Powerpoint Templates and Google slides for Best Security Company Of The Year
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
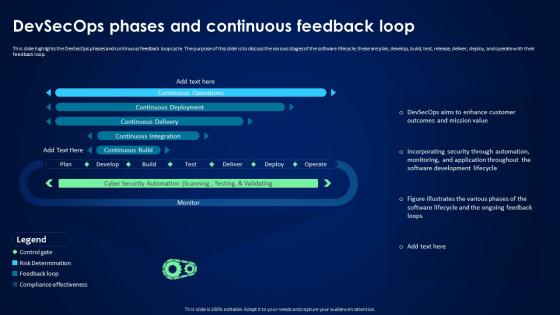 Devsecops Best Practices For Secure Devsecops Phases And Continuous Feedback Loop
Devsecops Best Practices For Secure Devsecops Phases And Continuous Feedback LoopThis slide highlights the DevSecOps phases and continuous feedback loop cycle. The purpose of this slide is to discuss the various stages of the software lifecycle, these are plan, develop, build, test, release, deliver, deploy, and operate with their feedback loop. Present the topic in a bit more detail with this Devsecops Best Practices For Secure Devsecops Phases And Continuous Feedback Loop. Use it as a tool for discussion and navigation on Continuous Operations, Continuous Deployment, Continuous Delivery, Continuous Integration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
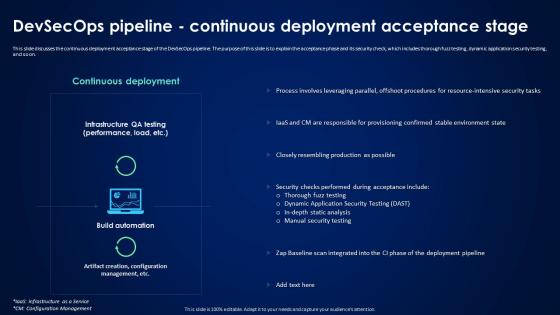 Devsecops Best Practices For Secure Devsecops Pipeline Continuous Deployment Acceptance Stage
Devsecops Best Practices For Secure Devsecops Pipeline Continuous Deployment Acceptance StageThis slide discusses the continuous deployment acceptance stage of the DevSecOps pipeline. The purpose of this slide is to explain the acceptance phase and its security check, which includes thorough fuzz testing, dynamic application security testing, and so on. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure Devsecops Pipeline Continuous Deployment Acceptance Stage. Dispense information and present a thorough explanation of Thorough Fuzz Testing, Dynamic Application Security Testing, In Depth Static Analysis, Manual Security Testing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Devsecops Best Practices For Secure Devsecops Pipeline Development Pre Commit Stage
Devsecops Best Practices For Secure Devsecops Pipeline Development Pre Commit StageThis slide discusses the development pre-commit stage of the DevSecOps pipeline. The purpose of this slide is to explain the pre-commit phase that includes initial defense on developer laptops, early security implementation, and Git pre-commit hooks for feedback. Increase audience engagement and knowledge by dispensing information using Devsecops Best Practices For Secure Devsecops Pipeline Development Pre Commit Stage. This template helps you present information on six stages. You can also present information on Static Analysis Scans, Security Engineer Peer Reviews, Lightweight Threat Modeling using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
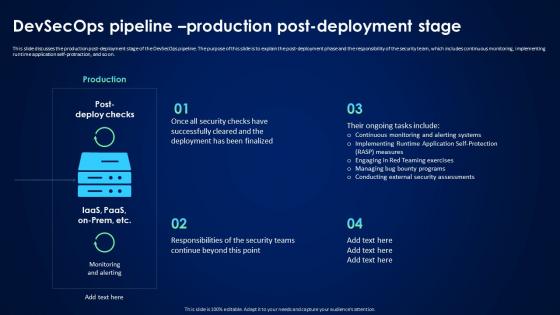 Devsecops Best Practices For Secure Devsecops Pipeline Production Post Deployment Stage
Devsecops Best Practices For Secure Devsecops Pipeline Production Post Deployment StageThis slide discusses the production post-deployment stage of the DevSecOps pipeline. The purpose of this slide is to explain the post-deployment phase and the responsibility of the security team, which includes continuous monitoring, implementing runtime application self-protraction, and so on. Present the topic in a bit more detail with this Devsecops Best Practices For Secure Devsecops Pipeline Production Post Deployment Stage. Use it as a tool for discussion and navigation on Engaging In Red Teaming Exercises, Managing Bug Bounty Programs, Conducting External Security Assessments. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Devsecops Best Practices For Secure Devsecops Transformation Phase Five Execute On Devsecops
Devsecops Best Practices For Secure Devsecops Transformation Phase Five Execute On DevsecopsThis slide discusses the fifth phase of DevSecOps transformation. The purpose of this slide is to explain the phase executed on DevSecOps, including phased execution in DevSecOps transformation and the advantages of starting with the new project. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure Devsecops Transformation Phase Five Execute On Devsecops. Dispense information and present a thorough explanation of Phased Execution In Devsecops Transformation, Advantages Of Starting With New Projects, Facilitates Alignment Of Expectations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Devsecops Best Practices For Secure Devsecops Trends Driving Adoption And Digital Transformation
Devsecops Best Practices For Secure Devsecops Trends Driving Adoption And Digital TransformationThis slide showcases the trends driving adoption and digital transformation in DevSecOps. The purpose of this slide is to highlight the various trends, including third-party risk management, infrastructure as a code, growing reliance on AIOps, and shift to cloud native. Introducing Devsecops Best Practices For Secure Devsecops Trends Driving Adoption And Digital Transformation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Third Party Risk Management, Growing Reliance On Aiops, Shift To Cloud Native Development, Infrastructure As Code, using this template. Grab it now to reap its full benefits.
