Powerpoint Templates and Google slides for BYOD Security Check
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
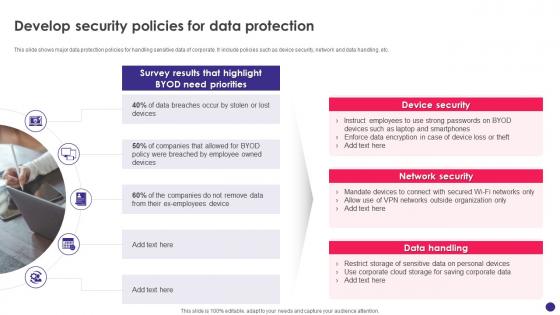 Implementing Byod Policy To Enhance Develop Security Policies For Data Protection
Implementing Byod Policy To Enhance Develop Security Policies For Data ProtectionThis slide shows major data protection policies for handling sensitive data of corporate. It include policies such as device security, network and data handling, etc. Introducing Implementing Byod Policy To Enhance Develop Security Policies For Data Protection to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Network Security, Data Handling, Device Security, Data Protection, using this template. Grab it now to reap its full benefits.
-
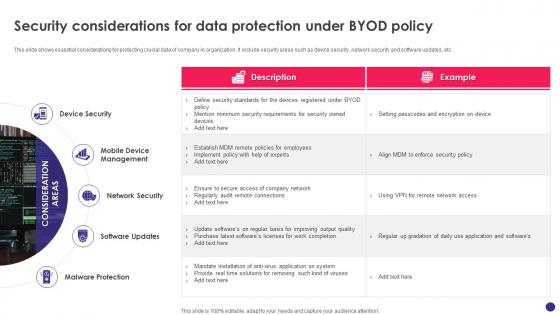 Implementing Byod Policy To Enhance Security Considerations For Data Protection Under Byod Policy
Implementing Byod Policy To Enhance Security Considerations For Data Protection Under Byod PolicyThis slide shows essential considerations for protecting crucial data of company in organization. It include security areas such as device security, network security and software updates, etc. Increase audience engagement and knowledge by dispensing information using Implementing Byod Policy To Enhance Security Considerations For Data Protection Under Byod Policy. This template helps you present information on five stages. You can also present information on Device Security, Mobile Device Management, Network Security, Malware Protection using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Policy Bring Your Own Device Byod Policy Objective And Scope
Cyber Security Policy Bring Your Own Device Byod Policy Objective And ScopeThis slide represents the bring your own device policy, including its objective and scope. It also includes the types of devices used in BYOD policy, which comprises cellphones, smartphones, tablets, laptops, and PCs. Present the topic in a bit more detail with this Cyber Security Policy Bring Your Own Device Byod Policy Objective And Scope. Use it as a tool for discussion and navigation on Technological, Compatibility, Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Policy Byod Lost Stolen Hacked Or Damaged Equipment
Cyber Security Policy Byod Lost Stolen Hacked Or Damaged EquipmentThis slide describes the scenarios of lost, stolen, hacked, or damaged personal equipment under BYOD policy. It also includes that remote wipe software should be installed on employees devices to remove the work data remotely in case of theft. Introducing Cyber Security Policy Byod Lost Stolen Hacked Or Damaged Equipment to increase your presentation threshold. Encompassed with seven stages, this template is a great option to educate and entice your audience. Dispence information on Equipment, Information, Department, using this template. Grab it now to reap its full benefits.
-
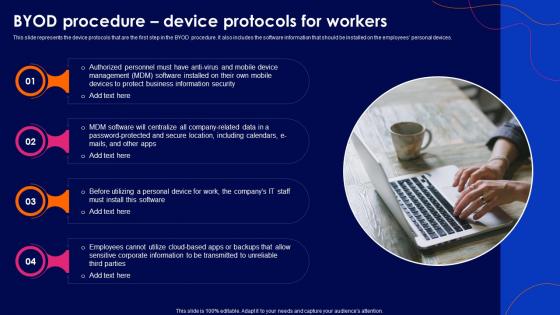 Cyber Security Policy Byod Procedure Device Protocols For Workers
Cyber Security Policy Byod Procedure Device Protocols For WorkersThis slide represents the device protocols that are the first step in the BYOD procedure. It also includes the software information that should be installed on the employees personal devices. Increase audience engagement and knowledge by dispensing information using Cyber Security Policy Byod Procedure Device Protocols For Workers. This template helps you present information on four stages. You can also present information on Software, Business, Information using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Policy Byod Restrictions On Authorized Use Personal Devices
Cyber Security Policy Byod Restrictions On Authorized Use Personal DevicesThis slide covers the restrictions on the authorized use of personal devices in corporate buildings or property. It also includes that employees should inform their friends and family about the policy to avoid personal concerns at work. Introducing Cyber Security Policy Byod Restrictions On Authorized Use Personal Devices to increase your presentation threshold. Encompassed with six stages, this template is a great option to educate and entice your audience. Dispence information on Discrimination, Business, Equipment, using this template. Grab it now to reap its full benefits.
