Powerpoint Templates and Google slides for Cyber Attacks Identification
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
 Reduce Risk Cyber Attack In Powerpoint And Google Slides Cpb
Reduce Risk Cyber Attack In Powerpoint And Google Slides CpbPresenting Reduce Risk Cyber Attack In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Reduce Risk Cyber Attack. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Malware Top Cyber Security Attacks In Powerpoint And Google Slides Cpb
Malware Top Cyber Security Attacks In Powerpoint And Google Slides CpbPresenting our Malware Top Cyber Security Attacks In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases two stages. It is useful to share insightful information on Malware Top Cyber Security Attacks This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Impact Cyber Attacks Critical Infrastructure In Powerpoint And Google Slides Cpb
Impact Cyber Attacks Critical Infrastructure In Powerpoint And Google Slides CpbPresenting Impact Cyber Attacks Critical Infrastructure In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase two stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Impact Cyber Attacks Critical Infrastructure This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Increase Cyber Attacks In Powerpoint And Google Slides Cpb
Increase Cyber Attacks In Powerpoint And Google Slides CpbPresenting our Increase Cyber Attacks In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Increase Cyber Attacks This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cyber Attacks In Powerpoint And Google Slides Cpb
Cyber Attacks In Powerpoint And Google Slides CpbPresenting Cyber Attacks In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase six stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cyber Attacks. This well structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Cyber Attack Recovery Plan In Powerpoint And Google Slides Cpb
Cyber Attack Recovery Plan In Powerpoint And Google Slides CpbPresenting Cyber Attack Recovery Plan In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Cyber Attack Recovery Plan. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Protect Cyber Attack In Powerpoint And Google Slides Cpb
Protect Cyber Attack In Powerpoint And Google Slides CpbPresenting our Protect Cyber Attack In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Protect Cyber Attack. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Business Cyber Attacks In Powerpoint And Google Slides Cpb
Business Cyber Attacks In Powerpoint And Google Slides CpbPresenting our Business Cyber Attacks In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Business Cyber Attacks. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Protect Against Cyber Attacks In Powerpoint And Google Slides Cpb
Protect Against Cyber Attacks In Powerpoint And Google Slides CpbPresenting our Protect Against Cyber Attacks In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases Three stages. It is useful to share insightful information on Protect Against Cyber Attacks This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Mitigation Cyber Attacks In Powerpoint And Google Slides Cpb
Mitigation Cyber Attacks In Powerpoint And Google Slides CpbPresenting our Mitigation Cyber Attacks In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Mitigation Cyber Attacks This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Agenda For Strategy To Minimize Cyber Attacks Risks Ppt Icon Clipart Images
Agenda For Strategy To Minimize Cyber Attacks Risks Ppt Icon Clipart ImagesIntroducing Agenda For Strategy To Minimize Cyber Attacks Risks Ppt Icon Clipart Images to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Risk Assessment, Cyber Attacks Risks, Attacks Frequency, Cybersecurity Risk, using this template. Grab it now to reap its full benefits.
-
 Icons Slide For Strategy To Minimize Cyber Attacks Risks Ppt Icon Templates
Icons Slide For Strategy To Minimize Cyber Attacks Risks Ppt Icon TemplatesPresenting our premium Icons Slide For Strategy To Minimize Cyber Attacks Risks Ppt Icon Templates set of slides with flexible icons. The icons are designed by our group of professionals. Add these Icons Slide For Strategy To Minimize Cyber Attacks Risks Ppt Icon Templates to your presentation to make it visually appealing. Also, edit them according to your requirement. Download it and captive your audience.
-
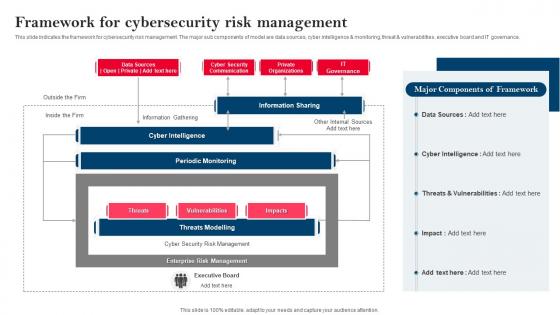 Strategy To Minimize Cyber Attacks Framework For Cybersecurity Risk Management
Strategy To Minimize Cyber Attacks Framework For Cybersecurity Risk ManagementThis slide indicates the framework for cybersecurity risk management. The major sub components of model are data sources, cyber intelligence and monitoring, threat and vulnerabilities, executive board and IT governance. Present the topic in a bit more detail with this Strategy To Minimize Cyber Attacks Framework For Cybersecurity Risk Management. Use it as a tool for discussion and navigation on Information Sharing, Components Of Framework, Framework For Cybersecurity, Risk Management. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