-
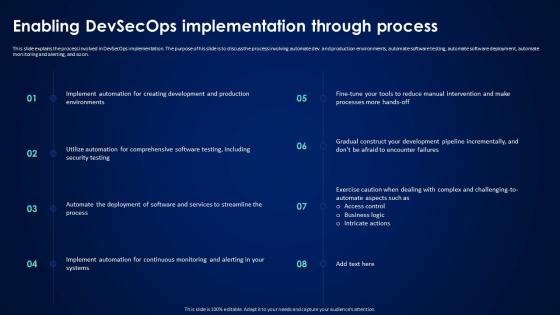 Devsecops Best Practices For Secure Enabling Devsecops Implementation Through Process
Devsecops Best Practices For Secure Enabling Devsecops Implementation Through ProcessThis slide explains the process involved in DevSecOps implementation. The purpose of his slide is to discuss the process involving automate dev. and production environments, automate software testing, automate software deployment, automate monitoring and alerting, and so on. Increase audience engagement and knowledge by dispensing information using Devsecops Best Practices For Secure Enabling Devsecops Implementation Through Process. This template helps you present information on eight stages. You can also present information on Devsecops Implementation, Production Environments, Automate Software Testing, Automate Software Deployment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
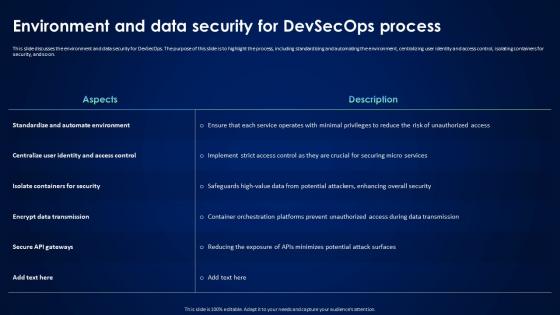 Devsecops Best Practices For Secure Environment And Data Security For Devsecops Process
Devsecops Best Practices For Secure Environment And Data Security For Devsecops ProcessThis slide discusses the environment and data security for DevSecOps. The purpose of this slide is to highlight the process, including standardizing and automating the environment, centralizing user identity and access control, isolating containers for security, and so on. Present the topic in a bit more detail with this Devsecops Best Practices For Secure Environment And Data Security For Devsecops Process. Use it as a tool for discussion and navigation on Standardize And Automate Environment, Isolate Containers For Security, Encrypt Data Transmission. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
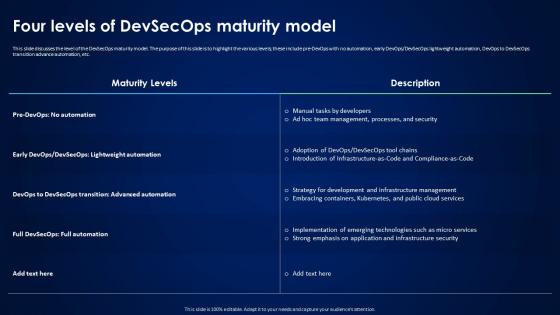 Devsecops Best Practices For Secure Four Levels Of Devsecops Maturity Model
Devsecops Best Practices For Secure Four Levels Of Devsecops Maturity ModelThis slide discusses the level of the DevSecOps maturity model. The purpose of this slide is to highlight the various levels, these include pre-DevOps with no automation, early DevOps or DevSecOps lightweight automation, DevOps to DevSecOps transition advance automation, etc. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure Four Levels Of Devsecops Maturity Model. Dispense information and present a thorough explanation of Lightweight Automation, Devops To Devsecops Transition, Application And Infrastructure Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Devsecops Best Practices For Secure Four Pillars For Achieving Devsecops Transformation
Devsecops Best Practices For Secure Four Pillars For Achieving Devsecops TransformationThis slide highlights the four pillars of transformation for DevSecOps. The purpose of this slide is to discuss the pillars for achieving change, including governance, people, process, and technology, and highlight their importance. Introducing Devsecops Best Practices For Secure Four Pillars For Achieving Devsecops Transformation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Governance, People, Process, Technology, Devsecops Transformation, using this template. Grab it now to reap its full benefits.
-
 Devsecops Best Practices For Secure Global Devsecops Market Research Analysis
Devsecops Best Practices For Secure Global Devsecops Market Research AnalysisThis slide highlights the global market analysis of DevSecOps. The purpose of this slide is to discuss the market factors that provide market analysis, these are market insight, market drivers, geographical analysis, and key companies. Increase audience engagement and knowledge by dispensing information using Devsecops Best Practices For Secure Global Devsecops Market Research Analysis. This template helps you present information on five stages. You can also present information on Rising Internet Penetration Rate, Online Platform, Geographical Analysis, Market Research Analysis using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
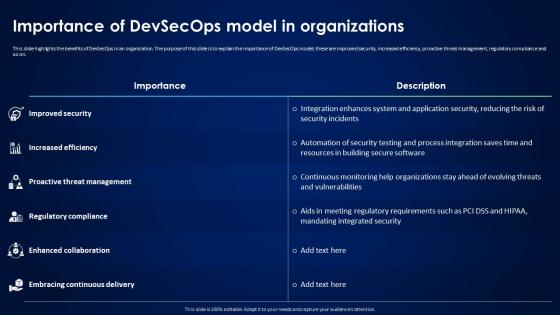 Devsecops Best Practices For Secure Importance Of Devsecops Model In Organizations
Devsecops Best Practices For Secure Importance Of Devsecops Model In OrganizationsThis slide highlights the benefits of DevSecOps in an organization. The purpose of this slide is to explain the importance of DevSecOps model, these are improved security, increased efficiency, proactive threat management, regulatory compliance and so on. Present the topic in a bit more detail with this Devsecops Best Practices For Secure Importance Of Devsecops Model In Organizations. Use it as a tool for discussion and navigation on Building Secure Software, Mandating Integrated Security, Integration Enhances System, Application Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
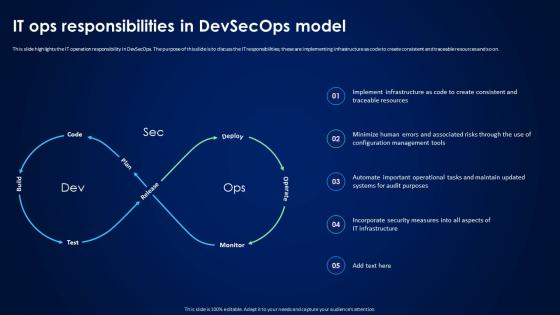 Devsecops Best Practices For Secure IT Ops Responsibilities In Devsecops Model
Devsecops Best Practices For Secure IT Ops Responsibilities In Devsecops ModelThis slide highlights the IT operation responsibility in DevSecOps. The purpose of this slide is to discuss the IT responsibilities these are implementing infrastructure as code to create consistent and traceable resources and so on. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure IT Ops Responsibilities In Devsecops Model. Dispense information and present a thorough explanation of Consistent And Traceable Resources, Configuration Management Tools, Incorporate Security Measures using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
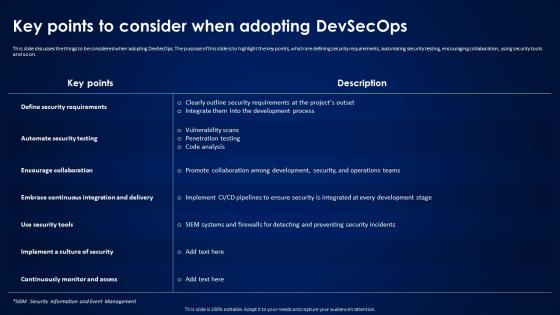 Devsecops Best Practices For Secure Key Points To Consider When Adopting Devsecops
Devsecops Best Practices For Secure Key Points To Consider When Adopting DevsecopsThis slide discusses the things to be considered when adopting DevSecOps. The purpose of this slide is to highlight the key points, which are defining security requirements, automating security testing, encouraging collaboration, using security tools and so on. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure Key Points To Consider When Adopting Devsecops. Dispense information and present a thorough explanation of Automate Security Testing, Encourage Collaboration, Continuously Monitor And Assess using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
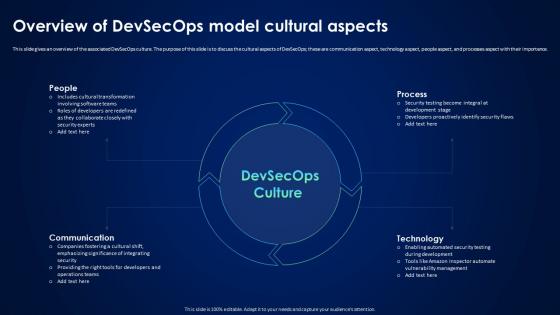 Devsecops Best Practices For Secure Overview Of Devsecops Model Cultural Aspects
Devsecops Best Practices For Secure Overview Of Devsecops Model Cultural AspectsThis slide gives an overview of the associated DevSecOps culture. The purpose of this slide is to discuss the cultural aspects of DevSecOps, these are communication aspect, technology aspect, people aspect, and processes aspect with their importance. Introducing Devsecops Best Practices For Secure Overview Of Devsecops Model Cultural Aspects to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Associated Devsecops Culture, Communication Aspect, Technology Aspect, using this template. Grab it now to reap its full benefits.
