Powerpoint Templates and Google slides for Cyber Check
Save Your Time and attract your audience with our fully editable PPT Templates and Slides.
-
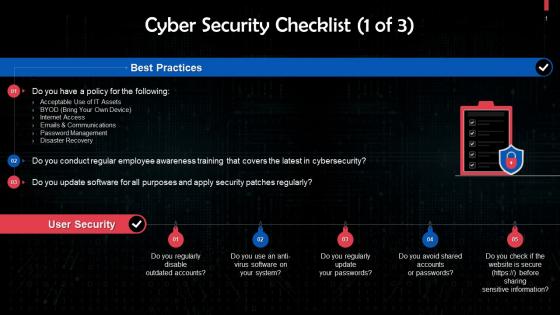 Cyber Security Checklist For Organizations Training Ppt
Cyber Security Checklist For Organizations Training PptPresenting Cyber Security Checklist for Organizations. This PPT presentation is thoroughly researched by the experts, and every slide consists of appropriate content. It is well crafted and designed by our PowerPoint specialists. Suitable for use by managers, employees, and organizations. You can edit the color, text, icon, and font size to suit your requirements. The PPT also supports Google Slides. Even Premium Customer Support is also available. Download now and present with confidence.
-
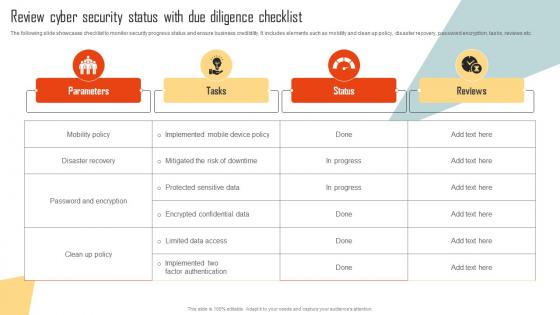 Review Cyber Security Status With Due Diligence Checklist Improving Cyber Security Risks Management
Review Cyber Security Status With Due Diligence Checklist Improving Cyber Security Risks ManagementThe following slide showcases checklist to monitor security progress status and ensure business credibility. It includes elements such as mobility and clean up policy, disaster recovery, password encryption, tasks, reviews etc. Present the topic in a bit more detail with this Review Cyber Security Status With Due Diligence Checklist Improving Cyber Security Risks Management. Use it as a tool for discussion and navigation on Disaster Recovery, Password And Encryption, Parameters. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
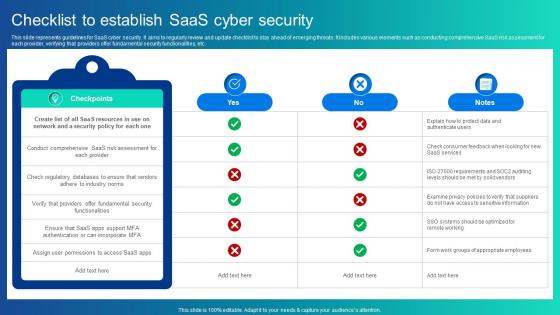 Checklist To Establish Saas Cyber Security
Checklist To Establish Saas Cyber SecurityThis slide represents guidelines for SaaS cyber security. It aims to regularly review and update checklist to stay ahead of emerging threats. It includes various elements such as conducting comprehensive SaaS risk assessment for each provider, verifying that providers offer fundamental security functionalities, etc. Introducing our Checklist To Establish Saas Cyber Security set of slides. The topics discussed in these slides are Incorporate MFA, Access Saas Apps This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Security Checklist To Protect Saas Applications
Cyber Security Checklist To Protect Saas ApplicationsThis slide represents cybersecurity checklist for SaaS applications to protect data. It aims to assist organizations in identifying potential vulnerabilities as well as examining security standards. It includes various elements such as backing up creation and testing, using real-time security service, etc. Introducing our Cyber Security Checklist To Protect Saas Applications set of slides. The topics discussed in these slides are Determines Data Isolation, Safeguards Against Data Theft This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
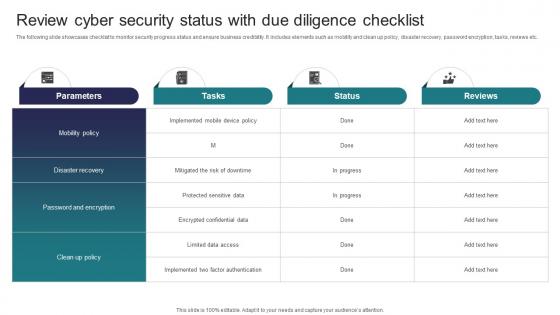 Implementing Strategies To Mitigate Cyber Security Review Cyber Security Status With Due Diligence Checklist
Implementing Strategies To Mitigate Cyber Security Review Cyber Security Status With Due Diligence ChecklistThe following slide showcases checklist to monitor security progress status and ensure business credibility. It includes elements such as mobility and clean up policy, disaster recovery, password encryption, tasks, reviews etc. Deliver an outstanding presentation on the topic using this Implementing Strategies To Mitigate Cyber Security Review Cyber Security Status With Due Diligence Checklist Dispense information and present a thorough explanation of Parameters, Tasks, Status using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
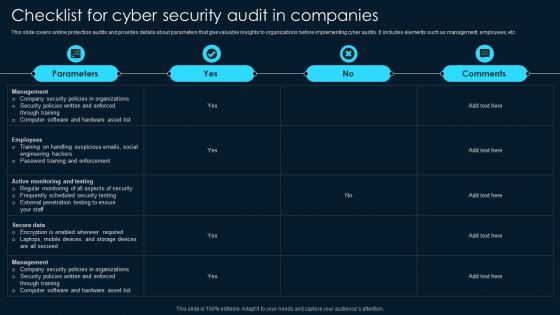 Checklist For Cyber Security Audit In Companies
Checklist For Cyber Security Audit In CompaniesThis slide covers online protection audits and provides details about parameters that give valuable insights to organizations before implementing cyber audits. It includes elements such as management, employees, etc. Introducing our Checklist For Cyber Security Audit In Companies set of slides. The topics discussed in these slides are Management, Company Security Policies Organizations, Security Policies Enforced. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
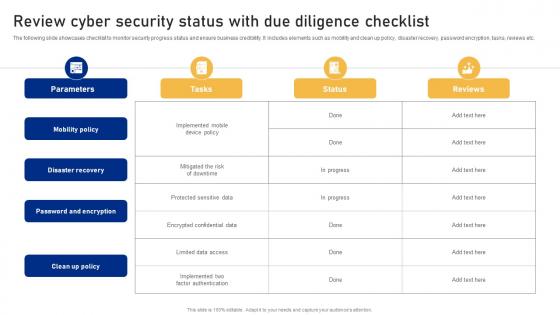 Review Cyber Security Status With Due Diligence Checklist Cyber Risk Assessment
Review Cyber Security Status With Due Diligence Checklist Cyber Risk AssessmentThe following slide showcases checklist to monitor security progress status and ensure business credibility. It includes elements such as mobility and clean up policy, disaster recovery, password encryption, tasks, reviews etc. Present the topic in a bit more detail with this Review Cyber Security Status With Due Diligence Checklist Cyber Risk Assessment Use it as a tool for discussion and navigation on Mobility Policy, Disaster Recovery, Password And Encryption This template is free to edit as deemed fit for your organization. Therefore download it now.