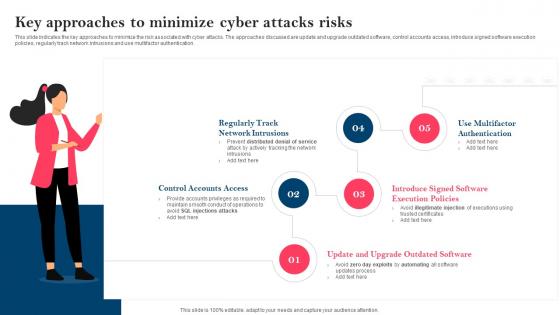 Strategy To Minimize Cyber Attacks Key Approaches To Minimize Cyber Attacks Risks
Strategy To Minimize Cyber Attacks Key Approaches To Minimize Cyber Attacks RisksThis slide indicates the key approaches to minimize the risk associated with cyber attacks. The approaches discussed are update and upgrade outdated software, control accounts access, introduce signed software execution policies, regularly track network intrusions and use multifactor authentication. Increase audience engagement and knowledge by dispensing information using Strategy To Minimize Cyber Attacks Key Approaches To Minimize Cyber Attacks Risks. This template helps you present information on five stages. You can also present information on Control Accounts Access, Software Execution Policies, Multifactor Authentication, Regularly Track Network Intrusions using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Strategy To Minimize Cyber Attacks Major Cyber Attacks Faced By Organization
Strategy To Minimize Cyber Attacks Major Cyber Attacks Faced By OrganizationThis purpose of this slide is to showcase the major cyber attacks faced by business organization. The key attacks listed are phishing, malware attack, denial of service attacks, SQL injections, and ransomware. It also provides details regarding the major IT assets impacted and primary objective of each of the attacks. Deliver an outstanding presentation on the topic using this Strategy To Minimize Cyber Attacks Major Cyber Attacks Faced By Organization. Dispense information and present a thorough explanation of Malware Attack, Denial Of Service Attack, Ransomware, Major Cyber Attacks using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
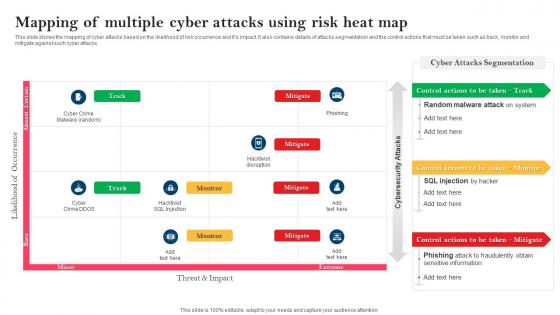 Strategy To Minimize Cyber Attacks Mapping Of Multiple Cyber Attacks Using Risk Heat Map
Strategy To Minimize Cyber Attacks Mapping Of Multiple Cyber Attacks Using Risk Heat MapThis slide shows the mapping of cyber attacks based on the likelihood of risk occurrence and its impact. It also contains details of attacks segmentation and the control actions that must be taken such as track, monitor and mitigate against such cyber attacks. Present the topic in a bit more detail with this Strategy To Minimize Cyber Attacks Mapping Of Multiple Cyber Attacks Using Risk Heat Map. Use it as a tool for discussion and navigation on Random Malware Attack, Phishing Attack, Fraudulently Obtain, Sensitive Information. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
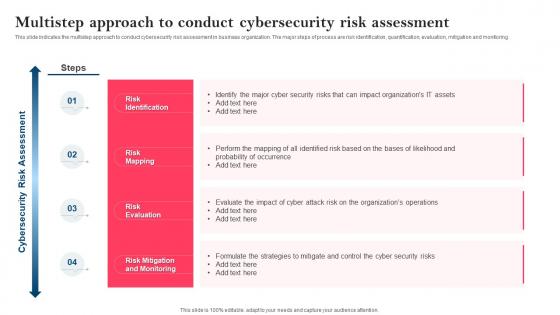 Strategy To Minimize Cyber Attacks Multistep Approach To Conduct Cybersecurity Risk Assessment
Strategy To Minimize Cyber Attacks Multistep Approach To Conduct Cybersecurity Risk AssessmentThis slide indicates the multistep approach to conduct cybersecurity risk assessment in business organization. The major steps of process are risk identification, quantification, evaluation, mitigation and monitoring. Introducing Strategy To Minimize Cyber Attacks Multistep Approach To Conduct Cybersecurity Risk Assessment to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Risk Identification, Risk Mapping, Risk Evaluation, Risk Mitigation And Monitoring, using this template. Grab it now to reap its full benefits.
-
 Strategy To Minimize Cyber Attacks Need Of Cybersecurity Program For Organization
Strategy To Minimize Cyber Attacks Need Of Cybersecurity Program For OrganizationThis slide depicts the value that a cybersecurity program with risk assessment module add to organization in terms of increased awareness of organization security landscape, identification of system vulnerabilities, actionable and prioritized list of cybersecurity risks and mitigation plan to tackle future threats. Increase audience engagement and knowledge by dispensing information using Strategy To Minimize Cyber Attacks Need Of Cybersecurity Program For Organization. This template helps you present information on four stages. You can also present information on Organization Security Landscape, Actionable And Prioritized, List Of Cybersecurity Risks, Identification Of System Vulnerabilities using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
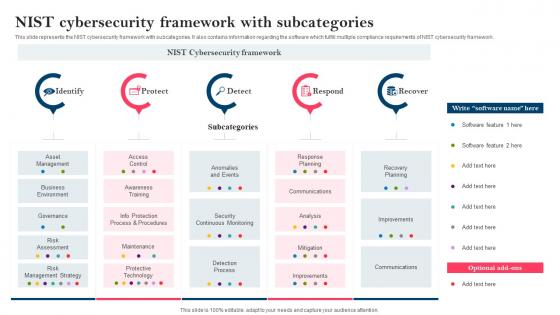 Strategy To Minimize Cyber Attacks NIST Cybersecurity Framework With Subcategories
Strategy To Minimize Cyber Attacks NIST Cybersecurity Framework With SubcategoriesThis slide represents the NIST cybersecurity framework with subcategories. It also contains information regarding the software which fulfill multiple compliance requirements of NIST cybersecurity framework. Introducing Strategy To Minimize Cyber Attacks NIST Cybersecurity Framework With Subcategories to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on NIST Cybersecurity, Framework With Subcategories, Contains Information, Compliance Requirements, using this template. Grab it now to reap its full benefits.