-
 Devsecops Best Practices For Secure Overview Of Working Process Of Devsecops Model
Devsecops Best Practices For Secure Overview Of Working Process Of Devsecops ModelThis slide discusses the workflow procedure of DevSecOps model. The purpose of this slide is to showcase the working steps of DevSecOps model for software building and enhancing security at each level these include coding, branch, repo, CI or CD, production, etc. Present the topic in a bit more detail with this Devsecops Best Practices For Secure Overview Of Working Process Of Devsecops Model. Use it as a tool for discussion and navigation on Workflow Procedure Of Devsecops, Software Building, Enhancing Security, Production. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
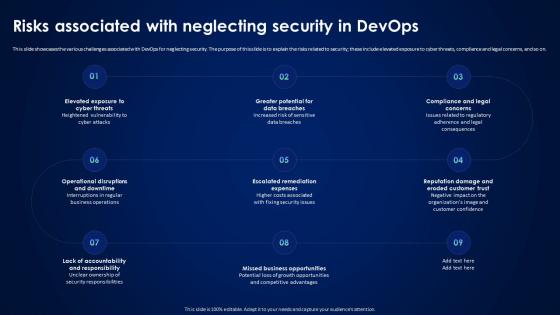 Devsecops Best Practices For Secure Risks Associated With Neglecting Security In Devops
Devsecops Best Practices For Secure Risks Associated With Neglecting Security In DevopsThis slide showcases the various challenges associated with DevOps for neglecting security. The purpose of this slide is to explain the risks related to security, these include elevated exposure to cyber threats, compliance and legal concerns, and so on. Increase audience engagement and knowledge by dispensing information using Devsecops Best Practices For Secure Risks Associated With Neglecting Security In Devops. This template helps you present information on nine stages. You can also present information on Greater Potential For Data Breaches, Escalated Remediation Expenses, Operational Disruptions, Downtime Interruptions In Regular using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Devsecops Best Practices For Secure Roadmap For Devsecops Implementation Strategy
Devsecops Best Practices For Secure Roadmap For Devsecops Implementation StrategyThis slide highlights the project roadmap to implement the DevSecOps plan in an organization. The purpose of this slide is to showcase the different phases of the DevSecOps implementation plan, such as foundation and preparation, tool selection and integration, etc. Introducing Devsecops Best Practices For Secure Roadmap For Devsecops Implementation Strategy to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Tool Selection And Integration, Compliance And Governance, Foundation And Preparation, Security As Code, using this template. Grab it now to reap its full benefits.
-
 Devsecops Best Practices For Secure Software Development Security Importance And Drivers
Devsecops Best Practices For Secure Software Development Security Importance And DriversThis slide discusses the importance and driver of software development security. The purpose of this slide is to explain the importance of security in software development and its key drivers, which are cyber threat defense, data privacy, regulatory adherence, and so on. Increase audience engagement and knowledge by dispensing information using Devsecops Best Practices For Secure Software Development Security Importance And Drivers. This template helps you present information on three stages. You can also present information on Reputation Protection, Financial Risk Reduction, Data Privacy, Operational Risk Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Devsecops Best Practices For Secure Specific Security Tool Common To All Devsecops Design
Devsecops Best Practices For Secure Specific Security Tool Common To All Devsecops DesignThis slide discusses the specific security tool common to DevSecOps design. The purpose of this slide is to explain the various tools, including runtime defense, vulnerability, CVE service host, artifact repository, and zero trust. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure Specific Security Tool Common To All Devsecops Design. Dispense information and present a thorough explanation of Cyber Security Vulnerability, Supplies Common Vulnerabilities, Artifact Repository using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Devsecops Best Practices For Secure Steps To Drive Sustainable Governance For Devsecops
Devsecops Best Practices For Secure Steps To Drive Sustainable Governance For DevsecopsThis slide discusses the approach to developing a sustainable governance model for DevSecOps. The purpose of this slide is to go through various aspects to drive scalable governance, these include role and responsibility, policies and procedures, security automation, and so on. Increase audience engagement and knowledge by dispensing information using Devsecops Best Practices For Secure Steps To Drive Sustainable Governance For Devsecops. This template helps you present information on five stages. You can also present information on Devsecops Roles And Responsibilities, Establish Policies And Procedures, Enable Security Automation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
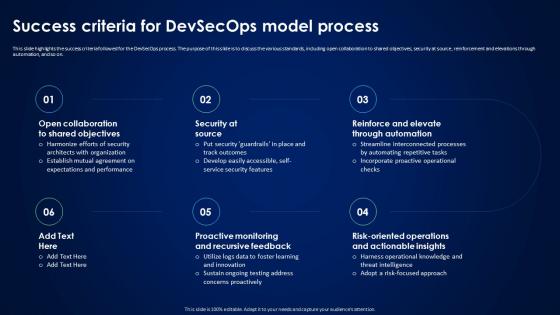 Devsecops Best Practices For Secure Success Criteria For Devsecops Model Process
Devsecops Best Practices For Secure Success Criteria For Devsecops Model ProcessThis slide highlights the success criteria followed for the DevSecOps process. The purpose of this slide is to discuss the various standards, including open collaboration to shared objectives, security at source, reinforcement and elevations through automation, and so on. Introducing Devsecops Best Practices For Secure Success Criteria For Devsecops Model Process to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Proactive Monitoring And Recursive, Reinforce And Elevate Through Automation, Security At Source, using this template. Grab it now to reap its full benefits.
