Powerpoint Templates and Google slides for Best Security Company Of The Year
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
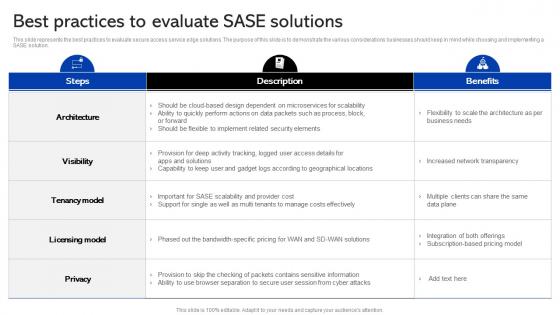 Sase Security Best Practices To Evaluate Sase Solutions
Sase Security Best Practices To Evaluate Sase SolutionsThis slide represents the best practices to evaluate secure access service edge solutions. The purpose of this slide is to demonstrate the various considerations businesses should keep in mind while choosing and implementing a SASE solution. Present the topic in a bit more detail with this Sase Security Best Practices To Evaluate Sase Solutions. Use it as a tool for discussion and navigation on Evaluate, Solutions, Considerations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
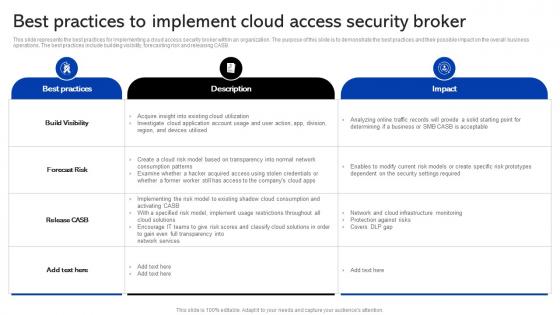 Sase Security Best Practices To Implement Cloud Access Security Broker
Sase Security Best Practices To Implement Cloud Access Security BrokerThis slide represents the best practices for implementing a cloud access security broker within an organization. The purpose of this slide is to demonstrate the best practices and their possible impact on the overall business operations. The best practices include building visibility, forecasting risk and releasing CASB. Deliver an outstanding presentation on the topic using this Sase Security Best Practices To Implement Cloud Access Security Broker. Dispense information and present a thorough explanation of Implementing, Solutions, Consumption using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
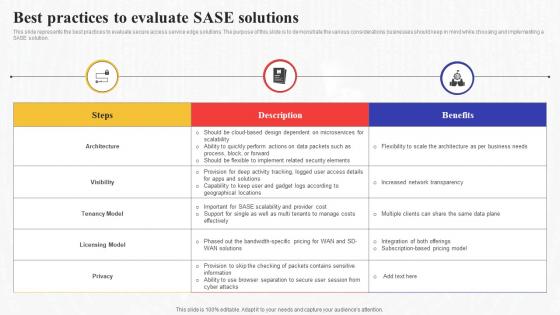 Best Practices To Evaluate Sase Solutions Secure Access Service Edge Sase
Best Practices To Evaluate Sase Solutions Secure Access Service Edge SaseThis slide represents the best practices to evaluate secure access service edge solutions. The purpose of this slide is to demonstrate the various considerations businesses should keep in mind while choosing and implementing a SASE solution. Present the topic in a bit more detail with this Best Practices To Evaluate Sase Solutions Secure Access Service Edge Sase. Use it as a tool for discussion and navigation on Solutions, Demonstrate, Considerations. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
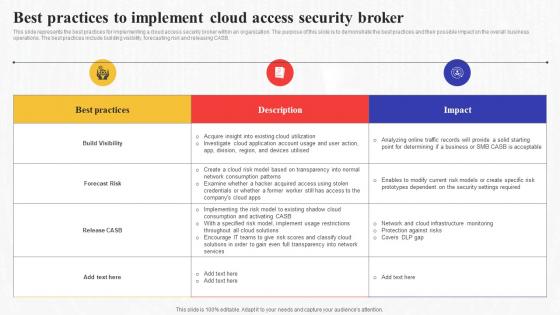 Best Practices To Implement Cloud Access Security Broker Secure Access Service Edge Sase
Best Practices To Implement Cloud Access Security Broker Secure Access Service Edge SaseThis slide represents the best practices for implementing a cloud access security broker within an organization. The purpose of this slide is to demonstrate the best practices and their possible impact on the overall business operations. The best practices include building visibility, forecasting risk and releasing CASB. Deliver an outstanding presentation on the topic using this Best Practices To Implement Cloud Access Security Broker Secure Access Service Edge Sase. Dispense information and present a thorough explanation of Consumption, Implementing, Solutions using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
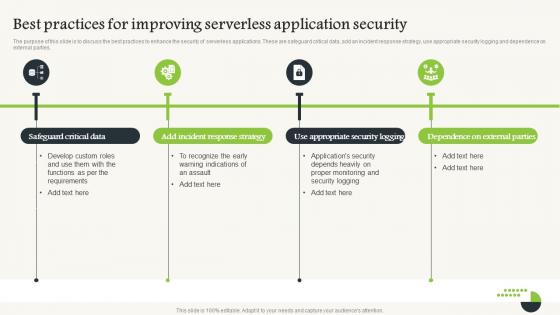 Serverless Computing V2 Best Practices For Improving Serverless Application Security
Serverless Computing V2 Best Practices For Improving Serverless Application SecurityThe purpose of this slide is to discuss the best practices to enhance the security of serverless applications. These are safeguard critical data, add an incident response strategy, use appropriate security logging and dependence on external parties. Introducing Serverless Computing V2 Best Practices For Improving Serverless Application Security to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Safeguard Critical Data, Incident Response Strategy, Serverless Application Security, Appropriate Security Logging, using this template. Grab it now to reap its full benefits.
-
 Best Secured Credit Card In Powerpoint And Google Slides Cpb
Best Secured Credit Card In Powerpoint And Google Slides CpbPresenting Best Secured Credit Card In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Best Secured Credit Card. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
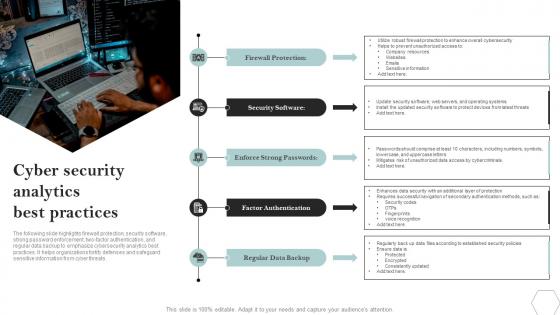 Cyber Security Analytics Best Practices
Cyber Security Analytics Best PracticesThe following slide highlights firewall protection, security software, strong password enforcement, two factor authentication, and regular data backup to emphasize cybersecurity analytics best practices. It helps organizations fortify defenses and safeguard sensitive information from cyber threats. Introducing our premium set of slides with Cyber Security Analytics Best Practices. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Protection, Software, Passwords. So download instantly and tailor it with your information.
