Powerpoint Templates and Google slides for By Security Type
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Overcome the it security challenges facing by healthcare company case competition complete deck
Overcome the it security challenges facing by healthcare company case competition complete deckDeliver this complete deck to your team members and other collaborators. Encompassed with stylized slides presenting various concepts, this Overcome The It Security Challenges Facing By Healthcare Company Case Competition Complete Deck is the best tool you can utilize. Personalize its content and graphics to make it unique and thought provoking. All the fourty six slides are editable and modifiable, so feel free to adjust them to your business setting. The font, color, and other components also come in an editable format making this PPT design the best choice for your next presentation. So, download now.
-
 Secure Email Solution Investor Funding Elevator Pitch Deck By Paubox Ppt Template
Secure Email Solution Investor Funding Elevator Pitch Deck By Paubox Ppt TemplateProvide your investors essential insights into your project and company with this influential Secure Email Solution Investor Funding Elevator Pitch Deck By Paubox Ppt Template. This is an in-depth pitch deck PPT template that covers all the extensive information and statistics of your organization. From revenue models to basic statistics, there are unique charts and graphs added to make your presentation more informative and strategically advanced. This gives you a competitive edge and ample amount of space to showcase your brands USP. Apart from this, all the thirty four slides added to this deck, helps provide a breakdown of various facets and key fundamentals. Including the history of your company, marketing strategies, traction, etc. The biggest advantage of this template is that it is pliable to any business domain be it e-commerce, IT revolution, etc, to introduce a new product or bring changes to the existing one. Therefore, download this complete deck now in the form of PNG, JPG, or PDF.
-
 Blockchain Impact On Education Industry By Providing Enhanced Security System Training Ppt
Blockchain Impact On Education Industry By Providing Enhanced Security System Training PptPresenting Blockchain Impact on Education Industry by Providing Enhanced Security System. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. All slides are customizable. You can add or delete the content as per your need. Download this professionally designed business presentation, add your content, and present it with confidence.
-
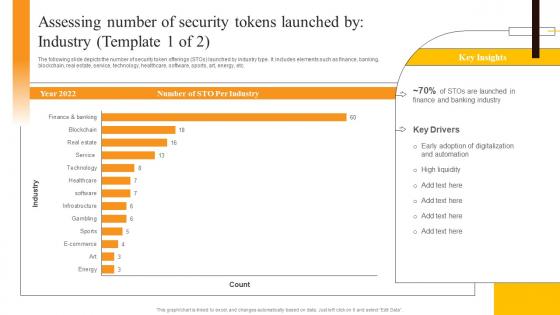 Assessing Number Of Security Tokens Launched By Industry Security Token Offerings BCT SS
Assessing Number Of Security Tokens Launched By Industry Security Token Offerings BCT SSThe following slide depicts the number of security token offerings STOs launched by industry type. It includes elements such as finance, banking, blockchain, real estate, service, technology, healthcare, software, sports, art, energy, etc. Present the topic in a bit more detail with this Assessing Number Of Security Tokens Launched By Industry Security Token Offerings BCT SS. Use it as a tool for discussion and navigation on Assessing Number, Security Tokens, Industry. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
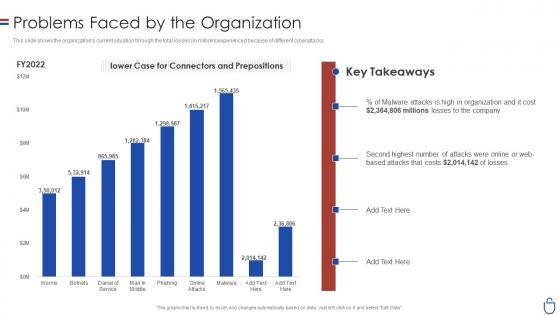 Data security it problems faced by the organization ppt slides layout
Data security it problems faced by the organization ppt slides layoutThis slide shows the organizations current situation through the total losses in millions experienced because of different cyberattacks. Deliver an outstanding presentation on the topic using this Data Security IT Problems Faced By The Organization Ppt Slides Layout. Dispense information and present a thorough explanation of Worms, Phishing, Online Attacks, Man Middle using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
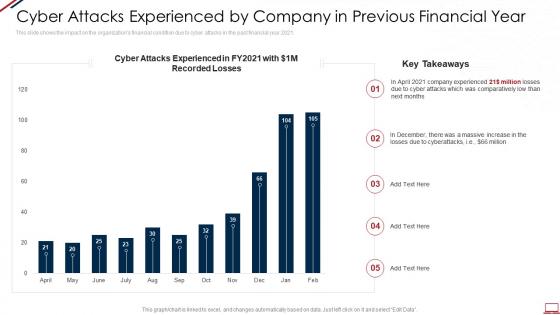 Computer system security cyber attacks experienced by company in previous financial year
Computer system security cyber attacks experienced by company in previous financial yearThis slide shows the impact on the organizations financial condition due to cyber attacks in the past financial year 2021. Present the topic in a bit more detail with this Computer System Security Cyber Attacks Experienced By Company In Previous Financial Year. Use it as a tool for discussion and navigation on Cyber Attacks Experienced By Company In Previous Financial Year. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
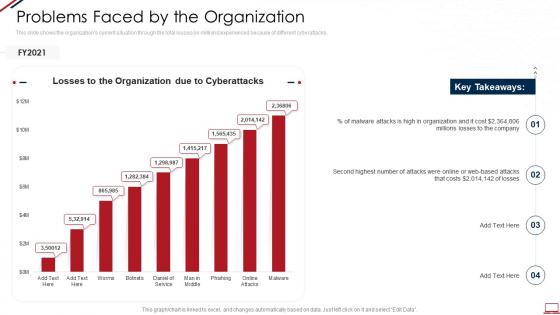 Computer system security problems faced by the organization
Computer system security problems faced by the organizationThis slide shows the organizations current situation through the total losses in millions experienced because of different cyberattacks. Deliver an outstanding presentation on the topic using this Computer System Security Problems Faced By The Organization. Dispense information and present a thorough explanation of Problems Faced By The Organization using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
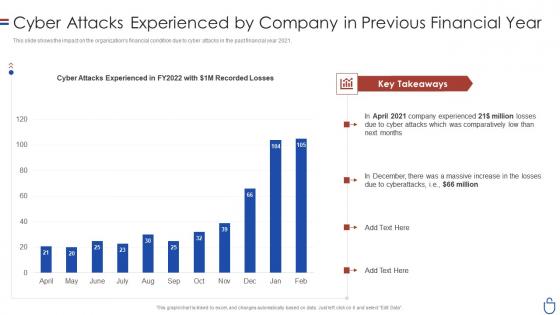 Data security it cyber attacks experienced by company in previous financial year
Data security it cyber attacks experienced by company in previous financial yearThis slide shows the impact on the organizations financial condition due to cyber attacks in the past financial year 2021. Deliver an outstanding presentation on the topic using this Data Security IT Cyber Attacks Experienced By Company In Previous Financial Year. Dispense information and present a thorough explanation of Cyber Attacks Experienced, FY2022, Comparatively using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