-
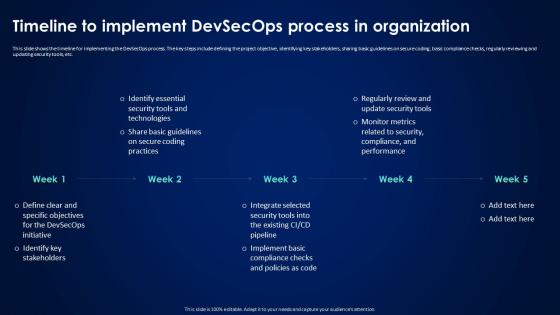 Devsecops Best Practices For Secure Timeline To Implement Devsecops Process In Organization
Devsecops Best Practices For Secure Timeline To Implement Devsecops Process In OrganizationThis slide shows the timeline for implementing the DevSecOps process. The key steps include defining the project objective, identifying key stakeholders, sharing basic guidelines on secure coding, basic compliance checks, regularly reviewing and updating security tools, etc. Increase audience engagement and knowledge by dispensing information using Devsecops Best Practices For Secure Timeline To Implement Devsecops Process In Organization. This template helps you present information on five stages. You can also present information on Timeline To Implement Devsecops, Regularly Reviewing, Updating Security Tools, Sharing Basic Guidelines using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
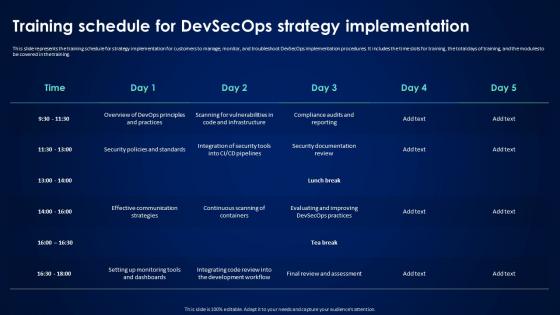 Devsecops Best Practices For Secure Training Schedule For Devsecops Strategy Implementation
Devsecops Best Practices For Secure Training Schedule For Devsecops Strategy ImplementationThis slide represents the training schedule for strategy implementation for customers to manage, monitor, and troubleshoot DevSecOps implementation procedures. It includes the time slots for training, the total days of training, and the modules to be covered in the training. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure Training Schedule For Devsecops Strategy Implementation. Dispense information and present a thorough explanation of Strategy Implementation, Monitor And Troubleshoot, Devsecops Implementation Procedures using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
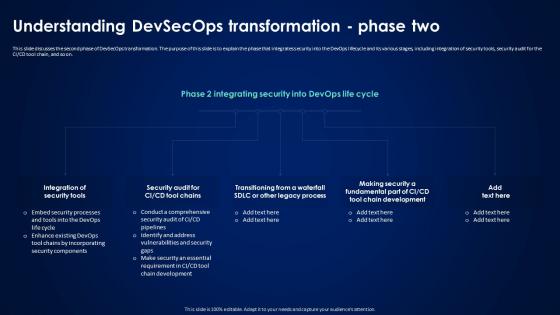 Devsecops Best Practices For Secure Understanding Devsecops Transformation Phase Two
Devsecops Best Practices For Secure Understanding Devsecops Transformation Phase TwoThis slide discusses the second phase of DevSecOps transformation. The purpose of this slide is to explain the phase that integrates security into the DevOps lifecycle and its various stages, including integration of security tools, security audit for the CI or CD tool chain, and so on. Introducing Devsecops Best Practices For Secure Understanding Devsecops Transformation Phase Two to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Integration Of Security Tools, Security Audit, Making Security A Fundamental Part, Tool Chain Development, using this template. Grab it now to reap its full benefits.
-
 Devsecops Best Practices For Secure Various Impact Of Devsecops Process In Organization
Devsecops Best Practices For Secure Various Impact Of Devsecops Process In OrganizationThis slide discusses the various impacts of the DevSecOps process in an organization. The purpose of this slide is to explain the impact of DevSecOps in terms of security, development, operations, compliance, customer trust, and resilience. Present the topic in a bit more detail with this Devsecops Best Practices For Secure Various Impact Of Devsecops Process In Organization. Use it as a tool for discussion and navigation on Automated Infrastructure Management, Vulnerability Management, Resilient Application Design. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Devsecops Best Practices For Secure Ways To Create Devsecops Culture In Organization
Devsecops Best Practices For Secure Ways To Create Devsecops Culture In OrganizationThis slide showcases the way to develop a DevSecOps culture in an organization. The purpose of this slide is to discuss the methods to create a DevSecOps culture, these include the value of security, early detection of vulnerabilities, small iterations, inclusive collaboration, etc. Deliver an outstanding presentation on the topic using this Devsecops Best Practices For Secure Ways To Create Devsecops Culture In Organization. Dispense information and present a thorough explanation of Inclusive Collaboration, Security Professionals, Audit Preparedness, Security Training using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
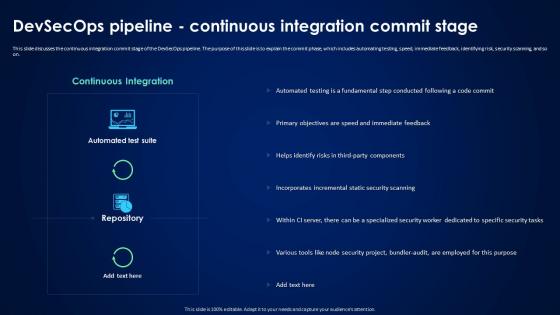 Devsecops Pipeline Continuous Integration Commit Devsecops Best Practices For Secure
Devsecops Pipeline Continuous Integration Commit Devsecops Best Practices For SecureThis slide discusses the continuous integration commit stage of the DevSecOps pipeline. The purpose of this slide is to explain the commit phase, which includes automating testing, speed, immediate feedback, identifying risk, security scanning, and so on. Deliver an outstanding presentation on the topic using this Devsecops Pipeline Continuous Integration Commit Devsecops Best Practices For Secure. Dispense information and present a thorough explanation of Continuous Integration, Devsecops Pipeline, Specialized Security Worker, Bundler Audit using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
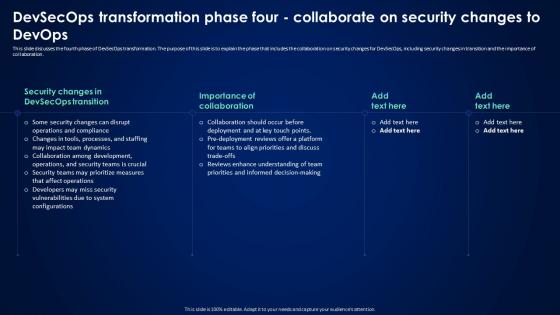 Devsecops Transformation Phase Four Collaborate On Security Devsecops Best Practices For Secure
Devsecops Transformation Phase Four Collaborate On Security Devsecops Best Practices For SecureThis slide discusses the fourth phase of DevSecOps transformation. The purpose of this slide is to explain the phase that includes the collaboration on security changes for DevSecOps, including security changes in transition and the importance of collaboration. Present the topic in a bit more detail with this Devsecops Transformation Phase Four Collaborate On Security Devsecops Best Practices For Secure. Use it as a tool for discussion and navigation on Devsecops Transformation, Collaboration On Security Changes, Importance Of Collaboration. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
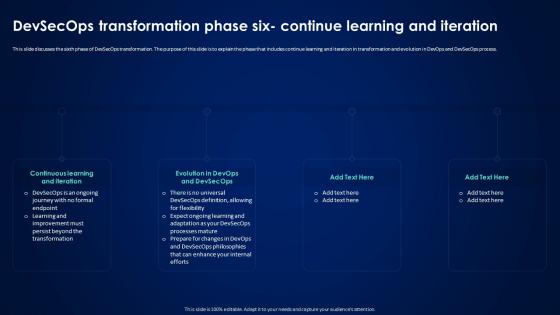 Devsecops Transformation Phase Six Continue Learning Devsecops Best Practices For Secure
Devsecops Transformation Phase Six Continue Learning Devsecops Best Practices For SecureThis slide discusses the sixth phase of DevSecOps transformation. The purpose of this slide is to explain the phase that includes continue learning and iteration in transformation and evolution in DevOps and DevSecOps process. Increase audience engagement and knowledge by dispensing information using Devsecops Transformation Phase Six Continue Learning Devsecops Best Practices For Secure. This template helps you present information on four stages. You can also present information on Continuous Learning And Iteration, Devsecops Transformation, Learning And Iteration, Devsecops Philosophies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons Slide For Devsecops Best Practices For Secure Applications
Icons Slide For Devsecops Best Practices For Secure ApplicationsIntroducing our well researched set of slides titled Icons Slide For Devsecops Best Practices For Secure Applications. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
 Y196 Hands On Blockchain Security Risk Management And Best Practices Table Of Contents BCT SS V
Y196 Hands On Blockchain Security Risk Management And Best Practices Table Of Contents BCT SS VIntroducing Y196 Hands On Blockchain Security Risk Management And Best Practices Table Of Contents BCT SS V to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Blockchain Cyber Security, Risk Management Process, using this template. Grab it now to reap its full benefits.