-
 Best Secured Credit Card Poor Credit In Powerpoint And Google Slides Cpb
Best Secured Credit Card Poor Credit In Powerpoint And Google Slides CpbPresenting our Best Secured Credit Card Poor Credit In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Best Secured Credit Card Poor Credit This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Comprehensive Guide To Understand Five Best Practices To Secure Bitcoin Fin SS
Comprehensive Guide To Understand Five Best Practices To Secure Bitcoin Fin SSThis slide shows details about best practices which can be adopted by Bitcoin holders to secure accounts against frauds. These tips includes hardware wallets, two factor authentication, strong passwords, etc. Introducing Comprehensive Guide To Understand Five Best Practices To Secure Bitcoin Fin SS to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Hardware Wallet, Two Factor Authentication, Strong Passwords, Update Software, using this template. Grab it now to reap its full benefits.
-
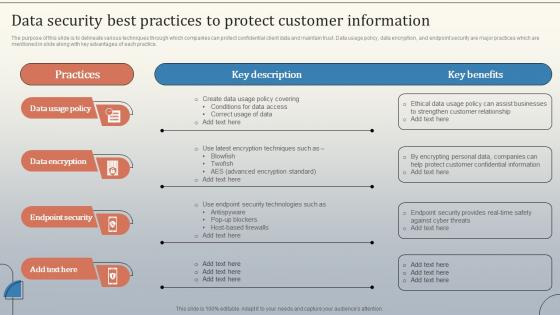 Data Security Best Practices To Protect Customer Database Marketing Strategies MKT SS V
Data Security Best Practices To Protect Customer Database Marketing Strategies MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Introducing Data Security Best Practices To Protect Customer Database Marketing Strategies MKT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Data Usage Policy, Data Encryption, using this template. Grab it now to reap its full benefits.
-
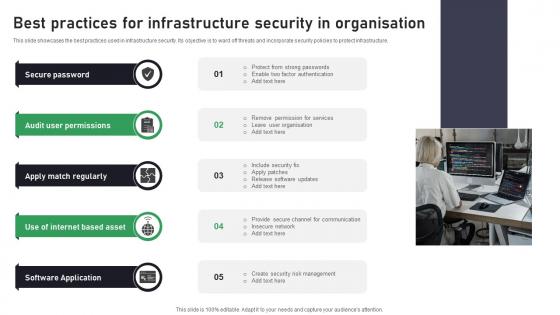 Best Practices For Infrastructure Security In Organisation
Best Practices For Infrastructure Security In OrganisationThis slide showcases the best practices used in infrastructure security. Its objective is to ward off threats and incorporate security policies to protect infrastructure. Introducing our premium set of slides with Best Practices For Infrastructure Security In Organisation. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Password, Permissions, Regularly. So download instantly and tailor it with your information.
-
 Best Practices To Ensure Saas Cyber Security
Best Practices To Ensure Saas Cyber SecurityThis slide represents effective strategies to follow for establishing SaaS cyber security. It aims to strengthen security posture, mitigate risks, and build more resilient platform for users. It includes various approaches such as end-to-end encryption, conducting risk assessment, etc. Presenting our set of slides with Best Practices To Ensure Saas Cyber Security This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Enforcing Data Security, Conduct Risk Assessment, Discovery And Inventory
-
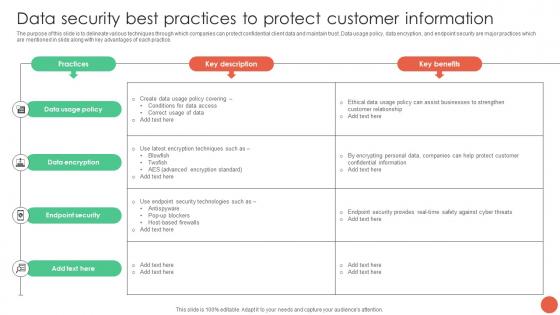 Data Security Best Practices To Protect Customer Information Database Marketing Techniques MKT SS V
Data Security Best Practices To Protect Customer Information Database Marketing Techniques MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Deliver an outstanding presentation on the topic using this Data Security Best Practices To Protect Customer Information Database Marketing Techniques MKT SS V. Dispense information and present a thorough explanation of Data Usage Policy, Data Encryption, Endpoint Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
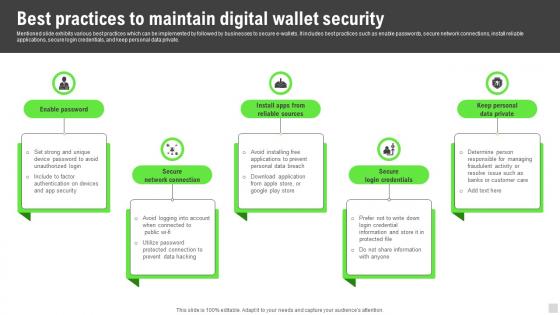 Best Practices To Maintain Digital Wallet Security Implementation Of Cashless Payment
Best Practices To Maintain Digital Wallet Security Implementation Of Cashless PaymentMentioned slide exhibits various best practices which can be implemented by followed by businesses to secure e wallets. It includes best practices such as enable passwords, secure network connections, install reliable applications, secure login credentials, and keep personal data private.Increase audience engagement and knowledge by dispensing information using Best Practices To Maintain Digital Wallet Security Implementation Of Cashless Payment This template helps you present information on five stages. You can also present information on Responsible Managers, Segregate Duties, Bank Statements using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Best Practices To Prevent Cyber Attacks Implementing Strategies To Mitigate Cyber Security Threats
Best Practices To Prevent Cyber Attacks Implementing Strategies To Mitigate Cyber Security ThreatsThe following slide illustrates some activities to minimize the probability of cybercrimes within the organization. It includes elements such as utilizing anti virus, preventing to open suspicious emails, keeping systems up to date etc. Introducing Best Practices To Prevent Cyber Attacks Implementing Strategies To Mitigate Cyber Security Threats to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Leverage Firewalls, Prevent Opening Suspicious Emails using this template. Grab it now to reap its full benefits.