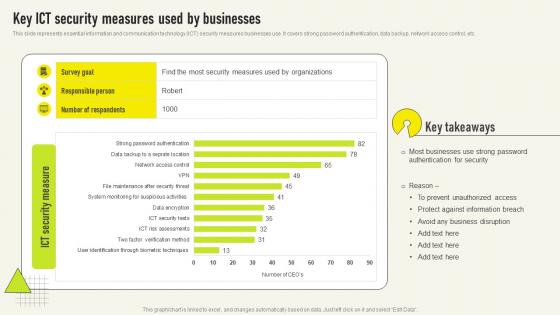 Key Ict Security Measures Used By Comprehensive Guide For Deployment Strategy SS V
Key Ict Security Measures Used By Comprehensive Guide For Deployment Strategy SS VThis slide represents essential information and communication technology ICT security measures businesses use It covers strong password authentication, data backup, network access control, etc Presenting our well structured Key Ict Security Measures Used By Comprehensive Guide For Deployment Strategy SS V The topics discussed in this slide are Authentication Security, Most Businesses, Protect Against This is an instantly available PowerPoint presentation that can be edited conveniently Download it right away and captivate your audience
-
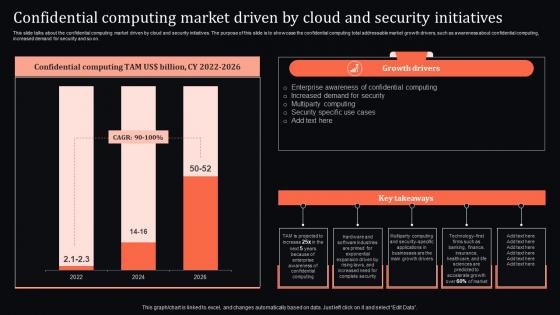 Confidential Driven By Cloud And Security Initiatives Confidential Computing System Technology
Confidential Driven By Cloud And Security Initiatives Confidential Computing System TechnologyThis slide talks about the confidential computing market driven by cloud and security initiatives. The purpose of this slide is to showcase the confidential computing total addressable market growth drivers, such as awareness about confidential computing, increased demand for security and so on. Deliver an outstanding presentation on the topic using this Confidential Driven By Cloud And Security Initiatives Confidential Computing System Technology. Dispense information and present a thorough explanation of Confidential, Enterprise, Awareness using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
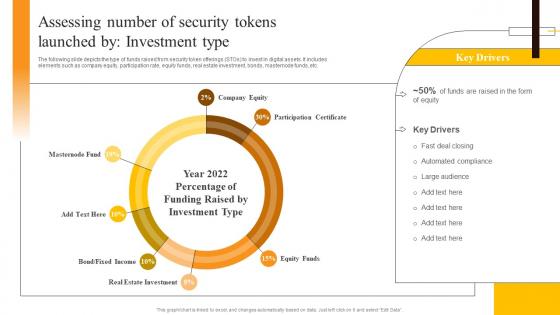 Assessing Number Of Security Tokens Launched By Investment Security Token Offerings BCT SS
Assessing Number Of Security Tokens Launched By Investment Security Token Offerings BCT SSThe following slide depicts the type of funds raised from security token offerings STOs to invest in digital assets. It includes elements such as company equity, participation rate, equity funds, real estate investment, bonds, masternode funds, etc. Deliver an outstanding presentation on the topic using this Assessing Number Of Security Tokens Launched By Investment Security Token Offerings BCT SS. Dispense information and present a thorough explanation of Real Estate Investment, Participation Certificate, Company Equity using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
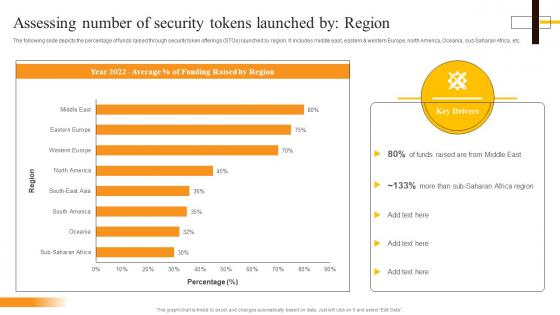 Assessing Number Of Security Tokens Launched By Region Security Token Offerings BCT SS
Assessing Number Of Security Tokens Launched By Region Security Token Offerings BCT SSThe following slide depicts the percentage of funds raised through security token offerings STOs launched by region. It includes middle east, eastern and western Europe, north America, Oceania, sub Saharan Africa, etc. Present the topic in a bit more detail with this Assessing Number Of Security Tokens Launched By Region Security Token Offerings BCT SS. Use it as a tool for discussion and navigation on Assessing Number, Security Tokens, Region. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
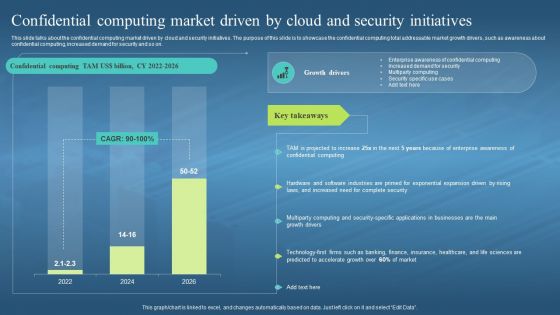 Confidential Computing Market Driven By Cloud And Security Confidential Computing Hardware
Confidential Computing Market Driven By Cloud And Security Confidential Computing HardwareThis slide talks about the confidential computing market driven by cloud and security initiatives. The purpose of this slide is to showcase the confidential computing total addressable market growth drivers, such as awareness about confidential computing, increased demand for security and so on. Deliver an outstanding presentation on the topic using this Confidential Computing Market Driven By Cloud And Security Confidential Computing Hardware. Dispense information and present a thorough explanation of Confidential Computing, Market Driven By Cloud, Security Initiatives, Awareness About Confidential Computing, Demand For Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
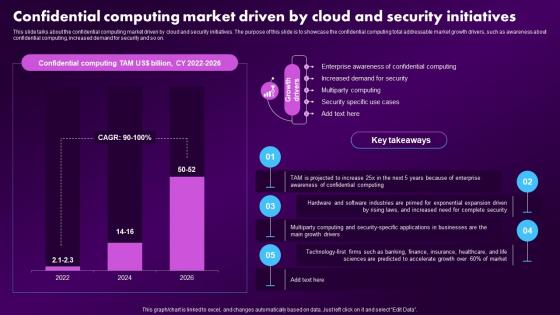 F1604 Confidential Computing Market Driven By Cloud And Security Confidential Computing Market
F1604 Confidential Computing Market Driven By Cloud And Security Confidential Computing MarketThis slide talks about the confidential computing market driven by cloud and security initiatives. The purpose of this slide is to showcase the confidential computing total addressable market growth drivers, such as awareness about confidential computing, increased demand for security and so on. Present the topic in a bit more detail with this F1604 Confidential Computing Market Driven By Cloud And Security Confidential Computing Market. Use it as a tool for discussion and navigation on Enterprise, Awareness, Confidential. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
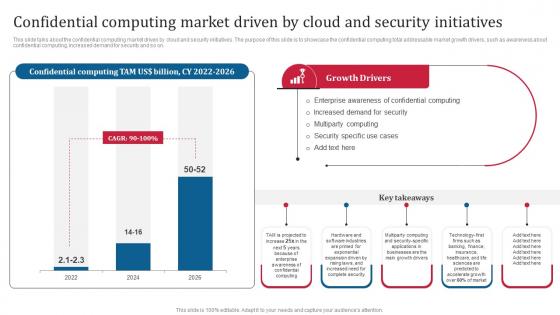 Confidential Computing Consortium Confidential Computing Market Driven By Cloud And Security
Confidential Computing Consortium Confidential Computing Market Driven By Cloud And SecurityThis slide talks about the confidential computing market driven by cloud and security initiatives. The purpose of this slide is to showcase the confidential computing total addressable market growth drivers, such as awareness about confidential computing, increased demand for security and so on. Present the topic in a bit more detail with this Confidential Computing Consortium Confidential Computing Market Driven By Cloud And Security. Use it as a tool for discussion and navigation on Confidential Computing, Market Driven By Cloud, Security Initiatives, Security Specific Use Cases. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