-
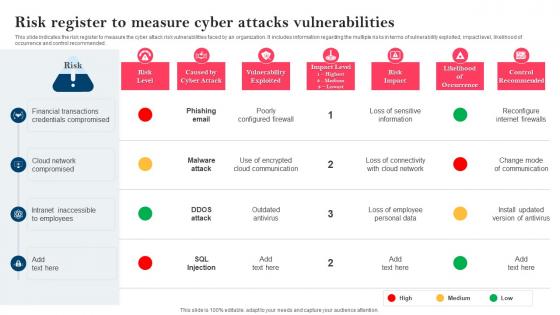 Strategy To Minimize Cyber Attacks Risk Register To Measure Cyber Attacks Vulnerabilities
Strategy To Minimize Cyber Attacks Risk Register To Measure Cyber Attacks VulnerabilitiesThis slide indicates the risk register to measure the cyber attack risk vulnerabilities faced by an organization. It includes information regarding the multiple risks in terms of vulnerability exploited, impact level, likelihood of occurrence and control recommended. Deliver an outstanding presentation on the topic using this Strategy To Minimize Cyber Attacks Risk Register To Measure Cyber Attacks Vulnerabilities. Dispense information and present a thorough explanation of Financial Transactions, Credentials Compromised, Cloud Network Compromised using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
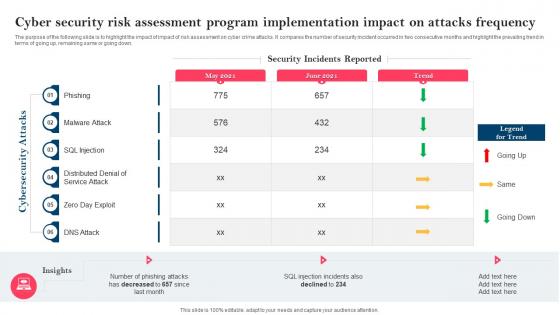 Strategy To Minimize Cyber Attacks Risks Cyber Security Risk Assessment Program Implementation
Strategy To Minimize Cyber Attacks Risks Cyber Security Risk Assessment Program ImplementationThe purpose of the following slide is to highlight the impact of impact of risk assessment on cyber crime attacks. It compares the number of security incident occurred in two consecutive months and highlight the prevailing trend in terms of going up, remaining same or going down. Present the topic in a bit more detail with this Strategy To Minimize Cyber Attacks Risks Cyber Security Risk Assessment Program Implementation. Use it as a tool for discussion and navigation on Cyber Security, Risk Assessment, Program Implementation, Impact On Attacks Frequency. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Strategy To Minimize Cyber Attacks Risks For Table Of Content Ppt Icon Elements
Strategy To Minimize Cyber Attacks Risks For Table Of Content Ppt Icon ElementsIncrease audience engagement and knowledge by dispensing information using Strategy To Minimize Cyber Attacks Risks For Table Of Content Ppt Icon Elements. This template helps you present information on one stages. You can also present information on Cyber Attacks Risks, Cyber Attacks Risk Mitigation, Mitigation Plan using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
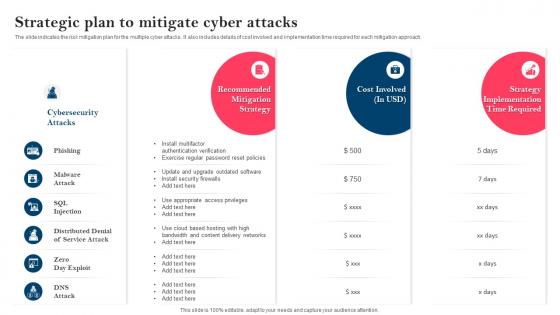 Strategy To Minimize Cyber Attacks Strategic Plan To Mitigate Cyber Attacks
Strategy To Minimize Cyber Attacks Strategic Plan To Mitigate Cyber AttacksThe slide indicates the risk mitigation plan for the multiple cyber attacks. It also includes details of cost involved and implementation time required for each mitigation approach. Deliver an outstanding presentation on the topic using this Strategy To Minimize Cyber Attacks Strategic Plan To Mitigate Cyber Attacks. Dispense information and present a thorough explanation of Phishing Cybersecurity Attacks, Strategic Plan, Mitigate Cyber Attacks, Denial Of Service Attack using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Table Of Contents For Strategy To Minimize Cyber Attacks Risks
Table Of Contents For Strategy To Minimize Cyber Attacks RisksIntroducing Table Of Contents For Strategy To Minimize Cyber Attacks Risks to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Cyber Attacks Faced By Organization, Risk Heatmap, Risk Register, Mitigation Plan, Cybersecurity Risk Assessment Program, using this template. Grab it now to reap its full benefits.
