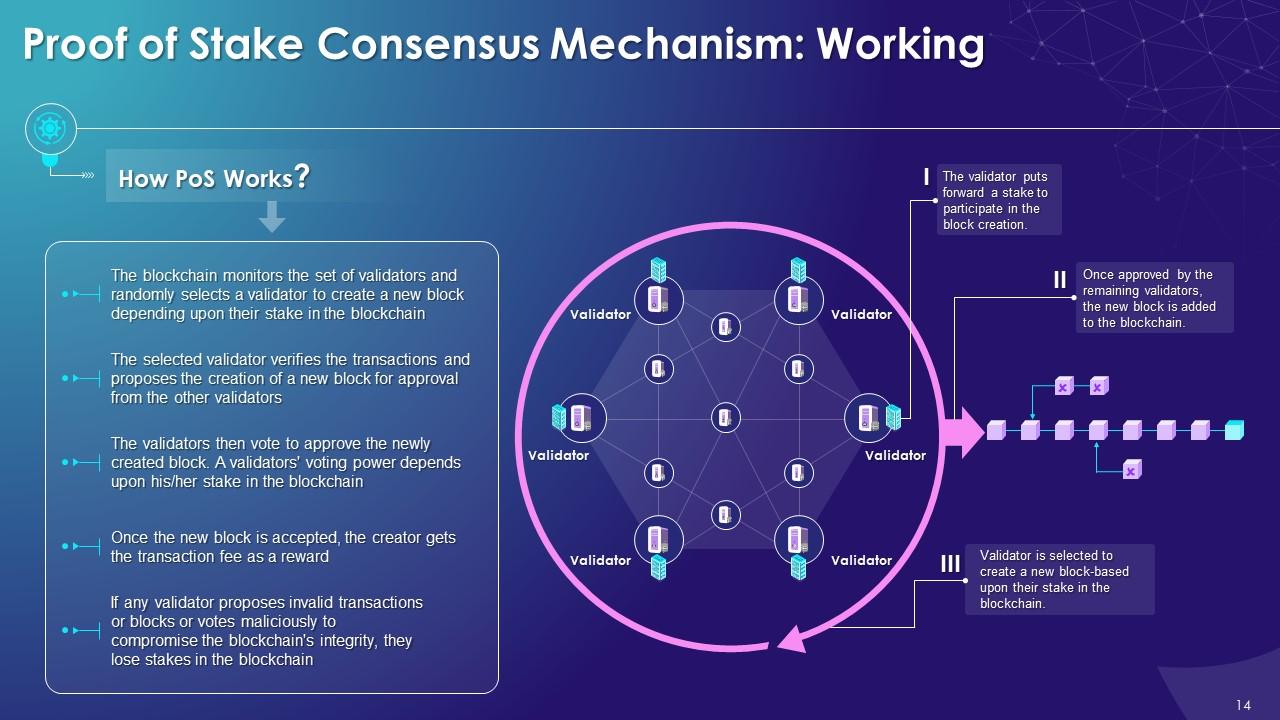
Slide 14
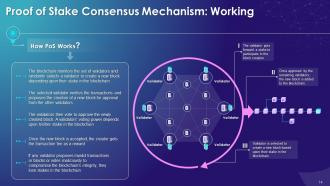
This slide illustrates the working of the PoS consensus algorithm in the blockchain, providing information regarding the selection of validators or forgers and approval voting for creating the new block.
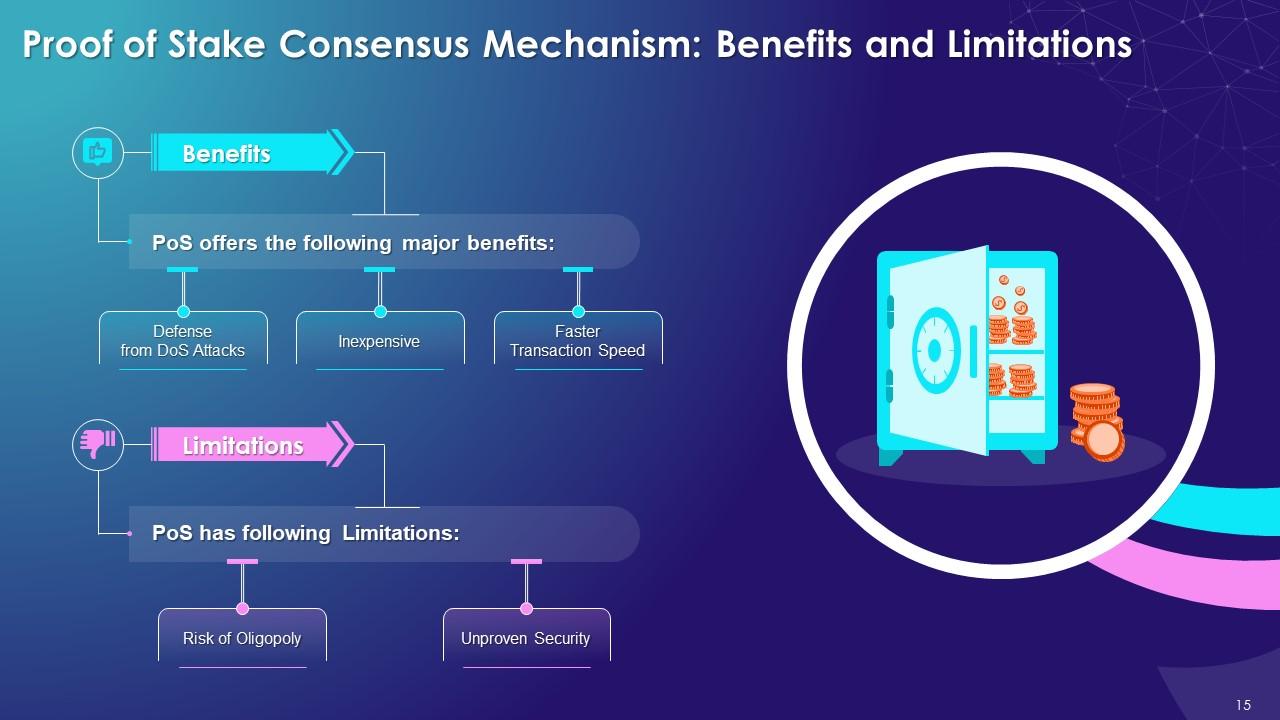
Slide 15
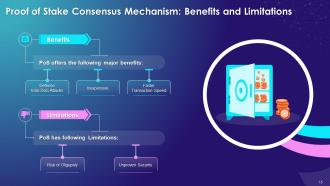
The slide contains details related to major advantages offered by the proof of stake consensus which are higher energy efficiency, inexpensive, and faster transaction speed. It also includes information about the disadvantages of PoS, such as unproven security and the risk of oligopoly.
Instructor’s Notes:
The major benefits offered by the PoS consensus mechanism are as follows:
- Higher Energy Efficiency: PoS uses far less energy to complete a blockchain transaction as there are no complex mathematical computations to perform
- Inexpensive: PoS is relatively cheap as there is no need for skilled talent and specialized hardware and software to execute the PoS consensus mechanism in the blockchain
- Faster Transaction Speed: PoS guarantees more transactions per second – up to 100,000 compared to only 64 transactions per second in PoW
The major limitations of the PoS consensus mechanism are as follows:
- Unproven Security: PoS as a consensus mechanism is relatively new hence its security still remains unproven for long-term usage
- Risk of Oligopoly: Individuals with a greater stake in the blockchain network can hold more influence than individuals with smaller stakes
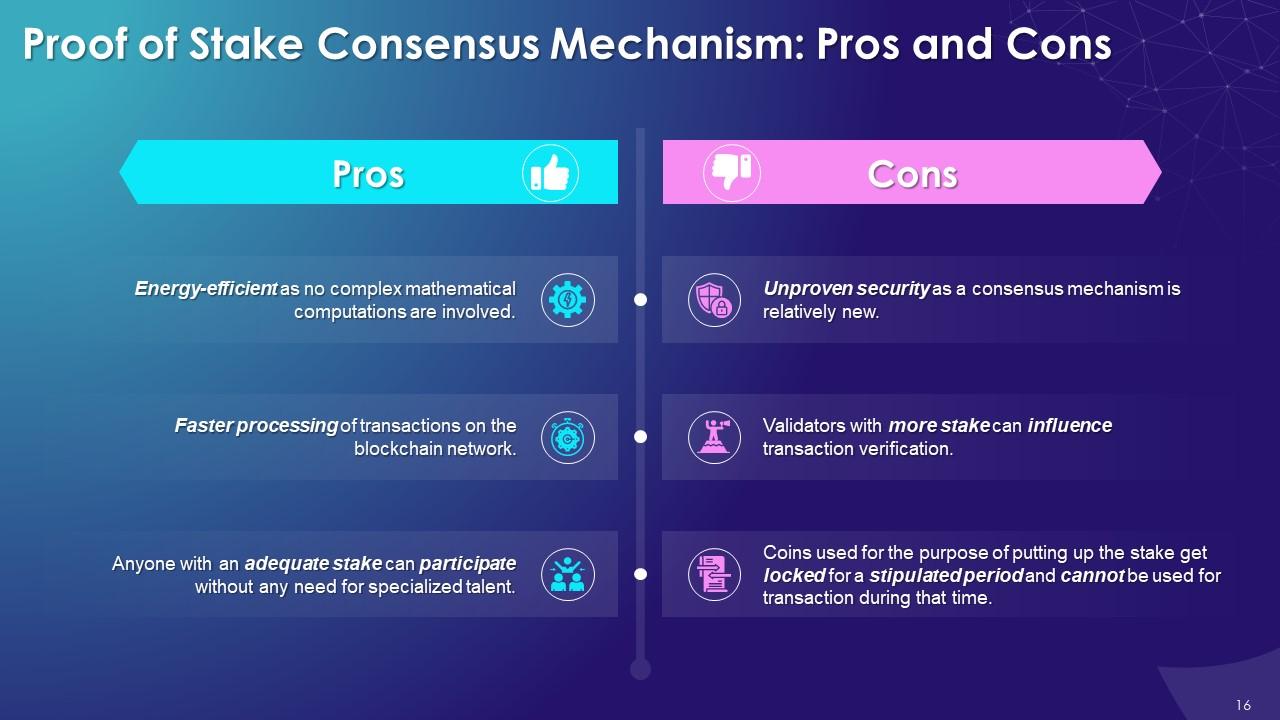
Slide 16
This slide tabulates the benefits and limitations of the PoS algorithm used in blockchain. The major advantages of the PoS consensus algorithm are high energy efficiency and faster transaction speed. The major disadvantages of the PoS consensus mechanism are unproven security and staking of coins for a stipulated time period.