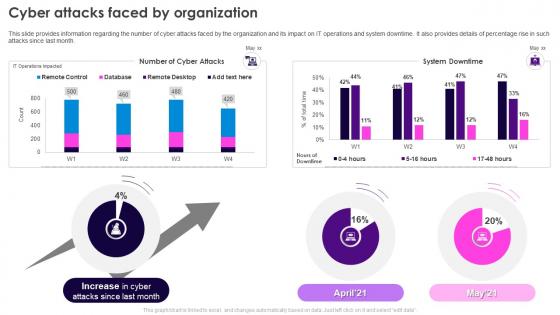 Cyber Attacks Faced By Organization Security Plan To Prevent Cyber
Cyber Attacks Faced By Organization Security Plan To Prevent CyberThis slide provides information regarding the number of cyber attacks faced by the organization and its impact on IT operations and system downtime. It also provides details of percentage rise in such attacks since last month. Present the topic in a bit more detail with this Cyber Attacks Faced By Organization Security Plan To Prevent Cyber. Use it as a tool for discussion and navigation on Cyber Attacks, IT Operations, System Downtime. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
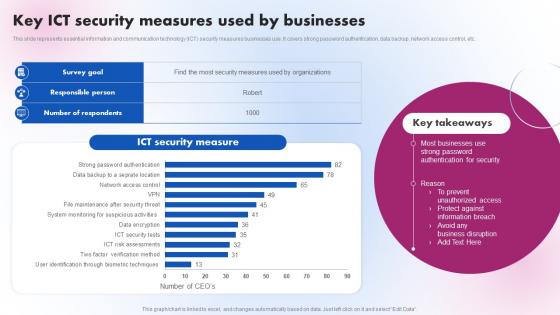 Key ICT Security Measures Used By Businesses Delivering ICT Services For Enhanced Business Strategy SS V
Key ICT Security Measures Used By Businesses Delivering ICT Services For Enhanced Business Strategy SS VThis slide represents essential information and communication technology ICT security measures businesses use. It covers strong password authentication, data backup, network access control, etc. Present the topic in a bit more detail with this Key ICT Security Measures Used By Businesses Delivering ICT Services For Enhanced Business Strategy SS V. Use it as a tool for discussion and navigation on Security Measure. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
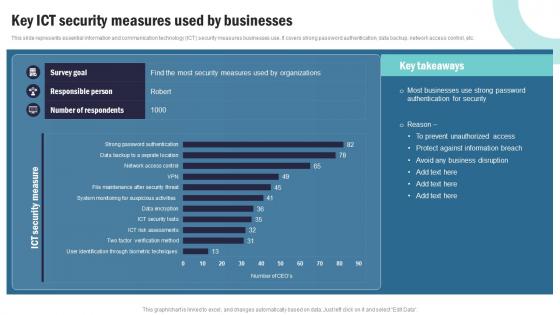 Strategic Plan To Implement Key Ict Security Measures Used By Businesses Strategy SS V
Strategic Plan To Implement Key Ict Security Measures Used By Businesses Strategy SS VThis slide represents essential information and communication technology ICT security measures businesses use. It covers strong password authentication, data backup, network access control, etc. Present the topic in a bit more detail with this Strategic Plan To Implement Key Ict Security Measures Used By Businesses Strategy SS V Use it as a tool for discussion and navigation on Data Sets And Compliance, IT Service Planning This template is free to edit as deemed fit for your organization. Therefore download it now.
-
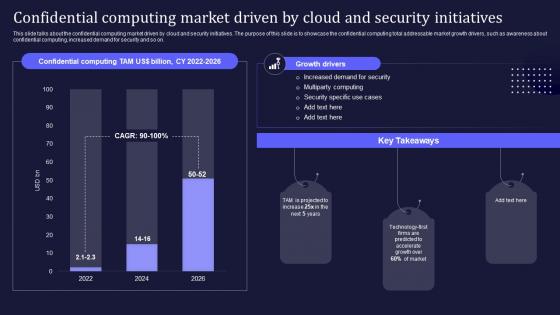 Confidential Computing V2 Market Driven By Cloud And Security Initiatives
Confidential Computing V2 Market Driven By Cloud And Security InitiativesThis slide talks about the confidential computing market driven by cloud and security initiatives. The purpose of this slide is to showcase the confidential computing total addressable market growth drivers, such as awareness about confidential computing, increased demand for security and so on. Deliver an outstanding presentation on the topic using this Confidential Computing V2 Market Driven By Cloud And Security Initiatives. Dispense information and present a thorough explanation of Confidential Computing Market, Cloud And Security Initiatives, Total Addressable Market using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
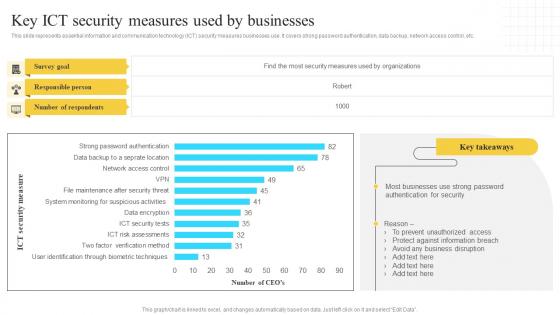 Implementation Of Information Key Ict Security Measures Used By Businesses Strategy SS V
Implementation Of Information Key Ict Security Measures Used By Businesses Strategy SS VThis slide represents essential information and communication technology ICT security measures businesses use. It covers strong password authentication, data backup, network access control, etc. Deliver an outstanding presentation on the topic using this Implementation Of Information Key Ict Security Measures Used By Businesses Strategy SS V. Dispense information and present a thorough explanation of Survey Goal, Responsible Person using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
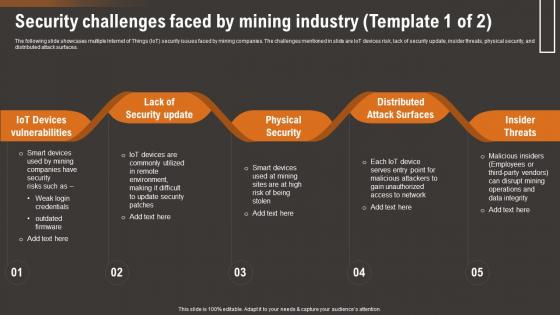 Security Challenges Faced By Mining Industry How IoT Technology Is Transforming IoT SS
Security Challenges Faced By Mining Industry How IoT Technology Is Transforming IoT SSThe following slide showcases multiple Internet of Things IoT security issues faced by mining companies. The challenges mentioned in slide are IoT devices risk, lack of security update, insider threats, physical security, and distributed attack surfaces. Present the topic in a bit more detail with this Security Challenges Faced By Mining Industry How IoT Technology Is Transforming IoT SS. Use it as a tool for discussion and navigation on Iot Devices Vulnerabilities, Lack Security Update, Physical Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
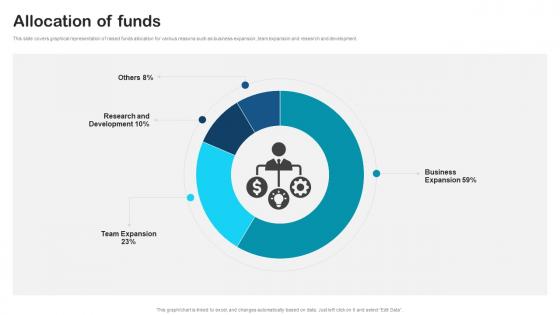 Allocation Of Funds Secure Email Solution Investor Funding Elevator Pitch Deck By Paubox
Allocation Of Funds Secure Email Solution Investor Funding Elevator Pitch Deck By PauboxThis slide covers graphical representation of raised funds allocation for various reasons such as business expansion, team expansion and research and development. Present the topic in a bit more detail with this Allocation Of Funds Secure Email Solution Investor Funding Elevator Pitch Deck By Paubox. Use it as a tool for discussion and navigation on Allocation Of Funds. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
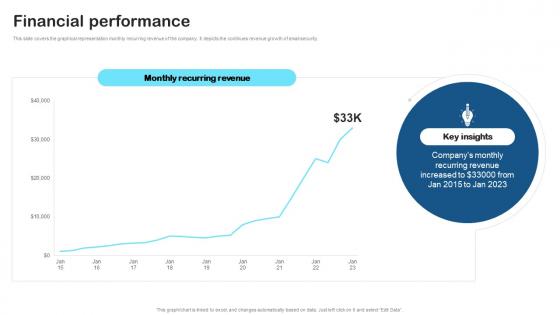 Financial Performance Secure Email Solution Investor Funding Elevator Pitch Deck By Paubox
Financial Performance Secure Email Solution Investor Funding Elevator Pitch Deck By PauboxThis slide covers the graphical representation monthly recurring revenue of the company. It depicts the continues revenue growth of email security. Present the topic in a bit more detail with this Financial Performance Secure Email Solution Investor Funding Elevator Pitch Deck By Paubox. Use it as a tool for discussion and navigation on Monthly Recurring Revenue, This template is free to edit as deemed fit for your organization. Therefore download it now.