-
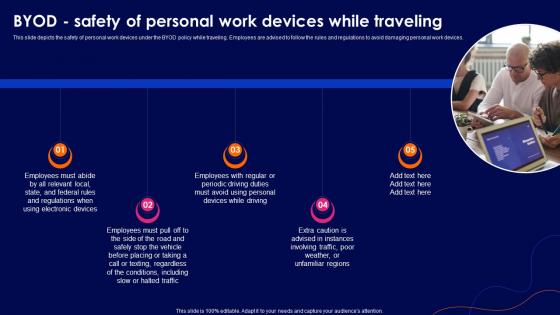 Cyber Security Policy Byod Safety Of Personal Work Devices While Traveling
Cyber Security Policy Byod Safety Of Personal Work Devices While TravelingThis slide depicts the safety of personal work devices under the BYOD policy while traveling. Employees are advised to follow the rules and regulations to avoid damaging personal work devices. Increase audience engagement and knowledge by dispensing information using Cyber Security Policy Byod Safety Of Personal Work Devices While Traveling. This template helps you present information on five stages. You can also present information on Conditions, Regulations, Electronic using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Policy Termination Of Employment And Violation Of Byod Policy
Cyber Security Policy Termination Of Employment And Violation Of Byod PolicyThis slide talks about the termination of employment and violation of BYOD policy. Both include the actions to be performed if any employee leaves or violates the BYOD policy. Introducing Cyber Security Policy Termination Of Employment And Violation Of Byod Policy to increase your presentation threshold. Encompassed with two stages, this template is a great option to educate and entice your audience. Dispence information on Employment, Termination, Business, using this template. Grab it now to reap its full benefits.
-
 BYOD Security Check In Organizations Icon
BYOD Security Check In Organizations IconPresenting our set of slides with BYOD Security Check In Organizations Icon. This exhibits information on three stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on BYOD Security Check, Organizations Icon.
-
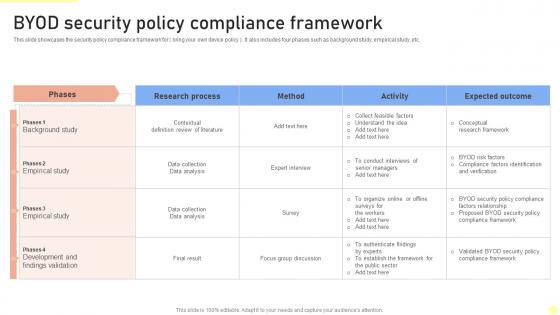 BYOD Security Policy Compliance Framework
BYOD Security Policy Compliance FrameworkThis slide showcases the security policy compliance framework for bring your own device policy. It also includes four phases such as background study, empirical study, etc. Introducing our BYOD Security Policy Compliance Framework set of slides. The topics discussed in these slides are Research Process, Background Study, Method. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
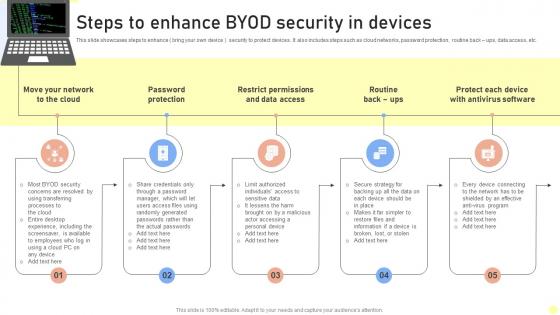 Steps To Enhance BYOD Security In Devices
Steps To Enhance BYOD Security In DevicesThis slide showcases steps to enhance bring your own device security to protect devices. It also includes steps such as cloud networks, password protection, routine back ups, data access, etc. Introducing our premium set of slides with Steps To Enhance BYOD Security In Devices. Ellicudate the five stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Network, Password Protection, Data Access. So download instantly and tailor it with your information.
-
 Factors Of Successful Byod Phone Security Policy
Factors Of Successful Byod Phone Security PolicyThis slide show factors for creating an effective BYOD security policy for phone. The purpose of this slide is to highlight all important factors for framing BYOD policy at workplace. It include factors such as be specific, follow strict policy, etc. Presenting our set of slides with Factors Of Successful Byod Phone Security Policy. This exhibits information on four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on Be Specific, Follow Strict Security.
-
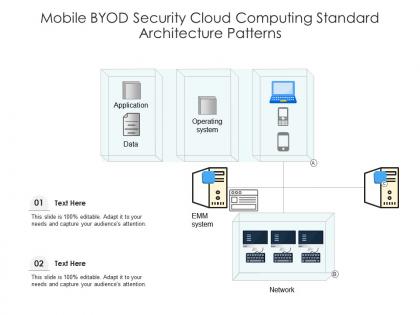 Mobile byod security cloud computing standard architecture patterns ppt presentation diagram
Mobile byod security cloud computing standard architecture patterns ppt presentation diagramUtilize this visually appealing slide titled Mobile BYOD Security Cloud Computing Standard Architecture Patterns Ppt Presentation Diagram. Elucidate the concept of cloud computing patterns using this editable PowerPoint presentation. Explain Operating System, Network, Data using this PPT theme. Instantly grab the attention of your audience by downloading this professionally designed PPT template.