-
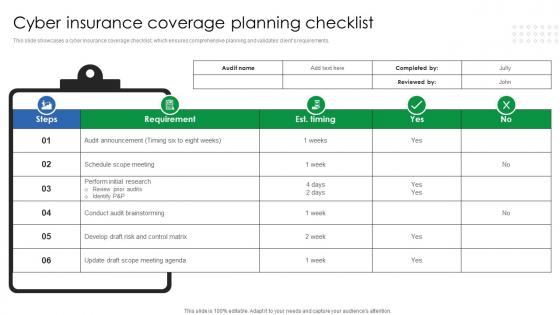 Cyber Insurance Coverage Planning Checklist
Cyber Insurance Coverage Planning ChecklistThis slide showcases a cyber insurance coverage checklist, which ensures comprehensive planning and validates clients requirements. Presenting our well structured Cyber Insurance Coverage Planning Checklist. The topics discussed in this slide are Cyber Insurance, Coverage Planning Checklist. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Cyber Security Insurance Audit Checklist
Cyber Security Insurance Audit ChecklistThis slide showcases cyber security insurance audit checklist which helps in providing coverage to reduce the financial risks associated with cybercrimes. Introducing our Cyber Security Insurance Audit Checklist set of slides. The topics discussed in these slides are Network And Perimeter Security, Password Policy And Authentication, Vulnerability Management, Backups And Disaster Recovery.This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Security Controls Checklist For Business
Cyber Security Controls Checklist For BusinessThis slide highlights the checklist for cyber security controls to prevent business from cyber attacks and protect company confidential data. It includes various KPIs such as password management, privacy and security of sensitive data. Presenting our well structured Cyber Security Controls Checklist For Business The topics discussed in this slide are Password Management, Security Awareness This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
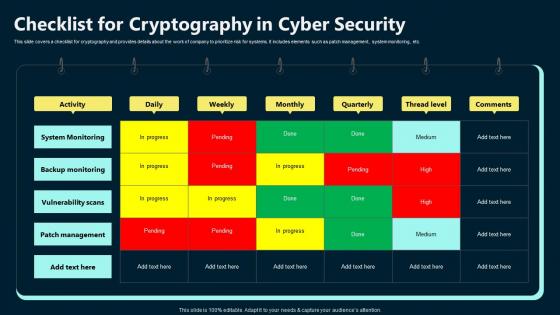 Checklist For Cryptography In Cyber Security
Checklist For Cryptography In Cyber SecurityThis slide covers a checklist for cryptography and provides details about the work of company to prioritize risk for systems. It includes elements such as patch management, system monitoring, etc. Introducing our Checklist For Cryptography In Cyber Security set of slides. The topics discussed in these slides are System Monitoring, Backup Monitoring, Vulnerability Scans . This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Cyber Incident Report Checklist Template For Decision Making
Cyber Incident Report Checklist Template For Decision MakingThis slide covers cyber report checklist for providing structured and standardized framework for documenting cybersecurity incidents. It includes aspects such as tasks, authorized head, relevant, irrelevant and notes. Presenting our well structured Cyber Incident Report Checklist Template For Decision Making. The topics discussed in this slide are Authorized Head, Irrelevant, Relevant. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
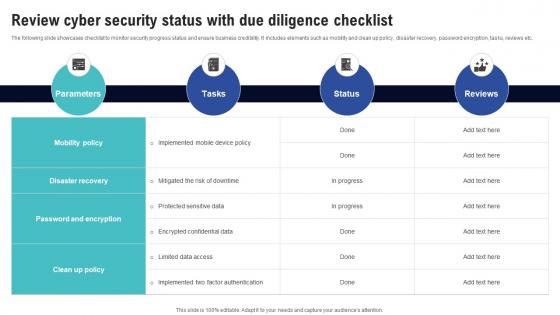 Review Cyber Security Status With Due Diligence Checklist Creating Cyber Security Awareness
Review Cyber Security Status With Due Diligence Checklist Creating Cyber Security AwarenessThe following slide showcases checklist to monitor security progress status and ensure business credibility. It includes elements such as mobility and clean up policy, disaster recovery, password encryption, tasks, reviews etc. Present the topic in a bit more detail with this Review Cyber Security Status With Due Diligence Checklist Creating Cyber Security Awareness Use it as a tool for discussion and navigation on Risk Probability, Risk Severity This template is free to edit as deemed fit for your organization. Therefore download it now.
-
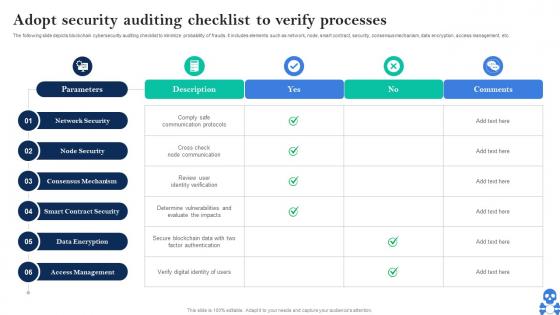 Cyber Threats In Blockchain Adopt Security Auditing Checklist To Verify Processes BCT SS V
Cyber Threats In Blockchain Adopt Security Auditing Checklist To Verify Processes BCT SS VThe following slide depicts blockchain cybersecurity auditing checklist to minimize probability of frauds. It includes elements such as network, node, smart contract, security, consensus mechanism, data encryption, access management, etc. Deliver an outstanding presentation on the topic using this Cyber Threats In Blockchain Adopt Security Auditing Checklist To Verify Processes BCT SS V Dispense information and present a thorough explanation of Consensus Mechanism, Smart Contract Security, Data Encryption using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
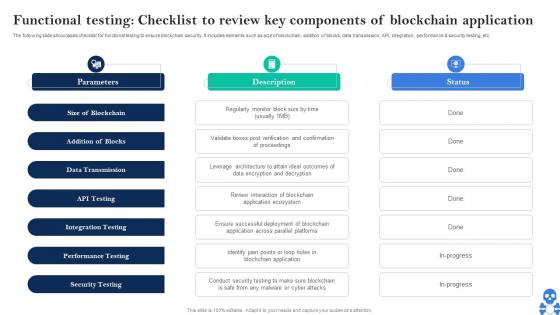 Cyber Threats In Blockchain Functional Testing Checklist To Review Key Components Of Blockchain BCT SS V
Cyber Threats In Blockchain Functional Testing Checklist To Review Key Components Of Blockchain BCT SS VThe following slide showcases checklist for functional testing to ensure blockchain security. It includes elements such as size of blockchain, addition of blocks, data transmission, API, integration, performance and security testing, etc. Introducing Cyber Threats In Blockchain Functional Testing Checklist To Review Key Components Of Blockchain BCT SS V to increase your presentation threshold. Encompassed with Three stages, this template is a great option to educate and entice your audience. Dispence information on Size Of Blockchain, Addition Of Blocks, Data Transmission using this template. Grab it now to reap its full benefits.