-
 Best Practices For Accepting Card Payment Enhancing Transaction Security With E Payment
Best Practices For Accepting Card Payment Enhancing Transaction Security With E PaymentFollowing slide provides information about various best practices which can be followed while accepting card payments from customers. It includes various best practices such as confirm customer Id, provide payment receipt, provide contact information, customer feedback, and verification. Introducing Best Practices For Accepting Card Payment Enhancing Transaction Security With E Payment to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Confirm Customer ID, Provide Payment Receipt, Provide Contact Information using this template. Grab it now to reap its full benefits.
-
 Best Practices For BNPL Payment Option Enhancing Transaction Security With E Payment
Best Practices For BNPL Payment Option Enhancing Transaction Security With E PaymentMentioned slide provides information best practices which can be implemented by businesses to enhance customer purchasing experience. It includes key practices such as select right solution, inform customers, collaborate BNPL to promotional activities, educate employee and trigger abandoned carts. Increase audience engagement and knowledge by dispensing information using Best Practices For BNPL Payment Option Enhancing Transaction Security With E Payment This template helps you present information on five stages. You can also present information on Right Solution, Inform Customers, Educate Employee using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
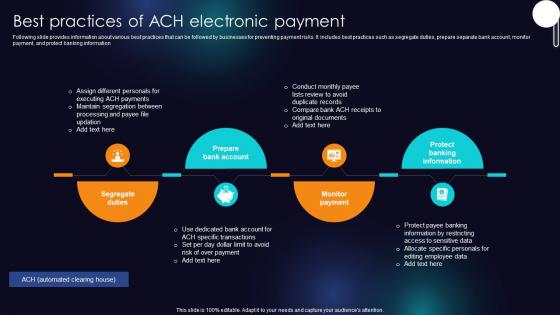 Best Practices Of ACH Electronic Payment Enhancing Transaction Security With E Payment
Best Practices Of ACH Electronic Payment Enhancing Transaction Security With E PaymentFollowing slide provides information about various best practices that can be followed by businesses for preventing payment risks. It includes best practices such as segregate duties, prepare separate bank account, monitor payment, and protect banking information Introducing Best Practices Of ACH Electronic Payment Enhancing Transaction Security With E Payment to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Segregate Duties, Prepare Bank Account, Monitor Payment using this template. Grab it now to reap its full benefits.
-
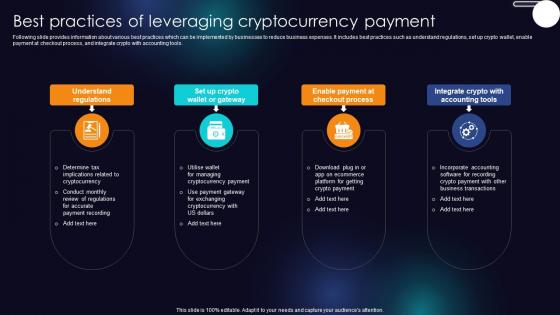 Best Practices Of Leveraging Cryptocurrency Payment Enhancing Transaction Security With E Payment
Best Practices Of Leveraging Cryptocurrency Payment Enhancing Transaction Security With E PaymentFollowing slide provides information about various best practices which can be implemented by businesses to reduce business expenses. It includes best practices such as understand regulations, set up crypto wallet, enable payment at checkout process, and integrate crypto with accounting tools. Increase audience engagement and knowledge by dispensing information using Best Practices Of Leveraging Cryptocurrency Payment Enhancing Transaction Security With E Payment This template helps you present information on four stages. You can also present information on Understand Regulations, Enable Payment Checkout Process, Integrate Crypto, Accounting Tools using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
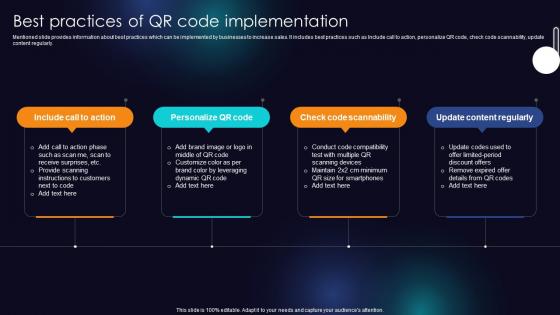 Best Practices Of QR Code Implementation Enhancing Transaction Security With E Payment
Best Practices Of QR Code Implementation Enhancing Transaction Security With E PaymentMentioned slide provides information about best practices which can be implemented by businesses to increase sales. It includes best practices such as Include call to action, personalize QR code, check code scannability, update content regularly. Introducing Best Practices Of QR Code Implementation Enhancing Transaction Security With E Payment to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Include Call To Action, Personalize QR Code, Check Code Scannability using this template. Grab it now to reap its full benefits.
-
 Best Practices To Maintain Digital Wallet Security Enhancing Transaction Security With E Payment
Best Practices To Maintain Digital Wallet Security Enhancing Transaction Security With E PaymentMentioned slide exhibits various best practices which can be implemented by followed by businesses to secure e-wallets. It includes best practices such as enable passwords, secure network connections, install reliable applications, secure login credentials, and keep personal data private. Increase audience engagement and knowledge by dispensing information using Best Practices To Maintain Digital Wallet Security Enhancing Transaction Security With E Payment This template helps you present information on five stages. You can also present information on Enable Password, Secure Network Connection, Secure Login Credentials using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
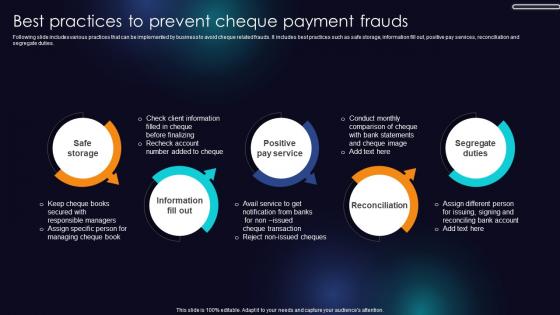 Best Practices To Prevent Cheque Payment Frauds Enhancing Transaction Security With E Payment
Best Practices To Prevent Cheque Payment Frauds Enhancing Transaction Security With E PaymentFollowing slide includes various practices that can be implemented by business to avoid cheque related frauds. It includes best practices such as safe storage, information fill out, positive pay services, reconciliation and segregate duties. Introducing Best Practices To Prevent Cheque Payment Frauds Enhancing Transaction Security With E Payment to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Safe Storage, Positive Pay Service, Reconciliation using this template. Grab it now to reap its full benefits.