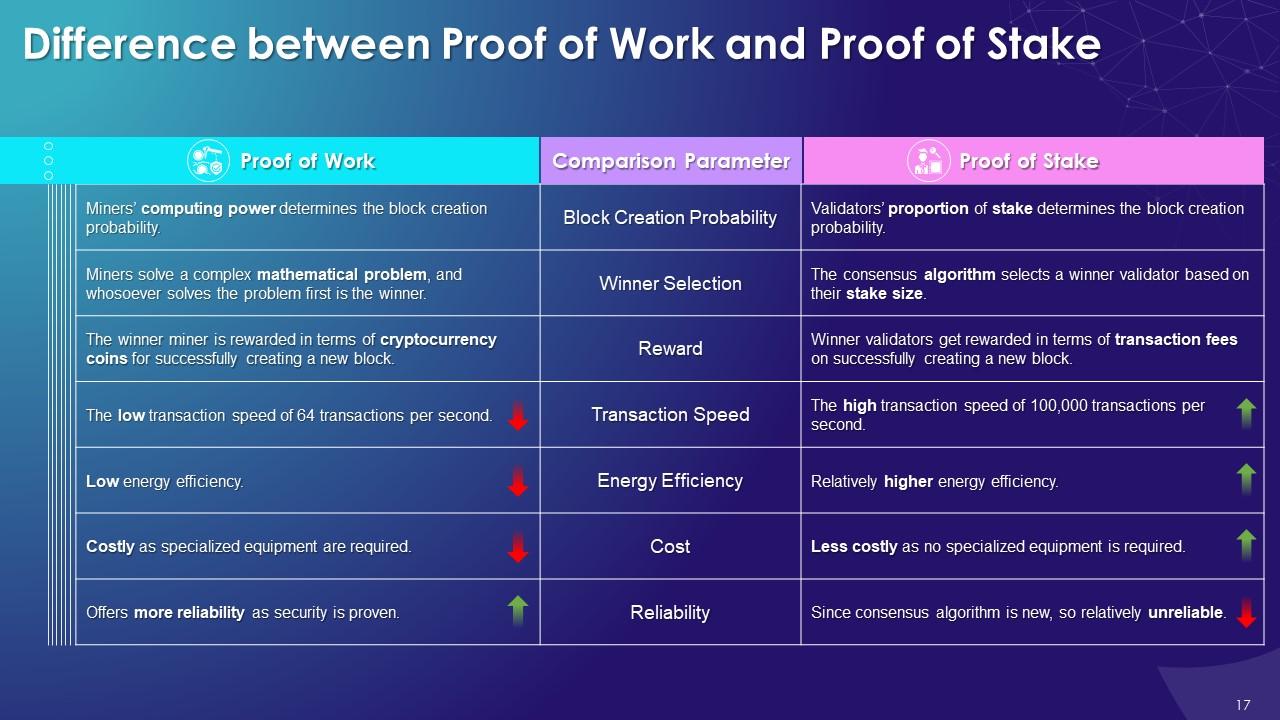
Slide 17
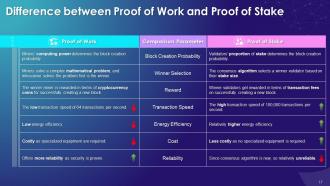
This slide highlights the difference between the Proof of Stake and Proof of Stake on multiple parameters such as block creation probability, winner selection, reward, transaction speed, energy efficiency, cost and reliability.
Slide 19
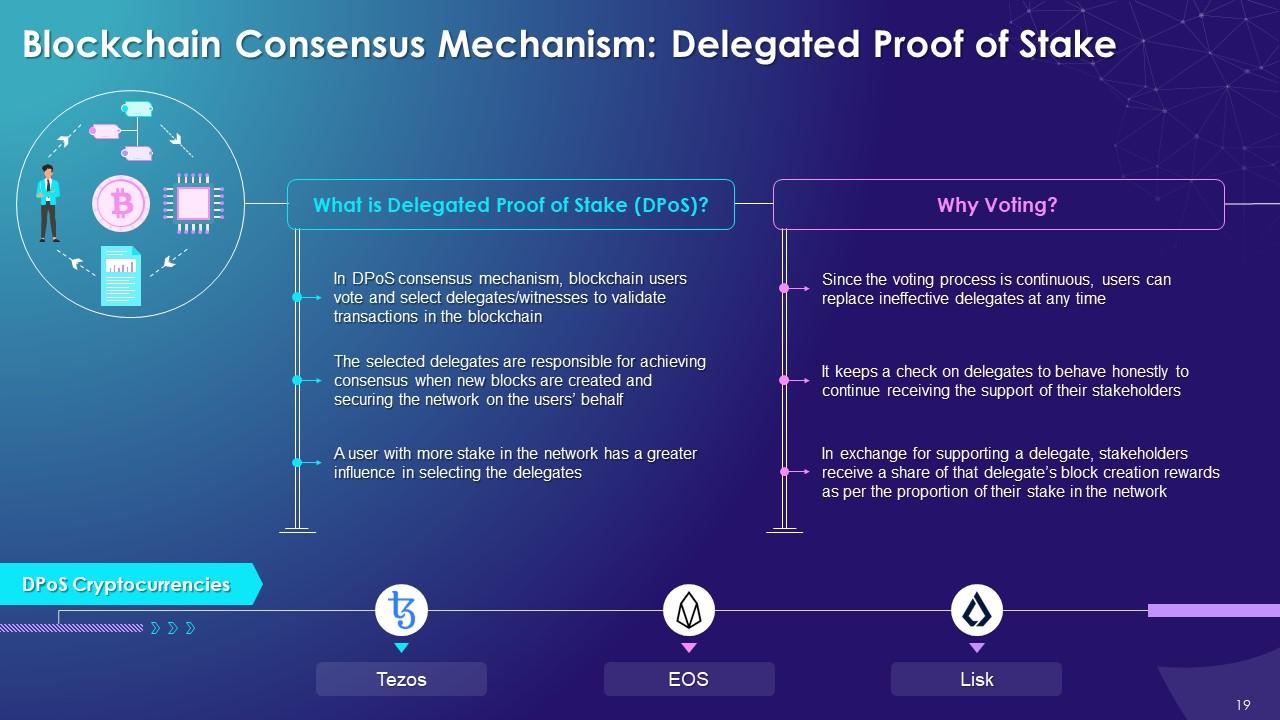
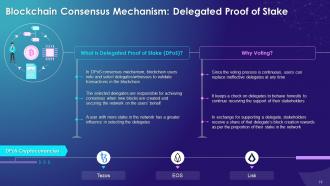
This slide illustrates the concept of Delegated Proof of Stake (DPoS) consensus mechanism in the blockchain. It also includes information regarding importance of voting in the DPoS algorithm and the details of multiple cryptocurrencies that use DPoS.
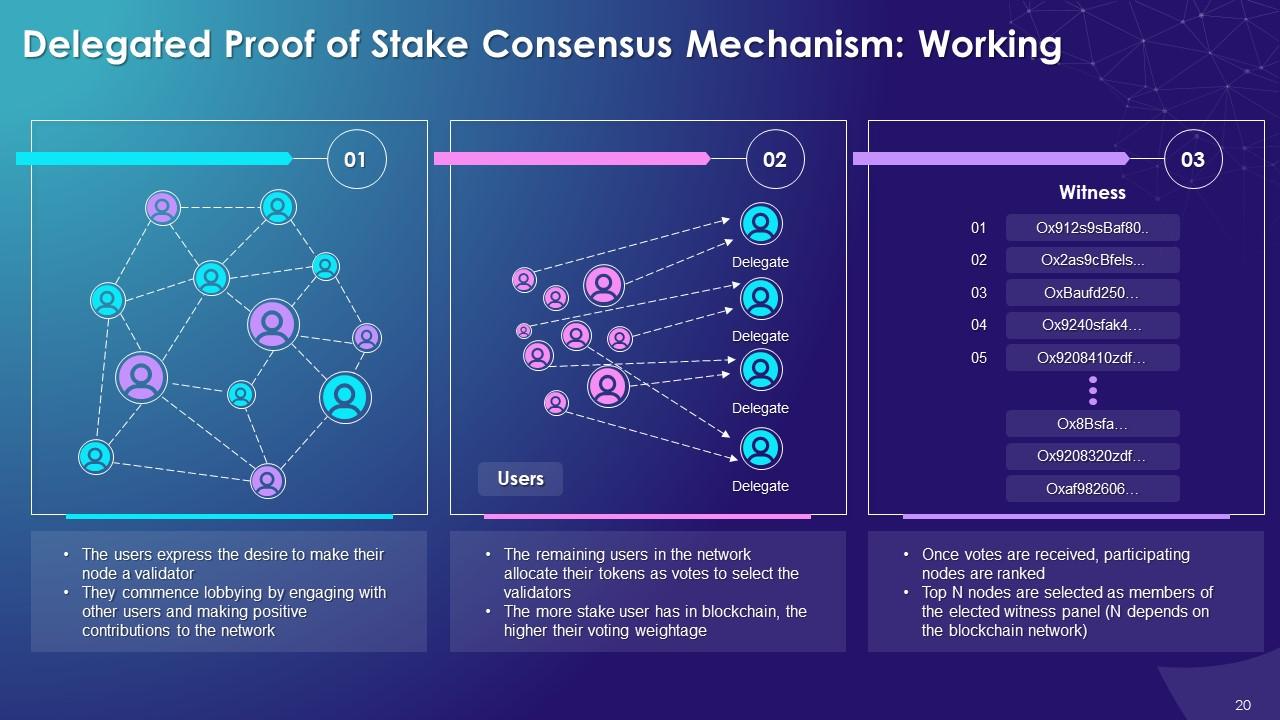
Slide 20
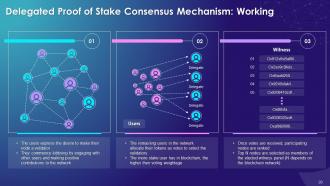
This slide visually presents the working of DPoS consensus mechanism in the blockchain highlighting significance of voting and ranking of nodes to select members of the elected witness panel.