-
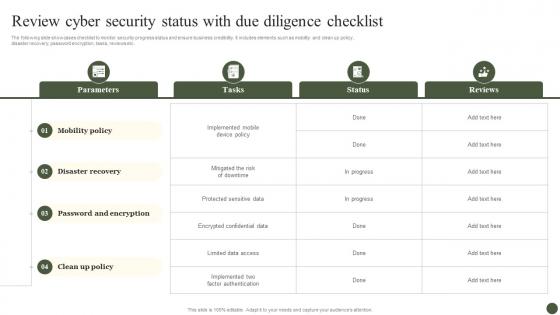 Review Cyber Security Status With Due Diligence Checklist Implementing Cyber Risk Management Process
Review Cyber Security Status With Due Diligence Checklist Implementing Cyber Risk Management ProcessThe following slide showcases checklist to monitor security progress status and ensure business credibility. It includes elements such as mobility and clean up policy, disaster recovery, password encryption, tasks, reviews etc. Present the topic in a bit more detail with this Review Cyber Security Status With Due Diligence Checklist Implementing Cyber Risk Management Process. Use it as a tool for discussion and navigation on Parameters, Tasks, Status, Reviews. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Checklist To Enhance Cyber Security Of SCADA Networks
Checklist To Enhance Cyber Security Of SCADA NetworksThis slide represents checklist that assist IT companies to enhance their SCADA networks cyber security for improving data protection. It includes various elements such as recognizing connections, disconnecting irrelevant networks, etc. Introducing our Checklist To Enhance Cyber Security Of SCADA Networks set of slides. The topics discussed in these slides are Essential Connections, Inadvertent Disclosure, SCADA Network This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Checklist To Establish Triage Capability In Cyber Security
Checklist To Establish Triage Capability In Cyber SecurityThis slide represents checklist to establish triage capability in cyber security which assists to analyse threat alerts and effectively response cyber threats. It includes checklist to establish triage capability in cyber security which includes steps such as type of events, skill levels, etc Introducing our Checklist To Establish Triage Capability In Cyber Security set of slides. The topics discussed in these slides are Types Of Events, Skills Levels, Channels Of Support. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 ATP Cyber Security Features Checklist
ATP Cyber Security Features ChecklistThis slide depicts the essential features checklist for cyber security ATP. Its aim is to include the essential features during advanced threat protection of a system. This slide includes file analytics, attacks surface management, combined prevention and rich threat intelligence, etc. Presenting our set of slides with name ATP Cyber Security Features Checklist. This exhibits information on Four stages of the process. This is an easy to edit and innovatively designed PowerPoint template. So download immediately and highlight information on File Analytics, Attack Surface Management, Combined Prevention, Rich Threat Intelligence.
-
 Checklist for effectively managing asset managing cyber risk in a digital age
Checklist for effectively managing asset managing cyber risk in a digital ageFollowing slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them. Present the topic in a bit more detail with this Checklist For Effectively Managing Asset Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Checklist For Effectively Managing Asset Security. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
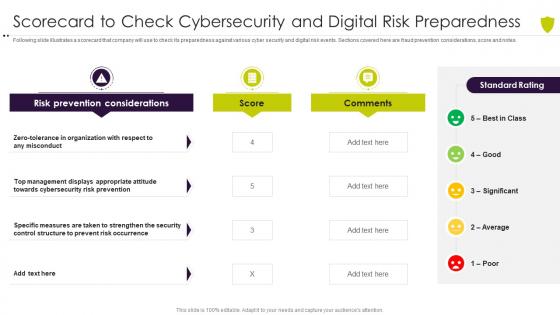 Scorecard to check cybersecurity managing cyber risk in a digital age
Scorecard to check cybersecurity managing cyber risk in a digital ageFollowing slide illustrates a scorecard that company will use to check its preparedness against various cyber security and digital risk events. Sections covered here are fraud prevention considerations, score and notes. Present the topic in a bit more detail with this Scorecard To Check Cybersecurity Managing Cyber Risk In A Digital Age. Use it as a tool for discussion and navigation on Organization, Misconduct, Prevention, Appropriate. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
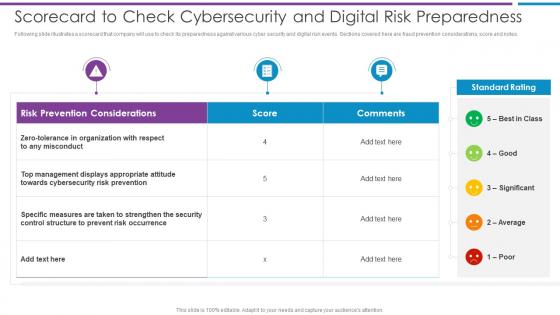 Scorecard To Check Cybersecurity Based Methodology To Cyber
Scorecard To Check Cybersecurity Based Methodology To CyberFollowing slide illustrates a scorecard that company will use to check its preparedness against various cyber security and digital risk events. Sections covered here are fraud prevention considerations, score and notes.Deliver an outstanding presentation on the topic using this Scorecard To Check Cybersecurity Based Methodology To Cyber Dispense information and present a thorough explanation of Organization With Respect, Management Displays, Cybersecurity Risk Prevention using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Terrorism Attacks Checklist To Deal With Cyber Terrorism Threats
Cyber Terrorism Attacks Checklist To Deal With Cyber Terrorism ThreatsThis slide represents the checklist to deal with cyber terrorism attacks threats which involve 24 7 monitoring, employee training, keeping software updated. Increase audience engagement and knowledge by dispensing information using Cyber Terrorism Attacks Checklist To Deal With Cyber Terrorism Threats. This template helps you present information on nine stages. You can also present information on Cyber Security Assessment, Limited Access Privileges, Employee Training, External Cyber Intelligence using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
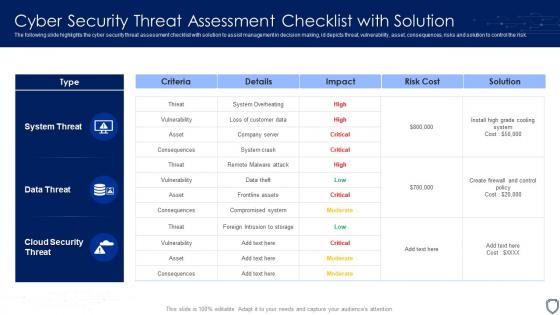 Cyber Security Threat Assessment Checklist With Solution
Cyber Security Threat Assessment Checklist With SolutionThe following slide highlights the cyber security threat assessment checklist with solution to assist management in decision making, id depicts threat, vulnerability, asset, consequences, risks and solution to control the risk. Introducing our Cyber Security Threat Assessment Checklist With Solution set of slides. The topics discussed in these slides are System Threat, Data Threat, Cloud Security Threat. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
 Third Party Cyber Security Implementation Checklist
Third Party Cyber Security Implementation ChecklistIntroducing our premium set of slides with name Third Party Cyber Security Implementation Checklist. Ellicudate the three stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Third Party Cyber Security, Implementation Checklist. So download instantly and tailor it with your information.