-
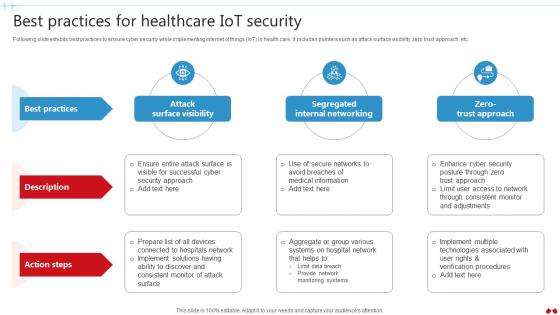 Best Practices For Healthcare IoT Security Transforming Healthcare Industry Through Technology IoT SS V
Best Practices For Healthcare IoT Security Transforming Healthcare Industry Through Technology IoT SS VFollowing slide exhibits best practices to ensure cyber security while implementing internet of things IoT in health care. It includes pointers such as attack surface visibility, zero trust approach, etc. Increase audience engagement and knowledge by dispensing information using Best Practices For Healthcare IoT Security Transforming Healthcare Industry Through Technology IoT SS V. This template helps you present information on two stages. You can also present information on Surface Visibility, Internal Networking, Trust Approach using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
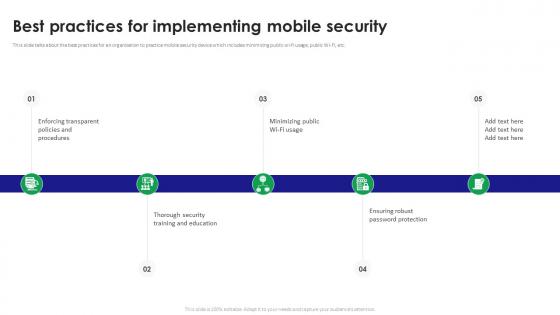 Best Practices For Implementing Mobile Security
Best Practices For Implementing Mobile SecurityThis slide talks about the best practices for an organization to practice mobile security device which includes minimizing public wi-fi usage, public Wi-Fi, etc. Introducing our premium set of slides with name Best Practices For Implementing Mobile Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Ensuring Robust Password Protection, Security Training And Education, Enforcing Transparent Policies. So download instantly and tailor it with your information.
-
 Best Practices For Mobile Security Framework
Best Practices For Mobile Security FrameworkThis slide talks about the best practices one should follow for securing mobile security framework which include multifactor authentication, security audits, etc. Presenting our set of slides with name Best Practices For Mobile Security Framework. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Mobile Security Framework, Multifactor Authentication, Security Audits.
-
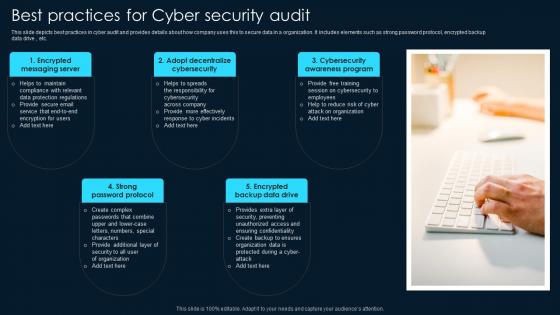 Best Practices For Cyber Security Audit
Best Practices For Cyber Security AuditThis slide depicts best practices in cyber audit and provides details about how company uses this to secure data in a organization. It includes elements such as strong password protocol, encrypted backup data drive , etc. Presenting our set of slides with Best Practices For Cyber Security Audit. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Encrypted Messaging Server, Adopt Decentralize Cybersecurity, Cybersecurity Awareness Program.
-
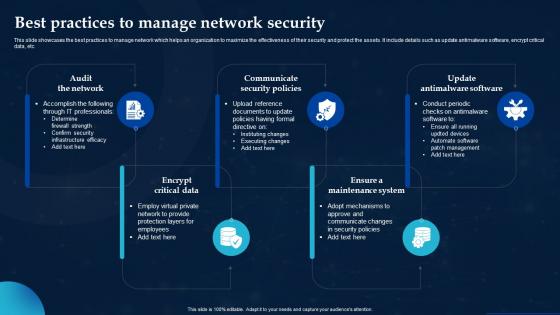 Best Practices To Manage Network Security
Best Practices To Manage Network SecurityThis slide showcases the best practices to manage network which helps an organization to maximize the effectiveness of their security and protect the assets. It include details such as update antimalware software, encrypt critical data, etc. Introducing our premium set of slides with Best Practices To Manage Network Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Audit Network, Encrypt Critical Data, Update Antimalware Software. So download instantly and tailor it with your information.