-
 Agenda For Hands On Blockchain Security Risk Management And Best Practices BCT SS V
Agenda For Hands On Blockchain Security Risk Management And Best Practices BCT SS VIntroducing Agenda For Hands On Blockchain Security Risk Management And Best Practices BCT SS V to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Cybersecurity Market Insights, Blockchain Technology, Threats And Attacks, using this template. Grab it now to reap its full benefits.
-
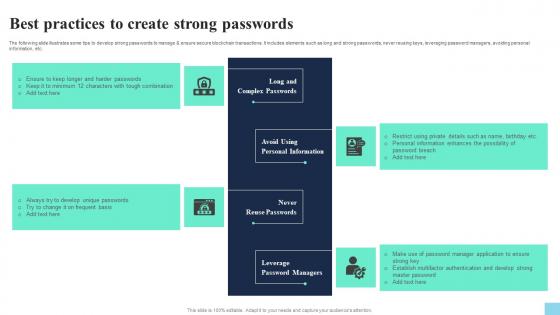 Best Practices To Create Strong Passwords Hands On Blockchain Security Risk BCT SS V
Best Practices To Create Strong Passwords Hands On Blockchain Security Risk BCT SS VThe following slide illustrates some tips to develop strong passwords to manage and ensure secure blockchain transactions. It includes elements such as long and strong passwords, never reusing keys, leveraging password managers, avoiding personal information, etc. Increase audience engagement and knowledge by dispensing information using Best Practices To Create Strong Passwords Hands On Blockchain Security Risk BCT SS V. This template helps you present information on four stages. You can also present information on Complex Passwords, Personal Information, Never Reuse Passwords using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Icons Slide For Hands On Blockchain Security Risk Management And Best Practices BCT SS V
Icons Slide For Hands On Blockchain Security Risk Management And Best Practices BCT SS VIntroducing our well researched set of slides titled Icons Slide For Hands On Blockchain Security Risk Management And Best Practices BCT SS V. It displays a hundred percent editable icons. You can use these icons in your presentation to captivate your audiences attention. Download now and use it multiple times.
-
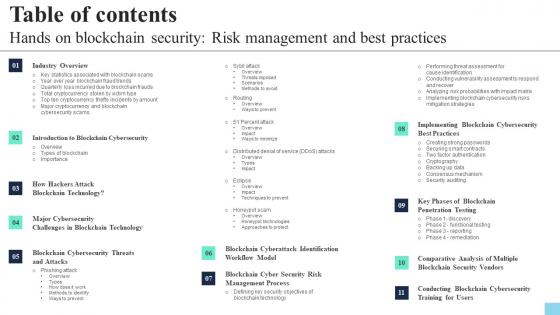 Table Of Contents Hands On Blockchain Security Risk Management And Best Practices BCT SS V
Table Of Contents Hands On Blockchain Security Risk Management And Best Practices BCT SS VIncrease audience engagement and knowledge by dispensing information using Table Of Contents Hands On Blockchain Security Risk Management And Best Practices BCT SS V. This template helps you present information on one stages. You can also present information on Industry Overview, Blockchain Cybersecurity, Blockchain Cyber Security Risk using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Crypto Wallets Types And Applications Best Practices For The Security Of Crypto Wallets In Market
Crypto Wallets Types And Applications Best Practices For The Security Of Crypto Wallets In MarketThis slide aims to highlight some broad security aspects of crypto wallets. This slide outlines the general security purposes such as passwords, 2FA accounts, phrases for secure passwords, secure hardware, keeping the seed phrase off devices as well, etc. Deliver an outstanding presentation on the topic using this Crypto Wallets Types And Applications Best Practices For The Security Of Crypto Wallets In Market. Dispense information and present a thorough explanation of Storage Mechanism, Network, Crypto Wallets In Market, Multisignature Wallets using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
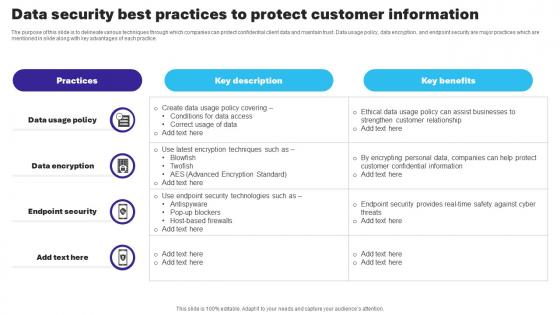 Essential Guide To Database Marketing Data Security Best Practices To Protect Customer Information MKT SS V
Essential Guide To Database Marketing Data Security Best Practices To Protect Customer Information MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Deliver an outstanding presentation on the topic using this Essential Guide To Database Marketing Data Security Best Practices To Protect Customer Information MKT SS V Dispense information and present a thorough explanation of Data Usage Policy, Data Encryption, Endpoint Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
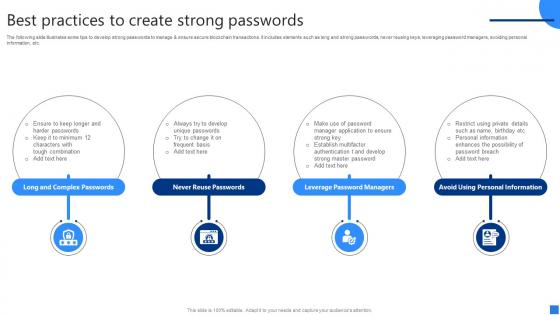 Best Practices To Create Securing Blockchain Transactions A Beginners Guide BCT SS V