-
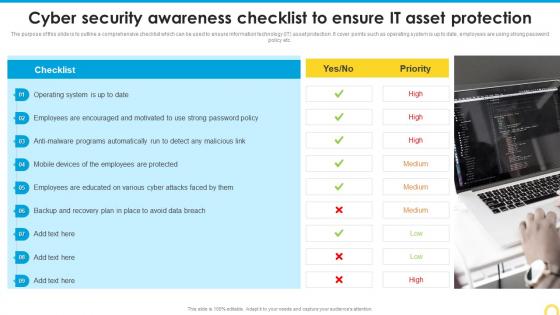 Cyber Security Awareness Checklist Building A Security Awareness Program
Cyber Security Awareness Checklist Building A Security Awareness ProgramThe purpose of this slide is to outline a comprehensive checklist which can be used to ensure information technology IT asset protection. It cover points such as operating system is up to date, employees are using strong password policy etc. Introducing Cyber Security Awareness Checklist Building A Security Awareness Program to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Operating System, Programs Automatically, Asset Protection, using this template. Grab it now to reap its full benefits.
-
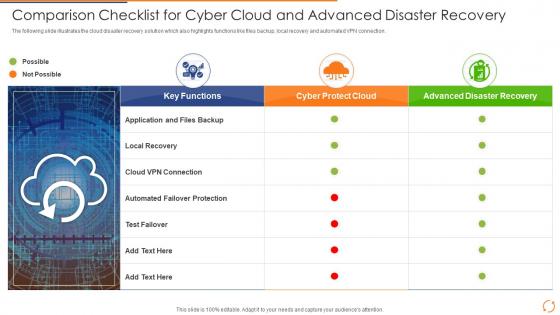 Comparison Checklist For Cyber Cloud And Advanced Disaster Recovery
Comparison Checklist For Cyber Cloud And Advanced Disaster RecoveryIntroducing our premium set of slides with Comparison Checklist For Cyber Cloud And Advanced Disaster Recovery. Ellicudate the four stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cloud Disaster Recovery Icon With Reload Sign. So download instantly and tailor it with your information.
-
 Cyberterrorism it checklist to deal with cyber terrorism threats ppt slides templates
Cyberterrorism it checklist to deal with cyber terrorism threats ppt slides templatesThis slide represents the checklist to deal with cyber terrorism threats which involve 24 7 monitoring, employee training, keeping software updated. Increase audience engagement and knowledge by dispensing information using Cyberterrorism IT Checklist To Deal With Cyber Terrorism Threats Ppt Slides Templates. This template helps you present information on one stages. You can also present information on Incident Response Plan, Limited Access Privileges, Evaluating Risk Third Party Vendor, Cyber Security Assessment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
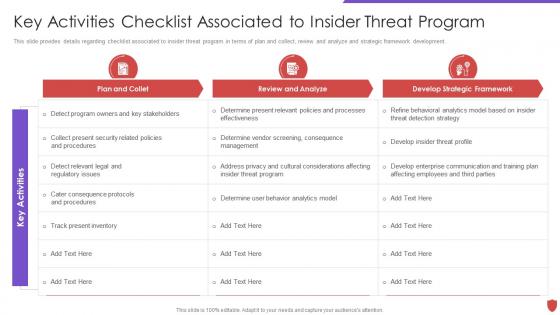 Cyber security risk management key activities checklist associated to insider threat
Cyber security risk management key activities checklist associated to insider threatThis slide provides details regarding checklist associated to insider threat program in terms of plan and collect, review and analyze and strategic framework development. Deliver an outstanding presentation on the topic using this Cyber Security Risk Management Key Activities Checklist Associated To Insider Threat. Dispense information and present a thorough explanation of Plan And Collet, Review And Analyze, Develop Strategic Framework, Track Present Inventory using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
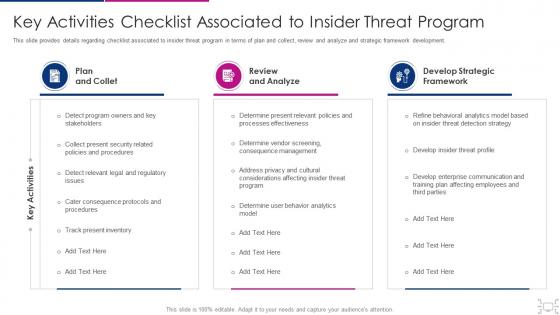 Cyber threat management workplace key activities checklist associated insider
Cyber threat management workplace key activities checklist associated insiderThis slide provides details regarding checklist associated to insider threat program in terms of plan and collect, review and analyze and strategic framework development. Present the topic in a bit more detail with this Cyber Threat Management Workplace Key Activities Checklist Associated Insider. Use it as a tool for discussion and navigation on Plan And Collet, Review And Analyze, Develop Strategic Framework, Track Present Inventory, Determine User Behavior Analytics Model . This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Awareness Checklist To Ensure Implementing Security Awareness Training
Cyber Security Awareness Checklist To Ensure Implementing Security Awareness TrainingThe purpose of this slide is to outline a comprehensive checklist which can be used to ensure information technology IT asset protection. It cover points such as operating system is up to date, employees are using strong password policy etc. Deliver an outstanding presentation on the topic using this Cyber Security Awareness Checklist To Ensure Implementing Security Awareness Training. Dispense information and present a thorough explanation of Cyber Security, Awareness Checklist, Asset Protection using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Checklist To Mitigate Threats Of Attack
Cyber Security Checklist To Mitigate Threats Of AttackThe given slide provides the key activities to be done to alleviate the effects of cyber threats. It includes managing social media profiles, backing up the data, crosschecking privacy and security settings etc. Introducing our premium set of slides with Cyber Security Checklist To Mitigate Threats Of Attack. Ellicudate the seven stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Cyber Security Checklist, Mitigate Threats Attack. So download instantly and tailor it with your information.
