How Does Phishing Attack Works On Blockchain Network Guide For Blockchain BCT SS V
The following slide depicts the workflow model of phishing attack carried out on blockchain network. It includes activities such as attackers sending emails to users, opening up emails, obtaining information from system, stealing data from user, etc.
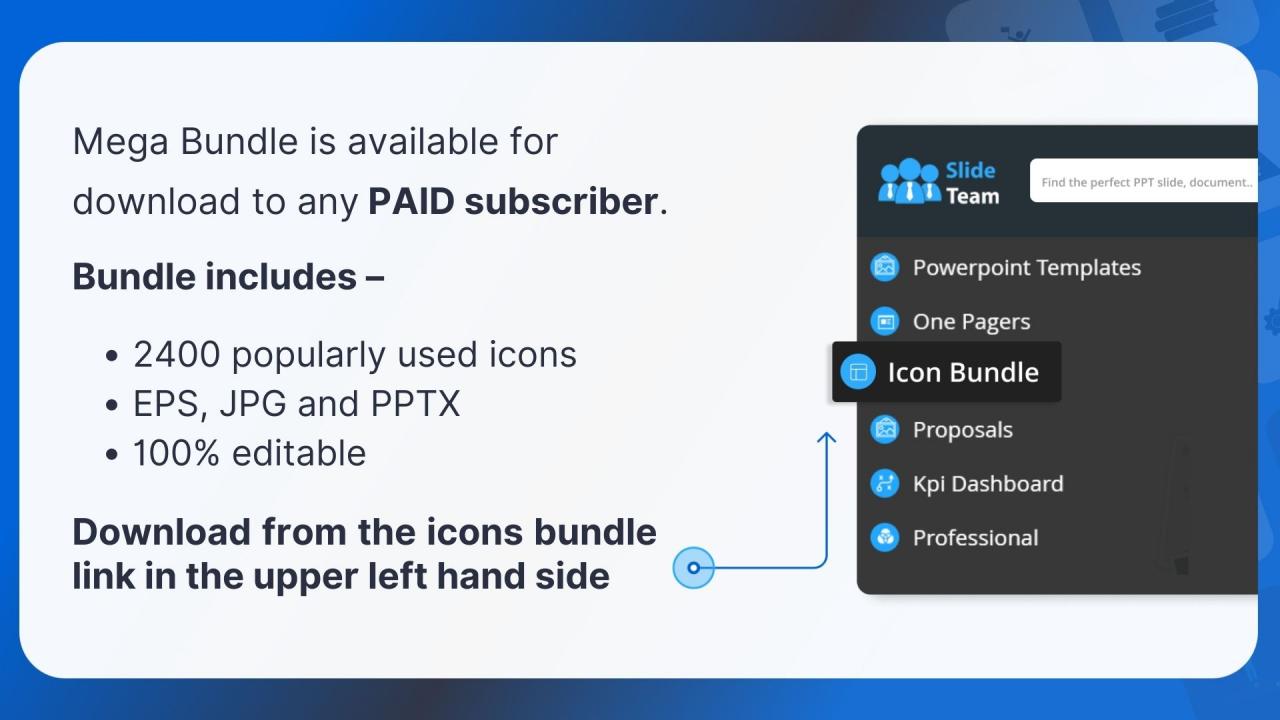
You must be logged in to download this presentation.
 Impress your
Impress your audience
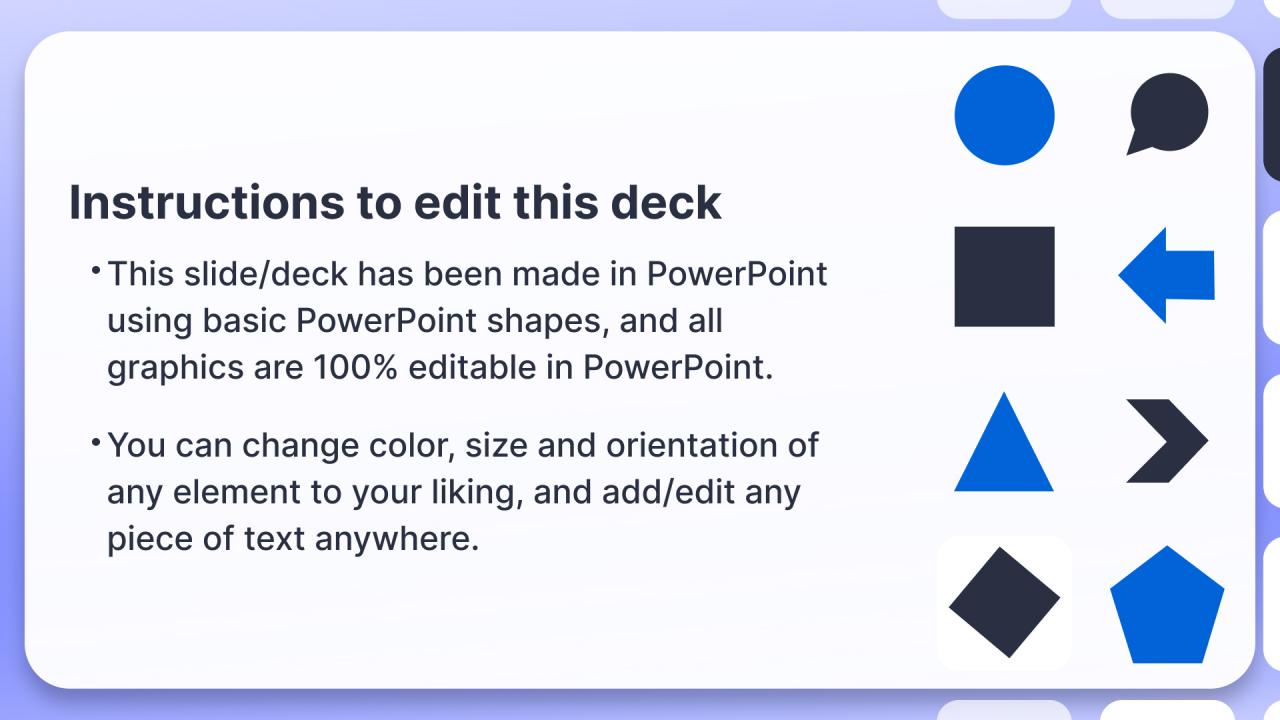
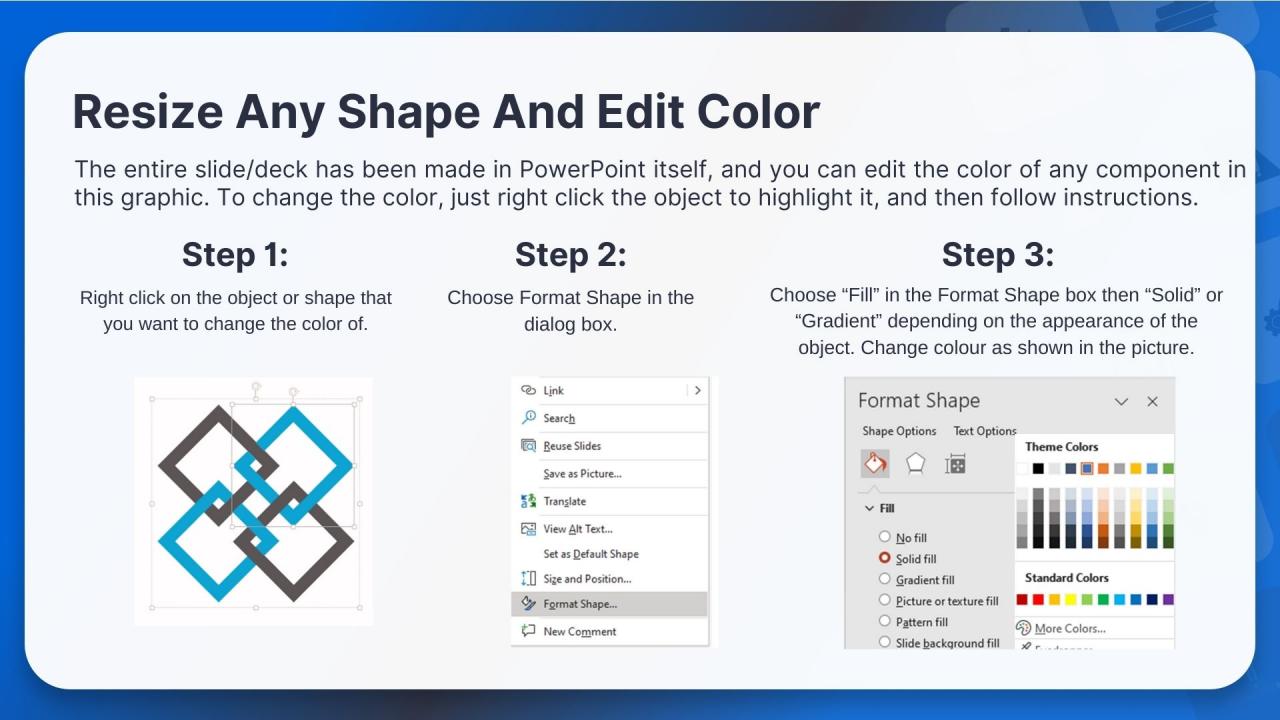
Editable
of Time
PowerPoint presentation slides
The following slide depicts the workflow model of phishing attack carried out on blockchain network. It includes activities such as attackers sending emails to users, opening up emails, obtaining information from system, stealing data from user, etc. Introducing How Does Phishing Attack Works On Blockchain Network Guide For Blockchain BCT SS V to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Attacker, Phishing Email, Internet Network using this template. Grab it now to reap its full benefits.
People who downloaded this PowerPoint presentation also viewed the following :
How Does Phishing Attack Works On Blockchain Network Guide For Blockchain BCT SS V with all 10 slides:
Use our How Does Phishing Attack Works On Blockchain Network Guide For Blockchain BCT SS V to effectively help you save your valuable time. They are readymade to fit into any presentation structure.
-
My search for complete decks ended with SlideTeam. Such a surplus collection of HD PowerPoints. Moreover, their standard and widescreen formats have helped me in delivering bullseye presentations.
-
Fantastic and innovative graphics with useful content. The templates are the best and latest in the industry.