-
 Reduce Cyber Security Internet Attacks Colored Icon In Powerpoint Pptx Png And Editable Eps Format
Reduce Cyber Security Internet Attacks Colored Icon In Powerpoint Pptx Png And Editable Eps FormatThis colourful PowerPoint icon is the perfect visual representation of reducing internet attacks. It features a shield with a green checkmark, showing that security is in place and that the user is protected. It is a great way to show the importance of online security in a visually appealing way.
-
 Reduce Cyber Security Internet Attacks Monotone Icon In Powerpoint Pptx Png And Editable Eps Format
Reduce Cyber Security Internet Attacks Monotone Icon In Powerpoint Pptx Png And Editable Eps FormatThis Monotone PowerPoint icon is the perfect visual aid to help reduce Internet attacks. It features a shield with a check mark, representing the protection of data and networks from malicious cyber threats. It is a simple yet powerful way to communicate the importance of cybersecurity.
-
 Cyber Attacks Increasing In Powerpoint And Google Slides Cpb
Cyber Attacks Increasing In Powerpoint And Google Slides CpbPresenting our Cyber Attacks Increasing In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases four stages. It is useful to share insightful information on Cyber Attacks Increasing. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Cyber Attack Companies In Powerpoint And Google Slides Cpb
Cyber Attack Companies In Powerpoint And Google Slides CpbPresenting our Cyber Attack Companies In Powerpoint And Google Slides Cpb PowerPoint template design. This PowerPoint slide showcases six stages. It is useful to share insightful information on Cyber Attack Companies This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Different Types Of Smishing Cyber Scams Phishing Attacks And Strategies
Different Types Of Smishing Cyber Scams Phishing Attacks And StrategiesThis slide talks about the various types of smishing cyber attacks. The purpose of this slide is to briefly explain different techniques of smishing scams used by the attackers to scam users. These are covid 19 smishing, financial services smishing, etc.Increase audience engagement and knowledge by dispensing information using Different Types Of Smishing Cyber Scams Phishing Attacks And Strategies. This template helps you present information on five stages. You can also present information on Confirmation Smishing, Services Smishing, Smishing Scams using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Different Types Of Vishing Cyber Attacks Phishing Attacks And Strategies
Different Types Of Vishing Cyber Attacks Phishing Attacks And StrategiesThis slide talks about the various types of vishing cyber attacks. The purpose of this slide is to briefly explain different techniques of vishing scams used by the attackers to scam users. These are caller ID spoofing, dumpster diving, wardialing, etc.Introducing Different Types Of Vishing Cyber Attacks Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Protocol Transmission, Achieved Automatically, Phishing Attack Victims, using this template. Grab it now to reap its full benefits.
-
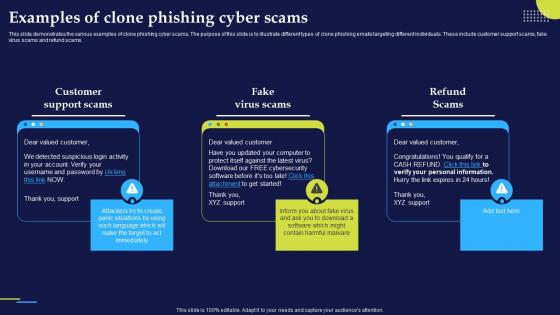 Examples Of Clone Phishing Cyber Scams Phishing Attacks And Strategies
Examples Of Clone Phishing Cyber Scams Phishing Attacks And StrategiesThis slide demonstrates the various examples of clone phishing cyber scams. The purpose of this slide is to illustrate different types of clone phishing emails targeting different individuals. These include customer support scams, fake virus scams and refund scams.Increase audience engagement and knowledge by dispensing information using Examples Of Clone Phishing Cyber Scams Phishing Attacks And Strategies. This template helps you present information on three stages. You can also present information on Detected Suspicious, Support Scams, Virus Scams using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
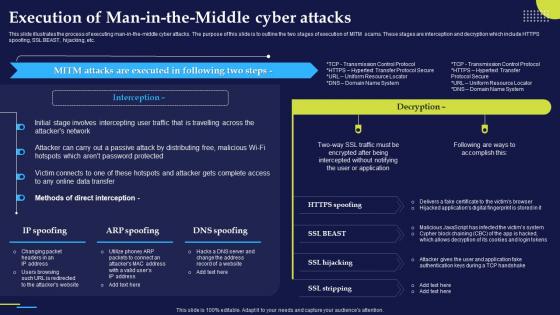 Execution Of Man In The Middle Cyber S Phishing Attacks And Strategies