-
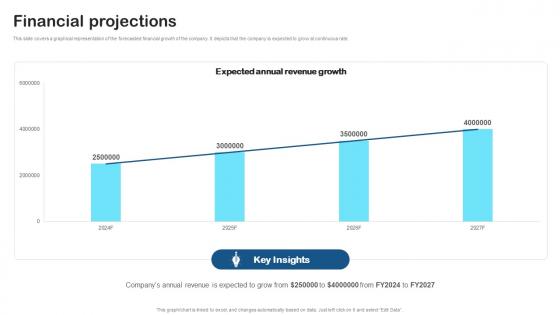 Financial Projections Secure Email Solution Investor Funding Elevator Pitch Deck By Paubox
Financial Projections Secure Email Solution Investor Funding Elevator Pitch Deck By PauboxThis slide covers a graphical representation of the forecasted financial growth of the company. It depicts that the company is expected to grow at continuous rate. Deliver an outstanding presentation on the topic using this Financial Projections Secure Email Solution Investor Funding Elevator Pitch Deck By Paubox. Dispense information and present a thorough explanation of Financial Projections using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
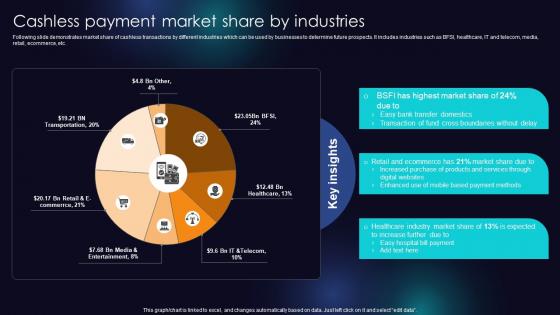 Cashless Payment Market Share By Industries Enhancing Transaction Security With E Payment
Cashless Payment Market Share By Industries Enhancing Transaction Security With E PaymentFollowing slide demonstrates market share of cashless transactions by different industries which can be used by businesses to determine future prospects. It includes industries such as BFSI, healthcare, IT and telecom, media, retail, ecommerce, etc. Deliver an outstanding presentation on the topic using this Cashless Payment Market Share By Industries Enhancing Transaction Security With E Payment Dispense information and present a thorough explanation of Bank Transfer Domestics, Payment Methods, Products And Services using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
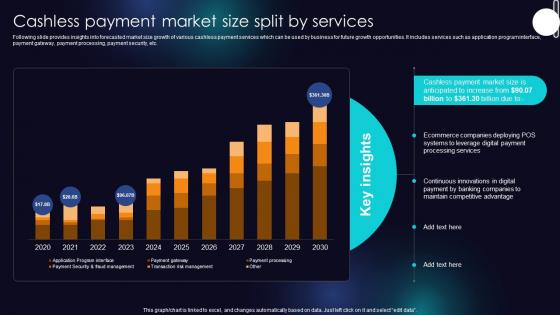 Cashless Payment Market Size Split By Services Enhancing Transaction Security With E Payment
Cashless Payment Market Size Split By Services Enhancing Transaction Security With E PaymentFollowing slide provides insights into forecasted market size growth of various cashless payment services which can be used by business for future growth opportunities. It includes services such as application program interface, payment gateway, payment processing, payment security, etc. Deliver an outstanding presentation on the topic using this Cashless Payment Market Size Split By Services Enhancing Transaction Security With E Payment Dispense information and present a thorough explanation of Processing Services, POS Systems, Ecommerce using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
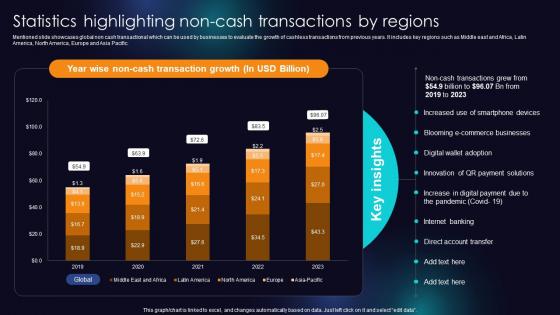 Statistics Highlighting Non Cash Transactions By Regions Enhancing Transaction Security With E Payment
Statistics Highlighting Non Cash Transactions By Regions Enhancing Transaction Security With E PaymentMentioned slide showcases global non cash transactional which can be used by businesses to evaluate the growth of cashless transactions from previous years. It includes key regions such as Middle east and Africa, Latin America, North America, Europe and Asia Pacific. Deliver an outstanding presentation on the topic using this Statistics Highlighting Non Cash Transactions By Regions Enhancing Transaction Security With E Payment Dispense information and present a thorough explanation of E Commerce Businesses, Smartphone Devices, Digital Payment using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
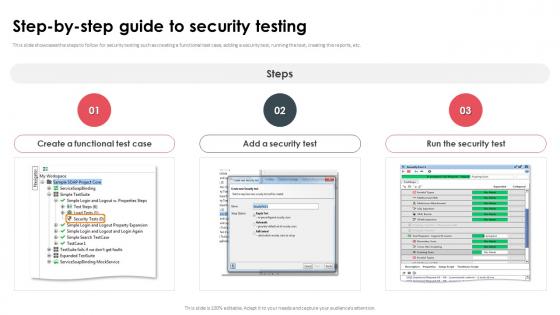 Step By Step Guide To Security Testing Ppt Icon Graphics Download
Step By Step Guide To Security Testing Ppt Icon Graphics DownloadThis slide showcases the steps to follow for security testing such as creating a functional test case, adding a security test, running the test, creating the reports, etc. Deliver an outstanding presentation on the topic using this Step By Step Guide To Security Testing Ppt Icon Graphics Download. Dispense information and present a thorough explanation of Create A Functional Test Case, Add A Security Test, Run The Security Test, Security Testing using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
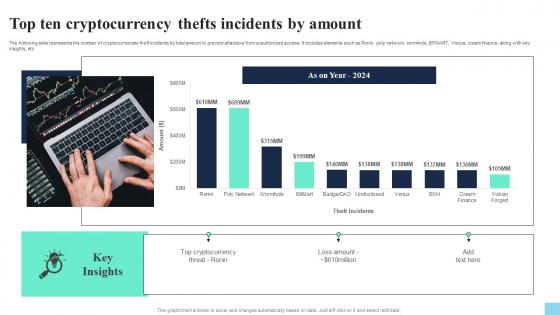 Top Ten Cryptocurrency Thefts Incidents By Amount Hands On Blockchain Security Risk BCT SS V
Top Ten Cryptocurrency Thefts Incidents By Amount Hands On Blockchain Security Risk BCT SS VThe following slide represents the number of cryptocurrencies theft incidents by total amount to prevent attackers from unauthorized access. It includes elements such as Ronin, poly network, wormhole, BITMART, Venus, cream finance, along with key insights, etc. Present the topic in a bit more detail with this Top Ten Cryptocurrency Thefts Incidents By Amount Hands On Blockchain Security Risk BCT SS V. Use it as a tool for discussion and navigation on Top Ten Cryptocurrency, Thefts Incidents By Amount. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
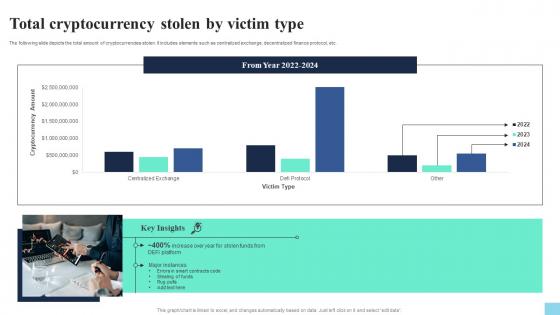 Total Cryptocurrency Stolen By Victim Type Hands On Blockchain Security Risk BCT SS V
Total Cryptocurrency Stolen By Victim Type Hands On Blockchain Security Risk BCT SS VThe following slide depicts the total amount of cryptocurrencies stolen. It includes elements such as centralized exchange, decentralized finance protocol, etc. Deliver an outstanding presentation on the topic using this Total Cryptocurrency Stolen By Victim Type Hands On Blockchain Security Risk BCT SS V. Dispense information and present a thorough explanation of Total Cryptocurrency, Stolen By Victim Type using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Analyzing Key Security Breaches Faced By Retail Comprehensive Retail Transformation DT SS