-
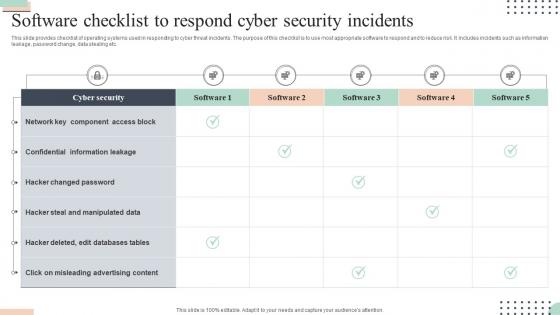 Software Checklist To Respond Cyber Security Incidents
Software Checklist To Respond Cyber Security IncidentsThis slide provides checklist of operating systems used in responding to cyber threat incidents. The purpose of this checklist is to use most appropriate software to respond and to reduce risk. It includes incidents such as information leakage, password change, data stealing etc.Presenting our well structured Software Checklist To Respond Cyber Security Incidents. The topics discussed in this slide are Confidential Information, Misleading Advertising, Hacker Changed. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
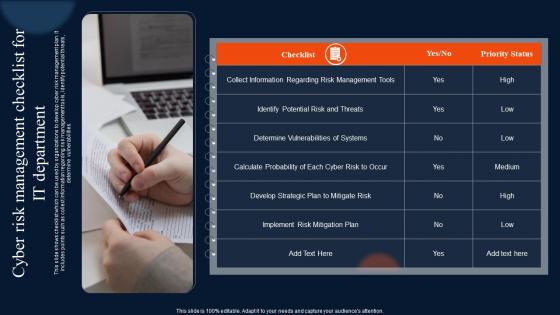 Cyber Risk Management Checklist For It Department
Cyber Risk Management Checklist For It DepartmentThis slide shows checklist which can be used by organizations to develop cyber risk management plan. It includes points such as collect information regarding risk management tools, identify potential threats, determine vulnerabilities. Presenting our well structured Cyber Risk Management Checklist For It Department. The topics discussed in this slide are Management, Department, Information. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
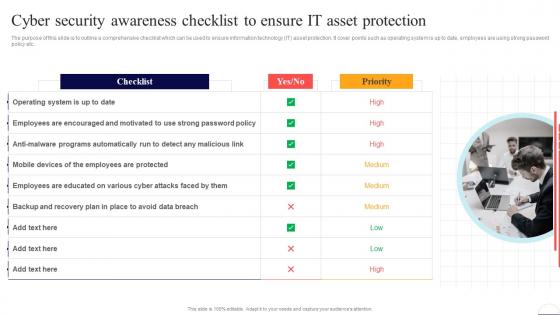 Cyber Security Awareness Checklist To Ensure It Asset Preventing Data Breaches Through Cyber Security
Cyber Security Awareness Checklist To Ensure It Asset Preventing Data Breaches Through Cyber SecurityThe purpose of this slide is to outline a comprehensive checklist which can be used to ensure information technology IT asset protection. It cover points such as operating system is up to date, employees are using strong password policy etc. Introducing Cyber Security Awareness Checklist To Ensure It Asset Preventing Data Breaches Through Cyber Security to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Employees, Data Breach, Operating System, using this template. Grab it now to reap its full benefits.
-
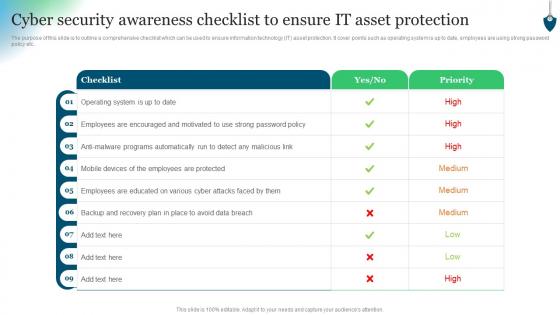 Cyber Security Awareness Checklist To Ensure IT Asset Protection Conducting Security Awareness
Cyber Security Awareness Checklist To Ensure IT Asset Protection Conducting Security AwarenessThe purpose of this slide is to outline a comprehensive checklist which can be used to ensure information technology IT asset protection. It cover points such as operating system is up to date, employees are using strong password policy etc. Present the topic in a bit more detail with this Cyber Security Awareness Checklist To Ensure IT Asset Protection Conducting Security Awareness. Use it as a tool for discussion and navigation on Checklist, Operating System, Employees Encouraged. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Incident Response Plan Checklist
Cyber Security Incident Response Plan ChecklistThis slide covers cyber security incident response plan checklist. It involves pre requisites such as identify fundamentals, terms and contracts, identify phases, team communication plan and incident response forms. Presenting our well structured Cyber Security Incident Response Plan Checklist. The topics discussed in this slide are Cyber Security, Incident Response, Plan Checklist. This is an instantly available PowerPoint presentation that can be edited conveniently. Download it right away and captivate your audience.
-
 Developing Cyber Security Awareness Cyber Security Awareness Checklist To Ensure It Asset Protection
Developing Cyber Security Awareness Cyber Security Awareness Checklist To Ensure It Asset ProtectionThe purpose of this slide is to outline a comprehensive checklist which can be used to ensure information technology IT asset protection. It cover points such as operating system is up to date, employees are using strong password policy etc. Introducing Developing Cyber Security Awareness Cyber Security Awareness Checklist To Ensure It Asset Protection to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Cyber Security, Awareness Checklist, IT Asset Protection, using this template. Grab it now to reap its full benefits.