Slide 21
This slide provides information regarding the major advantages and disadvantages offered by the DPoS consensus mechanism. The major pros of the DPoS algorithm are high speed, democratization of rewards, high energy efficiency, etc. The key cons of the DPoS algorithm are the formation of cartels and ease of organizing an attack.
Instructor’s Notes:
The major advantages offered by the DPoS consensus mechanism are as follows:
- High Speed: DPoS provides quicker processing of transactions as only selected delegates have to confirm the transactions on the network
- Democratization of Rewards: In DPoS, users elect only those delegates who will give them the most rewards, leading to better democratization of rewards
- High Energy Efficiency: DPoS consumes significantly less energy than other consensus mechanisms as it doesn't require specialized equipment for implementation
- Less Expensive: DPoS doesn't require any specialized equipment to implement, making it a less costly consensus mechanism
- Check on Bad Behavior: Since malicious delegates can be voted out at any time, it forces everyone to act to maintain and enhance the security of the blockchain
The major disadvantages of DPoS consensus mechanism are:
- Formation of Cartels: Delegates can form cartels taking control of the transaction approvals process, making the whole network less decentralized
- Rich may get Richer: In DPoS, users with more tokens have more influence on delegates selection, resulting in only the rich getting the more prosperous
- Easier to Organize Attack: In DPoS, it is far easier to organize a "51 percent" attack by lobbying delegate
- Low Voter Turnout: The whole concept of the DPoS mechanism can fail if voter turnout is low to select the delegates
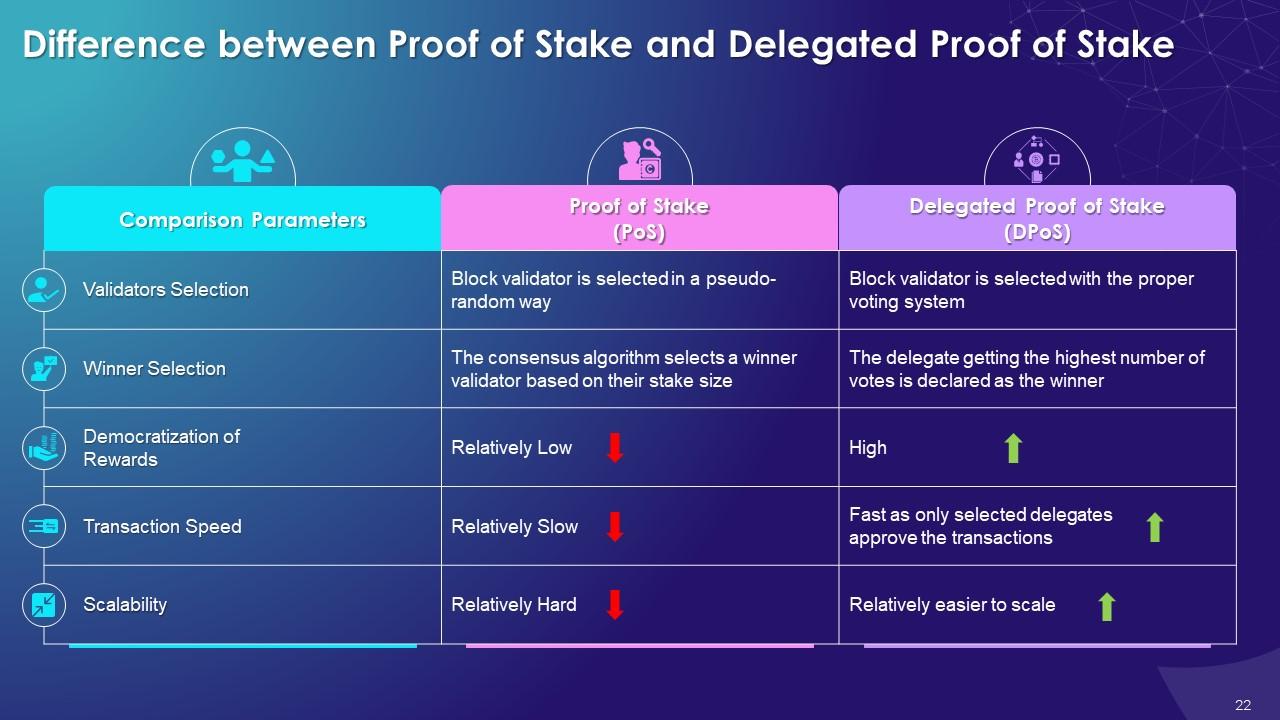
Slide 22
This slide highlights the difference between the Proof of Stake and Delegated Proof of Stake on multiple parameters such as validators selection, winner selection, democratization of rewards, transaction speed, and scalability.
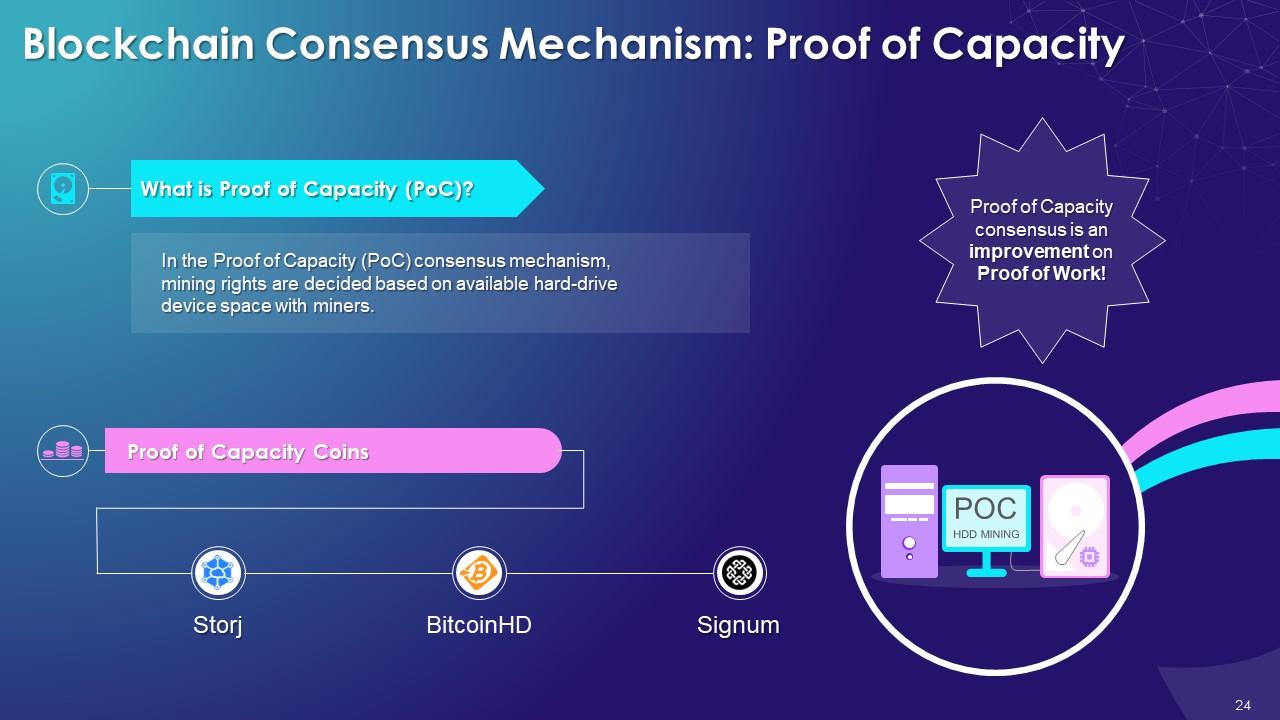
Slide 24
This slide illustrates the concept of the PoC consensus algorithm used in the blockchain. It also includes details of multiple Proof of Capacity coins such as Storj, BitcoinHD, and Signum.
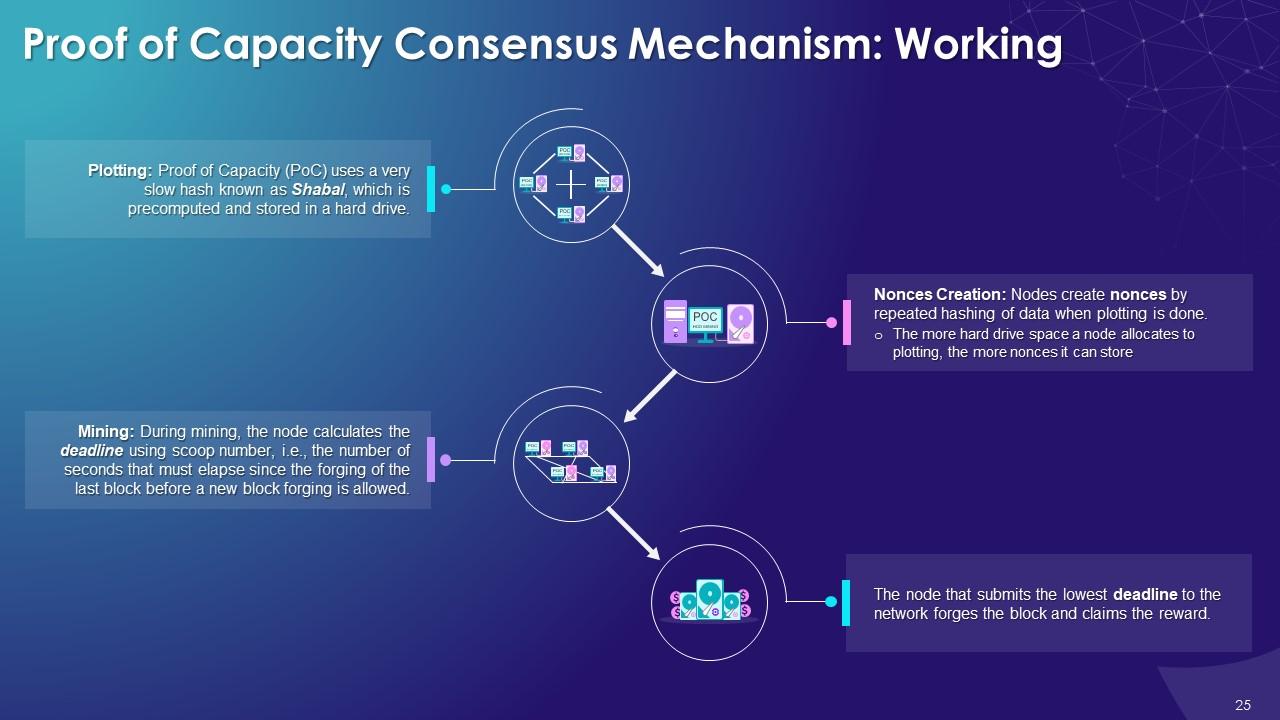
Slide 25
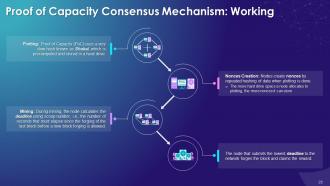
This slide depicts the implementation process (plotting, nonces creation, and mining) of the Proof of Capacity algorithm to achieve the consensus in the blockchain. It also includes details pertaining to the Shabal hash, scoop number, and deadline used in PoC.