-
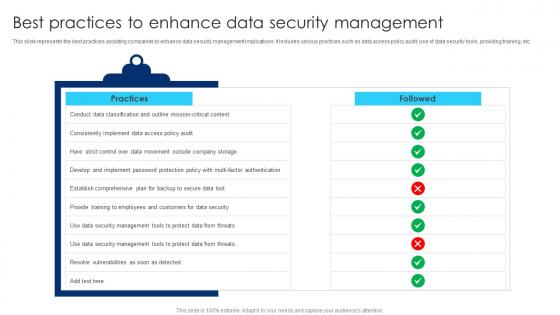 Best Practices To Enhance Data Security Management
Best Practices To Enhance Data Security ManagementThis slide represents the best practices assisting companies to enhance data security management implications. It includes various practices such as data access policy audit, use of data security tools, providing training, etc. Presenting our well structured Best Practices To Enhance Data Security Management. The topics discussed in this slide are Implement Data Access, Security Management Tools, Outside Company Storage. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
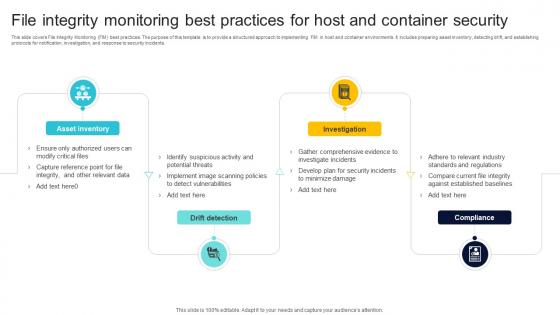 File Integrity Monitoring Best Practices For Host And Container Security
File Integrity Monitoring Best Practices For Host And Container SecurityThis slide covers File Integrity Monitoring FIM best practices. The purpose of this template is to provide a structured approach to implementing FIM in host and container environments. It includes preparing asset inventory, detecting drift, and establishing protocols for notification, investigation, and response to security incidents. Presenting our set of slides with File Integrity Monitoring Best Practices For Host And Container Security This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Asset Inventory, Drift Detection, Investigation
-
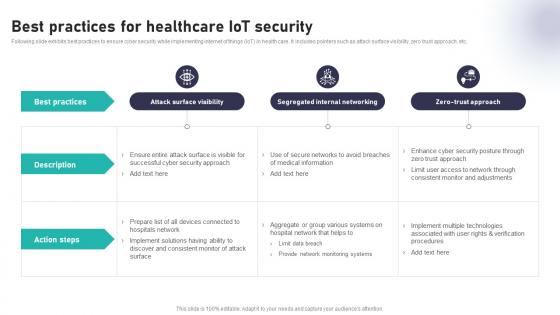 Best Practices For Healthcare IoT Security Impact Of IoT In Healthcare Industry IoT CD V
Best Practices For Healthcare IoT Security Impact Of IoT In Healthcare Industry IoT CD VFollowing slide exhibits best practices to ensure cyber security while implementing internet of things IoT in health care. It includes pointers such as attack surface visibility, zero trust approach, etc. Deliver an outstanding presentation on the topic using this Best Practices For Healthcare IoT Security Impact Of IoT In Healthcare Industry IoT CD V. Dispense information and present a thorough explanation of Surface Visibility, Segregated Internal, Trust Approach using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
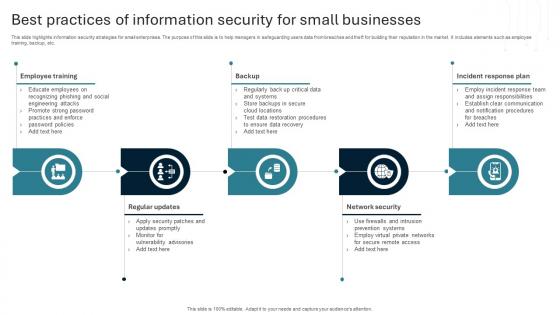 Best Practices Of Information Security For Small Businesses
Best Practices Of Information Security For Small BusinessesThis slide highlights information security strategies for small enterprises. The purpose of this slide is to help managers in safeguarding users data from breaches and theft for building their reputation in the market. It includes elements such as employee training, backup, etc. Presenting our set of slides with Best Practices Of Information Security For Small Businesses. This exhibits information on Five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Employee Training, Regular Updates, Network Security
-
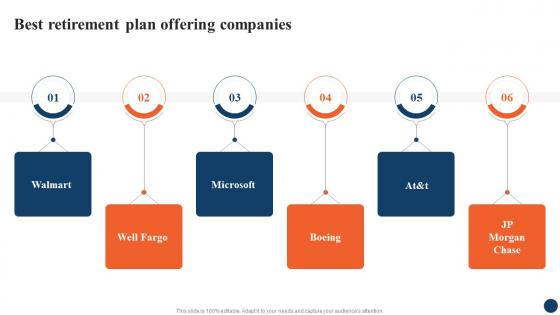 Best Retirement Plan Strategic Retirement Planning To Build Secure Future Fin SS
Best Retirement Plan Strategic Retirement Planning To Build Secure Future Fin SSIntroducing Best Retirement Plan Strategic Retirement Planning To Build Secure Future Fin SS to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Best Retirement Plan, Offering Companies, using this template. Grab it now to reap its full benefits.
-
 Crypto Wallet Security And Best Practices
Crypto Wallet Security And Best PracticesThis slide outlines the crypto wallet security and best practices which include choose a secure wallet, use strong passwords, regular wallet backups, etc. Presenting our set of slides with name Crypto Wallet Security And Best Practices. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Crypto Wallet, Security And Best Practices, Regular Wallet Backups.
-
 Best Practices For Email Domain Security
Best Practices For Email Domain SecurityThis slide is an overview of the best practices for email domain security which include secure email provider, strong, unique passwords and security audits. Introducing our premium set of slides with Best Practices For Email Domain Security. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Email Provider, Unique Passwords, Access Controls. So download instantly and tailor it with your information.
-
 Trending Email Security Best Practices
Trending Email Security Best PracticesThis slide outlines best practices followed in email security which includes use strong passwords, use proxies, regularly back up files and keep software updated. Presenting our set of slides with Trending Email Security Best Practices. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Trending Email Security, Best Practices.
-
 Top Security Testing Best Practices Ppt Icon Graphics Pictures
Top Security Testing Best Practices Ppt Icon Graphics PicturesThis slide represents the security testing best practices such as thorough testing across development, vulnerability identification and resolution, etc. Introducing Top Security Testing Best Practices Ppt Icon Graphics Pictures to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Consistent Security Updates, Automation Tools Utilization, Vulnerability Identification And Resolution, using this template. Grab it now to reap its full benefits.
-
 Additional Blockchain Data Security Tips And Best Comprehensive Approach To Privacy BCT SS
Additional Blockchain Data Security Tips And Best Comprehensive Approach To Privacy BCT SSThis slide covers essential guidance on safeguarding blockchain data to ensure integrity and confidentiality such as keeping private key confidential, utilizing VPN, use of link checker, opting for trusted crypto wallets. Introducing Additional Blockchain Data Security Tips And Best Comprehensive Approach To Privacy BCT SS to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Private Key Confidential, Security, Blockchain, Prevent Phishing Attacks, using this template. Grab it now to reap its full benefits.