Analyzing Key Security Breaches Faced By Retail Comprehensive Retail Transformation DT SSThis slide analyses the key vvulnerabilities that lead to cybersecurity breaches at retailers. It includes integration of new technologies, weak segregation of duties, outdated infrastructure, outdated anti malware systems leveraging AI, etc. Deliver an outstanding presentation on the topic using this Analyzing Key Security Breaches Faced By Retail Comprehensive Retail Transformation DT SS. Dispense information and present a thorough explanation of Outdated Infrastructure, Anti Malware Systems, New Technologies using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
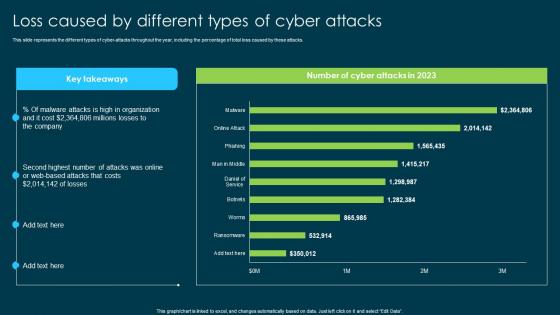 Ethical Hacking And Network Security Loss Caused By Different Types Of Cyber Attacks
Ethical Hacking And Network Security Loss Caused By Different Types Of Cyber AttacksThis slide represents the different types of cyber-attacks throughout the year, including the percentage of total loss caused by these attacks. Present the topic in a bit more detail with this Ethical Hacking And Network Security Loss Caused By Different Types Of Cyber Attacks. Use it as a tool for discussion and navigation on Cyber Attacks Throughout, Online Or Web Based Attacks, Malware Attacks. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
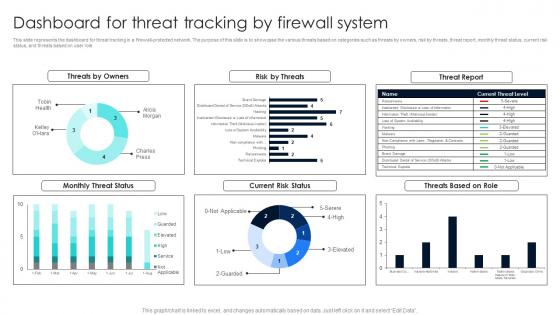 Firewall Network Security Dashboard For Threat Tracking By Firewall System
Firewall Network Security Dashboard For Threat Tracking By Firewall SystemThis slide represents the dashboard for threat tracking in a firewall-protected network. The purpose of this slide is to showcase the various threats based on categories such as threats by owners, risk by threats, threat report, monthly threat status, current risk status, and threats based on user role. Present the topic in a bit more detail with this Firewall Network Security Dashboard For Threat Tracking By Firewall System Use it as a tool for discussion and navigation on Threats By Owners, Current Risk Status, Threats Based On Role This template is free to edit as deemed fit for your organization. Therefore download it now.
-
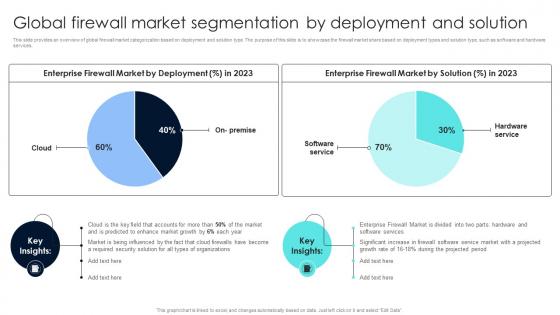 Firewall Network Security Global Firewall Market Segmentation By Deployment And Solution
Firewall Network Security Global Firewall Market Segmentation By Deployment And SolutionThis slide provides an overview of global firewall market categorization based on deployment and solution type. The purpose of this slide is to showcase the firewall market share based on deployment types and solution type, such as software and hardware services. Deliver an outstanding presentation on the topic using this Firewall Network Security Global Firewall Market Segmentation By Deployment And Solution Dispense information and present a thorough explanation of Oragnisation Size Segment Overview, Regional Analysis using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
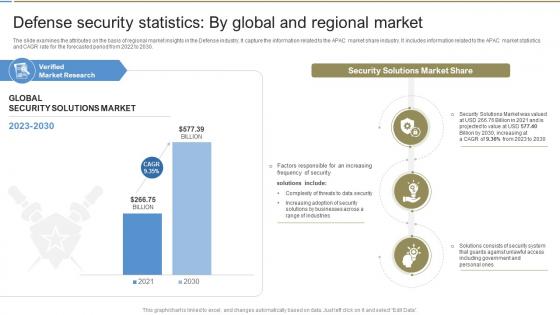 Defense Security Statistics By Global And Global Defense Industry Report IR SS
Defense Security Statistics By Global And Global Defense Industry Report IR SSThe slide examines the attributes on the basis of regional market insights in the Defense industry. It capture the information related to the APAC market share industry. It includes information related to the APAC market statistics and CAGR rate for the forecasted period from 2022 to 2030. Present the topic in a bit more detail with this Defense Security Statistics By Global And Global Defense Industry Report IR SS. Use it as a tool for discussion and navigation on Market Research, Security Solutions, Solutions Market. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
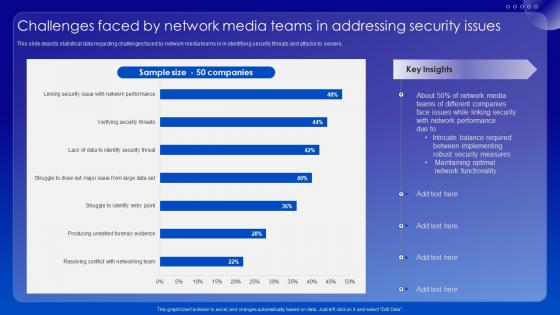 Challenges Faced By Network Media Teams In Addressing Security Issues
Challenges Faced By Network Media Teams In Addressing Security IssuesThis slide depicts statistical data regarding challenges faced by network media teams in in identifying security threats and attacks to servers. Introducing our Challenges Faced By Network Media Teams In Addressing Security Issues set of slides. The topics discussed in these slides are Network Functionality, Maintaining Optimal, Security Measures. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
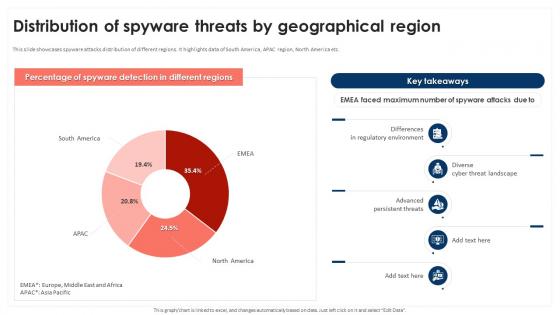 Distribution Of Spyware Threats By Geographical Region Mobile Device Security Cybersecurity SS
Distribution Of Spyware Threats By Geographical Region Mobile Device Security Cybersecurity SSThis slide showcases impact of mobile threats on organization. It highlights impact in terms of company financial loss, operational distribution, cybersecurity expenses, data breach etc. Present the topic in a bit more detail with this Distribution Of Spyware Threats By Geographical Region Mobile Device Security Cybersecurity SS Use it as a tool for discussion and navigation on Support And Maintenance, Device Troubleshooting, Access Control This template is free to edit as deemed fit for your organization. Therefore download it now.