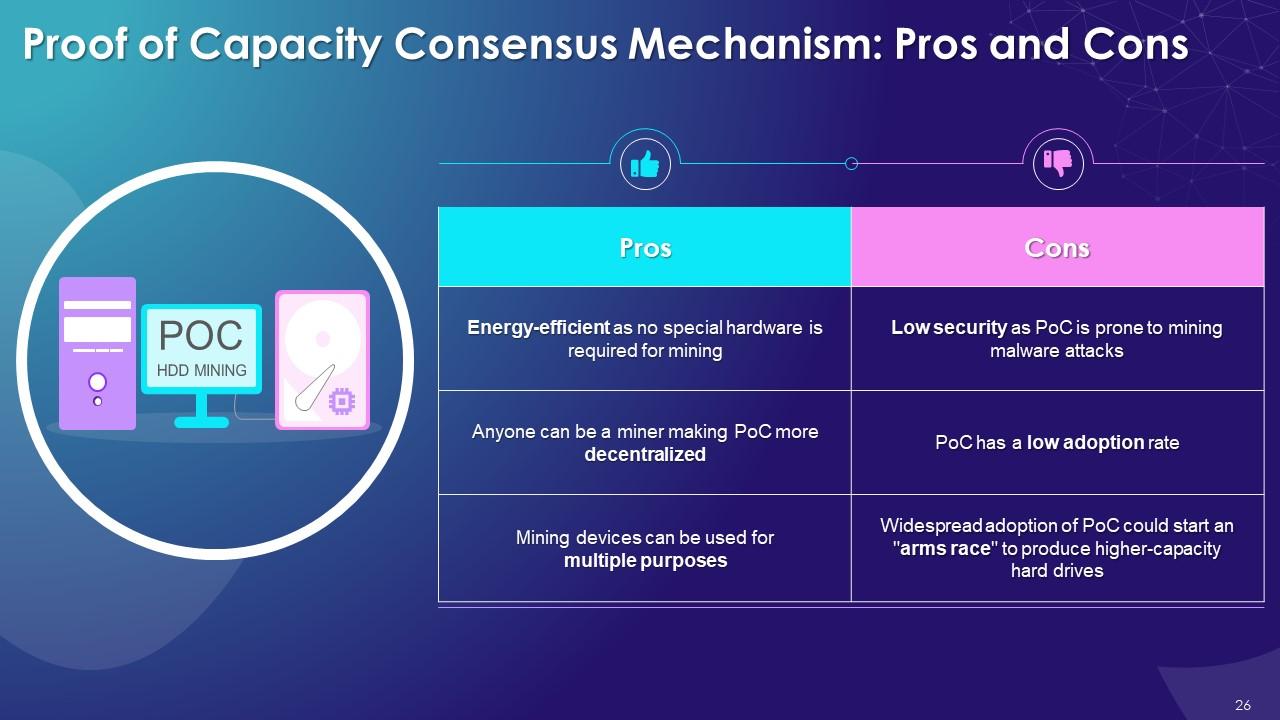
Slide 26
This slide lists down the advantages and disadvantages of the PoC consensus algorithm. The primary benefit of using Proof of Capacity is its high energy efficiency, and the major limitation is its vulnerability to mining malware attacks.
Slide 27
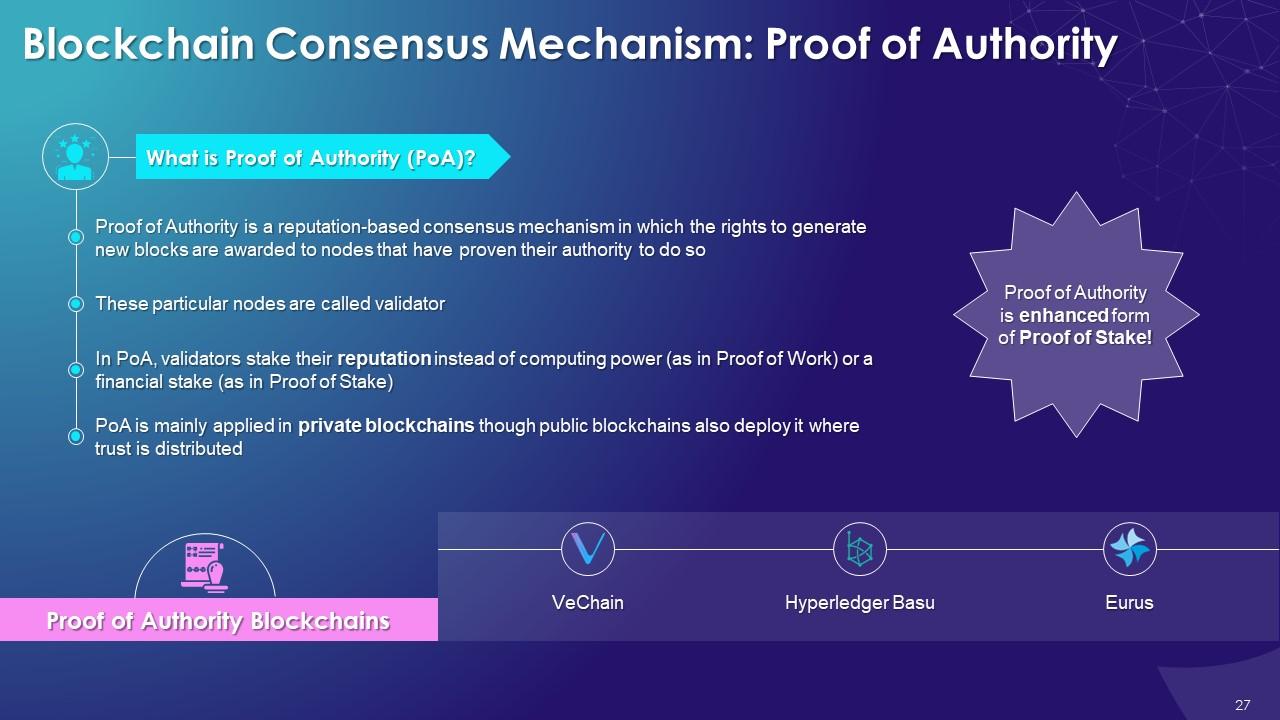
This slide provides information regarding the reputation-based consensus algorithm, Proof of Authority. It also includes details of multiple blockchains such as Hyperledger Basu, VeChain, and Eurus that use the PoA consensus mechanism.
Slide 28
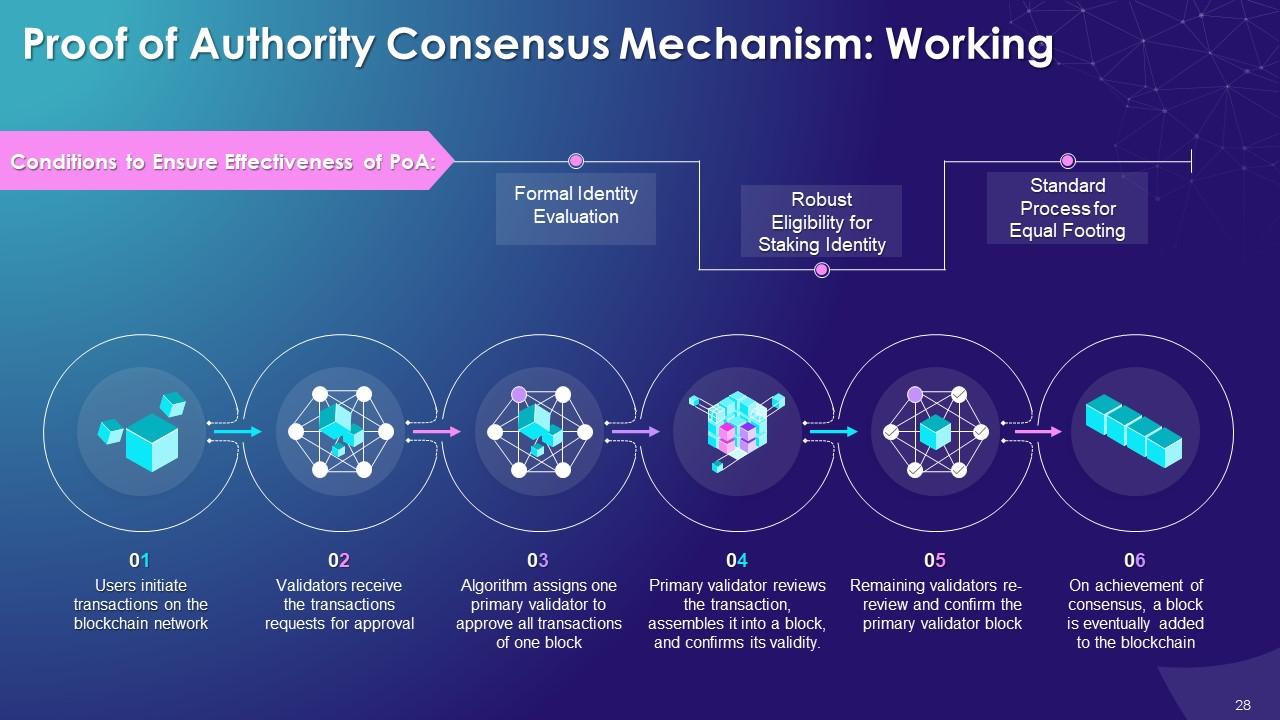
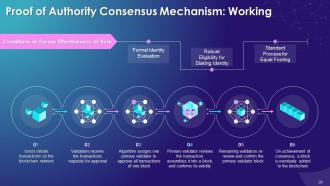
This slide provides details regarding the working of the PoA consensus algorithm. It also includes information about the multiple conditions that must be fulfilled to ensure the effectiveness of the Proof of Authority consensus mechanism in the blockchain.