Best Practices To Create Securing Blockchain Transactions A Beginners Guide BCT SS VThe following slide illustrates some tips to develop strong passwords to manage and ensure secure blockchain transactions. It includes elements such as long and strong passwords, never reusing keys, leveraging password managers, avoiding personal information, etc. Increase audience engagement and knowledge by dispensing information using Best Practices To Create Securing Blockchain Transactions A Beginners Guide BCT SS V. This template helps you present information on four stages. You can also present information on Long And Complex Passwords, Never Reuse Passwords, Leverage Password Managers using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
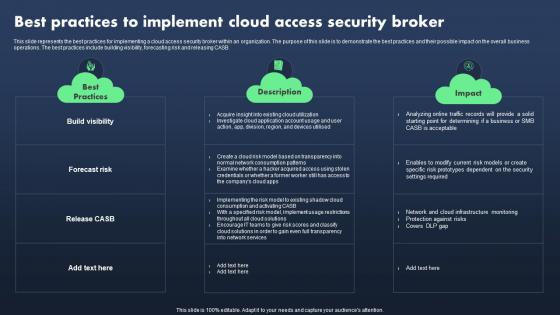 Sase Model Best Practices To Implement Cloud Access Security Broker
Sase Model Best Practices To Implement Cloud Access Security BrokerThis slide represents the best practices for implementing a cloud access security broker within an organization. The purpose of this slide is to demonstrate the best practices and their possible impact on the overall business operations. The best practices include building visibility, forecasting risk and releasing CASB. Present the topic in a bit more detail with this Sase Model Best Practices To Implement Cloud Access Security Broker. Use it as a tool for discussion and navigation on Best Practices, Description, Impact. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
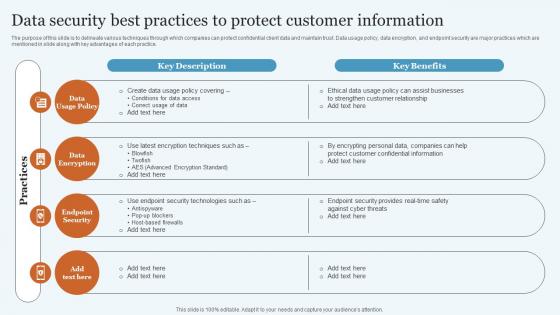 Data Security Best Practices To Protect Database Marketing Practices To Increase MKT SS V
Data Security Best Practices To Protect Database Marketing Practices To Increase MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Increase audience engagement and knowledge by dispensing information using Data Security Best Practices To Protect Database Marketing Practices To Increase MKT SS V. This template helps you present information on four stages. You can also present information on Policy, Encryption, Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
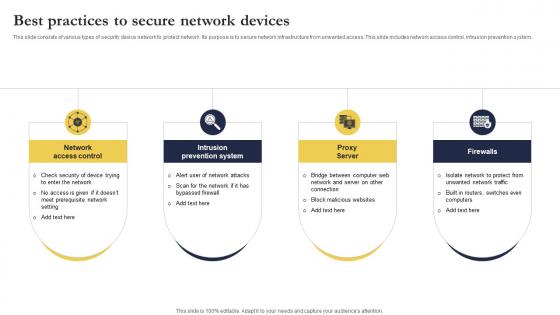 Best Practices To Secure Network Devices
Best Practices To Secure Network DevicesThis slide consists of various types of security device network to protect network. Its purpose is to secure network infrastructure from unwanted access. This slide includes network access control, intrusion prevention system. Introducing our premium set of slides with Best Practices To Secure Network Devices. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Network, System, Server. So download instantly and tailor it with your information.
-
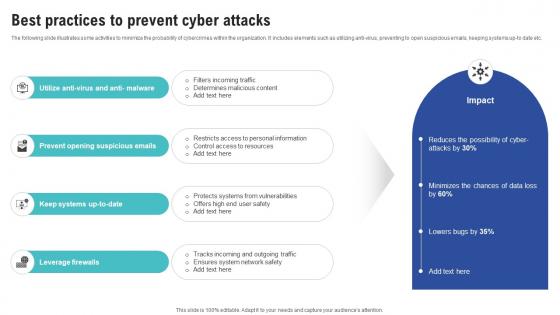 Best Practices To Prevent Cyber Attacks Creating Cyber Security Awareness
Best Practices To Prevent Cyber Attacks Creating Cyber Security AwarenessThe following slide illustrates some activities to minimize the probability of cybercrimes within the organization. It includes elements such as utilizing anti-virus, preventing to open suspicious emails, keeping systems up-to date etc. Introducing Best Practices To Prevent Cyber Attacks Creating Cyber Security Awareness to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on Opening Suspicious Emails, Leverage Firewalls using this template. Grab it now to reap its full benefits.
-
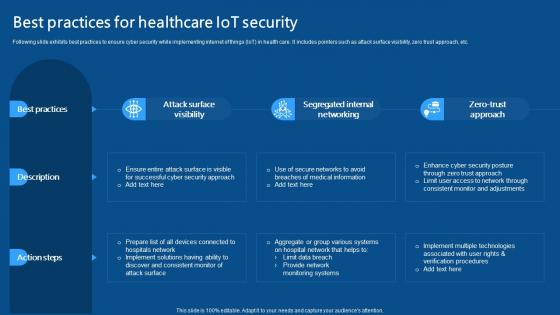 Best Practices For Healthcare IoT Security IoMT Applications In Medical Industry IoT SS V
Best Practices For Healthcare IoT Security IoMT Applications In Medical Industry IoT SS VFollowing slide exhibits best practices to ensure cyber security while implementing internet of things IoT in health care. It includes pointers such as attack surface visibility, zero trust approach, etc. Introducing Best Practices For Healthcare IoT Security IoMT Applications In Medical Industry IoT SS V to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Attack Surface Visibility, Segregated Internal Networking, Zero Trust Approach, using this template. Grab it now to reap its full benefits.