-
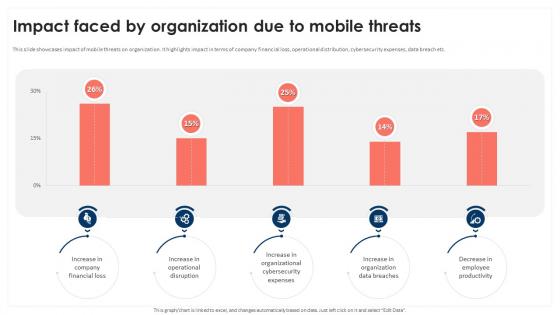 Impact Faced By Organization Due To Mobile Threats Mobile Device Security Cybersecurity SS
Impact Faced By Organization Due To Mobile Threats Mobile Device Security Cybersecurity SSThis slide showcases impact of mobile threats on organization. It highlights impact in terms of company financial loss, operational distribution, cybersecurity expenses, data breach etc. Present the topic in a bit more detail with this Impact Faced By Organization Due To Mobile Threats Mobile Device Security Cybersecurity SS Use it as a tool for discussion and navigation on Before Mobile Security, Management Plan This template is free to edit as deemed fit for your organization. Therefore download it now.
-
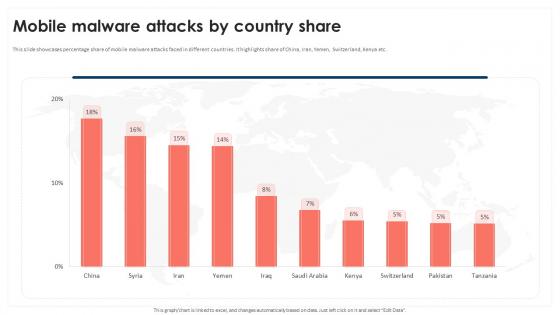 Mobile Malware Attacks By Country Share Mobile Device Security Cybersecurity SS
Mobile Malware Attacks By Country Share Mobile Device Security Cybersecurity SSThis slide showcases percentage share of mobile malware attacks faced in different countries. It highlights share of China, Iran, Yemen, Switzerland, Kenya etc. Present the topic in a bit more detail with this Mobile Malware Attacks By Country Share Mobile Device Security Cybersecurity SS Use it as a tool for discussion and navigation on Purpose, Scope, Loss And Theft This template is free to edit as deemed fit for your organization. Therefore download it now.
-
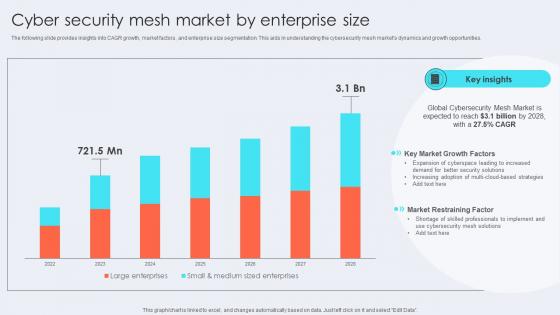 Cyber Security Mesh Market By Enterprise Size
Cyber Security Mesh Market By Enterprise SizeThe following slide provides insights into CAGR growth, market factors, and enterprise size segmentation. This aids in understanding the cybersecurity mesh markets dynamics and growth opportunities. Presenting our well structured Cyber Security Mesh Market By Enterprise Size The topics discussed in this slide are Key Market Growth Factors, Market Restraining Factor This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
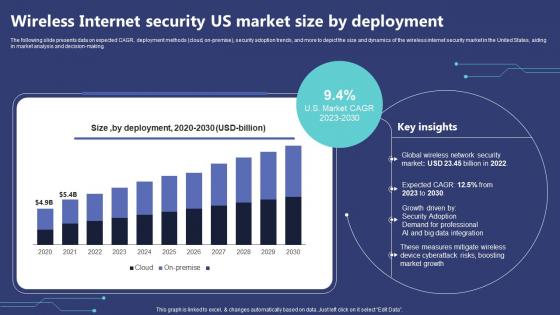 Wireless Internet Security Us Market Size By Deployment
Wireless Internet Security Us Market Size By DeploymentThe following slide presents data on expected CAGR, deployment methods cloud, on-premise, security adoption trends, and more to depict the size and dynamics of the wireless internet security market in the United States, aiding in market analysis and decision-making. Presenting our well structured Wireless Internet Security Us Market Size By Deployment. The topics discussed in this slide are Deployment, Professional, Growth. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
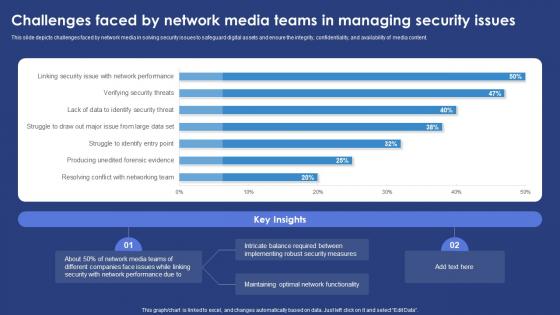 Challenges Faced By Network Media Teams In Managing Security Issues
Challenges Faced By Network Media Teams In Managing Security IssuesThis slide depicts challenges faced by network media in solving security issues to safeguard digital assets and ensure the integrity, confidentiality, and availability of media content. Introducing our Challenges Faced By Network Media Teams In Managing Security Issues set of slides. The topics discussed in these slides are Measures, Performance, Functionality. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Common Issues Addressed By Security Patch Management Process
Common Issues Addressed By Security Patch Management ProcessFollowing slide highlights common problems tackled by security patch management process. The purpose of this slide is to build an organizations overall security position and maintain the integrity of its IT and operational environment. It includes factors such as data breaches, loss of productivity, etc.Presenting our set of slides with Common Issues Addressed By Security Patch Management Process. This exhibits information on five stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Reputation Damage, Unintended System, Security Incidents.