Instructor’s Notes:
The conditions that must be set up to ensure the effectiveness of PoA:
- Formal Identity Evaluation: There should be a robust process with appropriate checks to verify the identity of validators
- Robust Eligibility for Staking Identity: There must be stringent conditions to become a validator. The authority must be perceived as having been earned, valued and unpleasant to lose
- Standard Process for Equal Footing: The process of establishing the validators' authority needs to be the same for all so that everyone is on an equal footing
Slide 29
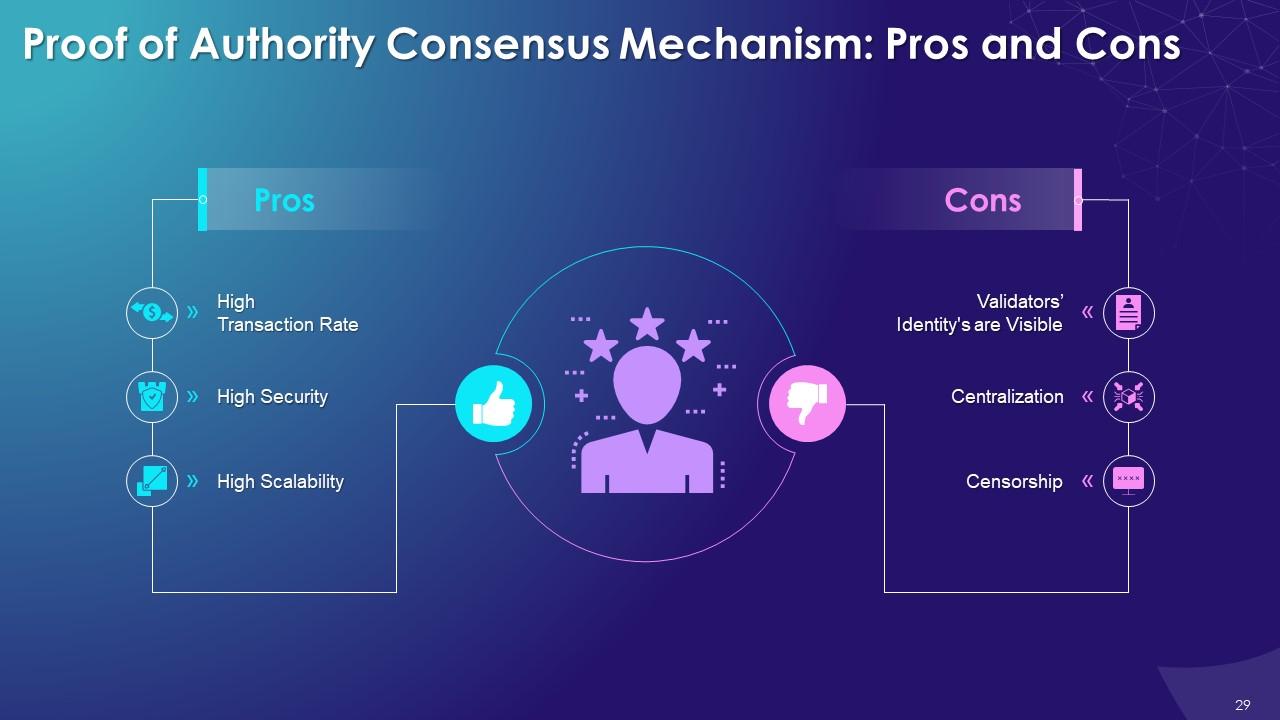
This slide lists the multiple advantages and disadvantages of the PoA consensus mechanism. The major benefits of the Proof of Authority algorithm are high security, high transaction rate, and significant limitations are centralization, validator's identity.
Instructor’s Notes:
The major advantages of the Proof of Authority consensus mechanism are:
- High Transaction Rate: PoA offers a high transaction rate as the consensus of only selected validators are required to approve the transaction
- High Security: In PoA, since validators’ reputation is at stake, they behave to ensure the integrity of the blockchain network
- High Scalability: As only a limited number of validators are required, it makes PoA a highly scalable consensus algorithm
The major disadvantages of the Proof of Authority consensus mechanism suffers are as follows:
- Validators' Identity's are Visible: Since the validators' identity is public, it makes them prone to third-party manipulations
- Centralization: The PoA is a centralized model and is against the principles of decentralization, which is crucial to the blockchain
- Censorship: PoA is subjected to criticism as it facilitates censorship and blacklisting of many users
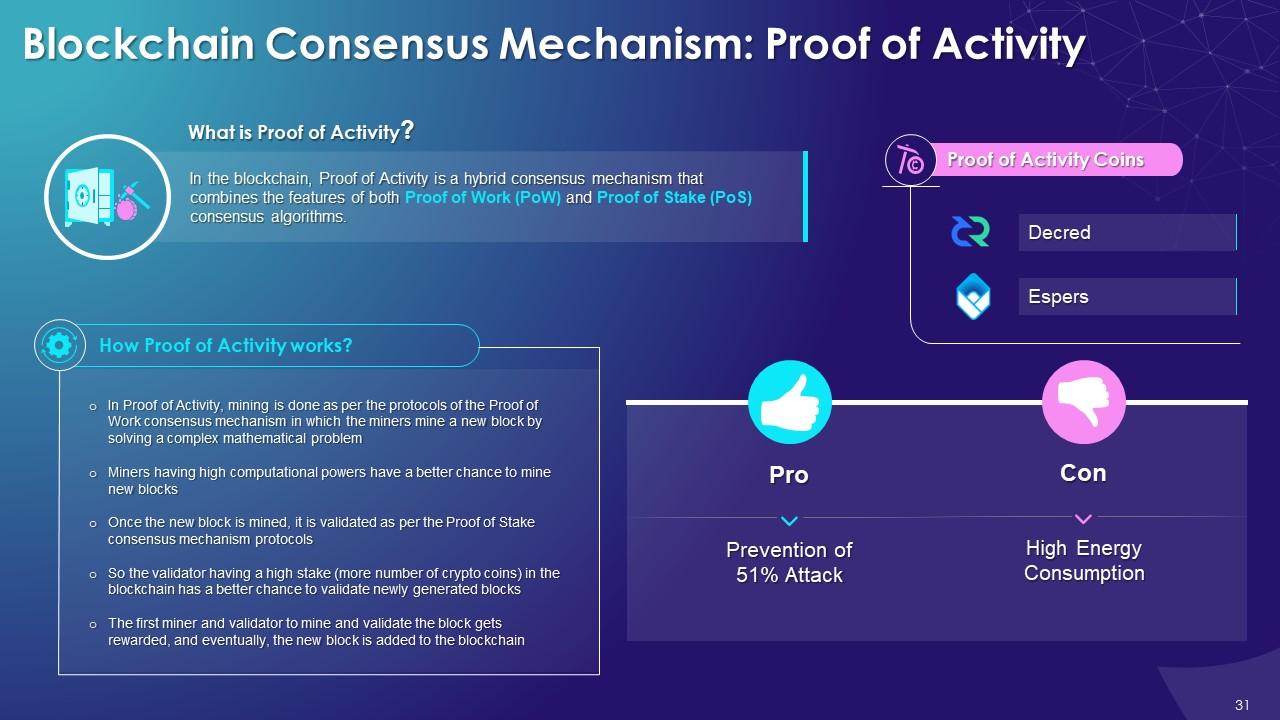
Slide 31
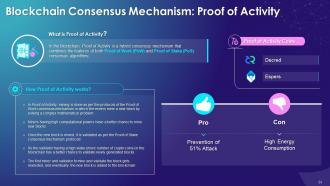
This slide depicts the overview of the proof of activity, a hybrid consensus algorithm of Proof of Work and Proof of Stake. It also includes information on working and multiple cryptocurrencies such as Decred and Espers that use PoA. Further, it covers details of the major benefit offered by PoA, which is the prevention of 51% attack, and the limitation it suffers from, which is high energy consumption.