Execution Of Man In The Middle Cyber S Phishing Attacks And StrategiesThis slide illustrates the process of executing man in the middle cyber attacks. The purpose of this slide is to outline the two stages of execution of MITM scams. These stages are interception and decryption which include HTTPS spoofing, SSL BEAST, hijacking, etc.Deliver an outstanding presentation on the topic using this Execution Of Man In The Middle Cyber S Phishing Attacks And Strategies. Dispense information and present a thorough explanation of Data Transfer, Direct Interception, Password Protected using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
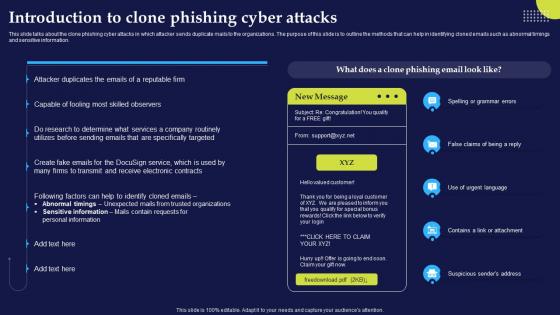 Introduction To Clone Phishing Cyber Attacks Phishing Attacks And Strategies
Introduction To Clone Phishing Cyber Attacks Phishing Attacks And StrategiesThis slide talks about the clone phishing cyber attacks in which attacker sends duplicate mails to the organizations. The purpose of this slide is to outline the methods that can help in identifying cloned emails such as abnormal timings and sensitive information.Present the topic in a bit more detail with this Introduction To Clone Phishing Cyber Attacks Phishing Attacks And Strategies. Use it as a tool for discussion and navigation on Personal Information, Sensitive Information, Abnormal Timings Unexpected. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
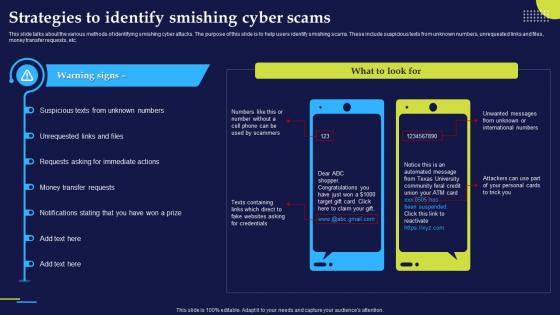 Strategies To Identify Smishing Cyber Scams Phishing Attacks And Strategies
Strategies To Identify Smishing Cyber Scams Phishing Attacks And StrategiesThis slide talks about the various methods of identifying smishing cyber attacks. The purpose of this slide is to help users identify smishing scams. These include suspicious texts from unknown numbers, unrequested links and files, money transfer requests, etc.Present the topic in a bit more detail with this Strategies To Identify Smishing Cyber Scams Phishing Attacks And Strategies. Use it as a tool for discussion and navigation on Requests Asking, Transfer Requests, Notifications Stating. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Working Process Of Cyber Phishing Attacks Phishing Attacks And Strategies
Working Process Of Cyber Phishing Attacks Phishing Attacks And StrategiesThis slide talks about the implementation and working of phishing attacks. The purpose of this slide is to explain how are cyber phishing scams conducted. The components include hacker, phishing mail, target, phishing website and original website.Introducing Working Process Of Cyber Phishing Attacks Phishing Attacks And Strategies to increase your presentation threshold. Encompassed with five stages, this template is a great option to educate and entice your audience. Dispence information on Information Website, Hacker Access Private, Credentials Victim, using this template. Grab it now to reap its full benefits.
-
 International Cyber Attacks In Powerpoint And Google Slides Cpb
International Cyber Attacks In Powerpoint And Google Slides CpbPresenting International Cyber Attacks In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase Three stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like International Cyber Attacks. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
 Cyber Attacks Banking Industry In Powerpoint And Google Slides Cpb
Cyber Attacks Banking Industry In Powerpoint And Google Slides CpbPresenting our Cyber Attacks Banking Industry In Powerpoint And Google Slides Cpb. PowerPoint template design. This PowerPoint slide showcases three stages. It is useful to share insightful information on Cyber Attacks Banking Industry. This PPT slide can be easily accessed in standard screen and widescreen aspect ratios. It is also available in various formats like PDF, PNG, and JPG. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your wish. Our PPT layout is compatible with Google Slides as well, so download and edit it as per your knowledge.
-
 Adopt Cyber Security Data Policies Cyber Attack Risks Mitigation
Adopt Cyber Security Data Policies Cyber Attack Risks MitigationThe following slide highlights various cyber security policies to manage data control and breach. It includes elements such as network security, data, workstations, remote access etc. Introducing Adopt Cyber Security Data Policies Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Network Security Policies, Data Security Policies, Workstation Policies, using this template. Grab it now to reap its full benefits.