-
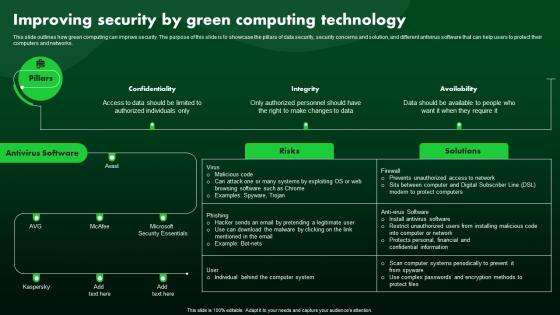 Improving Security By Green Computing Technology Green IT
Improving Security By Green Computing Technology Green ITThis slide outlines how green computing can improve security. The purpose of this slide is to showcase the pillars of data security, security concerns and solution, and different antivirus software that can help users to protect their computers and networks. Deliver an outstanding presentation on the topic using this Improving Security By Green Computing Technology Green IT. Dispense information and present a thorough explanation of Technology, Computing, Security using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
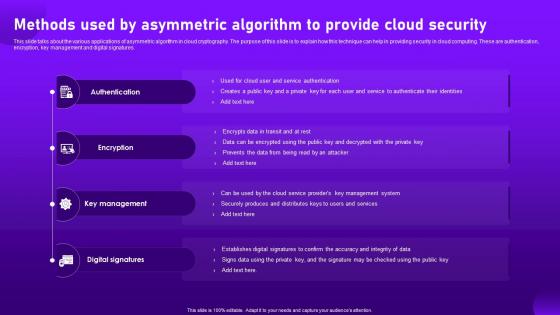 Methods Used By Asymmetric Algorithm To Provide Cloud Security Cloud Cryptography
Methods Used By Asymmetric Algorithm To Provide Cloud Security Cloud CryptographyThis slide talks about the various applications of asymmetric algorithm in cloud cryptography. The purpose of this slide is to explain how this technique can help in providing security in cloud computing. These are authentication, encryption, key management and digital signatures. Introducing Methods Used By Asymmetric Algorithm To Provide Cloud Security Cloud Cryptography to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Authentication, Key Management, Digital Signatures, using this template. Grab it now to reap its full benefits.
-
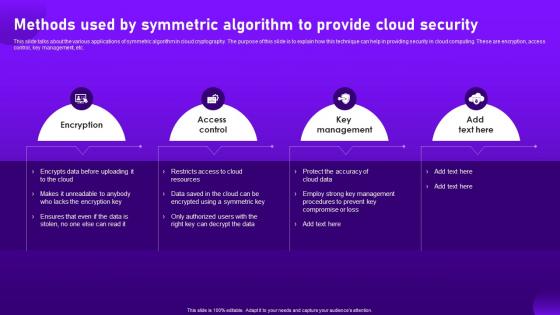 Methods Used By Symmetric Algorithm To Provide Cloud Security Cloud Cryptography
Methods Used By Symmetric Algorithm To Provide Cloud Security Cloud CryptographyThis slide talks about the various applications of symmetric algorithm in cloud cryptography. The purpose of this slide is to explain how this technique can help in providing security in cloud computing. These are encryption, access control, key management, etc. Increase audience engagement and knowledge by dispensing information using Methods Used By Symmetric Algorithm To Provide Cloud Security Cloud Cryptography. This template helps you present information on four stages. You can also present information on Encryption, Access Control, Key Management using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
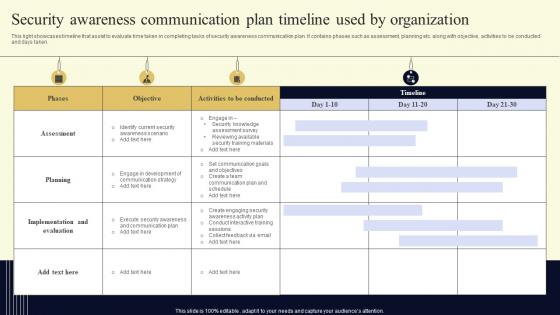 Security Awareness Communication Plan Timeline Used By Organization
Security Awareness Communication Plan Timeline Used By OrganizationThis light showcases timeline that assist to evaluate time taken in completing tasks of security awareness communication plan. It contains phases such as assessment, planning etc. along with objective, activities to be conducted and days taken. Presenting our well structured Security Awareness Communication Plan Timeline Used By Organization. The topics discussed in this slide are Security, Communication, Organization. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Data Breach Prevention Data Breach Prevention Services Provided By Security Tools
Data Breach Prevention Data Breach Prevention Services Provided By Security ToolsThis slide represents the multiple layers of protection provided by security solution providers against data breaches. These include database firewalls, data masking and encryption, Data Loss Prevention DLP, user behavior analytics, alert prioritization, etc. Present the topic in a bit more detail with this Data Breach Prevention Data Breach Prevention Services Provided By Security Tools. Use it as a tool for discussion and navigation on Data Breach Prevention, Services Provided By Security Tools, Obfuscates Sensitive Data. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Competitive Pricing Plan Offered By STO Marketing Agency Security Token Offerings BCT SS
Competitive Pricing Plan Offered By STO Marketing Agency Security Token Offerings BCT SSThe following slide showcases sample pricing plan of security token offering marketing services. It includes elements such as community promotion, ICI listing, airdrop program, support services, basic, advanced, premium, etc. Present the topic in a bit more detail with this Competitive Pricing Plan Offered By STO Marketing Agency Security Token Offerings BCT SS. Use it as a tool for discussion and navigation on Community Marketing, Advanced, Airdrop Program, Marketing Services. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Estimated STO Project Cost By Category Security Token Offerings BCT SS
Estimated STO Project Cost By Category Security Token Offerings BCT SSThe following slide provides brief overview of initial coin offering budget estimation by category. It includes elements such as white paper development, website, security audit, exchange listing, legal charges, marketing, etc. Present the topic in a bit more detail with this Estimated STO Project Cost By Category Security Token Offerings BCT SS. Use it as a tool for discussion and navigation on Activities, Exchange Listing, Blockchain Dev, Marketing. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Key Services Offered By STO Marketing Agency Security Token Offerings BCT SS
Key Services Offered By STO Marketing Agency Security Token Offerings BCT SSThe following slide illustrates various services offered by security token offering STO marketing agency to. It includes elements such as legal offerings, website development, listing on exchange, marketing, technical support, etc. Present the topic in a bit more detail with this Key Services Offered By STO Marketing Agency Security Token Offerings BCT SS. Use it as a tool for discussion and navigation on Legal Services, Website Development, Marketing, Technical Support. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
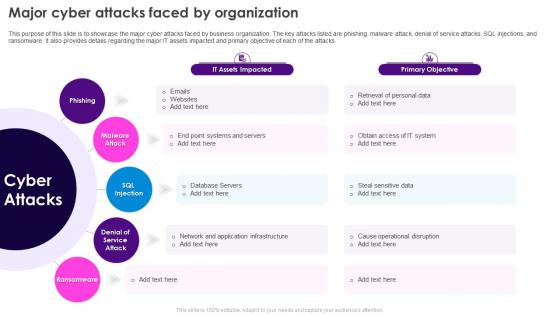 Security Plan To Prevent Cyber Major Cyber Attacks Faced By Organization
Security Plan To Prevent Cyber Major Cyber Attacks Faced By OrganizationThis purpose of this slide is to showcase the major cyber attacks faced by business organization. The key attacks listed are phishing, malware attack, denial of service attacks, SQL injections, and ransomware. It also provides details regarding the major IT assets impacted and primary objective of each of the attacks. Introducing Security Plan To Prevent Cyber Major Cyber Attacks Faced By Organization to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Network And Application Infrastructure, Database Servers, Cause Operational Disruption, using this template. Grab it now to reap its full benefits.