-
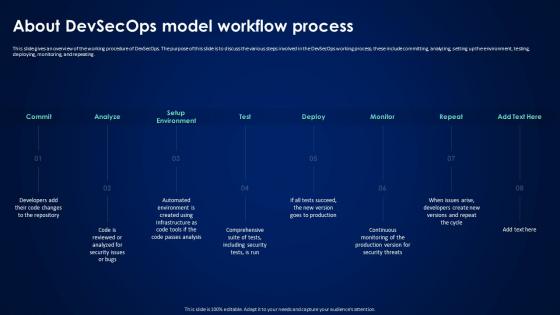 About Devsecops Model Workflow Process Devsecops Best Practices For Secure
About Devsecops Model Workflow Process Devsecops Best Practices For SecureThis slide gives an overview of the working procedure of DevSecOps. The purpose of this slide is to discuss the various steps involved in the DevSecOps working process, these include committing, analyzing, setting up the environment, testing, deploying, monitoring, and repeating. Introducing About Devsecops Model Workflow Process Devsecops Best Practices For Secure to increase your presentation threshold. Encompassed with eight stages, this template is a great option to educate and entice your audience. Dispence information on Devsecops Working Process, Analyzing, Testing, Deploying, Monitoring, using this template. Grab it now to reap its full benefits.
-
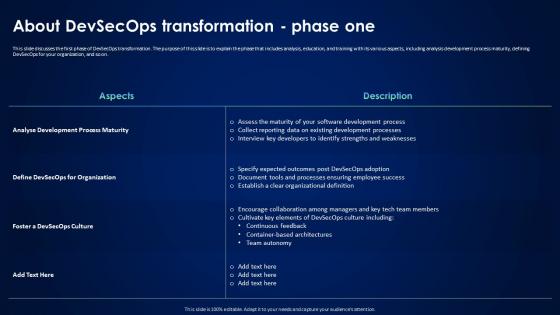 About Devsecops Transformation Phase One Devsecops Best Practices For Secure
About Devsecops Transformation Phase One Devsecops Best Practices For SecureThis slide discusses the first phase of DevSecOps transformation. The purpose of this slide is to explain the phase that includes analysis, education, and training with its various aspects, including analysis development process maturity, defining DevSecOps for your organization, and so on. Present the topic in a bit more detail with this About Devsecops Transformation Phase One Devsecops Best Practices For Secure. Use it as a tool for discussion and navigation on Analyse Development Process Maturity, Continuous Feedback, Container Based Architectures, Team Autonomy. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
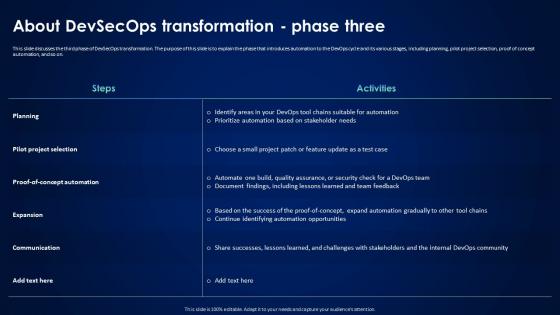 About Devsecops Transformation Phase Three Devsecops Best Practices For Secure
About Devsecops Transformation Phase Three Devsecops Best Practices For SecureThis slide discusses the third phase of DevSecOps transformation. The purpose of this slide is to explain the phase that introduces automation to the DevOps cycle and its various stages, including planning, pilot project selection, proof of concept automation, and so on. Deliver an outstanding presentation on the topic using this About Devsecops Transformation Phase Three Devsecops Best Practices For Secure. Dispense information and present a thorough explanation of Pilot Project Selection, Devsecops Transformation, Planning, Pilot Project Selection using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Agenda For Devsecops Best Practices For Secure Applications
Agenda For Devsecops Best Practices For Secure ApplicationsIncrease audience engagement and knowledge by dispensing information using Agenda For Devsecops Best Practices For Secure Applications. This template helps you present information on six stages. You can also present information on Driving Digital Transformation, Devsecops Best Practices, Secure Applications using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Devsecops Best Practices For Secure 30 60 90 Days Plan For Devsecops Implementation
Devsecops Best Practices For Secure 30 60 90 Days Plan For Devsecops ImplementationThis slide represents the 30-60-90-day plan for DevSecOps implementation. The purpose of this slide is to showcase the approaches that need to be followed as short-term, medium, and long-term goals to implement the DevSecOps. Introducing Devsecops Best Practices For Secure 30 60 90 Days Plan For Devsecops Implementation to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Devsecops Implementation, Vulnerability Scanning, Relevant Security Standards, using this template. Grab it now to reap its full benefits.
-
 Devsecops Best Practices For Secure About Devsecops Introduction And Working Process
Devsecops Best Practices For Secure About Devsecops Introduction And Working ProcessThis slide gives an overview of DevSecOps and its process. The purpose of this slide is to explain DevSecOps, including its process steps, which are release, deploy, operate, monitor, plan, code, build, and test. Present the topic in a bit more detail with this Devsecops Best Practices For Secure About Devsecops Introduction And Working Process. Use it as a tool for discussion and navigation on Development, Security, Operations, Smooth Integration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
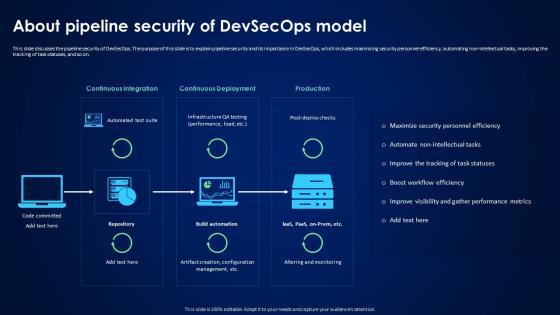 Devsecops Best Practices For Secure About Pipeline Security Of Devsecops Model
Devsecops Best Practices For Secure About Pipeline Security Of Devsecops ModelThis slide discusses the pipeline security of DevSecOps. The purpose of this slide is to explain pipeline security and its importance in DevSecOps, which includes maximizing security personnel efficiency, automating non-intellectual tasks, improving the tracking of task statuses, and so on. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure About Pipeline Security Of Devsecops Model. Dispense information and present a thorough explanation of Pipeline Security Devsecops, Pipeline Security, Security Personnel Efficiency, Non Intellectual Tasks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
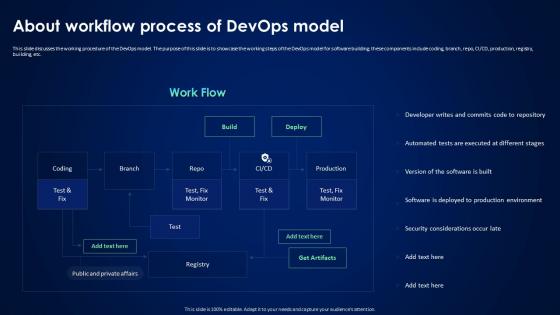 Devsecops Best Practices For Secure About Workflow Process Of Devops Model
Devsecops Best Practices For Secure About Workflow Process Of Devops ModelThis slide discusses the working procedure of the DevOps model. The purpose of this slide is to showcase the working steps of the DevOps model for software building, these components include coding, branch, repo, CI or CD, production, registry, building, etc. Present the topic in a bit more detail with this Devsecops Best Practices For Secure About Workflow Process Of Devops Model. Use it as a tool for discussion and navigation on Software Building, Coding, Production, Registry, Security Considerations Occur Late. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