-
 Opsec Cyber Security Best Practices Icon
Opsec Cyber Security Best Practices IconIntroducing our Opsec Cyber Security Best Practices Icon set of slides. The topics discussed in these slides are Cyber Security, Best Practices, Icon. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
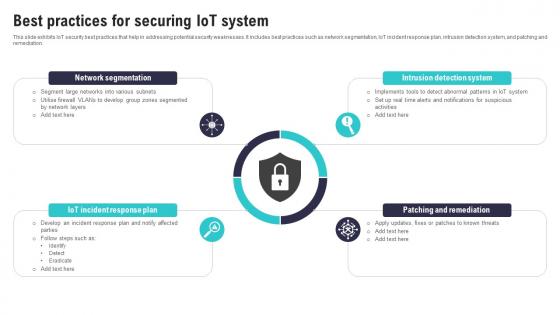 Best Practices For Securing IoT System IoT Security And Privacy Safeguarding IoT SS
Best Practices For Securing IoT System IoT Security And Privacy Safeguarding IoT SSThis slide exhibits IoT security best practices that help in addressing potential security weaknesses. It includes best practices such as network segmentation, IoT incident response plan, intrusion detection system, and patching and remediation. Increase audience engagement and knowledge by dispensing information using Best Practices For Securing IoT System IoT Security And Privacy Safeguarding IoT SS. This template helps you present information on four stages. You can also present information on Network Segmentation, Intrusion Detection System, Patching Remediation using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
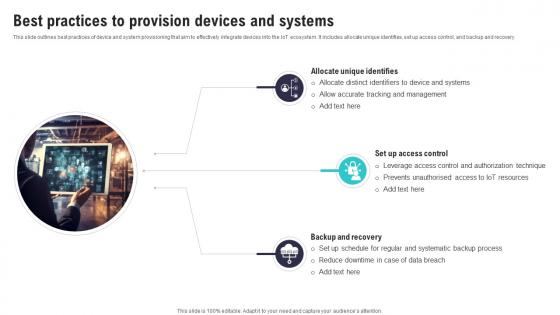 Best Practices To Provision Devices And Systems IoT Security And Privacy Safeguarding IoT SS
Best Practices To Provision Devices And Systems IoT Security And Privacy Safeguarding IoT SSThis slide outlines best practices of device and system provisioning that aim to effectively integrate devices into the IoT ecosystem. It includes allocate unique identifies, set up access control, and backup and recovery. Introducing Best Practices To Provision Devices And Systems IoT Security And Privacy Safeguarding IoT SS to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Unique Identifies, Systematic Backup Process, Reduce Downtime, using this template. Grab it now to reap its full benefits.
-
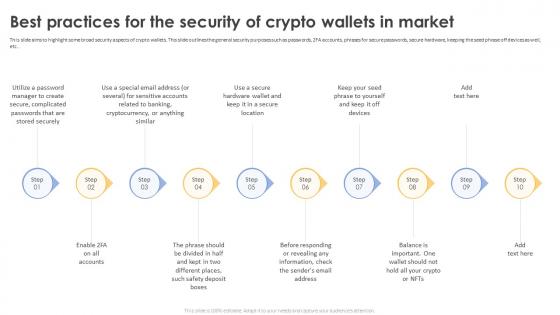 Secure Your Digital Assets Best Practices For The Security Of Crypto Wallets In Market
Secure Your Digital Assets Best Practices For The Security Of Crypto Wallets In MarketThis slide aims to highlight some broad security aspects of crypto wallets. This slide outlines the general security purposes such as passwords, 2FA accounts, phrases for secure passwords, secure hardware, keeping the seed phrase off devices as well, etc. Introducing Secure Your Digital Assets Best Practices For The Security Of Crypto Wallets In Market to increase your presentation threshold. Encompassed with ten stages, this template is a great option to educate and entice your audience. Dispence information on Security Of Crypto Wallets, Secure Hardware, Special Email Address, Complicated Passwords, using this template. Grab it now to reap its full benefits.
-
 Best Practices To Secure Continuous Deployment Pipeline
Best Practices To Secure Continuous Deployment PipelineThis slide represents continuous deployment pipeline best practices. It aims to conduct consistent comprehensive audits on system and code to control high level security and minimize risk of cyberattack. It includes various elements such as eliminating hardcoded credentials from tools, restricting access to non humans, etc. Presenting our set of slides with Best Practices To Secure Continuous Deployment Pipeline. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Reduce, Security, Human.
-
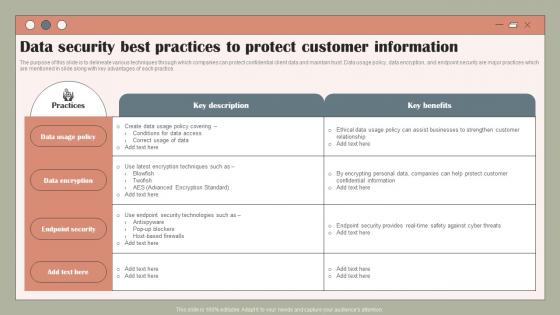 Data Security Best Practices To Protect Using Customer Data To Improve MKT SS V
Data Security Best Practices To Protect Using Customer Data To Improve MKT SS VThe purpose of this slide is to delineate various techniques through which companies can protect confidential client data and maintain trust. Data usage policy, data encryption, and endpoint security are major practices which are mentioned in slide along with key advantages of each practice. Deliver an outstanding presentation on the topic using this Data Security Best Practices To Protect Using Customer Data To Improve MKT SS V. Dispense information and present a thorough explanation of Policy, Data, Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
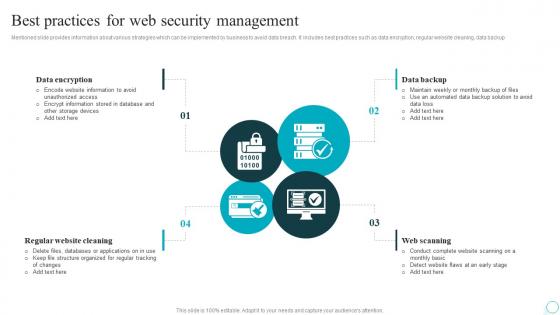 Best Practices For Web Security Management Strategic Guide For Web Design Company
Best Practices For Web Security Management Strategic Guide For Web Design CompanyMentioned slide provides information about various strategies which can be implemented by business to avoid data breach. It includes best practices such as data encryption, regular website cleaning, data backup Introducing Best Practices For Web Security Management Strategic Guide For Web Design Company to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Encryption, Cleaning, Scanning, using this template. Grab it now to reap its full benefits.