-
 Various Cyber Security Incidents Detected By Technology Deployment Plan To Improve Organizations
Various Cyber Security Incidents Detected By Technology Deployment Plan To Improve OrganizationsThis slide represents the detection of certain attacks which affected the systems and networks of the organization by the IT department of the organization. It includes detection of cyber security incidents such as insider threat, phishing attack, malware attack etc. Introducing Various Cyber Security Incidents Detected By Technology Deployment Plan To Improve Organizations to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Phishing, Malware, Application, using this template. Grab it now to reap its full benefits.
-
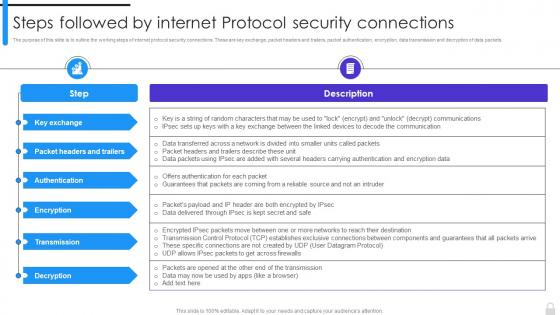 Encryption Implementation Strategies Steps Followed By Internet Protocol Security Connections
Encryption Implementation Strategies Steps Followed By Internet Protocol Security ConnectionsThe purpose of this slide is to outline the working steps of internet protocol security connections. These are key exchange, packet headers and trailers, packet authentication, encryption, data transmission and decryption of data packets. Present the topic in a bit more detail with this Encryption Implementation Strategies Steps Followed By Internet Protocol Security Connections. Use it as a tool for discussion and navigation on Protocol Security Connections, Packet Authentication, Encryption, Data Transmission, Decryption Of Data Packets. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
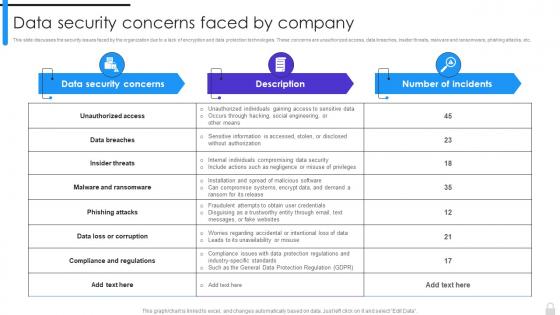 Encryption Implementation Strategies Data Security Concerns Faced By Company
Encryption Implementation Strategies Data Security Concerns Faced By CompanyThis slide discusses the security issues faced by the organization due to a lack of encryption and data protection technologies. These concerns are unauthorized access, data breaches, insider threats, malware and ransomware, phishing attacks, etc. Deliver an outstanding presentation on the topic using this Encryption Implementation Strategies Data Security Concerns Faced By Company. Dispense information and present a thorough explanation of Data Security Concerns, Phishing Attacks, Data Protection Technologies, Compliance And Regulations using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
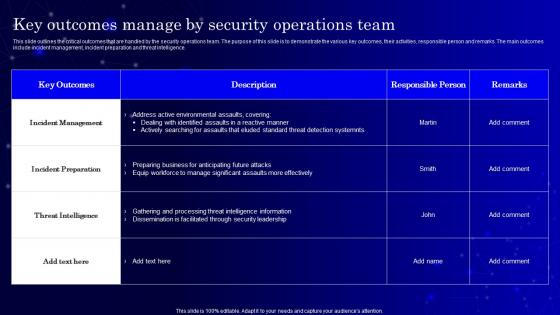 Secops V2 Key Outcomes Manage By Security Operations Team
Secops V2 Key Outcomes Manage By Security Operations TeamThis slide outlines the critical outcomes that are handled by the security operations team. The purpose of this slide is to demonstrate the various key outcomes, their activities, responsible person and remarks. The main outcomes include incident management, incident preparation and threat intelligence. Deliver an outstanding presentation on the topic using this Secops V2 Key Outcomes Manage By Security Operations Team. Dispense information and present a thorough explanation of Incident Management, Incident Preparation, Threat Intelligence, Security Leadership using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
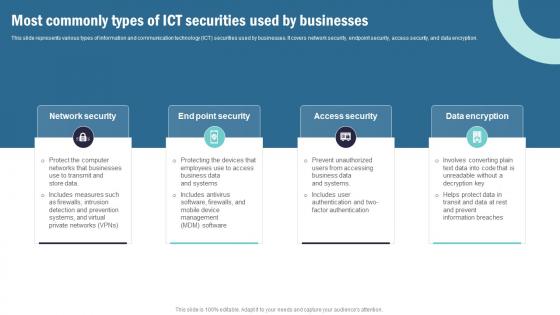 Strategic Plan To Implement Most Commonly Types Of Ict Securities Used By Businesses Strategy SS V
Strategic Plan To Implement Most Commonly Types Of Ict Securities Used By Businesses Strategy SS VThis slide represents various types of information and communication technology ICT securities used by businesses. It covers network security, endpoint security, access security, and data encryption. Introducing Strategic Plan To Implement Most Commonly Types Of Ict Securities Used By Businesses Strategy SS V to increase your presentation threshold. Encompassed with Four stages, this template is a great option to educate and entice your audience. Dispence information on IT Governance, Visualization, Resource Management using this template. Grab it now to reap its full benefits.
-
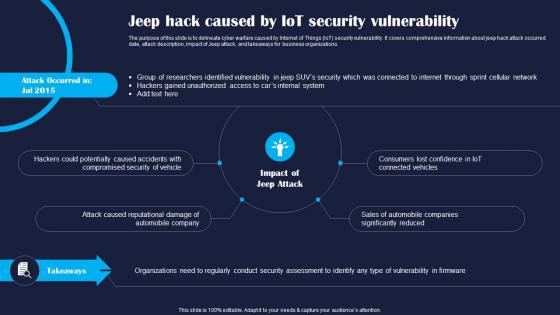 Jeep Hack Caused By IoT Security Improving IoT Device Cybersecurity IoT SS
Jeep Hack Caused By IoT Security Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to delineate cyber warfare caused by Internet of Things IoT security vulnerability. It covers comprehensive information about jeep hack attack occurred date, attack description, impact of Jeep attack, and takeaways for business organizations. Introducing Jeep Hack Caused By IoT Security Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Potentially, Security, Company, using this template. Grab it now to reap its full benefits.
-
 Stuxnet Attack Caused By IoT Security Improving IoT Device Cybersecurity IoT SS
Stuxnet Attack Caused By IoT Security Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to highlight overview of Stuxnet attack caused by Internet of Things IoT security vulnerability. The slide covers information about attack occurred date, its overview, impact of Stuxnet attack, and key takeaways for companies. Introducing Stuxnet Attack Caused By IoT Security Improving IoT Device Cybersecurity IoT SS to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Efficiency, Reduction, Damage, using this template. Grab it now to reap its full benefits.
-
 Verkada Hack Caused By IoT Security Improving IoT Device Cybersecurity IoT SS
Verkada Hack Caused By IoT Security Improving IoT Device Cybersecurity IoT SSThe purpose of this slide is to exhibit illustration of cyber beach caused by Internet of Things IoT security vulnerability. Information covered in this slide is related to attack launch date, attack description, impact of Verkada cyber attack, and key takeaways for business leaders. Increase audience engagement and knowledge by dispensing information using Verkada Hack Caused By IoT Security Improving IoT Device Cybersecurity IoT SS. This template helps you present information on four stages. You can also present information on Breach, Reputational, Consequences using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.