-
 Adopting Strategies By Cyber Attack Type Cyber Attack Risks Mitigation
Adopting Strategies By Cyber Attack Type Cyber Attack Risks MitigationThe following slide depicts the various strategies to manage data control and breach. It includes elements such as attrition, malware, hacking, social tactic, improper usage, train and educate employees, automate identification, data management etc. Present the topic in a bit more detail with this Adopting Strategies By Cyber Attack Type Cyber Attack Risks Mitigation. Use it as a tool for discussion and navigation on Educate Employees, Data Management, Automate Attack Identification. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
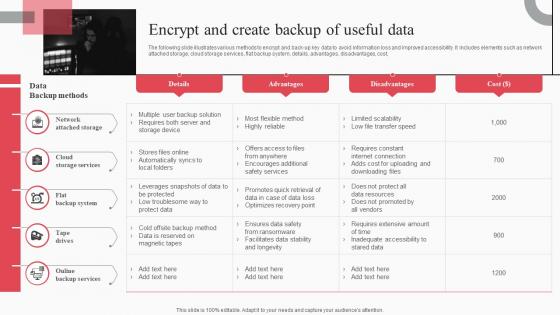 Encrypt And Create Backup Of Useful Data Cyber Attack Risks Mitigation
Encrypt And Create Backup Of Useful Data Cyber Attack Risks MitigationThe following slide illustrates various methods to encrypt and back-up key data to avoid information loss and improved accessibility. It includes elements such as network attached storage, cloud storage services, flat backup system, details, advantages, disadvantages, cost, Deliver an outstanding presentation on the topic using this Encrypt And Create Backup Of Useful Data Cyber Attack Risks Mitigation. Dispense information and present a thorough explanation of Network Attached Storage, Cloud Storage Services, Flat Backup System using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Impact Of Cyber Security Policies And Practices Cyber Attack Risks Mitigation
Impact Of Cyber Security Policies And Practices Cyber Attack Risks MitigationThe following slide focuses on drafting cyber security policies to manage data control and breach. It mainly includes elements such as impact of existing cyber safety policies, mitigation actions, etc. Present the topic in a bit more detail with this Impact Of Cyber Security Policies And Practices Cyber Attack Risks Mitigation. Use it as a tool for discussion and navigation on Inadequate Security Guidelines, Inappropriate Privacy Policies. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
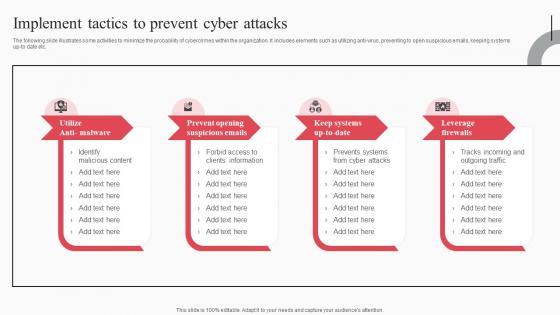 Implement Tactics To Prevent Cyber Attacks Cyber Attack Risks Mitigation
Implement Tactics To Prevent Cyber Attacks Cyber Attack Risks MitigationThe following slide illustrates some activities to minimize the probability of cybercrimes within the organization. It includes elements such as utilizing anti virus, preventing to open suspicious emails, keeping systems up to date etc. Introducing Implement Tactics To Prevent Cyber Attacks Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Prevent Opening Suspicious Emails, Keep Systems Up To Date, Leverage Firewalls, using this template. Grab it now to reap its full benefits.
-
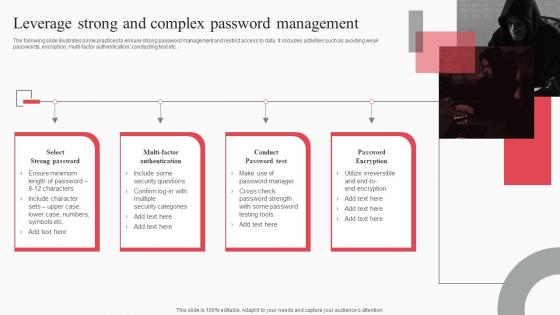 Leverage Strong And Complex Password Management Cyber Attack Risks Mitigation
Leverage Strong And Complex Password Management Cyber Attack Risks MitigationThe following slide illustrates some practices to ensure strong password management and restrict access to data. It includes activities such as avoiding weak passwords, encryption, multi-factor authentication, conducting test etc. Increase audience engagement and knowledge by dispensing information using Leverage Strong And Complex Password Management Cyber Attack Risks Mitigation. This template helps you present information on four stages. You can also present information on Select Strong Password, Multi Factor Authentication, Conduct Password Test using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Monitor And Assess Vendor Risk Management Cyber Attack Risks Mitigation
Monitor And Assess Vendor Risk Management Cyber Attack Risks MitigationThe following slide showcases vendor risk analysis checklist to ensure customer data safety. It includes key elements such as information security and privacy, physical assets, web application, infrastructure security etc. Introducing Monitor And Assess Vendor Risk Management Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Web Application Security, Infrastructure Security, Vendor Management, using this template. Grab it now to reap its full benefits.
-
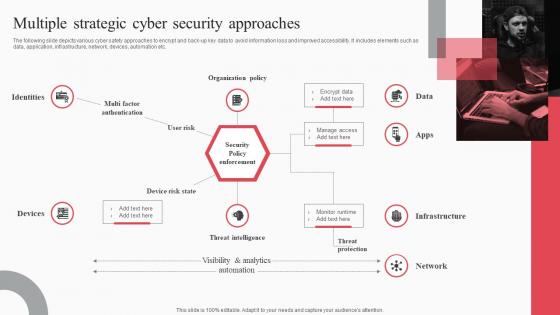 Multiple Strategic Cyber Security Approaches Cyber Attack Risks Mitigation
Multiple Strategic Cyber Security Approaches Cyber Attack Risks MitigationThe following slide depicts various cyber safety approaches to encrypt and back up key data to avoid information loss and improved accessibility. It includes elements such as data, application, infrastructure, network, devices, automation etc. Increase audience engagement and knowledge by dispensing information using Multiple Strategic Cyber Security Approaches Cyber Attack Risks Mitigation. This template helps you present information on one stage. You can also present information on Identities, Organization Policy, Threat Intelligence using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Organize Cyber Security Training For Employees Regularly Cyber Attack Risks Mitigation
Organize Cyber Security Training For Employees Regularly Cyber Attack Risks MitigationThe following slide depicts the staff cyber security training plan to educate them regarding technology threats and practices. It mainly includes elements such as topics to be covered, target audience, trainer name, mode, proposed date, timings etc. Introducing Organize Cyber Security Training For Employees Regularly Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Document Management, Response Process, Social Media Policy, using this template. Grab it now to reap its full benefits.