-
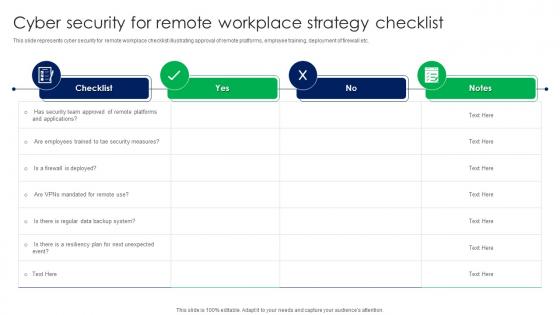 Cyber Security For Remote Workplace Strategy Checklist
Cyber Security For Remote Workplace Strategy ChecklistThis slide represents cyber security for remote workplace checklist illustrating approval of remote platforms, employee training, deployment of firewall etc. Introducing our Cyber Security For Remote Workplace Strategy Checklist set of slides. The topics discussed in these slides are Cyber Security, Remote Workplace, Strategy Checklist. This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
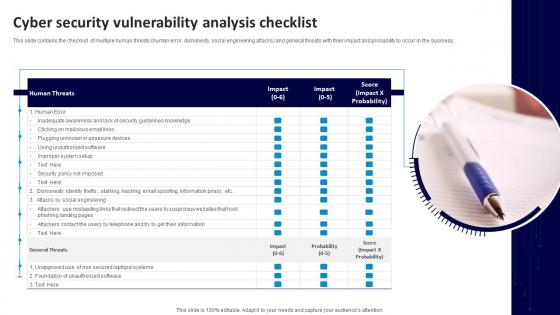 Cyber Security Vulnerability Analysis Checklist
Cyber Security Vulnerability Analysis ChecklistThis slide contains the checklist of multiple human threats human error, dishonesty, social engineering attacks and general threats with their impact and probability to occur in the business. Introducing our premium set of slides with Cyber Security Vulnerability Analysis Checklist. Ellicudate the one stages and present information using this PPT slide. This is a completely adaptable PowerPoint template design that can be used to interpret topics like Human Threats, General Threats, Unsecure Devices. So download instantly and tailor it with your information.
-
 Cyber Security Incident Handling Checklist Ppt Powerpoint Presentation Model Introduction
Cyber Security Incident Handling Checklist Ppt Powerpoint Presentation Model IntroductionThis slide represents the checklist to ensure activities to effectively handle and manage cyber security incidents. It includes details related to detection and analysis, containment, eradication and recovery and post incident activity. Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Handling Checklist Ppt Powerpoint Presentation Model Introduction. This template helps you present information on one stage. You can also present information on Detection And Analysis, Containment, Eradication And Recovery using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Incident Management Checklist After An Incident Ppt Guidelines
Cyber Security Incident Management Checklist After An Incident Ppt GuidelinesThis slide represents the checklist to effectively ensure activities aiming towards minimizing the impact of cyber security incidents on organizations. It includes checklist of cyber security incident management after the occurrence of the incident. Introducing Cyber Security Incident Management Checklist After An Incident Ppt Guidelines to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Cyber Security, Incident Management, Quantify Financial, using this template. Grab it now to reap its full benefits.
-
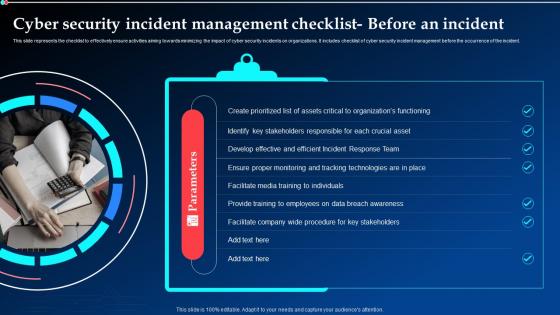 Cyber Security Incident Management Checklist Before An Incident Ppt Slides
Cyber Security Incident Management Checklist Before An Incident Ppt SlidesThis slide represents the checklist to effectively ensure activities aiming towards minimizing the impact of cyber security incidents on organizations. It includes checklist of cyber security incident management before the occurrence of the incident. Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Management Checklist Before An Incident Ppt Slides. This template helps you present information on one stage. You can also present information on Cyber Security, Incident Management, Technologies using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Incident Management Checklist During An Incident Ppt Clipart
Cyber Security Incident Management Checklist During An Incident Ppt ClipartThis slide represents the checklist to effectively ensure activities aiming towards minimizing the impact of cyber security incidents on organizations. It includes checklist of cyber security incident management during the occurrence of the incident. Introducing Cyber Security Incident Management Checklist During An Incident Ppt Clipart to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Cyber Security, Incident Management, Executive Management, using this template. Grab it now to reap its full benefits.
-
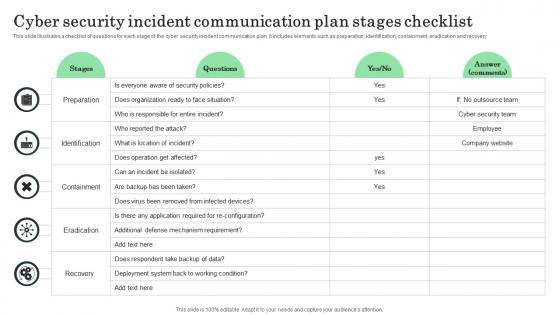 Cyber Security Incident Communication Plan Stages Checklist
Cyber Security Incident Communication Plan Stages ChecklistThis slide illustrates a checklist of questions for each stage of the cyber security incident communication plan. It includes elements such as preparation, identification, containment, eradication and recovery. Introducing our Cyber Security Incident Communication Plan Stages Checklist set of slides. The topics discussed in these slides are Preparation, Identification, Containment This is an immediately available PowerPoint presentation that can be conveniently customized. Download it and convince your audience.
-
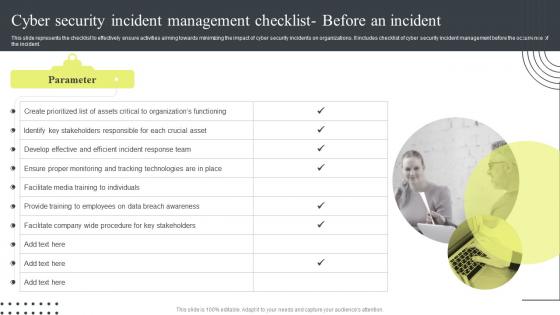 K55 Cyber Security Attacks Response Cyber Security Incident Management Checklist Before
K55 Cyber Security Attacks Response Cyber Security Incident Management Checklist BeforeThis slide represents the checklist to effectively ensure activities aiming towards minimizing the impact of cyber security incidents on organizations. It includes checklist of cyber security incident management before the occurrence of the incident. Increase audience engagement and knowledge by dispensing information using K55 Cyber Security Attacks Response Cyber Security Incident Management Checklist Before. This template helps you present information on one stages. You can also present information on Cyber Security, Incident Management, Checklist Before An Incident using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
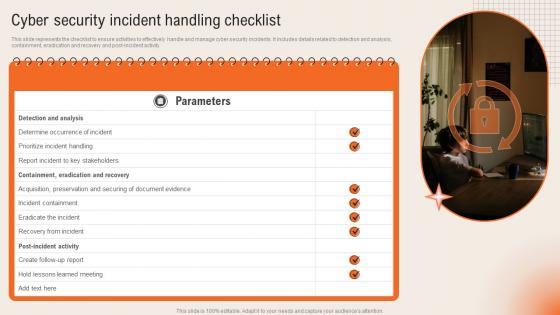 Cyber Security Incident Handling Checklist Deploying Computer Security Incident Management
Cyber Security Incident Handling Checklist Deploying Computer Security Incident ManagementThis slide represents the checklist to ensure activities to effectively handle and manage cyber security incidents. It includes details related to detection and analysis, containment, eradication and recovery and post incident activity.Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Handling Checklist Deploying Computer Security Incident Management. This template helps you present information on one stage. You can also present information on Containment Eradication, Acquisition Preservation, Incident Containment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
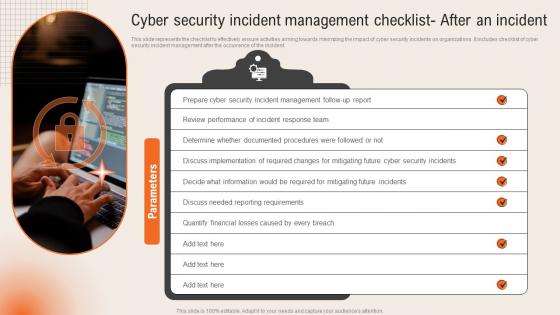 Cyber Security Incident Management Checklist After An Incident Deploying Computer Security
Cyber Security Incident Management Checklist After An Incident Deploying Computer SecurityThis slide represents the checklist to effectively ensure activities aiming towards minimizing the impact of cyber security incidents on organizations. It includes checklist of cyber security incident management after the occurrence of the incident.Introducing Cyber Security Incident Management Checklist After An Incident Deploying Computer Security to increase your presentation threshold. Encompassed with one stage, this template is a great option to educate and entice your audience. Dispence information on Incident Management, Reporting Requirements, Quantify Financial, using this template. Grab it now to reap its full benefits.