Instructor’s Notes:
The major advantage offered by the Proof of Activity consensus mechanism is as follows:
- Prevention of 51% attack: Proof of Activity offers high security to the blockchain network as an attacker needs to have the high computational power and considerable stake to execute a 51% attack
The Proof of Activity consensus algorithm also has the limitation as follows:
- High Energy Consumption: Proof of Activity consume high power as special hardware with high computational power is required to solve the complex mathematical problem
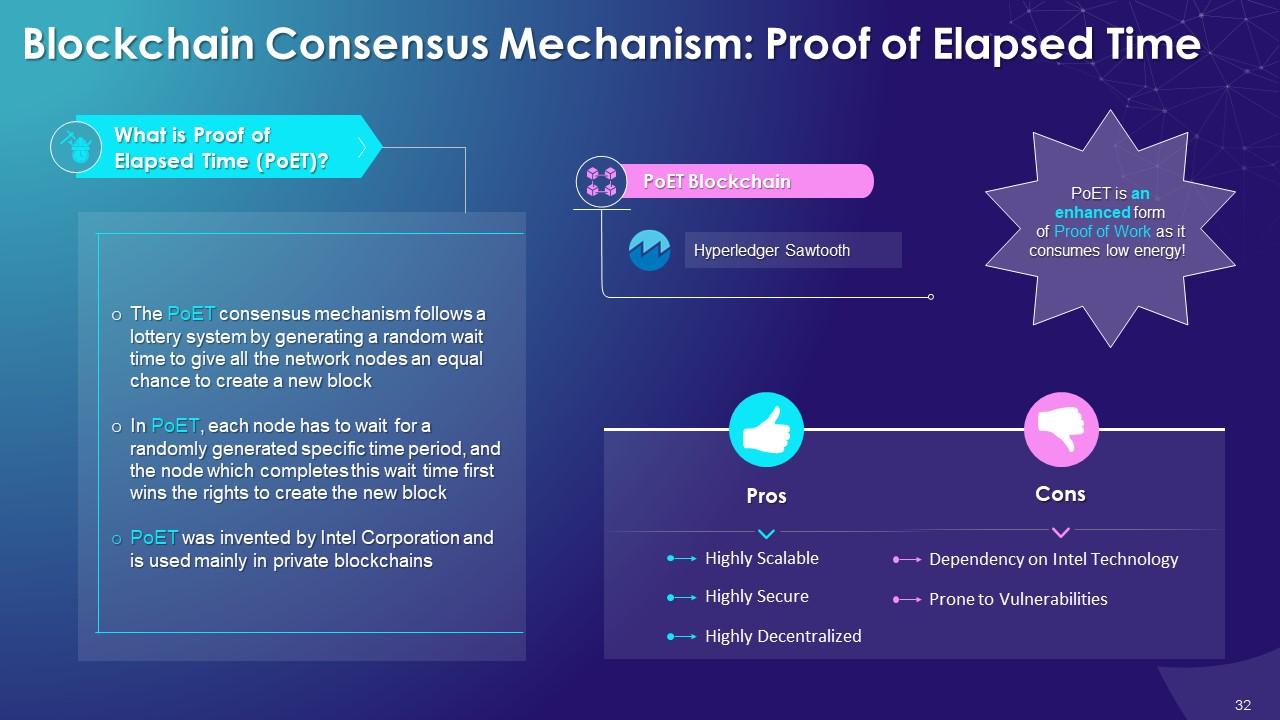
Slide 32
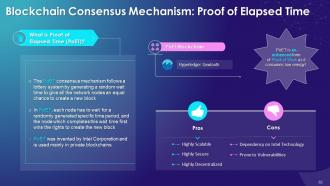
The purpose of this slide is to provide details of PoET, a private blockchain consensus algorithm developed by Intel Corporation. It also includes details of advantages offered by PoET that are high scalability and security and the disadvantages that are dependency on Intel technology and prone to vulnerabilities.
Slide 33
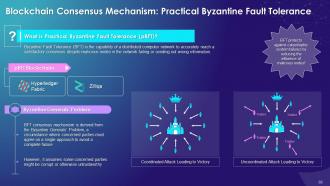
This slide contains information regarding the pBFT Blockchain Consensus Mechanism. It also contains details of the blockchains that use pBFT, such as Hyperledger Fabric and Zilliqa. Further, it covers details of Byzantine Generals’ Problem from which the consensus algorithm is derived.
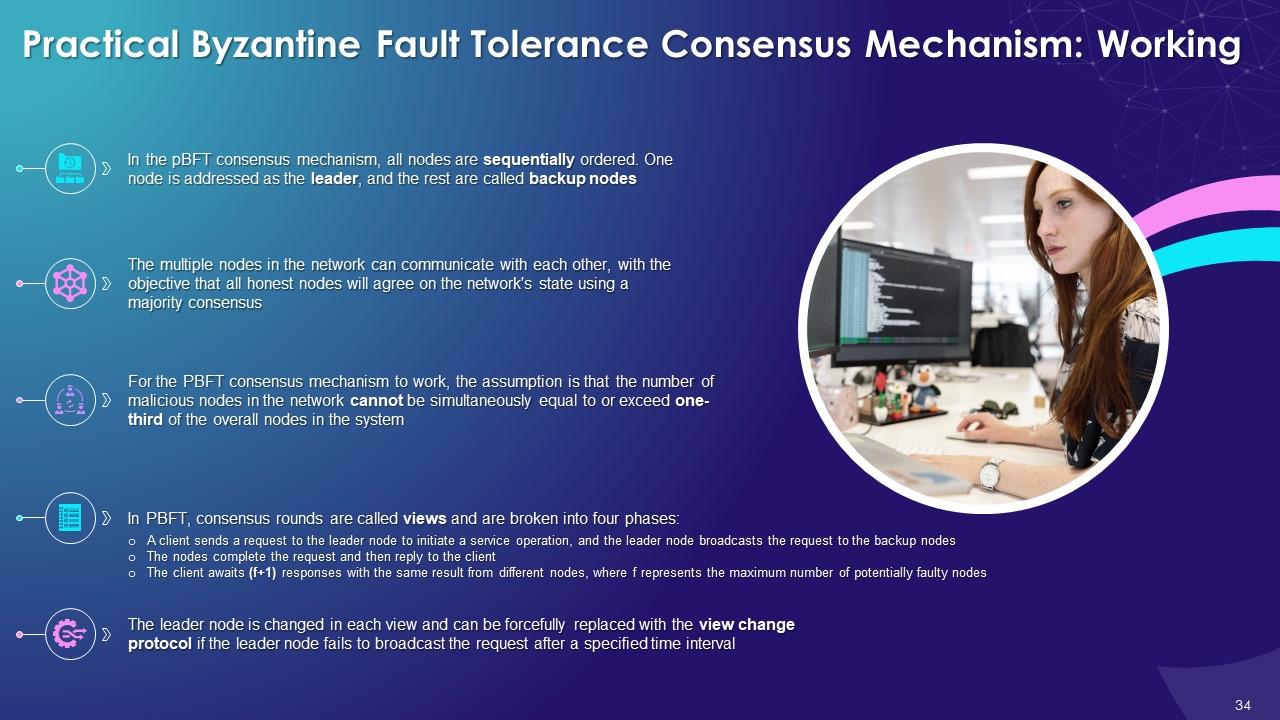
Slide 34
This slide depicts the working of the pBFT consensus algorithm covering details such as leader and backup nodes, and consensus rounds known as views, etc.
Slide 35
This slide lists the multiple advantages and disadvantages of the pBFT consensus mechanism. The benefits of the pBFT algorithm are transaction finality, energy efficiency, and low reward variance. Also, the limitations of pBFT are scaling and susceptibility to Sybil attacks.
Instructor’s Notes:
The major advantages of the pBFT consensus mechanism are as follows:
- Transaction Finality: The transactions can be agreed upon and finalized without multiple confirmations, so there is no waiting period to ensure transaction surety after including it in a block
- Energy Efficiency: pBFT can achieve network consensus without requiring energy-intensive computations
- Low Reward Variance: Every node in the pBFT can be incentivized to lower reward variance for miners since it requires a collective decision via voting on records by signing messages to reach a network consensus
The major disadvantages from which the pBFT consensus mechanism suffers are as follows:
- Scaling: pBFT is ideal for the small number of nodes but becomes inefficient for large networks as each node must talk to every other node to keep the network secure
- Sybil Attacks: The pBFT is susceptible to Sybil attacks, where a single party creates or manipulates many nodes and compromises network security
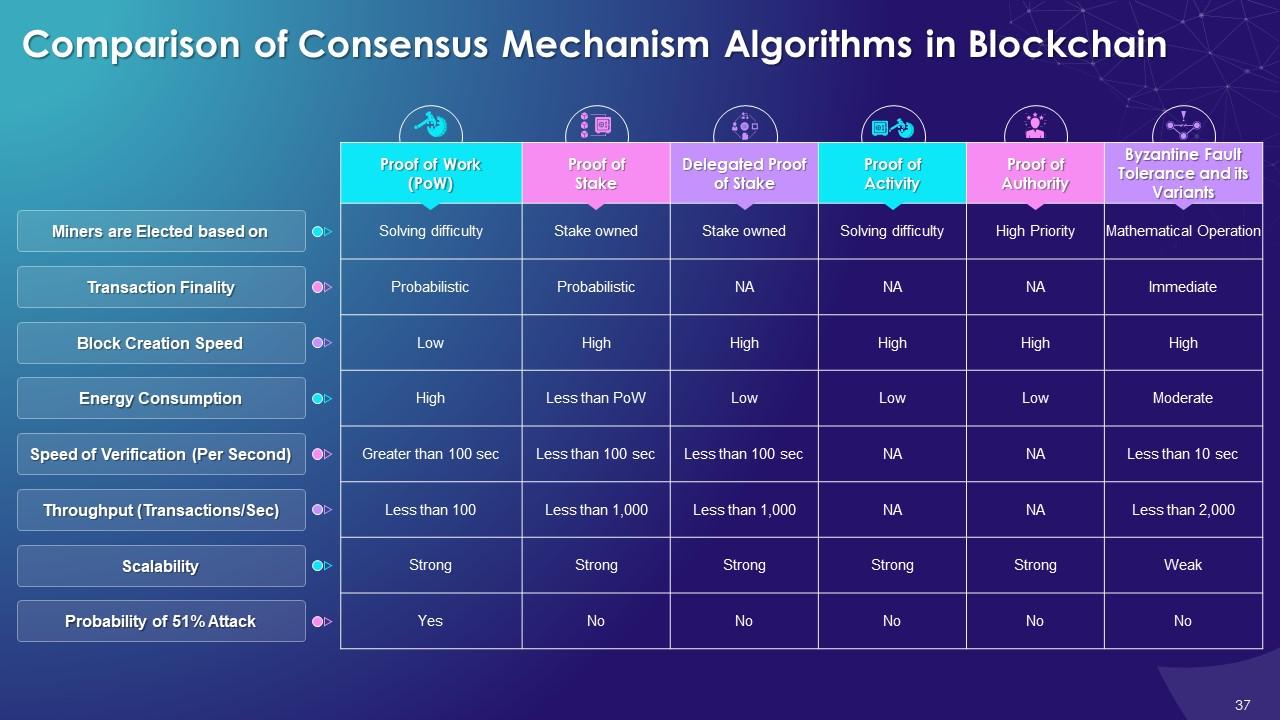
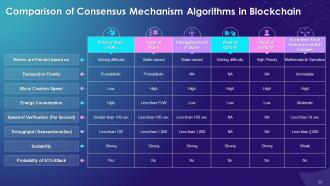
Slide 37
This slide tabulates the comparison of multiple consensus mechanism algorithms in blockchain on multiple parameters. The eight factors listed on the slide are miners' election, transaction finality, block creation speed, energy consumption, speed of verification (per second), throughout (transactions/sec), scalability and the probability of a 51% attack.