-
 Firewall Network Security Firewall Best Practices To Secure The Network
Firewall Network Security Firewall Best Practices To Secure The NetworkThis slide represents the different critical practices to secure a network through a firewall. The purpose of this slide is to showcase a few key steps that organizations should keep in mind to secure their network properly, such as strengthening and configuring the firewall correctly, planning firewall deployment, and so on. Deliver an outstanding presentation on the topic using this Firewall Network Security Firewall Best Practices To Secure The Network Dispense information and present a thorough explanation of Problem,Solution,Outcome using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Best Practices To Implement Cloud Access Security Broker Next Generation CASB
Best Practices To Implement Cloud Access Security Broker Next Generation CASBThis slide represents the best practices for implementing a cloud access security broker within an organization. The purpose of this slide is to demonstrate the best practices and their possible impact on the overall business operations. The best practices include building visibility, forecasting risk and releasing CASB. Deliver an outstanding presentation on the topic using this Best Practices To Implement Cloud Access Security Broker Next Generation CASB Dispense information and present a thorough explanation of Build Visibility, Forecast Risk, Release CASB, Best Practices using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
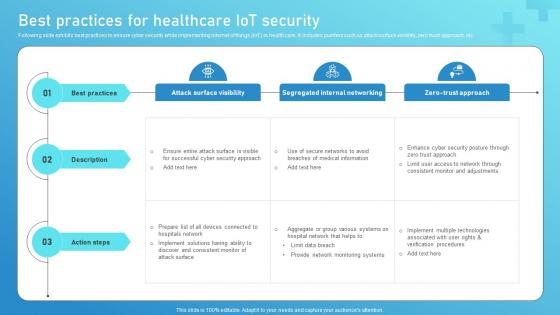 Best Practices For Healthcare IoT Security Guide To Networks For IoT Healthcare IoT SS V
Best Practices For Healthcare IoT Security Guide To Networks For IoT Healthcare IoT SS VFollowing slide exhibits best practices to ensure cyber security while implementing internet of things IoT in health care. It includes pointers such as attack surface visibility, zero trust approach, etc. Present the topic in a bit more detail with this Best Practices For Healthcare IoT Security Guide To Networks For IoT Healthcare IoT SS V. Use it as a tool for discussion and navigation on Attack Surface Visibility, Segregated Internal Networking, Zero Trust Approach. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
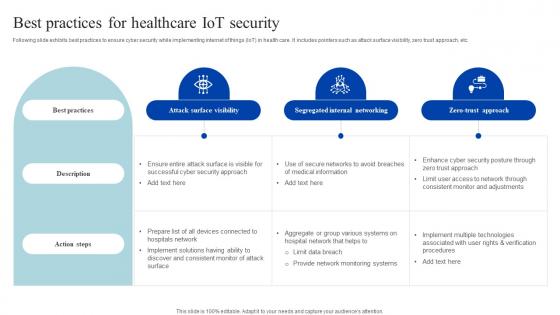 Best Practices For Healthcare Iot Security How Iomt Is Transforming Medical Industry IoT SS V
Best Practices For Healthcare Iot Security How Iomt Is Transforming Medical Industry IoT SS VFollowing slide exhibits best practices to ensure cyber security while implementing internet of things IoT in health care. It includes pointers such as attack surface visibility, zero trust approach, etc. Present the topic in a bit more detail with this Best Practices For Healthcare Iot Security How Iomt Is Transforming Medical Industry IoT SS V. Use it as a tool for discussion and navigation on Attack Surface Visibility, Segregated Internal Networking, Zero Trust Approach. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
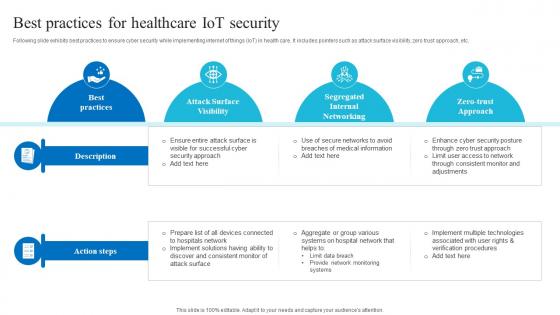 Best For Healthcare Iot Security Role Of Iot And Technology In Healthcare Industry IoT SS V
Best For Healthcare Iot Security Role Of Iot And Technology In Healthcare Industry IoT SS VFollowing slide exhibits best practices to ensure cyber security while implementing internet of things IoT in health care. It includes pointers such as attack surface visibility, zero trust approach, etc. Deliver an outstanding presentation on the topic using this Best For Healthcare Iot Security Role Of Iot And Technology In Healthcare Industry IoT SS V. Dispense information and present a thorough explanation of Attack Surface Visibility, Segregated Internal Networking, Zero Trust Approach using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Best Practices In Cyber Security Risk Management
Best Practices In Cyber Security Risk ManagementThis slide exhibits cyber risk management practices which enable businesses to prioritize risks and apply the right kinds of security controls to minimize impact. It include adaptive and continuous risk management, strict security protocols, cyber security risk management strategy. Introducing our premium set of slides with Best Practices In Cyber Security Risk Management. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Know Organizations IT Environment And Assets. Impose Strict Security Protocols, Adaptive And Continuous Risk Management . So download instantly and tailor it with your information.
-
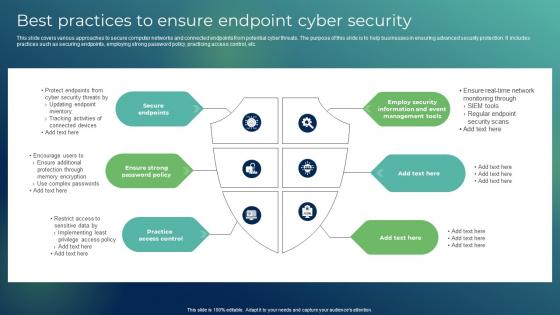 Best Practices To Ensure Endpoint Cyber Security
Best Practices To Ensure Endpoint Cyber SecurityThis slide covers various approaches to secure computer networks and connected endpoints from potential cyber threats. The purpose of this slide is to help businesses in ensuring advanced security protection. It includes practices such as securing endpoints, employing strong password policy, practicing access control, etc. Presenting our well structured Best Practices To Ensure Endpoint Cyber Security The topics discussed in this slide are Secure Endpoints, Ensure Strong Password Policy, Practice Access Control This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
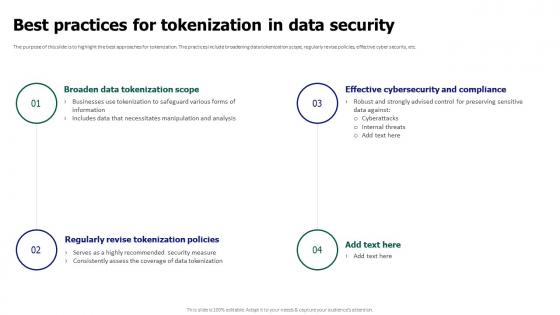 Tokenization For Improved Data Security Best Practices For Tokenization In Data Security
Tokenization For Improved Data Security Best Practices For Tokenization In Data SecurityThe purpose of this slide is to highlight the best approaches for tokenization. The practices include broadening data tokenization scope, regularly revise policies, effective cyber security, etc. Increase audience engagement and knowledge by dispensing information using Tokenization For Improved Data Security Best Practices For Tokenization In Data Security. This template helps you present information on four stages. You can also present information on Effective Cybersecurity And Compliance, Broaden Data Tokenization Scope, Regularly Revise Tokenization Policies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
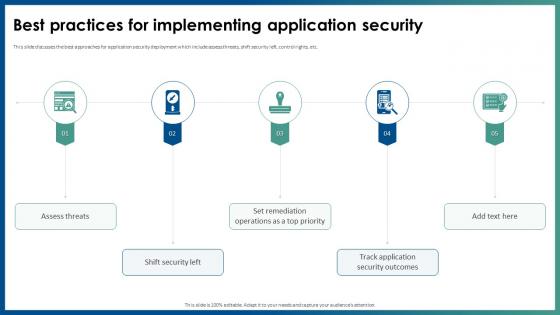 Best Practices For Implementing Application Security
Best Practices For Implementing Application SecurityThis slide discusses the best approaches for application security deployment which include assess threats, shift security left, control rights, etc. Increase audience engagement and knowledge by dispensing information using Best Practices For Implementing Application Security. This template helps you present information on five stages. You can also present information on Shift Security Left, Track Application Security Outcomes, Assess Threats, Application Security using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.