-
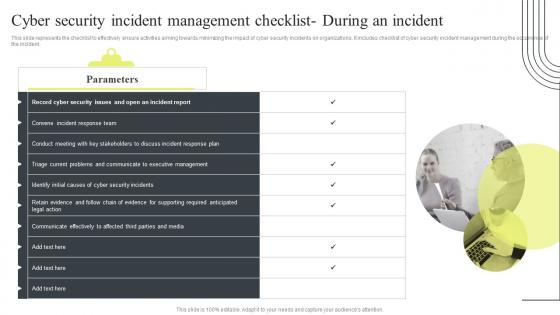 Cyber Security Attacks Response Guid Cyber Security Incident Management Checklist During An Incident
Cyber Security Attacks Response Guid Cyber Security Incident Management Checklist During An IncidentThis slide represents the checklist to effectively ensure activities aiming towards minimizing the impact of cyber security incidents on organizations. It includes checklist of cyber security incident management during the occurrence of the incident. Increase audience engagement and knowledge by dispensing information using Cyber Security Attacks Response Guid Cyber Security Incident Management Checklist During An Incident. This template helps you present information on one stages. You can also present information on Cyber Security, Incident Management, Checklist During An Incident using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
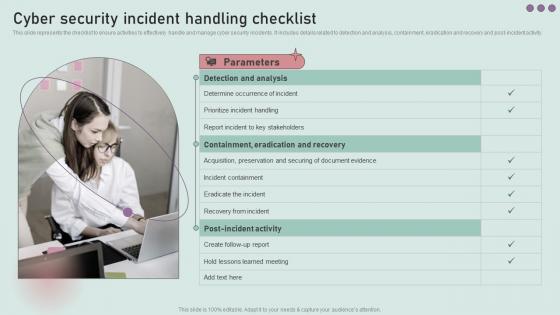 Cyber Security Incident Handling Checklist Development And Implementation Of Security
Cyber Security Incident Handling Checklist Development And Implementation Of SecurityThis slide represents the checklist to ensure activities to effectively handle and manage cyber security incidents. It includes details related to detection and analysis, containment, eradication and recovery and post incident activity. Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Handling Checklist Development And Implementation Of Security. This template helps you present information on three stages. You can also present information on Detection And Analysis, Prioritize Incident Handling, Incident Containment using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
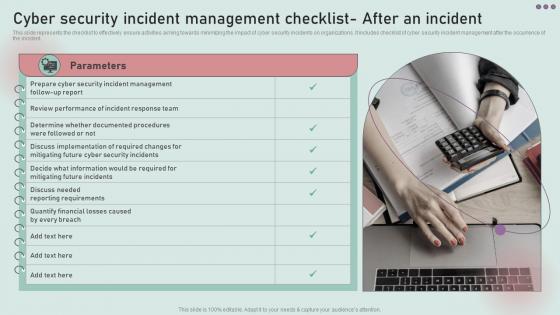 Cyber Security Incident Management Checklist After Development And Implementation Of Security
Cyber Security Incident Management Checklist After Development And Implementation Of SecurityThis slide represents the checklist to effectively ensure activities aiming towards minimizing the impact of cyber security incidents on organizations. It includes checklist of cyber security incident management after the occurrence of the incident. Introducing Cyber Security Incident Management Checklist After Development And Implementation Of Security to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Review Performance, Incident Response Team, using this template. Grab it now to reap its full benefits.
-
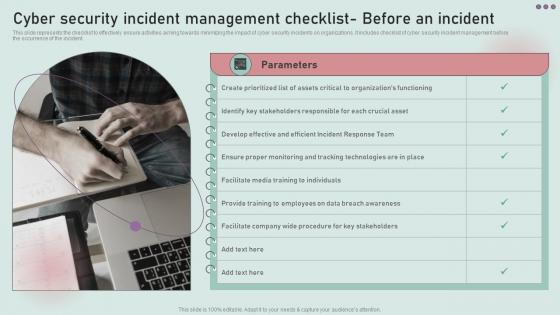 Cyber Security Incident Management Checklist Before Development And Implementation Of Security
Cyber Security Incident Management Checklist Before Development And Implementation Of SecurityThis slide represents the checklist to effectively ensure activities aiming towards minimizing the impact of cyber security incidents on organizations. It includes checklist of cyber security incident management before the occurrence of the incident. Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Management Checklist Before Development And Implementation Of Security. This template helps you present information on one stages. You can also present information on Develop Effective And Efficient, Incident Response Team using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
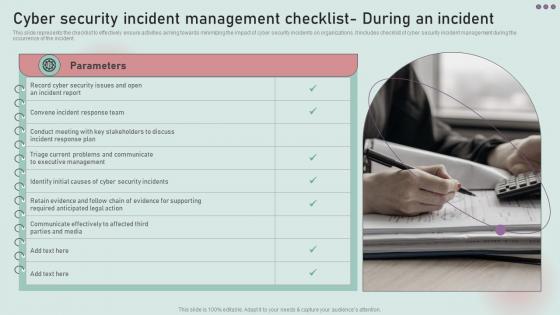 Cyber Security Incident Management Checklist During Development And Implementation Of Security
Cyber Security Incident Management Checklist During Development And Implementation Of SecurityThis slide represents the checklist to effectively ensure activities aiming towards minimizing the impact of cyber security incidents on organizations. It includes checklist of cyber security incident management during the occurrence of the incident. Introducing Cyber Security Incident Management Checklist During Development And Implementation Of Security to increase your presentation threshold. Encompassed with one stages, this template is a great option to educate and entice your audience. Dispence information on Triage Current Problems, Communicate, Executive Management, using this template. Grab it now to reap its full benefits.