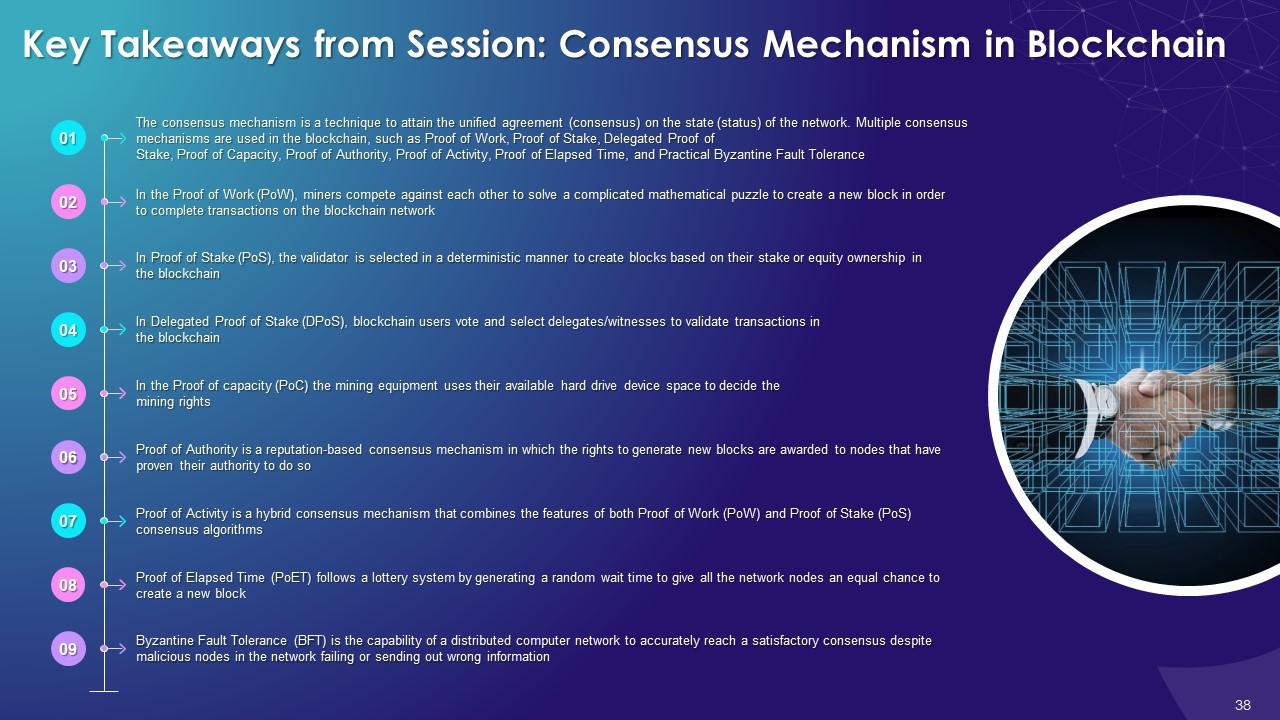
Slide 38
This slide depicts the summary of the consensus mechanism in the blockchain training session. The trainer can use it to highlight the essential concepts of the session to trainees.
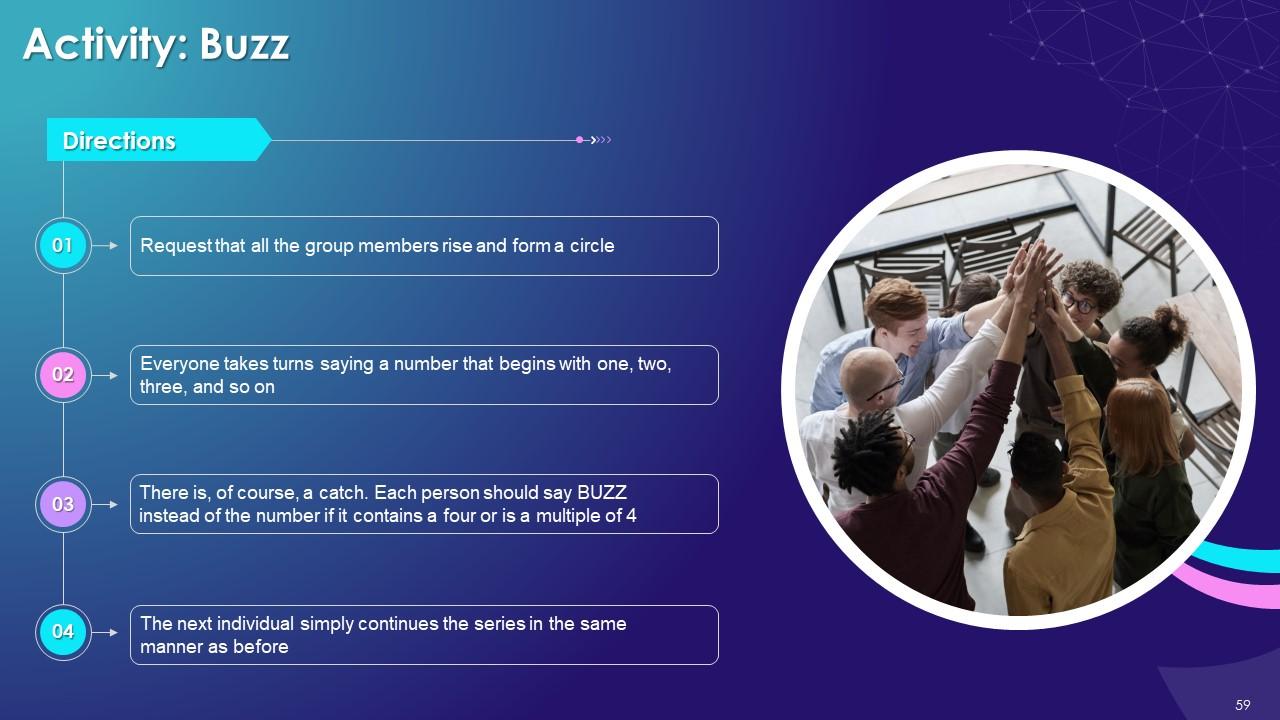
Slide 59 to 73
These slides contain energizer activities to engage the audience of the training session.
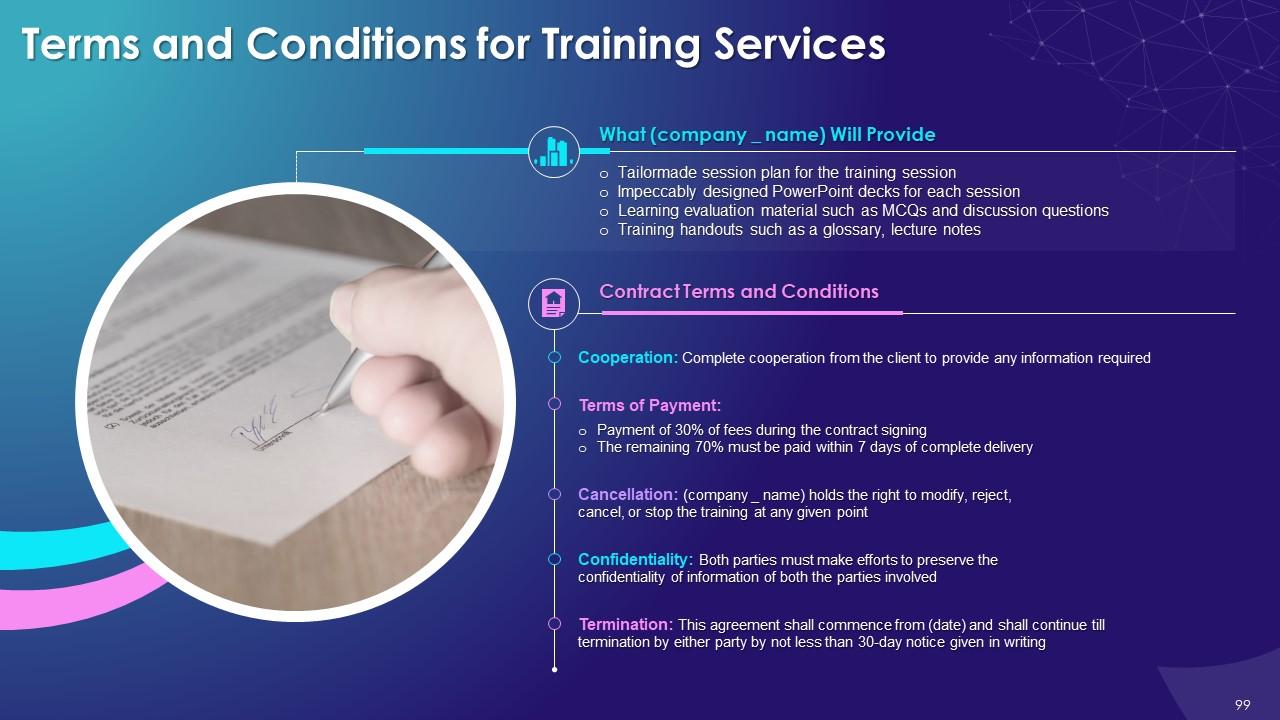
Slide 75 to 101
These slides contain a training proposal covering what the company providing corporate training can accomplish for the client.