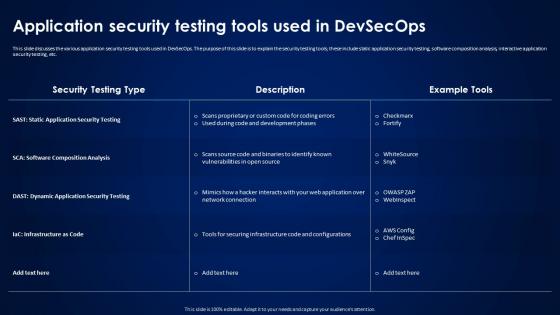 Devsecops Best Practices For Secure Application Security Testing Tools Used In Devsecops
Devsecops Best Practices For Secure Application Security Testing Tools Used In DevsecopsThis slide discusses the various application security testing tools used in DevSecOps. The purpose of this slide is to explain the security testing tools, these include static application security testing, software composition analysis, interactive application security testing, etc. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure Application Security Testing Tools Used In Devsecops. Dispense information and present a thorough explanation of Application Security Testing, Dynamic Application Security Testing, Infrastructure As Code using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Devsecops Best Practices For Secure Applications For Table Of Content
Devsecops Best Practices For Secure Applications For Table Of ContentThis slide showcases the comparative analysis of the before versus after DevSecOps implementation. The purpose of this slide is to discuss the different performance aspects and how DevSecOps has proved beneficial for these aspects. Present the topic in a bit more detail with this Devsecops Best Practices For Secure Applications For Table Of Content. Use it as a tool for discussion and navigation on Pipeline Security, Development Pre Commit Stage, Continuous Integration Commit Stage. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
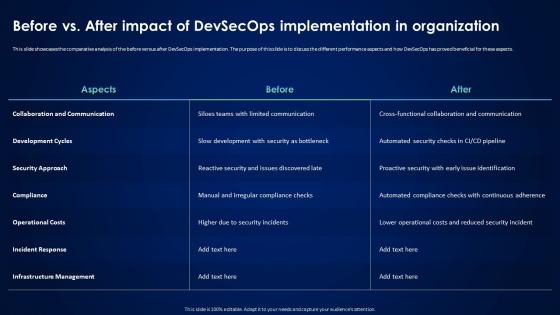 Devsecops Best Practices For Secure Before Vs After Impact Of Devsecops Implementation
Devsecops Best Practices For Secure Before Vs After Impact Of Devsecops ImplementationThis slide showcases the comparative analysis of the before versus after DevSecOps implementation. The purpose of this slide is to discuss the different performance aspects and how DevSecOps has proved beneficial for these aspects. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure Before Vs After Impact Of Devsecops Implementation. Dispense information and present a thorough explanation of Collaboration And Communication, Development Cycles, Operational Costs, Infrastructure Management using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
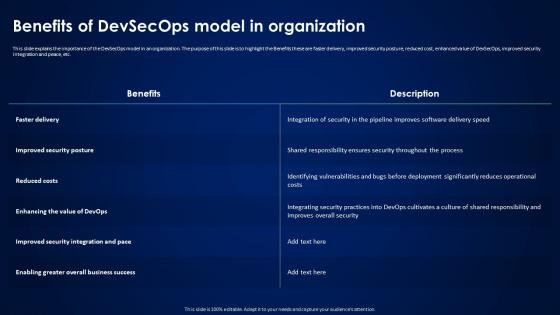 Devsecops Best Practices For Secure Benefits Of Devsecops Model In Organization
Devsecops Best Practices For Secure Benefits Of Devsecops Model In OrganizationThis slide explains the importance of the DevSecOps model in an organization. The purpose of this slide is to highlight the Benefits these are faster delivery, improved security posture, reduced cost, enhanced value of DevSecOps, improved security integration and peace, etc. Present the topic in a bit more detail with this Devsecops Best Practices For Secure Benefits Of Devsecops Model In Organization. Use it as a tool for discussion and navigation on Responsibility Ensures Security, Identifying Vulnerabilities, Reduced Costs. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Devsecops Best Practices For Secure Best Practices Followed In Organization For Devsecops
Devsecops Best Practices For Secure Best Practices Followed In Organization For DevsecopsThis slide showcases the best practices for the DevSecOps in an organization. The purpose of this slide is to highlight the best practices, these include shift security left, implementing CI or CD, obfuscation techniques, micro services architecture, and so on. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure Best Practices Followed In Organization For Devsecops. Dispense information and present a thorough explanation of Obfuscation Techniques, Cloud Native Technologies, Activity Monitoring And Logging using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Devsecops Best Practices For Secure Case Study Paypal Devsecops
Devsecops Best Practices For Secure Case Study Paypal DevsecopsThis slide discusses the case study related to DevSecOps. The purpose of this slide is to give an overview of PayPal company, which faces various challenges in providing security guarantees to customers, it also proved different solutions and outcomes. Present the topic in a bit more detail with this Devsecops Best Practices For Secure Case Study Paypal Devsecops. Use it as a tool for discussion and navigation on Transactions Presented Challenge, Software Development, Actionable Security Stories. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Devsecops Best Practices For Secure Characteristics Of Strong Devsecops Program In It
Devsecops Best Practices For Secure Characteristics Of Strong Devsecops Program In ItThis slide discusses the features adopted for a strong DevSecOps program. The purpose of this slide is to explain the various characteristics these are security awareness and ownership, automated operations, wide scope, shift-left and shift-right, etc. Increase audience engagement and knowledge by dispensing information using Devsecops Best Practices For Secure Characteristics Of Strong Devsecops Program In It. This template helps you present information on six stages. You can also present information on Automated Operations, Security Awareness And Ownership, Developer Acceptance using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
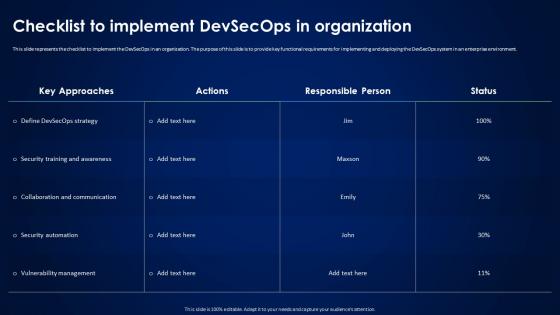 Devsecops Best Practices For Secure Checklist To Implement Devsecops In Organization