-
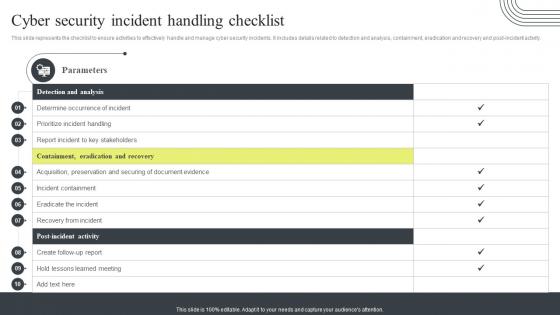 Cyber Security Incident Handling Checklist Cyber Security Attacks Response Plan
Cyber Security Incident Handling Checklist Cyber Security Attacks Response PlanThis slide represents the checklist to ensure activities to effectively handle and manage cyber security incidents. It includes details related to detection and analysis, containment, eradication and recovery and post incident activity. Present the topic in a bit more detail with this Cyber Security Incident Handling Checklist Cyber Security Attacks Response Plan. Use it as a tool for discussion and navigation on Containment, Eradication And Recovery, Detection And Analysis, Handling Checklist Acquisition. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
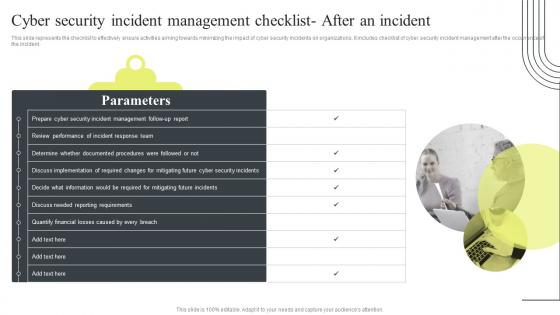 Cyber Security Incident Management Checklist After An Incident Cyber Security Attacks Response
Cyber Security Incident Management Checklist After An Incident Cyber Security Attacks ResponseThis slide represents the checklist to effectively ensure activities aiming towards minimizing the impact of cyber security incidents on organizations. It includes checklist of cyber security incident management after the occurrence of the incident. Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Management Checklist After An Incident Cyber Security Attacks Response. This template helps you present information on one stages. You can also present information on Cyber Security, Incident Management, Checklist After An Incident using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
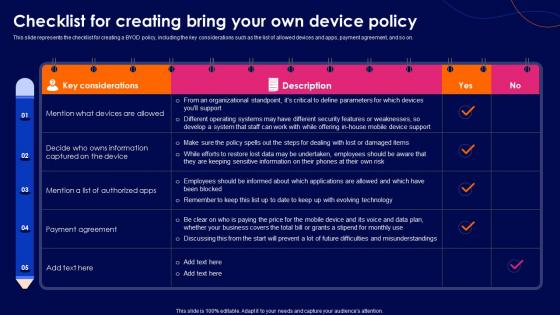 Cyber Security Policy Checklist For Creating Bring Your Own Device Policy
Cyber Security Policy Checklist For Creating Bring Your Own Device PolicyThis slide represents the checklist for creating a BYOD policy, including the key considerations such as the list of allowed devices and apps, payment agreement, and so on. Deliver an outstanding presentation on the topic using this Cyber Security Policy Checklist For Creating Bring Your Own Device Policy. Dispense information and present a thorough explanation of Considerations, Agreement, Represents using the slides given. This template can be altered and personalized to fit your needs. It is also available for immediate download. So grab it now.
-
 Cyber Security Policy Checklist For Writing An Effective It Policy
Cyber Security Policy Checklist For Writing An Effective It PolicyThis slide describes the checklist for an effective information technology policy, and it includes all the best practices that should be considered while writing an IT policy. Present the topic in a bit more detail with this Cyber Security Policy Checklist For Writing An Effective It Policy. Use it as a tool for discussion and navigation on Assessment, Essential, Weaknesses. This template is free to edit as deemed fit for your organization. Therefore download it now.
-
 Cyber Security Incident Handling Checklist Incident Response Strategies Deployment
Cyber Security Incident Handling Checklist Incident Response Strategies DeploymentThis slide represents the checklist to ensure activities to effectively handle and manage cyber security incidents. It includes details related to detection and analysis, containment, eradication and recovery and post incident activity. Introducing Cyber Security Incident Handling Checklist Incident Response Strategies Deployment to increase your presentation threshold. Encompassed with three stages, this template is a great option to educate and entice your audience. Dispence information on Parameters, Analysis, Containment, using this template. Grab it now to reap its full benefits.
-
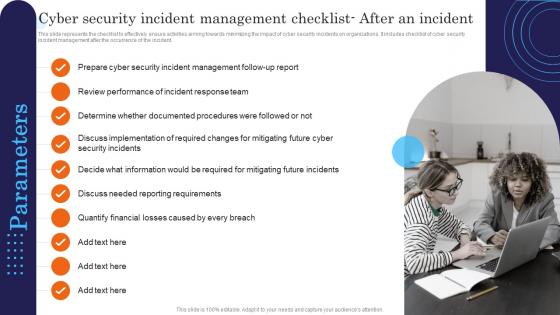 Cyber Security Incident Management Checklist After An Incident Response Strategies Deployment
Cyber Security Incident Management Checklist After An Incident Response Strategies DeploymentThis slide represents the checklist to effectively ensure activities aiming towards minimizing the impact of cyber security incidents on organizations. It includes checklist of cyber security incident management after the occurrence of the incident. Increase audience engagement and knowledge by dispensing information using Cyber Security Incident Management Checklist After An Incident Response Strategies Deployment. This template helps you present information on ten stages. You can also present information on Management, Security, Review using this PPT design. This layout is completely editable so personaize it now to meet your audiences expectations.
-
 Cyber Security Incident Management Checklist Before Incident Response Strategies Deployment
Cyber Security Incident Management Checklist Before Incident Response Strategies DeploymentThis slide represents the checklist to effectively ensure activities aiming towards minimizing the impact of cyber security incidents on organizations. It includes checklist of cyber security incident Management before the occurrence of the incident. Introducing Cyber Security Incident Management Checklist Before Incident Response Strategies Deployment to increase your presentation threshold. Encompassed with nine stages, this template is a great option to educate and entice your audience. Dispence information on Parameters, Security, Management, using this template. Grab it now to reap its full benefits.