-
 Passive Active And Offensive Cyber Security Strategies Cyber Attack Risks Mitigation
Passive Active And Offensive Cyber Security Strategies Cyber Attack Risks MitigationThe following slide showcases passive, active and offensive cyber safety techniques to ensure customer data safety. It includes elements such as inspecting vulnerabilities, penetration testing, deception technology, threat hunting etc. Increase audience engagement and knowledge by dispensing information using Passive Active And Offensive Cyber Security Strategies Cyber Attack Risks Mitigation. This template helps you present information on three stages. You can also present information on Passive Safety, Active Safety, Offensive Safety using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
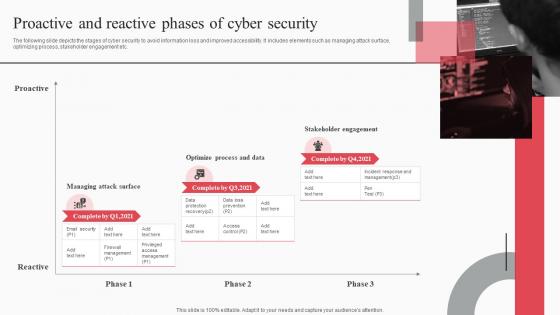 Proactive And Reactive Phases Of Cyber Security Cyber Attack Risks Mitigation
Proactive And Reactive Phases Of Cyber Security Cyber Attack Risks MitigationThe following slide depicts the stages of cyber security to avoid information loss and improved accessibility. It includes elements such as managing attack surface, optimizing process, stakeholder engagement etc. Introducing Proactive And Reactive Phases Of Cyber Security Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Proactive, Managing Attack Surface, Optimize Process, Stakeholder Engagement, using this template. Grab it now to reap its full benefits.
-
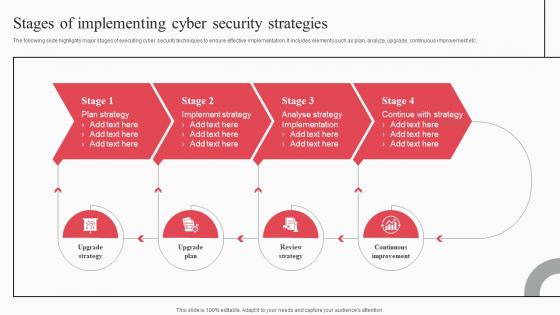 Stages Of Implementing Cyber Security Strategies Cyber Attack Risks Mitigation
Stages Of Implementing Cyber Security Strategies Cyber Attack Risks MitigationThe following slide highlights major stages of executing cyber security techniques to ensure effective implementation. It includes elements such as plan, analyze, upgrade, continuous improvement etc. Increase audience engagement and knowledge by dispensing information using Stages Of Implementing Cyber Security Strategies Cyber Attack Risks Mitigation. This template helps you present information on four stages. You can also present information on Plan Strategy, Implement Strategy, Analyse Strategy using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
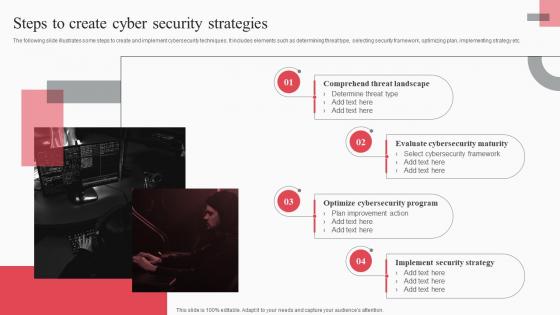 Steps To Create Cyber Security Strategies Cyber Attack Risks Mitigation
Steps To Create Cyber Security Strategies Cyber Attack Risks MitigationThe following slide illustrates some steps to create and implement cybersecurity techniques. It includes elements such as determining threat type, selecting security framework, optimizing plan, implementing strategy etc. Introducing Steps To Create Cyber Security Strategies Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Comprehend Threat Landscape, Evaluate Cybersecurity Maturity, Optimize Cybersecurity Program, using this template. Grab it now to reap its full benefits.