Devsecops Best Practices For Secure Checklist To Implement Devsecops In OrganizationThis slide represents the checklist to implement the DevSecOps in an organization. The purpose of this slide is to provide key functional requirements for implementing and deploying the DevSecOps system in an enterprise environment. Present the topic in a bit more detail with this Devsecops Best Practices For Secure Checklist To Implement Devsecops In Organization. Use it as a tool for discussion and navigation on Security Training And Awareness, Collaboration And Communication, Security Automation, Vulnerability Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Devsecops Best Practices For Secure Comparison Between Devops And Devsecops Models
Devsecops Best Practices For Secure Comparison Between Devops And Devsecops ModelsThis slide showcases the comparison between DevOps and DevSecOps models. The purpose of this slide is to highlight the key differences in terms of definition, objective, benefits, attack surface, tool and methods, collaboration and continuous improvement. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure Comparison Between Devops And Devsecops Models. Dispense information and present a thorough explanation of Benefits, Attack Surface, Tool And Methods, Collaboration And Continuous Improvement using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Devsecops Best Practices For Secure Continuous Integration And Continuous Delivery Process
Devsecops Best Practices For Secure Continuous Integration And Continuous Delivery ProcessThis slide discusses the continuous integration and continuous delivery process security for DevSecOps. The purpose of this slide is to highlight the process, including integrating container security scanners, automating security testing in CI, incorporating security tests in acceptance testing, and so on. Present the topic in a bit more detail with this Devsecops Best Practices For Secure Continuous Integration And Continuous Delivery Process. Use it as a tool for discussion and navigation on Integrate Container Security Scanners, Automate Security Updates, Automate Configuration Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Devsecops Best Practices For Secure Continuous Process Improvement In Devsecops
Devsecops Best Practices For Secure Continuous Process Improvement In DevsecopsThis slide discusses the DevSecOps program requirement for continuous improvement. The purpose of this slide is to explain the needs of the DevSecOps program for achieving efficiency, these include strategic goals, architecture operation, and program evaluation. Introducing Devsecops Best Practices For Secure Continuous Process Improvement In Devsecops to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Strategic Goals, Architecture And Operations, Program Evaluation, Devops Environment, using this template. Grab it now to reap its full benefits.
-
 Devsecops Best Practices For Secure Core Principles Followed In Devsecops Model
Devsecops Best Practices For Secure Core Principles Followed In Devsecops ModelThis slide discusses the core principle used in the DevSecOps model. The purpose of this slide is to explain the principles of DevSecOps in detail, these include automation, continuous monitoring, and collaboration across functions. Increase audience engagement and knowledge by dispensing information using Devsecops Best Practices For Secure Core Principles Followed In Devsecops Model. This template helps you present information on three stages. You can also present information on Continuous Monitoring, Collaboration Across Functions, Configuration Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
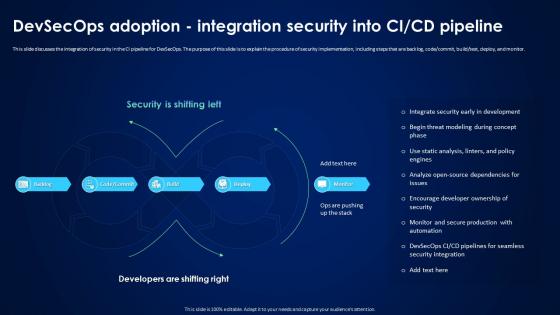 Devsecops Best Practices For Secure Devsecops Adoption Integration Security Into Ci Cd Pipeline
Devsecops Best Practices For Secure Devsecops Adoption Integration Security Into Ci Cd PipelineThis slide discusses the integration of security in the CI pipeline for DevSecOps. The purpose of this slide is to explain the procedure of security implementation, including steps that are backlog, code or commit, build ottest, deploy, and monitor. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure Devsecops Adoption Integration Security Into Ci Cd Pipeline. Dispense information and present a thorough explanation of Security Implementation, Devsecops Adoption, Integration Security, Seamless Security Integration using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Devsecops Best Practices For Secure Devsecops Development Security And Operations
Devsecops Best Practices For Secure Devsecops Development Security And OperationsThis slide discusses the working process of development, security and operations in DevSecOps. The purpose of this slide is to highlight the process followed by DevSecOps for providing, monitoring and managing security at each level of the software system. Introducing Devsecops Best Practices For Secure Devsecops Development Security And Operations to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Development, Security, Operations, Code Expedites Development, using this template. Grab it now to reap its full benefits.
-
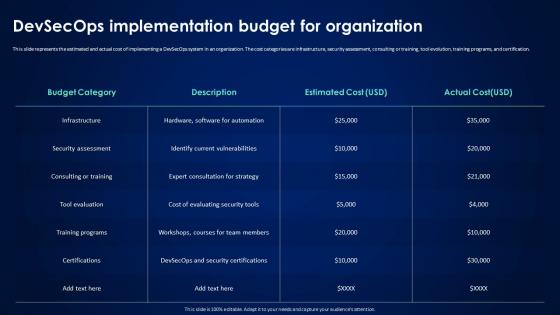 Devsecops Best Practices For Secure Devsecops Implementation Budget For Organization
Devsecops Best Practices For Secure Devsecops Implementation Budget For OrganizationThis slide represents the estimated and actual cost of implementing a DevSecOps system in an organization. The cost categories are infrastructure, security assessment, consulting or training, tool evolution, training programs, and certification. Present the topic in a bit more detail with this Devsecops Best Practices For Secure Devsecops Implementation Budget For Organization. Use it as a tool for discussion and navigation on Security Assessment, Consulting Or Training, Training Programs, Budget For Organization. This template is free to edit as deemed fit for your organization. Therefore download it now.