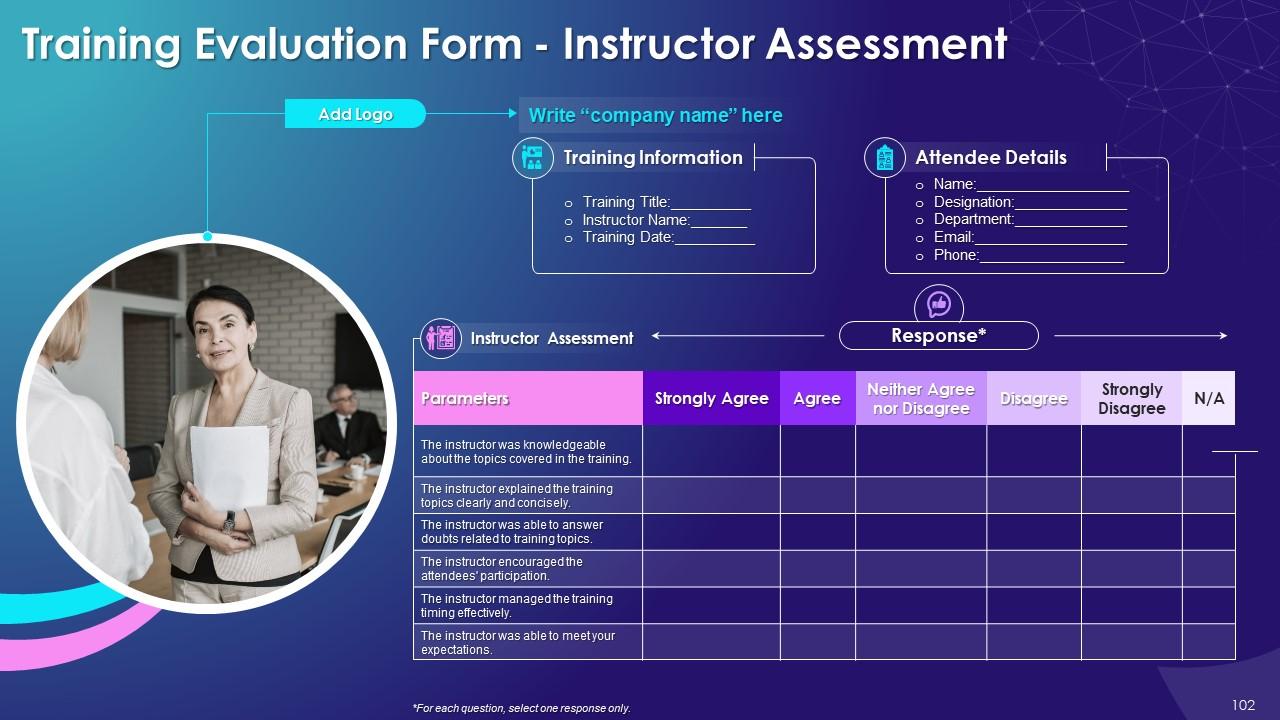
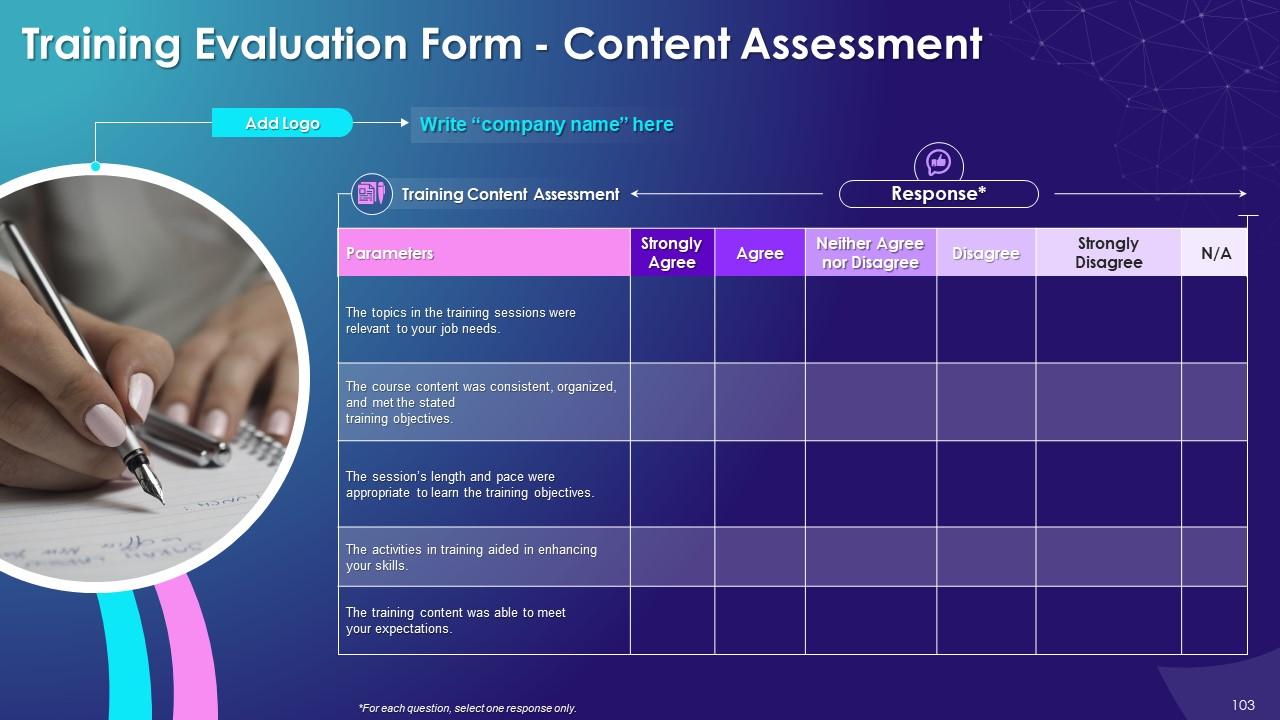
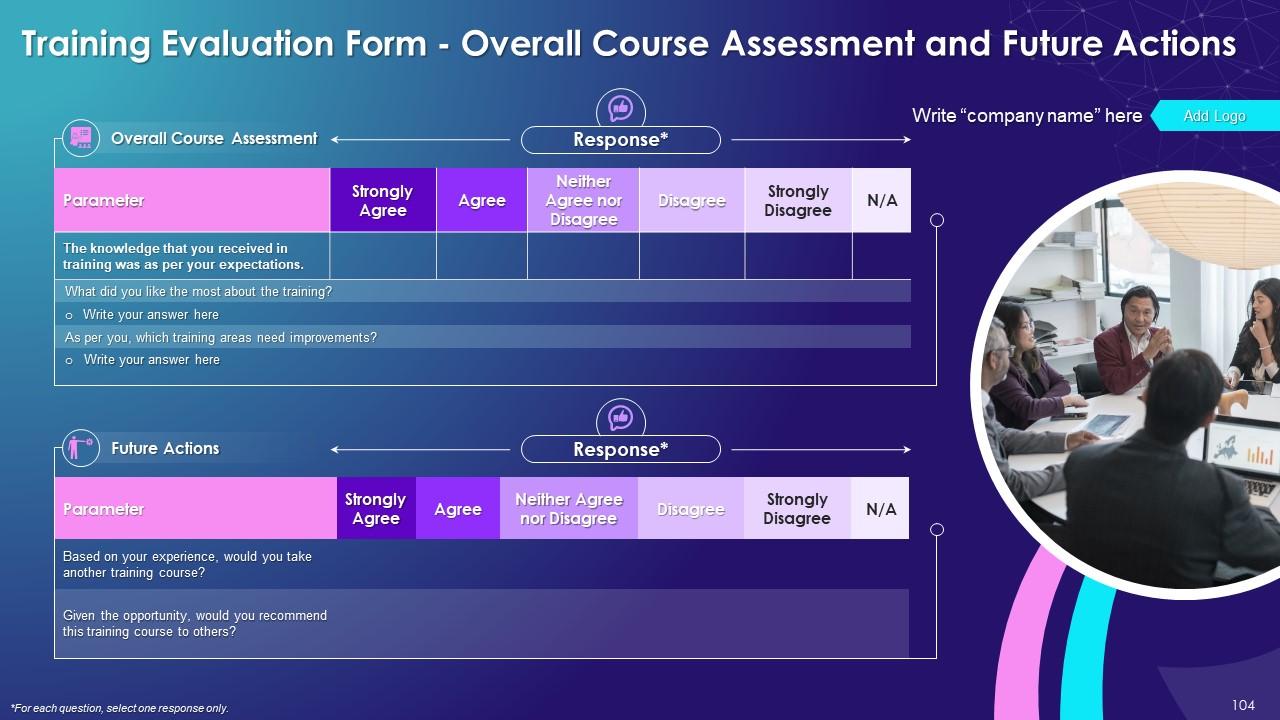
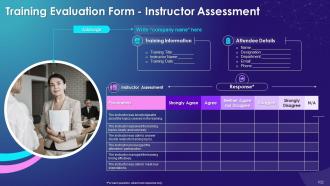
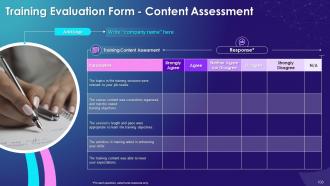
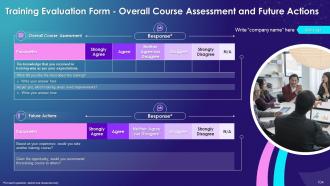
Slide 102 to 104
These slides include a training evaluation form for instructor, content and course assessment.
Consensus Mechanism in Blockchain Training Module on Blockchain Technology and its Applications Training Ppt with all 109 slides:
Use our Consensus Mechanism in Blockchain Training Module on Blockchain Technology and its Applications Training Ppt to effectively help you save your valuable time. They are readymade to fit into any presentation structure.
-
A perfect platform for all your presentation needs. Unlimited products at an affordable price.
-
Stunning collection! With a wide variety of options available, I was able to find a perfect slide for my presentation. Thank you, SlideTeam!