-
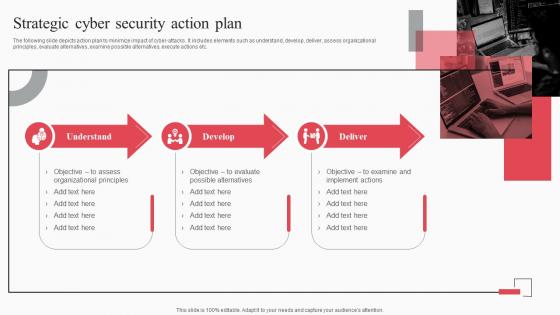 Strategic Cyber Security Action Plan Cyber Attack Risks Mitigation
Strategic Cyber Security Action Plan Cyber Attack Risks MitigationThe following slide depicts action plan to minimize impact of cyber attacks. It includes elements such as understand, develop, deliver, assess organizational principles, evaluate alternatives, examine possible alternatives, execute actions etc. Increase audience engagement and knowledge by dispensing information using Strategic Cyber Security Action Plan Cyber Attack Risks Mitigation. This template helps you present information on three stages. You can also present information on Understand, Develop, Deliver, Organizational Principles using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
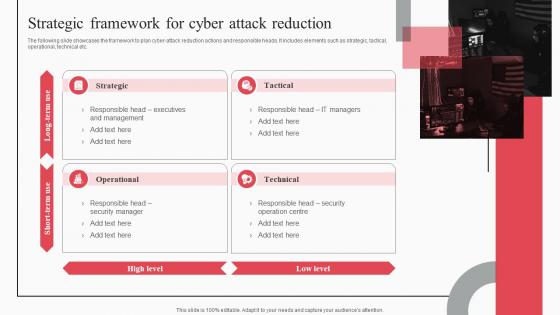 Strategic Framework For Cyber Attack Reduction Cyber Attack Risks Mitigation
Strategic Framework For Cyber Attack Reduction Cyber Attack Risks MitigationThe following slide showcases the framework to plan cyber-attack reduction actions and responsible heads. It includes elements such as strategic, tactical, operational, technical etc. Introducing Strategic Framework For Cyber Attack Reduction Cyber Attack Risks Mitigation to increase your presentation threshold. Encompassed with four stages, this template is a great option to educate and entice your audience. Dispence information on Strategic, Tactical, Operational, Technical, using this template. Grab it now to reap its full benefits.
-
 Table Of Contents For Cyber Attack Risks Mitigation Strategies Ppt Slides
Table Of Contents For Cyber Attack Risks Mitigation Strategies Ppt SlidesIntroducing Table Of Contents For Cyber Attack Risks Mitigation Strategies Ppt Slides to increase your presentation threshold. Encompassed with fifteen stages, this template is a great option to educate and entice your audience. Dispence information on Security Strategies, Strategic Framework, Password Management, using this template. Grab it now to reap its full benefits.
-
 Banks Cyber Attacks In Powerpoint And Google Slides Cpb
Banks Cyber Attacks In Powerpoint And Google Slides CpbPresenting Banks Cyber Attacks In Powerpoint And Google Slides Cpb slide which is completely adaptable. The graphics in this PowerPoint slide showcase four stages that will help you succinctly convey the information. In addition, you can alternate the color, font size, font type, and shapes of this PPT layout according to your content. This PPT presentation can be accessed with Google Slides and is available in both standard screen and widescreen aspect ratios. It is also a useful set to elucidate topics like Banks Cyber Attacks. This well-structured design can be downloaded in different formats like PDF, JPG, and PNG. So, without any delay, click on the download button now.
-
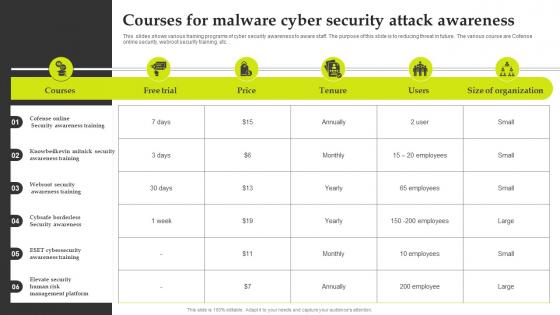 Courses For Malware Cyber Security Attack Awareness
Courses For Malware Cyber Security Attack AwarenessThis slides shows various training programs of cyber security awareness to aware staff. The purpose of this slide is to reducing threat in future. The various course are Cofense online security, webroot security training, etc.Introducing our Courses For Malware Cyber Security Attack Awareness set of slides. The topics discussed in these slides are Awareness Training, Security Awareness Training, Security Awareness. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Icon For Minimizing Digital Risk And Cyber Attacks
Icon For Minimizing Digital Risk And Cyber AttacksIntroducing our Icon For Minimizing Digital Risk And Cyber Attacks set of slides. The topics discussed in these slides are Minimizing Digital Risk Cyber Attacks This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Protection from cyber attacks ppt slide examples
Protection from cyber attacks ppt slide examplesPresenting protection from cyber attacks ppt slides examples PPT slide. The tension-free download is possible. Once downloaded, the presentation can be modified to any format like JPG, JPEG, PDF, etc. It’s also compatible with multiple software and Google Slides. The provided executive summary PPT presentation template can easily be used solely or as part of your pre-built presentation. Be happy to customize and personalize the presentation with company specifications.There is no hassle when any facts, figures or text is to be included or excluded in the presentation. Picture quality compatible with widescreen exposure.
-
 Purchases investment banking cyber security attacks marketing board cpb
Purchases investment banking cyber security attacks marketing board cpbPresenting this set of slides with name - Purchases Investment Banking Cyber Security Attacks Marketing Board Cpb. This is an editable three stages graphic that deals with topics like Purchases, Investment Banking, Cyber Security Attacks, Marketing Board to help convey your message better graphically. This product is a premium product available for immediate download, and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Types cyber attacks ppt powerpoint presentation infographics summary cpb
Types cyber attacks ppt powerpoint presentation infographics summary cpbPresenting this set of slides with name Types Cyber Attacks Ppt Powerpoint Presentation Infographics Summary Cpb. This is an editable Powerpoint graphic that deals with topics like Types Cyber Attacks to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
-
 Icon depicting information security from cyber attack
Icon depicting information security from cyber attackPresenting this set of slides with name Icon Depicting Information Security From Cyber Attack. This is a three stage process. The stages in this process are Icon Depicting, Information Security, Cyber Attack. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.



